| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/0cb75ce3-18a9-49fb-afb5-adc57982e293 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 17, 2025, 22:36:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
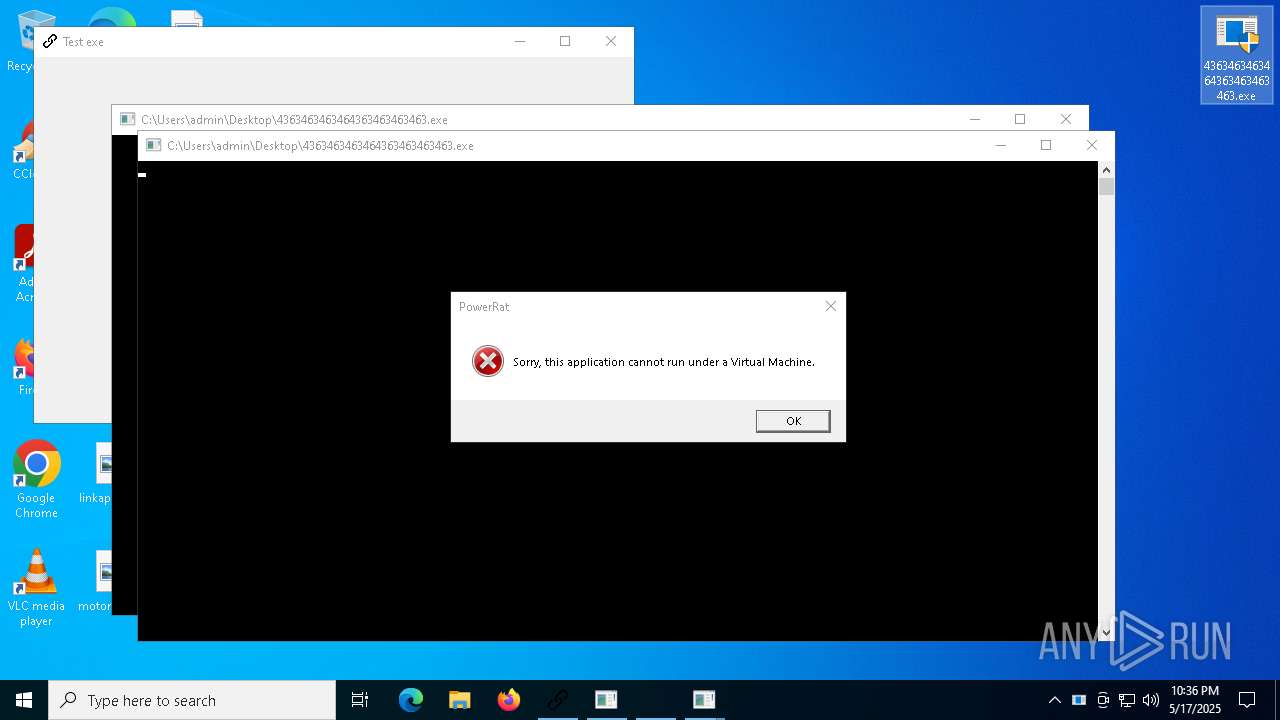
QUASARRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 1760)
- CleanerV2.exe (PID: 1532)
- 4363463463464363463463463.exe (PID: 7568)
- Client-built.exe (PID: 11572)
- WenzCord.exe (PID: 11360)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 8788)
- Java.exe (PID: 14672)
- spectrum.exe (PID: 13236)
- 4363463463464363463463463.exe (PID: 10800)
- 4363463463464363463463463.exe (PID: 9348)
Uses Task Scheduler to autorun other applications
- CleanerV2.exe (PID: 1532)
- Client.exe (PID: 5064)
- Client-built.exe (PID: 11572)
- WenzCord.exe (PID: 11360)
- spectrum.exe (PID: 13236)
- Java.exe (PID: 14672)
- Client-built10.exe (PID: 10700)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 1348)
GENERIC has been found (auto)
- update.exe (PID: 1280)
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 9900)
- 4363463463464363463463463.exe (PID: 8800)
- bot.exe (PID: 11924)
- 4363463463464363463463463.exe (PID: 8124)
- javaplatform.exe (PID: 672)
- 4363463463464363463463463.exe (PID: 11000)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 10088)
- javasupportw.exe (PID: 16644)
- 4363463463464363463463463.exe (PID: 10088)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5124)
- MSBuild.exe (PID: 14960)
- alex12312.exe (PID: 11872)
- MSBuild.exe (PID: 16168)
Connects to the CnC server
- svchost.exe (PID: 2196)
STEALER has been found (auto)
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 10416)
ASYNCRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 8892)
- 4363463463464363463463463.exe (PID: 1760)
- svchost.exe (PID: 8940)
- 4363463463464363463463463.exe (PID: 13000)
- 4363463463464363463463463.exe (PID: 728)
Stealers network behavior
- svchost.exe (PID: 2196)
- aspnet_compiler.exe (PID: 9460)
NJRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 8896)
- 4363463463464363463463463.exe (PID: 8800)
- njSilent.exe (PID: 12344)
- Server.exe (PID: 13156)
- 4363463463464363463463463.exe (PID: 13260)
- svchost.exe (PID: 13468)
- Device2.exe (PID: 9748)
- 4363463463464363463463463.exe (PID: 8748)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 10984)
- 4363463463464363463463463.exe (PID: 15068)
Run PowerShell with an invisible window
- powershell.exe (PID: 10796)
- powershell.exe (PID: 18444)
Changes powershell execution policy
- wscript.exe (PID: 10804)
- powershell.exe (PID: 10796)
Uses Task Scheduler to run other applications
- MSystem32.exe (PID: 10772)
- savedecrypter.exe (PID: 11956)
XWORM has been detected
- svchost.exe (PID: 8940)
Changes powershell execution policy (Bypass)
- XClient.exe (PID: 11480)
METERPRETER has been found (auto)
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 7320)
Adds path to the Windows Defender exclusion list
- XClient.exe (PID: 11480)
- cheese.exe (PID: 13388)
- Vikings.exe (PID: 14708)
Bypass execution policy to execute commands
- powershell.exe (PID: 14012)
Changes Windows Defender settings
- XClient.exe (PID: 11480)
- cheese.exe (PID: 13388)
Executing a file with an untrusted certificate
- inferno.exe (PID: 14264)
- jokererer.exe (PID: 16964)
- LukeJazz.exe (PID: 20080)
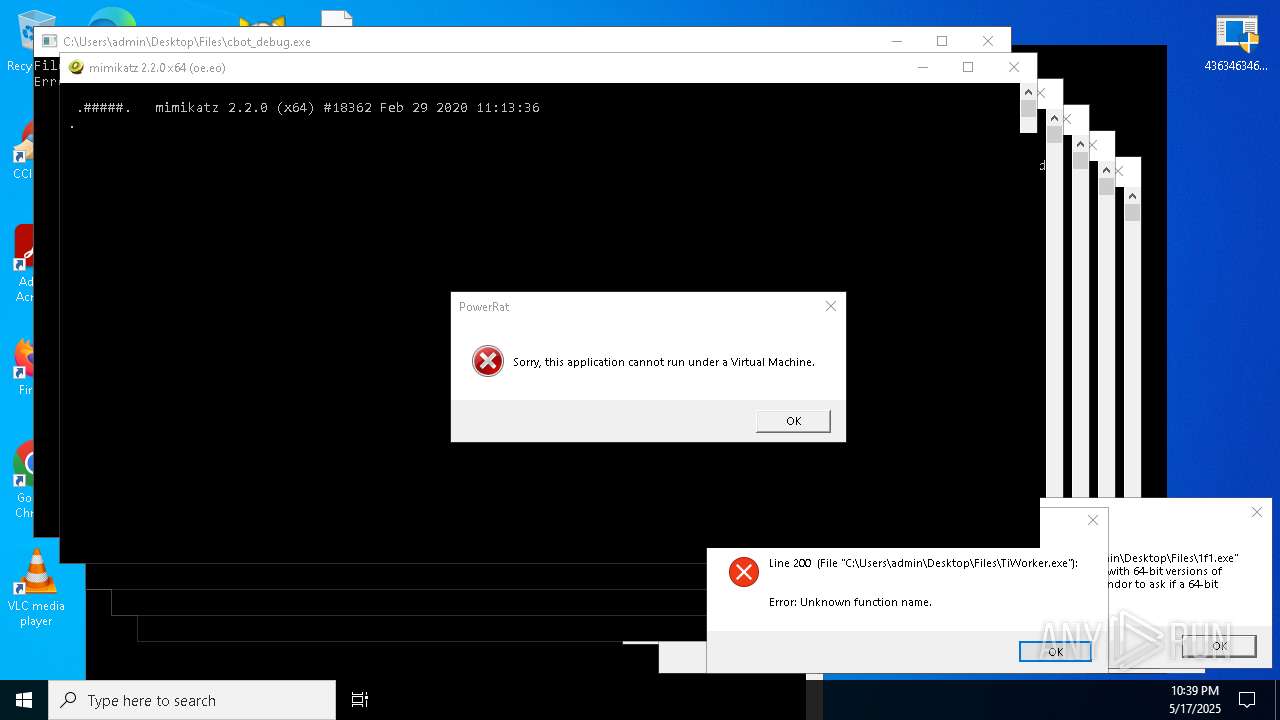
STORMKITTY has been detected (YARA)
- MSBuild.exe (PID: 2096)
DISCORDGRABBER has been detected (YARA)
- MSBuild.exe (PID: 2096)
QUASAR has been detected (YARA)
- Client.exe (PID: 5064)
AGENTTESLA has been detected (SURICATA)
- aspnet_compiler.exe (PID: 9460)
RAT has been found (auto)
- 4363463463464363463463463.exe (PID: 10416)
- 4363463463464363463463463.exe (PID: 7320)
METERPRETER has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 13260)
REMCOS has been found (auto)
- 4363463463464363463463463.exe (PID: 8124)
STEGOCAMPAIGN has been detected
- powershell.exe (PID: 18444)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
SMBSCAN has been detected (SURICATA)
- billi_e58d74e455634dc695ed8a7b8b320325.exe.dom_1.exe (PID: 13824)
SUSPICIOUS
Process drops legitimate windows executable
- 4363463463464363463463463.exe (PID: 1760)
- update.exe (PID: 1280)
- ytxgppknsh.exe (PID: 7476)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 8800)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 14308)
- 4363463463464363463463463.exe (PID: 14500)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 7224)
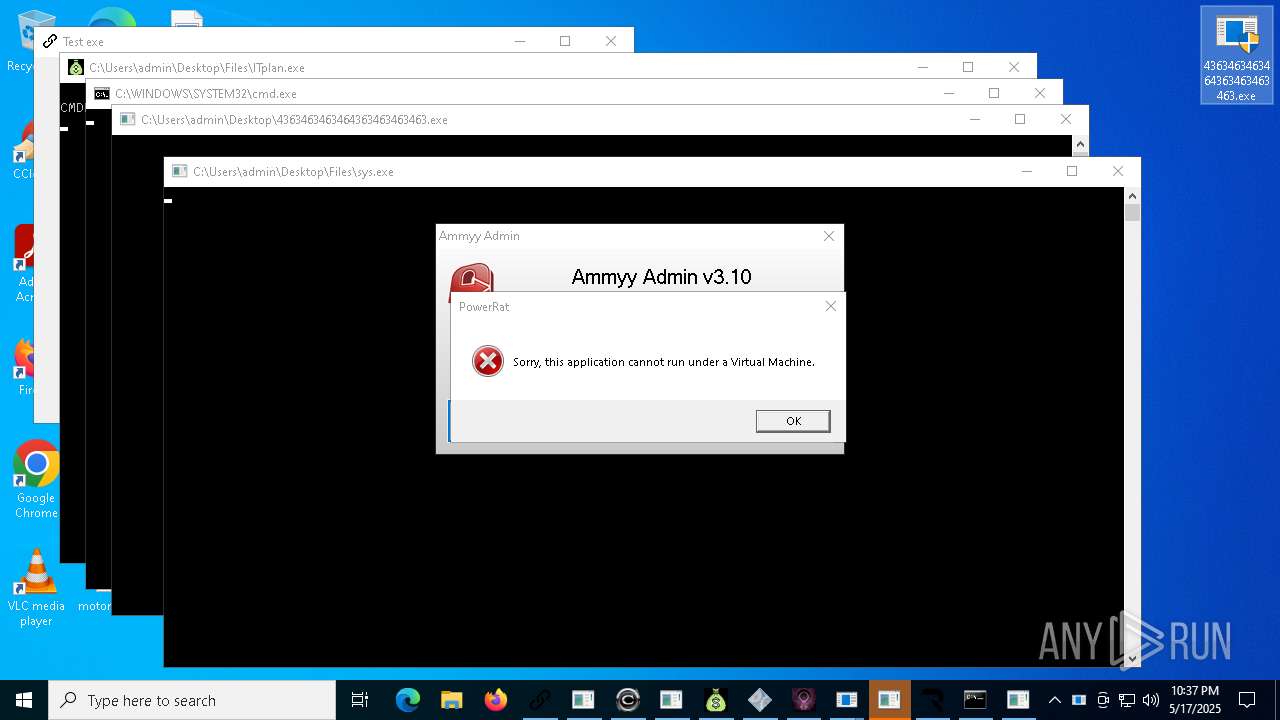
Starts a Microsoft application from unusual location
- cron1.exe (PID: 4488)
- ytxgppknsh.exe (PID: 7476)
- Lead.Upload.Report.Feb.2025.exe (PID: 8816)
- inferno.exe (PID: 14264)
- cro2.exe (PID: 14928)
- Serials_Checker.exe (PID: 14056)
- cr2.exe (PID: 16724)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 1760)
- Client.exe (PID: 5064)
- update.exe (PID: 1280)
- vmduyldboa.exe (PID: 6676)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 6148)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 8072)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 8628)
- 4363463463464363463463463.exe (PID: 8896)
- 4363463463464363463463463.exe (PID: 8892)
- 4363463463464363463463463.exe (PID: 7412)
- update.exe (PID: 7564)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 9900)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 10436)
- 4363463463464363463463463.exe (PID: 10088)
- 4363463463464363463463463.exe (PID: 10984)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 8740)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 10416)
- 4363463463464363463463463.exe (PID: 11432)
- 4363463463464363463463463.exe (PID: 7792)
- 4363463463464363463463463.exe (PID: 10800)
- 4363463463464363463463463.exe (PID: 12216)
- 4363463463464363463463463.exe (PID: 7500)
- 4363463463464363463463463.exe (PID: 13768)
- 4363463463464363463463463.exe (PID: 13396)
- 4363463463464363463463463.exe (PID: 15068)
- 4363463463464363463463463.exe (PID: 11784)
- 4363463463464363463463463.exe (PID: 14992)
- 4363463463464363463463463.exe (PID: 16132)
- 4363463463464363463463463.exe (PID: 13000)
- 4363463463464363463463463.exe (PID: 13804)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 968)
- 4363463463464363463463463.exe (PID: 8800)
- 4363463463464363463463463.exe (PID: 15960)
- 4363463463464363463463463.exe (PID: 9348)
- 4363463463464363463463463.exe (PID: 14500)
- 4363463463464363463463463.exe (PID: 11000)
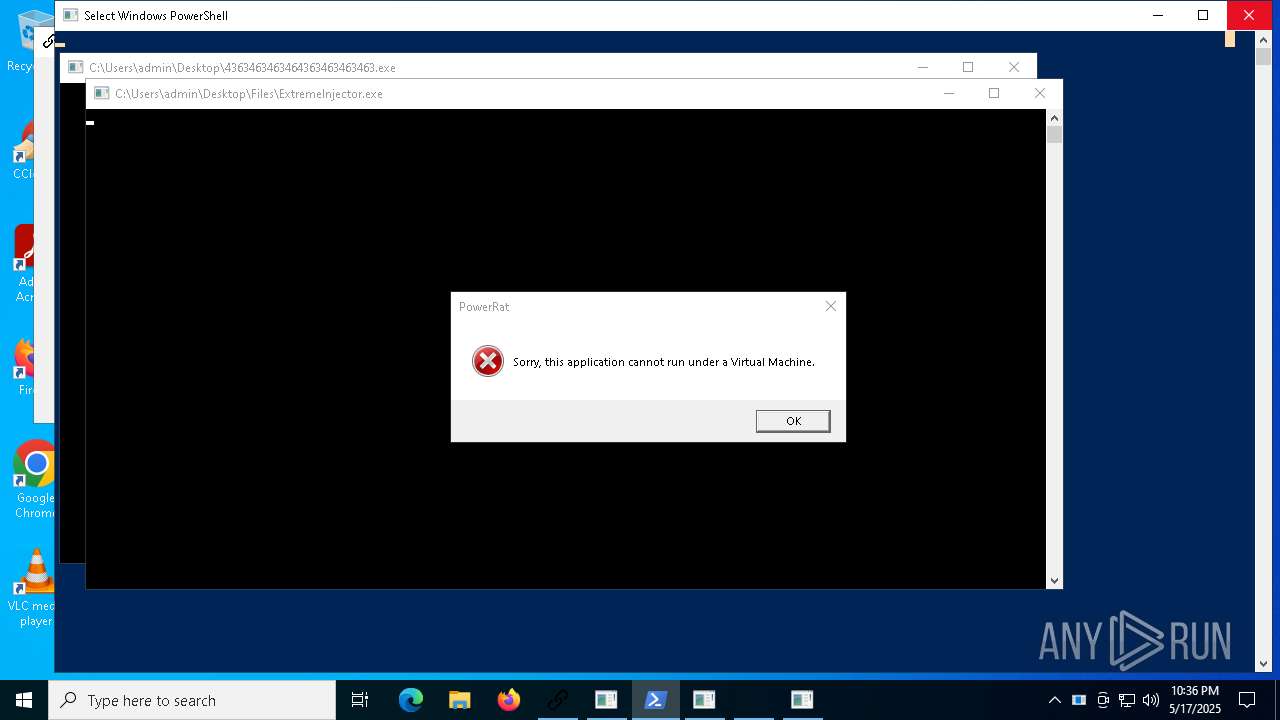
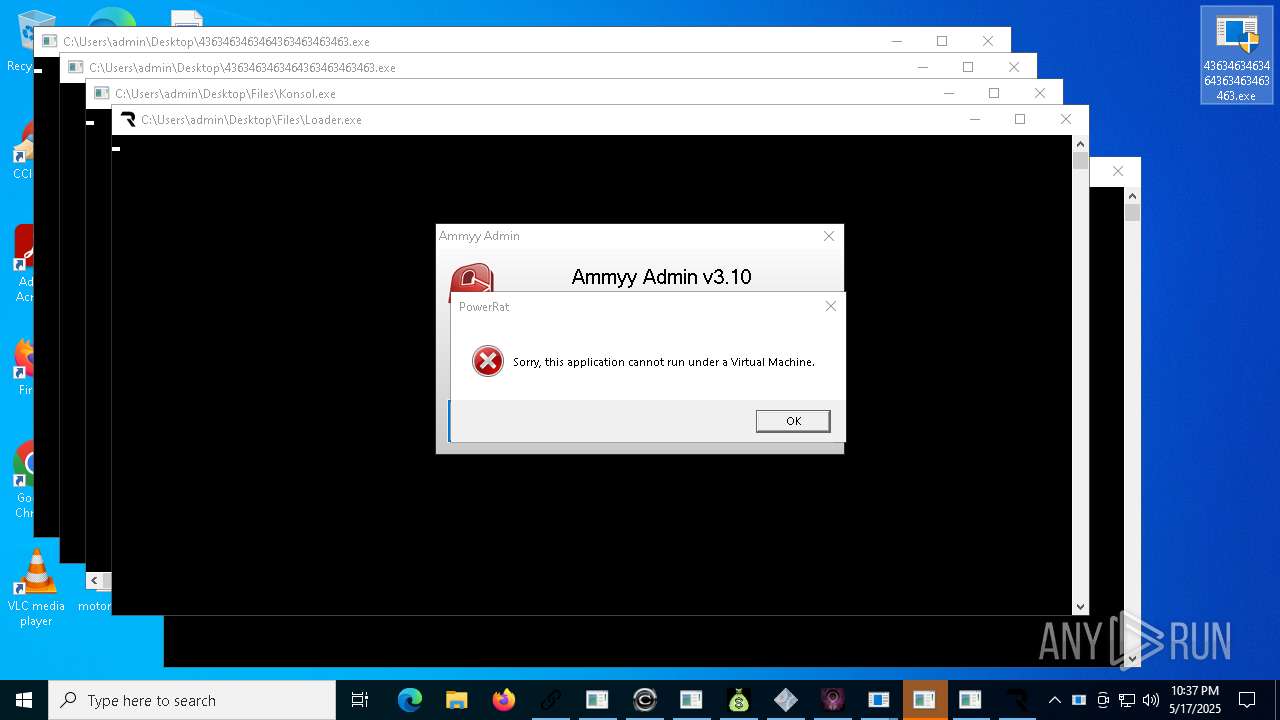
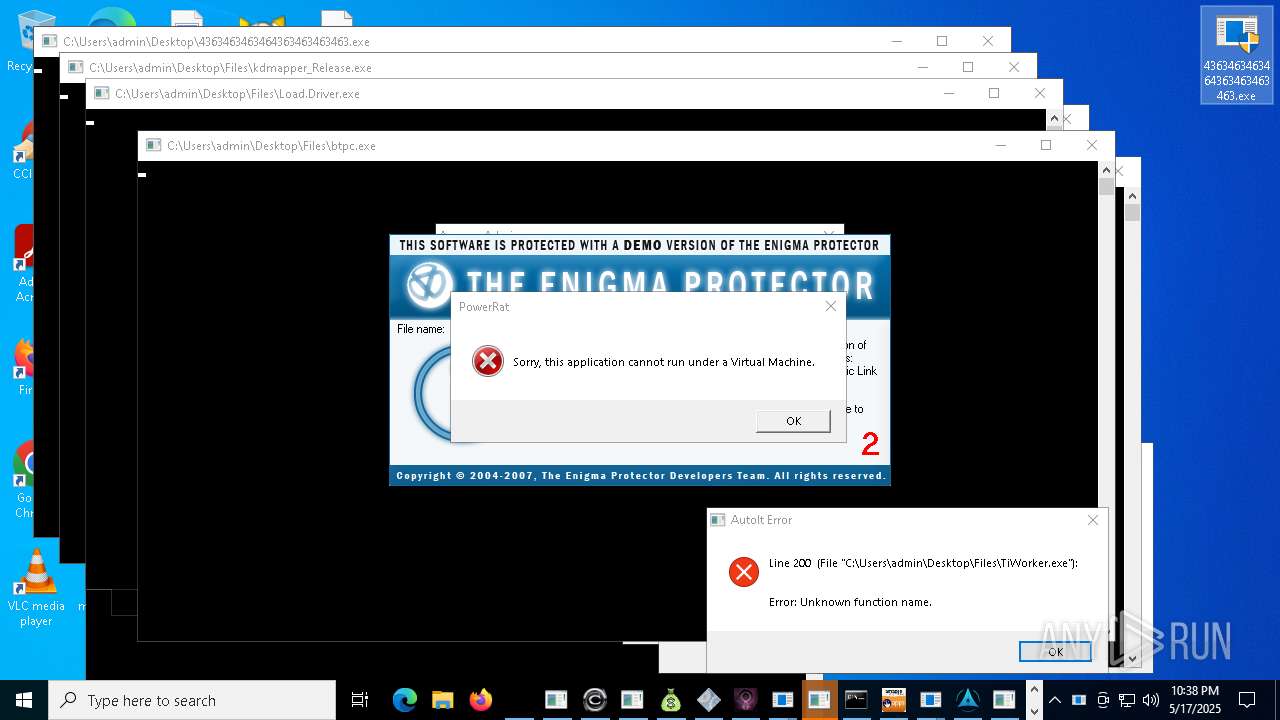
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 1760)
- CleanerV2.exe (PID: 1532)
- update.exe (PID: 1280)
- ytxgppknsh.exe (PID: 7476)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7792)
- 4363463463464363463463463.exe (PID: 8072)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 8748)
- 4363463463464363463463463.exe (PID: 8896)
- 4363463463464363463463463.exe (PID: 8892)
- 4363463463464363463463463.exe (PID: 8788)
- 4363463463464363463463463.exe (PID: 8800)
- ExtremeInjector.exe (PID: 10956)
- 4363463463464363463463463.exe (PID: 7568)
- 4363463463464363463463463.exe (PID: 7412)
- MSystem32.exe (PID: 10772)
- savedecrypter.exe (PID: 11956)
- 4363463463464363463463463.exe (PID: 1628)
- update.exe (PID: 7564)
- svchost.exe (PID: 8940)
- 4363463463464363463463463.exe (PID: 10200)
- WindowsServices.exe (PID: 9496)
- Client-built.exe (PID: 11572)
- 4363463463464363463463463.exe (PID: 10416)
- 4363463463464363463463463.exe (PID: 10088)
- WenzCord.exe (PID: 11360)
- 4363463463464363463463463.exe (PID: 10984)
- 4363463463464363463463463.exe (PID: 7928)
- njSilent.exe (PID: 12344)
- bot.exe (PID: 11924)
- Server.exe (PID: 13156)
- 4363463463464363463463463.exe (PID: 1348)
- rah.exe (PID: 14056)
- 4363463463464363463463463.exe (PID: 8740)
- 4363463463464363463463463.exe (PID: 11432)
- 4363463463464363463463463.exe (PID: 13260)
- 4363463463464363463463463.exe (PID: 8628)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 9348)
- javaplatform.exe (PID: 672)
- Java.exe (PID: 14672)
- 4363463463464363463463463.exe (PID: 11000)
- svchost.exe (PID: 13468)
- 4363463463464363463463463.exe (PID: 7500)
- spectrum.exe (PID: 13236)
- 4363463463464363463463463.exe (PID: 10220)
- Device2.exe (PID: 9748)
- 4363463463464363463463463.exe (PID: 10800)
- 4363463463464363463463463.exe (PID: 13000)
- 4363463463464363463463463.exe (PID: 13768)
- javasupportw.exe (PID: 16644)
- 4363463463464363463463463.exe (PID: 9908)
- 4363463463464363463463463.exe (PID: 14308)
- Client-built10.exe (PID: 10700)
- IMG001.exe (PID: 16756)
- 4363463463464363463463463.exe (PID: 14916)
- 4363463463464363463463463.exe (PID: 13804)
- WindowsServices.exe (PID: 13304)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 968)
- 4363463463464363463463463.exe (PID: 14992)
- giftorder.exe (PID: 18528)
- 4363463463464363463463463.exe (PID: 11784)
- 4363463463464363463463463.exe (PID: 15068)
- 4363463463464363463463463.exe (PID: 16132)
- 4363463463464363463463463.exe (PID: 10728)
- PowerShell.exe (PID: 18392)
- 4363463463464363463463463.exe (PID: 7224)
- 4363463463464363463463463.exe (PID: 9472)
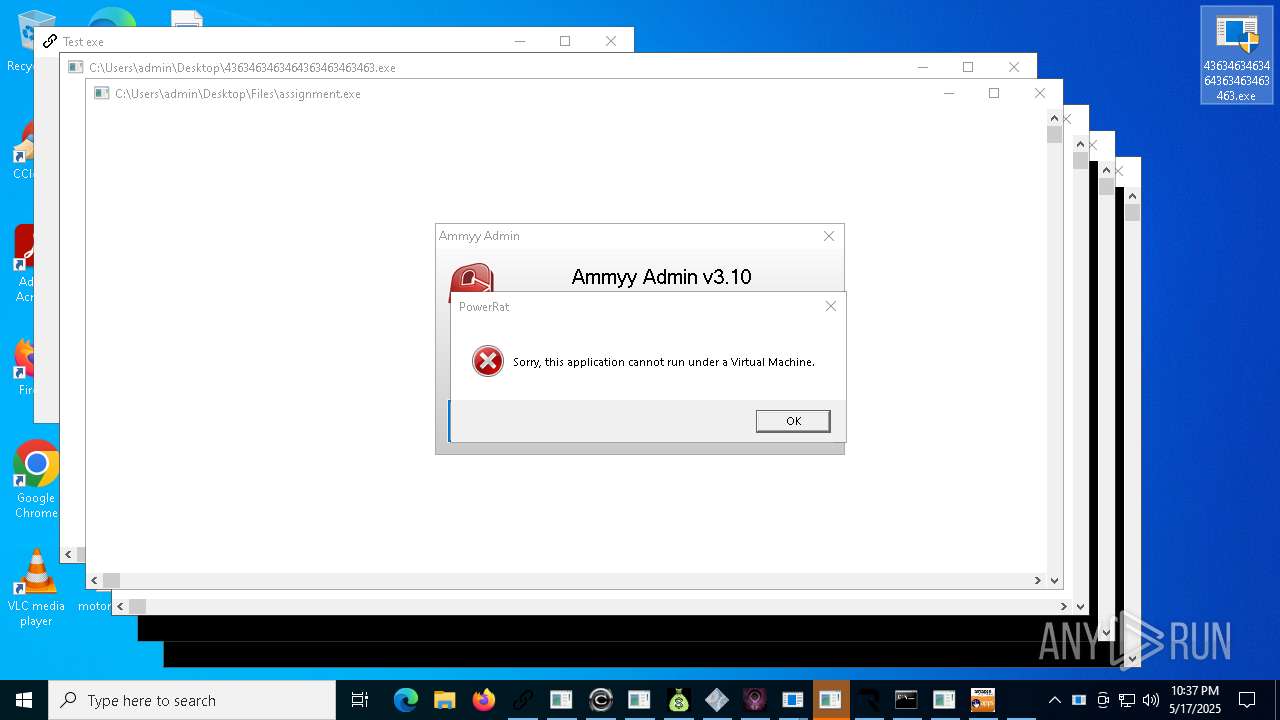
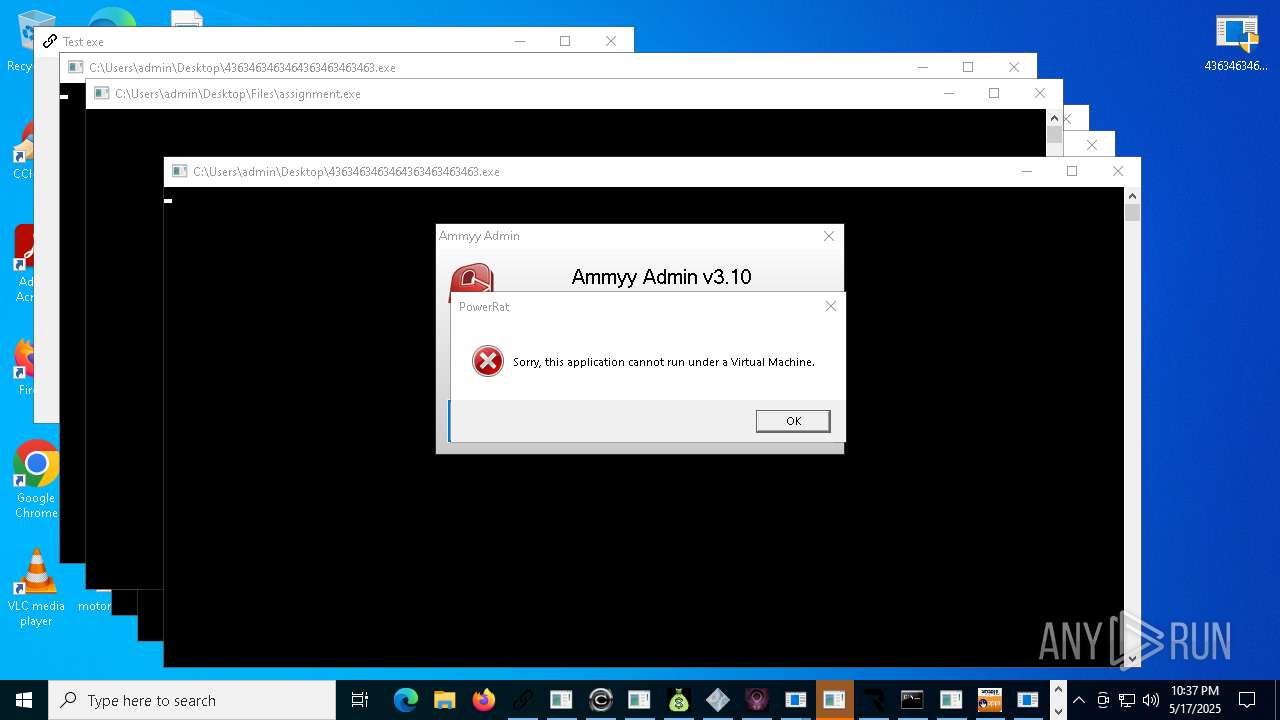
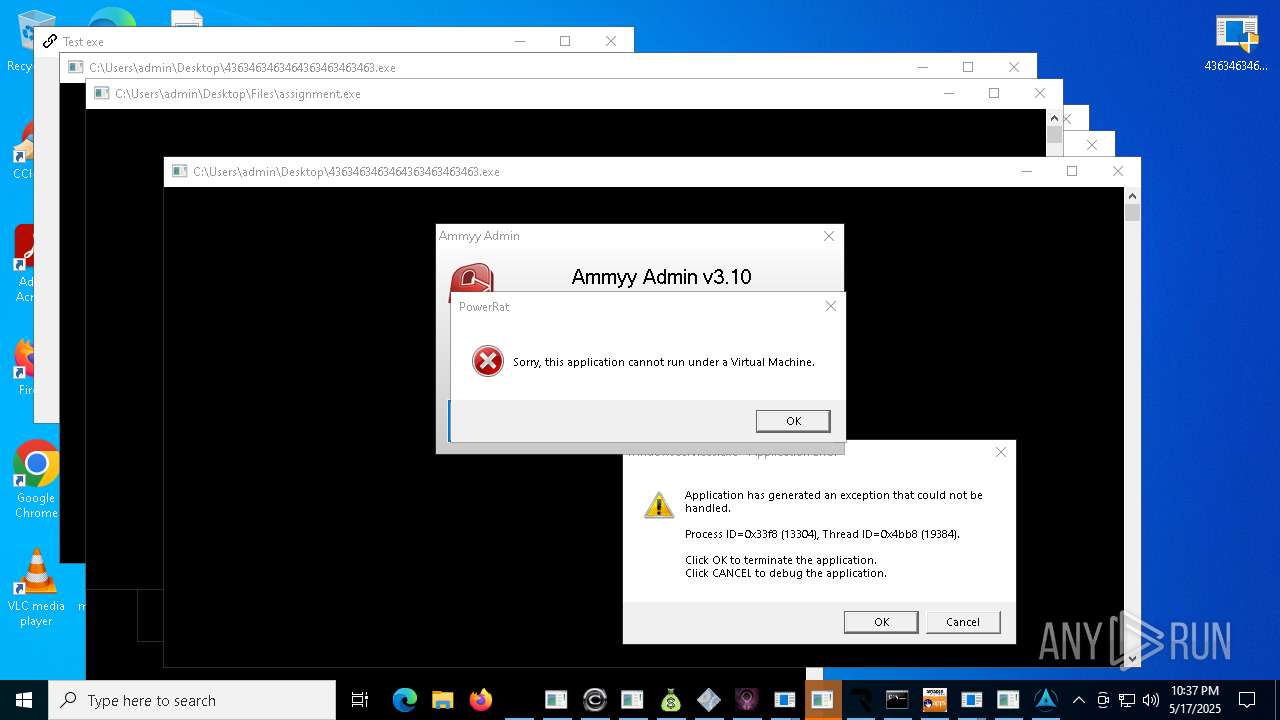
- assignment.exe (PID: 19020)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 7412)
- update.exe (PID: 7564)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 8740)
- 4363463463464363463463463.exe (PID: 10416)
- 4363463463464363463463463.exe (PID: 13768)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 11784)
- 4363463463464363463463463.exe (PID: 14992)
- 4363463463464363463463463.exe (PID: 13000)
- 4363463463464363463463463.exe (PID: 968)
- 4363463463464363463463463.exe (PID: 9348)
- 4363463463464363463463463.exe (PID: 11000)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 8740)
- 4363463463464363463463463.exe (PID: 10088)
- update.exe (PID: 7564)
- 4363463463464363463463463.exe (PID: 9900)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 8072)
- 4363463463464363463463463.exe (PID: 10984)
- 4363463463464363463463463.exe (PID: 11784)
- 4363463463464363463463463.exe (PID: 10416)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 11000)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 14500)
- 4363463463464363463463463.exe (PID: 10800)
- 4363463463464363463463463.exe (PID: 9348)
- 4363463463464363463463463.exe (PID: 8800)
- 4363463463464363463463463.exe (PID: 13000)
- 4363463463464363463463463.exe (PID: 15960)
- 4363463463464363463463463.exe (PID: 13768)
- 4363463463464363463463463.exe (PID: 968)
- 4363463463464363463463463.exe (PID: 14992)
- billi_e58d74e455634dc695ed8a7b8b320325.exe.dom_1.exe (PID: 13824)
Starts itself from another location
- CleanerV2.exe (PID: 1532)
- WindowsServices.exe (PID: 9496)
- bot.exe (PID: 11924)
- njSilent.exe (PID: 12344)
- rah.exe (PID: 14056)
- Server.exe (PID: 13156)
- javaplatform.exe (PID: 672)
- javasupportw.exe (PID: 16644)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5124)
- MSBuild.exe (PID: 14960)
- alex12312.exe (PID: 11872)
- MSBuild.exe (PID: 16168)
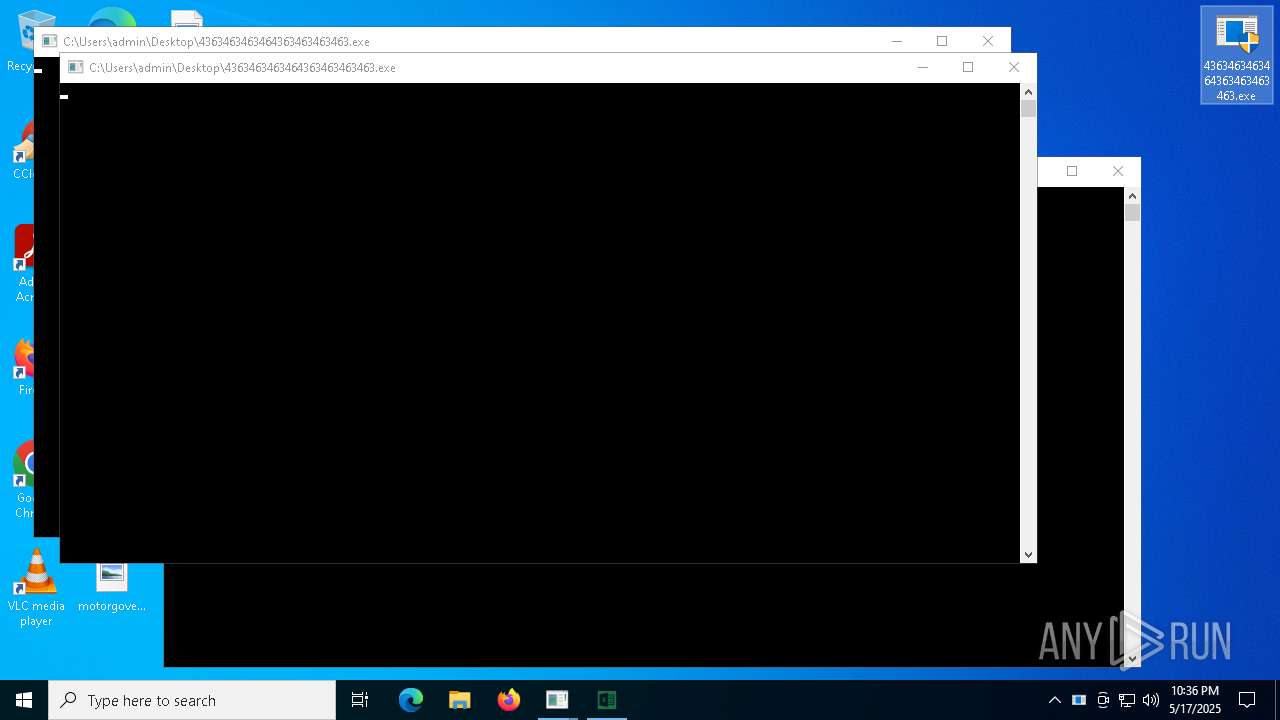
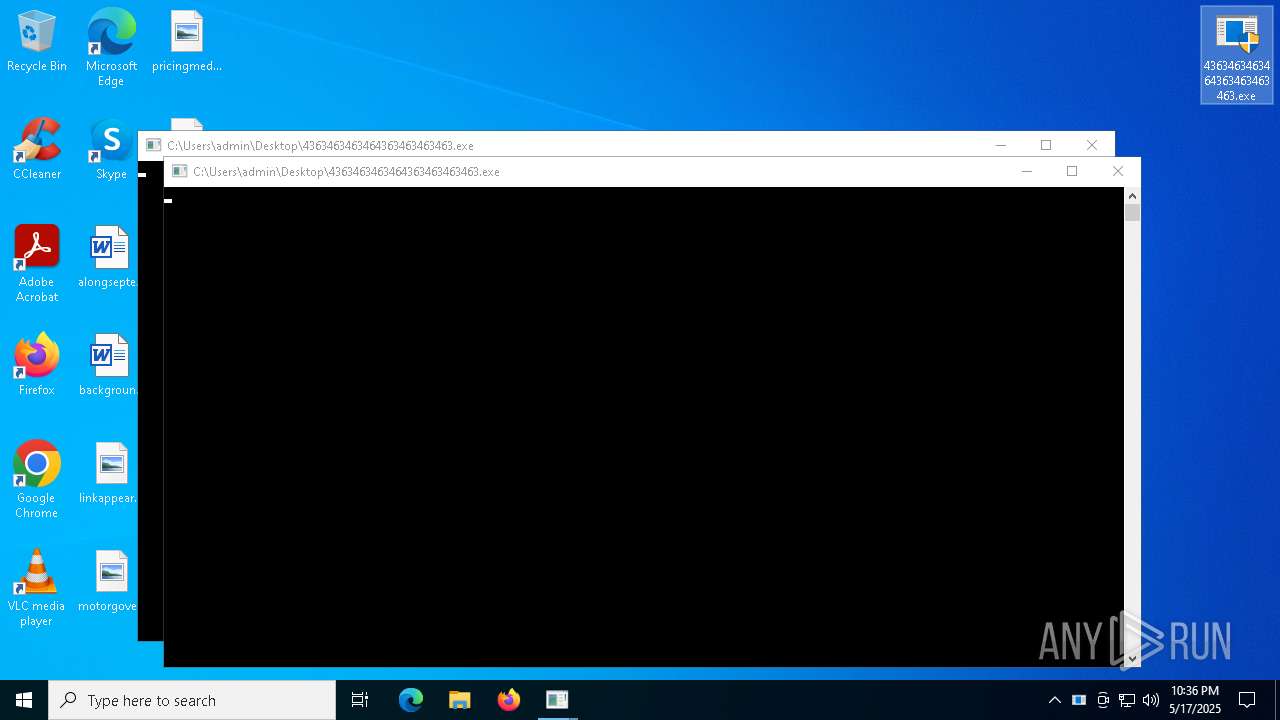
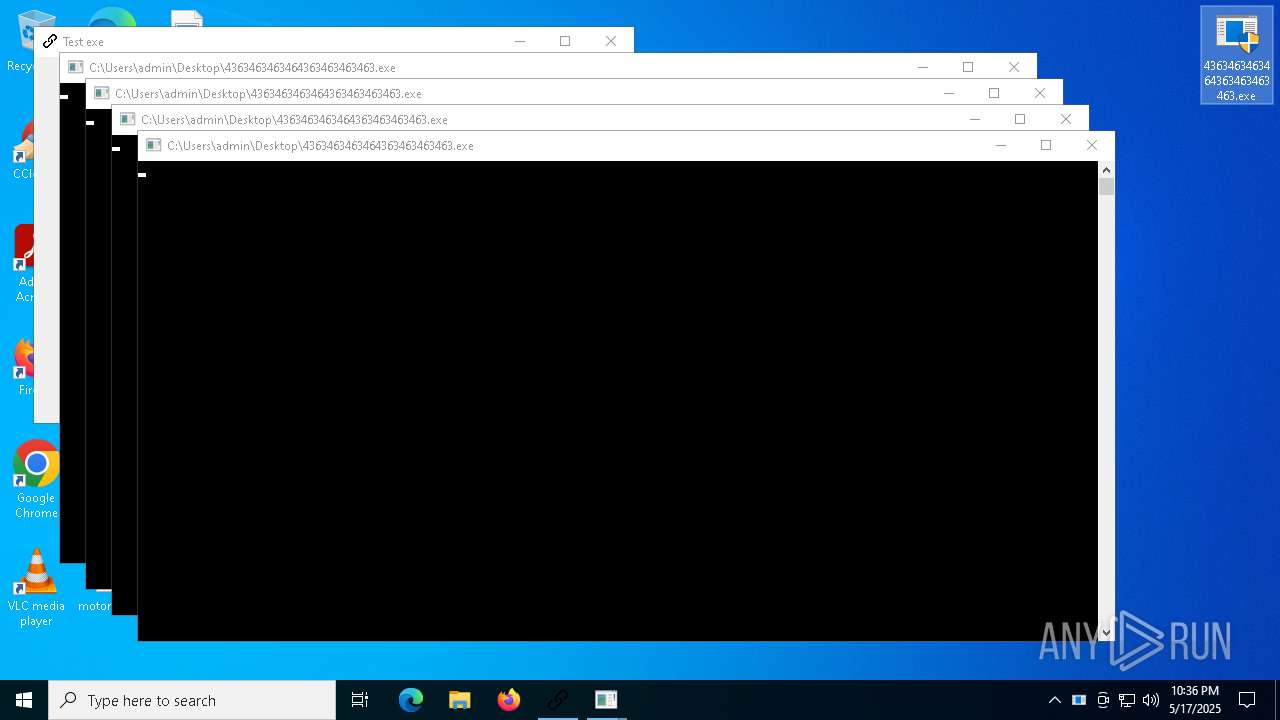
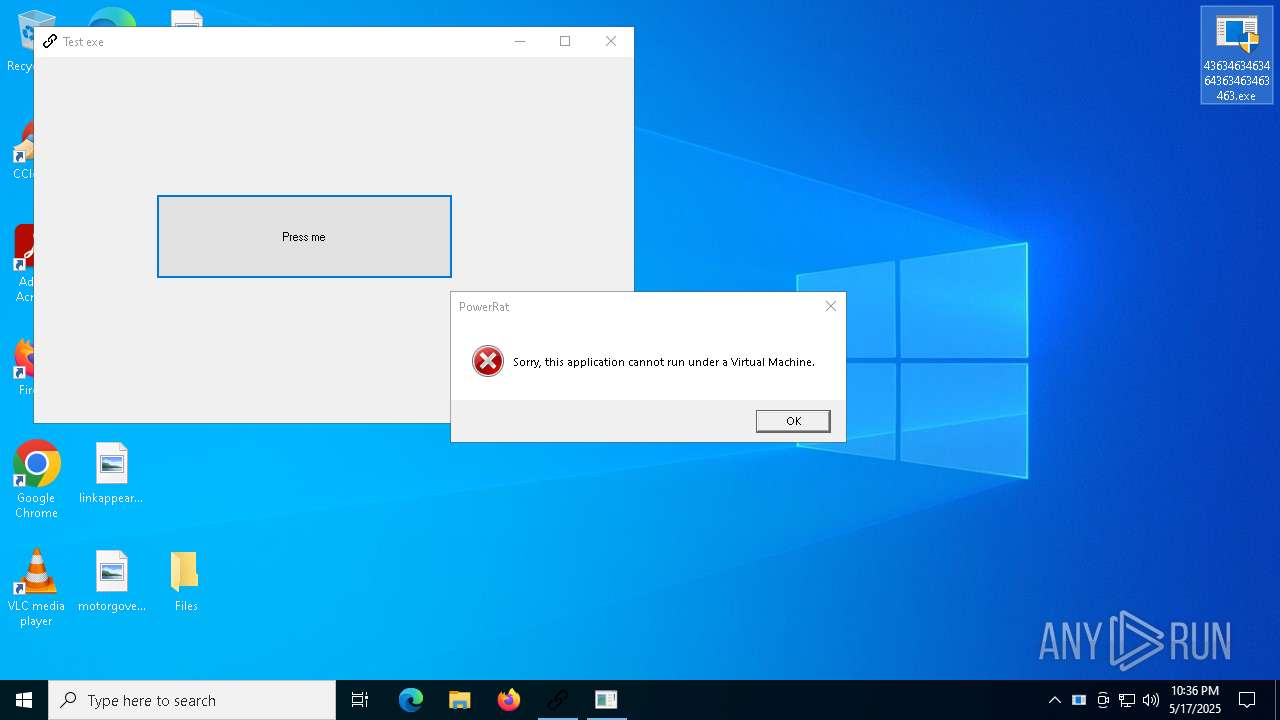
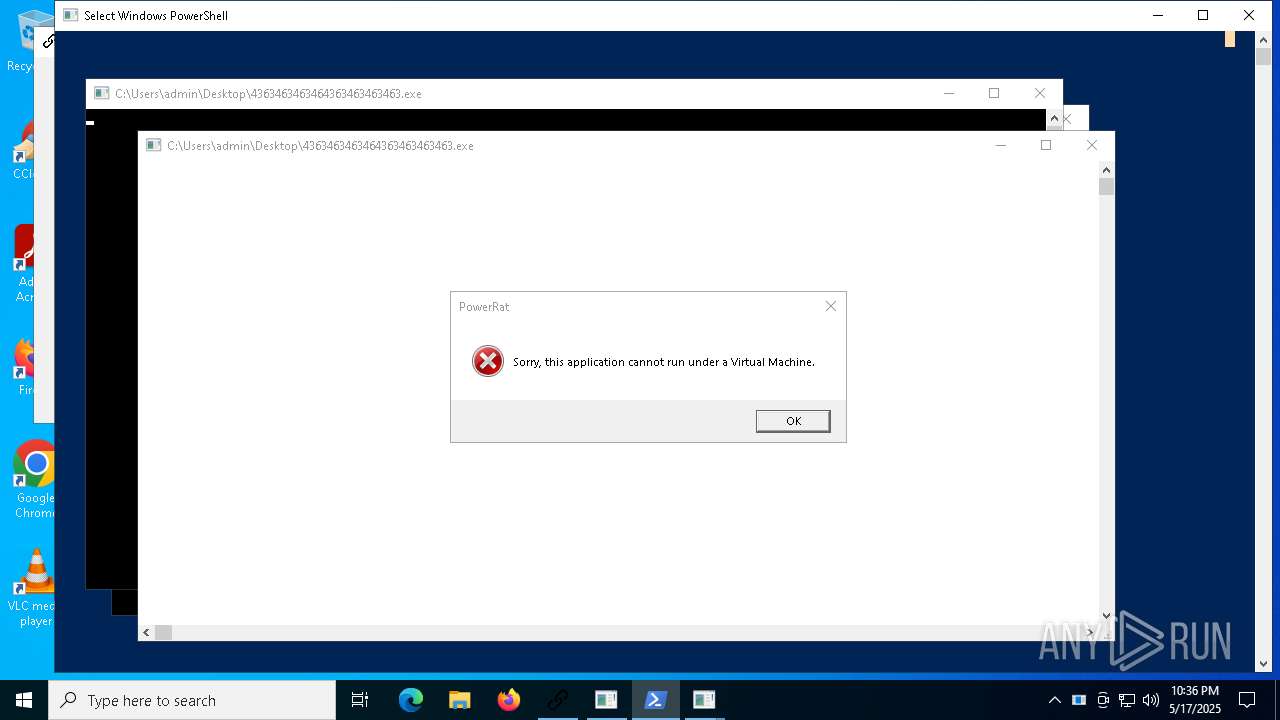
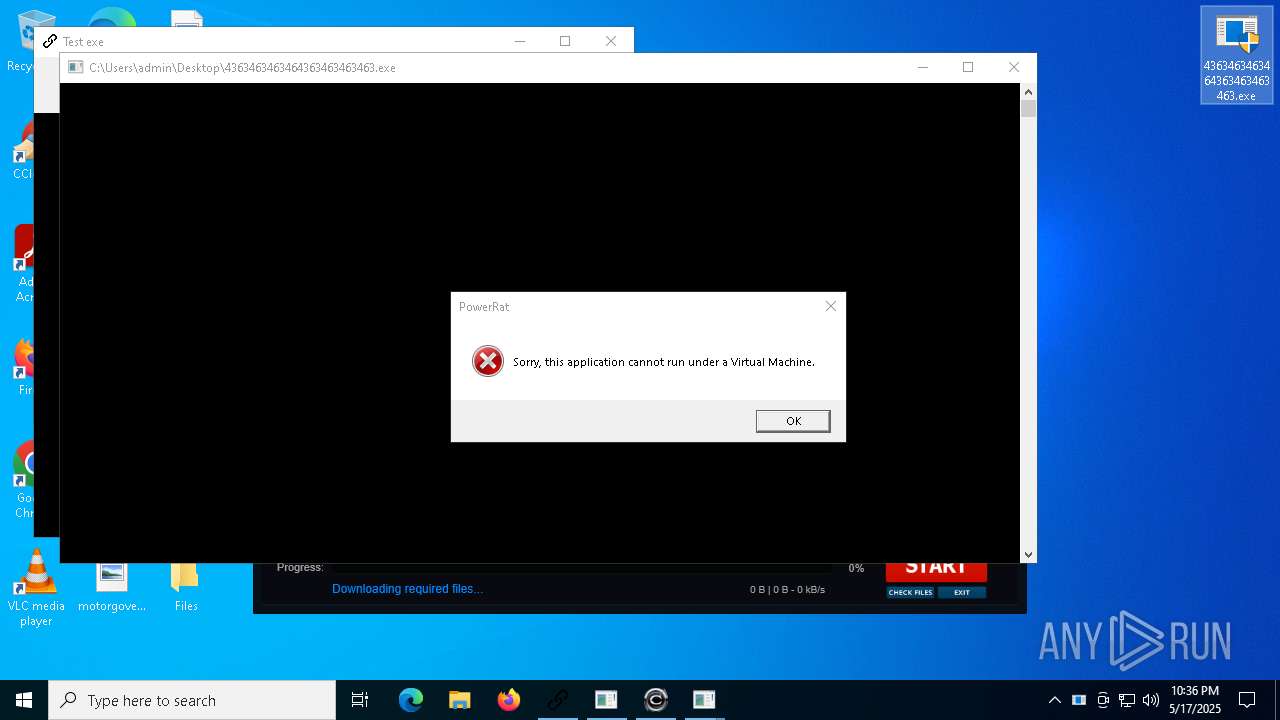
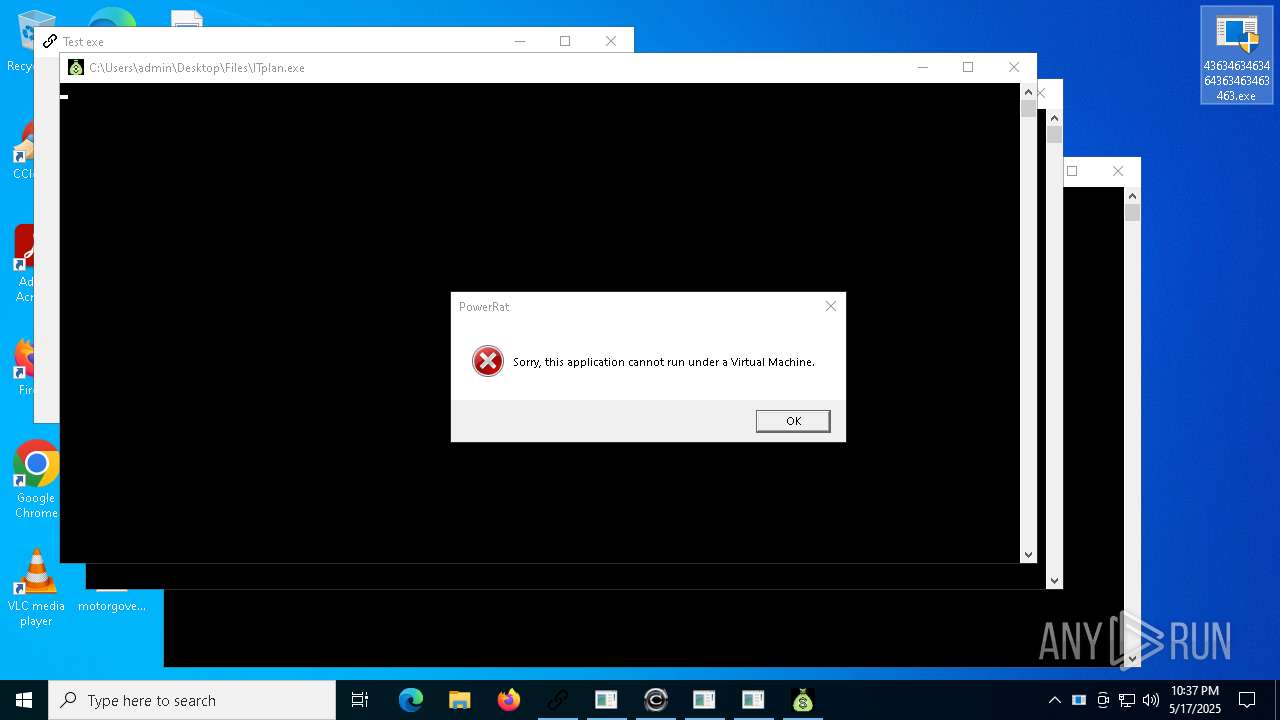
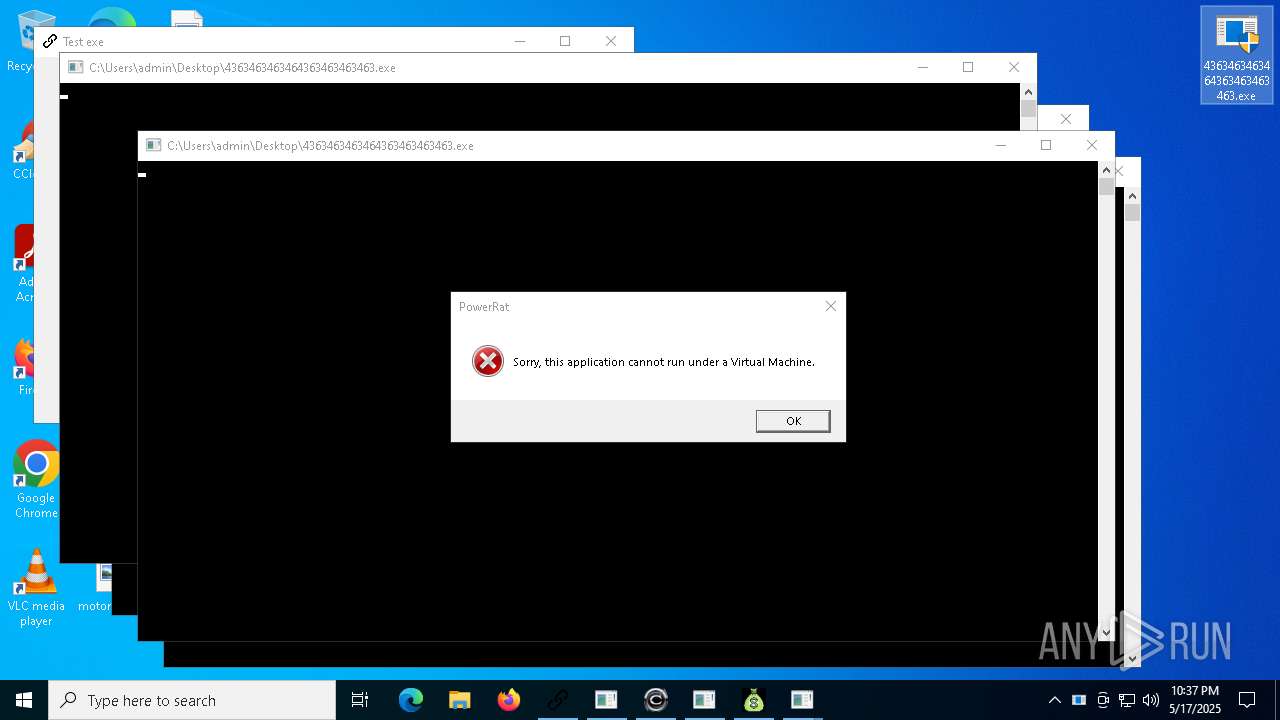
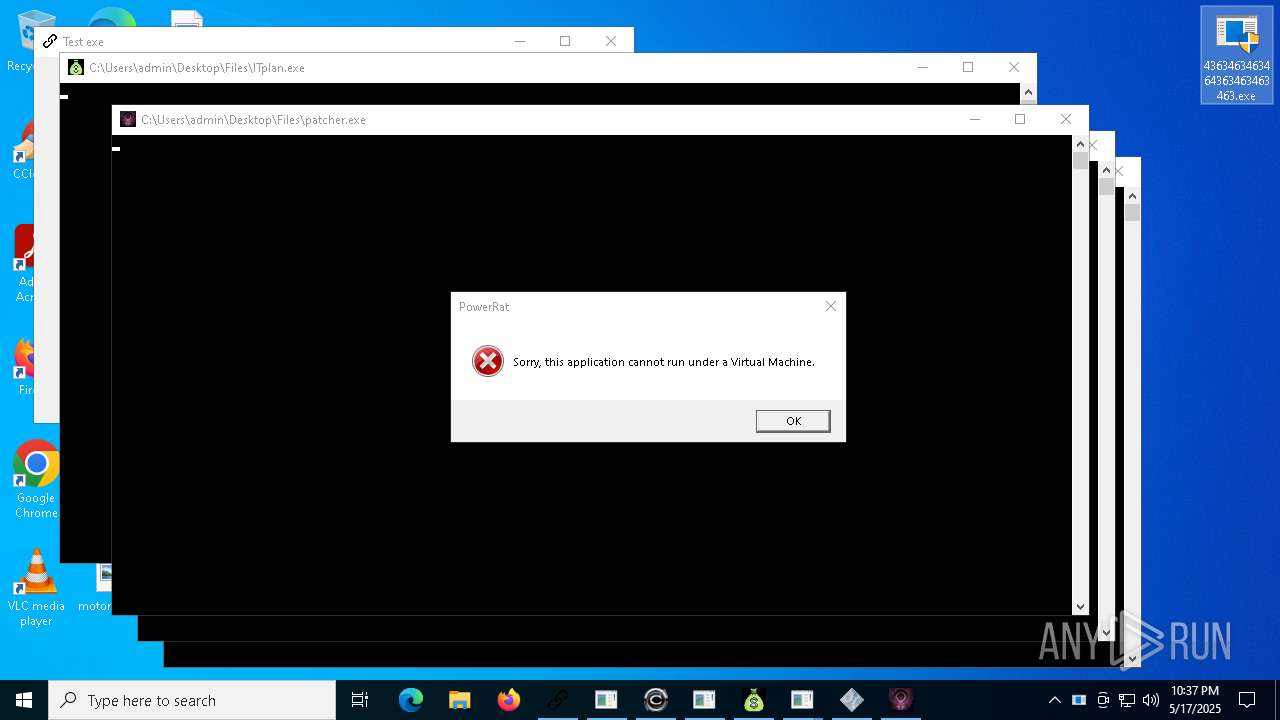
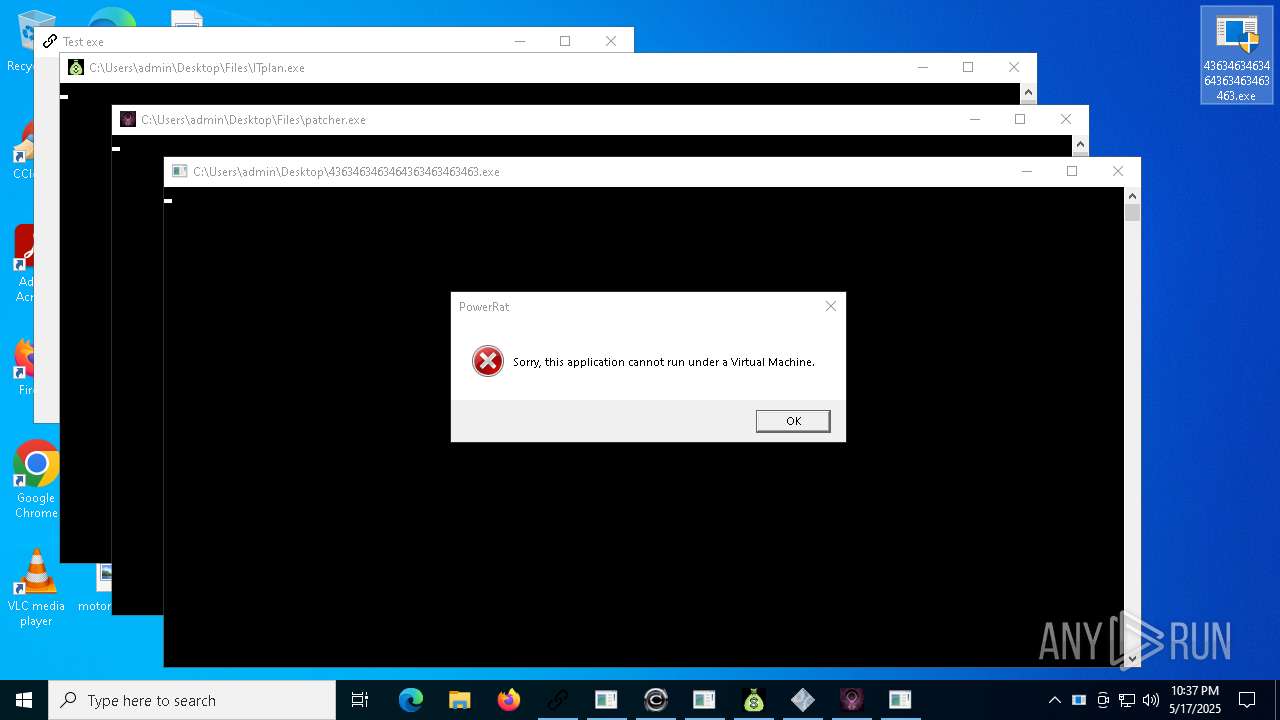
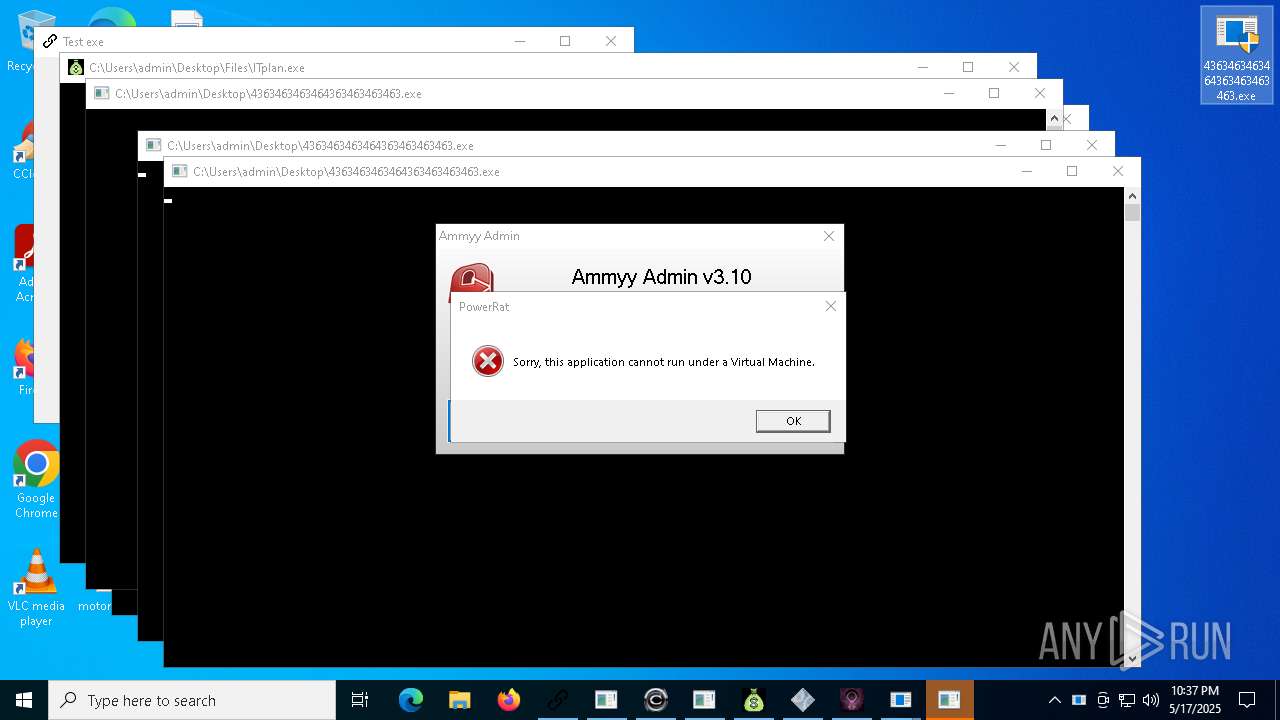
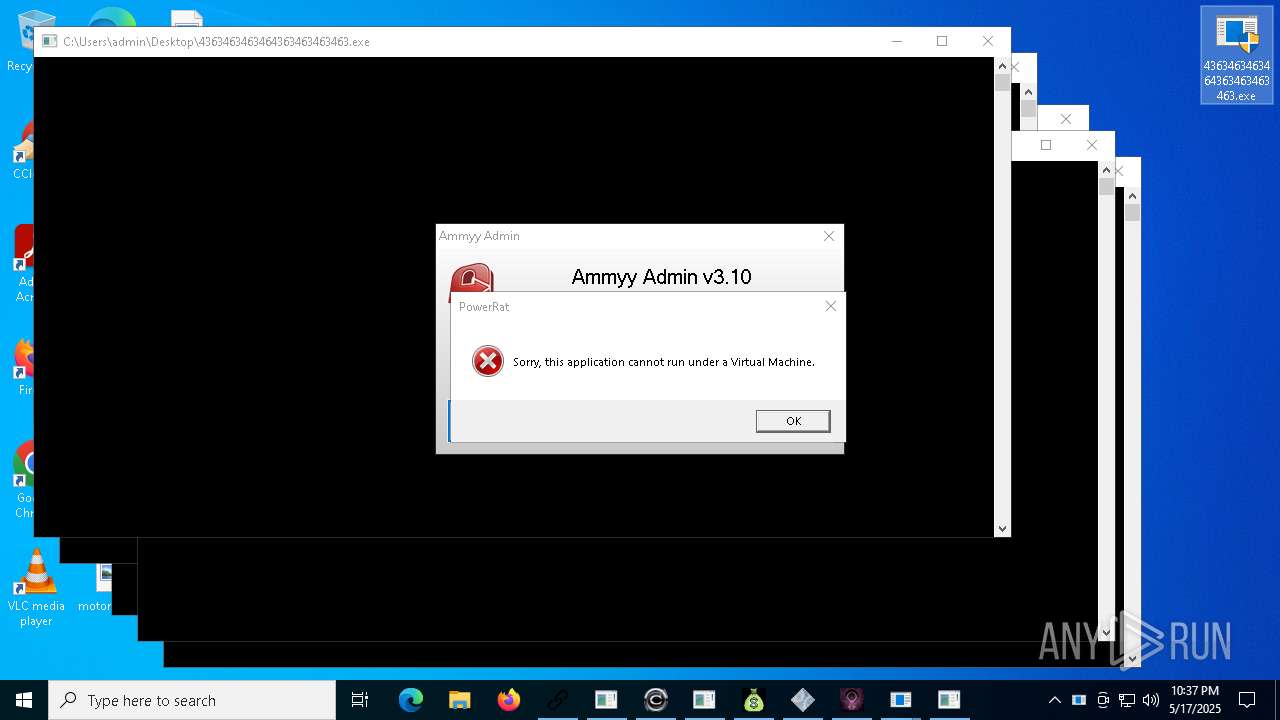
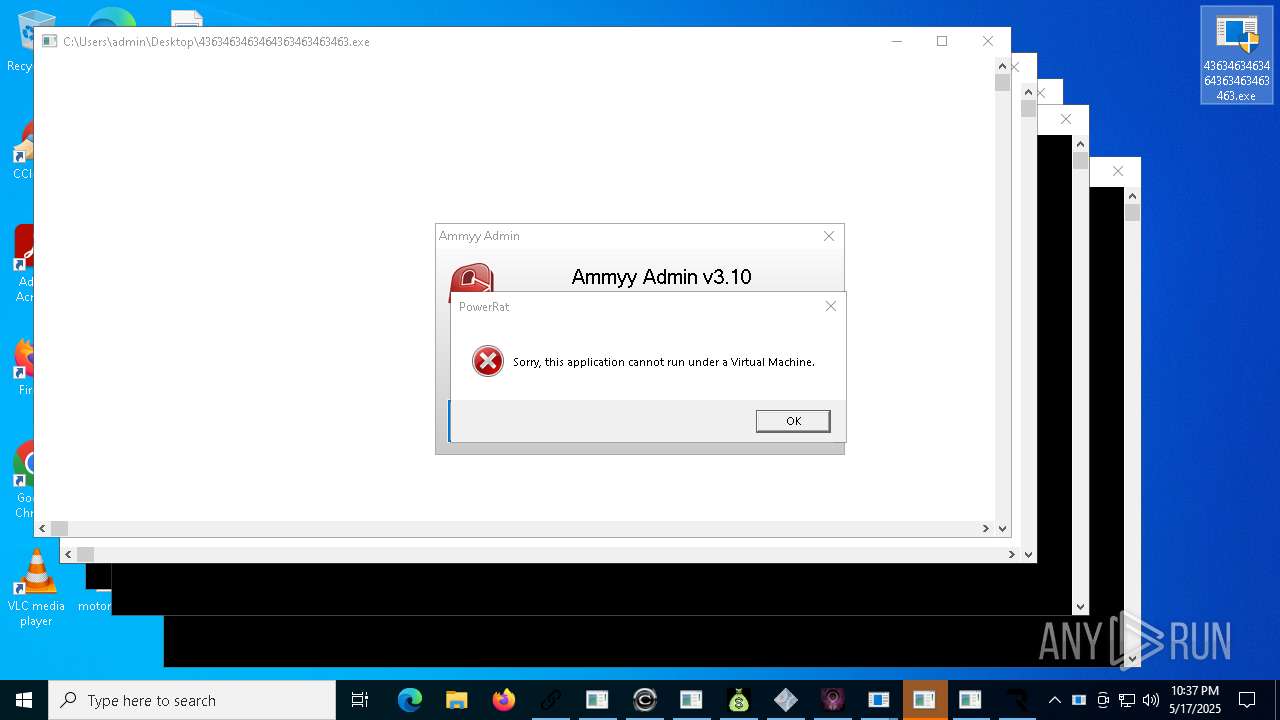
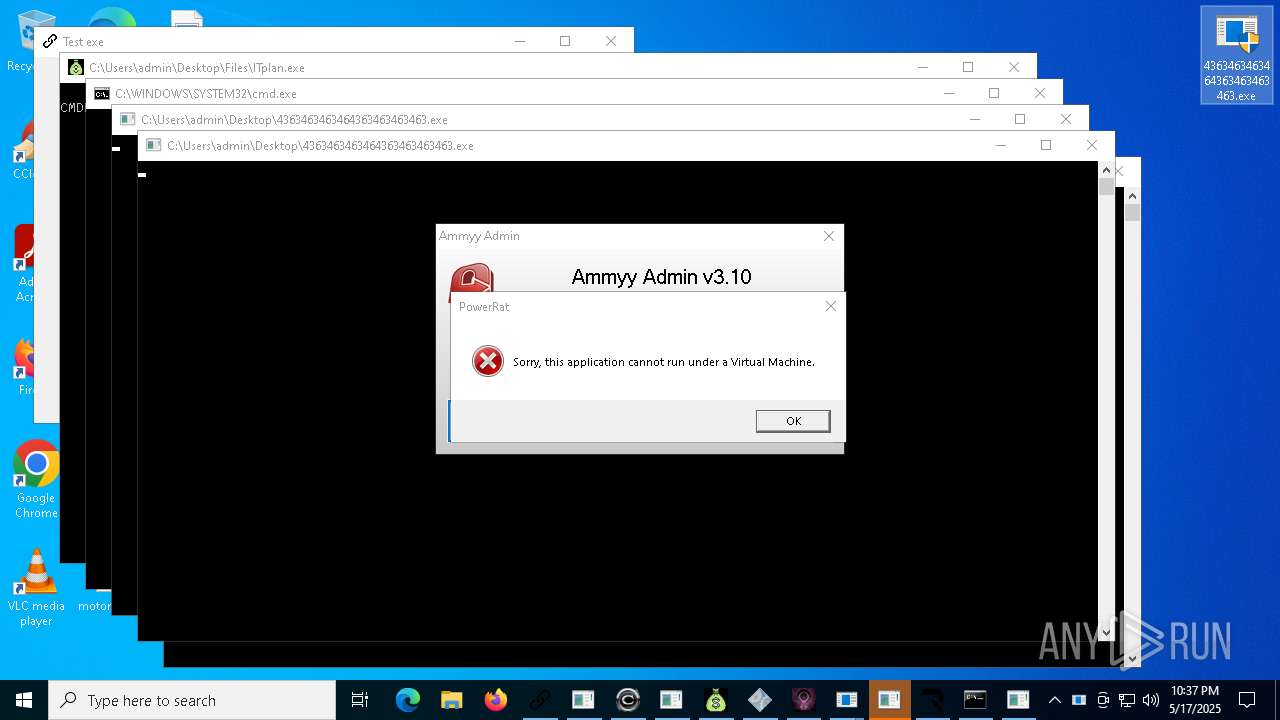
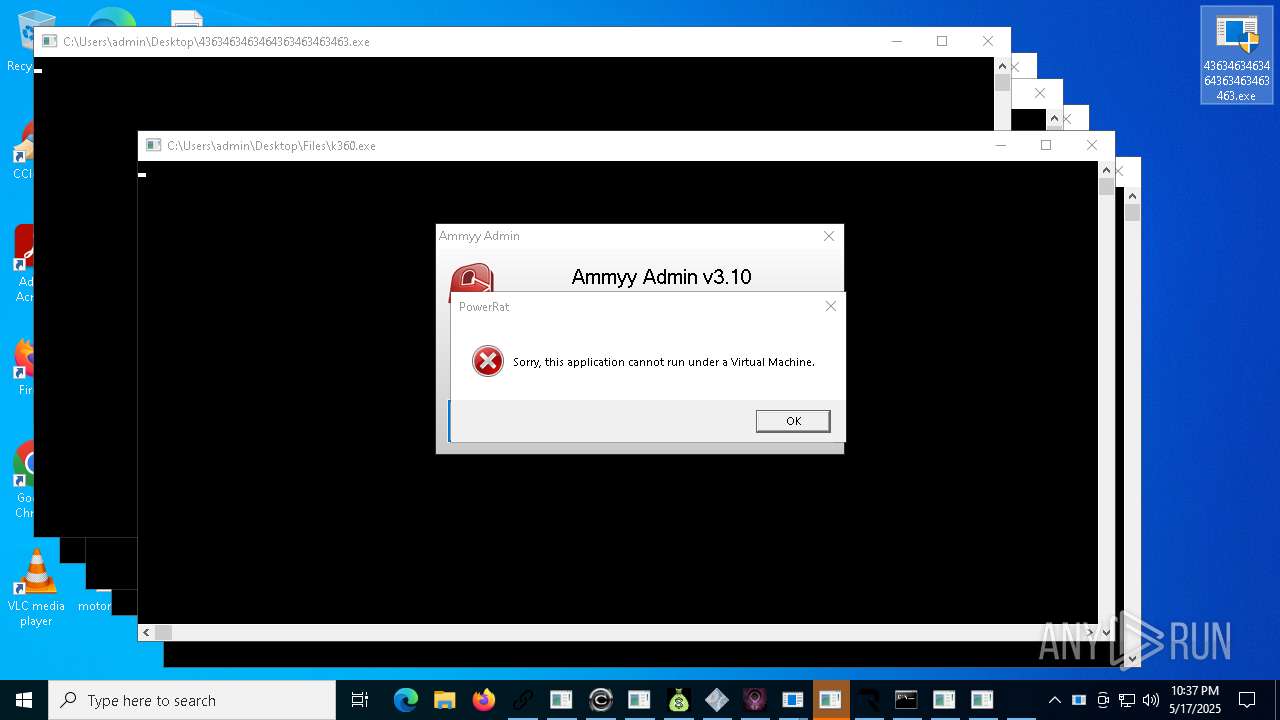
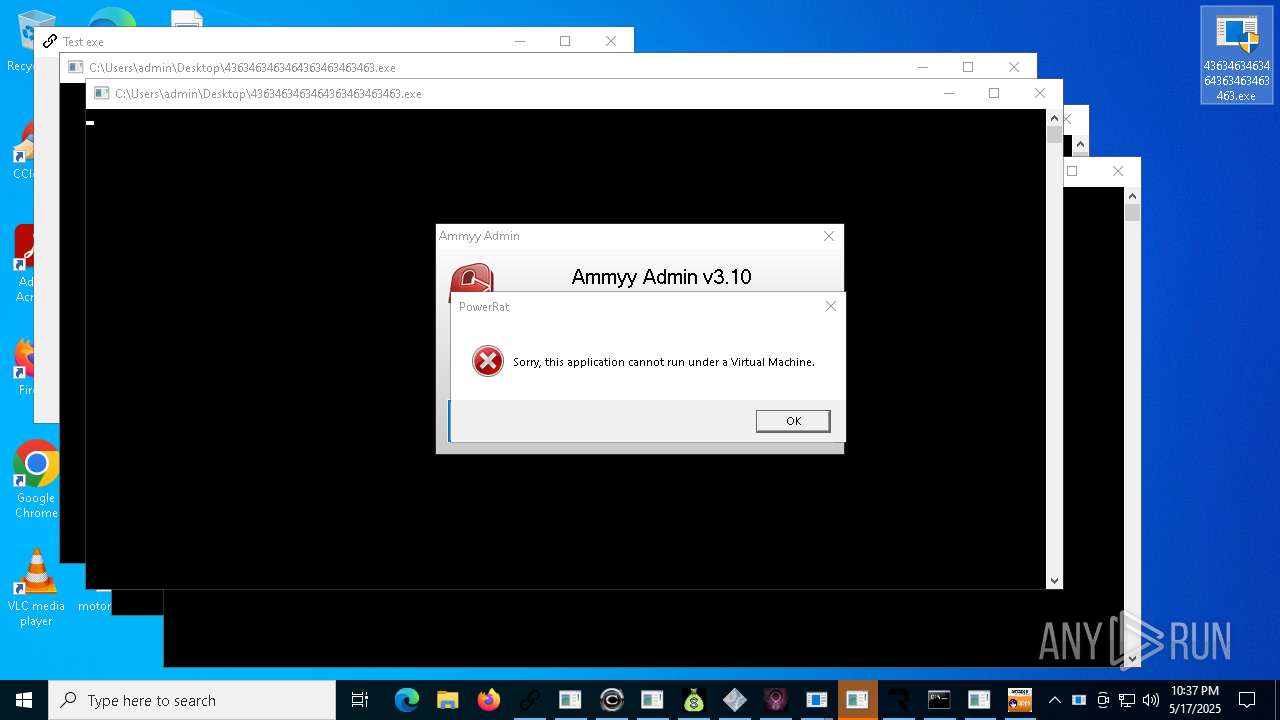
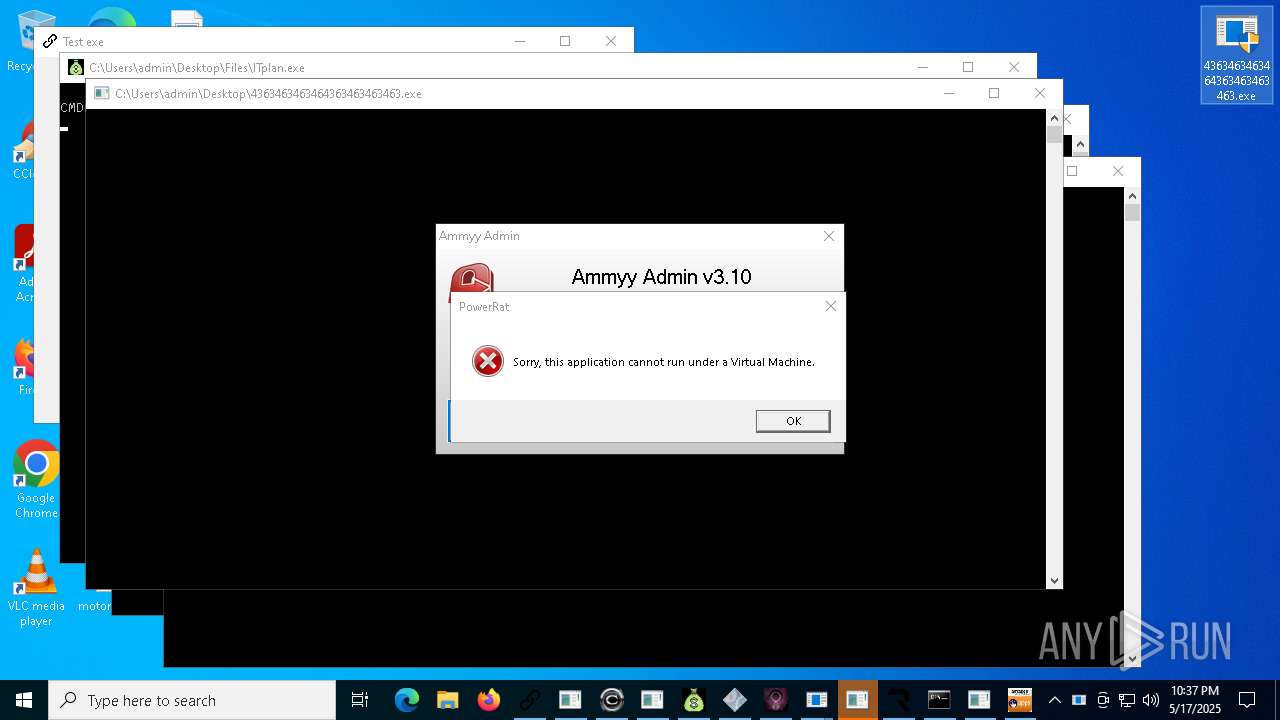
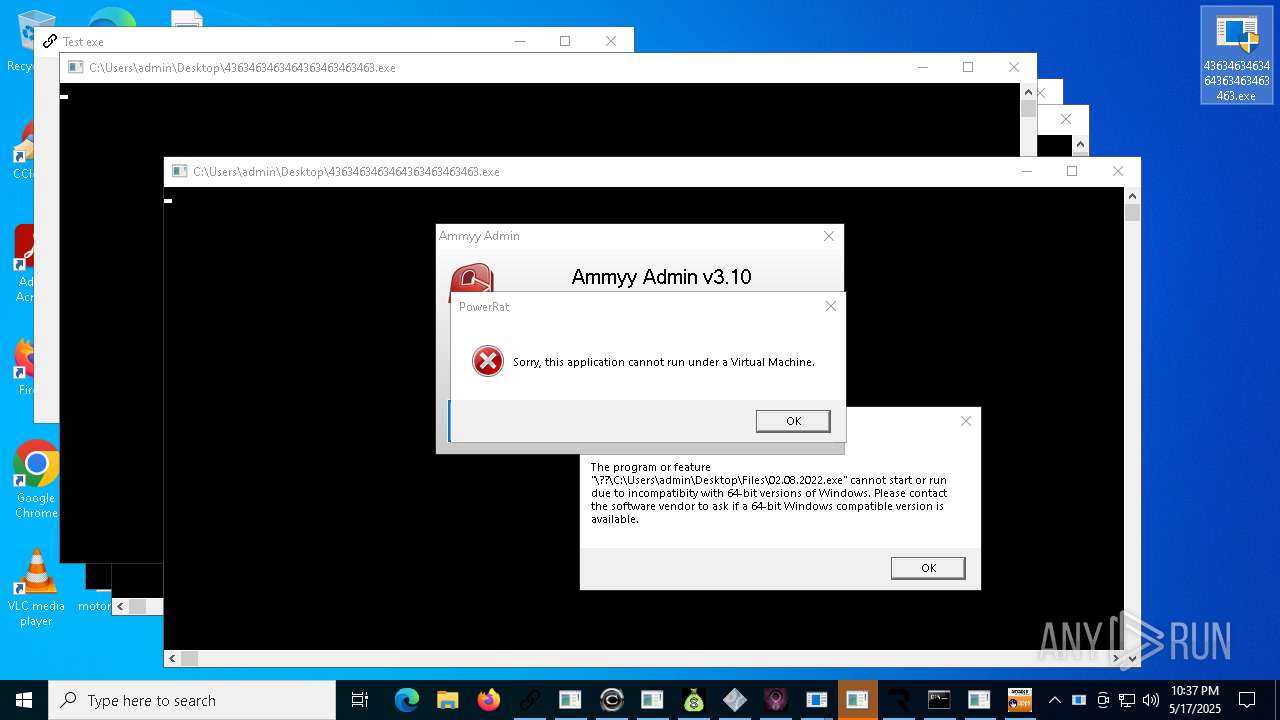
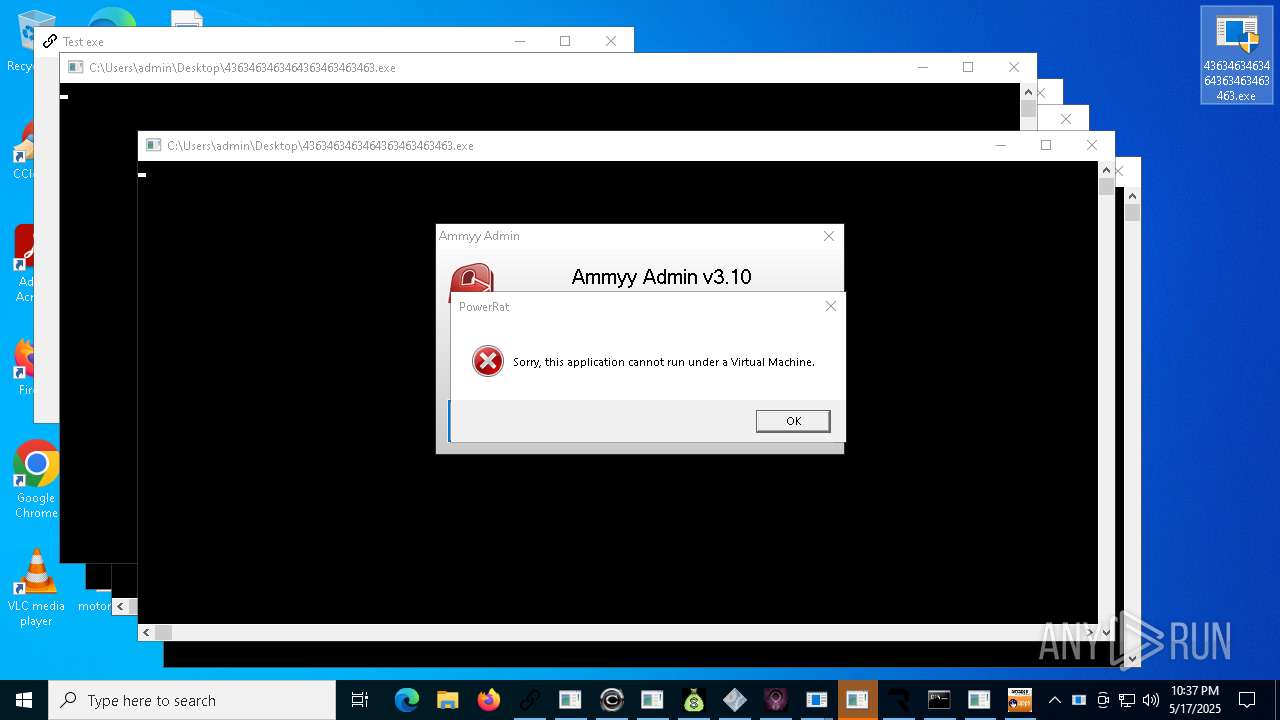
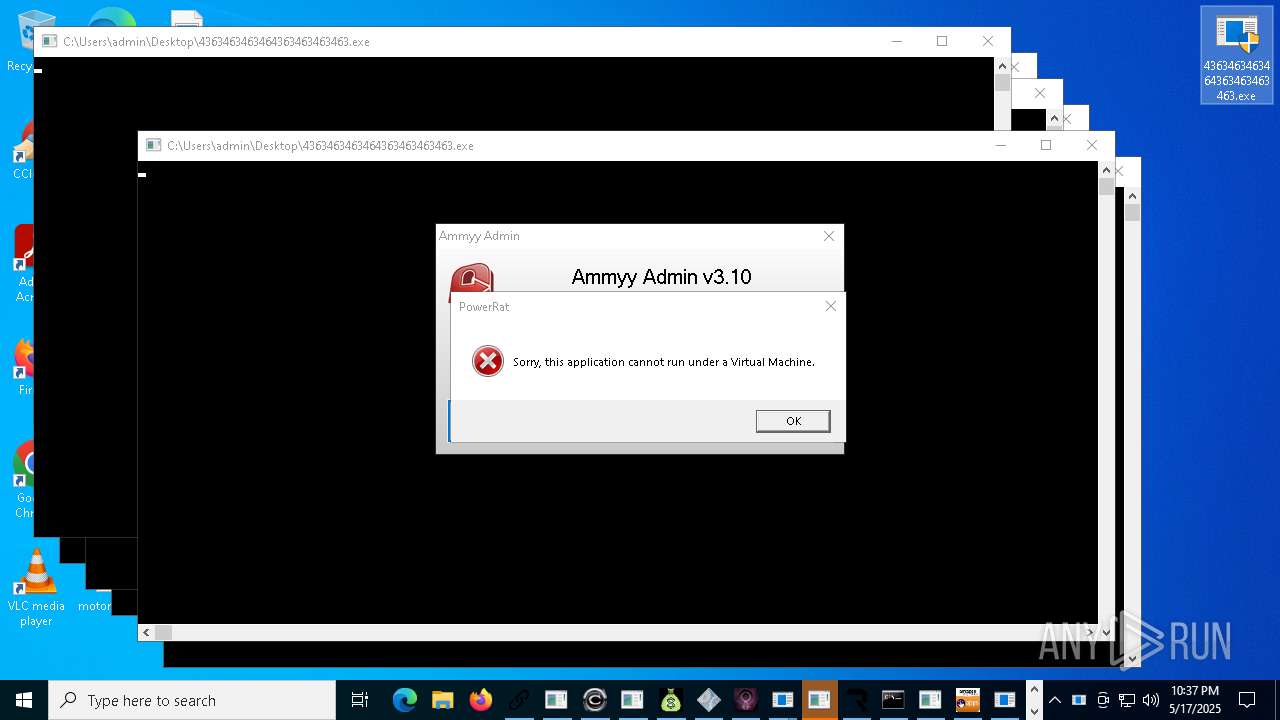
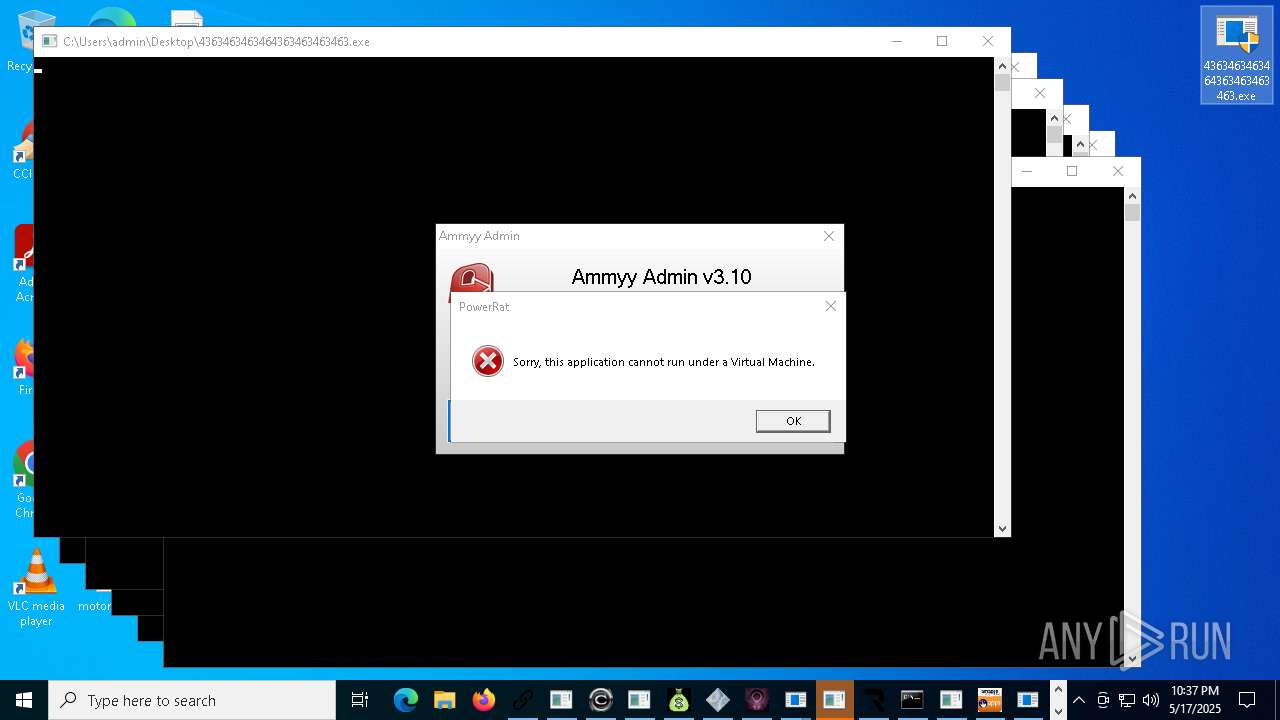
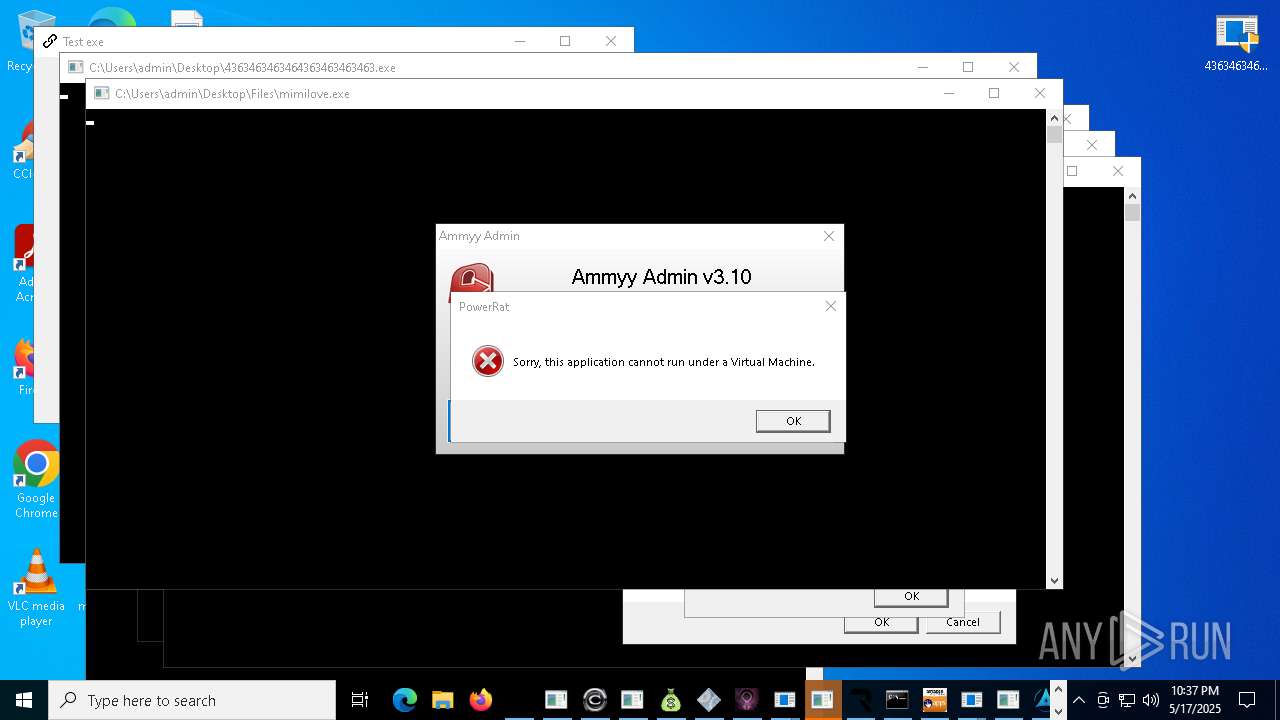
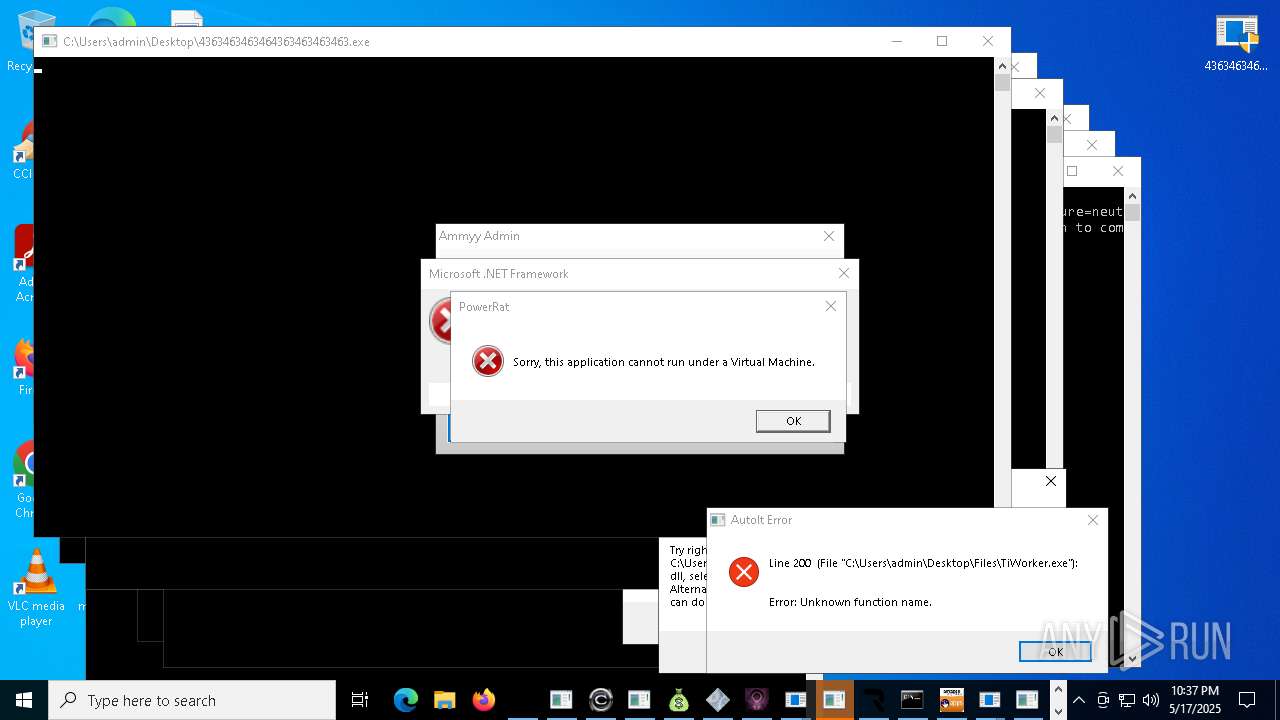
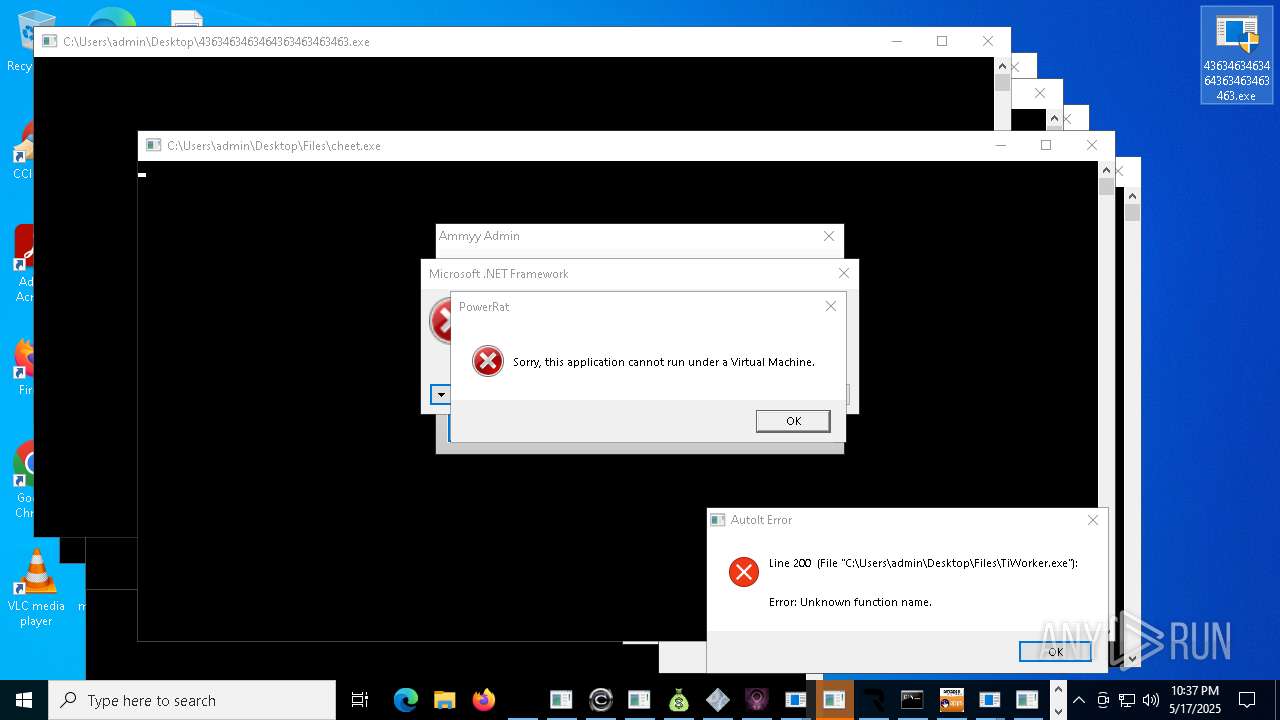
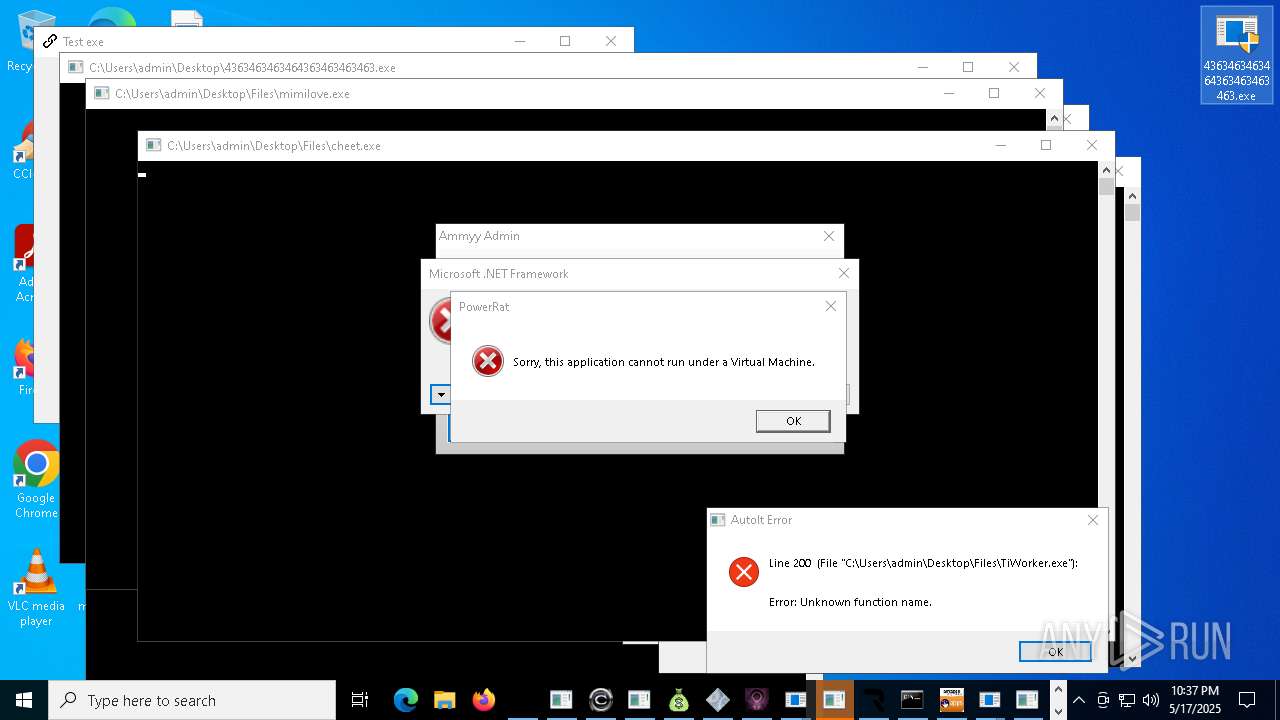
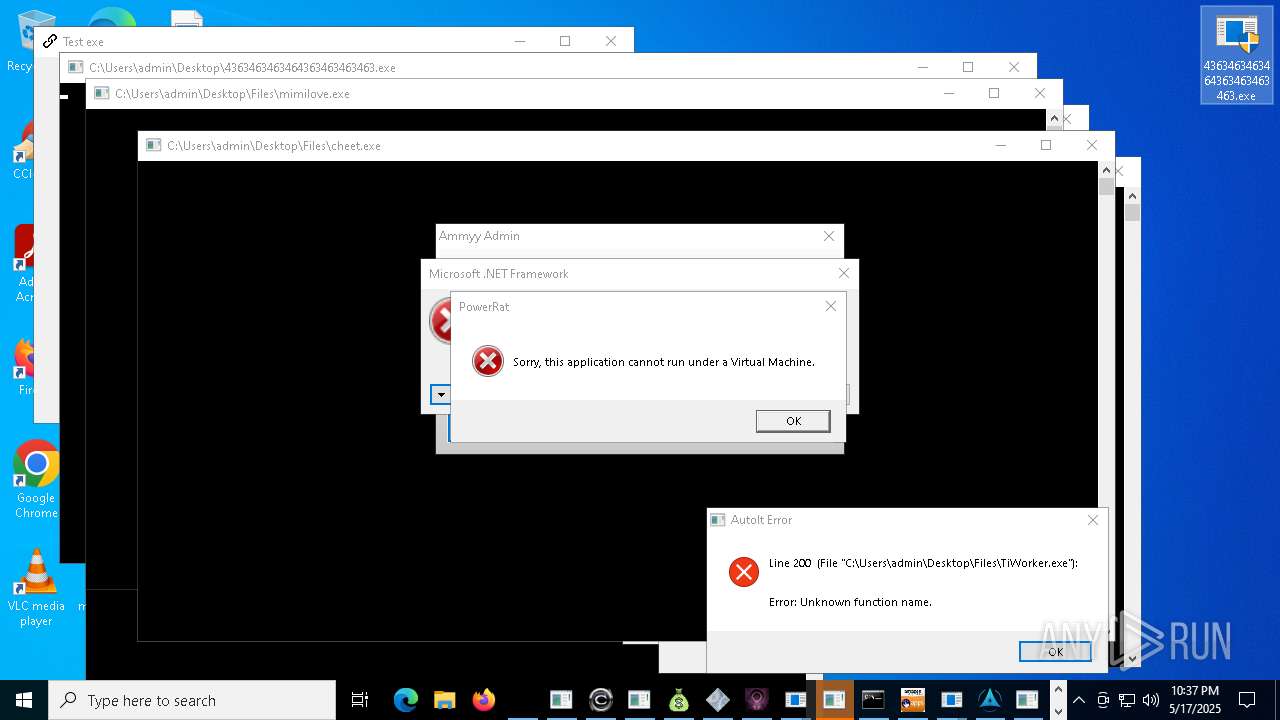
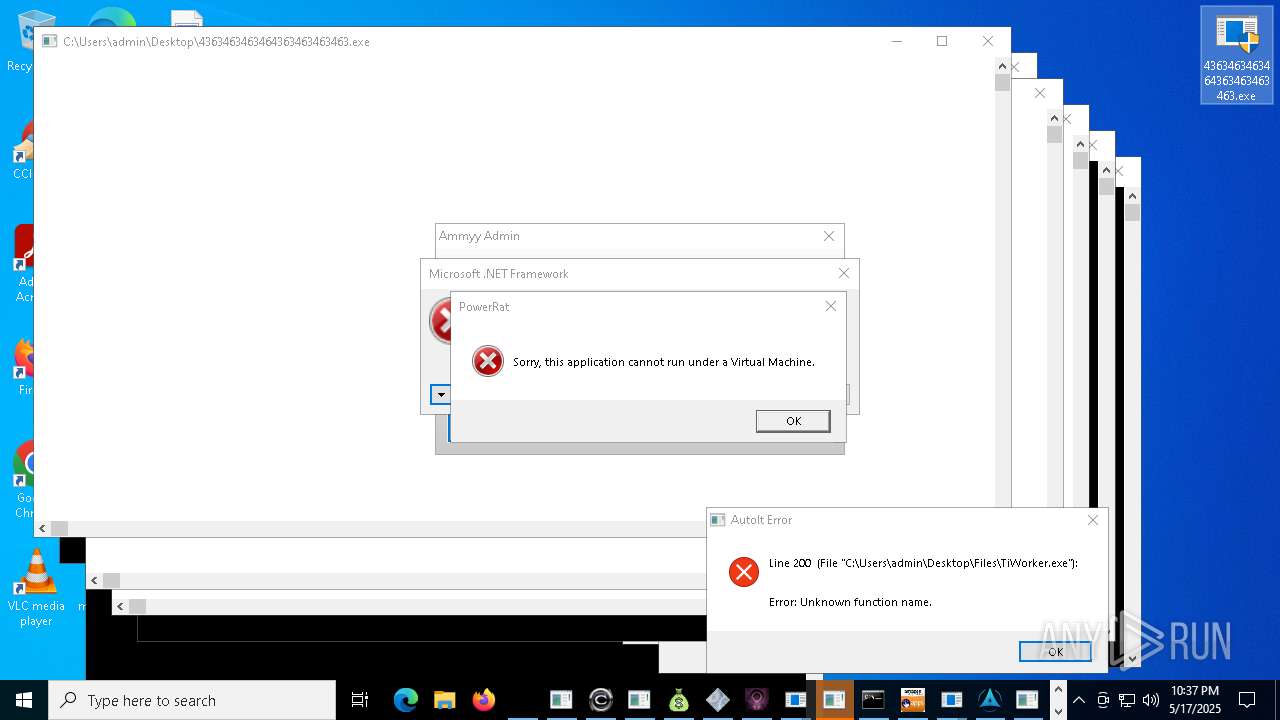
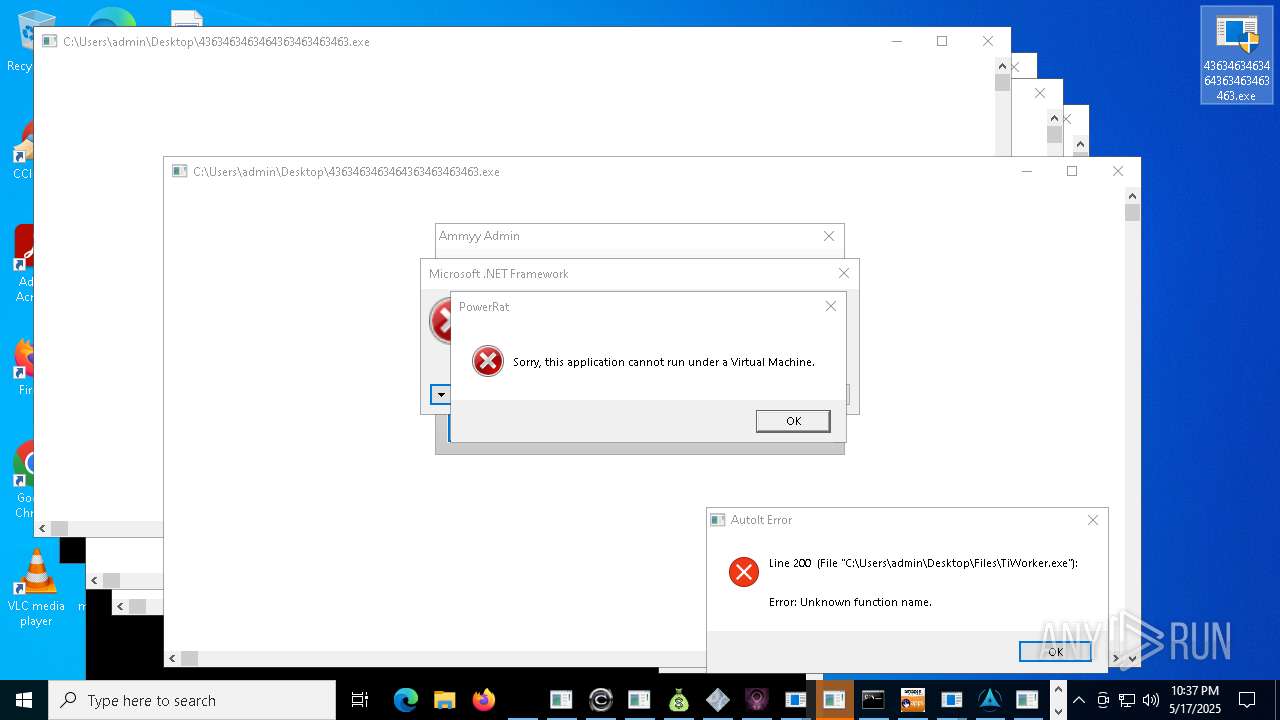
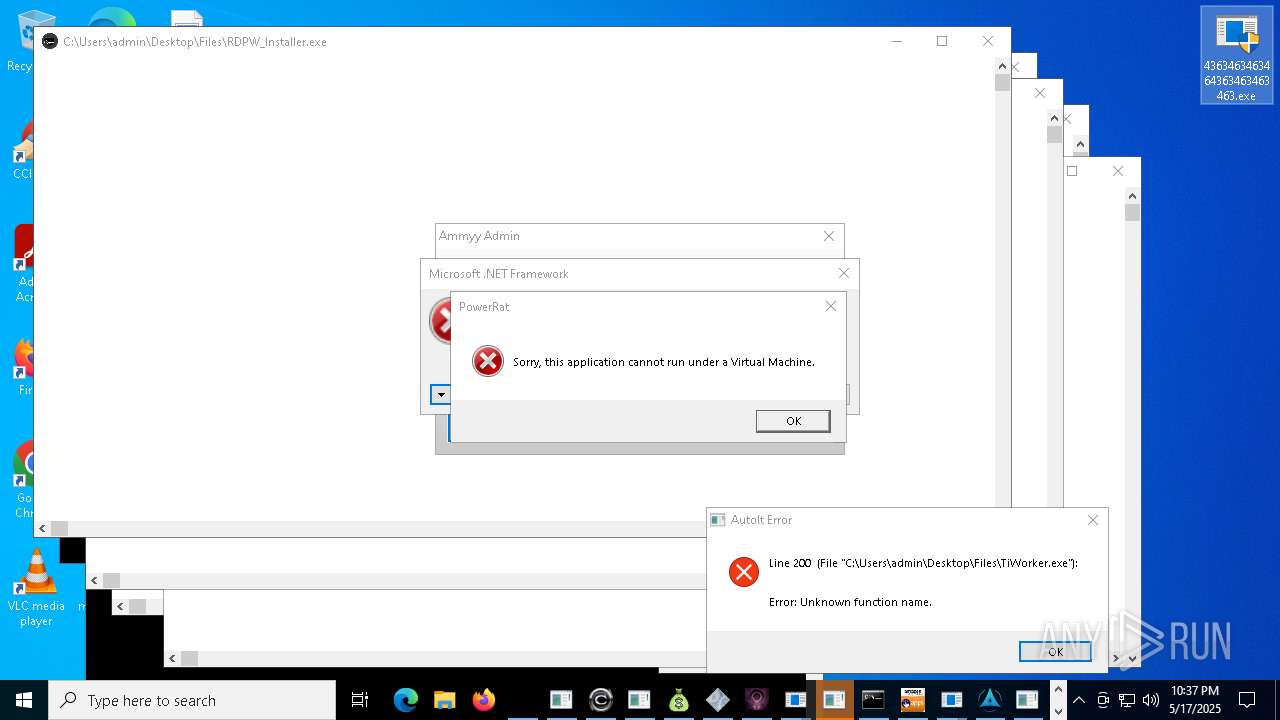
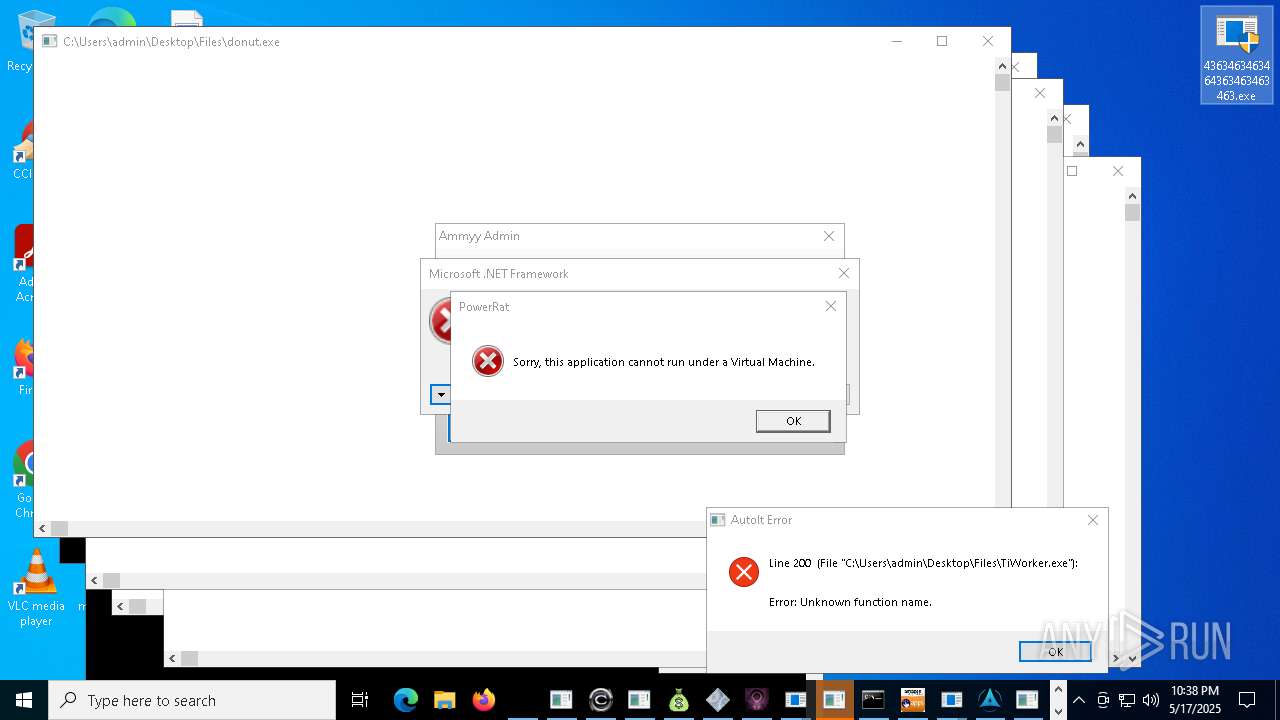
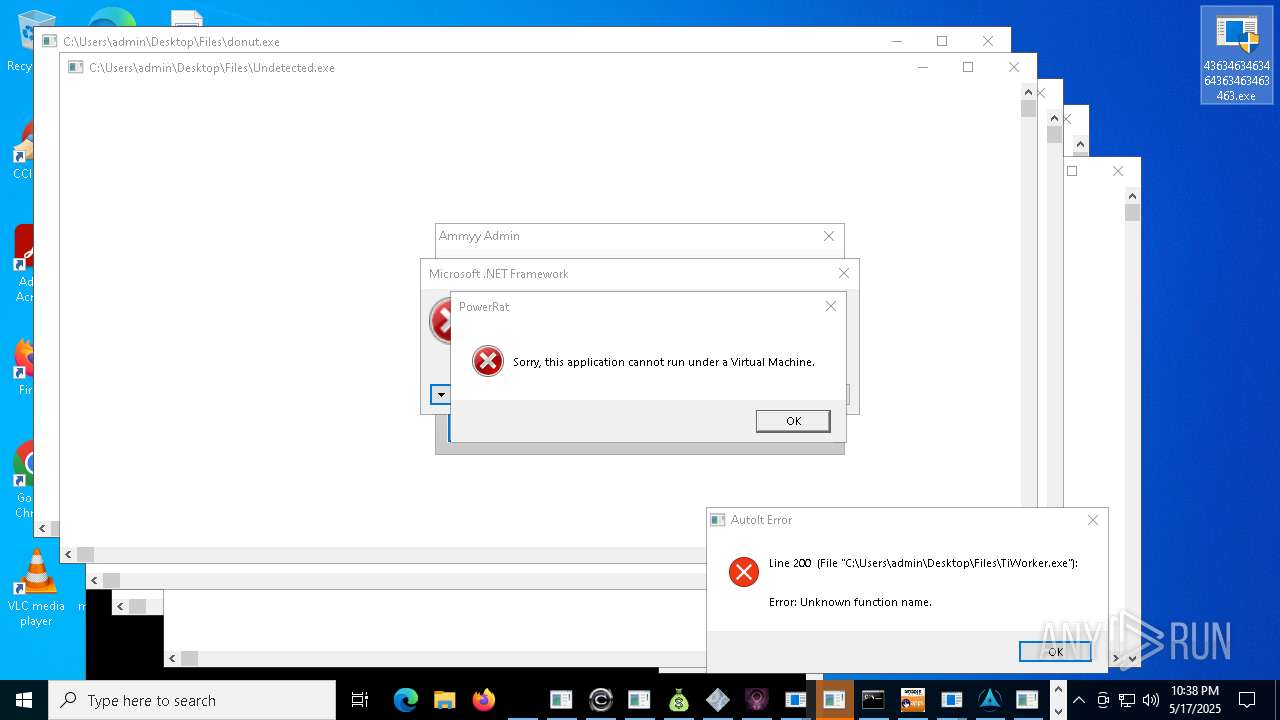
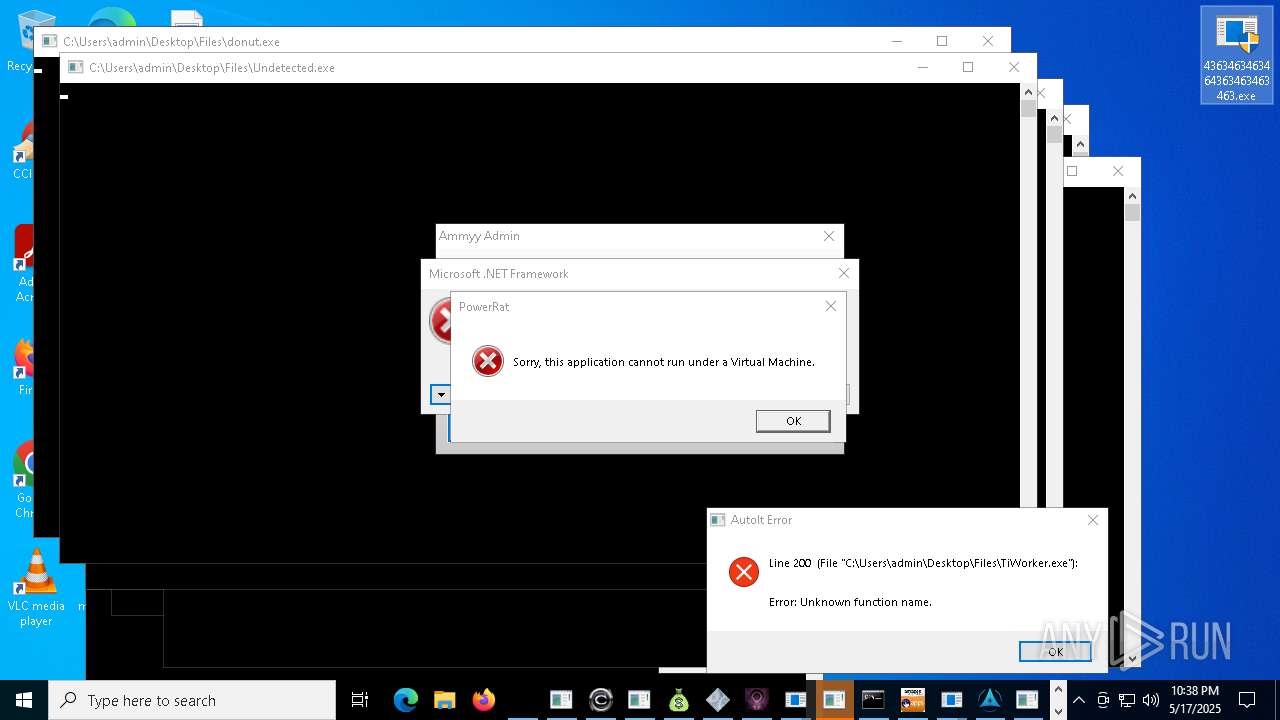
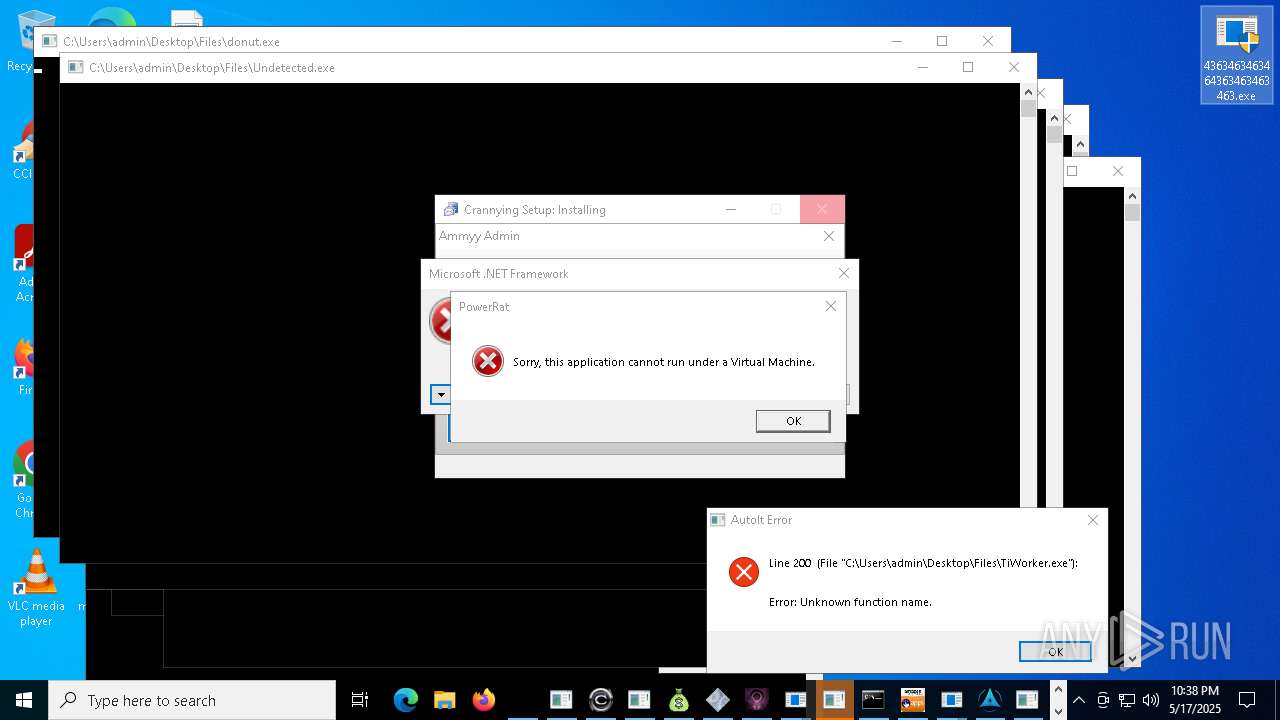
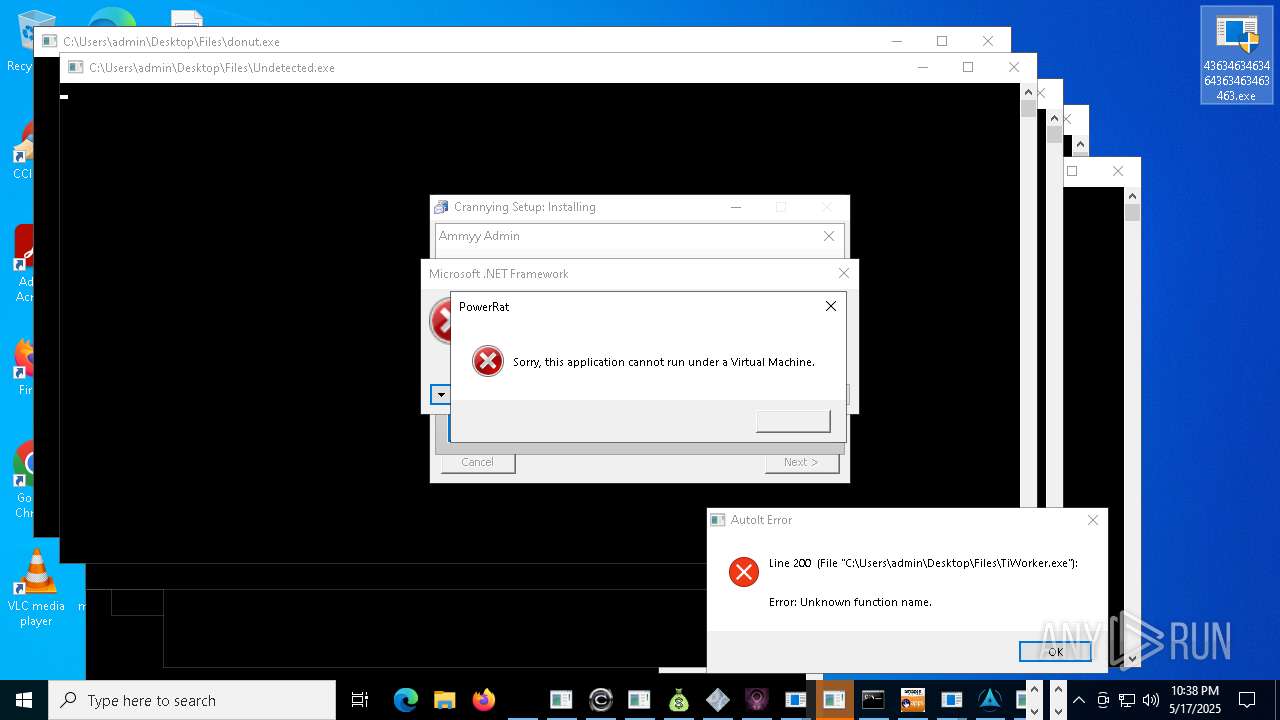
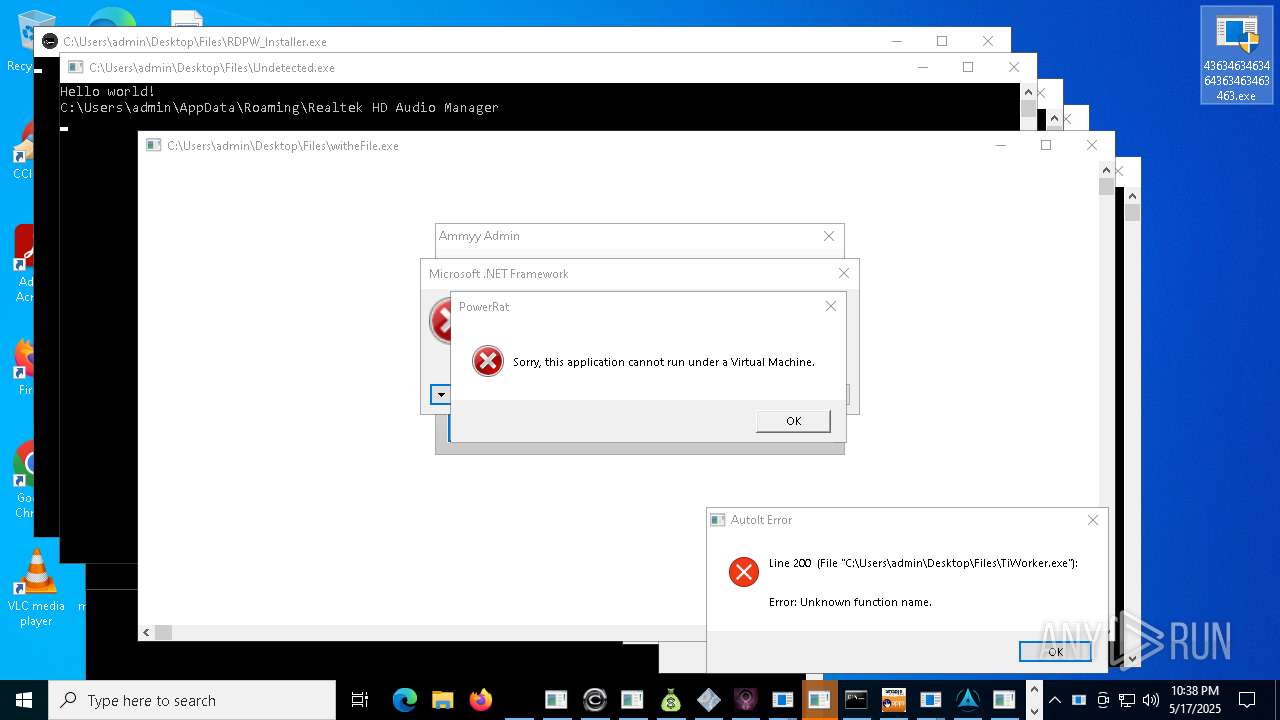
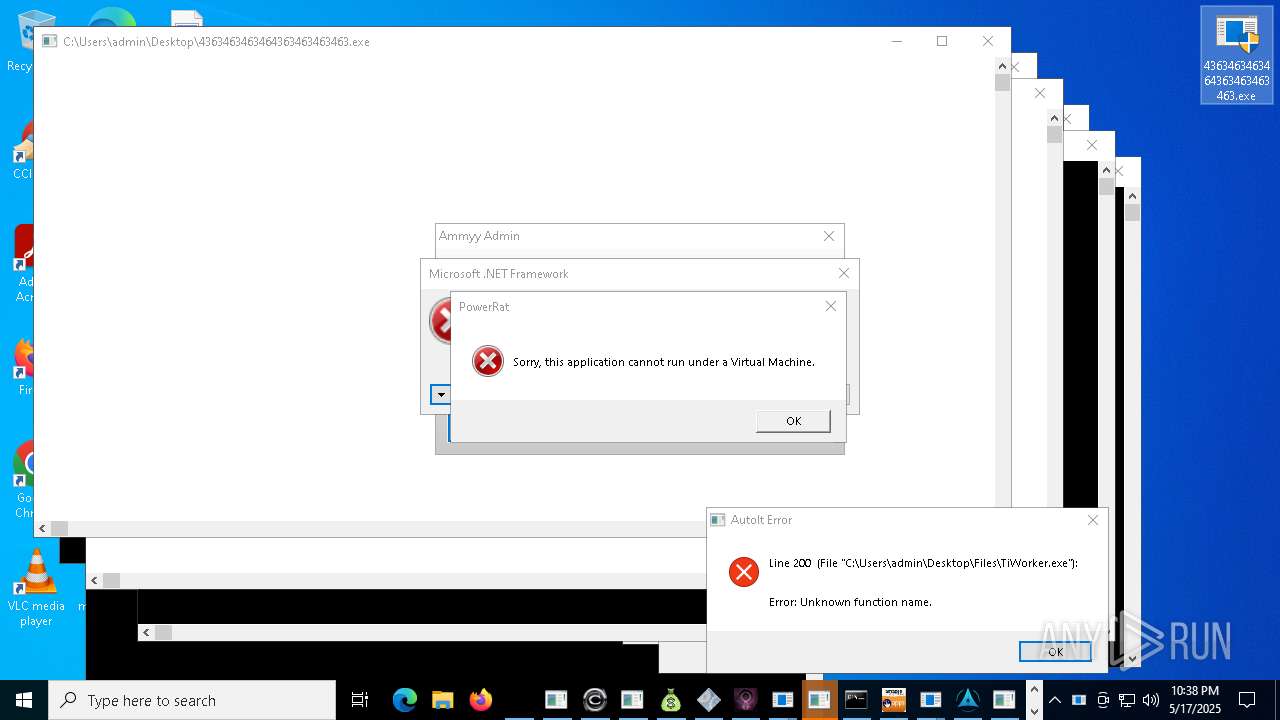
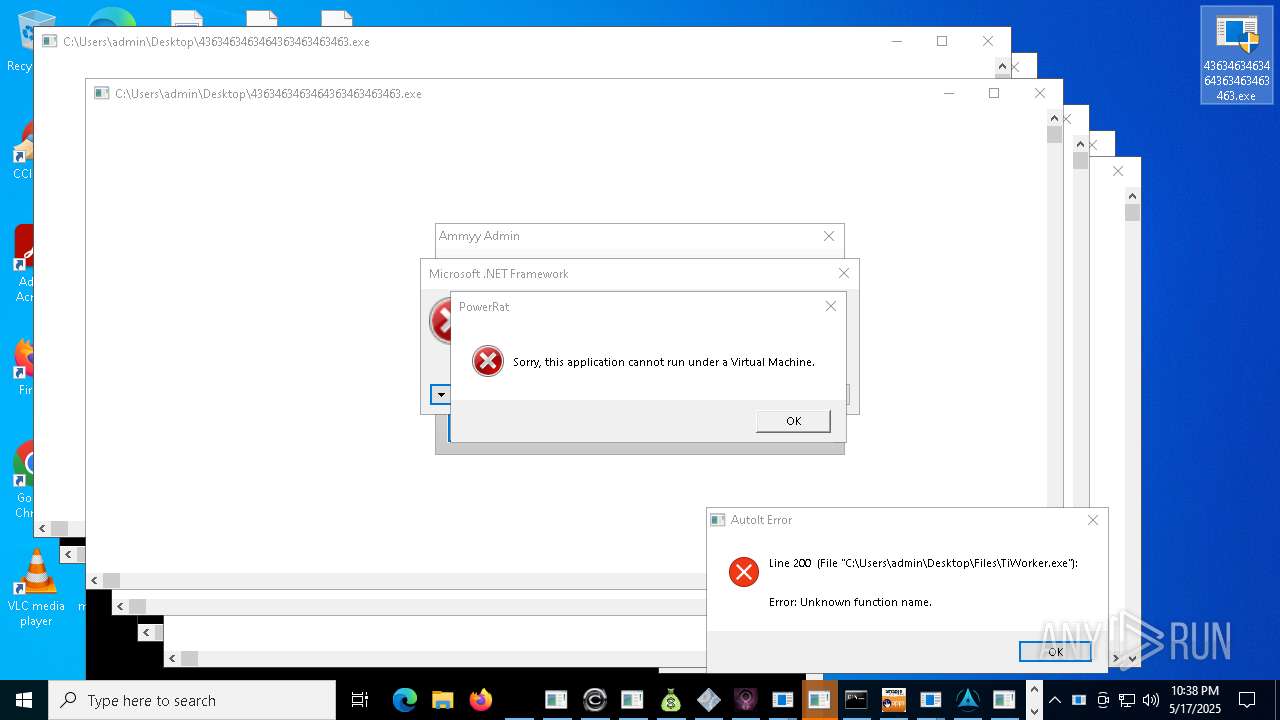
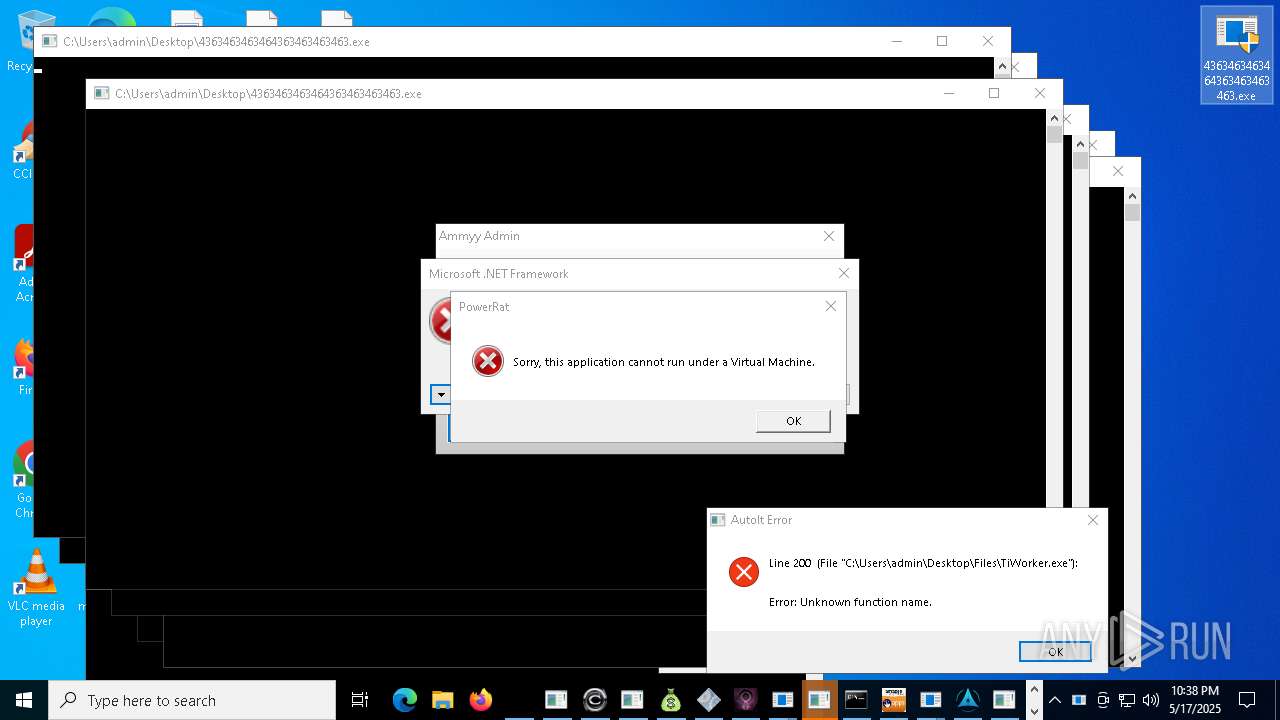
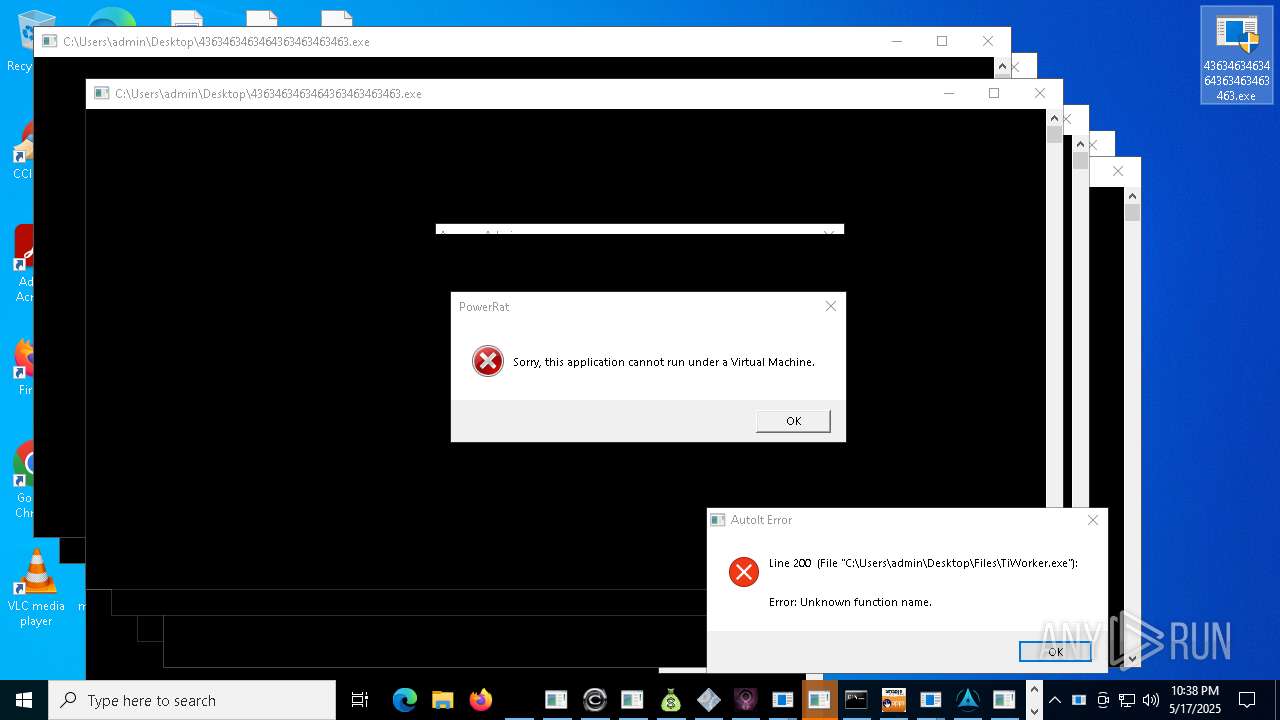
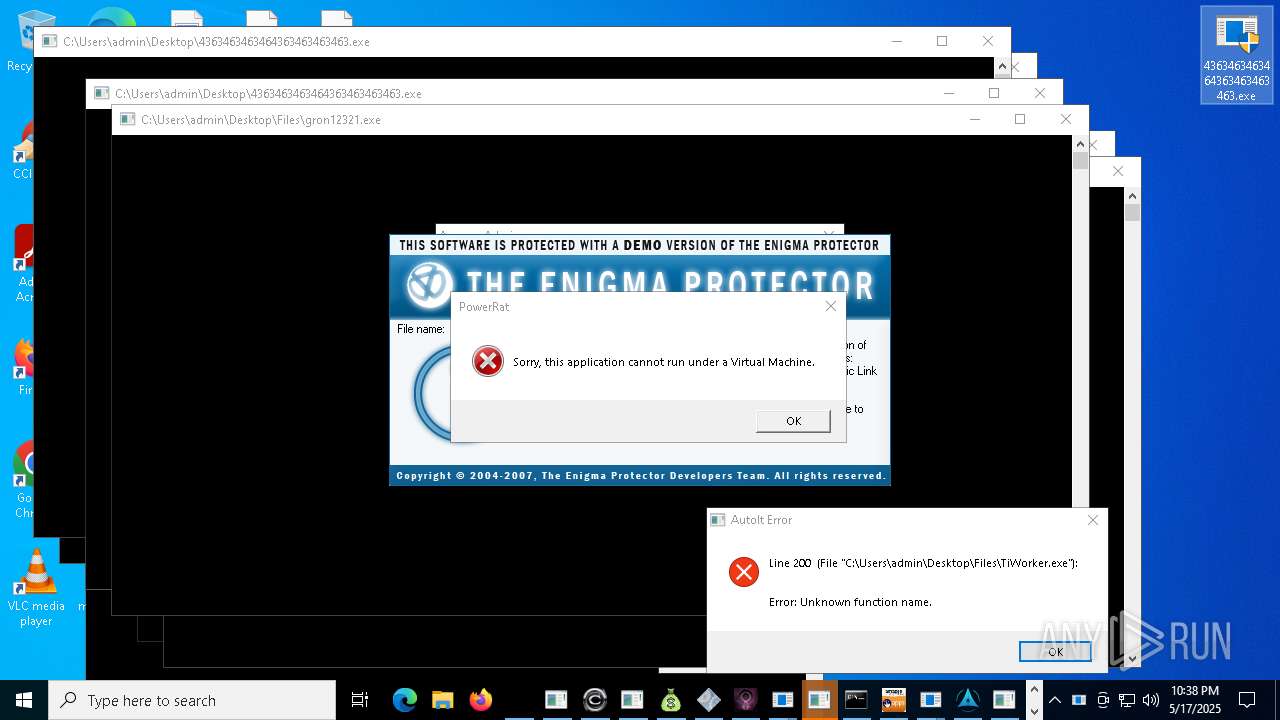
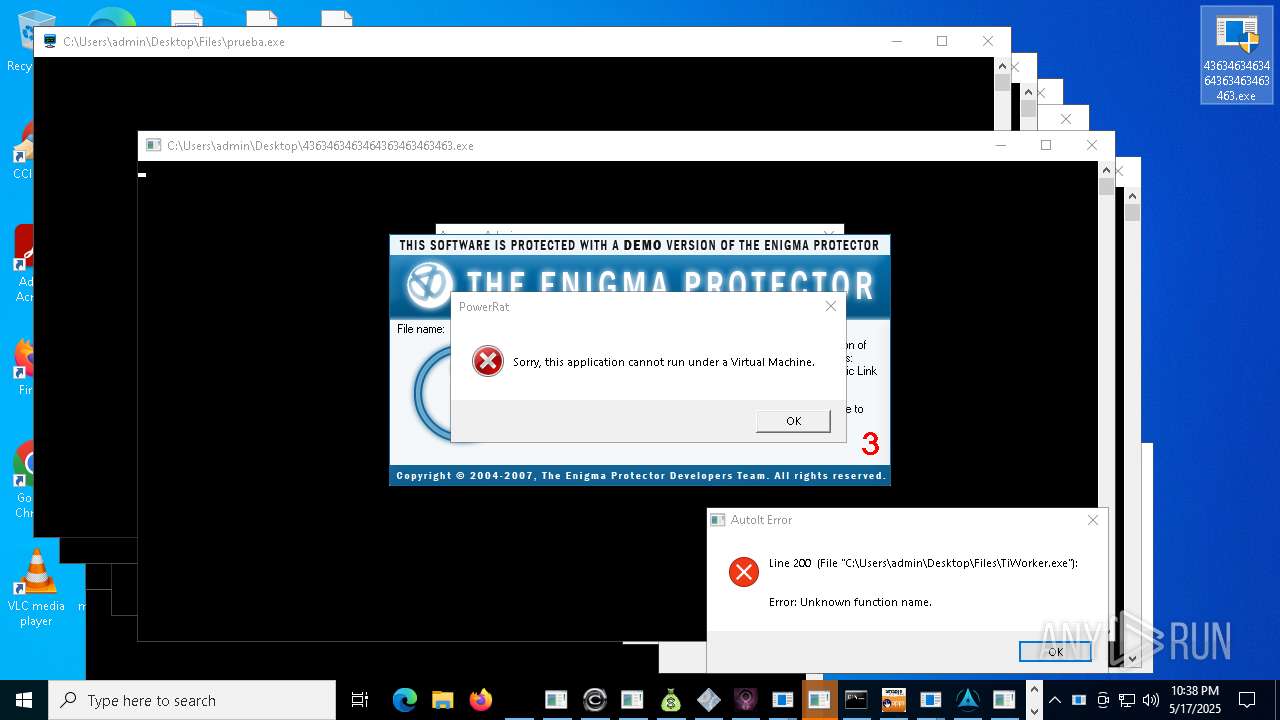
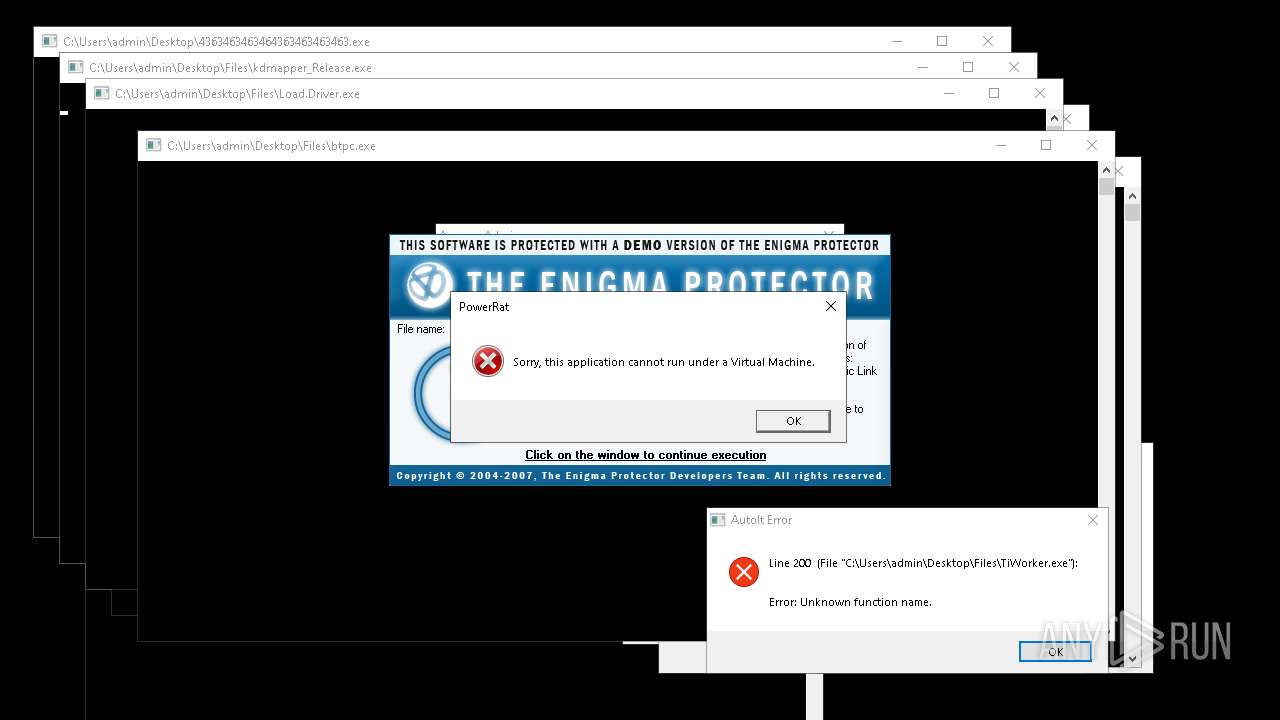
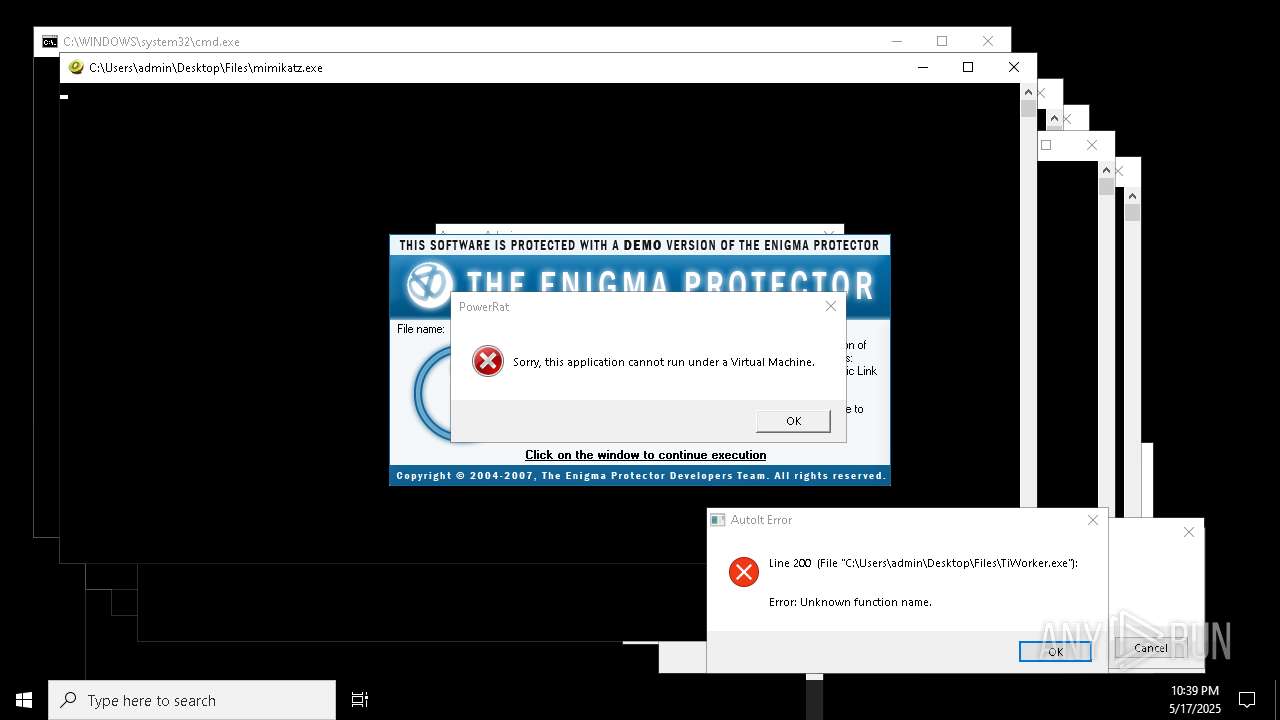
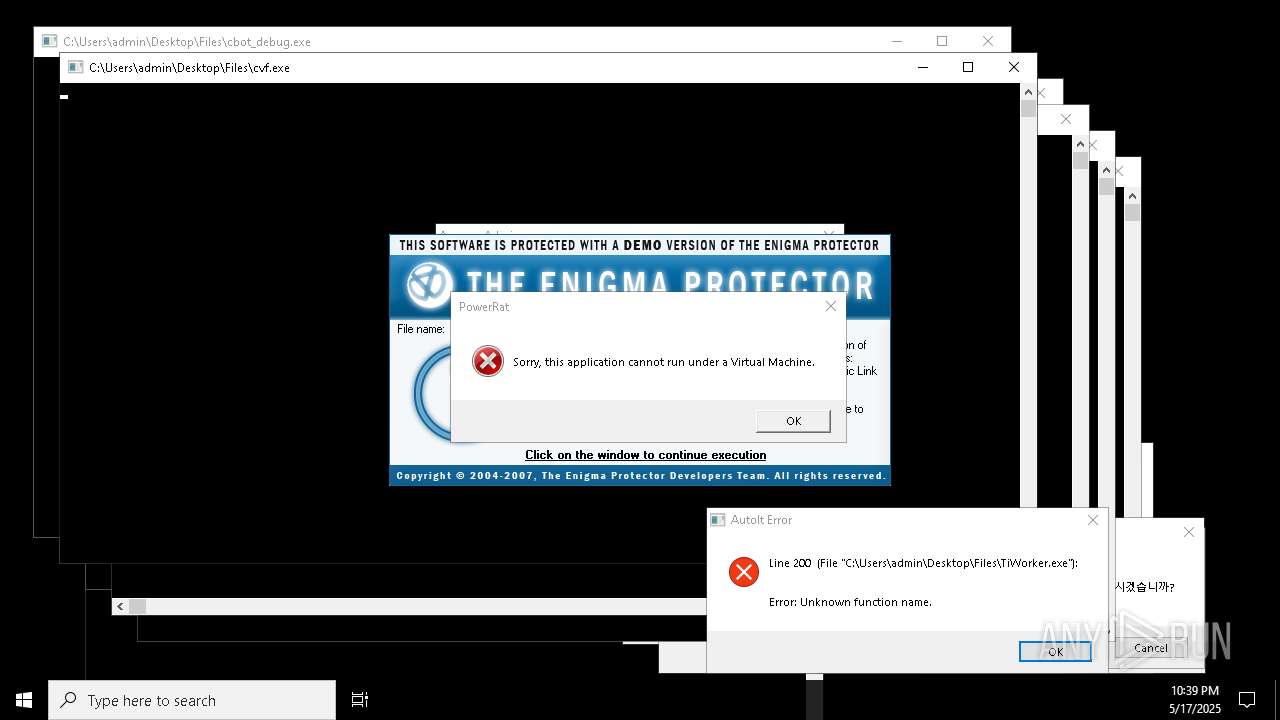
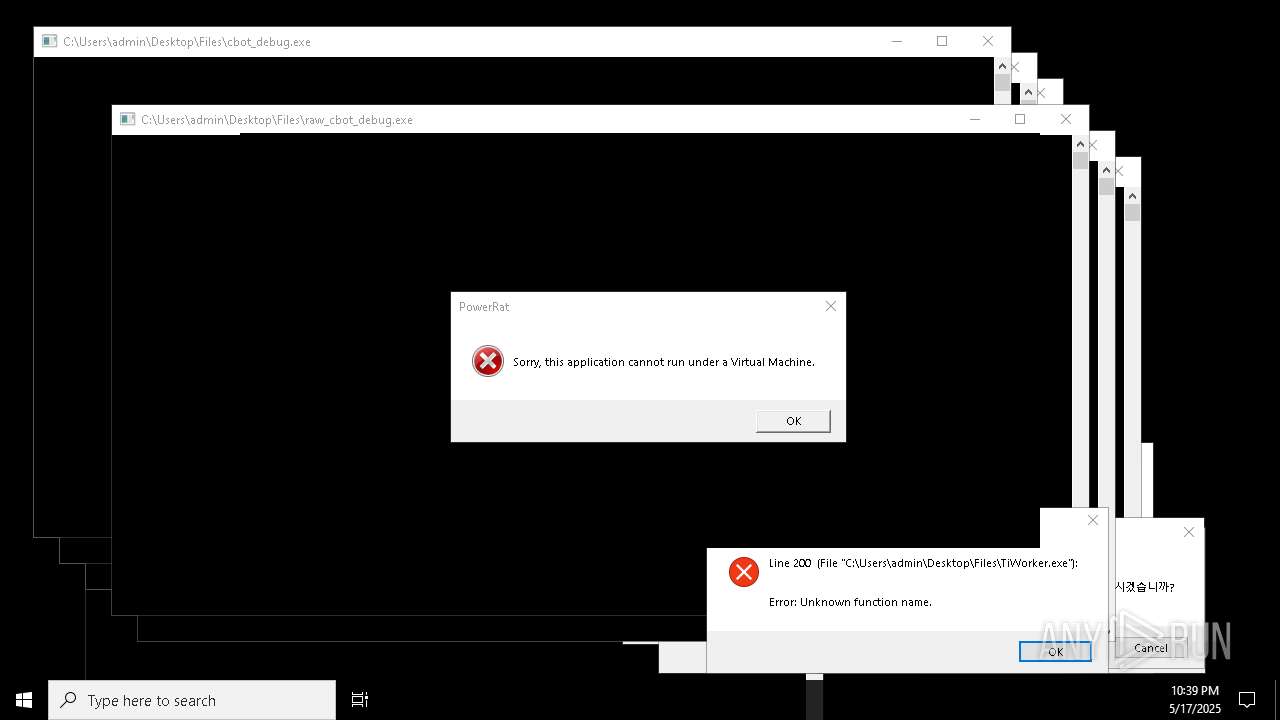
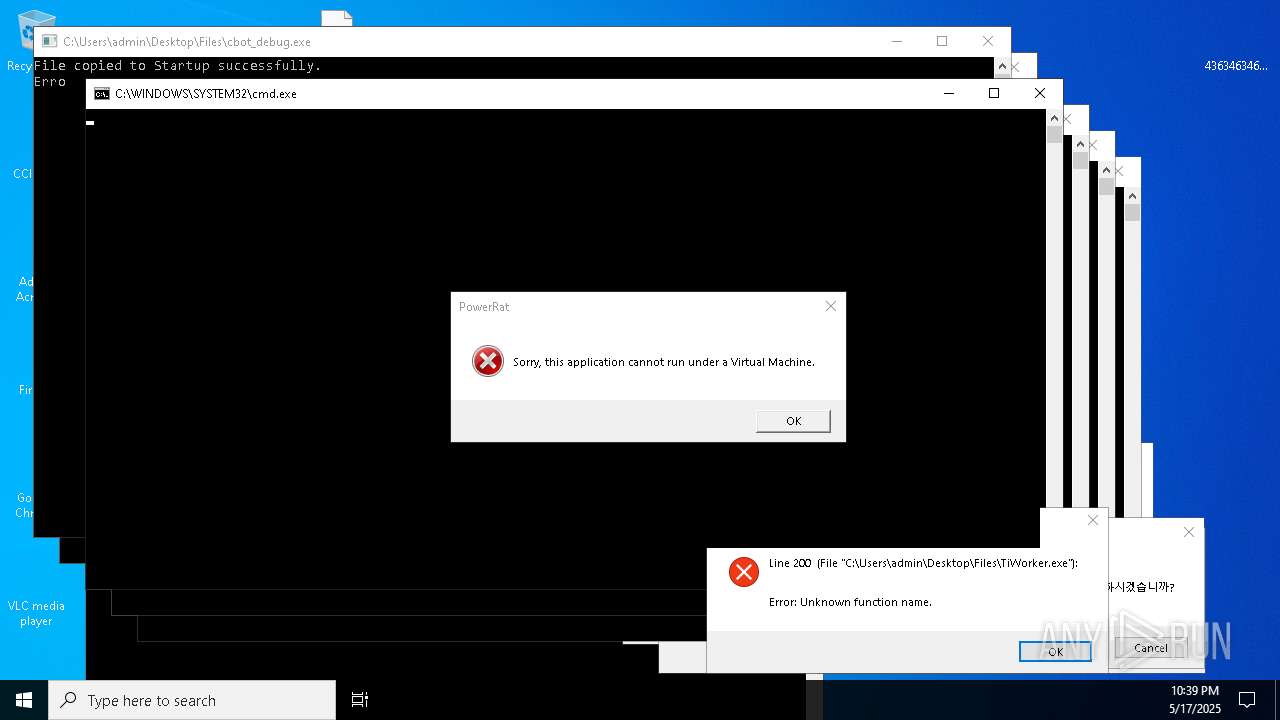
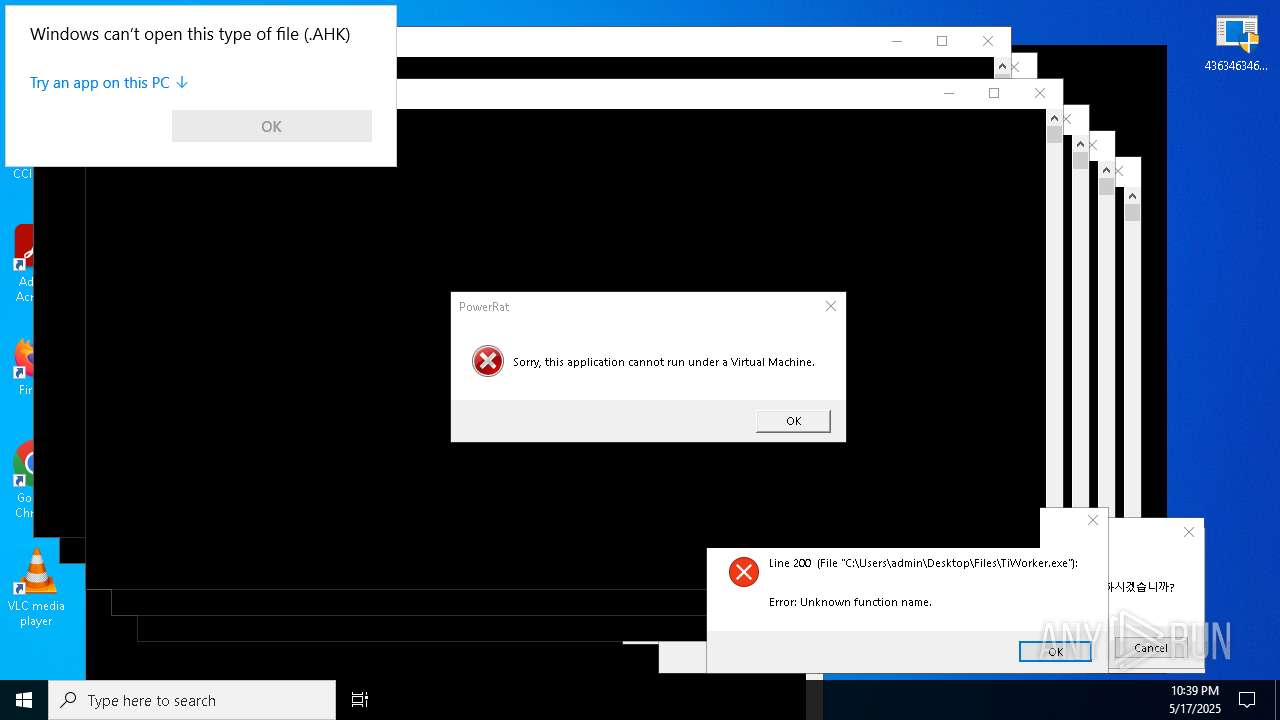
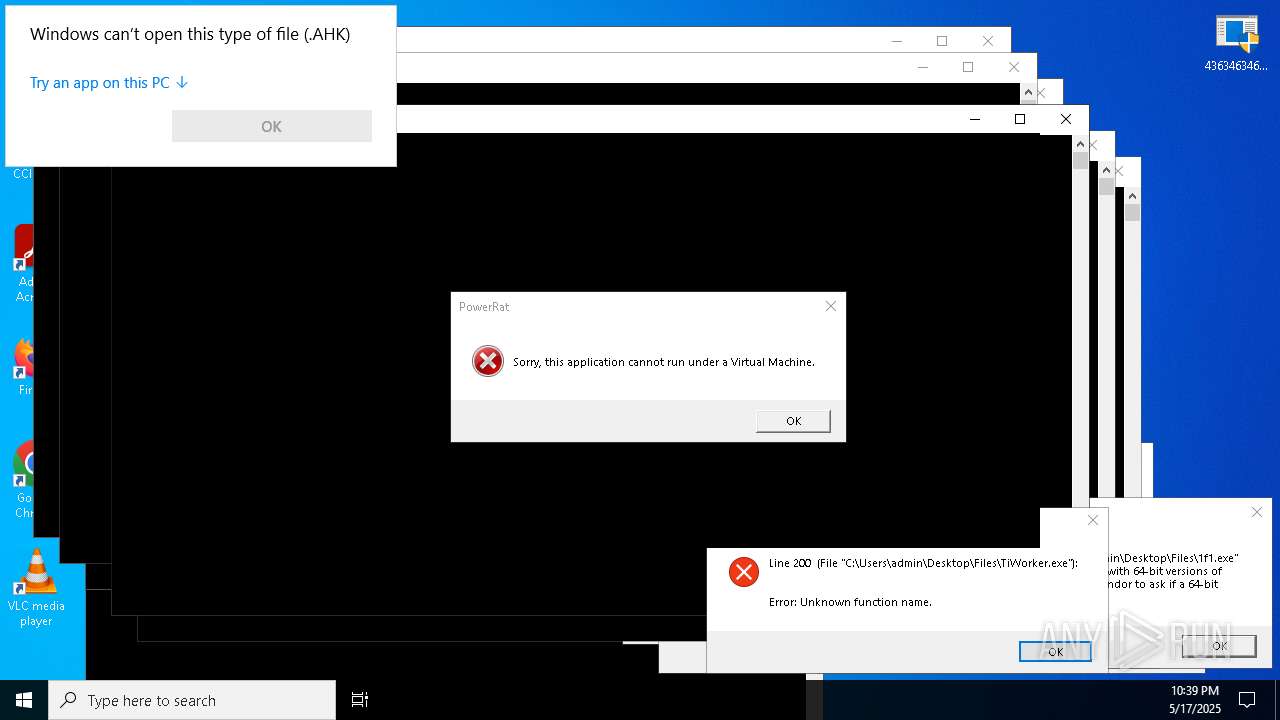
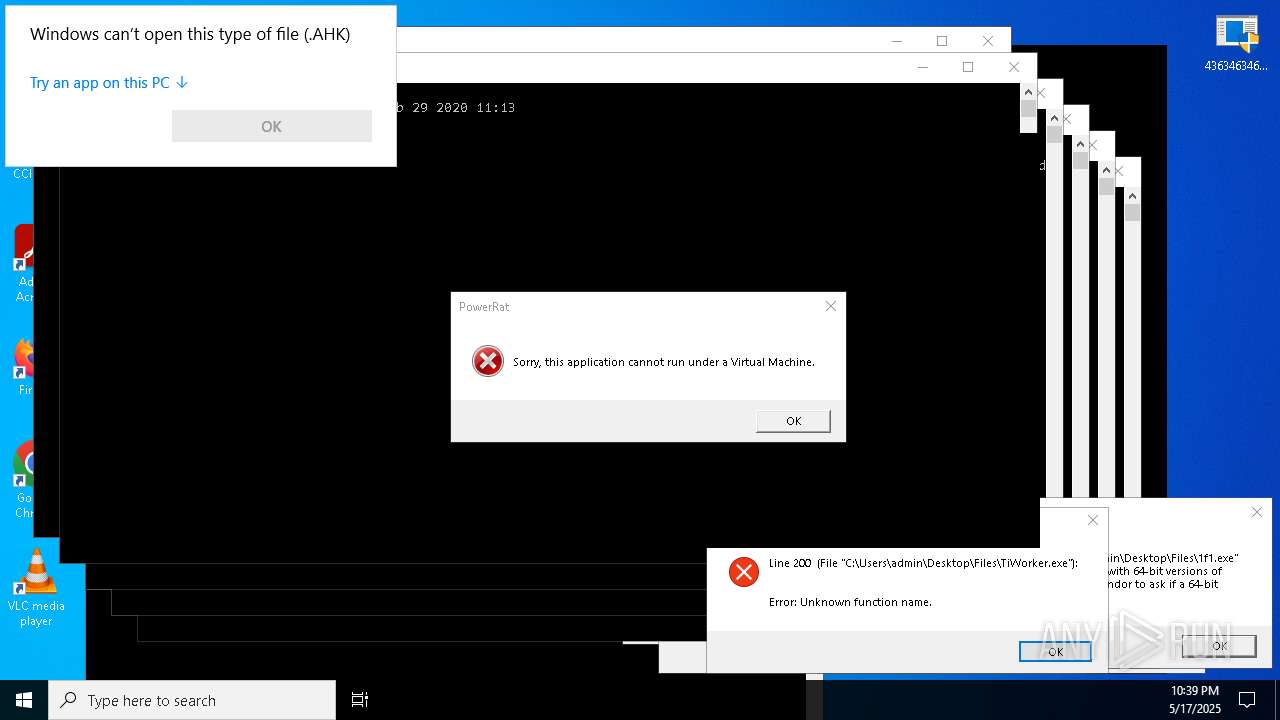
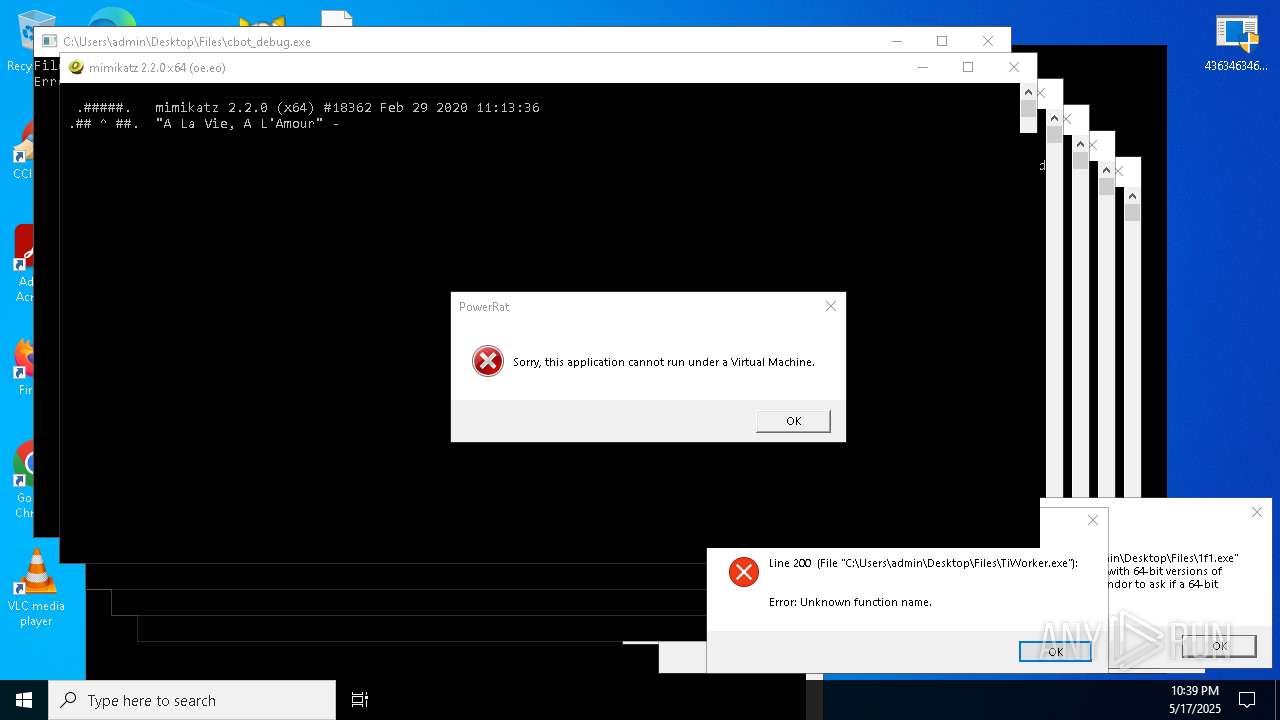
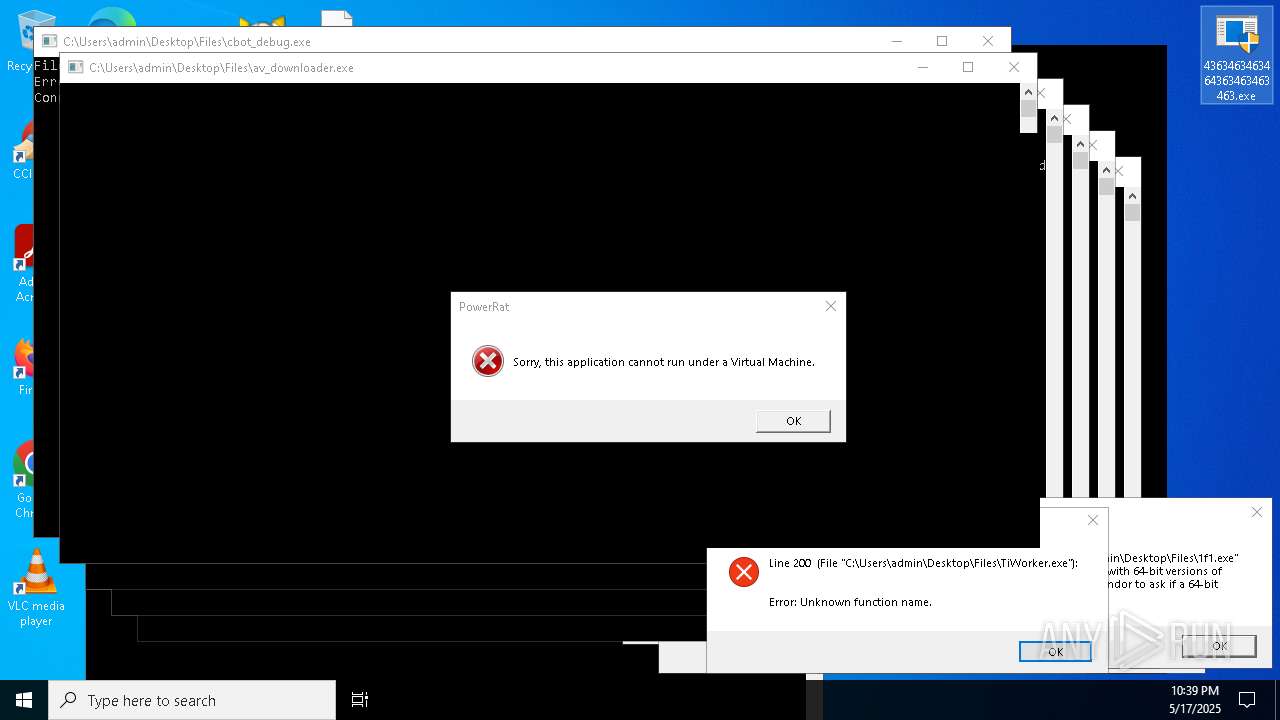
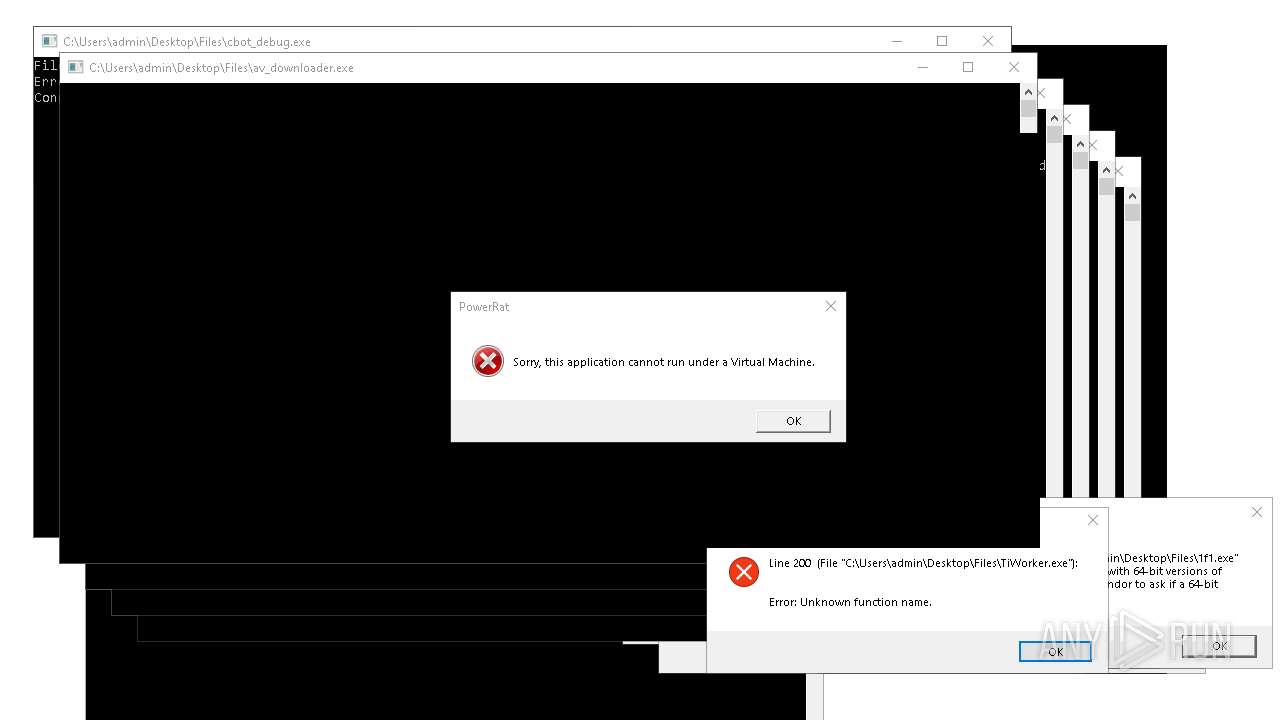
The process checks if it is being run in the virtual environment
- 4363463463464363463463463.exe (PID: 1760)
The process creates files with name similar to system file names
- 4363463463464363463463463.exe (PID: 7592)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 7500)
- 4363463463464363463463463.exe (PID: 8432)
- 4363463463464363463463463.exe (PID: 8748)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 9908)
- 4363463463464363463463463.exe (PID: 10088)
- Steanings.exe (PID: 11104)
- MSystem32.exe (PID: 10772)
- Device2.exe (PID: 9748)
- 4363463463464363463463463.exe (PID: 7156)
- 4363463463464363463463463.exe (PID: 10728)
- 4363463463464363463463463.exe (PID: 8800)
- Discord.exe (PID: 11912)
- aspnet_compiler.exe (PID: 9460)
- Server1.exe (PID: 9768)
- 4363463463464363463463463.exe (PID: 13148)
- svchost.exe (PID: 8940)
- 4363463463464363463463463.exe (PID: 8628)
- svchost.exe (PID: 13468)
- 4363463463464363463463463.exe (PID: 15320)
- benpolatalemdar.exe (PID: 18540)
- 4363463463464363463463463.exe (PID: 14916)
- 4363463463464363463463463.exe (PID: 13000)
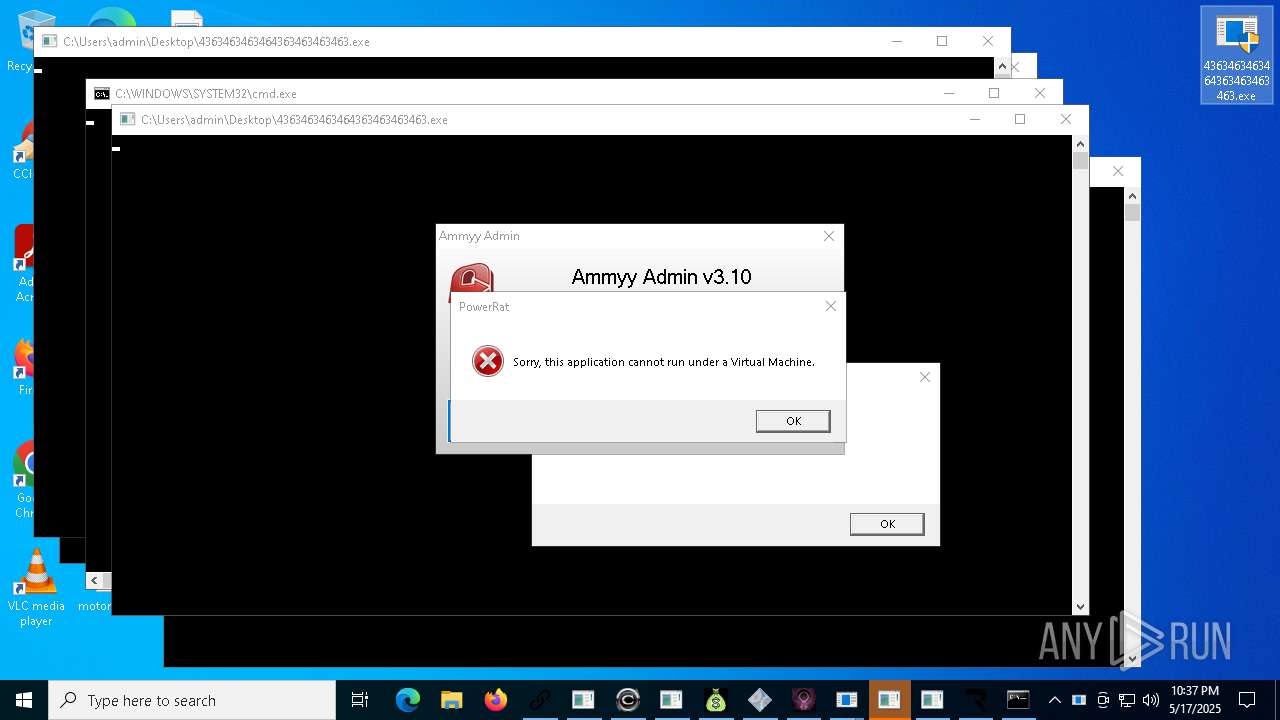
Starts CMD.EXE for commands execution
- Lead.Upload.Report.Feb.2025.exe (PID: 8816)
- ytxgppknsh.exe (PID: 7476)
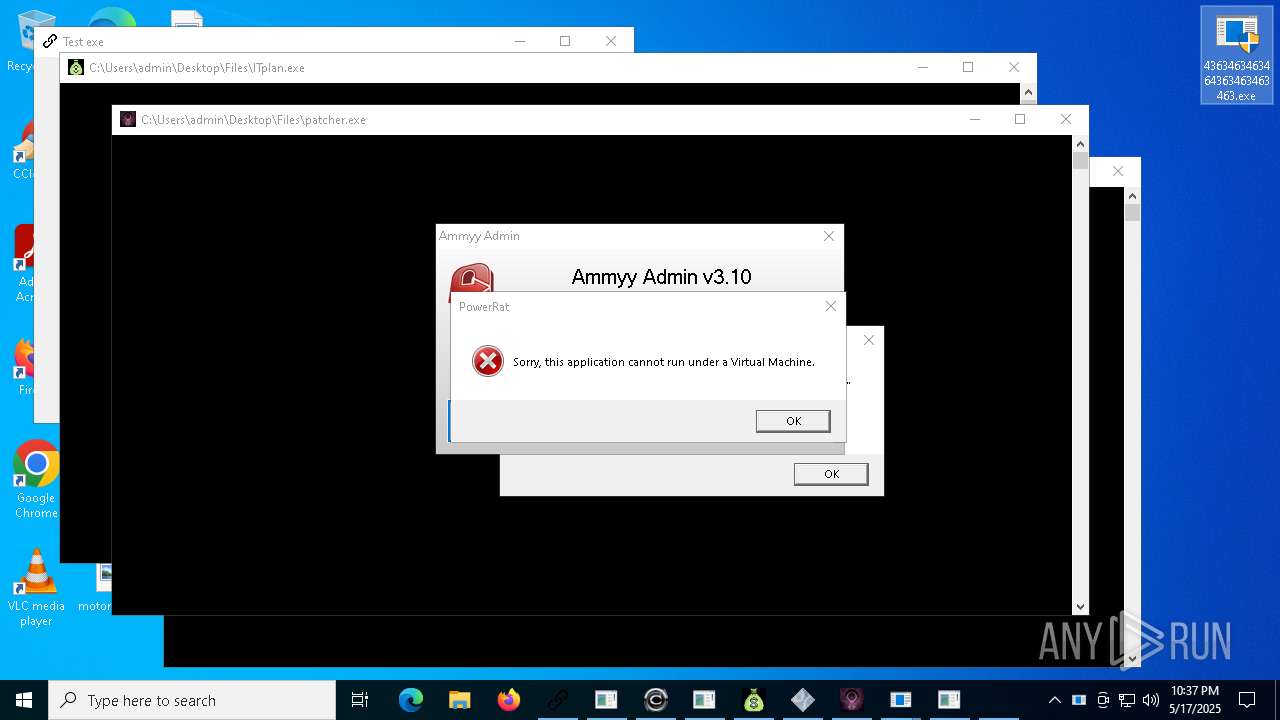
- ITplan.exe (PID: 11812)
- patcher.exe (PID: 11220)
- cheese.exe (PID: 13388)
- FreePhotoShop%20Meme%20Coin%20Packs.exe (PID: 13720)
- Serials_Checker.exe (PID: 14056)
- IMG001.exe (PID: 16756)
- music-play.exe (PID: 18864)
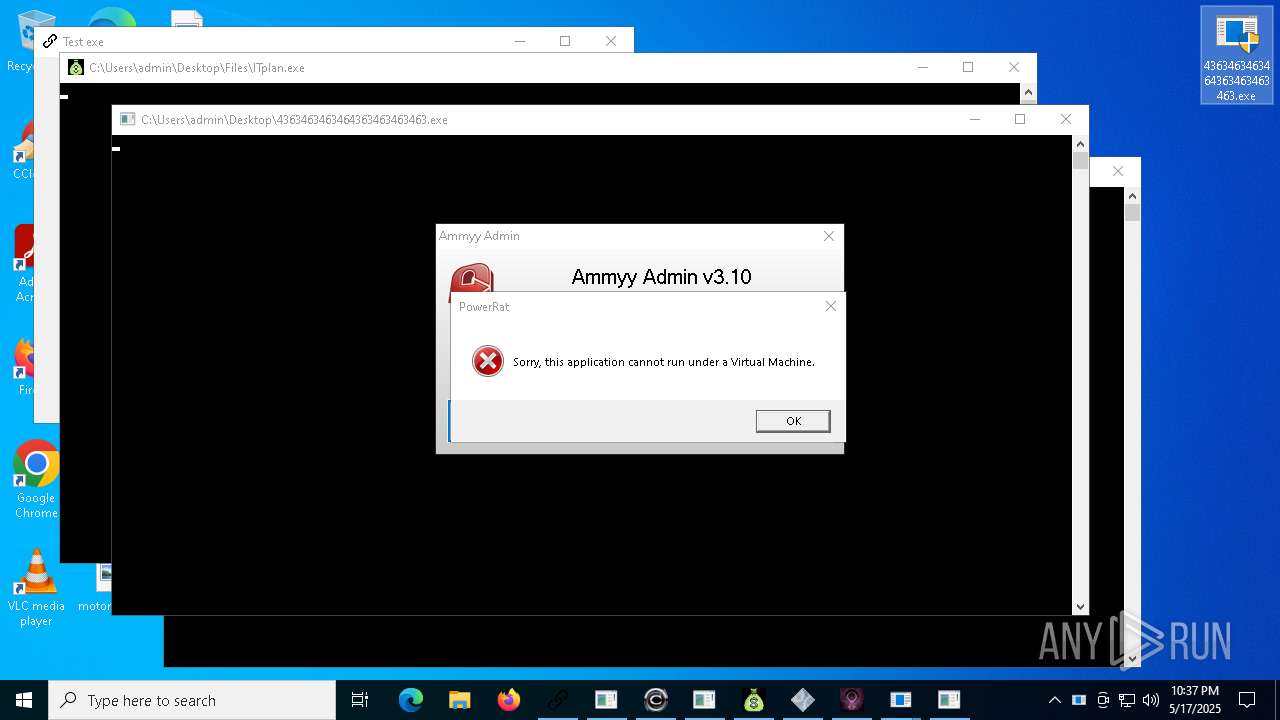
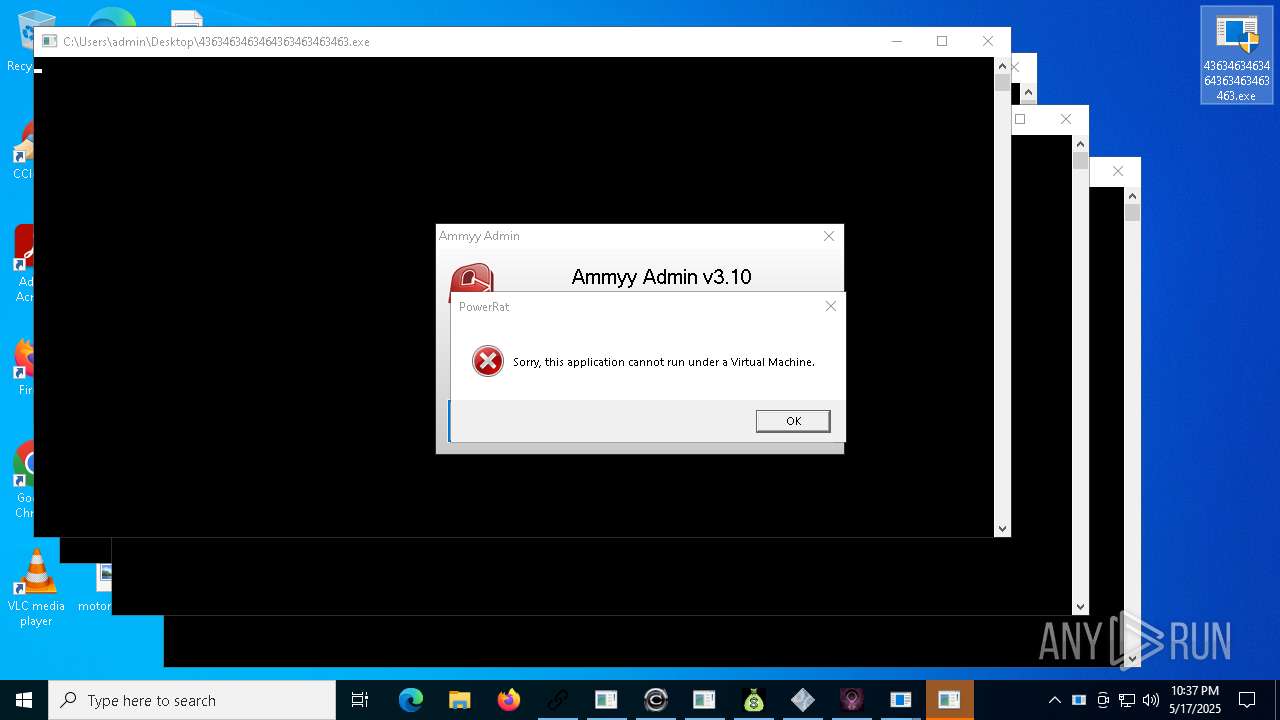
Application launched itself
- alex12112.exe (PID: 9320)
- AA_v3.exe (PID: 13592)
- alex12312.exe (PID: 14944)
- powershell.exe (PID: 10796)
Starts POWERSHELL.EXE for commands execution
- 4363463463464363463463463.exe (PID: 728)
- wscript.exe (PID: 10804)
- XClient.exe (PID: 11480)
- cheese.exe (PID: 13388)
- powershell.exe (PID: 10796)
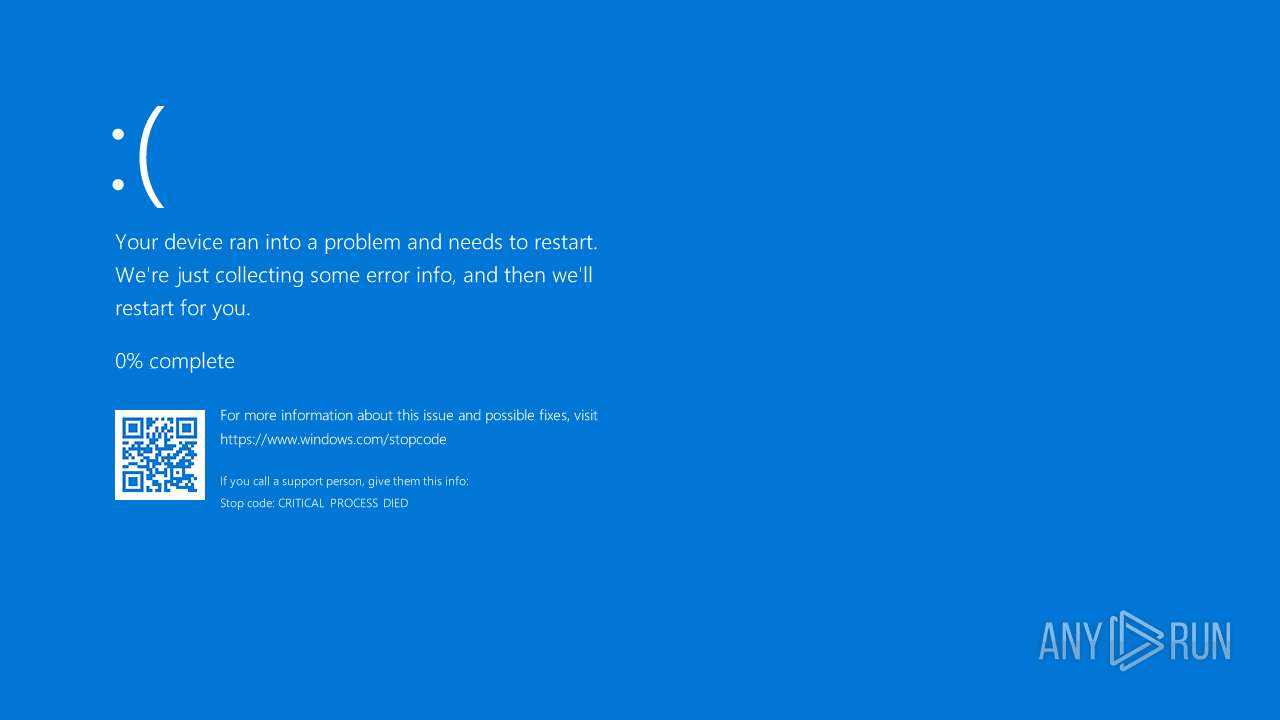
Executes application which crashes
- alex12112.exe (PID: 9320)
- MSBuild.exe (PID: 2096)
- alex12312.exe (PID: 14944)
- %EC%9D%B8%ED%84%B0%EB%84%B7_%EC%A2%85%EB%9F%89%EC%A0%9C_%ED%85%8C%EC%8A%A4%ED%8A%B8-cksal16.exe (PID: 16124)
The process executes VB scripts
- cmd.exe (PID: 8244)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 10804)
Checks for external IP
- svchost.exe (PID: 2196)
- aspnet_compiler.exe (PID: 9460)
- svchost.exe (PID: 8940)
- FreePhotoShop%20Meme%20Coin%20Packs.exe (PID: 13720)
Executing commands from a ".bat" file
- ITplan.exe (PID: 11812)
- patcher.exe (PID: 11220)
- ytxgppknsh.exe (PID: 7476)
- Serials_Checker.exe (PID: 14056)
- music-play.exe (PID: 18864)
Starts SC.EXE for service management
- cmd.exe (PID: 11596)
Windows service management via SC.EXE
- sc.exe (PID: 13184)
Script adds exclusion path to Windows Defender
- XClient.exe (PID: 11480)
- cheese.exe (PID: 13388)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Server1.exe (PID: 9768)
- svchost.exe (PID: 13468)
- Device2.exe (PID: 9748)
- WindowsServices.exe (PID: 13304)
Executes as Windows Service
- AA_v3.exe (PID: 13592)
Multiple wallet extension IDs have been found
- MSBuild.exe (PID: 2096)
Execution of CURL command
- cheese.exe (PID: 13388)
There is functionality for taking screenshot (YARA)
- Client.exe (PID: 5064)
Connects to FTP
- aspnet_compiler.exe (PID: 9460)
Starts application with an unusual extension
- cmd.exe (PID: 13400)
Found IP address in command line
- powershell.exe (PID: 18444)
Probably download files using WebClient
- powershell.exe (PID: 10796)
Contacting a server suspected of hosting an Exploit Kit
- 4363463463464363463463463.exe (PID: 8800)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 13400)
INFO
Checks proxy server information
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 7568)
- 4363463463464363463463463.exe (PID: 7792)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 7224)
Reads the computer name
- 4363463463464363463463463.exe (PID: 1760)
- CleanerV2.exe (PID: 1532)
- Client.exe (PID: 5064)
- MSBuild.exe (PID: 2096)
- MSBuild.exe (PID: 5124)
- update.exe (PID: 1280)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 728)
- ytxgppknsh.exe (PID: 7476)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 7568)
- vmduyldboa.exe (PID: 6676)
- 4363463463464363463463463.exe (PID: 7792)
- update.exe (PID: 7564)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 7224)
- XZCZFS222.exe (PID: 8440)
- 4363463463464363463463463.exe (PID: 8072)
- 4363463463464363463463463.exe (PID: 7500)
Checks supported languages
- 4363463463464363463463463.exe (PID: 1760)
- adsqwe.exe (PID: 6184)
- cron1.exe (PID: 4488)
- CleanerV2.exe (PID: 1532)
- Client.exe (PID: 5064)
- update.exe (PID: 1280)
- MSBuild.exe (PID: 2096)
- MSBuild.exe (PID: 5124)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 1348)
- vmduyldboa.exe (PID: 6676)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 1628)
- kollfdsf.exe (PID: 2420)
- MSBuild.exe (PID: 7456)
- ytxgppknsh.exe (PID: 7476)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7568)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 7792)
- update.exe (PID: 7564)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 7224)
- 4363463463464363463463463.exe (PID: 8072)
- XZCZFS222.exe (PID: 8440)
- 4363463463464363463463463.exe (PID: 7500)
Disables trace logs
- 4363463463464363463463463.exe (PID: 1760)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 7568)
- 4363463463464363463463463.exe (PID: 7792)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7224)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 8072)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 1760)
- CleanerV2.exe (PID: 1532)
- Client.exe (PID: 5064)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 7568)
- 4363463463464363463463463.exe (PID: 7792)
- 4363463463464363463463463.exe (PID: 7412)
- update.exe (PID: 7564)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 7224)
- 4363463463464363463463463.exe (PID: 8072)
- MSBuild.exe (PID: 2096)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 1760)
- update.exe (PID: 1280)
- vmduyldboa.exe (PID: 6676)
- 4363463463464363463463463.exe (PID: 728)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 1760)
- MSBuild.exe (PID: 5124)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 728)
- MSBuild.exe (PID: 7456)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 7568)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7792)
The sample compiled with english language support
- 4363463463464363463463463.exe (PID: 1760)
- update.exe (PID: 1280)
- ytxgppknsh.exe (PID: 7476)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 8800)
- 4363463463464363463463463.exe (PID: 10984)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 8788)
- 4363463463464363463463463.exe (PID: 14308)
- 4363463463464363463463463.exe (PID: 14500)
- 4363463463464363463463463.exe (PID: 10800)
- 4363463463464363463463463.exe (PID: 1348)
- giftorder.exe (PID: 18528)
- 4363463463464363463463463.exe (PID: 7224)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 728)
Reads Environment values
- CleanerV2.exe (PID: 1532)
- Client.exe (PID: 5064)
Creates files or folders in the user directory
- CleanerV2.exe (PID: 1532)
Manual execution by a user
- 4363463463464363463463463.exe (PID: 1532)
- 4363463463464363463463463.exe (PID: 4620)
- 4363463463464363463463463.exe (PID: 2552)
- 4363463463464363463463463.exe (PID: 6944)
- 4363463463464363463463463.exe (PID: 6148)
- 4363463463464363463463463.exe (PID: 1628)
- 4363463463464363463463463.exe (PID: 728)
- 4363463463464363463463463.exe (PID: 856)
- 4363463463464363463463463.exe (PID: 5964)
- 4363463463464363463463463.exe (PID: 1328)
- 4363463463464363463463463.exe (PID: 7240)
- 4363463463464363463463463.exe (PID: 1348)
- 4363463463464363463463463.exe (PID: 7568)
- 4363463463464363463463463.exe (PID: 7592)
- 4363463463464363463463463.exe (PID: 7612)
- 4363463463464363463463463.exe (PID: 7792)
- 4363463463464363463463463.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 7756)
- 4363463463464363463463463.exe (PID: 7856)
- 4363463463464363463463463.exe (PID: 7868)
- 4363463463464363463463463.exe (PID: 8124)
- 4363463463464363463463463.exe (PID: 7412)
- 4363463463464363463463463.exe (PID: 5360)
- 4363463463464363463463463.exe (PID: 7228)
- 4363463463464363463463463.exe (PID: 7500)
- 4363463463464363463463463.exe (PID: 7320)
- 4363463463464363463463463.exe (PID: 8072)
- 4363463463464363463463463.exe (PID: 7224)
- 4363463463464363463463463.exe (PID: 8200)
- 4363463463464363463463463.exe (PID: 7560)
- 4363463463464363463463463.exe (PID: 7500)
- 4363463463464363463463463.exe (PID: 8232)
- 4363463463464363463463463.exe (PID: 8272)
- 4363463463464363463463463.exe (PID: 8340)
- 4363463463464363463463463.exe (PID: 8432)
- 4363463463464363463463463.exe (PID: 8740)
- 4363463463464363463463463.exe (PID: 8748)
- 4363463463464363463463463.exe (PID: 8800)
- 4363463463464363463463463.exe (PID: 8824)
- 4363463463464363463463463.exe (PID: 8896)
- 4363463463464363463463463.exe (PID: 9024)
- 4363463463464363463463463.exe (PID: 9124)
- 4363463463464363463463463.exe (PID: 8628)
- 4363463463464363463463463.exe (PID: 9156)
- 4363463463464363463463463.exe (PID: 8788)
- 4363463463464363463463463.exe (PID: 8364)
- 4363463463464363463463463.exe (PID: 8892)
- 4363463463464363463463463.exe (PID: 9244)
- 4363463463464363463463463.exe (PID: 9252)
- 4363463463464363463463463.exe (PID: 9272)
- 4363463463464363463463463.exe (PID: 9300)
- 4363463463464363463463463.exe (PID: 10172)
- 4363463463464363463463463.exe (PID: 10096)
- 4363463463464363463463463.exe (PID: 9900)
- 4363463463464363463463463.exe (PID: 9804)
- 4363463463464363463463463.exe (PID: 9824)
- 4363463463464363463463463.exe (PID: 9908)
- 4363463463464363463463463.exe (PID: 9988)
- 4363463463464363463463463.exe (PID: 10088)
- 4363463463464363463463463.exe (PID: 10076)
- 4363463463464363463463463.exe (PID: 10124)
- 4363463463464363463463463.exe (PID: 10108)
- 4363463463464363463463463.exe (PID: 10200)
- 4363463463464363463463463.exe (PID: 10428)
- 4363463463464363463463463.exe (PID: 10416)
- 4363463463464363463463463.exe (PID: 10792)
- 4363463463464363463463463.exe (PID: 10436)
- 4363463463464363463463463.exe (PID: 10728)
- 4363463463464363463463463.exe (PID: 10512)
- 4363463463464363463463463.exe (PID: 10744)
- 4363463463464363463463463.exe (PID: 10764)
- 4363463463464363463463463.exe (PID: 10728)
- 4363463463464363463463463.exe (PID: 9472)
- 4363463463464363463463463.exe (PID: 7156)
- 4363463463464363463463463.exe (PID: 7928)
- 4363463463464363463463463.exe (PID: 10984)
- 4363463463464363463463463.exe (PID: 10608)
- 4363463463464363463463463.exe (PID: 9924)
- 4363463463464363463463463.exe (PID: 10776)
- 4363463463464363463463463.exe (PID: 10908)
- 4363463463464363463463463.exe (PID: 11064)
- 4363463463464363463463463.exe (PID: 10836)
- 4363463463464363463463463.exe (PID: 10976)
- 4363463463464363463463463.exe (PID: 12244)
- 4363463463464363463463463.exe (PID: 12216)
- 4363463463464363463463463.exe (PID: 12028)
- 4363463463464363463463463.exe (PID: 12272)
- 4363463463464363463463463.exe (PID: 968)
- 4363463463464363463463463.exe (PID: 10220)
- 4363463463464363463463463.exe (PID: 10684)
- 4363463463464363463463463.exe (PID: 10800)
- 4363463463464363463463463.exe (PID: 9348)
- 4363463463464363463463463.exe (PID: 12448)
- 4363463463464363463463463.exe (PID: 11784)
- 4363463463464363463463463.exe (PID: 11432)
- 4363463463464363463463463.exe (PID: 13148)
- 4363463463464363463463463.exe (PID: 13260)
- 4363463463464363463463463.exe (PID: 11000)
- 4363463463464363463463463.exe (PID: 12100)
- 4363463463464363463463463.exe (PID: 13208)
- 4363463463464363463463463.exe (PID: 6136)
- 4363463463464363463463463.exe (PID: 12980)
- 4363463463464363463463463.exe (PID: 9884)
- 4363463463464363463463463.exe (PID: 12216)
- 4363463463464363463463463.exe (PID: 12552)
- 4363463463464363463463463.exe (PID: 12988)
- 4363463463464363463463463.exe (PID: 14064)
- 4363463463464363463463463.exe (PID: 10300)
- 4363463463464363463463463.exe (PID: 13484)
- 4363463463464363463463463.exe (PID: 11976)
- 4363463463464363463463463.exe (PID: 13000)
- 4363463463464363463463463.exe (PID: 13768)
- 4363463463464363463463463.exe (PID: 13740)
- 4363463463464363463463463.exe (PID: 14308)
- 4363463463464363463463463.exe (PID: 13804)
- 4363463463464363463463463.exe (PID: 14500)
- 4363463463464363463463463.exe (PID: 12140)
- 4363463463464363463463463.exe (PID: 6760)
- 4363463463464363463463463.exe (PID: 12396)
- 4363463463464363463463463.exe (PID: 13192)
- 4363463463464363463463463.exe (PID: 13396)
- 4363463463464363463463463.exe (PID: 15208)
- 4363463463464363463463463.exe (PID: 15252)
- 4363463463464363463463463.exe (PID: 15220)
- 4363463463464363463463463.exe (PID: 15264)
- 4363463463464363463463463.exe (PID: 14916)
- 4363463463464363463463463.exe (PID: 14992)
- 4363463463464363463463463.exe (PID: 15068)
- 4363463463464363463463463.exe (PID: 15200)
- 4363463463464363463463463.exe (PID: 6584)
- 4363463463464363463463463.exe (PID: 15320)
- 4363463463464363463463463.exe (PID: 15328)
- 4363463463464363463463463.exe (PID: 15340)
- 4363463463464363463463463.exe (PID: 12188)
- 4363463463464363463463463.exe (PID: 15904)
- 4363463463464363463463463.exe (PID: 16132)
- 4363463463464363463463463.exe (PID: 16144)
- 4363463463464363463463463.exe (PID: 16352)
- 4363463463464363463463463.exe (PID: 16268)
- 4363463463464363463463463.exe (PID: 15912)
- 4363463463464363463463463.exe (PID: 15960)
- 4363463463464363463463463.exe (PID: 16220)
- 4363463463464363463463463.exe (PID: 16228)
- 4363463463464363463463463.exe (PID: 15256)
- 4363463463464363463463463.exe (PID: 15840)
- 4363463463464363463463463.exe (PID: 11728)
- 4363463463464363463463463.exe (PID: 12740)
- 4363463463464363463463463.exe (PID: 16512)
- 4363463463464363463463463.exe (PID: 16792)
- 4363463463464363463463463.exe (PID: 16784)
- 4363463463464363463463463.exe (PID: 17180)
- 4363463463464363463463463.exe (PID: 17208)
- 4363463463464363463463463.exe (PID: 14904)
- 4363463463464363463463463.exe (PID: 13456)
- 4363463463464363463463463.exe (PID: 208)
- 4363463463464363463463463.exe (PID: 15080)
- 4363463463464363463463463.exe (PID: 15900)
- 4363463463464363463463463.exe (PID: 6584)
- 4363463463464363463463463.exe (PID: 2332)
- 4363463463464363463463463.exe (PID: 17956)
- 4363463463464363463463463.exe (PID: 18116)
- 4363463463464363463463463.exe (PID: 18124)
- 4363463463464363463463463.exe (PID: 18236)
- 4363463463464363463463463.exe (PID: 17972)
- 4363463463464363463463463.exe (PID: 18376)
- 4363463463464363463463463.exe (PID: 16984)
- 4363463463464363463463463.exe (PID: 17892)
- 4363463463464363463463463.exe (PID: 18176)
- 4363463463464363463463463.exe (PID: 18180)
- 4363463463464363463463463.exe (PID: 19088)
- 4363463463464363463463463.exe (PID: 19124)
- 4363463463464363463463463.exe (PID: 19156)
- 4363463463464363463463463.exe (PID: 19164)
- 4363463463464363463463463.exe (PID: 19228)
- 4363463463464363463463463.exe (PID: 19268)
- 4363463463464363463463463.exe (PID: 19824)
- 4363463463464363463463463.exe (PID: 19920)
Create files in a temporary directory
- update.exe (PID: 1280)
Executes as Windows Service
- SearchIndexer.exe (PID: 7676)
Creates files in the program directory
- SearchIndexer.exe (PID: 7676)
Execution of CURL command
- cmd.exe (PID: 13144)
- cmd.exe (PID: 13608)
The sample compiled with korean language support
- 4363463463464363463463463.exe (PID: 10088)
Changes the display of characters in the console
- cmd.exe (PID: 13400)
Drops a (possible) Coronavirus decoy
- 4363463463464363463463463.exe (PID: 8788)
The sample compiled with polish language support
- 4363463463464363463463463.exe (PID: 10088)
Starts MODE.COM to configure console settings
- mode.com (PID: 20276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
StormKitty
(PID) Process(2096) MSBuild.exe
C2 (1)95.216.115.242
Ports (1)9090
VersionRAT + hVNC 6.0.8
Options
AutoRunfalse
Mutextmlqlqxozhv
InstallFolder%PreLoadSQLite_TargetFramework%
Certificates
Cert1MIICLjCCAZegAwIBAgIVANZXxu6AsB29WvppNGNmRvzME7YnMA0GCSqGSIb3DQEBDQUAMGIxFTATBgNVBAMMDFZlbm9tIFNlcnZlcjESMBAGA1UECwwJYWxleGVpa3VuMRswGQYDVQQKDBJWZW5vbSBCeSBhbGV4ZWlrdW4xCzAJBgNVBAcMAlNIMQswCQYDVQQGEwJDTjAeFw0yNDA2MjEyMTQ5NThaFw0zNTAzMzEyMTQ5NThaMBAxDjAMBgNVBAMMBVZlbm9tMIGfMA0GCSqGSIb3DQEBAQUAA4GNADCB...
Server_SignaturesAbSyM/pwaiqfJqgAZOGMzUAG6XwCy/fSpMLxPGrhfH6Ri++mOAfR5mR0wjiZcKrDspdBKx7G/KA5S2cS4V1Ntggz7Epe5Z+8VMUVh5/yYOOOt26KJEJSk1ekAEzj2DF/sU5nCogmVEDUQbVa2Ux7RNaSevyw1V66ZeiGaLRgcQ=
Keys
AES31756a88379c06d8d9abc7916a9a193996e943f6e97353e572a24dd0ccaf9dd9
SaltVenomRATByVenom
Quasar
(PID) Process(5064) Client.exe
Version1.4.1
C2 (2)192.168.4.185:4782
Sub_DirSubDir
Install_NameClient.exe
Mutex1607a026-352e-4041-bc1f-757dd6cd2e95
StartupCleanerV2
TagCleanerV2
LogDirClean
SignatureaRogJrq9hUhroi2yRCxFCfE+mXc/GvQG7eVh7ArjCeuURH+zboKSDt31Wff+SIInkno4hIQs7tRc6uLFL+H8LqKGy5JPvKlBVH/vsLgQMz2Hri+jlAj+4J5ZX0Qs23sz7UqIoRbwMHdNzuyTEDKHt/bsObNt8K+mybe50A+4iIlVs0lofsrxI8a8dSh5IxFx4M80uR9L+SGmloN53TuHqrpUrdi65VcSjCa61BUkfKqpOiJaQqZ9zqC/rXbMAu0KTssZ9Nlucysj04DgLCV83TfJfpVpZerpVLZvUsSr/BiW...
CertificateMIIE9DCCAtygAwIBAgIQAOw5PfKqmSNRWe7n9URebzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDYzMDExMjUxNFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAq68uWSLSM7tj6l08I9iy5ilFsS9PluFC5ENWxT8Kmp0gDJD1br0B0Nr+ZIofw9ykVSR9kDvk...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
703
Monitored processes
481
Malicious processes
64
Suspicious processes
18
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\Desktop\4363463463464363463463463.exe" | C:\Users\admin\Desktop\4363463463464363463463463.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 664 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | adsqwe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 672 | C:\Users\admin\AppData\Roaming\Oracle\javaplatform.exe | C:\Users\admin\AppData\Roaming\Oracle\javaplatform.exe | bot.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 728 | "C:\Users\admin\Desktop\4363463463464363463463463.exe" | C:\Users\admin\Desktop\4363463463464363463463463.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 744 | "c:\program files (x86)\internet explorer\iexplore.exe" | C:\Program Files (x86)\Internet Explorer\iexplore.exe | — | rea.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Users\admin\Desktop\4363463463464363463463463.exe" | C:\Users\admin\Desktop\4363463463464363463463463.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\Users\admin\Desktop\4363463463464363463463463.exe" | C:\Users\admin\Desktop\4363463463464363463463463.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 1280 | "C:\Users\admin\Desktop\Files\update.exe" | C:\Users\admin\Desktop\Files\update.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\Desktop\4363463463464363463463463.exe" | C:\Users\admin\Desktop\4363463463464363463463463.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
151 117
Read events
150 830
Write events
248
Delete events
39
Modification events
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1760) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
140
Suspicious files
48
Text files
43
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7676 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Windows.edb | — | |
MD5:— | SHA256:— | |||
| 1760 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\update.exe | binary | |
MD5:5AFCB4C2E736EBD78C92A7C50587F3D6 | SHA256:A7C4E301417D4DC2E8DCB04924432D32CD08862E36720BDCBE078C67564EF545 | |||
| 1760 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\cron1.exe | executable | |
MD5:9940C3F537CE81F8552C1932533EFF6B | SHA256:63BAED48106A805A1758D3CEDDF73ABAC873925483AF8A8436BE5FD6EF92D7E7 | |||
| 1532 | CleanerV2.exe | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | executable | |
MD5:E6AEB08AE65E312D03F1092DF3BA422C | SHA256:74FC53844845B75A441D394B74932CAA7C7AD583E091EC0521C78EBAD718100E | |||
| 6148 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\Lead.Upload.Report.Feb.2025.exe | executable | |
MD5:6CA1D8895E299EA630A4673213536564 | SHA256:A734FE104A195867D9EE77F75DE288B7FC58435761EE2DBA4EDE88095CA0B554 | |||
| 7592 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\svchost.exe | executable | |
MD5:35DE149D3C81727EA4CCE81A09F08581 | SHA256:1803C1F48E626B2EC0E2620649D818EBF546BFE58DFFDDFBAD224F20A8106BA0 | |||
| 1760 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\CleanerV2.exe | executable | |
MD5:E6AEB08AE65E312D03F1092DF3BA422C | SHA256:74FC53844845B75A441D394B74932CAA7C7AD583E091EC0521C78EBAD718100E | |||
| 1760 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\kollfdsf.exe | executable | |
MD5:B3D5B12B5A8975EA11A53DFE3589DAA0 | SHA256:59774180353DD5CF48C73B66D0675AFE2A04408F0888595C85A9F6495CAA79FC | |||
| 1280 | update.exe | C:\Users\admin\AppData\Local\Temp\vmduyldboa.exe | executable | |
MD5:E48B89715BF5E4C55EB5A1FED67865D9 | SHA256:C25D90168FC2026D8ED2A69C066BD5A7E11004C3899928A7DB24CB7636FC4D9E | |||
| 1760 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\adsqwe.exe | executable | |
MD5:44C6626441548E0115B35014FCDC9ED2 | SHA256:0A3A0C19A18AD4EA4AB933CA094B21BBF2DB42E2A602ABC7D3D00D37B43C305D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
212
TCP/UDP connections
4 528
DNS requests
636
Threats
975
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1760 | 4363463463464363463463463.exe | GET | 301 | 140.82.121.3:80 | http://github.com/skibidisigmer/FNcleanerV2/releases/download/CleanerV2/CleanerV2.exe | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1760 | 4363463463464363463463463.exe | GET | 200 | 168.138.162.78:80 | http://168.138.162.78/output0/client/update.exe | unknown | — | — | unknown |
728 | 4363463463464363463463463.exe | GET | 200 | 176.65.144.23:80 | http://176.65.144.23/HOST/XZCZFS222.exe | unknown | — | — | malicious |
7592 | 4363463463464363463463463.exe | GET | 301 | 140.82.121.3:80 | http://github.com/charshop/sigma-nonrat/raw/main/svchost.exe | unknown | — | — | whitelisted |
7612 | 4363463463464363463463463.exe | GET | 301 | 140.82.121.3:80 | http://github.com/Deroxs/PowerRat-leak/raw/refs/heads/main/PowerRat.exe | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1760 | 4363463463464363463463463.exe | 151.101.2.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
1760 | 4363463463464363463463463.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
1760 | 4363463463464363463463463.exe | 185.199.110.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1760 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1760 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
1760 | 4363463463464363463463463.exe | Misc activity | ET INFO Packed Executable Download |
1760 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1760 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
1760 | 4363463463464363463463463.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (orjinalecza .net) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (tortoisgfe .top) |
5124 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (orjinalecza .net) in TLS SNI |