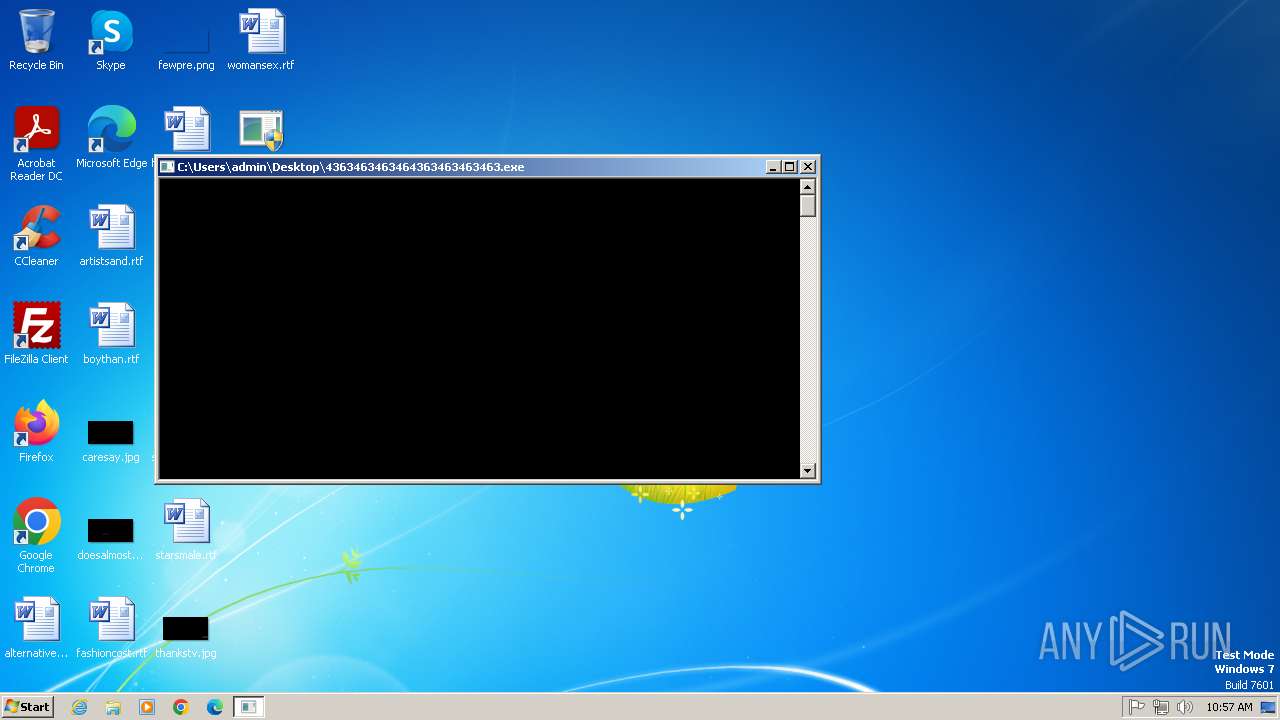
| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/3350ed92-b23b-4361-9fc2-95bbba13eb04 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 16, 2025, 09:57:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
NJRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
- main.exe (PID: 1440)
- dllhost.exe (PID: 3632)
QUASARRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
- Quas_Autre_ncrypt.exe (PID: 2508)
- Sentil.exe (PID: 2508)
- 4363463463464363463463463.exe (PID: 1748)
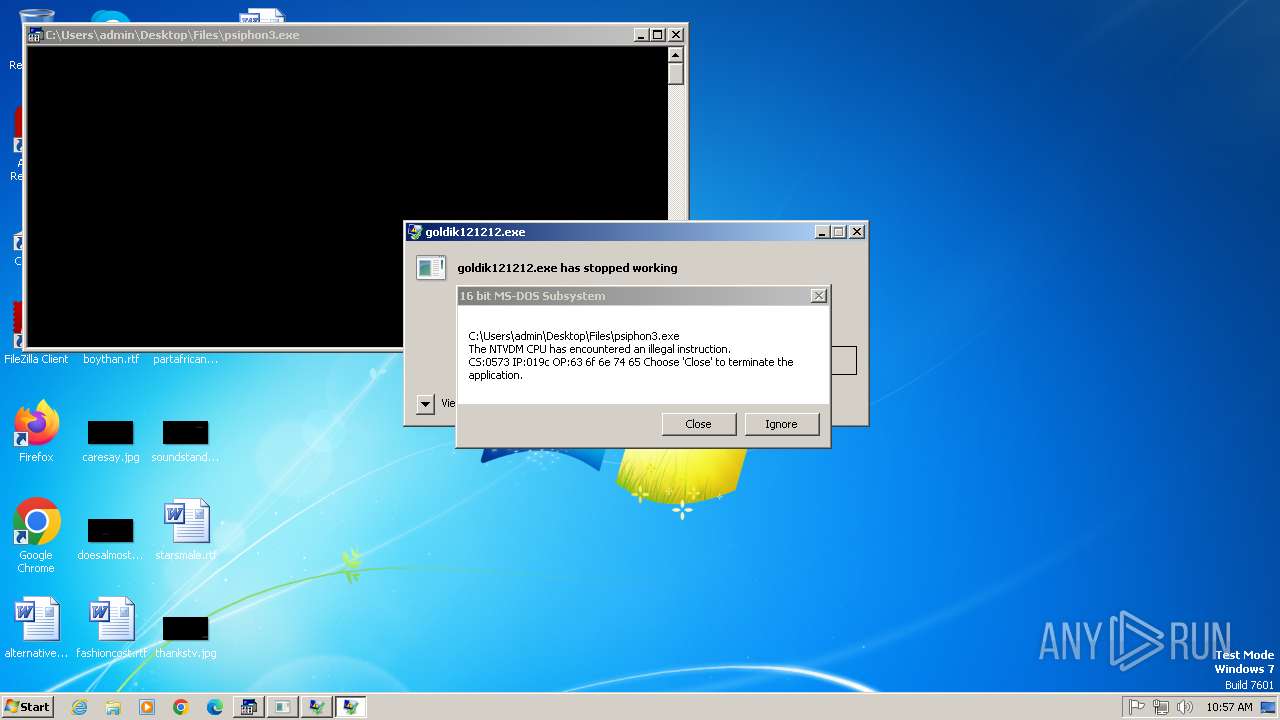
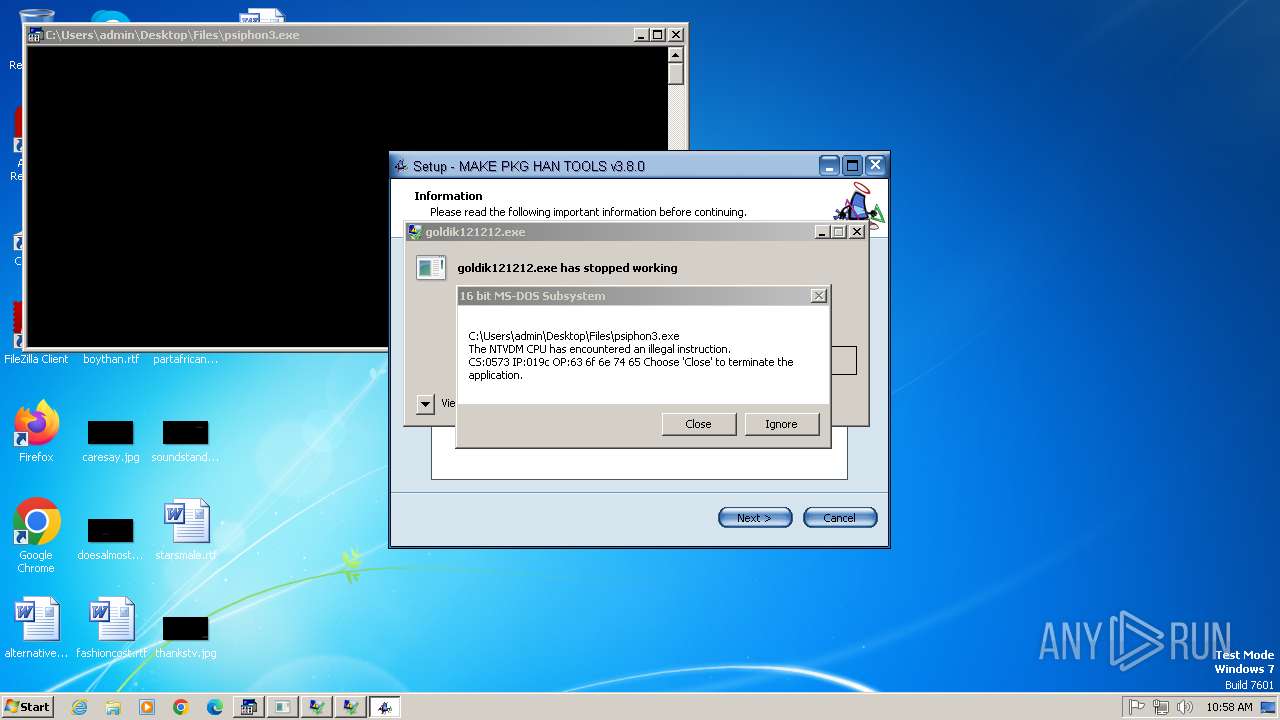
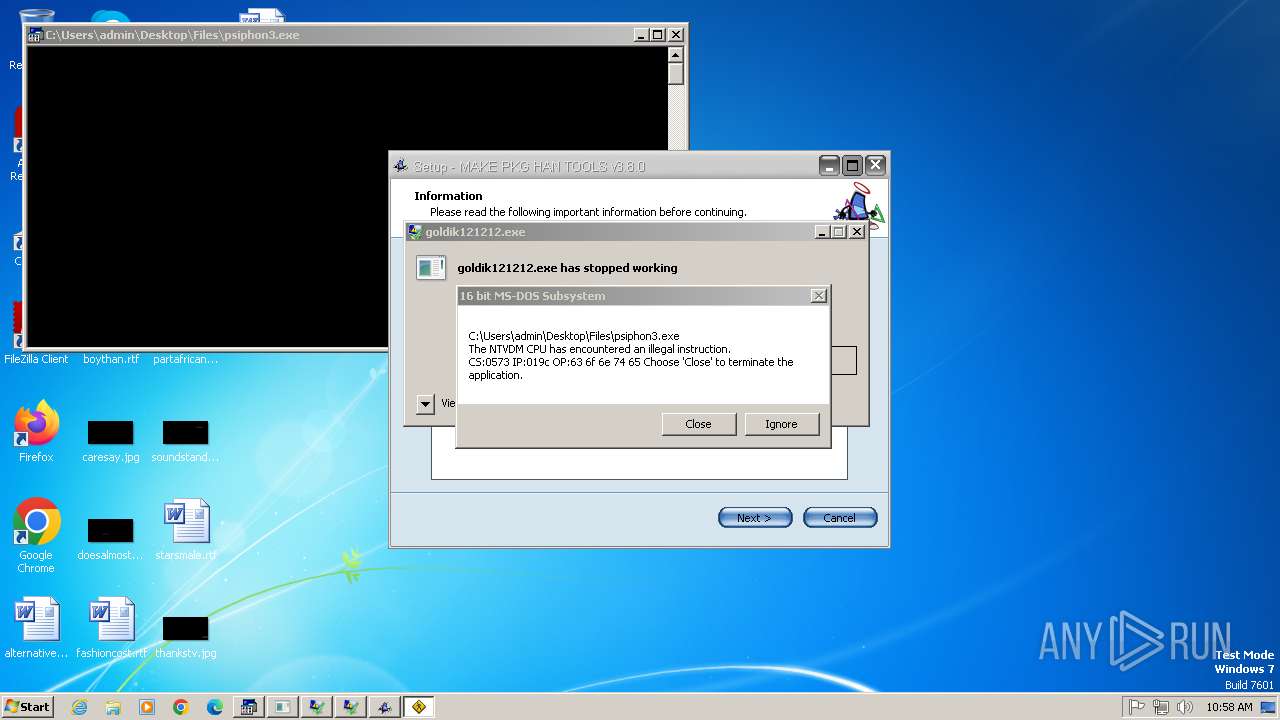
Executing a file with an untrusted certificate
- goldik121212.exe (PID: 2464)
- goldik121212.exe (PID: 3004)
- goldik121212.exe (PID: 2724)
LUMMA has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
ASYNCRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
NJRAT mutex has been found
- main.exe (PID: 1440)
- dllhost.exe (PID: 3632)
- dllhost.exe (PID: 2400)
- dllhost.exe (PID: 3920)
Connects to the CnC server
- svchost.exe (PID: 1080)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 1080)
Uses Task Scheduler to autorun other applications
- Quas_Autre_ncrypt.exe (PID: 2508)
- Clients.exe (PID: 3712)
- 80.exe (PID: 3536)
- Clients.exe (PID: 1276)
- Clients.exe (PID: 3844)
- Clients.exe (PID: 3144)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
- Clients.exe (PID: 124)
- Clients.exe (PID: 3648)
- Client.exe (PID: 752)
- Clients.exe (PID: 3836)
- Client-built10.exe (PID: 996)
- Sentil.exe (PID: 2508)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 1748)
Changes the autorun value in the registry
- dllhost.exe (PID: 3632)
- svchost.exe (PID: 848)
- services.exe (PID: 3588)
Create files in the Startup directory
- dllhost.exe (PID: 3632)
- svchost.exe (PID: 848)
- server.exe (PID: 2428)
Uses Task Scheduler to run other applications
- dllhost.exe (PID: 3632)
GENERIC has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
NjRAT is detected
- svchost.exe (PID: 848)
METERPRETER has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 1748)
STEALER has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
MINER has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
ASYNCRAT has been detected (YARA)
- Discord.exe (PID: 1028)
NJRAT has been detected (YARA)
- svchost.exe (PID: 848)
LimeRAT is detected
- Wsystem.exe (PID: 3860)
XWORM has been detected (YARA)
- services.exe (PID: 3588)
QUASAR has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
- Test2.exe (PID: 2448)
COINMINER has been found (auto)
- 4363463463464363463463463.exe (PID: 1748)
SUSPICIOUS
Reads the Internet Settings
- 4363463463464363463463463.exe (PID: 1748)
- XClient.exe (PID: 2916)
- main.exe (PID: 1440)
- Clients.exe (PID: 3712)
- clientside.exe (PID: 2728)
- 80.exe (PID: 3552)
- asistenciaok3.exe (PID: 3164)
- trojan.exe (PID: 1092)
- 80.exe (PID: 3536)
- Wsystem.exe (PID: 2744)
- Clients.exe (PID: 1276)
- Clients.exe (PID: 3844)
- Clients.exe (PID: 3144)
- Wsystem.exe (PID: 3860)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
Reads settings of System Certificates
- 4363463463464363463463463.exe (PID: 1748)
- goldik121212.exe (PID: 3004)
- alex1213321.exe (PID: 3052)
- Wsystem.exe (PID: 3860)
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 1748)
- Quas_Autre_ncrypt.exe (PID: 2508)
- main.exe (PID: 1440)
- clientside.exe (PID: 2728)
- dllhost.exe (PID: 3632)
- svchost.exe (PID: 848)
- setup.exe (PID: 3404)
- setup.tmp (PID: 3732)
- trojan.exe (PID: 1092)
- services.exe (PID: 3588)
- server.exe (PID: 2428)
- 80.exe (PID: 3536)
- Test2.exe (PID: 2448)
- Client-built10.exe (PID: 996)
- Sentil.exe (PID: 2508)
Adds/modifies Windows certificates
- 4363463463464363463463463.exe (PID: 1748)
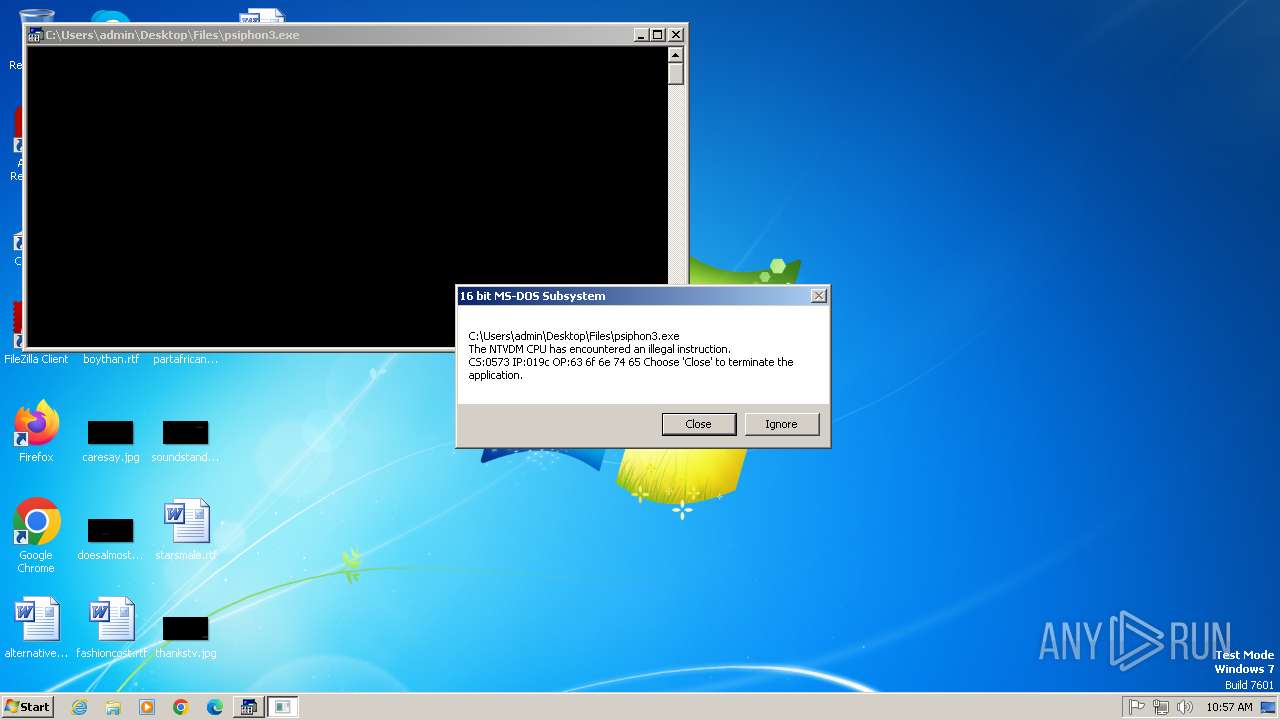
Creates file in the systems drive root
- ntvdm.exe (PID: 2352)
- svchost.exe (PID: 848)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 1748)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 1748)
- main.exe (PID: 1440)
- Clients.exe (PID: 3712)
- clientside.exe (PID: 2728)
- 80.exe (PID: 3552)
- trojan.exe (PID: 1092)
- Wsystem.exe (PID: 2744)
- 80.exe (PID: 3536)
- Clients.exe (PID: 1276)
- Clients.exe (PID: 3844)
- Clients.exe (PID: 3144)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 1748)
- svchost.exe (PID: 1080)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 1748)
Checks for external IP
- svchost.exe (PID: 1080)
- XClient.exe (PID: 2916)
Application launched itself
- goldik121212.exe (PID: 2464)
- 80.exe (PID: 3552)
- alex1213321.exe (PID: 3616)
- Wsystem.exe (PID: 2744)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 1080)
Starts itself from another location
- Quas_Autre_ncrypt.exe (PID: 2508)
- main.exe (PID: 1440)
- clientside.exe (PID: 2728)
- trojan.exe (PID: 1092)
- 80.exe (PID: 3536)
- Client-built10.exe (PID: 996)
- Sentil.exe (PID: 2508)
- Test2.exe (PID: 2448)
The process creates files with name similar to system file names
- main.exe (PID: 1440)
- clientside.exe (PID: 2728)
- dllhost.exe (PID: 3632)
- svchost.exe (PID: 848)
- 4363463463464363463463463.exe (PID: 1748)
- 80.exe (PID: 3536)
- cmd.exe (PID: 2772)
Executing commands from a ".bat" file
- Clients.exe (PID: 3712)
- Clients.exe (PID: 1276)
- Clients.exe (PID: 3844)
- Clients.exe (PID: 3144)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
- Clients.exe (PID: 124)
- Clients.exe (PID: 3648)
- Clients.exe (PID: 3836)
- Client.exe (PID: 1596)
Starts CMD.EXE for commands execution
- Clients.exe (PID: 3712)
- 80.exe (PID: 3552)
- main.exe (PID: 1440)
- Wsystem.exe (PID: 2744)
- Clients.exe (PID: 1276)
- Clients.exe (PID: 3844)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3144)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
- Clients.exe (PID: 124)
- Clients.exe (PID: 3648)
- Clients.exe (PID: 3836)
- Client.exe (PID: 1596)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 2776)
- cmd.exe (PID: 3904)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 1104)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 3208)
- cmd.exe (PID: 3184)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 2676)
- cmd.exe (PID: 1952)
Starts application with an unusual extension
- cmd.exe (PID: 2776)
- cmd.exe (PID: 3904)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 1104)
- cmd.exe (PID: 3208)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 3184)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 2676)
Connects to unusual port
- Discord.exe (PID: 1028)
- 4363463463464363463463463.exe (PID: 1748)
- dllhost.exe (PID: 3632)
- services.exe (PID: 3588)
- Client.exe (PID: 752)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 4072)
- schtasks.exe (PID: 3376)
- schtasks.exe (PID: 608)
- schtasks.exe (PID: 2888)
- schtasks.exe (PID: 1072)
- schtasks.exe (PID: 984)
- schtasks.exe (PID: 1612)
Uses NETSH.EXE to add a firewall rule or allowed programs
- svchost.exe (PID: 848)
- server.exe (PID: 2428)
Uses TASKKILL.EXE to kill process
- dllhost.exe (PID: 3632)
Checks for Java to be installed
- asistenciaok3.exe (PID: 3164)
Reads the Windows owner or organization settings
- setup.tmp (PID: 3732)
Process drops legitimate windows executable
- 4363463463464363463463463.exe (PID: 1748)
- services.exe (PID: 3588)
Starts a Microsoft application from unusual location
- services.exe (PID: 3588)
Found strings related to reading or modifying Windows Defender settings
- Wsystem.exe (PID: 2744)
There is functionality for taking screenshot (YARA)
- setup.tmp (PID: 3732)
The process executes via Task Scheduler
- dllhost.exe (PID: 2400)
- dllhost.exe (PID: 3920)
INFO
Reads the computer name
- 4363463463464363463463463.exe (PID: 1748)
- dc-.exe (PID: 2948)
- main.exe (PID: 1440)
- XClient.exe (PID: 2916)
- Quas_Autre_ncrypt.exe (PID: 2508)
- Discord.exe (PID: 1028)
- goldik121212.exe (PID: 2464)
- goldik121212.exe (PID: 3004)
- 80.exe (PID: 3552)
- dllhost.exe (PID: 3632)
- clientside.exe (PID: 2728)
- Clients.exe (PID: 3712)
- svchost.exe (PID: 848)
- setup.tmp (PID: 3732)
- Yellow%20Pages%20Scraper.exe (PID: 2032)
- asistenciaok3.exe (PID: 3164)
- trojan.exe (PID: 1092)
- services.exe (PID: 3588)
- alex1213321.exe (PID: 3616)
- alex1213321.exe (PID: 3052)
- server.exe (PID: 2428)
- 80.exe (PID: 3536)
- Wsystem.exe (PID: 2744)
- Clients.exe (PID: 1276)
- Wsystem.exe (PID: 3860)
- Clients.exe (PID: 3844)
- STHealthBQ.exe (PID: 392)
- dllhost.exe (PID: 2400)
- Clients.exe (PID: 3144)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3580)
- dllhost.exe (PID: 3920)
- Clients.exe (PID: 1496)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 1748)
- Quas_Autre_ncrypt.exe (PID: 2508)
- XClient.exe (PID: 2916)
- 80.exe (PID: 3552)
- Discord.exe (PID: 1028)
- Clients.exe (PID: 3712)
- main.exe (PID: 1440)
- clientside.exe (PID: 2728)
- goldik121212.exe (PID: 3004)
- dllhost.exe (PID: 3632)
- svchost.exe (PID: 848)
- STHealthBQ.exe (PID: 392)
- Yellow%20Pages%20Scraper.exe (PID: 2032)
- trojan.exe (PID: 1092)
- services.exe (PID: 3588)
- asistenciaok3.exe (PID: 3164)
- server.exe (PID: 2428)
- 80.exe (PID: 3536)
- Wsystem.exe (PID: 2744)
- alex1213321.exe (PID: 3052)
- Clients.exe (PID: 1276)
- Wsystem.exe (PID: 3860)
- Clients.exe (PID: 3844)
- dllhost.exe (PID: 2400)
- Clients.exe (PID: 3144)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
- dllhost.exe (PID: 3920)
Reads Environment values
- 4363463463464363463463463.exe (PID: 1748)
- XClient.exe (PID: 2916)
- Quas_Autre_ncrypt.exe (PID: 2508)
- Clients.exe (PID: 3712)
- dllhost.exe (PID: 3632)
- svchost.exe (PID: 848)
- Clients.exe (PID: 1276)
- Wsystem.exe (PID: 3860)
- Clients.exe (PID: 3844)
- Clients.exe (PID: 3144)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
Checks supported languages
- dc-.exe (PID: 2948)
- main.exe (PID: 1440)
- XClient.exe (PID: 2916)
- Quas_Autre_ncrypt.exe (PID: 2508)
- Discord.exe (PID: 1028)
- goldik121212.exe (PID: 2464)
- clientside.exe (PID: 2728)
- goldik121212.exe (PID: 3004)
- 80.exe (PID: 3552)
- Clients.exe (PID: 3712)
- dllhost.exe (PID: 3632)
- 4363463463464363463463463.exe (PID: 1748)
- chcp.com (PID: 3652)
- svchost.exe (PID: 848)
- setup.exe (PID: 3404)
- setup.tmp (PID: 3732)
- Yellow%20Pages%20Scraper.exe (PID: 2032)
- trojan.exe (PID: 1092)
- services.exe (PID: 3588)
- alex1213321.exe (PID: 3616)
- alex1213321.exe (PID: 3052)
- server.exe (PID: 2428)
- 80.exe (PID: 3536)
- Wsystem.exe (PID: 2744)
- Clients.exe (PID: 1276)
- asistenciaok3.exe (PID: 3164)
- Wsystem.exe (PID: 3860)
- STHealthBQ.exe (PID: 392)
- Clients.exe (PID: 3844)
- chcp.com (PID: 4060)
- dllhost.exe (PID: 2400)
- chcp.com (PID: 492)
- Clients.exe (PID: 3144)
- chcp.com (PID: 3048)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3812)
- chcp.com (PID: 1576)
- chcp.com (PID: 2324)
- dllhost.exe (PID: 3920)
- chcp.com (PID: 2000)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
- chcp.com (PID: 3636)
Disables trace logs
- 4363463463464363463463463.exe (PID: 1748)
- XClient.exe (PID: 2916)
- Wsystem.exe (PID: 3860)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 1748)
- goldik121212.exe (PID: 3004)
- alex1213321.exe (PID: 3052)
- Wsystem.exe (PID: 3860)
Creates files in the program directory
- Quas_Autre_ncrypt.exe (PID: 2508)
- main.exe (PID: 1440)
- asistenciaok3.exe (PID: 3164)
Create files in a temporary directory
- Clients.exe (PID: 3712)
- setup.exe (PID: 3404)
- asistenciaok3.exe (PID: 3164)
- setup.tmp (PID: 3732)
- 4363463463464363463463463.exe (PID: 1748)
- trojan.exe (PID: 1092)
- server.exe (PID: 2428)
- Clients.exe (PID: 1276)
- Clients.exe (PID: 3844)
- Clients.exe (PID: 3144)
- Clients.exe (PID: 3452)
- Clients.exe (PID: 3812)
- Clients.exe (PID: 3580)
- Clients.exe (PID: 1496)
Changes the display of characters in the console
- cmd.exe (PID: 2776)
- cmd.exe (PID: 3904)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 3208)
- cmd.exe (PID: 1104)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 3184)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 2676)
Creates files or folders in the user directory
- dllhost.exe (PID: 3632)
- svchost.exe (PID: 848)
- trojan.exe (PID: 1092)
- services.exe (PID: 3588)
- server.exe (PID: 2428)
- 80.exe (PID: 3536)
The sample compiled with english language support
- setup.tmp (PID: 3732)
- 4363463463464363463463463.exe (PID: 1748)
Process checks Powershell version
- setup.tmp (PID: 3732)
Checks proxy server information
- asistenciaok3.exe (PID: 3164)
.NET Reactor protector has been detected
- goldik121212.exe (PID: 2464)
- STHealthBQ.exe (PID: 392)
Compiled with Borland Delphi (YARA)
- setup.exe (PID: 3404)
- setup.tmp (PID: 3732)
Detects InnoSetup installer (YARA)
- setup.exe (PID: 3404)
- setup.tmp (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1028) Discord.exe
C2 (1)2.tcp.eu.ngrok.io
Ports (1)19695
Version0.5.8
BotnetDefault
Options
AutoRunfalse
Mutexgonq3XlXWgiz
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAP0oyiOz3B6IlGmGQxDdOTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjQxMjI3MTYwODExWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAOL81KWlg/fnIqdbRhcZAWTJXSZyblsfdmVXtpoDKqUW3mZW6wAser7vp+5ZFOyoziZ07q+uPix+...
Server_SignatureF16HEKRGmDveP59ZWNHrIKJnOoOgkTCqtfpo0YdfgUvZsl7RlghXY1RewN8Z9fOLS3grlsnbISI1AN8PbruBAbVYvKpFTE4BrcyAoPqcO7j0j3cYR/PGxs92VgHC08DV5LTssICTfAh3sCTLYfaxclSC+hO024lZ7JVPyyjYroqJ0N4z1QFz84orIFDeer44n9dT5nawSG+RU1dJggO/i9aBx873aYOsN4/3LAXOxeahVjsPuAzigBeQEuzf0yOGpR8KhZYCIxqpHzJwh//A57xeg5Wt0bV2Y/uey1D329GW...
Keys
AESf4497857b1b9e862c007143c89a14df64950947c72036f15cc987cbb4caf7375
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
NjRat
(PID) Process(848) svchost.exe
C2moneroman.ddns.net
Ports1194
BotnetHacKed_NotFully
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\5f1c1f4a8f4a8082788e31e499b05f88
Splitter|'|'|
Versionim523
XWorm
(PID) Process(3588) services.exe
C2onlinegames.ddnsfree.com:2004
Keys
AES<01234567890>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.6
MutexLYpVZXdS0V7g4Ng2
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
235
Monitored processes
132
Malicious processes
27
Suspicious processes
21
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\SubDare\Clients.exe" | C:\Program Files\SubDare\Clients.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Quasar Client Exit code: 0 Version: 1.4.1 Modules
| |||||||||||||||
| 184 | "schtasks" /create /tn "WindowsSystemTask" /sc ONLOGON /tr "C:\Program Files\SubDare\Clients.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Clients.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Users\admin\Desktop\Files\STHealthBQ.exe" | C:\Users\admin\Desktop\Files\STHealthBQ.exe | — | 4363463463464363463463463.exe | |||||||||||
User: admin Integrity Level: HIGH Description: STHealthBQ Version: 1.0.0.0 Modules
| |||||||||||||||
| 492 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | schtasks /create /f /sc ONLOGON /RL HIGHEST /tn LimeRAT-Admin /tr "'C:\Users\admin\AppData\Roaming\DefenderUpdate\Wsystem.exe'" | C:\Windows\System32\schtasks.exe | — | 80.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 608 | schtasks /delete /tn "MicrosoftEdgeUpdateTaskMachine" /f | C:\Windows\System32\schtasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | "C:\Program Files\kazeku\Client.exe" | C:\Program Files\kazeku\Client.exe | Client-built10.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Quasar Client Version: 1.4.1 Modules
| |||||||||||||||
| 848 | "C:\Windows\svchost.exe" | C:\Windows\svchost.exe | clientside.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
NjRat(PID) Process(848) svchost.exe C2moneroman.ddns.net Ports1194 BotnetHacKed_NotFully Options Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\5f1c1f4a8f4a8082788e31e499b05f88 Splitter|'|'| Versionim523 | |||||||||||||||
| 984 | schtasks /delete /tn "MicrosoftEdgeUpdateTaskMachine" /f | C:\Windows\System32\schtasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | "C:\Users\admin\Desktop\Files\Client-built10.exe" | C:\Users\admin\Desktop\Files\Client-built10.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Quasar Client Exit code: 3 Version: 1.4.1 Modules
| |||||||||||||||
Total events
46 935
Read events
45 639
Write events
1 268
Delete events
28
Modification events
| (PID) Process: | (1080) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Nla\Cache\Intranet |
| Operation: | write | Name: | {4040CF00-1B3E-486A-B407-FA14C56B6FC0} |
Value: D4DA6D3E3157 | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1748) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
37
Suspicious files
9
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2352 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs299C.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 1748 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\Discord.exe | executable | |
MD5:9DCD35FE3CAFEC7A25AA3CDD08DED1F4 | SHA256:CE4F85D935FE68A1C92469367B945F26C40C71FEB656EF844C30A5483DC5C0BE | |||
| 1748 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\main.exe | executable | |
MD5:915756AE44759560E8476467163B0F5D | SHA256:0A5FE6735794D87D1CB917AA4B92947F571EFF6B5541008CC1F76A666DF4FBFB | |||
| 1748 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\psiphon3.exe | html | |
MD5:EA06B65498F0FD58E14B8EB30A860DCC | SHA256:6098D8EAF10B32F8881C56BAD9D5B5B20074B2CA27E4492D0A6170F9382B39C0 | |||
| 2728 | clientside.exe | C:\Windows\svchost.exe | executable | |
MD5:AA83D654A4475F46E61C95FBD89EE18F | SHA256:B89B75073B10B07BDBB1B6C9D718A6CFDC3F595D8EAC444088E7C0692C304310 | |||
| 1748 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\Quas_Autre_ncrypt.exe | executable | |
MD5:2BE44F2F5EA83CBC61FBD13B50C0F88C | SHA256:CD3DEA94C6C2DDB8EFC1EFA8C5E105EDDE87ECBB18AB75B5D5FB7BC502542F5A | |||
| 848 | svchost.exe | C:\svchost.exe | executable | |
MD5:AA83D654A4475F46E61C95FBD89EE18F | SHA256:B89B75073B10B07BDBB1B6C9D718A6CFDC3F595D8EAC444088E7C0692C304310 | |||
| 1748 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\80.exe | executable | |
MD5:AB3338C54E7C9C6C3281D9C603371018 | SHA256:44F974DCA0393AB17C93643EFEE874E36E826199407360943F5F6F20A37A9C2B | |||
| 2352 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs298C.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 848 | svchost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\5f1c1f4a8f4a8082788e31e499b05f88.exe | executable | |
MD5:AA83D654A4475F46E61C95FBD89EE18F | SHA256:B89B75073B10B07BDBB1B6C9D718A6CFDC3F595D8EAC444088E7C0692C304310 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
136
DNS requests
45
Threats
59
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1748 | 4363463463464363463463463.exe | GET | 301 | 140.82.121.4:80 | http://github.com/minhdmkk6/bot1/raw/refs/heads/main/XClient.exe | unknown | — | — | whitelisted |
1748 | 4363463463464363463463463.exe | GET | 200 | 51.195.19.98:80 | http://dddos.persiangig.com/.tslijj732W/other/psiphon3.exe | unknown | — | — | unknown |
1748 | 4363463463464363463463463.exe | GET | 200 | 93.176.52.107:80 | http://93.176.52.107/Quas_Autre_ncrypt.exe | unknown | — | — | malicious |
1748 | 4363463463464363463463463.exe | GET | 301 | 140.82.121.4:80 | http://github.com/jackyz777/activebypass/raw/refs/heads/main/Discord.exe | unknown | — | — | whitelisted |
2916 | XClient.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
1748 | 4363463463464363463463463.exe | GET | 200 | 188.165.53.185:80 | http://faubourg-70.fr/1/80.exe | unknown | — | — | malicious |
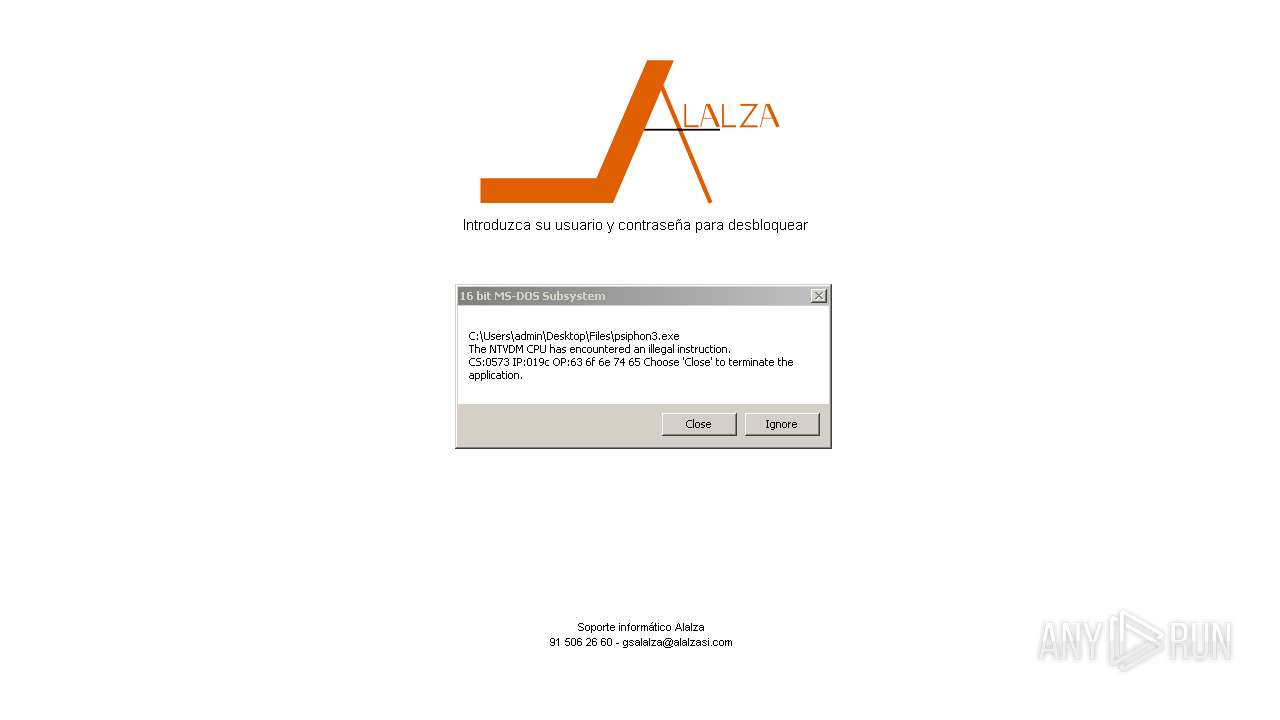
1748 | 4363463463464363463463463.exe | GET | 200 | 217.160.0.100:80 | http://loginods.alalzasi.com/asistenciaok3.exe | unknown | — | — | unknown |
1748 | 4363463463464363463463463.exe | GET | 200 | 47.104.173.216:9876 | http://47.104.173.216:9876/STHealthBQ.exe | unknown | — | — | unknown |
1748 | 4363463463464363463463463.exe | GET | 200 | 23.50.131.200:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a882559faf1bc9a9 | unknown | — | — | whitelisted |
3164 | asistenciaok3.exe | GET | 200 | 217.160.0.100:80 | http://loginods.alalzasi.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1748 | 4363463463464363463463463.exe | 151.101.130.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1748 | 4363463463464363463463463.exe | 89.163.145.170:443 | envs.sh | myLoc managed IT AG | DE | unknown |
1748 | 4363463463464363463463463.exe | 51.195.19.98:80 | dddos.persiangig.com | OVH SAS | FR | suspicious |
1748 | 4363463463464363463463463.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
1748 | 4363463463464363463463463.exe | 140.82.121.4:80 | github.com | GITHUB | US | whitelisted |
1748 | 4363463463464363463463463.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
1748 | 4363463463464363463463463.exe | 93.176.52.107:80 | — | — | MQ | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
envs.sh |
| unknown |
dddos.persiangig.com |
| unknown |
raw.githubusercontent.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
ip-api.com |
| whitelisted |
faubourg-70.fr |
| malicious |
pleasedcfrown.biz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1748 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1748 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
1748 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
1748 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1080 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
1080 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2916 | XClient.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2916 | XClient.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
1748 | 4363463463464363463463463.exe | A Network Trojan was detected | ET MALWARE JS/Nemucod requesting EXE payload 2016-02-01 |
Process | Message |
|---|---|
XClient.exe | CLR: Managed code called FailFast without specifying a reason.
|
80.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
80.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
80.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
80.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
80.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
80.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
80.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
80.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
80.exe |
*** Status propagated: -1073741471
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 147
|