| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/13c7e3f4-3347-4374-8e09-fc73129cac38 |
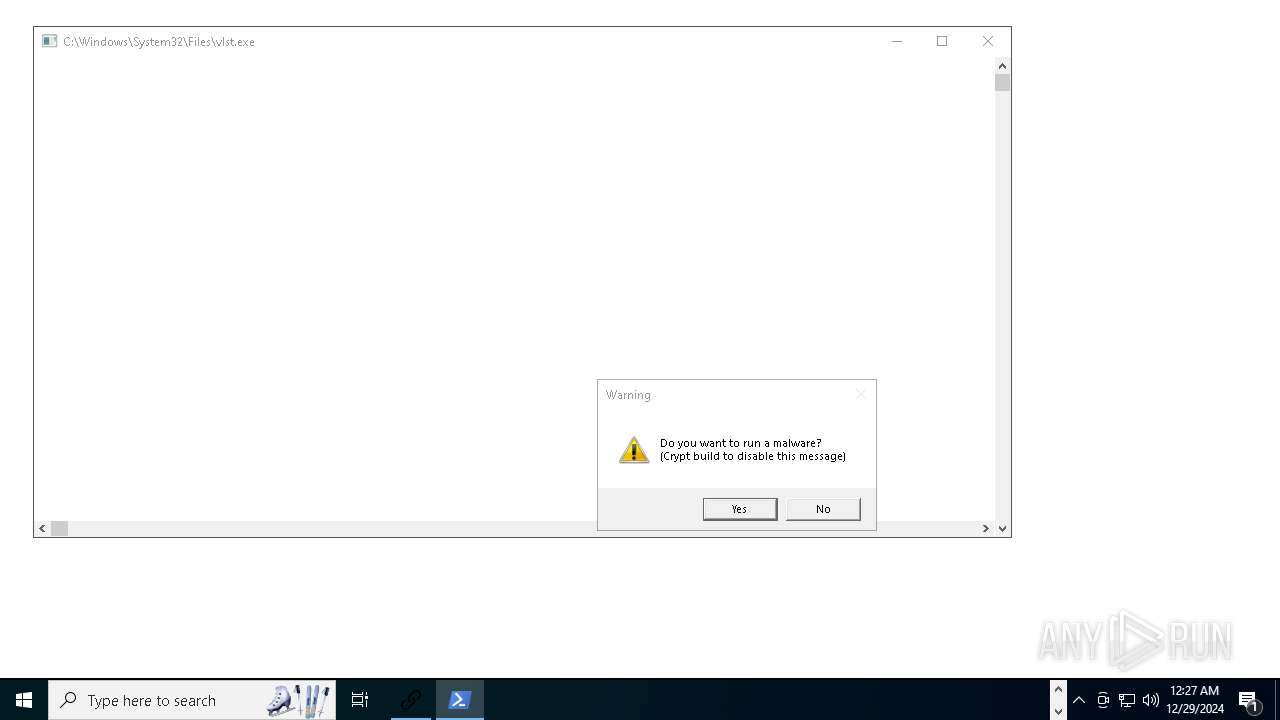
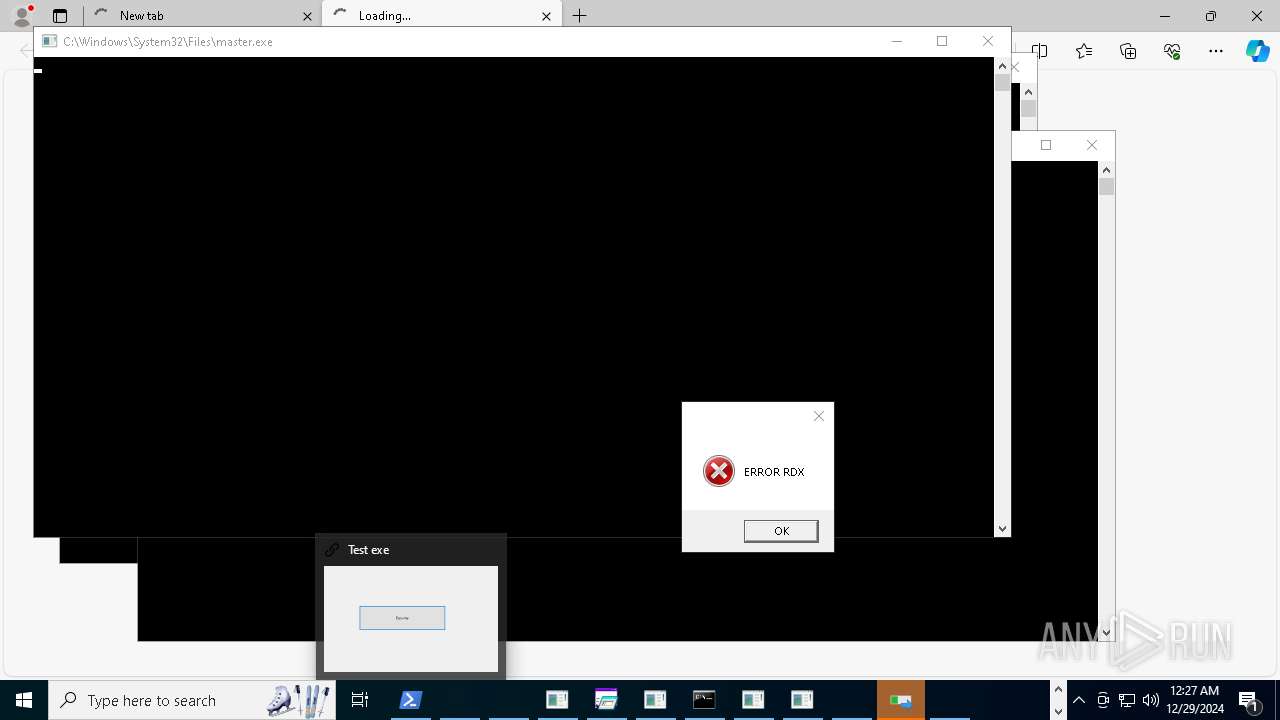
| Verdict: | Malicious activity |
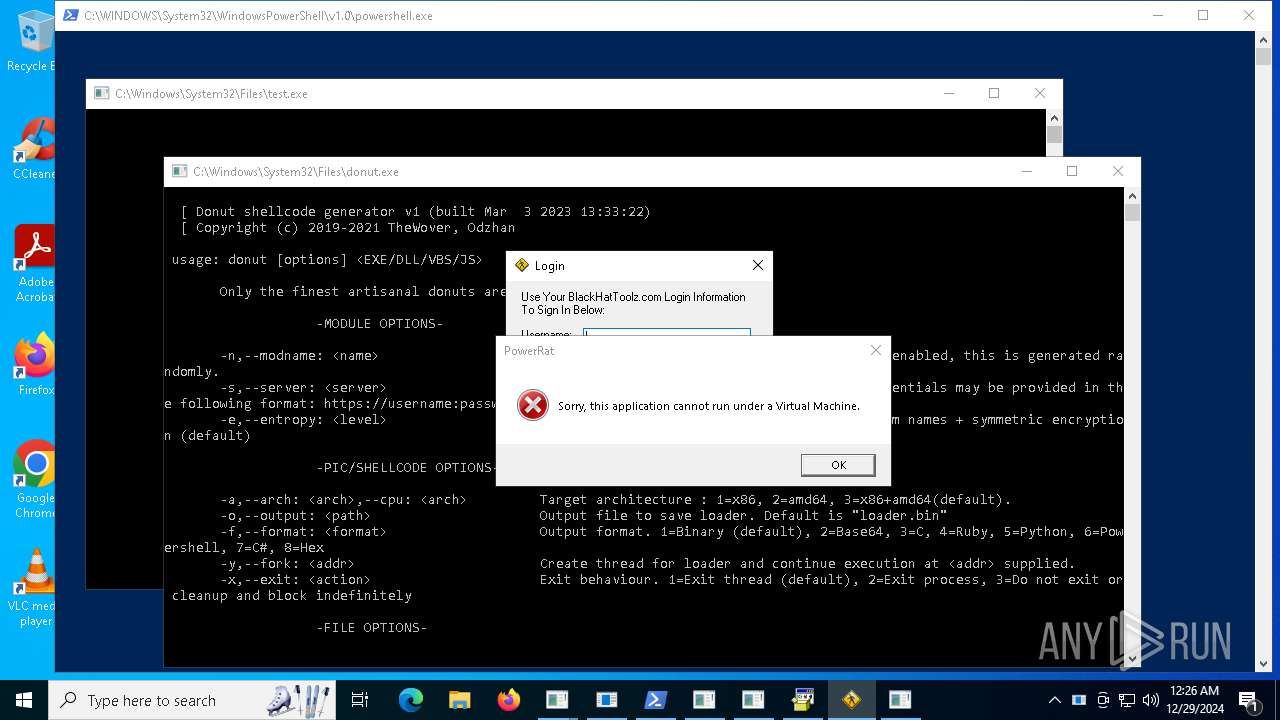
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | December 29, 2024, 00:24:42 |
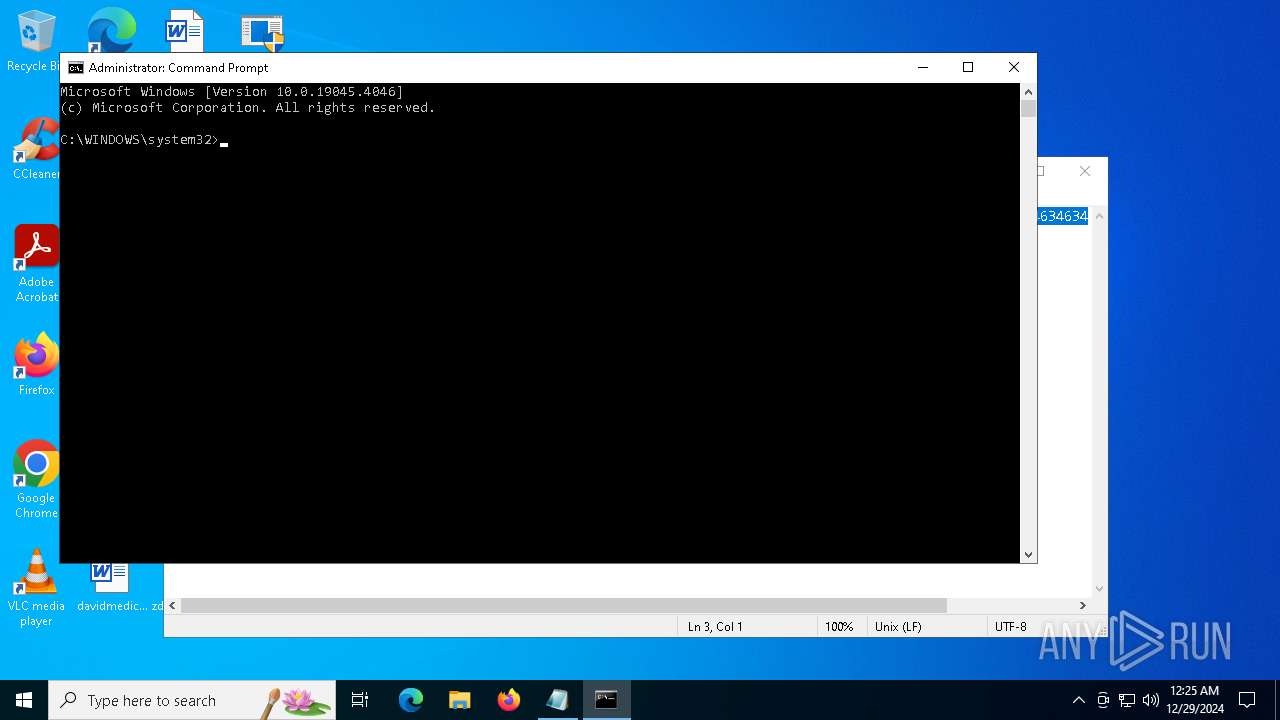
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 5992)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 5460)
GENERIC has been found (auto)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 5316)
- ovrflw.exe (PID: 21764)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 3288)
NJRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 9488)
- testingg.exe (PID: 15116)
- server.exe (PID: 15244)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 7400)
- Minet.exe (PID: 16568)
- server.exe (PID: 19312)
- 4363463463464363463463463.exe (PID: 3144)
- Steam.Upgreyd.exe (PID: 16648)
- 4363463463464363463463463.exe (PID: 5740)
- njSilent.exe (PID: 21656)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 6756)
- cnct.exe (PID: 24284)
- 4363463463464363463463463.exe (PID: 7928)
- svchost.exe (PID: 17916)
- main.exe (PID: 26140)
VIDAR has been found (auto)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 9756)
VIDAR mutex has been found
- TPB-1.exe (PID: 15164)
- build_2024-07-27_00-41.exe (PID: 19736)
- pjthjsdjgjrtavv.exe (PID: 21648)
- pyjnkasedf.exe (PID: 20320)
- jtkhikadjthsad.exe (PID: 23036)
Changes the autorun value in the registry
- System.exe (PID: 15344)
- NOTallowedtocrypt.exe (PID: 16236)
- 76y5trfed675ytg.exe (PID: 17492)
- curlapp64.exe (PID: 19068)
- NVIDIA.exe (PID: 18480)
- CoronaVirus.exe (PID: 16056)
- server.exe (PID: 19312)
- bildnewl.exe (PID: 19644)
- nano.exe (PID: 20220)
- Steam.Upgreyd.exe (PID: 16648)
- system32.exe (PID: 19376)
- ovrflw.exe (PID: 21764)
- NJRat.exe (PID: 18648)
- networkmanager.exe (PID: 21756)
- 4.exe (PID: 23052)
- nbothjkd.exe (PID: 15240)
- Survox.exe (PID: 23068)
- kitty.exe (PID: 23488)
- svhostc.exe (PID: 26936)
- newfile.exe (PID: 18724)
- svchost.exe (PID: 17916)
- NOTallowedtocrypt.exe (PID: 28284)
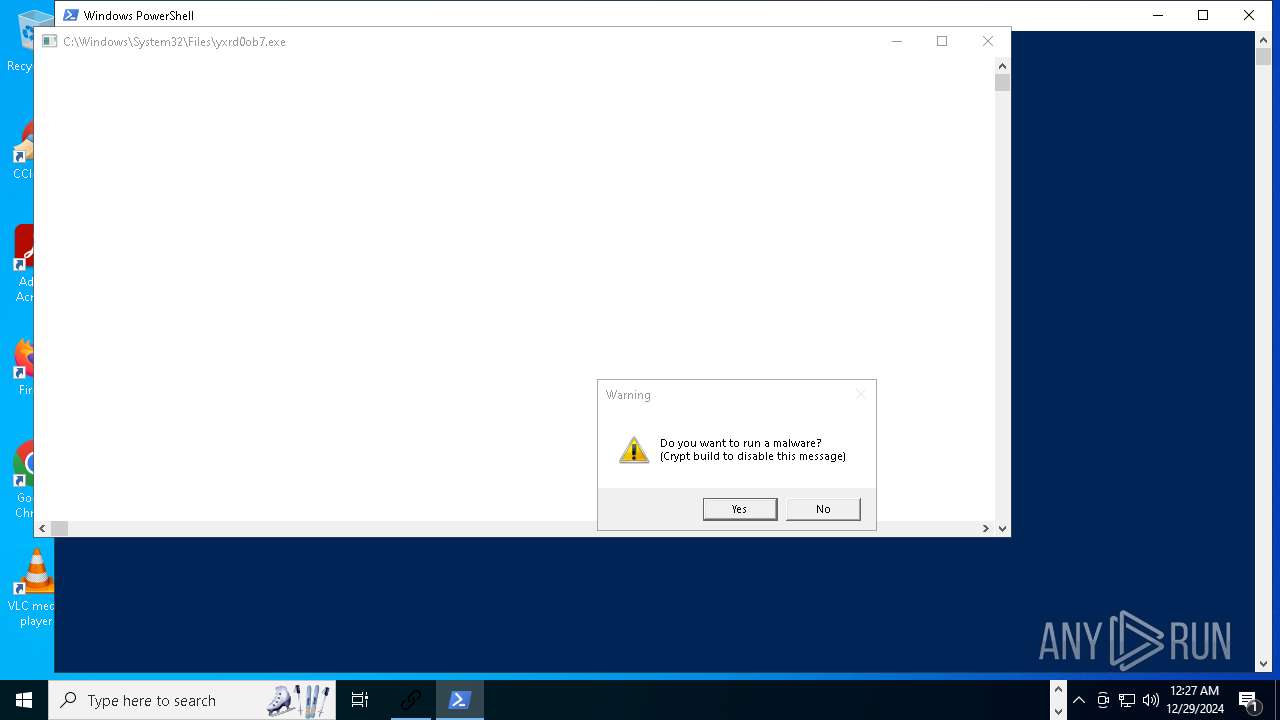
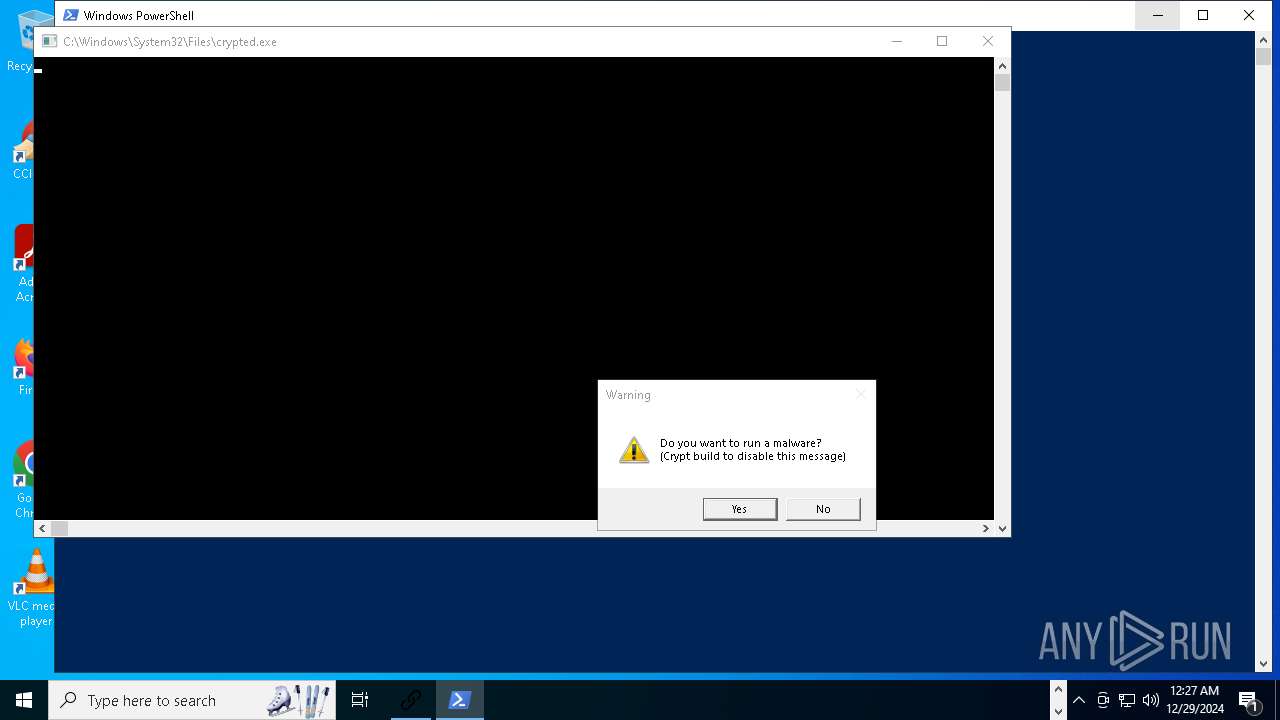
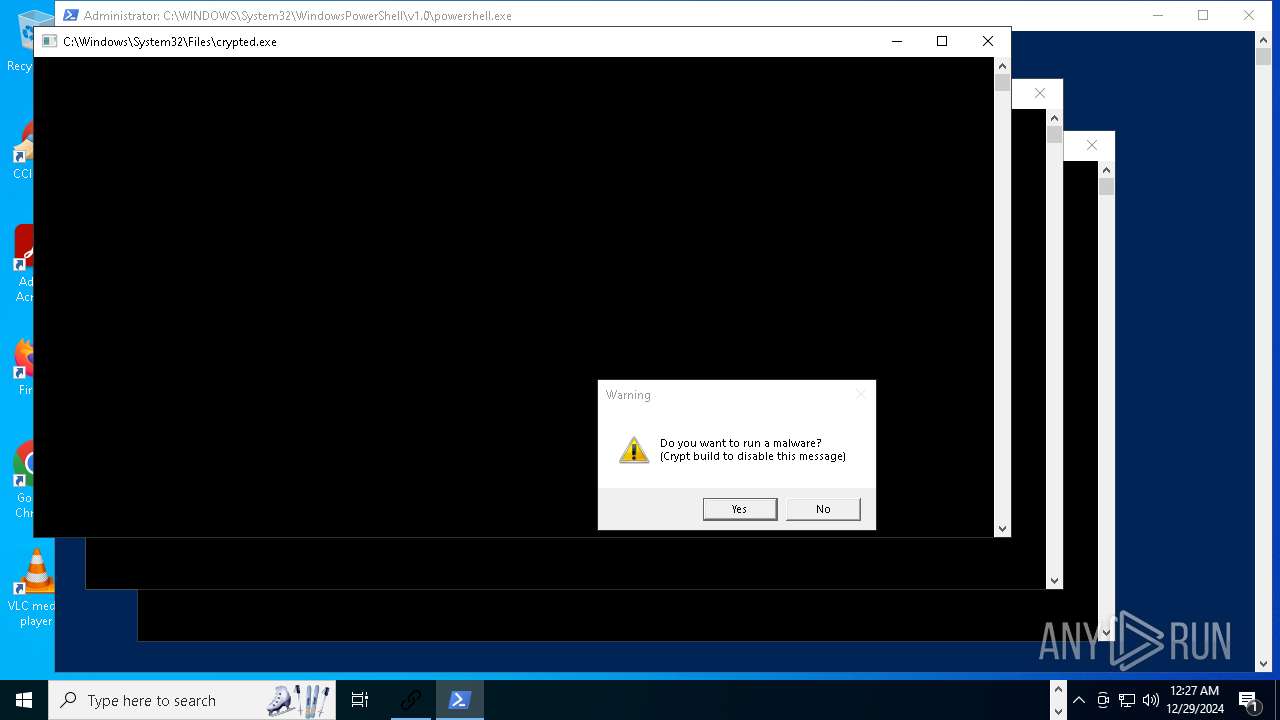
Executing a file with an untrusted certificate
- NorthSperm.exe (PID: 15044)
- kxfh9qhs.exe (PID: 5268)
- GIFT-INFO.lMG.exe (PID: 6952)
- qth5kdee.exe (PID: 21804)
- PURCHASE%20ORDER%20006-2024%20GIA-AV%20Rev%201_pdf.exe (PID: 22076)
- chicken123.exe (PID: 22060)
- GIFT-INFO.lMG.exe (PID: 22440)
- 2kudv4ea.exe (PID: 23060)
- 2kudv4ea.exe (PID: 23720)
- build.exe (PID: 17784)
- xworm.exe (PID: 26160)
- soft2.exe (PID: 20204)
- PctOccurred.exe (PID: 21796)
- InstallerPack_20.1.23770_win64.exe (PID: 23116)
- hhnjqu9y.exe (PID: 10960)
- phost.exe (PID: 27776)
- x6uvjuko.exe (PID: 27784)
Create files in the Startup directory
- server.exe (PID: 15244)
- baedawdgh.exe (PID: 14984)
- CoronaVirus.exe (PID: 16056)
- server.exe (PID: 19312)
- Steam.Upgreyd.exe (PID: 16648)
- imagelogger.exe (PID: 19168)
- NJRat.exe (PID: 18648)
- system32.exe (PID: 19376)
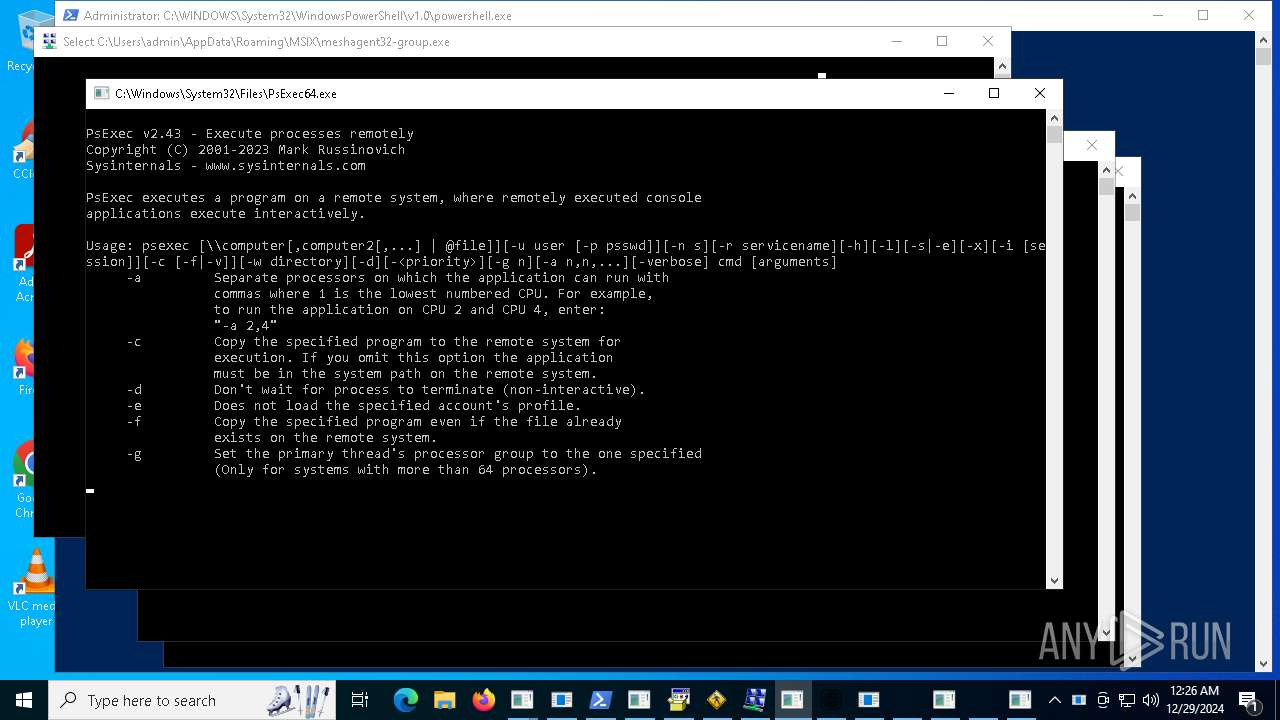
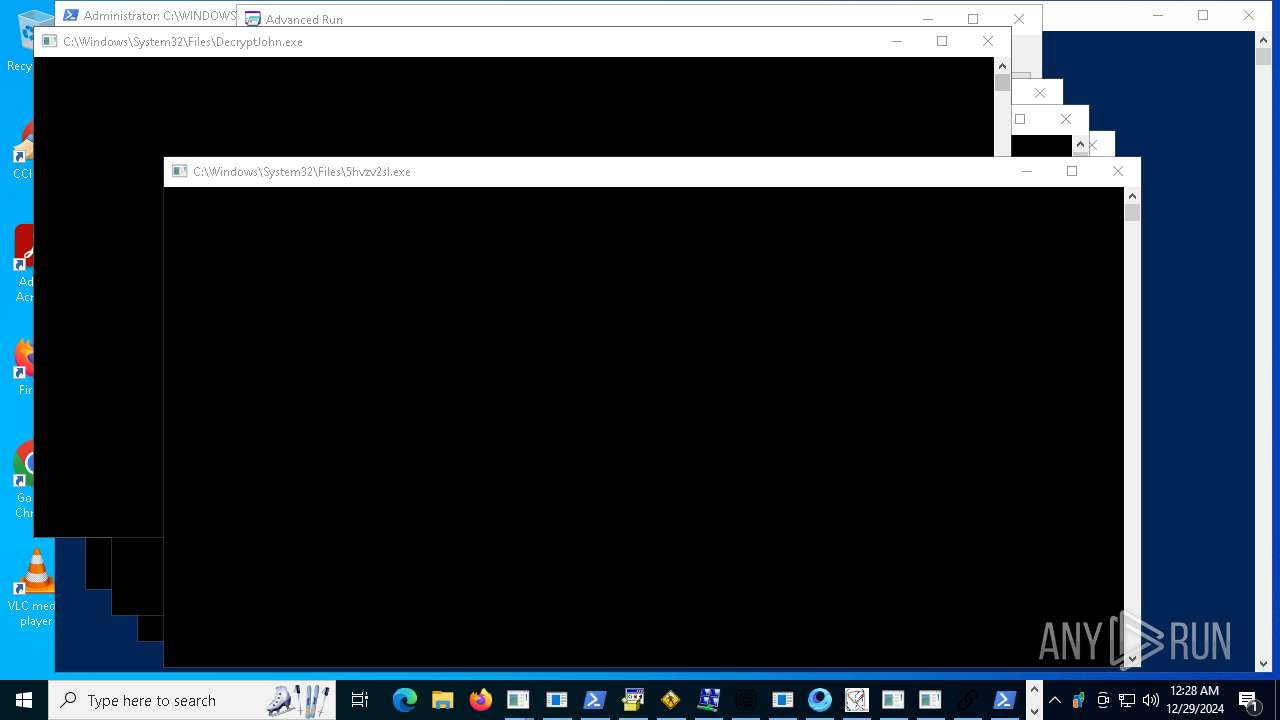
Bypass execution policy to execute commands
- powershell.exe (PID: 15536)
- powershell.exe (PID: 15552)
- powershell.exe (PID: 15568)
- powershell.exe (PID: 1016)
- powershell.exe (PID: 21928)
- powershell.exe (PID: 10296)
- powershell.exe (PID: 16928)
- powershell.exe (PID: 27800)
- powershell.exe (PID: 27912)
Changes powershell execution policy (Bypass)
- ._cache_System.exe (PID: 4328)
- svchost.exe (PID: 3124)
- XClient.exe (PID: 6212)
- crss.exe (PID: 16588)
- com%20surrogate.exe (PID: 19216)
- cmd.exe (PID: 23944)
- fuag.exe (PID: 20992)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
Adds path to the Windows Defender exclusion list
- XClient.exe (PID: 6212)
- ._cache_System.exe (PID: 4328)
- svchost.exe (PID: 3124)
- crss.exe (PID: 16588)
- TTDesktop18.exe (PID: 17004)
- com%20surrogate.exe (PID: 19216)
- powershell.exe (PID: 19000)
- fuag.exe (PID: 20992)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
Actions looks like stealing of personal data
- TPB-1.exe (PID: 15164)
- gagagggagagag.exe (PID: 19988)
- CoronaVirus.exe (PID: 16056)
- gsprout.exe (PID: 19788)
- bypass.exe (PID: 22756)
- build.exe (PID: 17784)
- k360.exe (PID: 23076)
- pjthjsdjgjrtavv.exe (PID: 21648)
- lkyhjksefa.exe (PID: 21388)
- RegAsm.exe (PID: 22236)
- build.exe (PID: 19688)
- qth5kdee.exe (PID: 21804)
Connects to the CnC server
- Synaptics.exe (PID: 776)
- svchost.exe (PID: 2192)
- server.exe (PID: 15244)
- MSBuild.exe (PID: 18076)
- Server1.exe (PID: 16664)
- nano.exe (PID: 20220)
- server.exe (PID: 19312)
- gsprout.exe (PID: 19788)
- 22.exe (PID: 20784)
- build.exe (PID: 19688)
- evetbeta.exe (PID: 21776)
- 4363463463464363463463463.exe (PID: 10580)
- system32.exe (PID: 19376)
- xmbld.exe (PID: 18544)
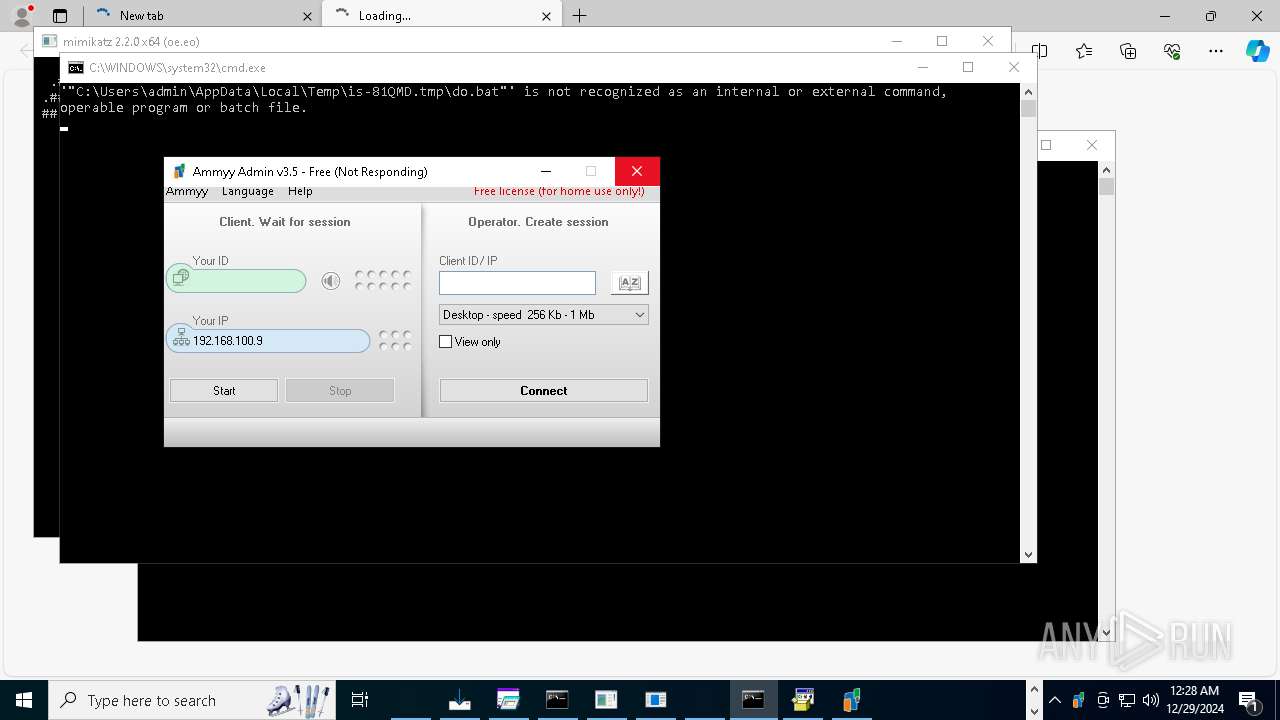
- Ammyy.exe (PID: 27280)
- 4363463463464363463463463.exe (PID: 8320)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 14964)
- kitty.exe (PID: 23488)
SYSTEMBC has been found (auto)
- 4363463463464363463463463.exe (PID: 13888)
LUMMA has been found (auto)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 1804)
ASYNCRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 11748)
- imagelogger.exe (PID: 19168)
- AsyncClient.exe (PID: 16700)
- 4363463463464363463463463.exe (PID: 13888)
- Discord.exe (PID: 16680)
- 4363463463464363463463463.exe (PID: 3288)
- temp.exe (PID: 18792)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 3988)
PHORPIEX has been detected (SURICATA)
- svchost.exe (PID: 2192)
STEALER has been found (auto)
- 4363463463464363463463463.exe (PID: 6664)
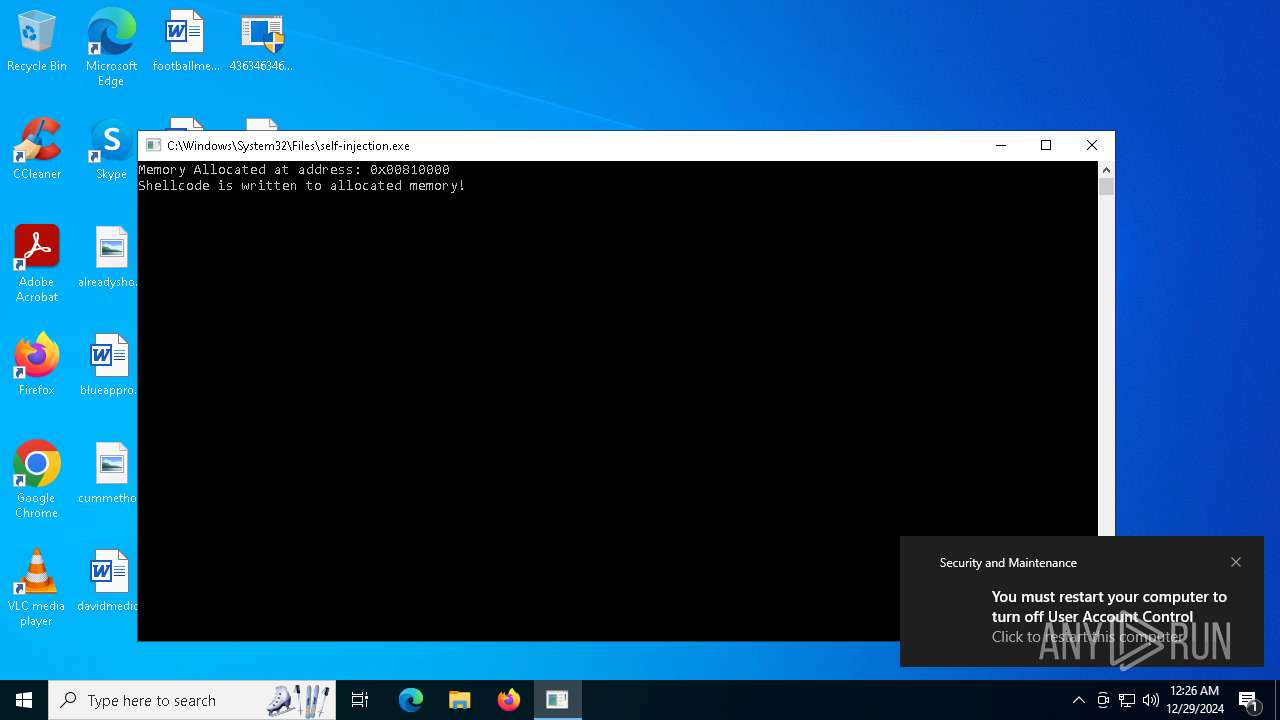
UAC/LUA settings modification
- reg.exe (PID: 16820)
- reg.exe (PID: 18484)
- reg.exe (PID: 19016)
- wefhrf.exe (PID: 21204)
METASPLOIT has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 13868)
CRYPTBOT has been found (auto)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 9556)
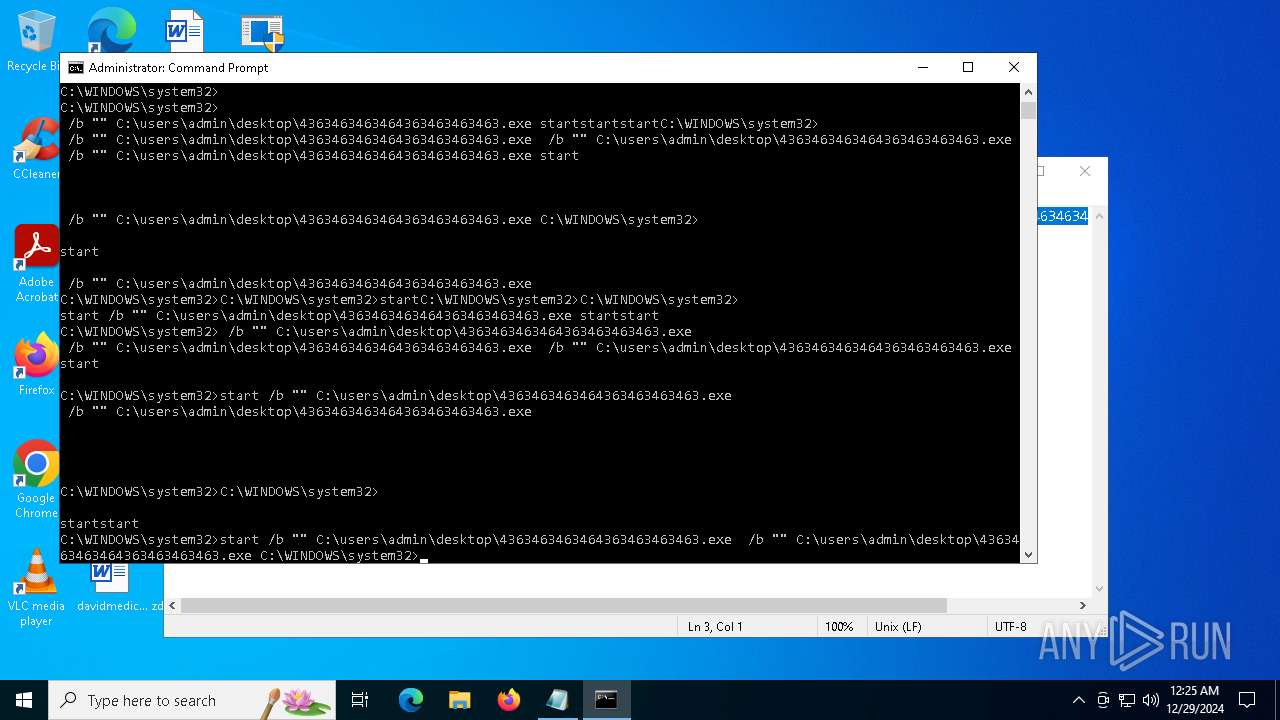
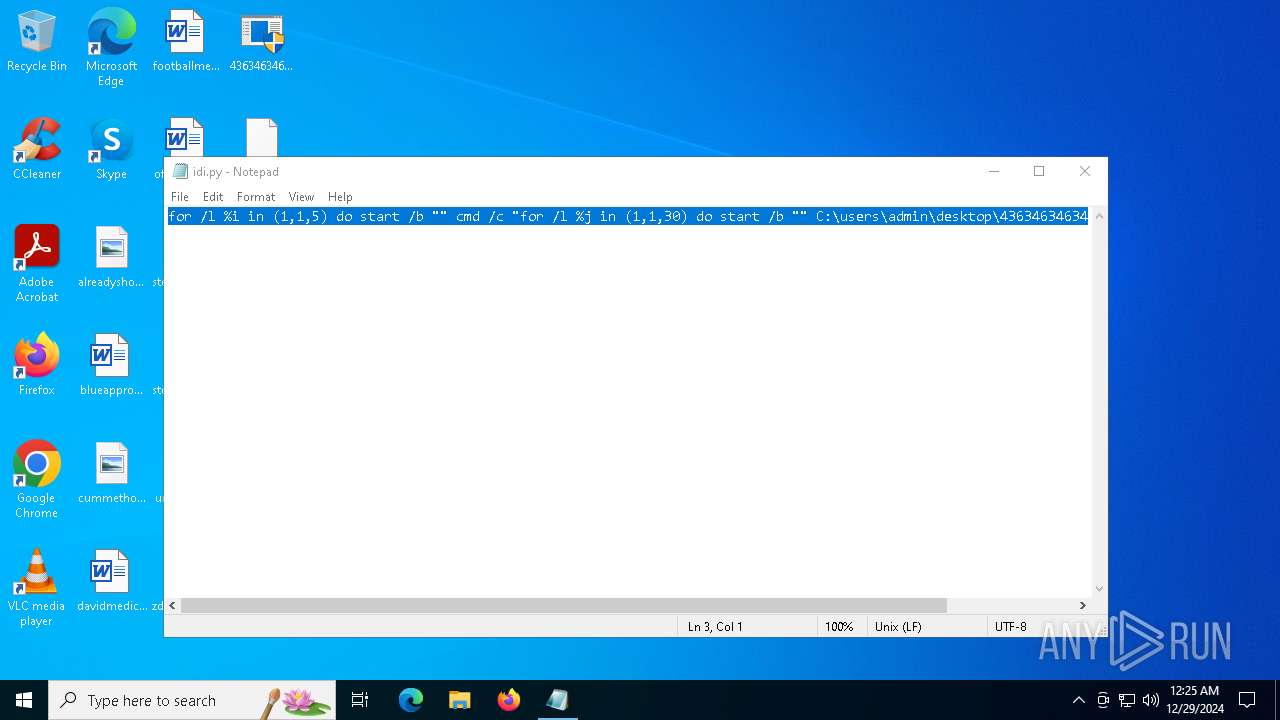
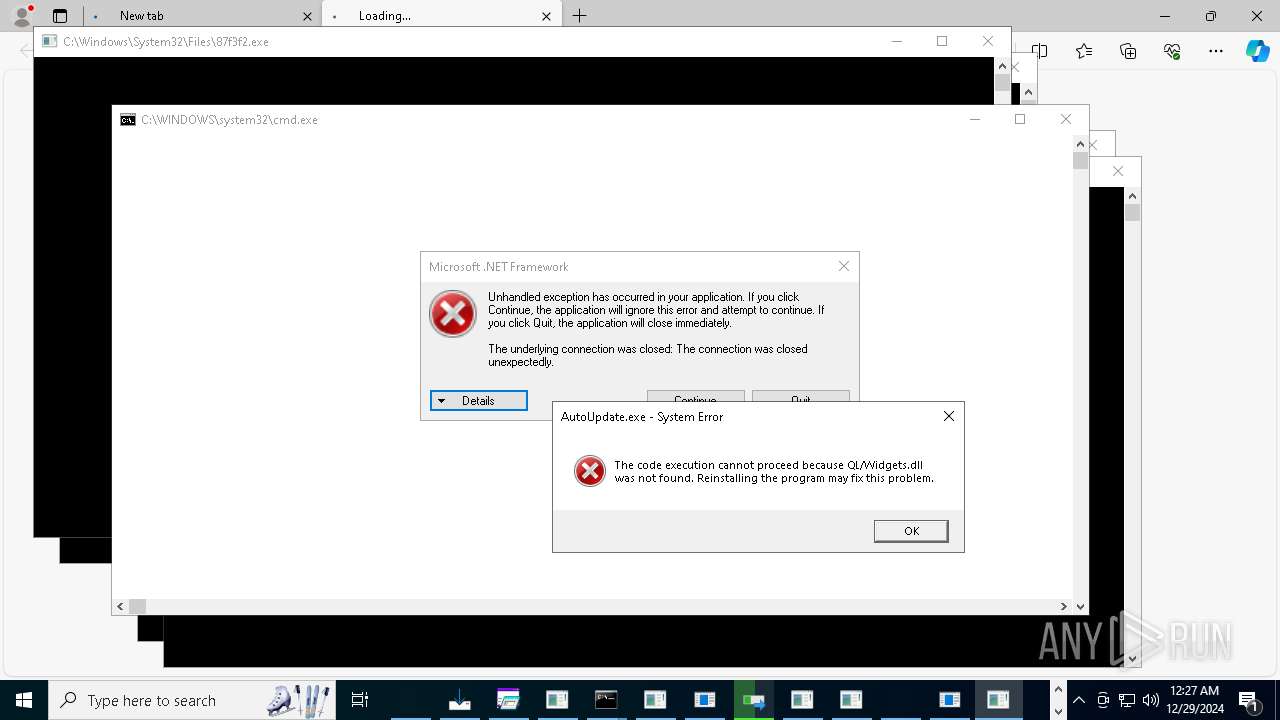
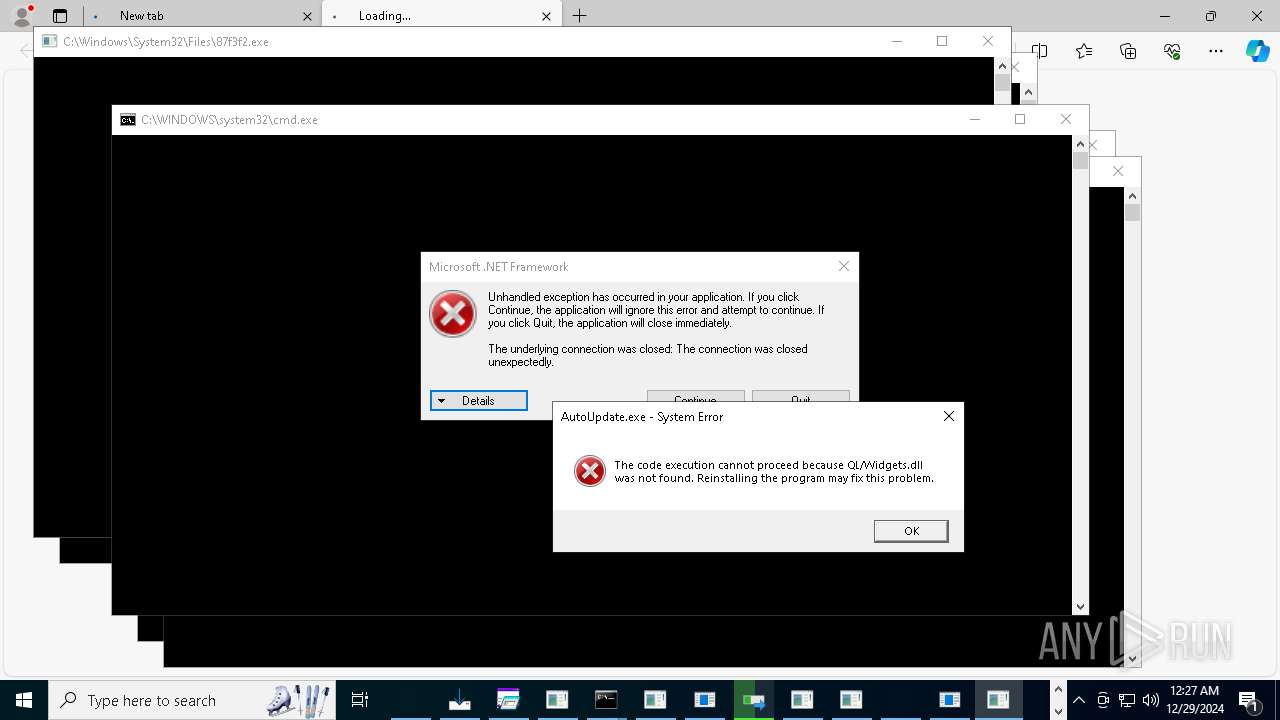
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 17588)
RHADAMANTHYS has been found (auto)
- 4363463463464363463463463.exe (PID: 11872)
METERPRETER has been found (auto)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 13684)
Starts CMD.EXE for self-deleting
- feb9sxwk.exe (PID: 18348)
BRUTERATEL has been found (auto)
- 4363463463464363463463463.exe (PID: 9844)
NJRAT mutex has been found
- Steam.Upgreyd.exe (PID: 16648)
- system32.exe (PID: 19376)
NJRAT has been detected (SURICATA)
- server.exe (PID: 15244)
- Server1.exe (PID: 16664)
- server.exe (PID: 19312)
- system32.exe (PID: 19376)
SLIVER has been found (auto)
- 4363463463464363463463463.exe (PID: 3724)
PURELOGSTEALER has been found (auto)
- 4363463463464363463463463.exe (PID: 11848)
- NVIDIA.exe (PID: 18480)
REDLINE has been found (auto)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 5000)
PURECRYPTER has been detected (SURICATA)
- MSBuild.exe (PID: 18076)
RANSOMWARE has been detected
- CoronaVirus.exe (PID: 16056)
Renames files like ransomware
- CoronaVirus.exe (PID: 16056)
NjRAT is detected
- server.exe (PID: 19312)
- NJRat.exe (PID: 18648)
- svchost.exe (PID: 17916)
BABADEDA has been found (auto)
- 4363463463464363463463463.exe (PID: 7804)
XRED has been found (auto)
- 4363463463464363463463463.exe (PID: 7728)
COINMINER has been found (auto)
- 4363463463464363463463463.exe (PID: 3144)
DCRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 6756)
GULOADER has been found (auto)
- 4363463463464363463463463.exe (PID: 11632)
QUASARRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 8320)
- Amogus.exe (PID: 21716)
- CleanerV2.exe (PID: 24060)
- svhost.exe (PID: 25652)
- Client-built-Playit.exe (PID: 23796)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 6624)
ASYNCRAT has been detected (MUTEX)
- gagagggagagag.exe (PID: 19988)
- aspnet_regbrowsers.exe (PID: 21044)
- aaa%20(3).exe (PID: 23688)
REMCOS has been found (auto)
- 4363463463464363463463463.exe (PID: 12804)
ASYNCRAT has been detected (SURICATA)
- gagagggagagag.exe (PID: 19988)
- 2v6wf6kn.exe (PID: 23260)
TGBDOWNLOADER has been detected
- GLP_installer_900223086_market.exe (PID: 8280)
Adds process to the Windows Defender exclusion list
- wefhrf.exe (PID: 21204)
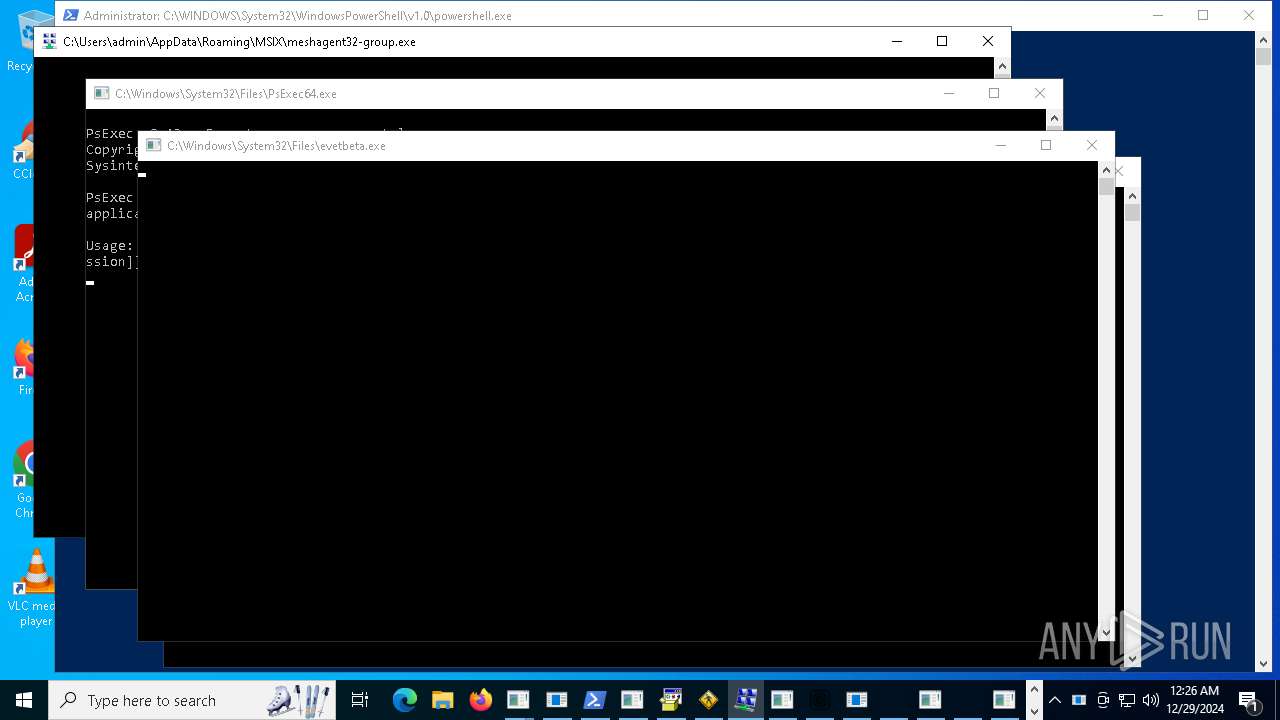
REMCOS mutex has been found
- evetbeta.exe (PID: 21776)
REMCOS has been detected
- evetbeta.exe (PID: 21776)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- asd.exe (PID: 24632)
FORMBOOK has been found (auto)
- 4363463463464363463463463.exe (PID: 6664)
NANOCORE has been detected (SURICATA)
- nano.exe (PID: 20220)
Steals credentials from Web Browsers
- gagagggagagag.exe (PID: 19988)
- gsprout.exe (PID: 19788)
- bypass.exe (PID: 22756)
- build.exe (PID: 17784)
- build.exe (PID: 19688)
- lkyhjksefa.exe (PID: 21388)
- qth5kdee.exe (PID: 21804)
TAURUS has been detected (SURICATA)
- gsprout.exe (PID: 19788)
StealC has been detected
- jdrgsotrti.exe (PID: 22740)
- kisteruop.exe (PID: 24176)
- 12.exe (PID: 18572)
- krgawdtyjawd.exe (PID: 24624)
- RegAsm.exe (PID: 25808)
- num.exe (PID: 26736)
Adds extension to the Windows Defender exclusion list
- h5a71wdy.exe (PID: 19640)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 21936)
- nbothjkd.exe (PID: 15240)
- cmd.exe (PID: 22712)
- cmd.exe (PID: 25300)
SILVERFOX has been detected (SURICATA)
- 22.exe (PID: 20784)
METASTEALER has been detected (SURICATA)
- build.exe (PID: 19688)
REDLINE has been detected (SURICATA)
- build.exe (PID: 19688)
Stealers network behavior
- build.exe (PID: 19688)
REMCOS has been detected (SURICATA)
- evetbeta.exe (PID: 21776)
- iexplore.exe (PID: 17588)
STEALC mutex has been found
- 4363463463464363463463463.exe (PID: 10848)
XWORM has been detected (SURICATA)
- imagelogger.exe (PID: 19168)
TAS17 has been detected
- Mswgoudnv.exe (PID: 23916)
NESHTA has been found (auto)
- 4363463463464363463463463.exe (PID: 3724)
BLANKGRABBER has been found (auto)
- 4363463463464363463463463.exe (PID: 6752)
PANDASTEALER has been found (auto)
- 4363463463464363463463463.exe (PID: 7744)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2192)
Connecting to InterPlanetary File System domains
- svchost.exe (PID: 2192)
METERPRETER has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 13868)
Creates or modifies Windows services
- ._cache_blq.exe (PID: 24520)
Runs injected code in another process
- pyl64.exe (PID: 18560)
Application was injected by another process
- explorer.exe (PID: 4488)
Run PowerShell with an invisible window
- powershell.exe (PID: 17288)
- powershell.exe (PID: 10296)
LUMMA mutex has been found
- lkyhjksefa.exe (PID: 21388)
PETYA has been found (auto)
- 4363463463464363463463463.exe (PID: 11532)
VENOMRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 7652)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 21876)
METASPLOIT has been found (auto)
- 4363463463464363463463463.exe (PID: 13160)
ZHARKBOT has been found (auto)
- 4363463463464363463463463.exe (PID: 10588)
ONLINECLIPPER mutex has been found
- svhostc.exe (PID: 26936)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2192)
- 4363463463464363463463463.exe (PID: 13876)
- xmbld.exe (PID: 18544)
RAT has been found (auto)
- 4363463463464363463463463.exe (PID: 13720)
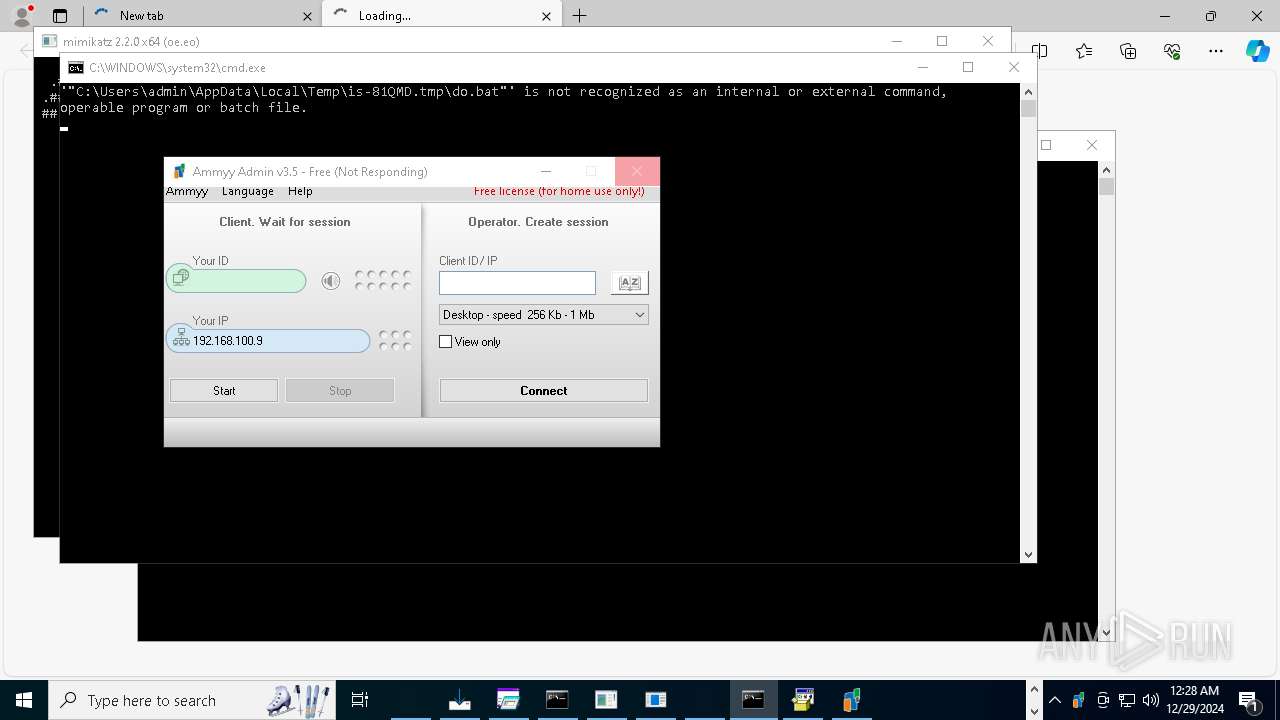
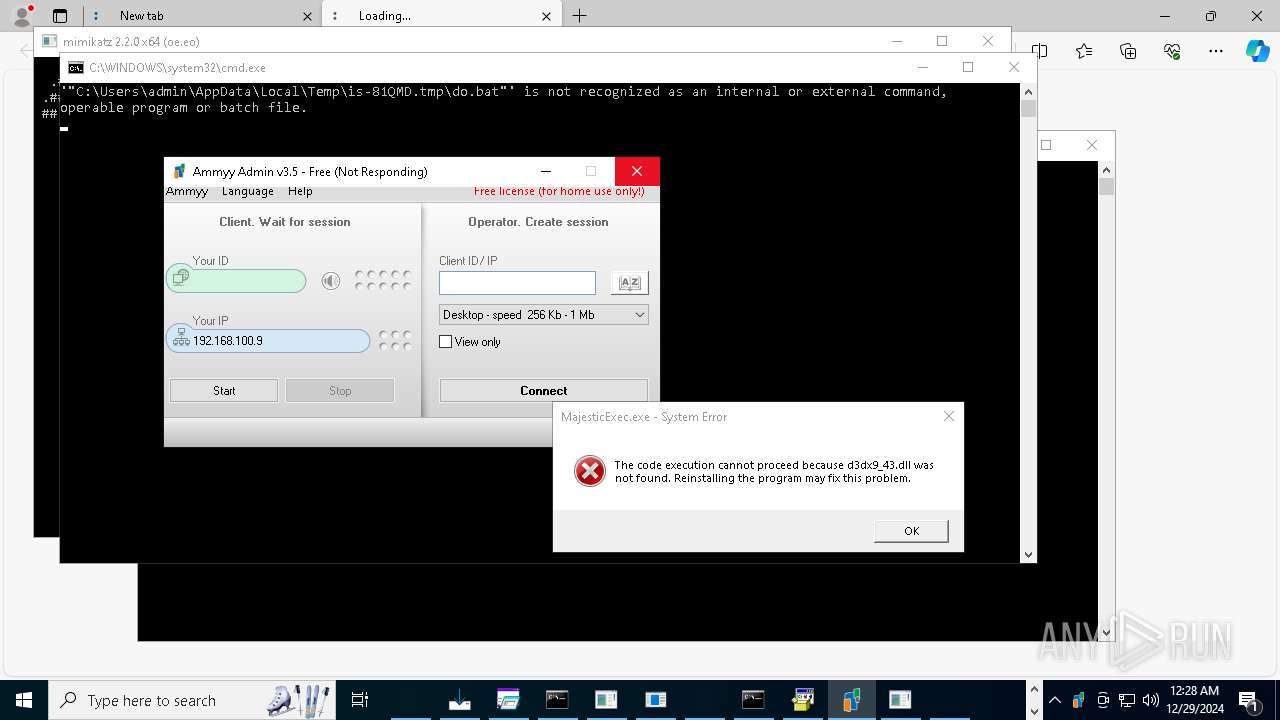
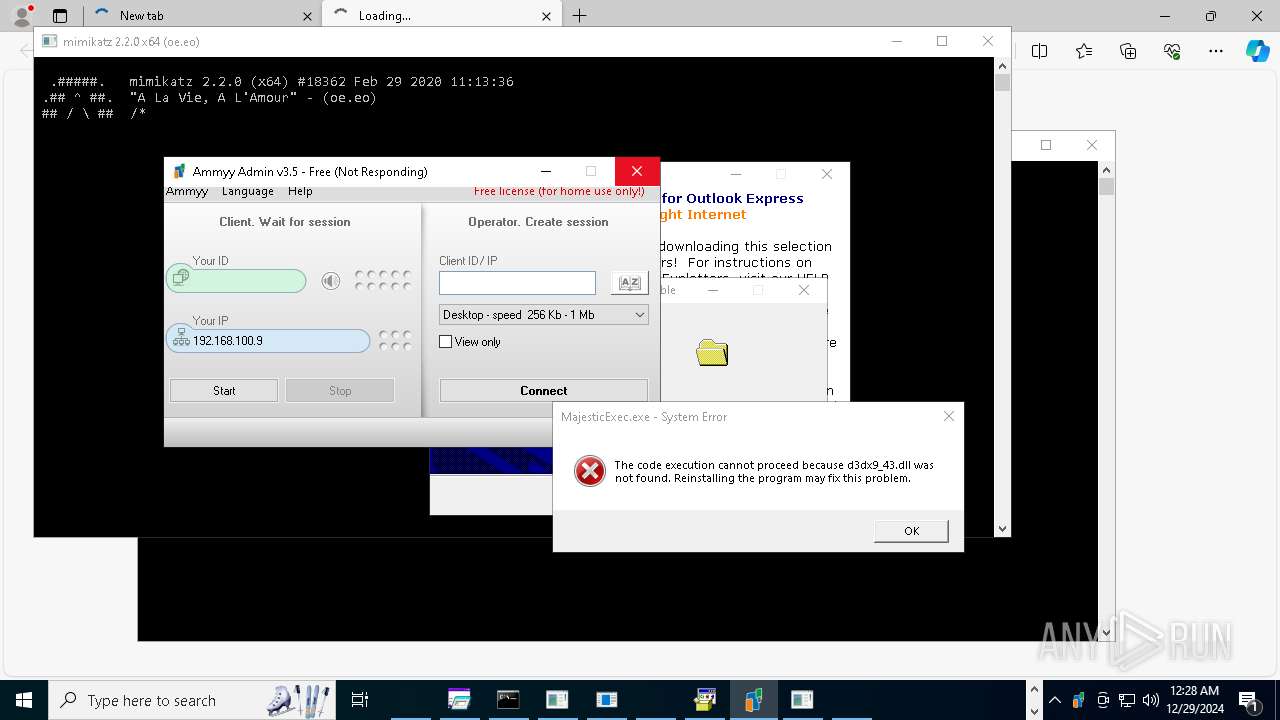
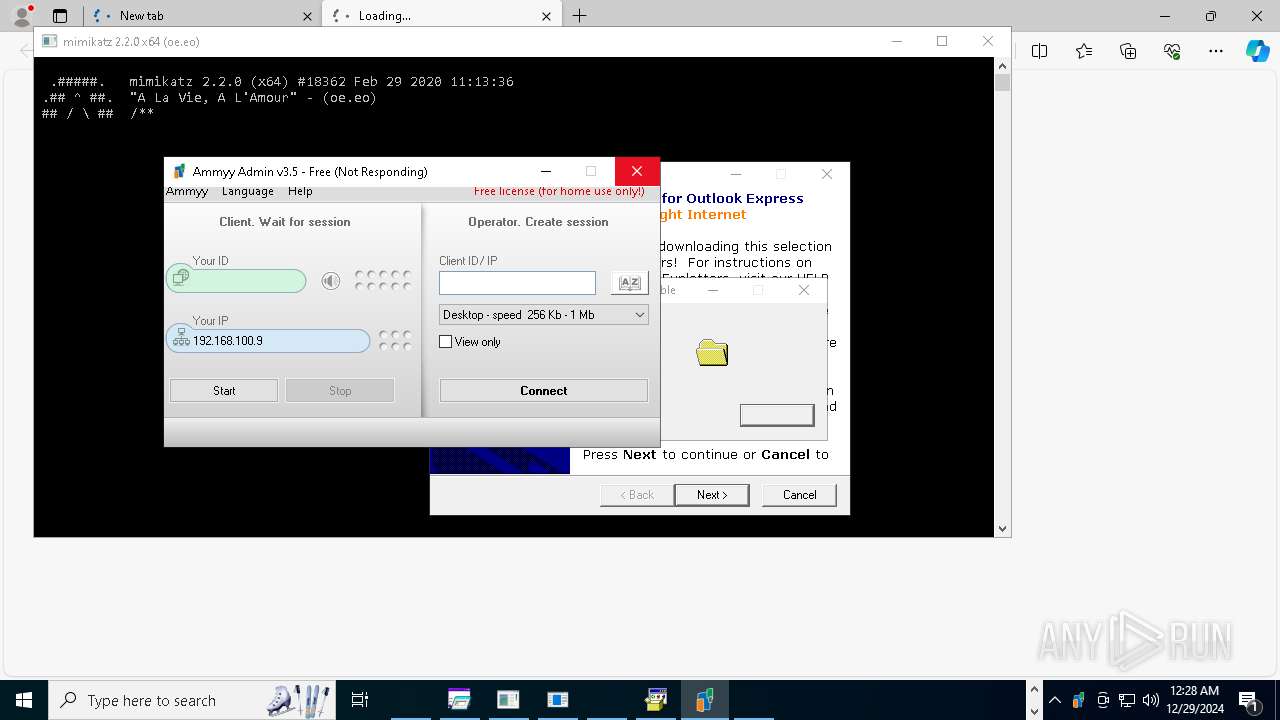
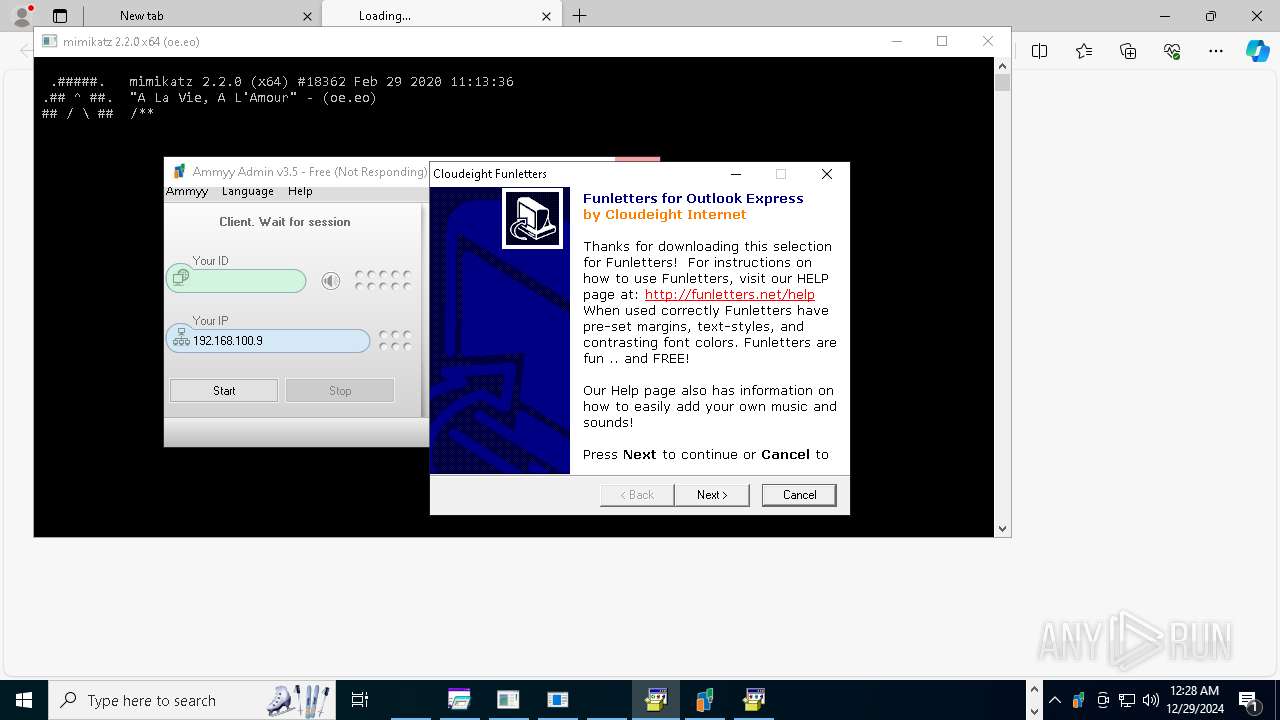
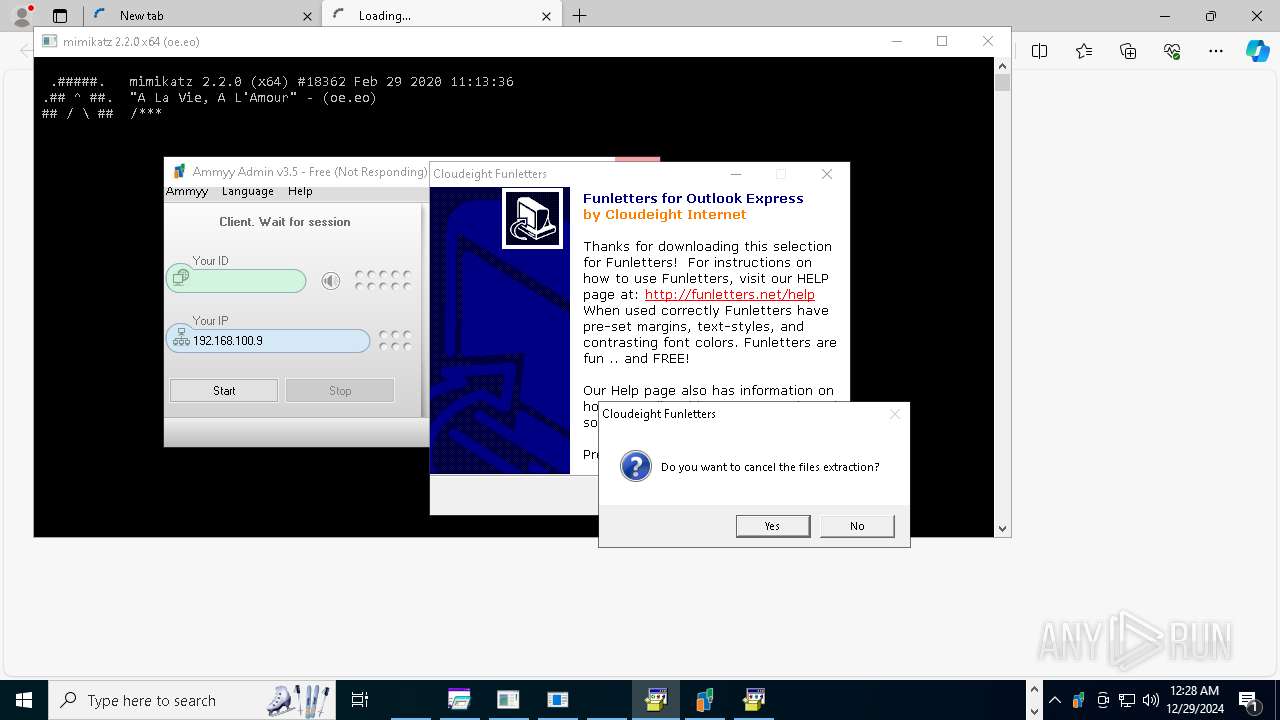
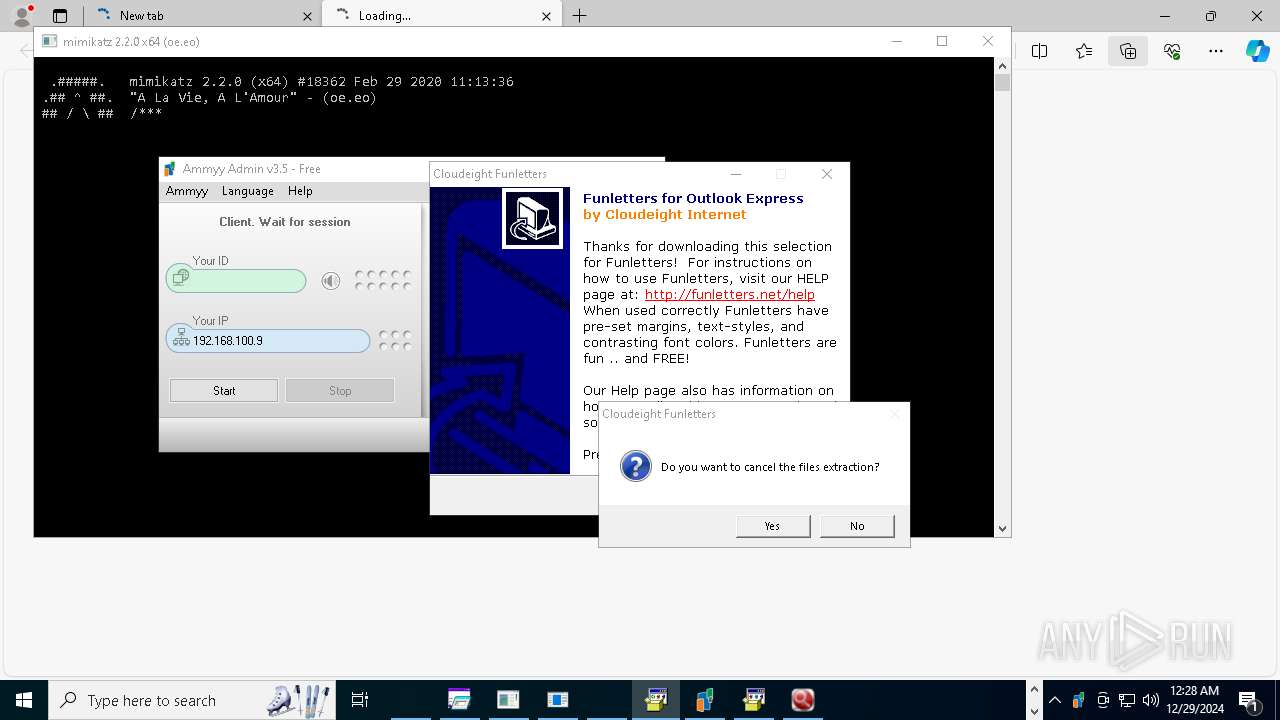
AMMYY has been detected (SURICATA)
- Ammyy.exe (PID: 27280)
GCLEANER has been detected (SURICATA)
- univ.exe (PID: 3812)
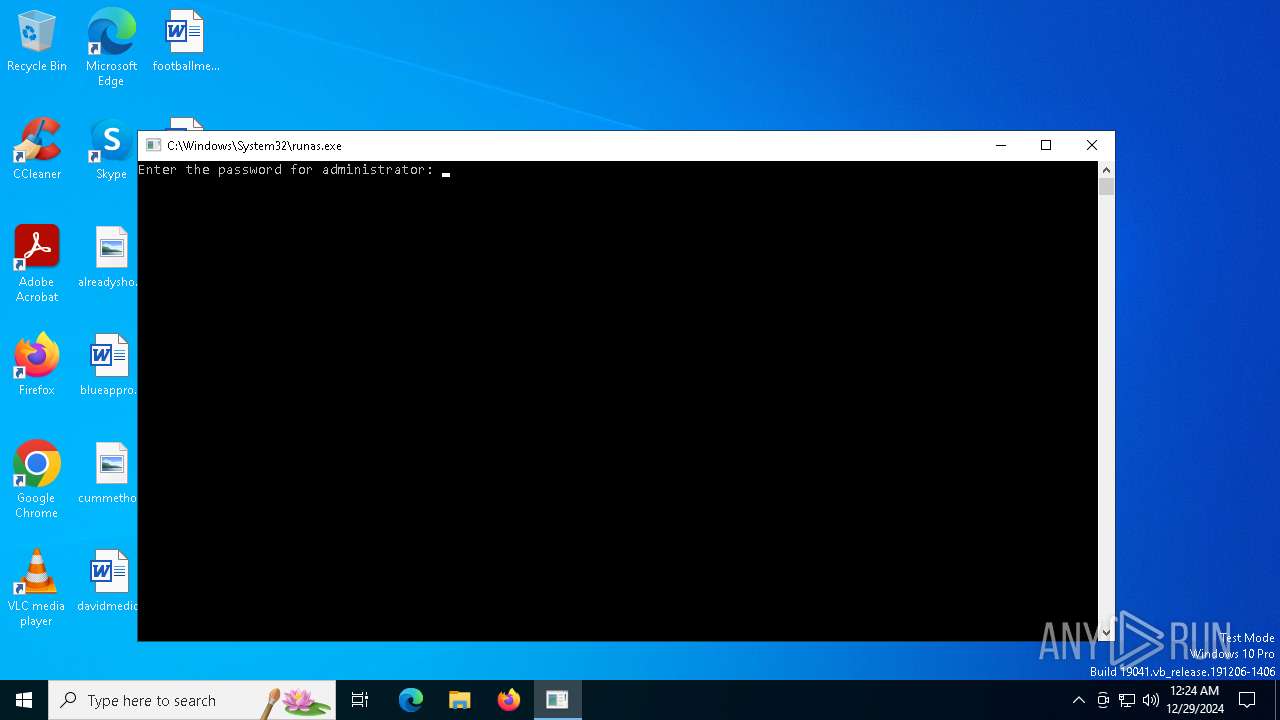
SUSPICIOUS
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 6280)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 4488)
- cmd.exe (PID: 5200)
- NorthSperm.exe (PID: 15044)
- baedawdgh.exe (PID: 14984)
- NOTallowedtocrypt.exe (PID: 16236)
- 76y5trfed675ytg.exe (PID: 17492)
- vpn.exe (PID: 16240)
- feb9sxwk.exe (PID: 18348)
- av_downloader1.1.exe (PID: 18576)
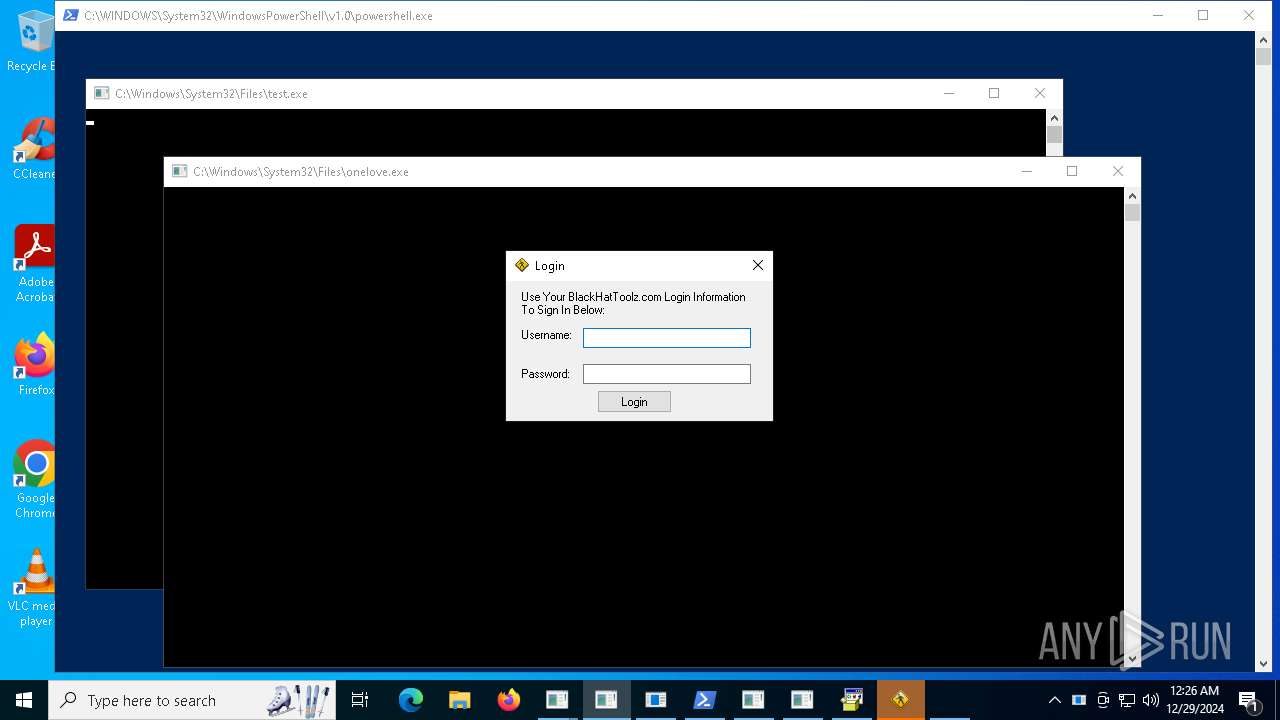
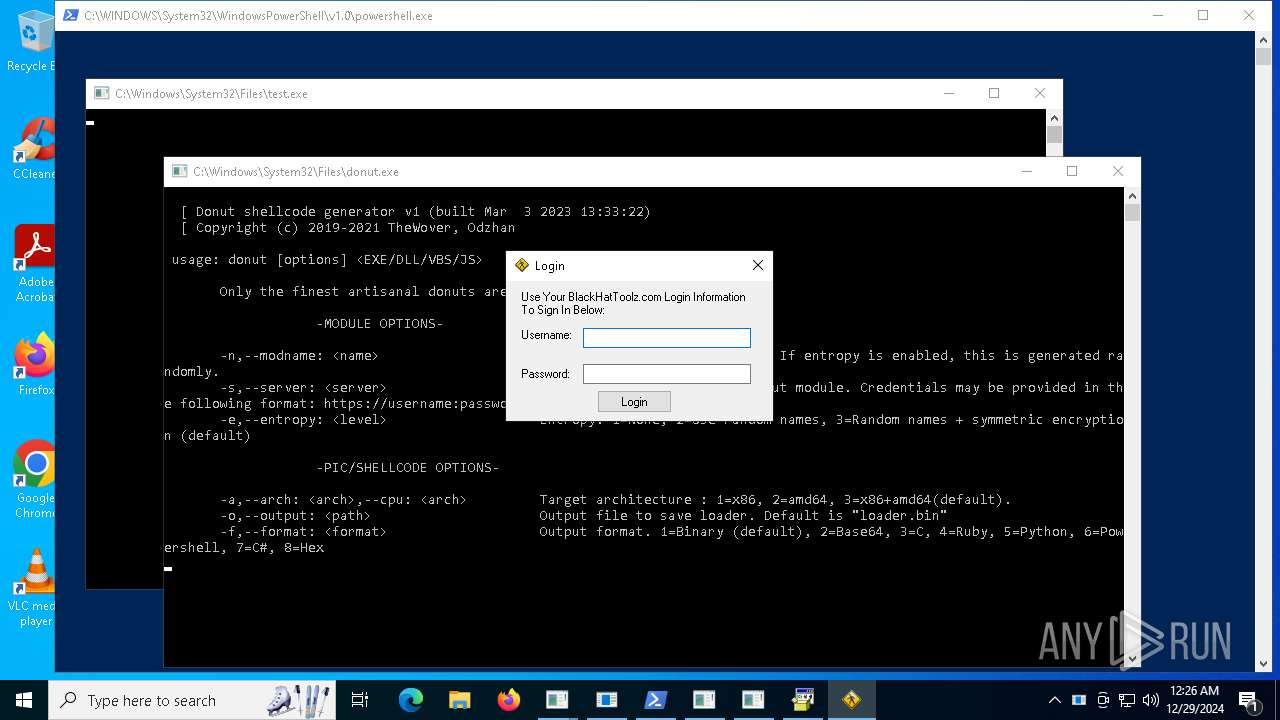
- onelove.exe (PID: 19108)
- run.exe (PID: 4056)
- test.exe (PID: 20172)
- CoronaVirus.exe (PID: 16056)
- AsyncClient.exe (PID: 16700)
- in.exe (PID: 20460)
- Microsoft.exe (PID: 21160)
- Discord.exe (PID: 16680)
- 4.exe (PID: 23052)
- temp.exe (PID: 18792)
- h5a71wdy.exe (PID: 19640)
- sharpmonoinjector.exe (PID: 21732)
- uhigdbf.exe (PID: 21664)
- IT_plan_cifs.exe (PID: 23448)
- utility-inst.tmp (PID: 25240)
- av_downloader1.1.exe (PID: 23440)
- NOTallowedtocrypt.exe (PID: 28284)
Application launched itself
- cmd.exe (PID: 5200)
- armadegon.exe (PID: 15308)
- GIFT-INFO.lMG.exe (PID: 6952)
- 2kudv4ea.exe (PID: 23060)
- powershell.exe (PID: 19000)
- svhostc.exe (PID: 24460)
- Ammyy.exe (PID: 21700)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 8760)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 8336)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 4764)
- 4363463463464363463463463.exe (PID: 12840)
- cli.exe (PID: 16796)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 11664)
- server.exe (PID: 15244)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 9812)
- MSBuild.exe (PID: 18076)
- 4363463463464363463463463.exe (PID: 9804)
- fern_wifi_recon%252.34.exe (PID: 19196)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 13876)
- NVIDIA.exe (PID: 18480)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 10692)
- Client-built.exe (PID: 15168)
- MSBuild.exe (PID: 21360)
- Server1.exe (PID: 16664)
- server.exe (PID: 19312)
- Sync.exe (PID: 20440)
- gagagggagagag.exe (PID: 19988)
- nano.exe (PID: 20220)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 4024)
- system32.exe (PID: 19376)
- aspnet_regbrowsers.exe (PID: 21044)
- 22.exe (PID: 20784)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 11560)
- imagelogger.exe (PID: 19168)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 10880)
- RegAsm.exe (PID: 1328)
- networkmanager.exe (PID: 21756)
- evetbeta.exe (PID: 21776)
- build.exe (PID: 19688)
- 14082024.exe (PID: 15480)
- GIFT-INFO.lMG.exe (PID: 22440)
- mswabnet.exe (PID: 24580)
- fontdrvhost.exe (PID: 15124)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 9572)
- MYNEWRDX.exe (PID: 19596)
- nbothjkd.exe (PID: 15240)
- morphic.exe (PID: 21740)
- 4363463463464363463463463.exe (PID: 11804)
- MSBuild.exe (PID: 24028)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 12772)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 10160)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 9004)
- jhnykawfkth.exe (PID: 18752)
- anticheat.exe (PID: 1596)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 12864)
- MSBuild.exe (PID: 23016)
- 4363463463464363463463463.exe (PID: 3144)
- buildred.exe (PID: 22696)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 7728)
- update.exe (PID: 23596)
- xmbld.exe (PID: 18544)
- Survox.exe (PID: 23068)
- 3344.exe (PID: 22760)
- system404.exe (PID: 24852)
- 4363463463464363463463463.exe (PID: 6664)
- windowsexecutable.exe (PID: 20216)
- 2v6wf6kn.exe (PID: 23260)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 7384)
- bildnewl.exe (PID: 19644)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 13004)
- networkmanager.exe (PID: 21756)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 8380)
- wefhrf.exe (PID: 21204)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 11584)
- InstallSetup.exe (PID: 24404)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 6820)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 5544)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 10868)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 4764)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 10032)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 13536)
- 4363463463464363463463463.exe (PID: 1804)
- svchost.exe (PID: 2192)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 3640)
- InstallSetup.exe (PID: 24404)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 6752)
- xmbld.exe (PID: 18544)
- Ammyy.exe (PID: 27280)
- 4363463463464363463463463.exe (PID: 11568)
- 4363463463464363463463463.exe (PID: 9804)
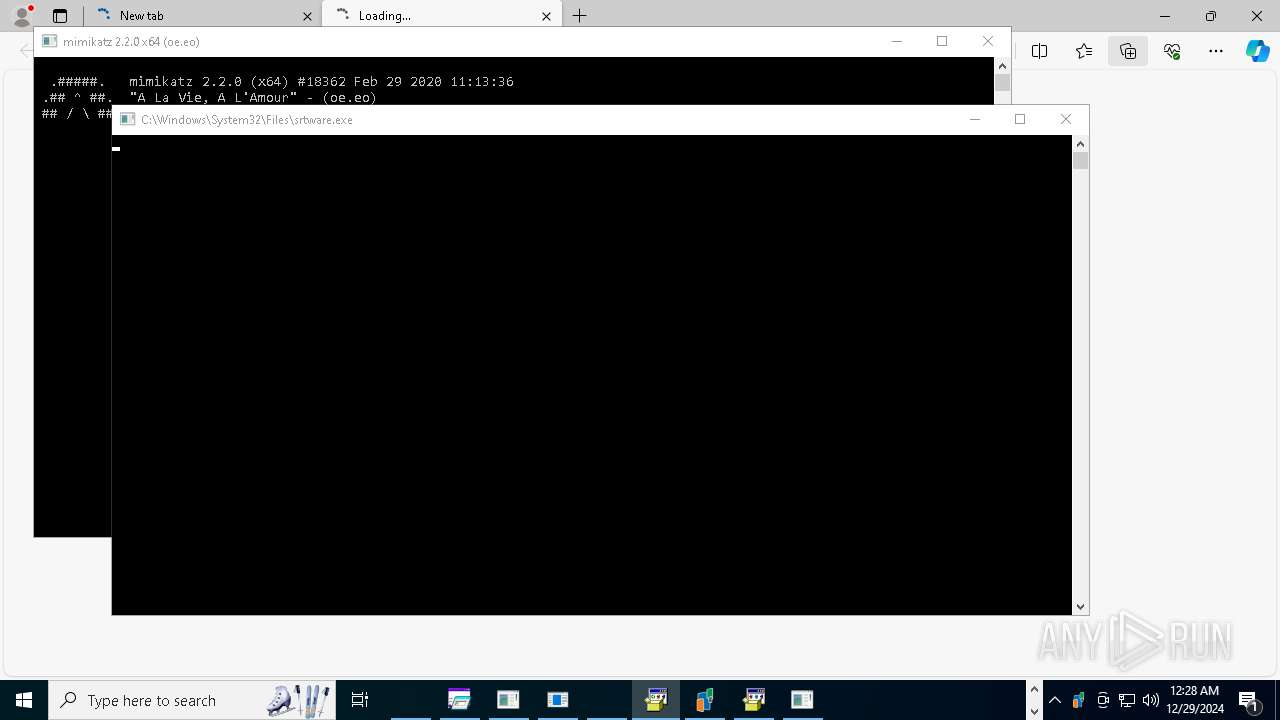
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 9556)
- testingg.exe (PID: 15116)
- System.exe (PID: 15344)
- Synaptics.exe (PID: 776)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 8760)
- server.exe (PID: 15244)
- baedawdgh.exe (PID: 14984)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 13720)
- NOTallowedtocrypt.exe (PID: 16236)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 10868)
- 4363463463464363463463463.exe (PID: 10032)
- 3544436.exe (PID: 17252)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 10572)
- feb9sxwk.exe (PID: 18348)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 3144)
- Minet.exe (PID: 16568)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 2076)
- NVIDIA.exe (PID: 18480)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 3988)
- Destover.exe (PID: 20588)
- china.exe (PID: 20616)
- 4363463463464363463463463.exe (PID: 10692)
- CoronaVirus.exe (PID: 16056)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 11748)
- server.exe (PID: 19312)
- 4363463463464363463463463.exe (PID: 7776)
- 123.exe (PID: 19512)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 6672)
- bildnewl.exe (PID: 19644)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 6668)
- Steam.Upgreyd.exe (PID: 16648)
- steel.exe (PID: 21416)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 5316)
- nano.exe (PID: 20220)
- steel.tmp (PID: 20872)
- 4363463463464363463463463.exe (PID: 11632)
- Installeraus.exe (PID: 21372)
- 2klz.exe (PID: 20624)
- GLP_installer_900223086_market.exe (PID: 8280)
- blq.exe (PID: 15400)
- imagelogger.exe (PID: 19168)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 11892)
- Microsoft.exe (PID: 21160)
- Final.exe (PID: 21724)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 11596)
- NJRat.exe (PID: 18648)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 8320)
- AsyncClient.exe (PID: 16700)
- SrbijaSetupHokej.exe (PID: 21672)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 6664)
- system32.exe (PID: 19376)
- ovrflw.exe (PID: 21764)
- 4363463463464363463463463.exe (PID: 13576)
- basx.exe (PID: 22408)
- SrbijaSetupHokej.tmp (PID: 19040)
- 4363463463464363463463463.exe (PID: 11620)
- collinssplashpro32.exe (PID: 21300)
- 4363463463464363463463463.exe (PID: 10596)
- basx.tmp (PID: 17936)
- 4363463463464363463463463.exe (PID: 11780)
- njSilent.exe (PID: 21656)
- 4363463463464363463463463.exe (PID: 11716)
- Discord.exe (PID: 16680)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 11540)
- kitty.exe (PID: 23488)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 2928)
- Amogus.exe (PID: 21716)
- 4363463463464363463463463.exe (PID: 11640)
- Mswgoudnv.exe (PID: 23916)
- utility-inst.exe (PID: 23696)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 8380)
- ._cache_blq.exe (PID: 24520)
- 4363463463464363463463463.exe (PID: 6752)
- hailhydra.exe (PID: 22172)
- utility-inst.tmp (PID: 25240)
- temp.exe (PID: 18792)
- Survox.exe (PID: 23068)
- uhigdbf.exe (PID: 21664)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 13868)
- CleanerV2.exe (PID: 24060)
- cvv.exe (PID: 24376)
- 4363463463464363463463463.exe (PID: 4516)
- 2r61ahry.exe (PID: 25632)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 13160)
- dvdvideomedia2.exe (PID: 23624)
- 4363463463464363463463463.exe (PID: 11576)
- PowerShell.exe (PID: 21688)
- 4363463463464363463463463.exe (PID: 7928)
- cnct.exe (PID: 24284)
- svchost.exe (PID: 17916)
- svhost.exe (PID: 25652)
- svhostc.exe (PID: 26936)
- mountain-pasture.exe (PID: 20012)
- newfile.exe (PID: 18724)
- Client-built-Playit.exe (PID: 23796)
- dxwebsetup.exe (PID: 12060)
- armadegon.exe (PID: 17504)
- 87f3f2.exe (PID: 24816)
- crypteda.exe (PID: 12116)
- qsjxfirefkza.exe (PID: 27212)
- file.exe (PID: 26228)
- cudo.exe (PID: 24684)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 8036)
- main.exe (PID: 26140)
- clamer.exe (PID: 15036)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 12848)
- creal.exe (PID: 15836)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 6624)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 9572)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 7812)
- 4363463463464363463463463.exe (PID: 8176)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 3420)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 11576)
- InstallSetup.exe (PID: 24404)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 6820)
The process creates files with name similar to system file names
- 4363463463464363463463463.exe (PID: 13820)
- System.exe (PID: 15344)
- 4363463463464363463463463.exe (PID: 11560)
- server.exe (PID: 15244)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 10332)
- nano.exe (PID: 20220)
- CoronaVirus.exe (PID: 16056)
- 4363463463464363463463463.exe (PID: 6352)
- njSilent.exe (PID: 21656)
- 4363463463464363463463463.exe (PID: 13548)
- Survox.exe (PID: 23068)
- PowerShell.exe (PID: 21688)
- svhost.exe (PID: 25652)
- main.exe (PID: 26140)
- 4363463463464363463463463.exe (PID: 11532)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 13820)
- TPB-1.exe (PID: 15164)
- testingg.exe (PID: 15116)
- 4363463463464363463463463.exe (PID: 9556)
- System.exe (PID: 15344)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 13876)
- zts.exe (PID: 1304)
- NorthSperm.exe (PID: 15044)
- Synaptics.exe (PID: 776)
- 4363463463464363463463463.exe (PID: 8760)
- baedawdgh.exe (PID: 14984)
- XClient.exe (PID: 6212)
- ._cache_System.exe (PID: 4328)
- svchost.exe (PID: 3124)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 9636)
- NOTallowedtocrypt.exe (PID: 16236)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 9812)
- ShellExperienceHost.exe (PID: 16436)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 3144)
- PCclear_Eng_mini.exe (PID: 18764)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 13548)
- av_downloader1.1.exe (PID: 18576)
- 4363463463464363463463463.exe (PID: 11652)
- Minet.exe (PID: 16568)
- Client-built.exe (PID: 15168)
- crss.exe (PID: 16588)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 5556)
- run.exe (PID: 4056)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 3988)
- gsprout.exe (PID: 19788)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 6668)
- 22.exe (PID: 20784)
- 4363463463464363463463463.exe (PID: 5316)
- c1.exe (PID: 7868)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 11632)
- AsyncClient.exe (PID: 16700)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 4024)
- in.exe (PID: 20460)
- 4363463463464363463463463.exe (PID: 11532)
- build_2024-07-27_00-41.exe (PID: 19736)
- wefhrf.exe (PID: 21204)
- Discord.exe (PID: 16680)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 11596)
- blq.exe (PID: 15400)
- Microsoft.exe (PID: 21160)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 13576)
- pjthjsdjgjrtavv.exe (PID: 21648)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 11780)
- Final.exe (PID: 21724)
- alphaTweaks.exe (PID: 18640)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 11172)
- ovrflw.exe (PID: 21764)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 13344)
- njSilent.exe (PID: 21656)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 12864)
- 4363463463464363463463463.exe (PID: 10548)
- pyjnkasedf.exe (PID: 20320)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 3288)
- jtkhikadjthsad.exe (PID: 23036)
- InstallSetup.exe (PID: 24404)
- sharpmonoinjector.exe (PID: 21732)
- uhigdbf.exe (PID: 21664)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 6752)
- av_downloader1.1.exe (PID: 23440)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 8380)
- utility-inst.tmp (PID: 25240)
- fuag.exe (PID: 20992)
- armadegon.exe (PID: 17504)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 11524)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 13160)
- univ.exe (PID: 3812)
- Ammyy.exe (PID: 27280)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 7928)
- setup8.exe (PID: 24588)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 11640)
- 4363463463464363463463463.exe (PID: 6700)
- xs.exe (PID: 19996)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 11872)
- PowerShell.exe (PID: 21688)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 12848)
- cvv.exe (PID: 24376)
Checks Windows Trust Settings
- TPB-1.exe (PID: 15164)
- zts.exe (PID: 1304)
- alphaTweaks.exe (PID: 18640)
- c1.exe (PID: 7868)
- build_2024-07-27_00-41.exe (PID: 19736)
- Synaptics.exe (PID: 776)
- pjthjsdjgjrtavv.exe (PID: 21648)
- pyjnkasedf.exe (PID: 20320)
- jtkhikadjthsad.exe (PID: 23036)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- TPB-1.exe (PID: 15164)
- build_2024-07-27_00-41.exe (PID: 19736)
- pjthjsdjgjrtavv.exe (PID: 21648)
- pyjnkasedf.exe (PID: 20320)
- setup8.exe (PID: 24588)
- jtkhikadjthsad.exe (PID: 23036)
Starts itself from another location
- testingg.exe (PID: 15116)
- NOTallowedtocrypt.exe (PID: 16236)
- Minet.exe (PID: 16568)
- ovrflw.exe (PID: 21764)
- njSilent.exe (PID: 21656)
Reads the BIOS version
- zts.exe (PID: 1304)
- random.exe (PID: 18152)
- qth5kdee.exe (PID: 21804)
- kitty.exe (PID: 23488)
- v_dolg.exe (PID: 25020)
- petya.exe (PID: 27236)
- hhnjqu9y.exe (PID: 10960)
Executing commands from ".cmd" file
- NorthSperm.exe (PID: 15044)
Uses NETSH.EXE to add a firewall rule or allowed programs
- server.exe (PID: 15244)
- Server1.exe (PID: 16664)
- server.exe (PID: 19312)
- NJRat.exe (PID: 18648)
- testme.exe (PID: 7612)
- svchost.exe (PID: 17916)
Creates file in the systems drive root
- explorer.exe (PID: 4488)
- server.exe (PID: 15244)
- CoronaVirus.exe (PID: 16056)
- GLP_installer_900223086_market.exe (PID: 8280)
- svchost.exe (PID: 17916)
Searches for installed software
- TPB-1.exe (PID: 15164)
- pjthjsdjgjrtavv.exe (PID: 21648)
Probably fake Windows Update file has been dropped
- server.exe (PID: 15244)
Checks for external IP
- svchost.exe (PID: 2192)
- ._cache_System.exe (PID: 4328)
- XClient.exe (PID: 6212)
- svchost.exe (PID: 3124)
- crss.exe (PID: 16588)
- com%20surrogate.exe (PID: 19216)
- imagelogger.exe (PID: 19168)
- nbothjkd.exe (PID: 15240)
- bypass.exe (PID: 22756)
- taskhost.exe (PID: 22360)
- fuag.exe (PID: 20992)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- Ammyy.exe (PID: 27280)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- server.exe (PID: 15244)
Reads the date of Windows installation
- ._cache_System.exe (PID: 4328)
- svchost.exe (PID: 3124)
- XClient.exe (PID: 6212)
- crss.exe (PID: 16588)
- Microsoft.exe (PID: 21160)
- ovrflw.exe (PID: 21764)
- sharpmonoinjector.exe (PID: 21732)
- uhigdbf.exe (PID: 21664)
- Indentif.exe (PID: 22944)
- fuag.exe (PID: 20992)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- setup8.exe (PID: 24588)
- PowerShell.exe (PID: 21688)
- xs.exe (PID: 19996)
Starts POWERSHELL.EXE for commands execution
- ._cache_System.exe (PID: 4328)
- svchost.exe (PID: 3124)
- XClient.exe (PID: 6212)
- sound.exe (PID: 18496)
- crss.exe (PID: 16588)
- TTDesktop18.exe (PID: 17004)
- com%20surrogate.exe (PID: 19216)
- wefhrf.exe (PID: 21204)
- 4363463463464363463463463.exe (PID: 6352)
- h5a71wdy.exe (PID: 19640)
- powershell.exe (PID: 19000)
- cmd.exe (PID: 22256)
- cmd.exe (PID: 23944)
- cmd.exe (PID: 26584)
- fuag.exe (PID: 20992)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
Script adds exclusion path to Windows Defender
- svchost.exe (PID: 3124)
- ._cache_System.exe (PID: 4328)
- XClient.exe (PID: 6212)
- crss.exe (PID: 16588)
- TTDesktop18.exe (PID: 17004)
- com%20surrogate.exe (PID: 19216)
- wefhrf.exe (PID: 21204)
- h5a71wdy.exe (PID: 19640)
- powershell.exe (PID: 19000)
- fuag.exe (PID: 20992)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
Contacting a server suspected of hosting an CnC
- Synaptics.exe (PID: 776)
- svchost.exe (PID: 2192)
- server.exe (PID: 15244)
- MSBuild.exe (PID: 18076)
- Server1.exe (PID: 16664)
- gagagggagagag.exe (PID: 19988)
- server.exe (PID: 19312)
- nano.exe (PID: 20220)
- gsprout.exe (PID: 19788)
- 22.exe (PID: 20784)
- evetbeta.exe (PID: 21776)
- imagelogger.exe (PID: 19168)
- 4363463463464363463463463.exe (PID: 10580)
- iexplore.exe (PID: 17588)
- system32.exe (PID: 19376)
- asd.exe (PID: 24632)
- 4363463463464363463463463.exe (PID: 8320)
- 2v6wf6kn.exe (PID: 23260)
The process executes via Task Scheduler
- service.exe (PID: 15460)
- Cerker.exe (PID: 27352)
- lxrv.exe (PID: 13788)
- ednfosi.exe (PID: 24548)
Process drops legitimate windows executable
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 13876)
- steel.tmp (PID: 20872)
- 4363463463464363463463463.exe (PID: 11632)
- basx.tmp (PID: 17936)
- CoronaVirus.exe (PID: 16056)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 6752)
- hailhydra.exe (PID: 22172)
- 4363463463464363463463463.exe (PID: 8612)
- dxwebsetup.exe (PID: 12060)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 16260)
- cmd.exe (PID: 17536)
- cmd.exe (PID: 17648)
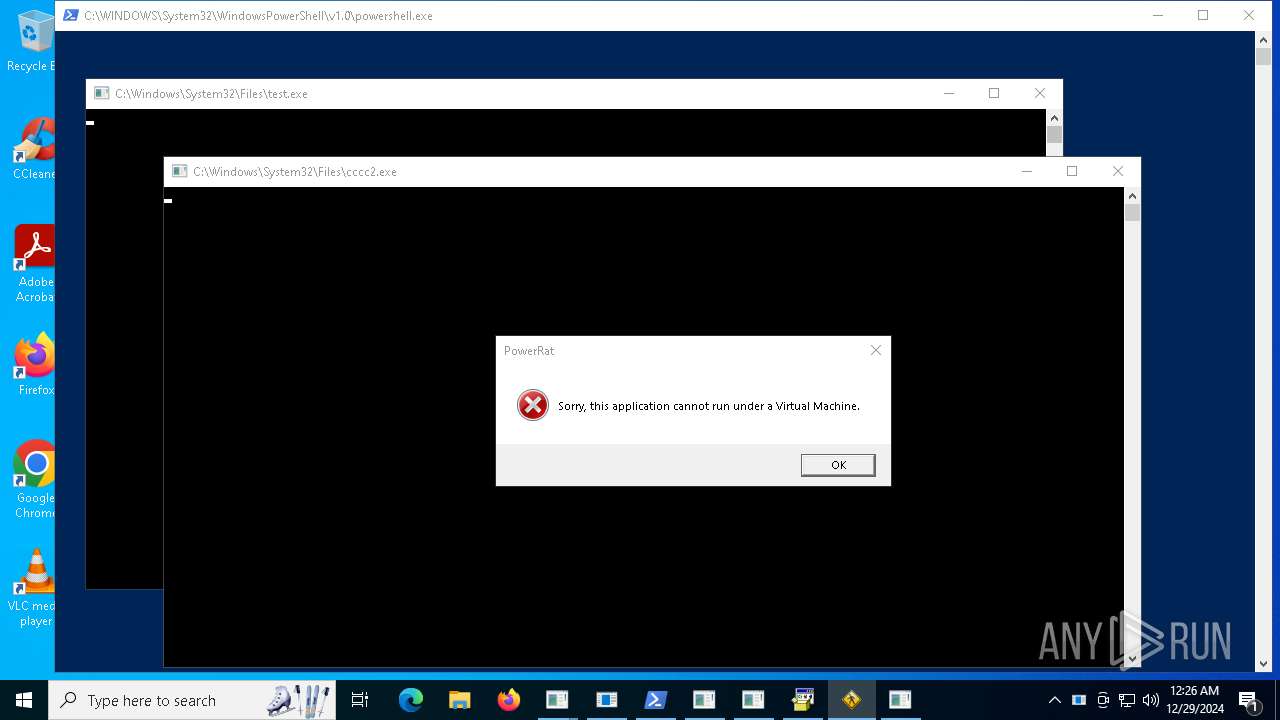
The process checks if it is being run in the virtual environment
- 4363463463464363463463463.exe (PID: 10472)
- conhost.exe (PID: 20232)
- fontdrvhost.exe (PID: 15124)
- tn8cdkzn.exe (PID: 22952)
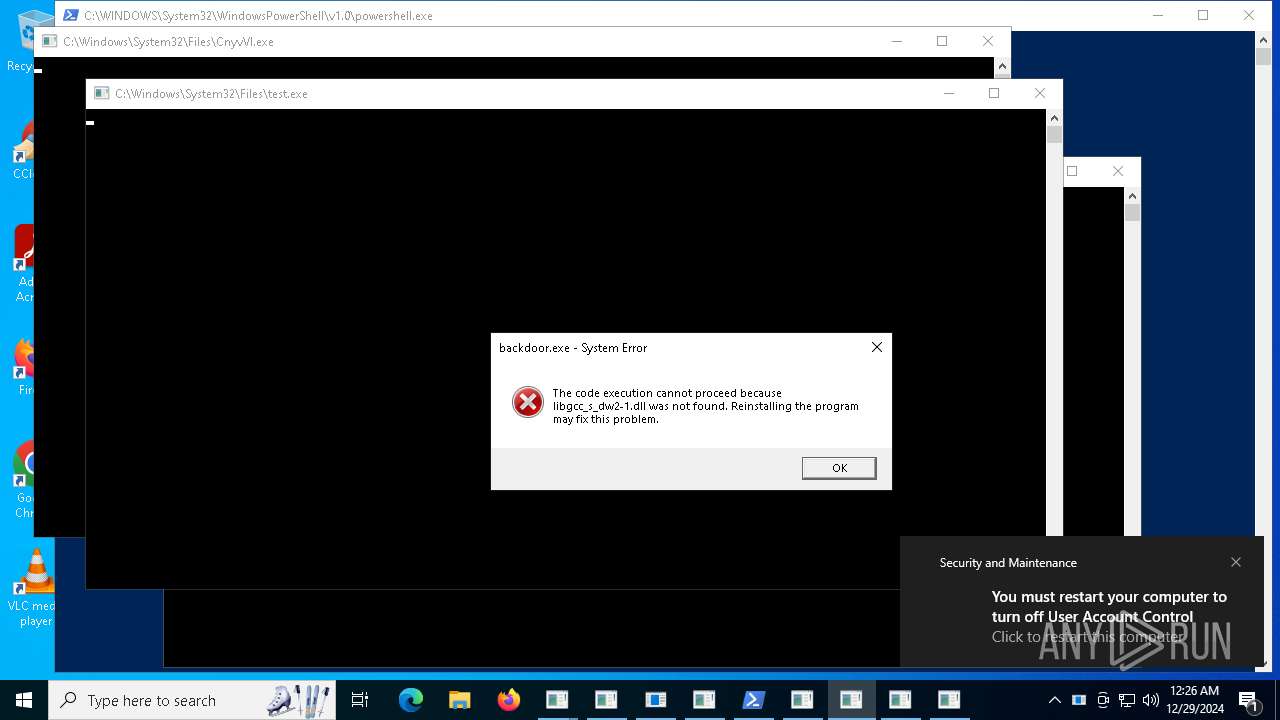
Executing commands from a ".bat" file
- av_downloader1.1.exe (PID: 18576)
- onelove.exe (PID: 19108)
- run.exe (PID: 4056)
- test.exe (PID: 20172)
- AsyncClient.exe (PID: 16700)
- in.exe (PID: 20460)
- Discord.exe (PID: 16680)
- 4.exe (PID: 23052)
- temp.exe (PID: 18792)
- sharpmonoinjector.exe (PID: 21732)
- uhigdbf.exe (PID: 21664)
- IT_plan_cifs.exe (PID: 23448)
- utility-inst.tmp (PID: 25240)
- av_downloader1.1.exe (PID: 23440)
The process executes Powershell scripts
- sound.exe (PID: 18496)
- cmd.exe (PID: 23944)
Downloads file from URI via Powershell
- powershell.exe (PID: 19288)
Possibly malicious use of IEX has been detected
- sound.exe (PID: 18496)
- cmd.exe (PID: 26584)
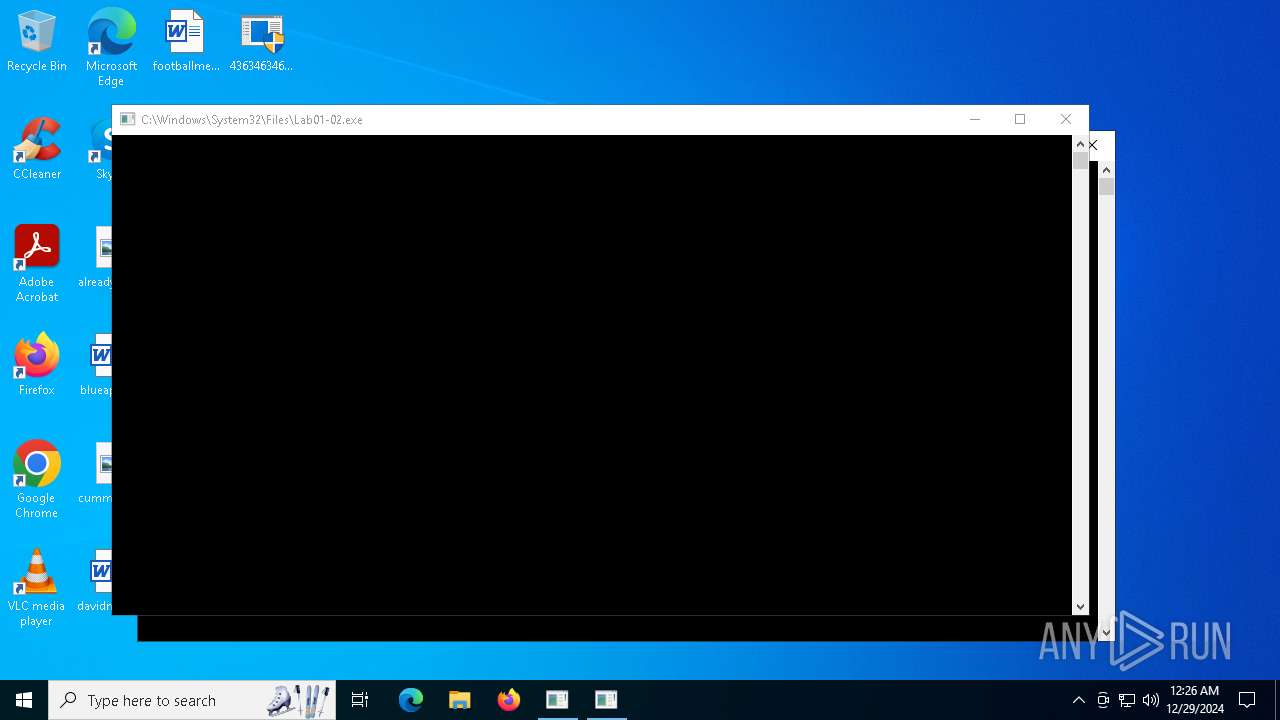
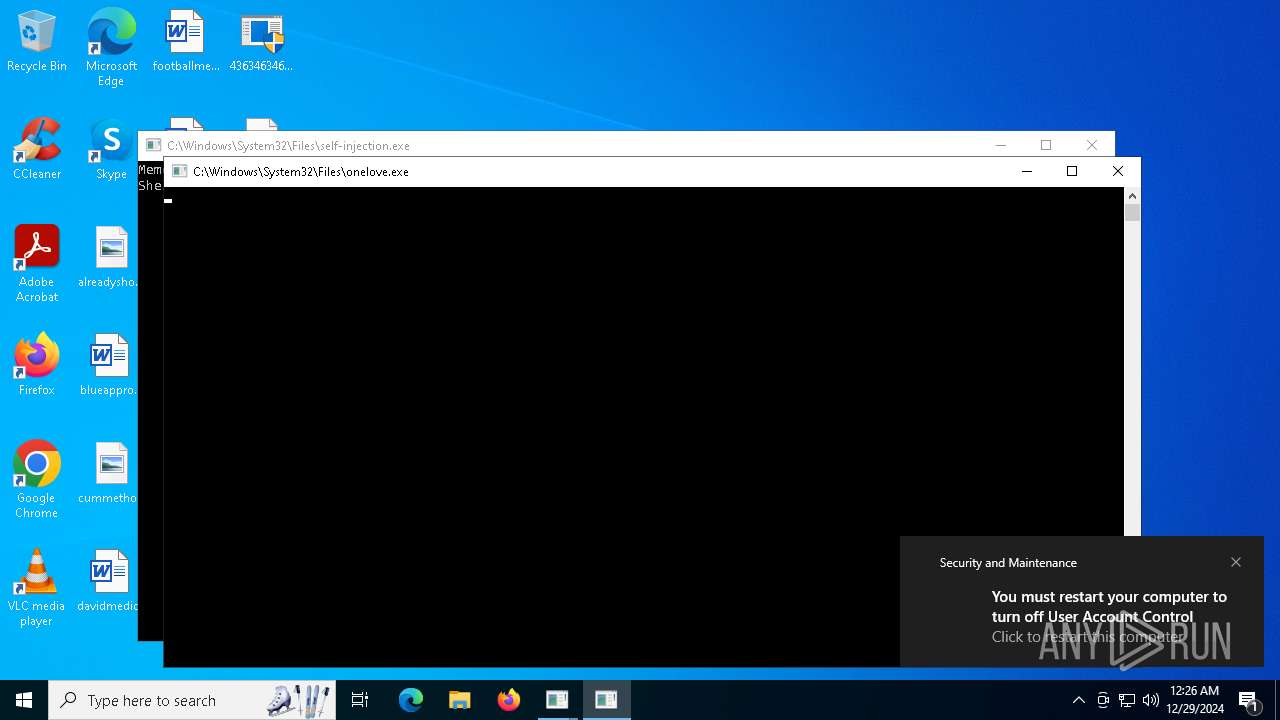
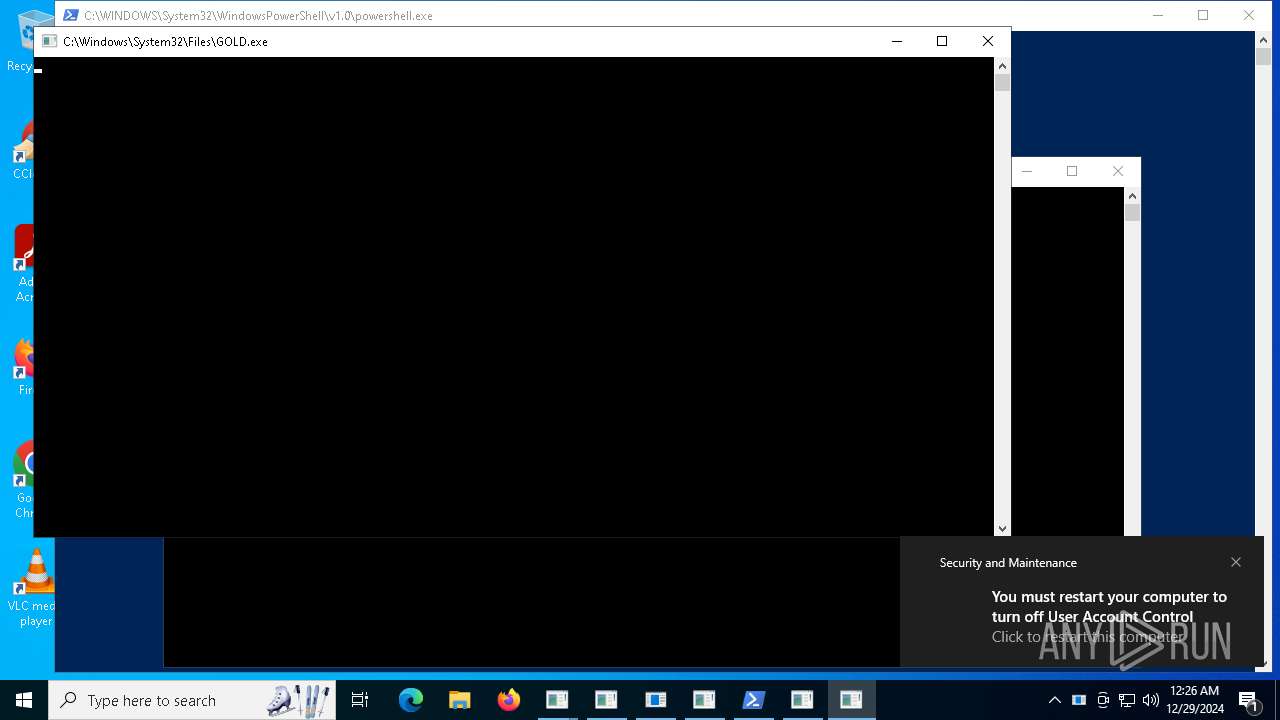
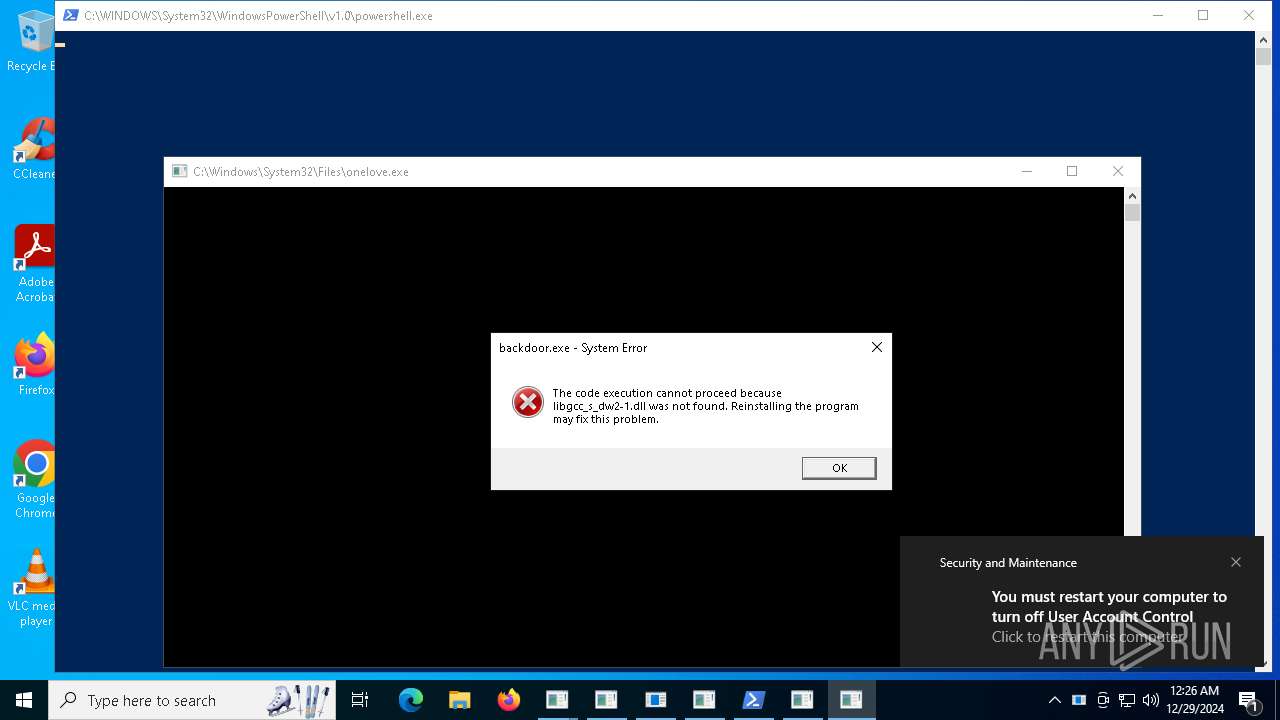
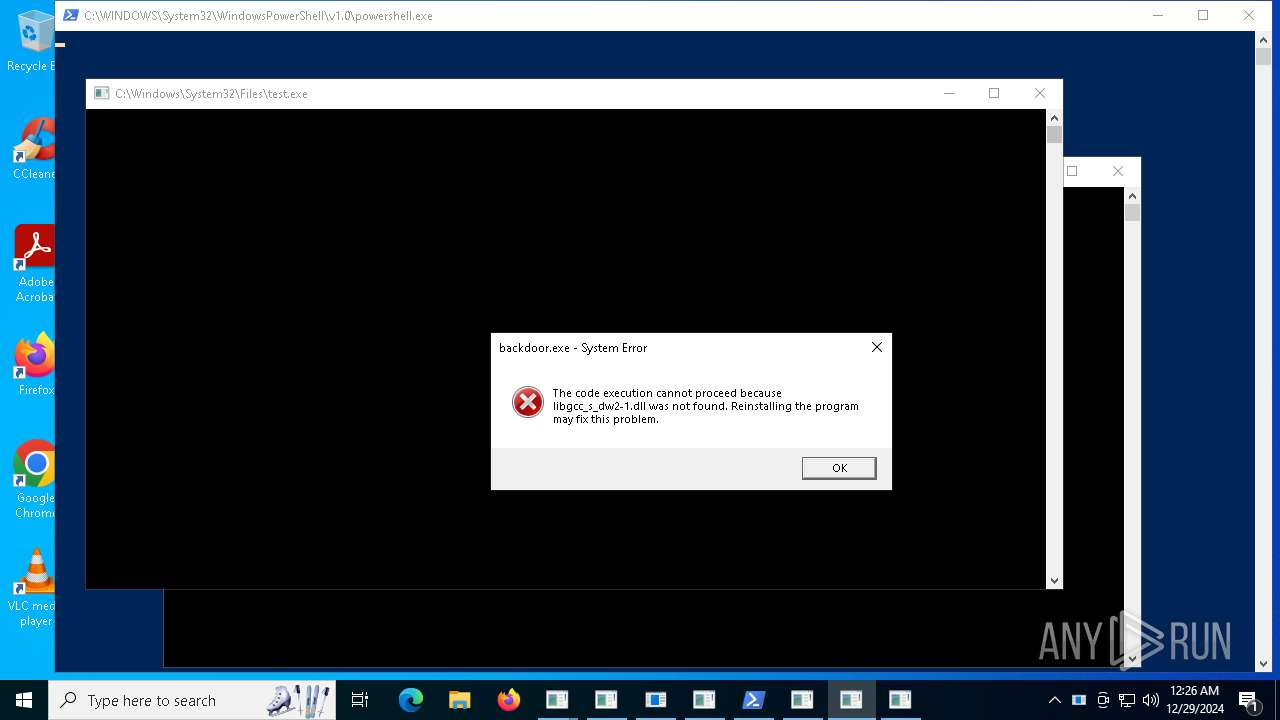
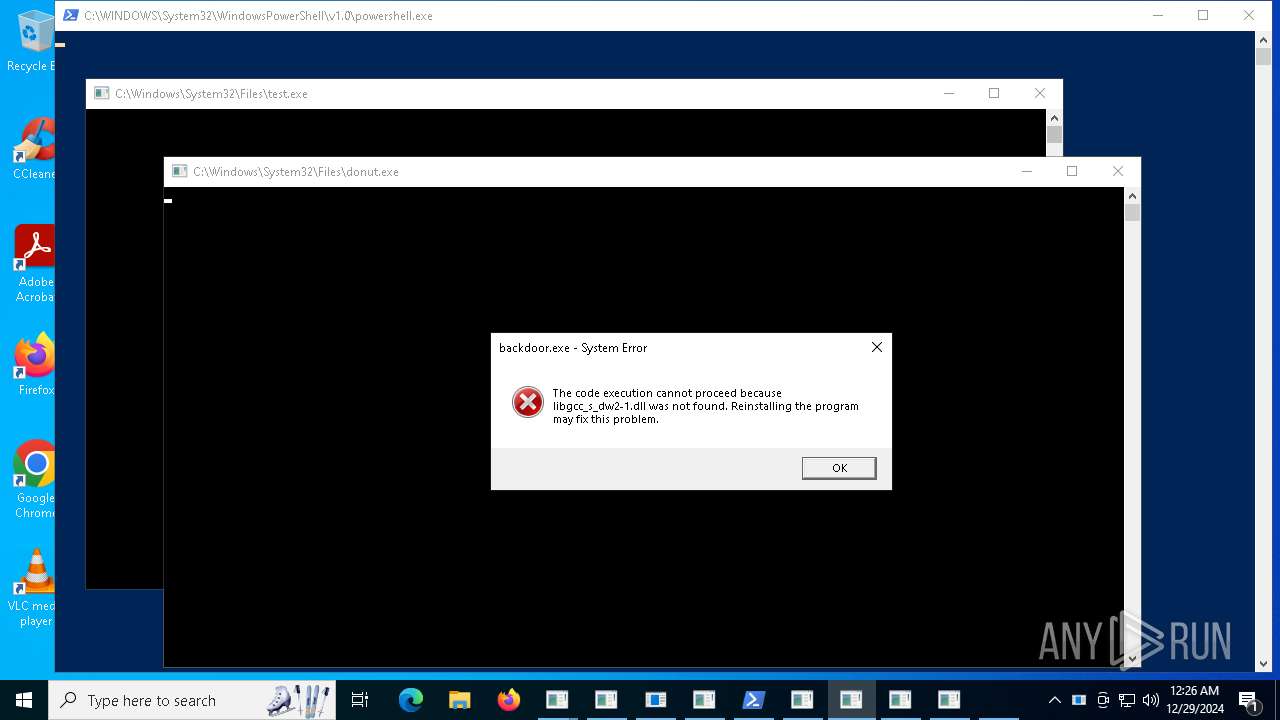
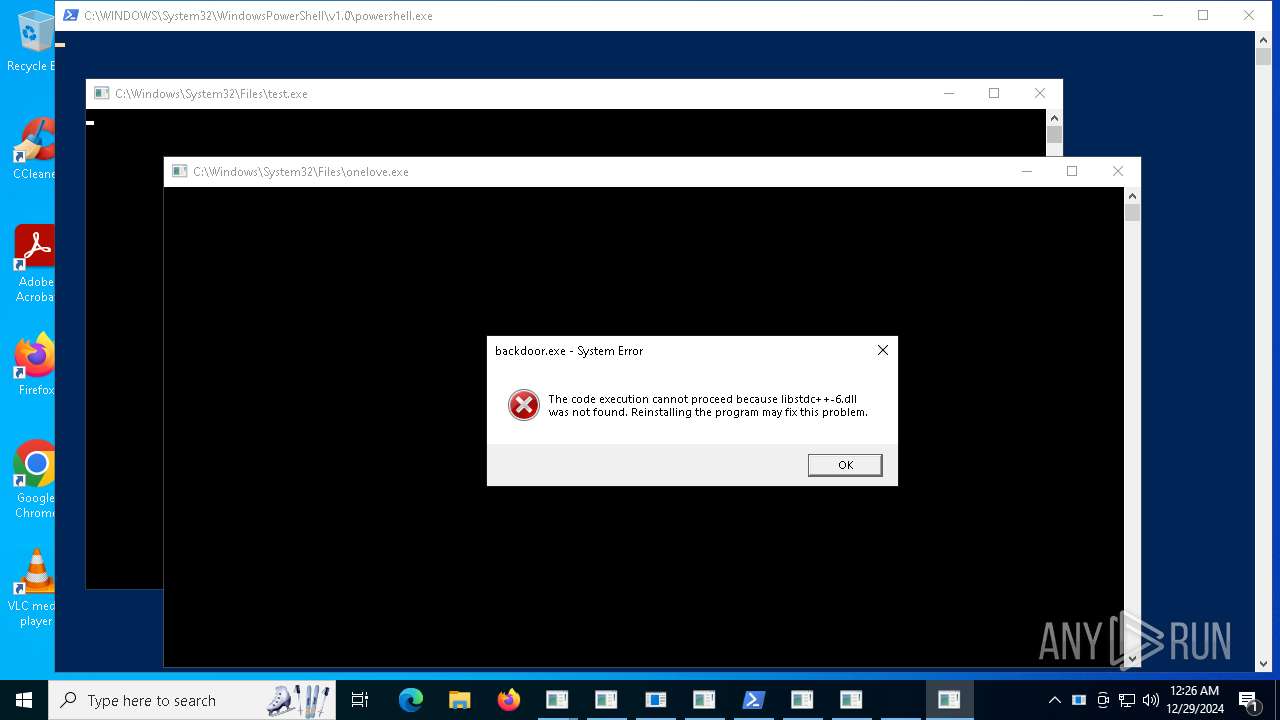
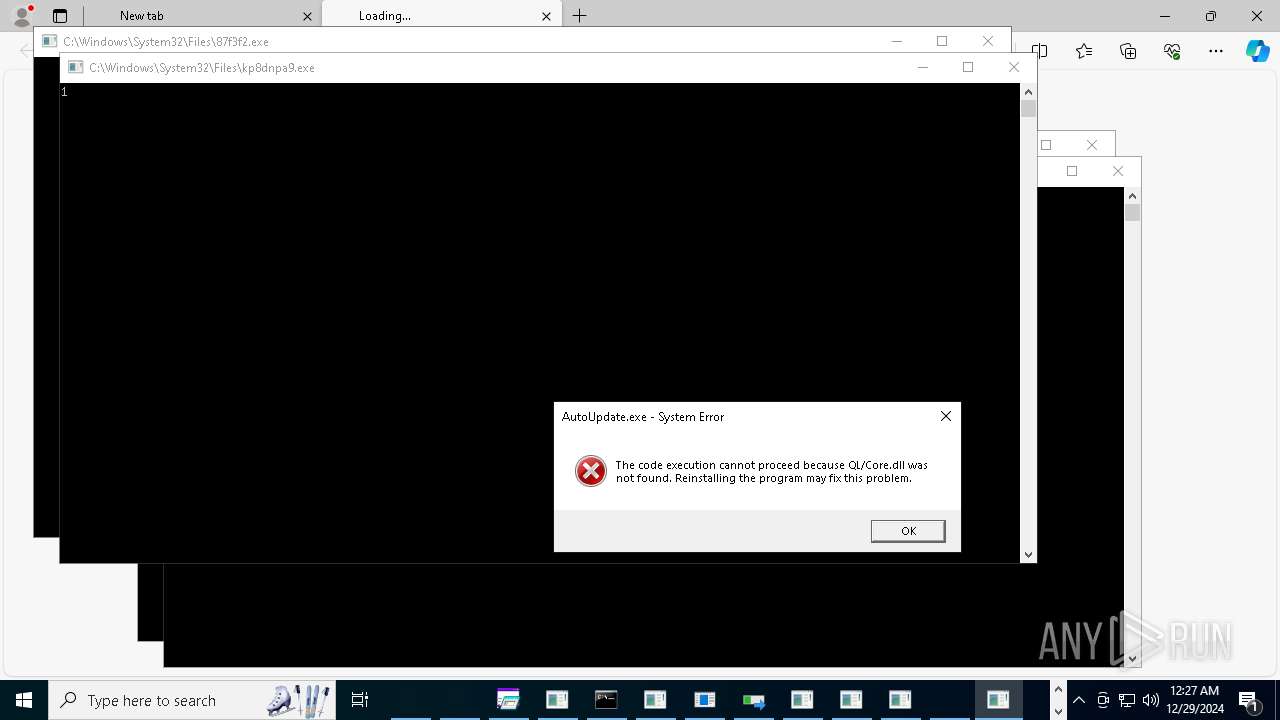
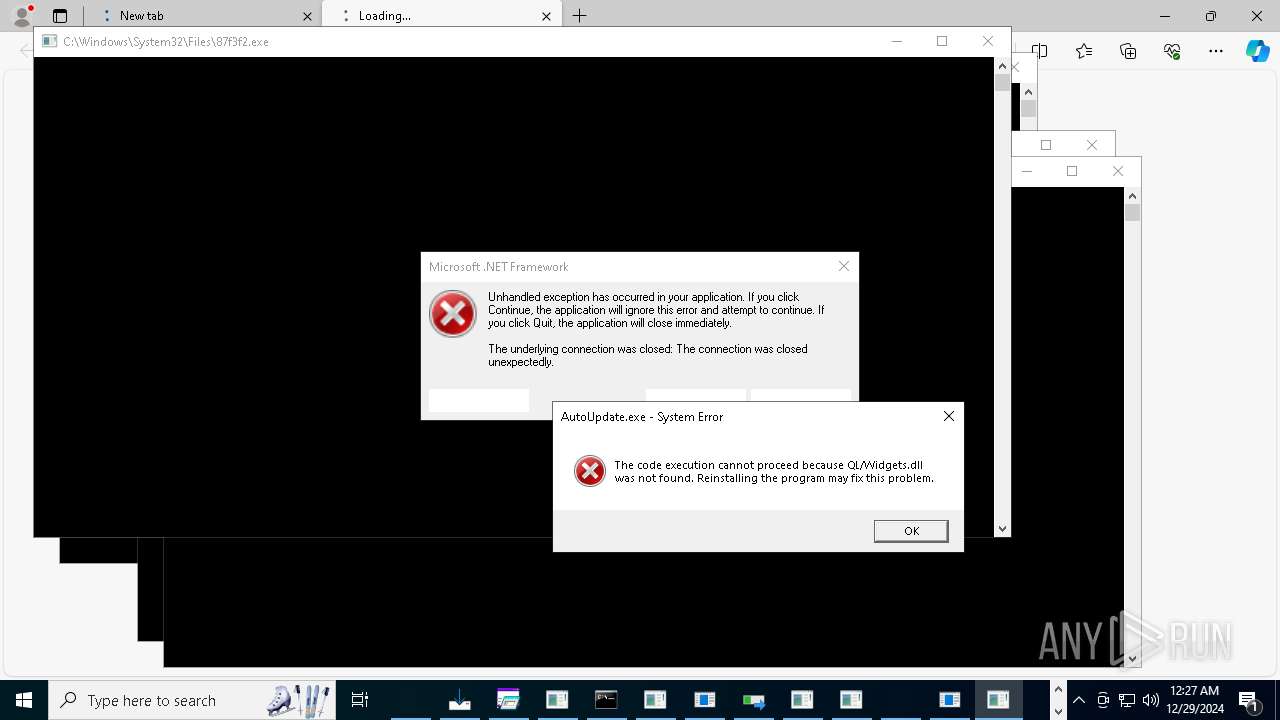
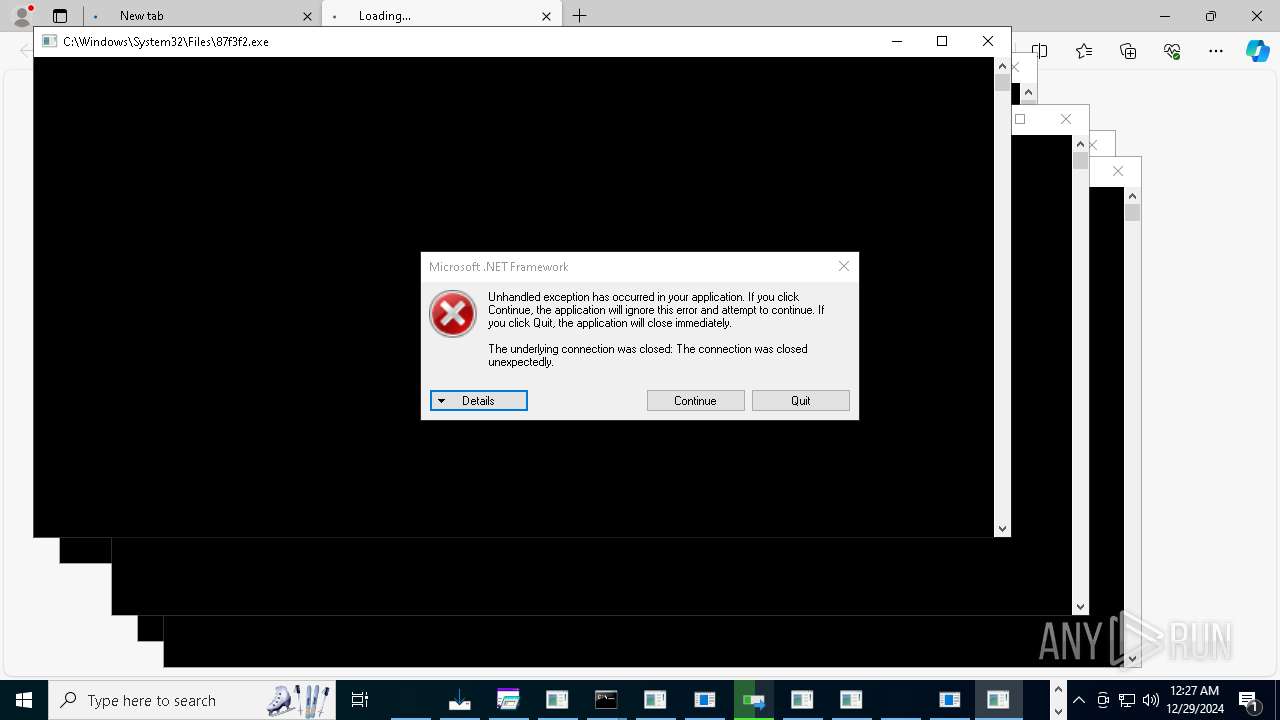
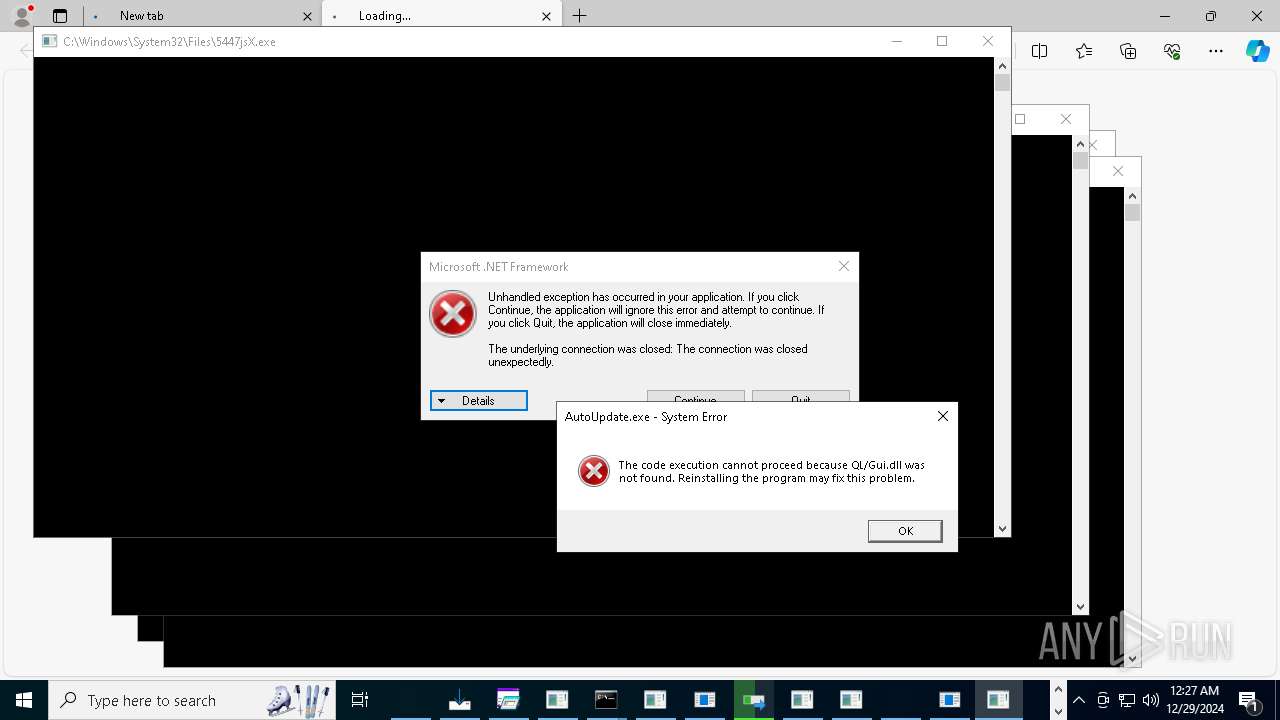
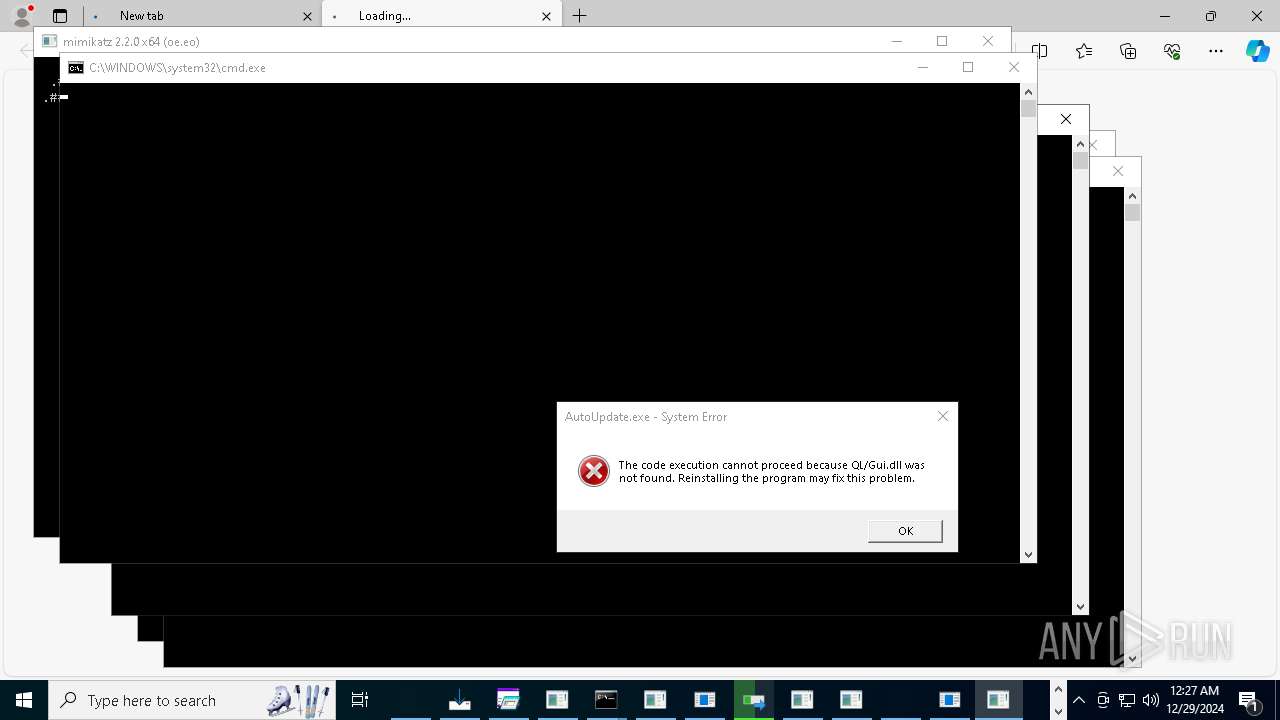
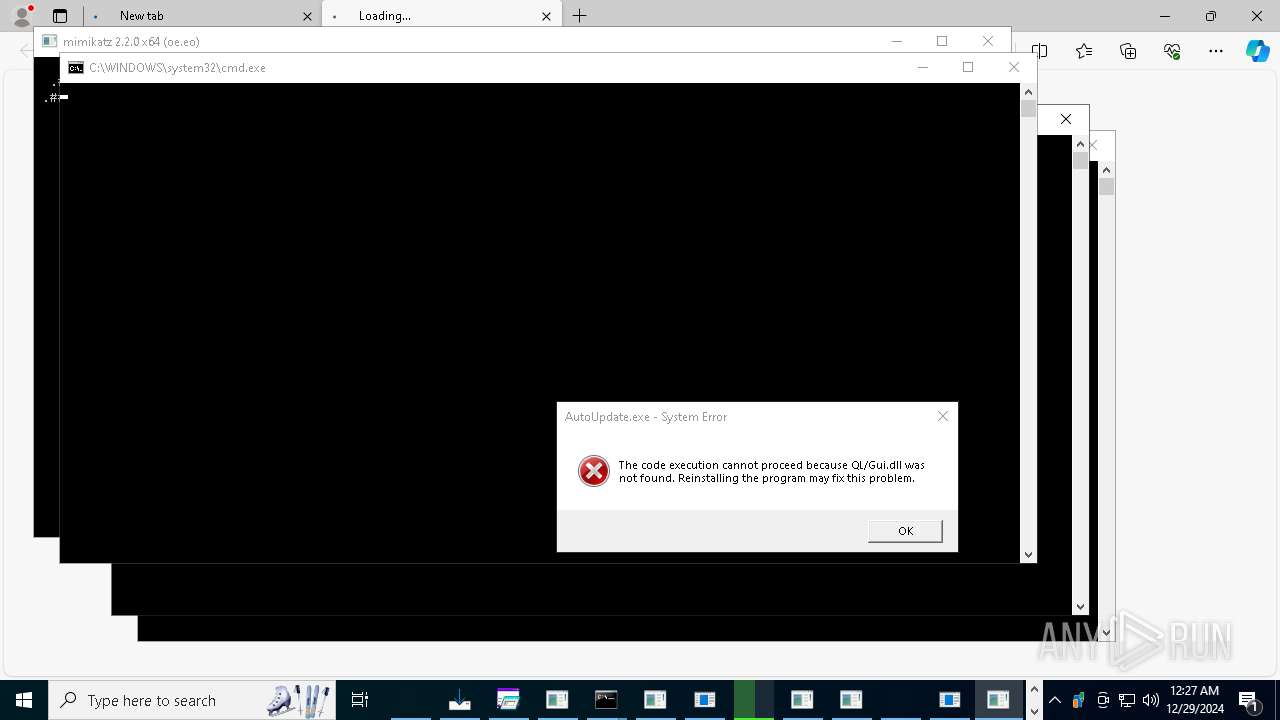
Executes application which crashes
- CnyvVl.exe (PID: 19868)
- 2kudv4ea.exe (PID: 23060)
- chicken123.exe (PID: 22060)
- SVC.exe (PID: 18328)
- gsprout.exe (PID: 19788)
Working with threads in the GNU C Compiler (GCC) libraries related mutex has been found
- c1.exe (PID: 7868)
- c2.exe (PID: 21680)
Reads the Windows owner or organization settings
- steel.tmp (PID: 20872)
- SrbijaSetupHokej.tmp (PID: 19040)
- basx.tmp (PID: 17936)
- utility-inst.tmp (PID: 25240)
Adds/modifies Windows certificates
- RegAsm.exe (PID: 1328)
- powershell.exe (PID: 19288)
- powershell.exe (PID: 19000)
The process drops C-runtime libraries
- steel.tmp (PID: 20872)
- hailhydra.exe (PID: 22172)
- basx.tmp (PID: 17936)
Start notepad (likely ransomware note)
- c2.exe (PID: 21680)
Script adds exclusion process to Windows Defender
- wefhrf.exe (PID: 21204)
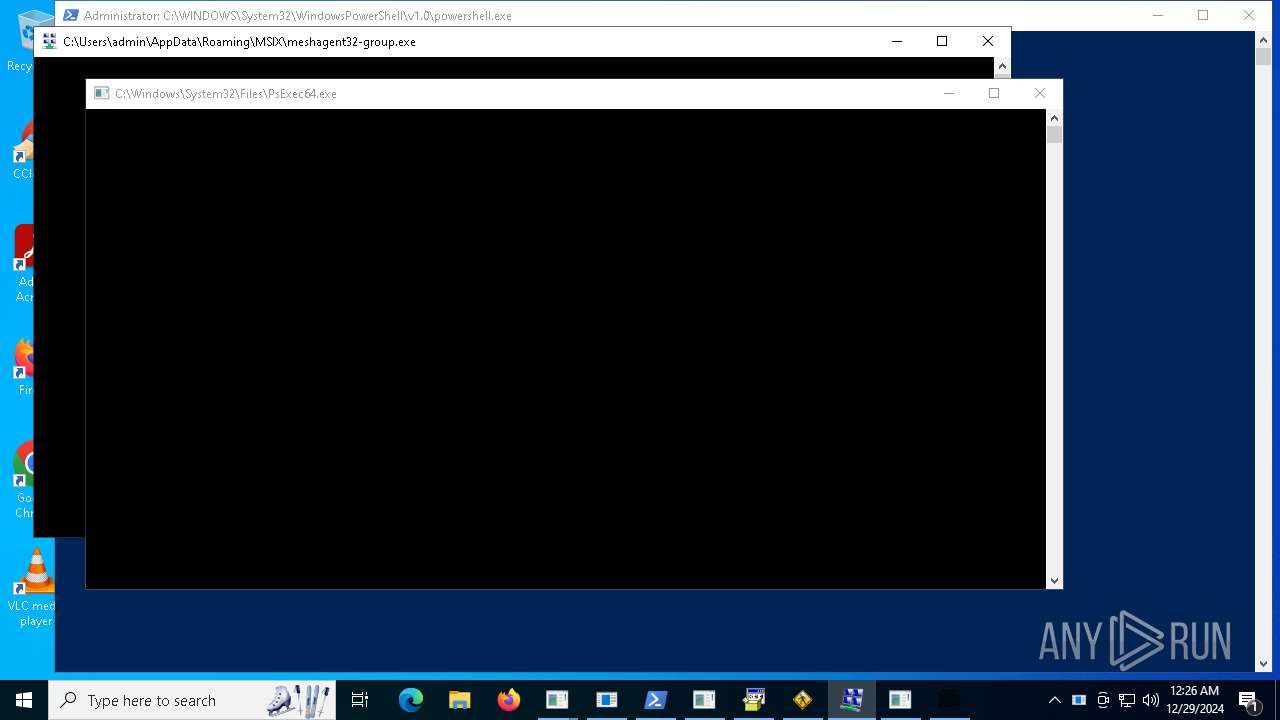
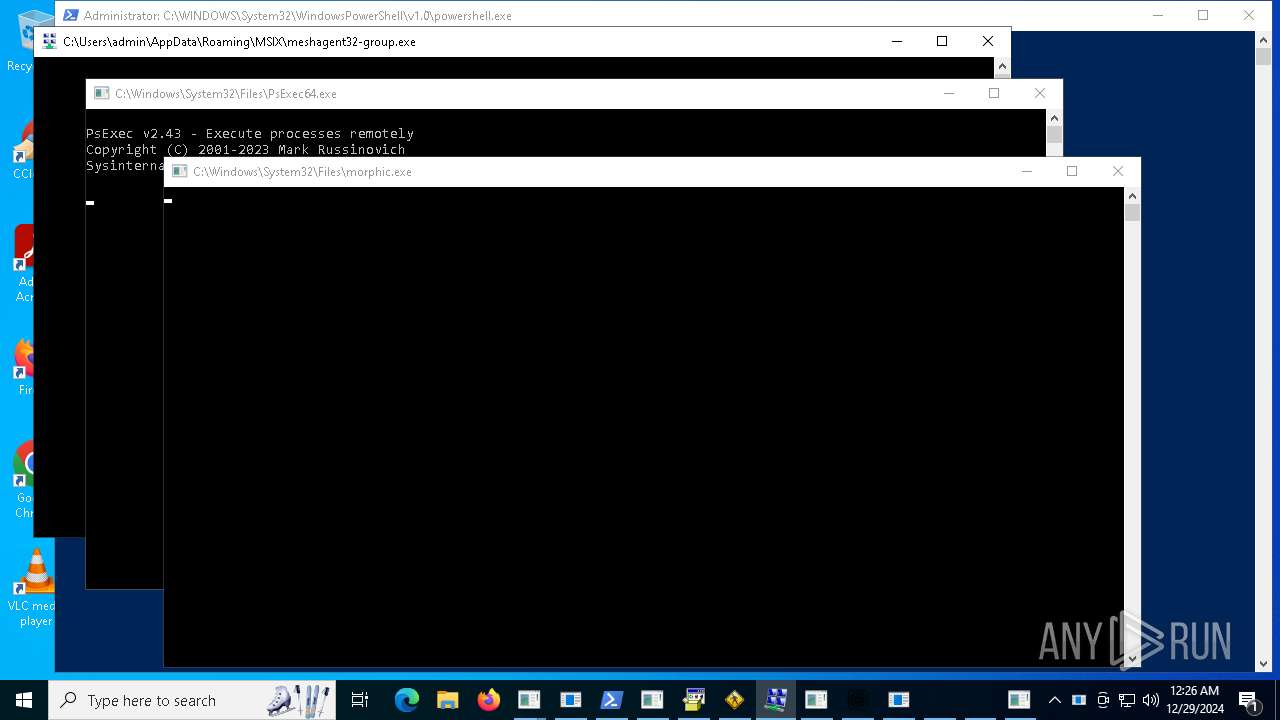
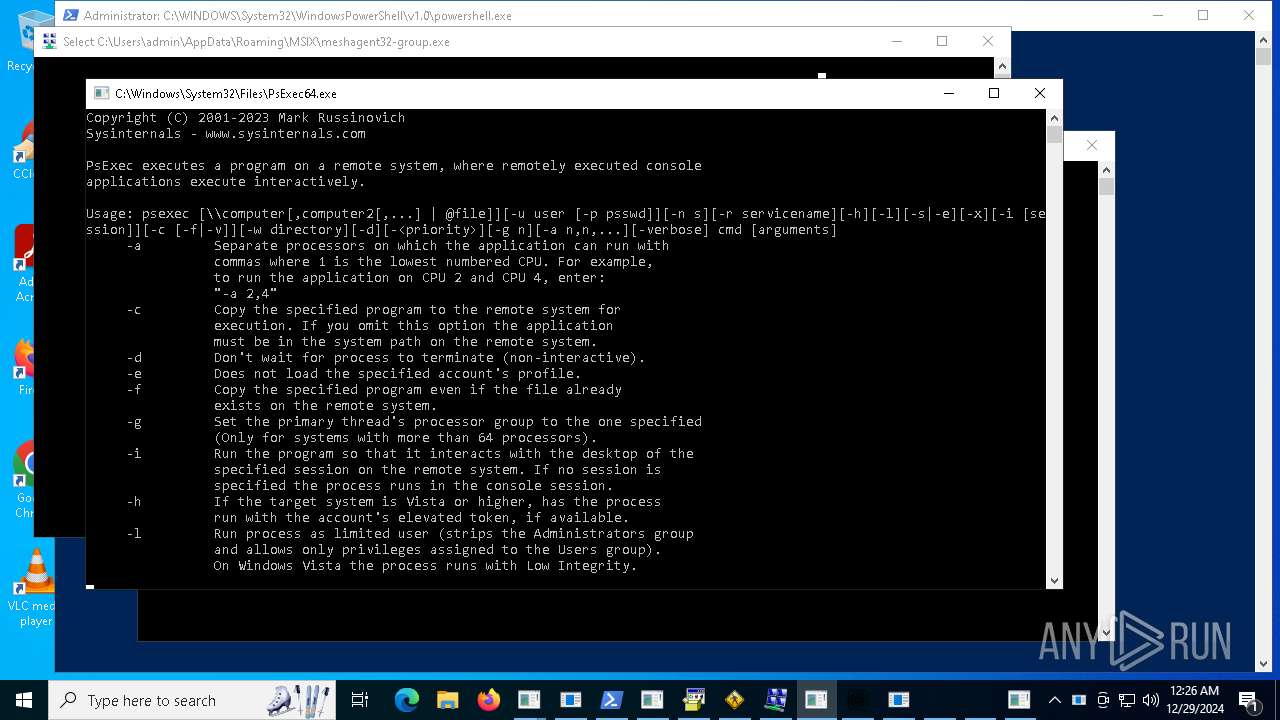
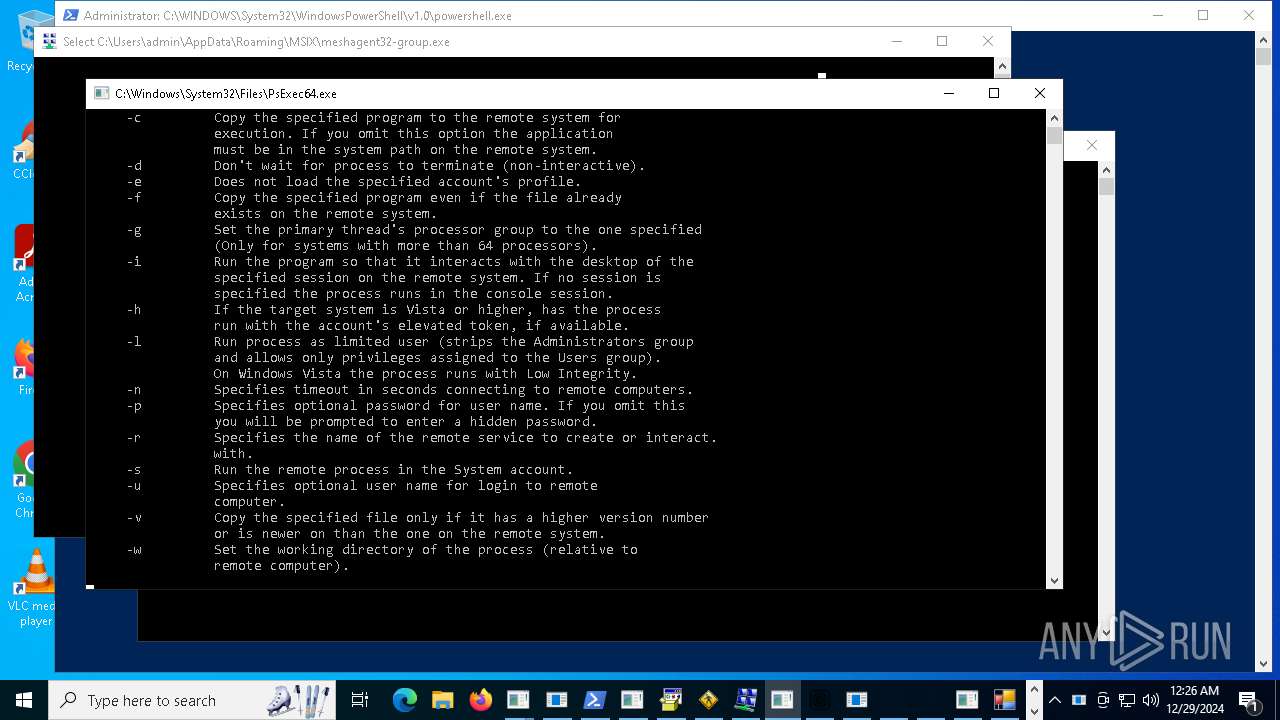
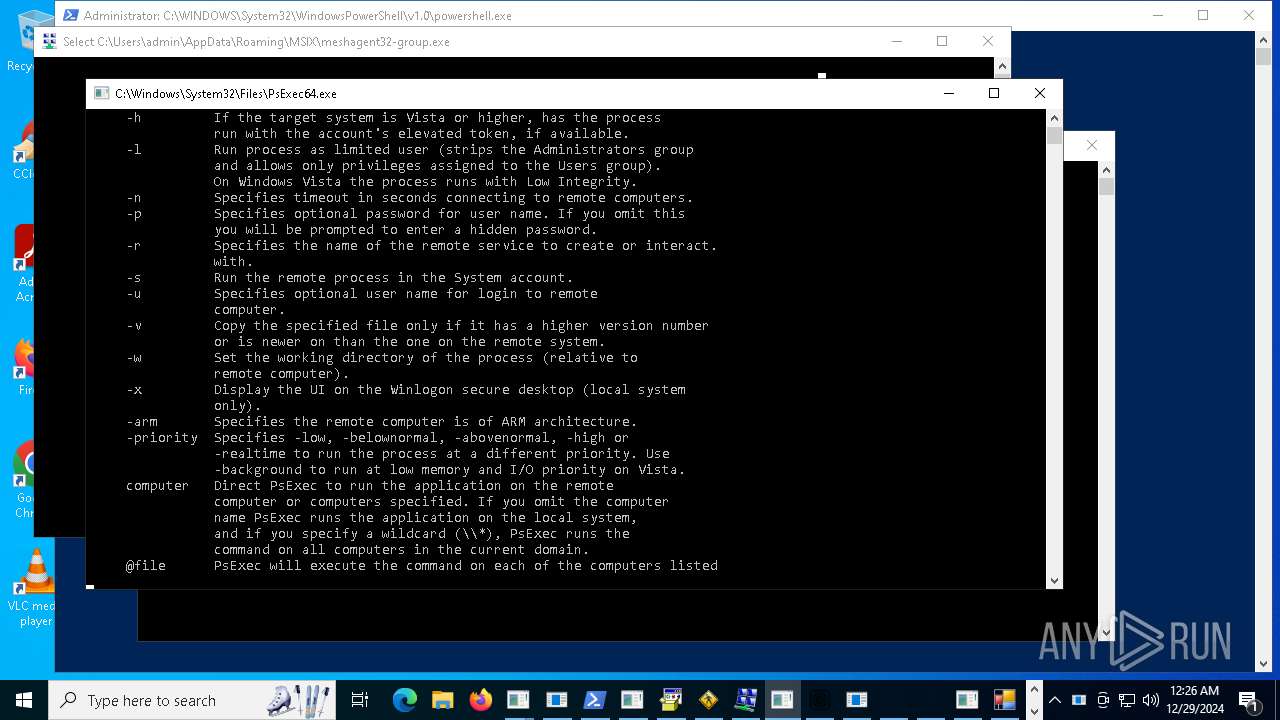
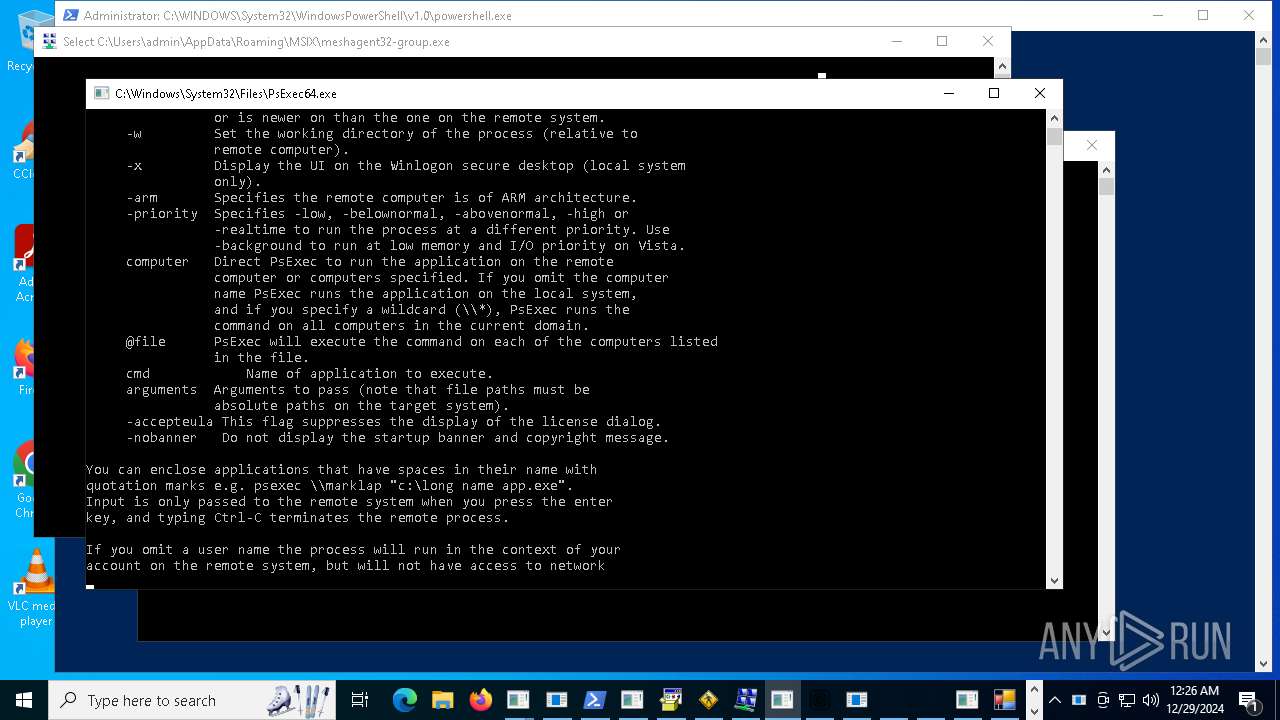
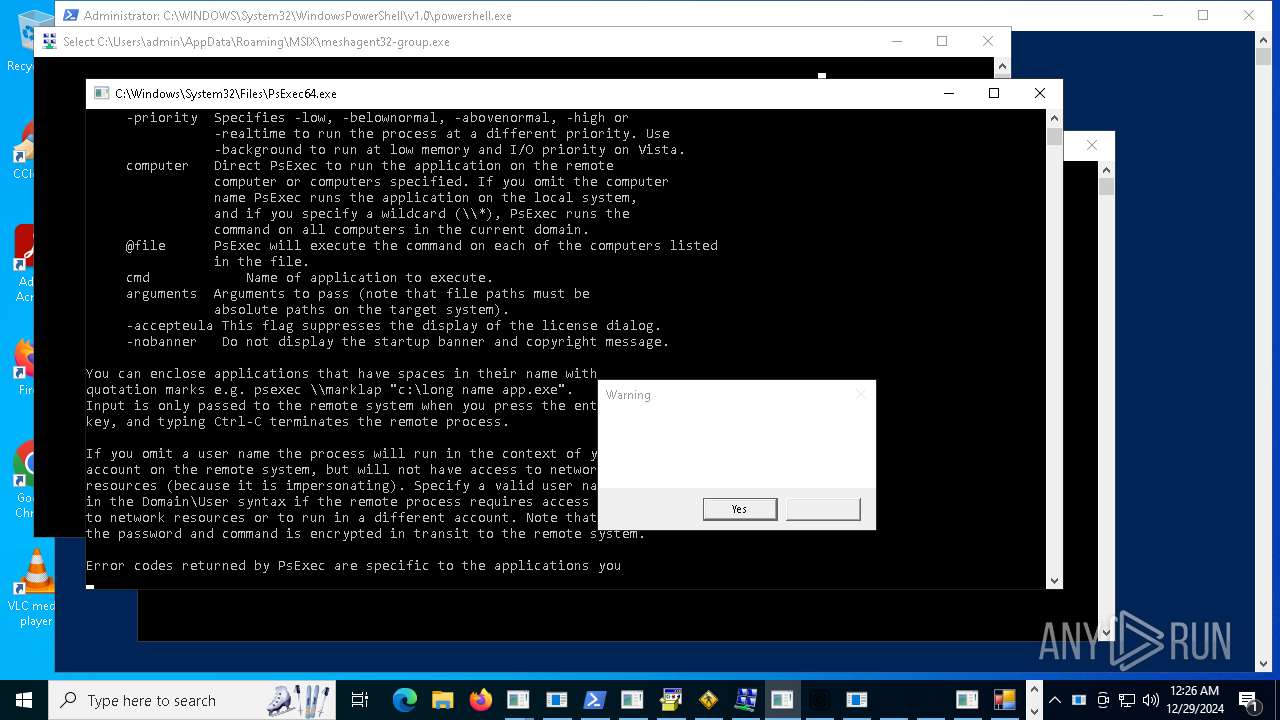
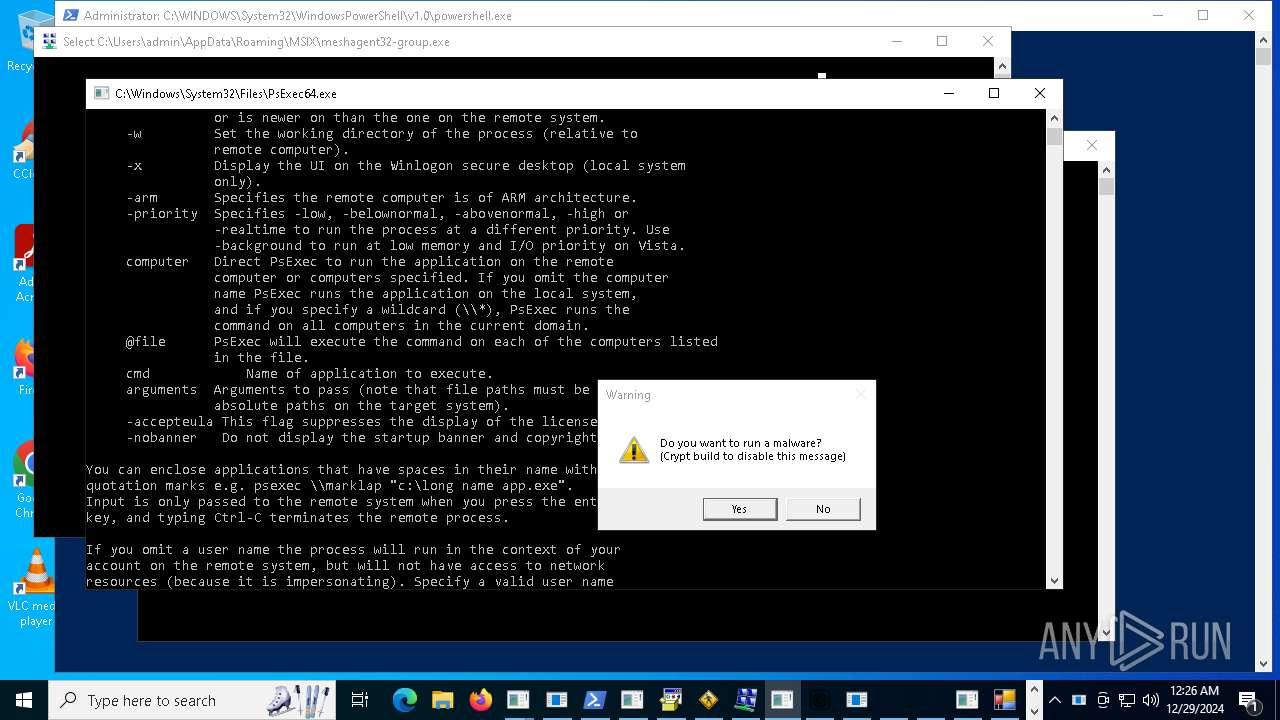
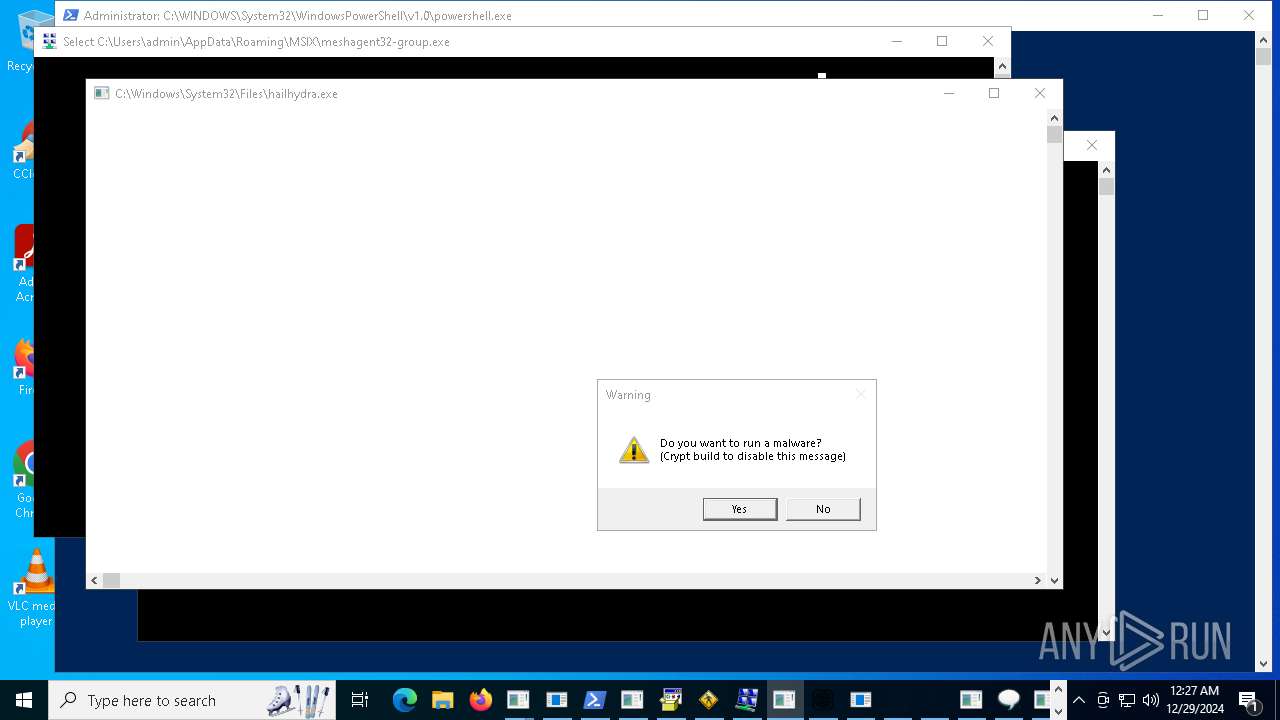
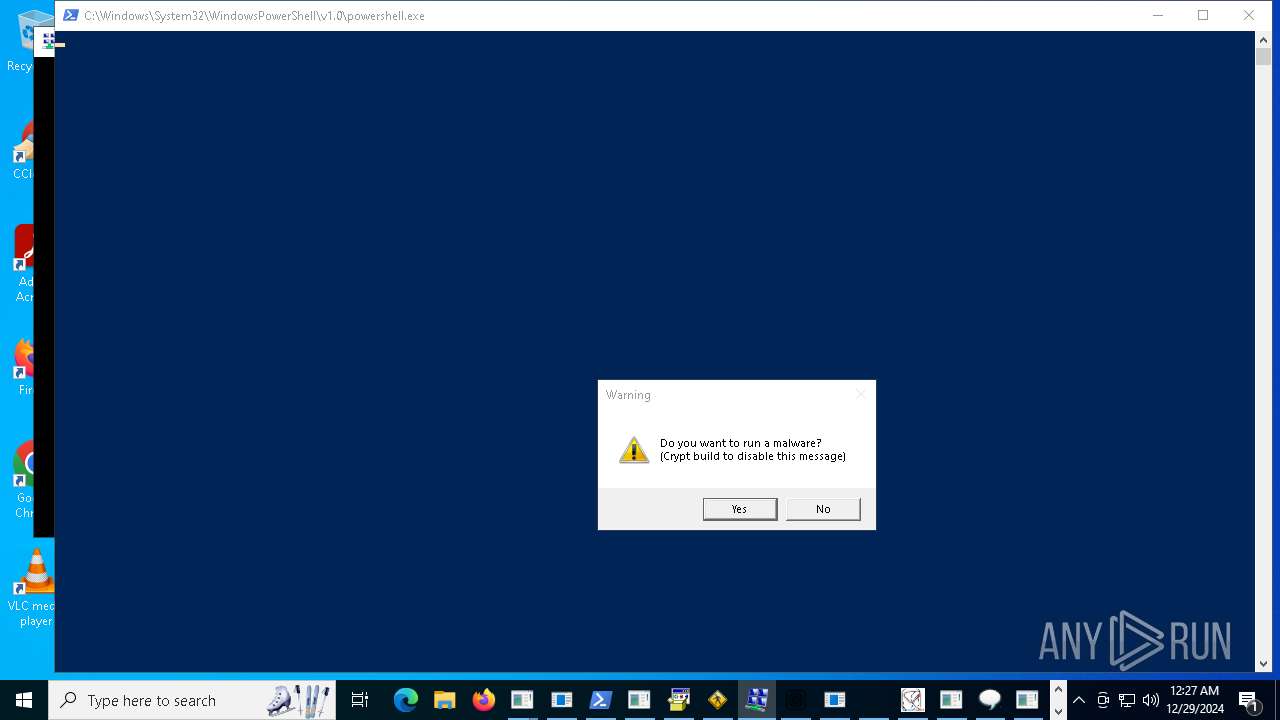
PSEXEC has been detected
- PsExec64.exe (PID: 19364)
Payload loading activity detected
- 22.exe (PID: 20784)
Windows Defender mutex has been found
- jdrgsotrti.exe (PID: 22740)
- kisteruop.exe (PID: 24176)
- 12.exe (PID: 18572)
- krgawdtyjawd.exe (PID: 24624)
- RegAsm.exe (PID: 25808)
- num.exe (PID: 26736)
Reads Microsoft Outlook installation path
- alphaTweaks.exe (PID: 18640)
Connects to FTP
- networkmanager.exe (PID: 21756)
Manipulates environment variables
- powershell.exe (PID: 23776)
Script adds exclusion extension to Windows Defender
- h5a71wdy.exe (PID: 19640)
Connects to SSH
- networkmanager.exe (PID: 21756)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 22068)
- cmd.exe (PID: 23140)
- cmd.exe (PID: 25736)
Reads Internet Explorer settings
- alphaTweaks.exe (PID: 18640)
Loads DLL from Mozilla Firefox
- bypass.exe (PID: 22756)
Process drops python dynamic module
- hailhydra.exe (PID: 22172)
- creal.exe (PID: 15836)
Connecting to InterPlanetary File System domains
- svchost.exe (PID: 2192)
Executes as Windows Service
- Ammyy.exe (PID: 21700)
- qsjxfirefkza.exe (PID: 27212)
Uses powercfg.exe to modify the power settings
- 2r61ahry.exe (PID: 25632)
- qsjxfirefkza.exe (PID: 27212)
- h5a71wdy.exe (PID: 19640)
Windows service management via SC.EXE
- sc.exe (PID: 25180)
- sc.exe (PID: 10720)
Starts SC.EXE for service management
- 2r61ahry.exe (PID: 25632)
- h5a71wdy.exe (PID: 19640)
The executable file from the user directory is run by the CMD process
- update.exe (PID: 23596)
- Discord.exe (PID: 25936)
- clamer.exe (PID: 15036)
- roIrMC.exe (PID: 28600)
Creates a new Windows service
- sc.exe (PID: 17096)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 23944)
Stops a currently running service
- sc.exe (PID: 20012)
- sc.exe (PID: 22396)
- sc.exe (PID: 6984)
- sc.exe (PID: 19004)
- sc.exe (PID: 17872)
- sc.exe (PID: 22056)
Process uninstalls Windows update
- wusa.exe (PID: 23108)
Possible Social Engineering Attempted
- svchost.exe (PID: 2192)
Drops a system driver (possible attempt to evade defenses)
- qsjxfirefkza.exe (PID: 27212)
- file.exe (PID: 26228)
Starts application with an unusual extension
- cmd.exe (PID: 15908)
Crypto Currency Mining Activity Detected
- 4363463463464363463463463.exe (PID: 13876)
- xmbld.exe (PID: 18544)
Mutex name with non-standard characters
- xmbld.exe (PID: 18544)
Write to the desktop.ini file (may be used to cloak folders)
- uhigdbf.exe (PID: 21664)
Starts a Microsoft application from unusual location
- roIrMC.exe (PID: 28600)
INFO
The process uses the downloaded file
- explorer.exe (PID: 4488)
- OpenWith.exe (PID: 6844)
- 4363463463464363463463463.exe (PID: 9488)
- testingg.exe (PID: 15116)
- 4363463463464363463463463.exe (PID: 13820)
- System.exe (PID: 15344)
- armadegon.exe (PID: 15308)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 13684)
- NorthSperm.exe (PID: 15044)
- baedawdgh.exe (PID: 14984)
- 4363463463464363463463463.exe (PID: 8760)
- XClient.exe (PID: 6212)
- ._cache_System.exe (PID: 4328)
- svchost.exe (PID: 3124)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 8596)
- NOTallowedtocrypt.exe (PID: 16236)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 4024)
- av_downloader1.1.exe (PID: 18576)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 11652)
- Minet.exe (PID: 16568)
- Client-built.exe (PID: 15168)
- 4363463463464363463463463.exe (PID: 9564)
- crss.exe (PID: 16588)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 12804)
- run.exe (PID: 4056)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 11560)
- nano.exe (PID: 20220)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 5740)
- 2klz.exe (PID: 20624)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 6664)
- com%20surrogate.exe (PID: 19216)
- 4363463463464363463463463.exe (PID: 10472)
- AsyncClient.exe (PID: 16700)
- 4363463463464363463463463.exe (PID: 9756)
- in.exe (PID: 20460)
- wefhrf.exe (PID: 21204)
- 4363463463464363463463463.exe (PID: 6672)
- Discord.exe (PID: 16680)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 11596)
- Microsoft.exe (PID: 21160)
- 4363463463464363463463463.exe (PID: 11632)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 11780)
- Final.exe (PID: 21724)
- 4363463463464363463463463.exe (PID: 11172)
- Amogus.exe (PID: 21716)
- sharpmonoinjector.exe (PID: 21732)
- blq.exe (PID: 15400)
- Runtime%20Broker.exe (PID: 21748)
- temp.exe (PID: 18792)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 7632)
- ovrflw.exe (PID: 21764)
- njSilent.exe (PID: 21656)
- 4363463463464363463463463.exe (PID: 11756)
- mshta.exe (PID: 9592)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 10020)
- nbothjkd.exe (PID: 15240)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 12864)
- Survox.exe (PID: 23068)
- CleanerV2.exe (PID: 24060)
- uhigdbf.exe (PID: 21664)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 10316)
- av_downloader1.1.exe (PID: 23440)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 11640)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 6752)
- Client-built-Playit.exe (PID: 23796)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 3696)
- fuag.exe (PID: 20992)
- svhost.exe (PID: 25652)
- 4363463463464363463463463.exe (PID: 11524)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- 4363463463464363463463463.exe (PID: 13344)
- taskhost.exe (PID: 22360)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 13160)
- armadegon.exe (PID: 17504)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 10288)
- setup8.exe (PID: 24588)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 11824)
- xs.exe (PID: 19996)
- PowerShell.exe (PID: 21688)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 12848)
Checks supported languages
- SearchApp.exe (PID: 5064)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 5544)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 6096)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 5992)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 4764)
- 4363463463464363463463463.exe (PID: 3420)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 6624)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 7624)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 7812)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 8176)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 8336)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8760)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 9572)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 10032)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 10160)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 10868)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 11568)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 11632)
- 4363463463464363463463463.exe (PID: 11640)
- 4363463463464363463463463.exe (PID: 11732)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 11796)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 11664)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 11856)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 12772)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 12868)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 12864)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 13388)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 13536)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 13564)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 13868)
- IATInfect2008_64.exe (PID: 15036)
- testingg.exe (PID: 15116)
- TPB-1.exe (PID: 15164)
- 4363463463464363463463463.exe (PID: 13820)
- server.exe (PID: 15244)
- armadegon.exe (PID: 15308)
- System.exe (PID: 15344)
- Synaptics.exe (PID: 776)
- 4363463463464363463463463.exe (PID: 13876)
- XClient.exe (PID: 6212)
- svchost.exe (PID: 3124)
- zts.exe (PID: 1304)
- NorthSperm.exe (PID: 15044)
- baedawdgh.exe (PID: 14984)
- ._cache_System.exe (PID: 4328)
- CoronaVirus.exe (PID: 16056)
- NOTallowedtocrypt.exe (PID: 16236)
- Minet.exe (PID: 16568)
- Steam.Upgreyd.exe (PID: 16648)
- crss.exe (PID: 16588)
- Discord.exe (PID: 16680)
- AsyncClient.exe (PID: 16700)
- Server1.exe (PID: 16664)
- TTDesktop18.exe (PID: 17004)
- cli.exe (PID: 16796)
- 76y5trfed675ytg.exe (PID: 17492)
- 3544436.exe (PID: 17252)
- Lab01-02.exe (PID: 17232)
- MSBuild.exe (PID: 18076)
- vpn.exe (PID: 16240)
- feb9sxwk.exe (PID: 18348)
- random.exe (PID: 18152)
- Client-built.exe (PID: 15168)
- 4363463463464363463463463.exe (PID: 10572)
- sound.exe (PID: 18496)
- ShellExperienceHost.exe (PID: 16436)
- NJRat.exe (PID: 18648)
- s.exe (PID: 18384)
- Discordd.exe (PID: 18864)
- PCclear_Eng_mini.exe (PID: 18764)
- Discord3.exe (PID: 18908)
- av_downloader1.1.exe (PID: 18576)
- curlapp64.exe (PID: 19068)
- fern_wifi_recon%252.34.exe (PID: 19196)
- self-injection.exe (PID: 18672)
- onelove.exe (PID: 19108)
- server.exe (PID: 19312)
- Tutorial.exe (PID: 19328)
- Yellow%20Pages%20Scraper.exe (PID: 17124)
- run.exe (PID: 4056)
- NVIDIA.exe (PID: 18480)
- bildnewl.exe (PID: 19644)
- build_2024-07-27_00-41.exe (PID: 19736)
- gsprout.exe (PID: 19788)
- gagagggagagag.exe (PID: 19988)
- xs.exe (PID: 19996)
- system32.exe (PID: 19376)
- GOLD.exe (PID: 19744)
- 123.exe (PID: 19512)
- Sync.exe (PID: 20440)
- nano.exe (PID: 20220)
- nthnaedltg.exe (PID: 19976)
- RegAsm.exe (PID: 1328)
- china.exe (PID: 20616)
- test.exe (PID: 20172)
- 2klz.exe (PID: 20624)
- build3.exe (PID: 20728)
- Mswgoudnv.exe (PID: 21000)
- wefhrf.exe (PID: 21204)
- donut.exe (PID: 20288)
- MSBuild.exe (PID: 21360)
- lkyhjksefa.exe (PID: 21388)
- alphaTweaks.exe (PID: 18640)
- Installeraus.exe (PID: 21372)
- univ.exe (PID: 3812)
- hfaewdth.exe (PID: 21292)
- PowerRat.exe (PID: 6840)
- 22.exe (PID: 20784)
- steel.exe (PID: 21416)
- in.exe (PID: 20460)
- c1.exe (PID: 7868)
- steel.tmp (PID: 20872)
- nbothjkd.exe (PID: 15240)
- aspnet_regbrowsers.exe (PID: 21044)
- GLP_installer_900223086_market.exe (PID: 8280)
- 14082024.exe (PID: 15480)
- build.exe (PID: 19688)
- cccc2.exe (PID: 16220)
- blq.exe (PID: 15400)
- testme.exe (PID: 7612)
- fuag.exe (PID: 20992)
- GIFT-INFO.lMG.exe (PID: 6952)
- armadegon.exe (PID: 17504)
- njSilent.exe (PID: 21656)
- Final.exe (PID: 21724)
- Microsoft.exe (PID: 21160)
- SrbijaSetupHokej.exe (PID: 21672)
- Runtime%20Broker.exe (PID: 21748)
- sharpmonoinjector.exe (PID: 21732)
- qth5kdee.exe (PID: 21804)
- ovrflw.exe (PID: 21764)
- Amogus.exe (PID: 21716)
- pjthjsdjgjrtavv.exe (PID: 21648)
- c2.exe (PID: 21680)
- chicken123.exe (PID: 22060)
- taskhost.exe (PID: 22360)
- RegAsm.exe (PID: 22236)
- meshagent32-group.exe (PID: 1512)
- evetbeta.exe (PID: 21776)
- DeliciousPart.exe (PID: 16240)
- PsExec64.exe (PID: 19364)
- networkmanager.exe (PID: 21756)
- 12.exe (PID: 18572)
- GIFT-INFO.lMG.exe (PID: 22440)
- collinssplashpro32.exe (PID: 21300)
- PURCHASE%20ORDER%20006-2024%20GIA-AV%20Rev%201_pdf.exe (PID: 22076)
- basx.exe (PID: 22408)
- SrbijaSetupHokej.tmp (PID: 19040)
- morphic.exe (PID: 21740)
- kxfh9qhs.exe (PID: 5268)
- basx.tmp (PID: 17936)
- MYNEWRDX.exe (PID: 19596)
- TestExe.exe (PID: 19612)
- pyjnkasedf.exe (PID: 20320)
- AdvancedRun.exe (PID: 22680)
- jdrgsotrti.exe (PID: 22740)
- 2kudv4ea.exe (PID: 23060)
- builder.exe (PID: 22888)
- Indentif.exe (PID: 22944)
- buildred.exe (PID: 22696)
- h5a71wdy.exe (PID: 19640)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- RDX123456.exe (PID: 23092)
- Survox.exe (PID: 23068)
- bypass.exe (PID: 22756)
- jtkhikadjthsad.exe (PID: 23036)
- kitty.exe (PID: 23488)
- SVC.exe (PID: 18328)
- anticheat.exe (PID: 1596)
- imagelogger.exe (PID: 19168)
- 2kudv4ea.exe (PID: 23720)
- service.exe (PID: 15460)
- windowsexecutable.exe (PID: 20216)
- dayum.exe (PID: 23792)
- bundle.exe (PID: 23808)
- utility-inst.exe (PID: 23696)
- MSBuild.exe (PID: 24028)
- tn8cdkzn.exe (PID: 22952)
- Mswgoudnv.exe (PID: 23916)
- aaa%20(3).exe (PID: 23688)
- cvv.exe (PID: 24376)
- neon.exe (PID: 23784)
- mzjfgebm.exe (PID: 24292)
- svhostc.exe (PID: 24460)
- build.exe (PID: 17784)
- InstallSetup.exe (PID: 24404)
- CleanerV2.exe (PID: 24060)
- cnct.exe (PID: 24284)
- ._cache_blq.exe (PID: 24520)
- jerniuiopu.exe (PID: 22792)
- mswabnet.exe (PID: 24580)
- hailhydra.exe (PID: 22172)
- utility-inst.tmp (PID: 25240)
- crypted.exe (PID: 22976)
- svchost.exe (PID: 17916)
- kisteruop.exe (PID: 24176)
- av_downloader1.1.exe (PID: 23440)
- LummaC222222.exe (PID: 22732)
- vlst.exe (PID: 24392)
- yxrd0ob7.exe (PID: 23500)
- DIFF.exe (PID: 25644)
- Client-built-Playit.exe (PID: 23796)
- asd.exe (PID: 24632)
- IT_plan_cifs.exe (PID: 23448)
- 2r61ahry.exe (PID: 25632)
- pyl64.exe (PID: 18560)
- Ammyy.exe (PID: 18188)
- krgawdtyjawd.exe (PID: 24624)
- splwow64.exe (PID: 24872)
- master.exe (PID: 24452)
- main.exe (PID: 26140)
- dvdvideomedia2.exe (PID: 23624)
- boleto.exe (PID: 18624)
- PowerShell.exe (PID: 21688)
- svhost.exe (PID: 25652)
- 87f3f2.exe (PID: 24816)
- cudo.exe (PID: 24684)
- setup8.exe (PID: 24588)
- uhigdbf.exe (PID: 21664)
- xworm.exe (PID: 26160)
- 41m98slk.exe (PID: 26152)
- kp8dnpa9.exe (PID: 23804)
- file.exe (PID: 26228)
- update.exe (PID: 23596)
- lummetc.exe (PID: 23084)
- dxwebsetup.exe (PID: 12060)
- newfile.exe (PID: 18724)
- Update.exe (PID: 9648)
- jwnv23gb.exe (PID: 22392)
- crypteda.exe (PID: 12116)
- NBYS%20AH.NET.exe (PID: 8400)
- S.S.A_Statement_969351.exe (PID: 22932)
- trru7rd2.exe (PID: 25636)
- soft2.exe (PID: 20204)
- jhnykawfkth.exe (PID: 18752)
- kfhtksfesek.exe (PID: 27032)
- svhostc.exe (PID: 26936)
- LummaC22222.exe (PID: 27024)
- te3tlsre.exe (PID: 27132)
- Identification.exe (PID: 26252)
- AppLaunch.exe (PID: 26924)
- mountain-pasture.exe (PID: 20012)
- LedgerUpdater.exe (PID: 6984)
- Discord.exe (PID: 25936)
- svchostinter.exe (PID: 11684)
- qsjxfirefkza.exe (PID: 27212)
- PctOccurred.exe (PID: 21796)
- NoMoreRansom.exe (PID: 20080)
- Ammyy.exe (PID: 27280)
- 5447jsX.exe (PID: 25332)
- 2v6wf6kn.exe (PID: 23260)
- 3e3ev3.exe (PID: 21240)
- ewrvuh.exe (PID: 26676)
- NVIDIAS.exe (PID: 18352)
- v_dolg.exe (PID: 25020)
- MSBuild.exe (PID: 23016)
- MSBuild.exe (PID: 17328)
- petya.exe (PID: 27236)
- clamer.exe (PID: 15036)
- chcp.com (PID: 17080)
- RegAsm.exe (PID: 25808)
- dw20.exe (PID: 24212)
- lxrv.exe (PID: 13788)
- ednfosi.exe (PID: 24548)
- creal.exe (PID: 15836)
- request.exe (PID: 16912)
- xmbld.exe (PID: 18544)
- visagiftcardgen.exe (PID: 27472)
- InstallerPack_20.1.23770_win64.exe (PID: 23116)
- myrdx.exe (PID: 19488)
- yoyf.exe (PID: 15180)
- hhnjqu9y.exe (PID: 10960)
- khtoawdltrha.exe (PID: 17116)
- num.exe (PID: 26736)
- qqq.exe (PID: 27892)
- sgx4824p.exe (PID: 27956)
- x6uvjuko.exe (PID: 27784)
- ddosziller.exe (PID: 28168)
- NOTallowedtocrypt.exe (PID: 28284)
- Setup2.exe (PID: 23900)
- PURLOG.exe (PID: 28364)
- jgesfyhjsefa.exe (PID: 28568)
- VidsUsername.exe (PID: 28492)
- ataturk.exe (PID: 28640)
- scj7cm7v.exe (PID: 24744)
- dw20.exe (PID: 4772)
- 3344.exe (PID: 22760)
- dw20.exe (PID: 27864)
- fud2.exe (PID: 15804)
- XClient_protected.exe (PID: 28740)
- hjgesadfseawd.exe (PID: 26016)
- system404.exe (PID: 24852)
- roIrMC.exe (PID: 28600)
- srtware.exe (PID: 27656)
- DecryptJohn.exe (PID: 27872)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
- OpenWith.exe (PID: 6844)
- notepad.exe (PID: 6992)
- cmd.exe (PID: 18600)
- com%20surrogate.exe (PID: 19216)
- cmd.exe (PID: 20896)
- temp.exe (PID: 18792)
- notepad.exe (PID: 22456)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4488)
- OpenWith.exe (PID: 6844)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 5544)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 6624)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 4764)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 6096)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 5992)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 3420)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 7624)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 7812)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 8176)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8336)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 8760)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 9572)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 10032)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 10160)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 10868)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 11568)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 11796)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 11732)
- 4363463463464363463463463.exe (PID: 11664)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 11640)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11856)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 12772)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 12868)
- 4363463463464363463463463.exe (PID: 12864)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 13388)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 13536)
- 4363463463464363463463463.exe (PID: 13564)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 13820)
- TPB-1.exe (PID: 15164)
- armadegon.exe (PID: 15308)
- ._cache_System.exe (PID: 4328)
- XClient.exe (PID: 6212)
- zts.exe (PID: 1304)
- svchost.exe (PID: 3124)
- 4363463463464363463463463.exe (PID: 11632)
- server.exe (PID: 15244)
- crss.exe (PID: 16588)
- cli.exe (PID: 16796)
- Discord.exe (PID: 16680)
- Client-built.exe (PID: 15168)
- imagelogger.exe (PID: 19168)
- AsyncClient.exe (PID: 16700)
- Discord3.exe (PID: 18908)
- Discordd.exe (PID: 18864)
- MSBuild.exe (PID: 18076)
- Tutorial.exe (PID: 19328)
- Yellow%20Pages%20Scraper.exe (PID: 17124)
- NVIDIA.exe (PID: 18480)
- nano.exe (PID: 20220)
- RegAsm.exe (PID: 1328)
- gagagggagagag.exe (PID: 19988)
- bildnewl.exe (PID: 19644)
- Mswgoudnv.exe (PID: 21000)
- Steam.Upgreyd.exe (PID: 16648)
- server.exe (PID: 19312)
- MSBuild.exe (PID: 21360)
- Server1.exe (PID: 16664)
- xs.exe (PID: 19996)
- 2klz.exe (PID: 20624)
- alphaTweaks.exe (PID: 18640)
- Sync.exe (PID: 20440)
- aspnet_regbrowsers.exe (PID: 21044)
- nbothjkd.exe (PID: 15240)
- build.exe (PID: 19688)
- 14082024.exe (PID: 15480)
- Final.exe (PID: 21724)
- fuag.exe (PID: 20992)
- GIFT-INFO.lMG.exe (PID: 6952)
- Amogus.exe (PID: 21716)
- c1.exe (PID: 7868)
- build_2024-07-27_00-41.exe (PID: 19736)
- Runtime%20Broker.exe (PID: 21748)
- NJRat.exe (PID: 18648)
- GLP_installer_900223086_market.exe (PID: 8280)
- system32.exe (PID: 19376)
- GIFT-INFO.lMG.exe (PID: 22440)
- taskhost.exe (PID: 22360)
- TestExe.exe (PID: 19612)
- morphic.exe (PID: 21740)
- wefhrf.exe (PID: 21204)
- bypass.exe (PID: 22756)
- sharpmonoinjector.exe (PID: 21732)
- Synaptics.exe (PID: 776)
- Survox.exe (PID: 23068)
- windowsexecutable.exe (PID: 20216)
- MYNEWRDX.exe (PID: 19596)
- pjthjsdjgjrtavv.exe (PID: 21648)
- anticheat.exe (PID: 1596)
- MSBuild.exe (PID: 24028)
- buildred.exe (PID: 22696)
- build.exe (PID: 17784)
- pyjnkasedf.exe (PID: 20320)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- mswabnet.exe (PID: 24580)
- gsprout.exe (PID: 19788)
- testme.exe (PID: 7612)
- aaa%20(3).exe (PID: 23688)
- neon.exe (PID: 23784)
- DIFF.exe (PID: 25644)
- CleanerV2.exe (PID: 24060)
- vlst.exe (PID: 24392)
- Client-built-Playit.exe (PID: 23796)
- PowerShell.exe (PID: 21688)
- Indentif.exe (PID: 22944)
- boleto.exe (PID: 18624)
- jwnv23gb.exe (PID: 22392)
- svhost.exe (PID: 25652)
- jtkhikadjthsad.exe (PID: 23036)
- bundle.exe (PID: 23808)
- trru7rd2.exe (PID: 25636)
- newfile.exe (PID: 18724)
- te3tlsre.exe (PID: 27132)
- svchost.exe (PID: 17916)
- S.S.A_Statement_969351.exe (PID: 22932)
- svchostinter.exe (PID: 11684)
- LedgerUpdater.exe (PID: 6984)
- update.exe (PID: 23596)
- 3e3ev3.exe (PID: 21240)
- MSBuild.exe (PID: 23016)
- 2v6wf6kn.exe (PID: 23260)
- NVIDIAS.exe (PID: 18352)
- MSBuild.exe (PID: 17328)
- NBYS%20AH.NET.exe (PID: 8400)
- jerniuiopu.exe (PID: 22792)
- dw20.exe (PID: 24212)
- lxrv.exe (PID: 13788)
- ednfosi.exe (PID: 24548)
- yoyf.exe (PID: 15180)
- Discord.exe (PID: 25936)
- PURLOG.exe (PID: 28364)
- jgesfyhjsefa.exe (PID: 28568)
- ddosziller.exe (PID: 28168)
- dw20.exe (PID: 4772)
- scj7cm7v.exe (PID: 24744)
- dw20.exe (PID: 27864)
- hjgesadfseawd.exe (PID: 26016)
Manual execution by a user
- cmd.exe (PID: 5200)
- msedge.exe (PID: 20832)
- Mswgoudnv.exe (PID: 23916)
- cmd.exe (PID: 26584)
- InstallUtil.exe (PID: 21180)
- InstallUtil.exe (PID: 9860)
- InstallUtil.exe (PID: 20804)
- InstallUtil.exe (PID: 15908)
- InstallUtil.exe (PID: 17440)
- InstallUtil.exe (PID: 10720)
- InstallUtil.exe (PID: 21288)
- InstallUtil.exe (PID: 13916)
Process checks computer location settings
- SearchApp.exe (PID: 5064)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 9556)
- testingg.exe (PID: 15116)
- System.exe (PID: 15344)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 11560)
- NorthSperm.exe (PID: 15044)
- baedawdgh.exe (PID: 14984)
- 4363463463464363463463463.exe (PID: 8760)
- ._cache_System.exe (PID: 4328)
- svchost.exe (PID: 3124)
- XClient.exe (PID: 6212)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 10936)
- NOTallowedtocrypt.exe (PID: 16236)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 6740)
- av_downloader1.1.exe (PID: 18576)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 9804)
- Minet.exe (PID: 16568)
- 4363463463464363463463463.exe (PID: 11652)
- crss.exe (PID: 16588)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 11604)
- run.exe (PID: 4056)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 10472)
- AsyncClient.exe (PID: 16700)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 9756)
- blq.exe (PID: 15400)
- in.exe (PID: 20460)
- 4363463463464363463463463.exe (PID: 10332)
- wefhrf.exe (PID: 21204)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 8360)
- Discord.exe (PID: 16680)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 3436)
- Microsoft.exe (PID: 21160)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 11632)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 11780)
- Final.exe (PID: 21724)
- ovrflw.exe (PID: 21764)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 11540)
- njSilent.exe (PID: 21656)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 10548)
- sharpmonoinjector.exe (PID: 21732)
- uhigdbf.exe (PID: 21664)
- 4363463463464363463463463.exe (PID: 11716)
- fuag.exe (PID: 20992)
- jhnykawfkth.exe (PID: 18752)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 11640)
- svhostc.exe (PID: 26936)
- av_downloader1.1.exe (PID: 23440)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- taskhost.exe (PID: 22360)
- Ammyy.exe (PID: 27280)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 7652)
- armadegon.exe (PID: 17504)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 10684)
- setup8.exe (PID: 24588)
- 4363463463464363463463463.exe (PID: 8972)
- xs.exe (PID: 19996)
- 4363463463464363463463463.exe (PID: 11824)
- PowerShell.exe (PID: 21688)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 12848)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 5992)
- 4363463463464363463463463.exe (PID: 6624)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 5544)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 3420)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 4764)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 6096)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 7624)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 7812)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8336)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 9572)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 10160)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 10032)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 11568)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11856)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 13536)
- 4363463463464363463463463.exe (PID: 12772)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 13388)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 12864)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 13564)
- 4363463463464363463463463.exe (PID: 11664)
- 4363463463464363463463463.exe (PID: 11732)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 10868)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 11796)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 11640)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 9812)
- TPB-1.exe (PID: 15164)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 8760)
- zts.exe (PID: 1304)
- 4363463463464363463463463.exe (PID: 11632)
- 4363463463464363463463463.exe (PID: 8176)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 12868)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 11848)
- Tutorial.exe (PID: 19328)
- 4363463463464363463463463.exe (PID: 10848)
- Client-built.exe (PID: 15168)
- gagagggagagag.exe (PID: 19988)
- 4363463463464363463463463.exe (PID: 12804)
- c1.exe (PID: 7868)
- build_2024-07-27_00-41.exe (PID: 19736)
- alphaTweaks.exe (PID: 18640)
- cmd.exe (PID: 20896)
- lkyhjksefa.exe (PID: 21388)
- Synaptics.exe (PID: 776)
- notepad.exe (PID: 22456)
- pjthjsdjgjrtavv.exe (PID: 21648)
- pyjnkasedf.exe (PID: 20320)
- RegAsm.exe (PID: 22236)
- qth5kdee.exe (PID: 21804)
- bypass.exe (PID: 22756)
- kxfh9qhs.exe (PID: 5268)
- 2kudv4ea.exe (PID: 23720)
- setup8.exe (PID: 24588)
- jtkhikadjthsad.exe (PID: 23036)
- InstallSetup.exe (PID: 24404)
- Indentif.exe (PID: 22944)
- RDX123456.exe (PID: 23092)
- asd.exe (PID: 24632)
- LummaC222222.exe (PID: 22732)
- 3e3ev3.exe (PID: 21240)
- 2v6wf6kn.exe (PID: 23260)
Reads the computer name
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 4764)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 6096)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 5992)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 5544)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 3420)
- 4363463463464363463463463.exe (PID: 6624)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 7624)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 7812)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 8176)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 8336)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 8760)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 9572)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 10032)
- 4363463463464363463463463.exe (PID: 10160)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 10868)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 11568)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 11632)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 11640)
- 4363463463464363463463463.exe (PID: 11732)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 11664)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 11796)
- 4363463463464363463463463.exe (PID: 11856)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 12772)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 12864)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 12868)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 13388)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 13536)
- 4363463463464363463463463.exe (PID: 13564)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 13868)
- TPB-1.exe (PID: 15164)
- testingg.exe (PID: 15116)
- armadegon.exe (PID: 15308)
- System.exe (PID: 15344)
- server.exe (PID: 15244)
- ._cache_System.exe (PID: 4328)
- Synaptics.exe (PID: 776)
- zts.exe (PID: 1304)
- XClient.exe (PID: 6212)
- svchost.exe (PID: 3124)
- NorthSperm.exe (PID: 15044)
- baedawdgh.exe (PID: 14984)
- CoronaVirus.exe (PID: 16056)
- NOTallowedtocrypt.exe (PID: 16236)
- crss.exe (PID: 16588)
- Steam.Upgreyd.exe (PID: 16648)
- Discord.exe (PID: 16680)
- AsyncClient.exe (PID: 16700)
- Server1.exe (PID: 16664)
- cli.exe (PID: 16796)
- TTDesktop18.exe (PID: 17004)
- 3544436.exe (PID: 17252)
- Lab01-02.exe (PID: 17232)
- MSBuild.exe (PID: 18076)
- ShellExperienceHost.exe (PID: 16436)
- Client-built.exe (PID: 15168)
- alphaTweaks.exe (PID: 18640)
- av_downloader1.1.exe (PID: 18576)
- NJRat.exe (PID: 18648)
- Minet.exe (PID: 16568)
- Discordd.exe (PID: 18864)
- Discord3.exe (PID: 18908)
- PCclear_Eng_mini.exe (PID: 18764)
- curlapp64.exe (PID: 19068)
- self-injection.exe (PID: 18672)
- imagelogger.exe (PID: 19168)
- run.exe (PID: 4056)
- Yellow%20Pages%20Scraper.exe (PID: 17124)
- system32.exe (PID: 19376)
- Tutorial.exe (PID: 19328)
- gsprout.exe (PID: 19788)
- bildnewl.exe (PID: 19644)
- xs.exe (PID: 19996)
- gagagggagagag.exe (PID: 19988)
- GOLD.exe (PID: 19744)
- 123.exe (PID: 19512)
- nthnaedltg.exe (PID: 19976)
- RegAsm.exe (PID: 1328)
- Sync.exe (PID: 20440)
- NVIDIA.exe (PID: 18480)
- 2klz.exe (PID: 20624)
- Mswgoudnv.exe (PID: 21000)
- china.exe (PID: 20616)
- server.exe (PID: 19312)
- wefhrf.exe (PID: 21204)
- MSBuild.exe (PID: 21360)
- lkyhjksefa.exe (PID: 21388)
- PowerRat.exe (PID: 6840)
- steel.tmp (PID: 20872)
- c1.exe (PID: 7868)
- 22.exe (PID: 20784)
- build.exe (PID: 19688)
- 14082024.exe (PID: 15480)
- nbothjkd.exe (PID: 15240)
- aspnet_regbrowsers.exe (PID: 21044)
- build_2024-07-27_00-41.exe (PID: 19736)
- nano.exe (PID: 20220)
- in.exe (PID: 20460)
- cccc2.exe (PID: 16220)
- testme.exe (PID: 7612)
- blq.exe (PID: 15400)
- fuag.exe (PID: 20992)
- GIFT-INFO.lMG.exe (PID: 6952)
- GLP_installer_900223086_market.exe (PID: 8280)
- armadegon.exe (PID: 17504)
- Microsoft.exe (PID: 21160)
- Final.exe (PID: 21724)
- Amogus.exe (PID: 21716)
- Runtime%20Broker.exe (PID: 21748)
- pjthjsdjgjrtavv.exe (PID: 21648)
- sharpmonoinjector.exe (PID: 21732)
- RegAsm.exe (PID: 22236)
- ovrflw.exe (PID: 21764)
- kxfh9qhs.exe (PID: 5268)
- taskhost.exe (PID: 22360)
- SrbijaSetupHokej.tmp (PID: 19040)
- GIFT-INFO.lMG.exe (PID: 22440)
- meshagent32-group.exe (PID: 1512)
- uhigdbf.exe (PID: 21664)
- PsExec64.exe (PID: 19364)
- DeliciousPart.exe (PID: 16240)
- collinssplashpro32.exe (PID: 21300)
- basx.tmp (PID: 17936)
- univ.exe (PID: 3812)
- morphic.exe (PID: 21740)
- TestExe.exe (PID: 19612)
- njSilent.exe (PID: 21656)
- qth5kdee.exe (PID: 21804)
- pyjnkasedf.exe (PID: 20320)
- AdvancedRun.exe (PID: 22680)
- evetbeta.exe (PID: 21776)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- Indentif.exe (PID: 22944)
- PURCHASE%20ORDER%20006-2024%20GIA-AV%20Rev%201_pdf.exe (PID: 22076)
- jdrgsotrti.exe (PID: 22740)
- jtkhikadjthsad.exe (PID: 23036)
- kitty.exe (PID: 23488)
- SVC.exe (PID: 18328)
- buildred.exe (PID: 22696)
- bypass.exe (PID: 22756)
- MYNEWRDX.exe (PID: 19596)
- windowsexecutable.exe (PID: 20216)
- 2kudv4ea.exe (PID: 23720)
- tn8cdkzn.exe (PID: 22952)
- MSBuild.exe (PID: 24028)
- aaa%20(3).exe (PID: 23688)
- bundle.exe (PID: 23808)
- CleanerV2.exe (PID: 24060)
- InstallSetup.exe (PID: 24404)
- anticheat.exe (PID: 1596)
- neon.exe (PID: 23784)
- build.exe (PID: 17784)
- Mswgoudnv.exe (PID: 23916)
- mswabnet.exe (PID: 24580)
- LummaC222222.exe (PID: 22732)
- dayum.exe (PID: 23792)
- utility-inst.tmp (PID: 25240)
- RDX123456.exe (PID: 23092)
- hailhydra.exe (PID: 22172)
- cvv.exe (PID: 24376)
- 12.exe (PID: 18572)
- kisteruop.exe (PID: 24176)
- ._cache_blq.exe (PID: 24520)
- av_downloader1.1.exe (PID: 23440)
- lummetc.exe (PID: 23084)
- DIFF.exe (PID: 25644)
- Ammyy.exe (PID: 18188)
- crypted.exe (PID: 22976)
- Client-built-Playit.exe (PID: 23796)
- krgawdtyjawd.exe (PID: 24624)
- setup8.exe (PID: 24588)
- jerniuiopu.exe (PID: 22792)
- boleto.exe (PID: 18624)
- k360.exe (PID: 23076)
- svhost.exe (PID: 25652)
- PowerShell.exe (PID: 21688)
- vlst.exe (PID: 24392)
- Survox.exe (PID: 23068)
- file.exe (PID: 26228)
- jwnv23gb.exe (PID: 22392)
- jhnykawfkth.exe (PID: 18752)
- asd.exe (PID: 24632)
- trru7rd2.exe (PID: 25636)
- NBYS%20AH.NET.exe (PID: 8400)
- newfile.exe (PID: 18724)
- dvdvideomedia2.exe (PID: 23624)
- S.S.A_Statement_969351.exe (PID: 22932)
- 41m98slk.exe (PID: 26152)
- svhostc.exe (PID: 26936)
- Identification.exe (PID: 26252)
- te3tlsre.exe (PID: 27132)
- cnct.exe (PID: 24284)
- Discord.exe (PID: 25936)
- svchost.exe (PID: 17916)
- update.exe (PID: 23596)
- Update.exe (PID: 9648)
- main.exe (PID: 26140)
- 87f3f2.exe (PID: 24816)
- LedgerUpdater.exe (PID: 6984)
- AppLaunch.exe (PID: 26924)
- kfhtksfesek.exe (PID: 27032)
- svchostinter.exe (PID: 11684)
- NoMoreRansom.exe (PID: 20080)
- cudo.exe (PID: 24684)
- Ammyy.exe (PID: 27280)
- dxwebsetup.exe (PID: 12060)
- 3e3ev3.exe (PID: 21240)
- ewrvuh.exe (PID: 26676)
- NVIDIAS.exe (PID: 18352)
- MSBuild.exe (PID: 23016)
- 2v6wf6kn.exe (PID: 23260)
- mountain-pasture.exe (PID: 20012)
- Setup2.exe (PID: 23900)
- crypteda.exe (PID: 12116)
- MSBuild.exe (PID: 17328)
- soft2.exe (PID: 20204)
- clamer.exe (PID: 15036)
- RegAsm.exe (PID: 25808)
- LummaC22222.exe (PID: 27024)
- dw20.exe (PID: 24212)
- v_dolg.exe (PID: 25020)
- lxrv.exe (PID: 13788)
- petya.exe (PID: 27236)
- ednfosi.exe (PID: 24548)
- creal.exe (PID: 15836)
- request.exe (PID: 16912)
- xmbld.exe (PID: 18544)
- visagiftcardgen.exe (PID: 27472)
- InstallerPack_20.1.23770_win64.exe (PID: 23116)
- num.exe (PID: 26736)
- yoyf.exe (PID: 15180)
- khtoawdltrha.exe (PID: 17116)
- ddosziller.exe (PID: 28168)
- PURLOG.exe (PID: 28364)
- sgx4824p.exe (PID: 27956)
- jgesfyhjsefa.exe (PID: 28568)
- ataturk.exe (PID: 28640)
- NOTallowedtocrypt.exe (PID: 28284)
- hhnjqu9y.exe (PID: 10960)
- VidsUsername.exe (PID: 28492)
- scj7cm7v.exe (PID: 24744)
- dw20.exe (PID: 4772)
- dw20.exe (PID: 27864)
- srtware.exe (PID: 27656)
- hjgesadfseawd.exe (PID: 26016)
- XClient_protected.exe (PID: 28740)
Disables trace logs
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 5992)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 4764)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 5544)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 3420)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 6624)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 6096)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 7624)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 7812)
- 4363463463464363463463463.exe (PID: 8176)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 8336)
- 4363463463464363463463463.exe (PID: 8760)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 9572)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 10032)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 10160)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 10868)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 11568)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 11632)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 11796)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 11664)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 11732)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 11640)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 11856)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 12772)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 12868)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 12864)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 13388)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 13536)
- 4363463463464363463463463.exe (PID: 13564)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 13820)
- XClient.exe (PID: 6212)
- svchost.exe (PID: 3124)
- ._cache_System.exe (PID: 4328)
- crss.exe (PID: 16588)
- Tutorial.exe (PID: 19328)
- bildnewl.exe (PID: 19644)
- imagelogger.exe (PID: 19168)
- com%20surrogate.exe (PID: 19216)
- alphaTweaks.exe (PID: 18640)
- bypass.exe (PID: 22756)
- nbothjkd.exe (PID: 15240)
- powershell.exe (PID: 19288)
- wefhrf.exe (PID: 21204)
- fuag.exe (PID: 20992)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- 3e3ev3.exe (PID: 21240)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 6756)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 6588)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 3144)
- 4363463463464363463463463.exe (PID: 6740)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 5568)
- 4363463463464363463463463.exe (PID: 6624)
- 4363463463464363463463463.exe (PID: 3436)
- 4363463463464363463463463.exe (PID: 3288)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 3420)
- 4363463463464363463463463.exe (PID: 3724)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 6672)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 6096)
- 4363463463464363463463463.exe (PID: 4996)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 5992)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 6352)
- 4363463463464363463463463.exe (PID: 5544)
- 4363463463464363463463463.exe (PID: 3696)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 6004)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 6652)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 4516)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 4764)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 7368)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 7624)
- 4363463463464363463463463.exe (PID: 7632)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 7812)
- 4363463463464363463463463.exe (PID: 7728)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 8176)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 8320)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 8596)
- 4363463463464363463463463.exe (PID: 8532)
- 4363463463464363463463463.exe (PID: 8360)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 8336)
- 4363463463464363463463463.exe (PID: 8760)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 9004)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 9488)
- 4363463463464363463463463.exe (PID: 9572)
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 10160)
- 4363463463464363463463463.exe (PID: 10020)
- 4363463463464363463463463.exe (PID: 10032)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 10288)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 10548)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 10572)
- 4363463463464363463463463.exe (PID: 10596)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 10868)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 10880)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 10936)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 11172)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 11796)
- 4363463463464363463463463.exe (PID: 11756)
- 4363463463464363463463463.exe (PID: 11568)
- 4363463463464363463463463.exe (PID: 11632)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 11748)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 11892)
- 4363463463464363463463463.exe (PID: 11664)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 11532)
- 4363463463464363463463463.exe (PID: 11872)
- 4363463463464363463463463.exe (PID: 11780)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 11732)
- 4363463463464363463463463.exe (PID: 11524)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 11620)
- 4363463463464363463463463.exe (PID: 11584)
- 4363463463464363463463463.exe (PID: 11640)
- 4363463463464363463463463.exe (PID: 11848)
- 4363463463464363463463463.exe (PID: 11812)
- 4363463463464363463463463.exe (PID: 11856)
- 4363463463464363463463463.exe (PID: 11596)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 12848)
- 4363463463464363463463463.exe (PID: 12772)
- 4363463463464363463463463.exe (PID: 12868)
- 4363463463464363463463463.exe (PID: 12804)
- 4363463463464363463463463.exe (PID: 12864)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 13388)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 13564)
- 4363463463464363463463463.exe (PID: 13576)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 13720)
- 4363463463464363463463463.exe (PID: 13536)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 13868)
- TPB-1.exe (PID: 15164)
- zts.exe (PID: 1304)
- Synaptics.exe (PID: 776)
- XClient.exe (PID: 6212)
- svchost.exe (PID: 3124)
- ._cache_System.exe (PID: 4328)
- crss.exe (PID: 16588)
- PCclear_Eng_mini.exe (PID: 18764)
- Tutorial.exe (PID: 19328)
- gsprout.exe (PID: 19788)
- bildnewl.exe (PID: 19644)
- imagelogger.exe (PID: 19168)
- com%20surrogate.exe (PID: 19216)
- c1.exe (PID: 7868)
- 22.exe (PID: 20784)
- build_2024-07-27_00-41.exe (PID: 19736)
- alphaTweaks.exe (PID: 18640)
- pjthjsdjgjrtavv.exe (PID: 21648)
- notepad.exe (PID: 22456)
- pyjnkasedf.exe (PID: 20320)
- bypass.exe (PID: 22756)
- nbothjkd.exe (PID: 15240)
- jtkhikadjthsad.exe (PID: 23036)
- powershell.exe (PID: 19288)
- InstallSetup.exe (PID: 24404)
- mshta.exe (PID: 9592)
- univ.exe (PID: 3812)
- wefhrf.exe (PID: 21204)
- fuag.exe (PID: 20992)
- Ammyy.exe (PID: 18188)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- utility-inst.tmp (PID: 25240)
- Indentif.exe (PID: 22944)
- 3e3ev3.exe (PID: 21240)
The sample compiled with czech language support
- 4363463463464363463463463.exe (PID: 9564)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 6672)
- InstallSetup.exe (PID: 24404)
Sends debugging messages
- 4363463463464363463463463.exe (PID: 13876)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 7400)
- 4363463463464363463463463.exe (PID: 4024)
- 4363463463464363463463463.exe (PID: 5992)
- 4363463463464363463463463.exe (PID: 11856)
- 4363463463464363463463463.exe (PID: 11892)
- random.exe (PID: 18152)
- 4363463463464363463463463.exe (PID: 6668)
- 4363463463464363463463463.exe (PID: 5316)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 7776)
- 4363463463464363463463463.exe (PID: 7384)
- 4363463463464363463463463.exe (PID: 13432)
- 4363463463464363463463463.exe (PID: 9636)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 5000)
- 4363463463464363463463463.exe (PID: 11540)
- 4363463463464363463463463.exe (PID: 10316)
- 4363463463464363463463463.exe (PID: 13868)
- 4363463463464363463463463.exe (PID: 2076)
- 4363463463464363463463463.exe (PID: 9572)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 13820)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 13452)
- 4363463463464363463463463.exe (PID: 7652)
- 4363463463464363463463463.exe (PID: 8336)
- 4363463463464363463463463.exe (PID: 8972)
- 4363463463464363463463463.exe (PID: 13160)
- 4363463463464363463463463.exe (PID: 8760)
- 4363463463464363463463463.exe (PID: 12772)
- 4363463463464363463463463.exe (PID: 10968)
- 4363463463464363463463463.exe (PID: 11576)
- 4363463463464363463463463.exe (PID: 6700)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 3640)
- 4363463463464363463463463.exe (PID: 3928)
- 4363463463464363463463463.exe (PID: 11664)
- 4363463463464363463463463.exe (PID: 3532)
- 4363463463464363463463463.exe (PID: 10588)
- 4363463463464363463463463.exe (PID: 11824)
- 4363463463464363463463463.exe (PID: 10580)
- 4363463463464363463463463.exe (PID: 11568)
- 4363463463464363463463463.exe (PID: 9812)
- 4363463463464363463463463.exe (PID: 9844)
- 4363463463464363463463463.exe (PID: 6820)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 11652)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 11920)
- 4363463463464363463463463.exe (PID: 10860)
- 4363463463464363463463463.exe (PID: 11848)
- petya.exe (PID: 27236)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 3988)
- 4363463463464363463463463.exe (PID: 2928)
- 4363463463464363463463463.exe (PID: 6652)
The sample compiled with turkish language support
- 4363463463464363463463463.exe (PID: 13820)
- System.exe (PID: 15344)
- Synaptics.exe (PID: 776)
- 4363463463464363463463463.exe (PID: 7728)
Creates files or folders in the user directory
- testingg.exe (PID: 15116)
- TPB-1.exe (PID: 15164)
- server.exe (PID: 15244)
- baedawdgh.exe (PID: 14984)
- zts.exe (PID: 1304)
- NOTallowedtocrypt.exe (PID: 16236)
- 3544436.exe (PID: 17252)
- CoronaVirus.exe (PID: 16056)
- 123.exe (PID: 19512)
- server.exe (PID: 19312)
- Steam.Upgreyd.exe (PID: 16648)
- nano.exe (PID: 20220)
- Installeraus.exe (PID: 21372)
- RegAsm.exe (PID: 1328)
- 2klz.exe (PID: 20624)
- GLP_installer_900223086_market.exe (PID: 8280)
- 14082024.exe (PID: 15480)
- steel.tmp (PID: 20872)
- imagelogger.exe (PID: 19168)
- NJRat.exe (PID: 18648)
- system32.exe (PID: 19376)
- 22.exe (PID: 20784)
- ovrflw.exe (PID: 21764)
- build_2024-07-27_00-41.exe (PID: 19736)
- Discord.exe (PID: 16680)
- GIFT-INFO.lMG.exe (PID: 22440)
- Amogus.exe (PID: 21716)
- Synaptics.exe (PID: 776)
- pjthjsdjgjrtavv.exe (PID: 21648)
- MSBuild.exe (PID: 24028)
- pyjnkasedf.exe (PID: 20320)
- explorer.exe (PID: 4488)
- PURCHASE%20ORDER%20006-2024%20GIA-AV%20Rev%201_pdf.exe (PID: 22076)
- basx.tmp (PID: 17936)
- anticheat.exe (PID: 1596)
- buildred.exe (PID: 22696)
- nbothjkd.exe (PID: 15240)
- bypass.exe (PID: 22756)
- CleanerV2.exe (PID: 24060)
- PowerShell.exe (PID: 21688)
- Client-built-Playit.exe (PID: 23796)
- svhost.exe (PID: 25652)
- bundle.exe (PID: 23808)
- crypteda.exe (PID: 12116)
- 87f3f2.exe (PID: 24816)
- cudo.exe (PID: 24684)
- jtkhikadjthsad.exe (PID: 23036)
- LedgerUpdater.exe (PID: 6984)
- InstallSetup.exe (PID: 24404)
Create files in a temporary directory
- testingg.exe (PID: 15116)
- server.exe (PID: 15244)
- Synaptics.exe (PID: 776)
- NorthSperm.exe (PID: 15044)
- Server1.exe (PID: 16664)
- av_downloader1.1.exe (PID: 18576)
- Minet.exe (PID: 16568)
- alphaTweaks.exe (PID: 18640)
- onelove.exe (PID: 19108)
- run.exe (PID: 4056)
- NVIDIA.exe (PID: 18480)
- china.exe (PID: 20616)
- test.exe (PID: 20172)
- nthnaedltg.exe (PID: 19976)
- steel.exe (PID: 21416)
- Installeraus.exe (PID: 21372)
- steel.tmp (PID: 20872)
- in.exe (PID: 20460)
- imagelogger.exe (PID: 19168)
- GLP_installer_900223086_market.exe (PID: 8280)
- testme.exe (PID: 7612)
- Microsoft.exe (PID: 21160)
- SrbijaSetupHokej.exe (PID: 21672)
- AsyncClient.exe (PID: 16700)
- Final.exe (PID: 21724)
- basx.exe (PID: 22408)
- SrbijaSetupHokej.tmp (PID: 19040)
- basx.tmp (PID: 17936)
- Discord.exe (PID: 16680)
- 4.exe (PID: 23052)
- kitty.exe (PID: 23488)
- av_downloader1.1.exe (PID: 23440)
- utility-inst.exe (PID: 23696)
- bypass.exe (PID: 22756)
- DeliciousPart.exe (PID: 16240)
- sharpmonoinjector.exe (PID: 21732)
- temp.exe (PID: 18792)
- uhigdbf.exe (PID: 21664)
- hailhydra.exe (PID: 22172)
- utility-inst.tmp (PID: 25240)
- setup8.exe (PID: 24588)
- cnct.exe (PID: 24284)
- build.exe (PID: 17784)
- IT_plan_cifs.exe (PID: 23448)
- svchost.exe (PID: 17916)
- dxwebsetup.exe (PID: 12060)
- armadegon.exe (PID: 17504)
- mountain-pasture.exe (PID: 20012)
- S.S.A_Statement_969351.exe (PID: 22932)
- splwow64.exe (PID: 24872)
- 3e3ev3.exe (PID: 21240)
- clamer.exe (PID: 15036)
- InstallSetup.exe (PID: 24404)
- vcredist_x86.exe (PID: 16888)
- creal.exe (PID: 15836)
- phost.exe (PID: 27776)
- sgx4824p.exe (PID: 27956)
- VidsUsername.exe (PID: 28492)
Creates files in the program directory
- TPB-1.exe (PID: 15164)
- System.exe (PID: 15344)
- Synaptics.exe (PID: 776)
- server.exe (PID: 15244)
- iexplore.exe (PID: 17588)
- CoronaVirus.exe (PID: 16056)
- bildnewl.exe (PID: 19644)
- nano.exe (PID: 20220)
- build_2024-07-27_00-41.exe (PID: 19736)
- pjthjsdjgjrtavv.exe (PID: 21648)
- collinssplashpro32.exe (PID: 21300)
- pyjnkasedf.exe (PID: 20320)
- jtkhikadjthsad.exe (PID: 23036)
- Mswgoudnv.exe (PID: 23916)
- ._cache_blq.exe (PID: 24520)
- Survox.exe (PID: 23068)
- Ammyy.exe (PID: 18188)
- dvdvideomedia2.exe (PID: 23624)
- 2r61ahry.exe (PID: 25632)
- newfile.exe (PID: 18724)
- main.exe (PID: 26140)
- dw20.exe (PID: 24212)
- dw20.exe (PID: 4772)
- dw20.exe (PID: 27864)
The sample compiled with english language support
- 4363463463464363463463463.exe (PID: 9556)
- 4363463463464363463463463.exe (PID: 13888)
- 4363463463464363463463463.exe (PID: 9756)
- 4363463463464363463463463.exe (PID: 5556)
- 4363463463464363463463463.exe (PID: 10916)
- 4363463463464363463463463.exe (PID: 11716)
- 4363463463464363463463463.exe (PID: 6004)
- feb9sxwk.exe (PID: 18348)
- 4363463463464363463463463.exe (PID: 13548)
- 4363463463464363463463463.exe (PID: 10332)
- 4363463463464363463463463.exe (PID: 11604)
- 4363463463464363463463463.exe (PID: 13876)
- Destover.exe (PID: 20588)
- 4363463463464363463463463.exe (PID: 10692)
- 4363463463464363463463463.exe (PID: 13004)
- 4363463463464363463463463.exe (PID: 10880)
- CoronaVirus.exe (PID: 16056)
- 4363463463464363463463463.exe (PID: 5460)
- 4363463463464363463463463.exe (PID: 5740)
- 4363463463464363463463463.exe (PID: 11560)
- 4363463463464363463463463.exe (PID: 11632)
- steel.tmp (PID: 20872)
- Installeraus.exe (PID: 21372)
- Microsoft.exe (PID: 21160)
- 4363463463464363463463463.exe (PID: 10472)
- 4363463463464363463463463.exe (PID: 9488)
- basx.tmp (PID: 17936)
- 4363463463464363463463463.exe (PID: 10848)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 11804)
- 4363463463464363463463463.exe (PID: 1804)
- 4363463463464363463463463.exe (PID: 6752)
- 4363463463464363463463463.exe (PID: 9004)
- hailhydra.exe (PID: 22172)
- 4363463463464363463463463.exe (PID: 13344)
- 4363463463464363463463463.exe (PID: 8612)
- 4363463463464363463463463.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 9476)
- 4363463463464363463463463.exe (PID: 10316)
- 2r61ahry.exe (PID: 25632)
- 4363463463464363463463463.exe (PID: 6820)
- dxwebsetup.exe (PID: 12060)
- 4363463463464363463463463.exe (PID: 8036)
- 4363463463464363463463463.exe (PID: 13684)
- 4363463463464363463463463.exe (PID: 6664)
- 4363463463464363463463463.exe (PID: 12840)
- 4363463463464363463463463.exe (PID: 11552)
- 4363463463464363463463463.exe (PID: 8380)
- 4363463463464363463463463.exe (PID: 10904)
- 4363463463464363463463463.exe (PID: 13720)
Reads Environment values
- svchost.exe (PID: 3124)
- ._cache_System.exe (PID: 4328)
- XClient.exe (PID: 6212)
- TPB-1.exe (PID: 15164)
- Client-built.exe (PID: 15168)
- crss.exe (PID: 16588)
- alphaTweaks.exe (PID: 18640)
- NVIDIA.exe (PID: 18480)
- 2klz.exe (PID: 20624)
- bildnewl.exe (PID: 19644)
- imagelogger.exe (PID: 19168)
- Microsoft.exe (PID: 21160)
- Amogus.exe (PID: 21716)
- sharpmonoinjector.exe (PID: 21732)
- Runtime%20Broker.exe (PID: 21748)
- build_2024-07-27_00-41.exe (PID: 19736)
- bypass.exe (PID: 22756)
- CleanerV2.exe (PID: 24060)
- 22.exe (PID: 20784)
- build.exe (PID: 17784)
- fuag.exe (PID: 20992)
- pjthjsdjgjrtavv.exe (PID: 21648)
- taskhost.exe (PID: 22360)
- NJRAT%20DANGEROUS.exe (PID: 23008)
- setup8.exe (PID: 24588)
- Client-built-Playit.exe (PID: 23796)
- svhost.exe (PID: 25652)
- jhnykawfkth.exe (PID: 18752)
- newfile.exe (PID: 18724)
- 3e3ev3.exe (PID: 21240)
- dw20.exe (PID: 24212)
Reads product name
- TPB-1.exe (PID: 15164)
- Microsoft.exe (PID: 21160)
- build_2024-07-27_00-41.exe (PID: 19736)
- 22.exe (PID: 20784)
- pjthjsdjgjrtavv.exe (PID: 21648)
- setup8.exe (PID: 24588)
- jhnykawfkth.exe (PID: 18752)
- dw20.exe (PID: 24212)
Reads CPU info
- TPB-1.exe (PID: 15164)
- Microsoft.exe (PID: 21160)
- pjthjsdjgjrtavv.exe (PID: 21648)
- setup8.exe (PID: 24588)
- bypass.exe (PID: 22756)
Drops a (possible) Coronavirus decoy
- 4363463463464363463463463.exe (PID: 13888)
- CoronaVirus.exe (PID: 16056)
Application launched itself
- chrome.exe (PID: 16096)
- msedge.exe (PID: 18884)
- msedge.exe (PID: 20832)
- chrome.exe (PID: 25812)
- chrome.exe (PID: 27572)
The sample compiled with chinese language support
- 4363463463464363463463463.exe (PID: 11104)
- 4363463463464363463463463.exe (PID: 5460)
- GLP_installer_900223086_market.exe (PID: 8280)
- 4363463463464363463463463.exe (PID: 6672)
Connects to unusual port
- iexplore.exe (PID: 17588)
The sample compiled with korean language support
- 4363463463464363463463463.exe (PID: 4024)
Drops encrypted JS script (Microsoft Script Encoder)
- sound.exe (PID: 18496)
Drops encrypted VBS script (Microsoft Script Encoder)
- sound.exe (PID: 18496)
- CoronaVirus.exe (PID: 16056)
- gsprout.exe (PID: 19788)
- cvv.exe (PID: 24376)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 15568)
- powershell.exe (PID: 15552)
- powershell.exe (PID: 15536)
- powershell.exe (PID: 1016)
- powershell.exe (PID: 23776)
- powershell.exe (PID: 21928)
Process checks whether UAC notifications are on
- nano.exe (PID: 20220)
- wefhrf.exe (PID: 21204)
- qth5kdee.exe (PID: 21804)
- Survox.exe (PID: 23068)
- v_dolg.exe (PID: 25020)
- hhnjqu9y.exe (PID: 10960)
Reads Internet Explorer settings
- mshta.exe (PID: 9592)
The sample compiled with french language support
- blq.exe (PID: 15400)
The sample compiled with russian language support
- steel.tmp (PID: 20872)
- basx.tmp (PID: 17936)
Creates a software uninstall entry
- steel.tmp (PID: 20872)
- basx.tmp (PID: 17936)
NirSoft software is detected
- AdvancedRun.exe (PID: 22680)
Attempting to connect via WebSocket
- networkmanager.exe (PID: 21756)
Attempting to use instant messaging service
- build_2024-07-27_00-41.exe (PID: 19736)
- pjthjsdjgjrtavv.exe (PID: 21648)
- pyjnkasedf.exe (PID: 20320)
- jtkhikadjthsad.exe (PID: 23036)
Connecting to InterPlanetary File System domains
- 4363463463464363463463463.exe (PID: 11540)
- svchost.exe (PID: 2192)
- 4363463463464363463463463.exe (PID: 11824)
The sample compiled with japanese language support
- qsjxfirefkza.exe (PID: 27212)
- file.exe (PID: 26228)
Changes the display of characters in the console
- cmd.exe (PID: 15908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
859
Monitored processes
702
Malicious processes
236
Suspicious processes
47
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | cmd /c "for /l %j in (1,1,30) do start /b "" C:\users\admin\desktop\4363463463464363463463463.exe" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\ProgramData\Synaptics\Synaptics.exe" InjUpdate | C:\ProgramData\Synaptics\Synaptics.exe | System.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: HIGH Description: Synaptics Pointing Device Driver Version: 1.0.0.4 Modules
| |||||||||||||||
| 1016 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Windows\SysWOW64\Files\crss.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | crss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | cmd /c "for /l %j in (1,1,30) do start /b "" C:\users\admin\desktop\4363463463464363463463463.exe" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1304 | "C:\Windows\System32\Files\zts.exe" | C:\Windows\SysWOW64\Files\zts.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1328 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | GOLD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1512 | "C:\Users\admin\AppData\Roaming\MSIX\meshagent32-group.exe" -fullinstall | C:\Users\admin\AppData\Roaming\MSIX\meshagent32-group.exe | — | Installeraus.exe | |||||||||||
User: admin Integrity Level: HIGH Description: MeshCentral Background Service Agent Version: 2022-Dec-2 11:42:16-0800 Modules
| |||||||||||||||
| 1596 | "C:\Windows\System32\Files\anticheat.exe" | C:\Windows\SysWOW64\Files\anticheat.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: XHP Version: 12.9.1.22 Modules
| |||||||||||||||
| 1804 | C:\users\admin\desktop\4363463463464363463463463.exe | C:\Users\admin\Desktop\4363463463464363463463463.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 2076 | C:\users\admin\desktop\4363463463464363463463463.exe | C:\Users\admin\Desktop\4363463463464363463463463.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
424 436
Read events
422 811
Write events
1 526
Delete events
99
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000007034E |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010013000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C000000130000000000000061006C0072006500610064007900730068006F0077002E0070006E0067003E00200020000000170000000000000062006C007500650061007000700072006F007000720069006100740065002E007200740066003E002000200000001200000000000000630075006D006D006500740068006F00640073002E006A00700067003E002000200000001400000000000000640061007600690064006D00650064006900630061006C002E007200740066003E00200020000000160000000000000066006F006F007400620061006C006C006D0065006400690075006D002E007200740066003E0020002000000012000000000000006F0066006600690063006500610072006D0079002E007200740066003E002000200000001000000000000000730074006500700074006F006F006B002E0070006E0067003E002000200000001300000000000000730074006F00720069006500730074006800610074002E007200740066003E00200020000000110000000000000075006E006C006500730073007000730074002E007200740066003E0020002000000015000000000000007A0064006900730074007200690062007500740069006F006E002E006A00700067003E00200020000000210000000000000034003300360033003400360033003400360033003400360034003300360033003400360033003400360033003400360033002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001300000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A0401100000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000004040000000001200 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: D096706700000000 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000007034E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 50667 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | IndexedLanguage |
Value: en-US | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\AppIndexer |
| Operation: | write | Name: | LatestCacheFileName |
Value: 410070007000430061006300680065003100330033003700390039003000350034003800350032003200300032003200330031002E0074007800740000007971A9148859DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\AppIndexer |
| Operation: | write | Name: | InstalledWin32AppsRevision |
Value: 7B00420037004100440036003000440037002D0030004400310042002D0034003000410034002D0039003200390035002D003300380034004400360044003800330030003000300044007D0000007971A9148859DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
Executable files
469
Suspicious files
2 148
Text files
472
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\Internet Explorer\DOMStore\ZWUI0EBX\www.bing[1].xml | text | |
MD5:DA8E036C56B9550048F91E451F11BDD3 | SHA256:C3A27E8AD2F3B1202CB11D282ED6FB2AA28A53506193F433C449AEC54904ACE7 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\hCdM5V3UaZXhX_wN6FhxhcULfoU[1].js | binary | |
MD5:974B999F9F10DCF784EE257E2AA2F953 | SHA256:5A0F2478D335D70CD2510F8EF00BFC0CA2057B787302771EBD411970F1C0ED44 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\95d9a2a97a42f02325559b453ba7f8fe839baa18.tbres | binary | |
MD5:4A0ABA2B5230A3E5895B45356E7807E4 | SHA256:46FD5ECC36B0BC32343296EA85D518860EEE9FCD6DEFDB7BEF9AD70DF6909873 | |||
| 4488 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{40f5e756-3b6f-4df7-a021-b27790f271a0}\0.1.filtertrie.intermediate.txt | text | |
MD5:34BD1DFB9F72CF4F86E6DF6DA0A9E49A | SHA256:8E1E6A3D56796A245D0C7B0849548932FEE803BBDB03F6E289495830E017F14C | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\QNBBNqWD9F_Blep-UqQSqnMp-FI[1].css | text | |
MD5:77373397A17BD1987DFCA2E68D022ECF | SHA256:A319AF2E953E7AFDA681B85A62F629A5C37344AF47D2FCD23AB45E1D99497F13 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:2F4DE30E1B37B2AA0B5E2731C2F2FCBF | SHA256:B538BA86881493A80B9A6EDC50C74EB31830663E3ED35BDFC7086749F6510492 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\I6nommjaUrH5K7RnL_cFpH5R7jM[1].css | text | |
MD5:C1AC4CCA38EA836717738D7CF72B45B9 | SHA256:E4C0BF089E674482FA2FE7D558F64F9D3EBDD414EAED18908E34A6140D09B727 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\dg0bEoz0nxScOpJJ_JI0IxFBuTs[1].css | text | |
MD5:071CD9CDFB86B42F65CCD66A7413EAC1 | SHA256:C1D6F71AF2376013D3B3FC25DB91CC9DA8D961084641312CCB96B3045AD921D5 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\FgBbpIj0thGWZOh_xFnM9i4O7ek[1].css | text | |
MD5:908111EB0FFB1360D5DD61279C21703E | SHA256:1ED87CF425DED994B05A842271AB4D28A76F399E571688CF2E7B186F70DC3059 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
433
TCP/UDP connections
1 627
DNS requests
321
Threats
1 300
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
736 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
736 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
13868 | 4363463463464363463463463.exe | GET | — | 150.158.37.254:9529 | http://150.158.37.254:9529/02.08.2022.exe | unknown | — | — | unknown |
9812 | 4363463463464363463463463.exe | GET | 301 | 140.82.121.3:80 | http://github.com/LuisPhantom/Vemom/raw/refs/heads/main/Client-built.exe | unknown | — | — | shared |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
736 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 184.86.251.22:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
736 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
r.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
t-ring-s2.msedge.net |
| unknown |
urlhaus.abuse.ch |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
13876 | 4363463463464363463463463.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
13876 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
13876 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
9636 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
13876 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
13876 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
13876 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
9636 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
9636 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
122 ETPRO signatures available at the full report
Process | Message |
|---|---|
4363463463464363463463463.exe | An exception occurred during a WebClient request.
|
4363463463464363463463463.exe | An exception occurred during a WebClient request.
|
4363463463464363463463463.exe | An exception occurred during a WebClient request.
|
4363463463464363463463463.exe | An exception occurred during a WebClient request.
|
4363463463464363463463463.exe | An exception occurred during a WebClient request.
|
4363463463464363463463463.exe | An exception occurred during a WebClient request.
|
4363463463464363463463463.exe | An exception occurred during a WebClient request.
|
random.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
4363463463464363463463463.exe | The remote server returned an error: (403) Forbidden.
|
4363463463464363463463463.exe | The remote server returned an error: (403) Forbidden.
|