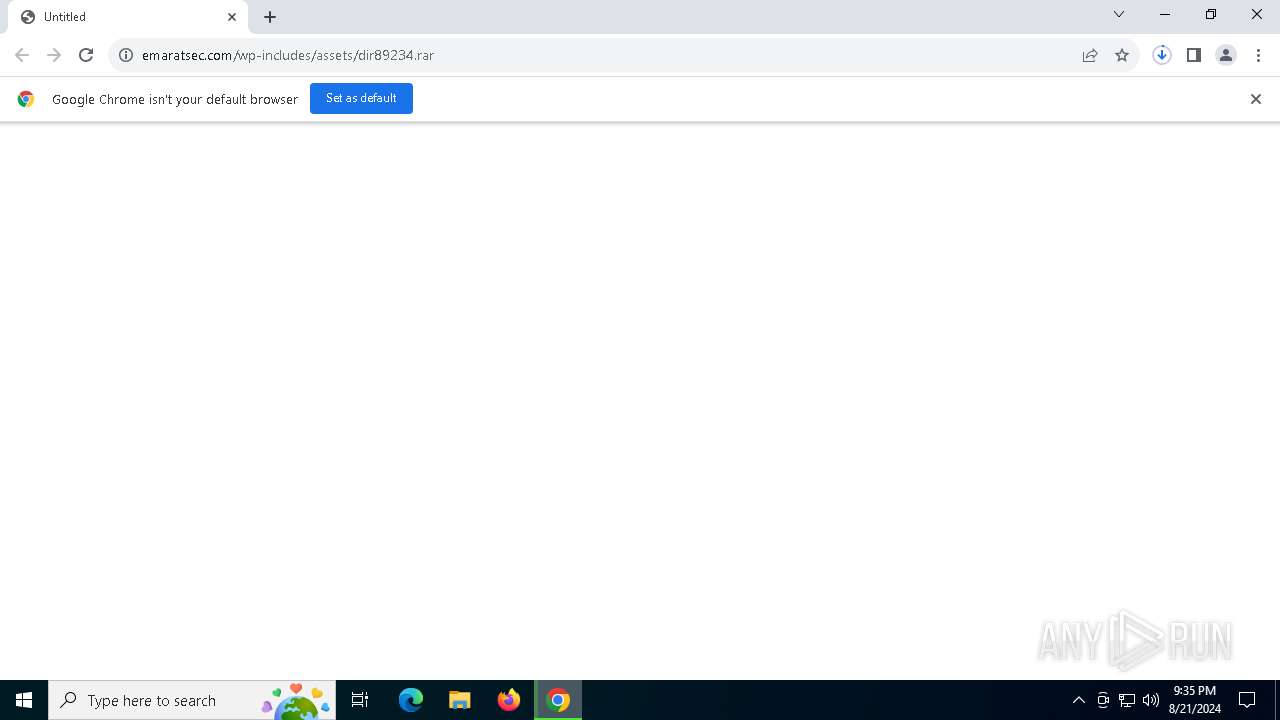
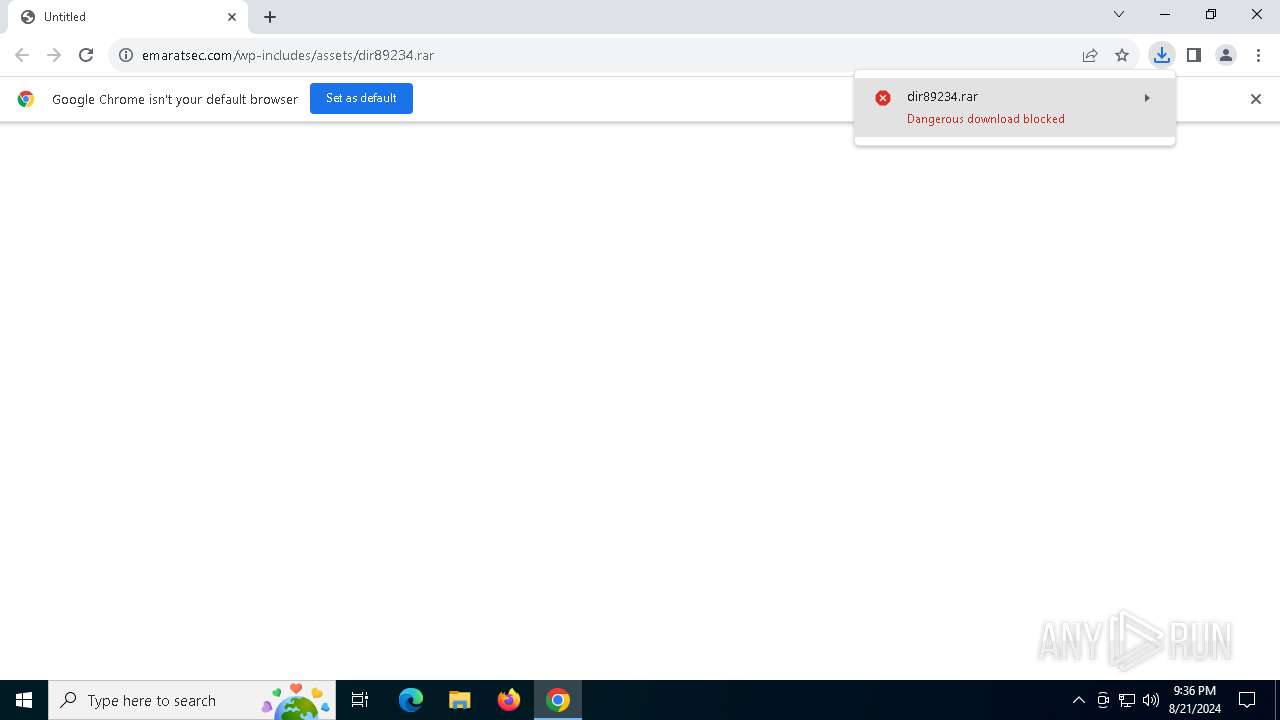
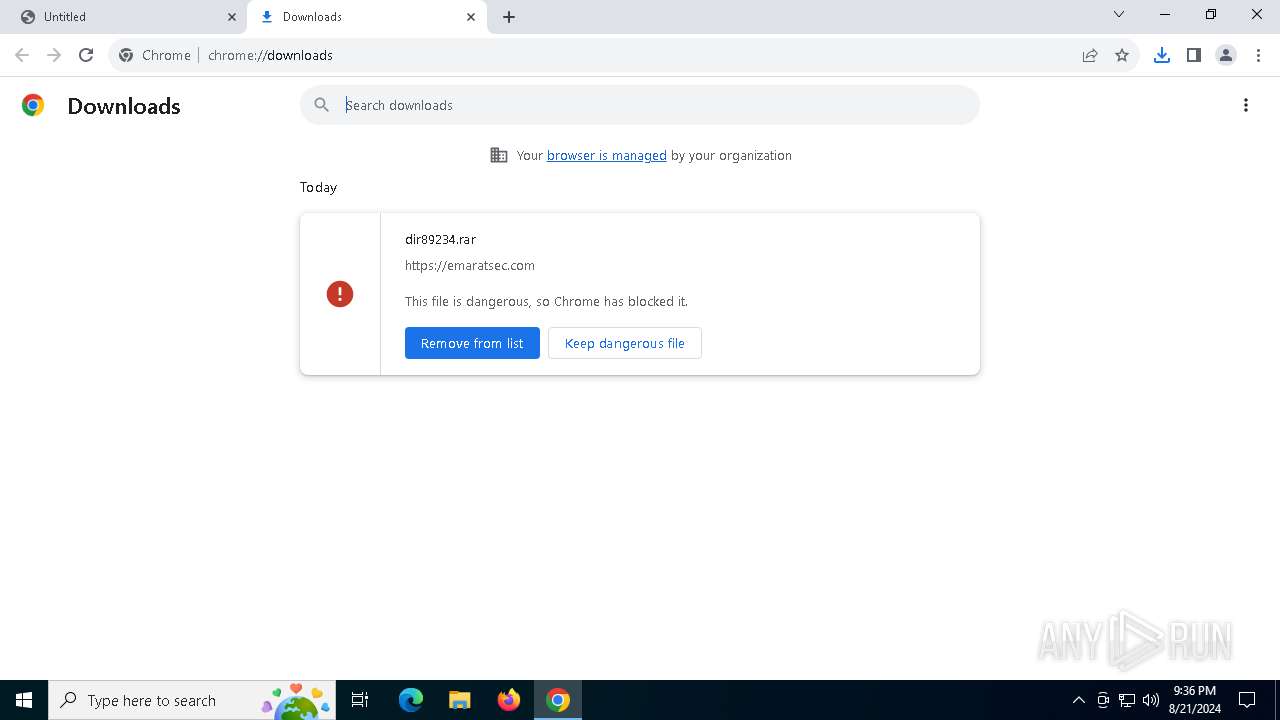
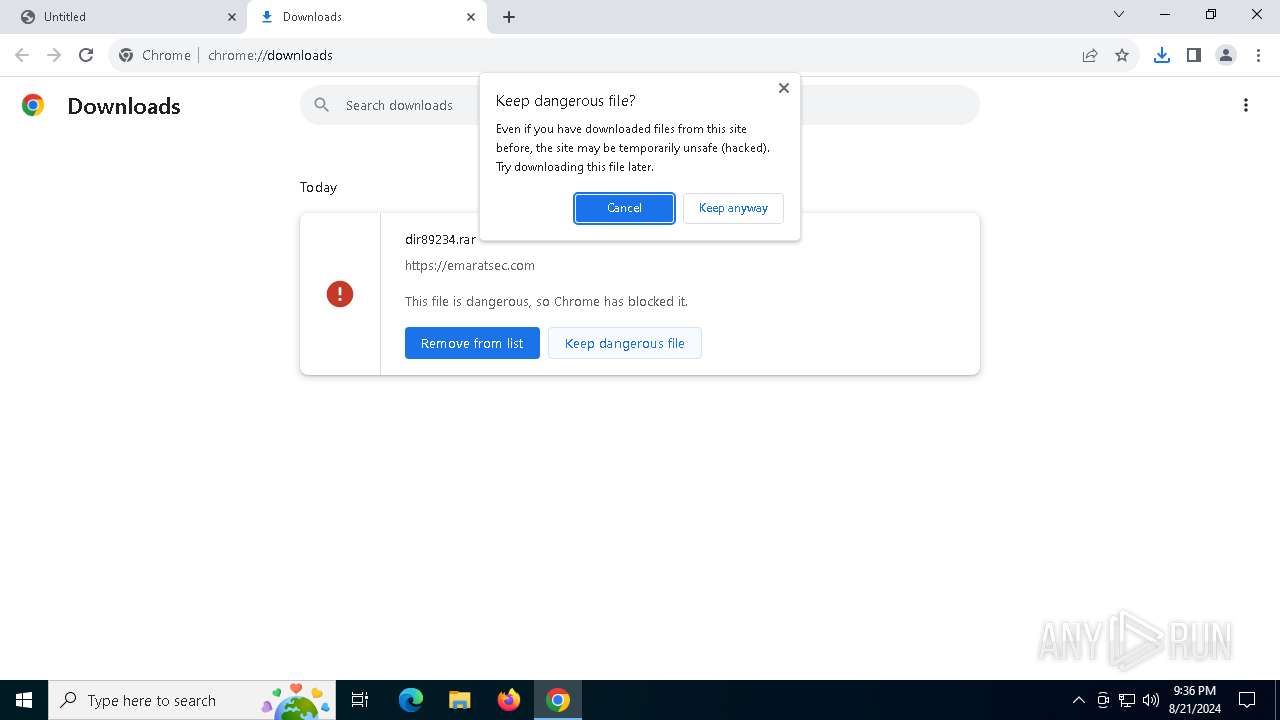
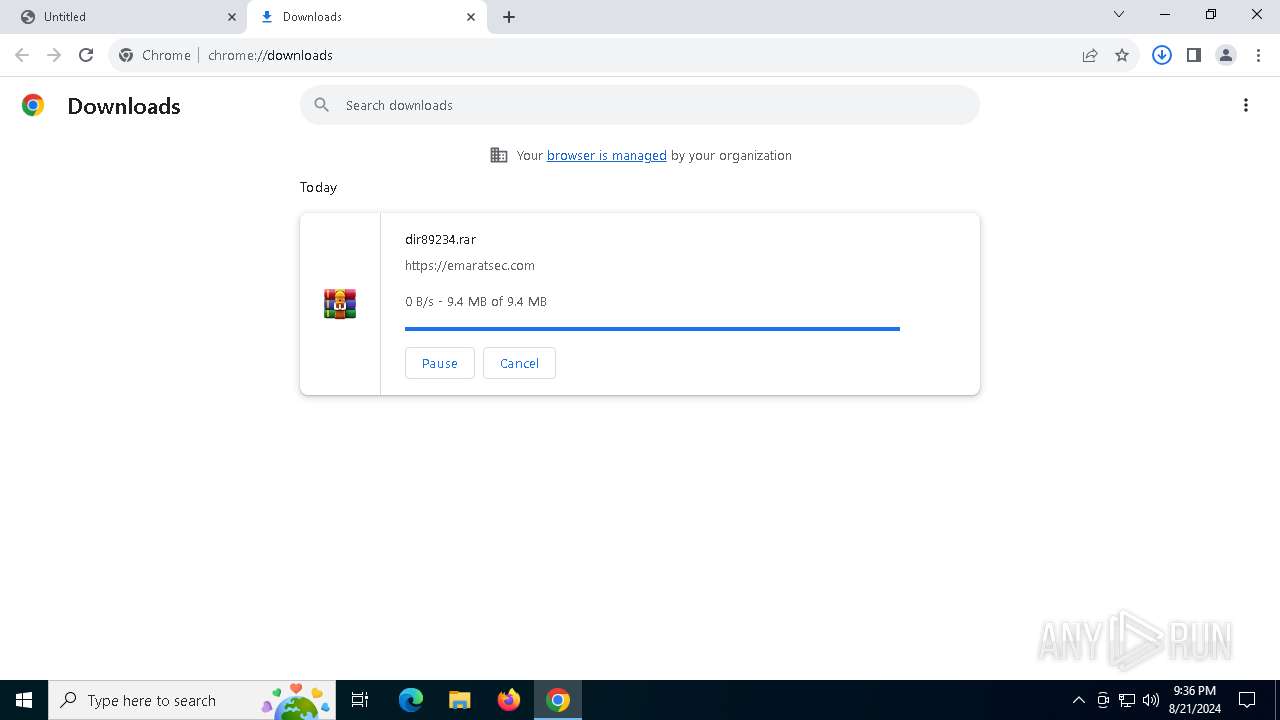
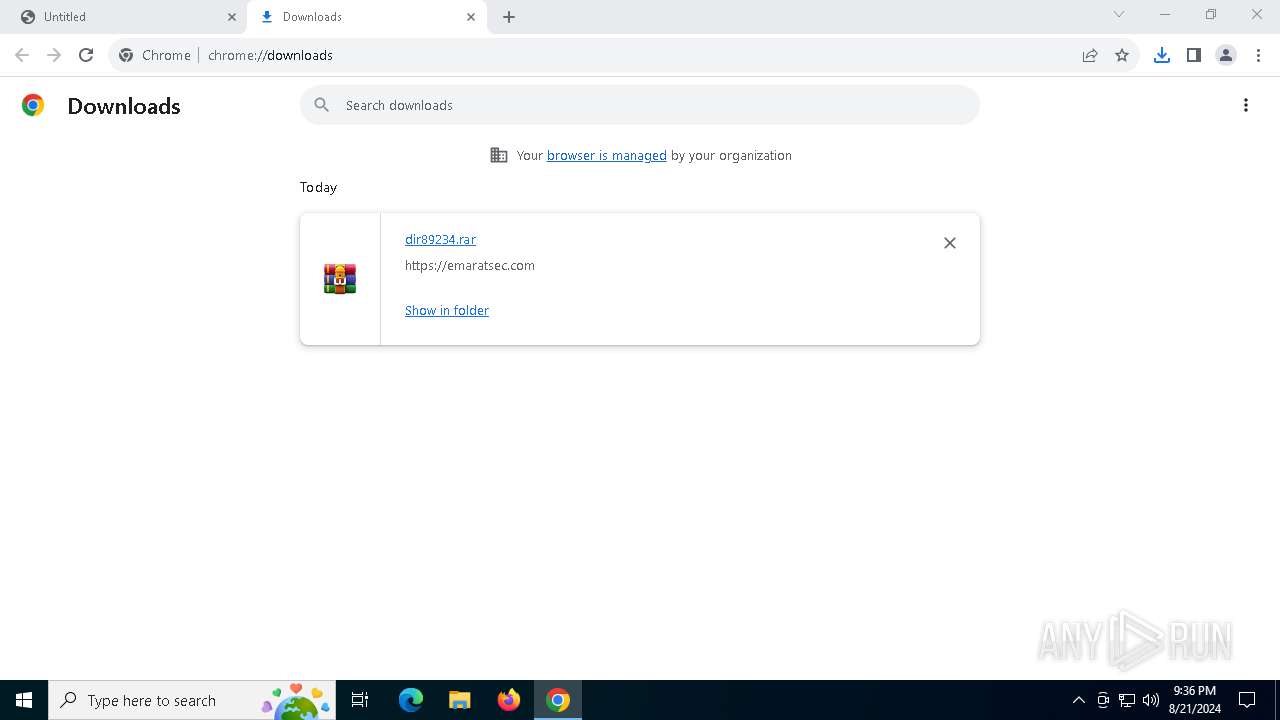
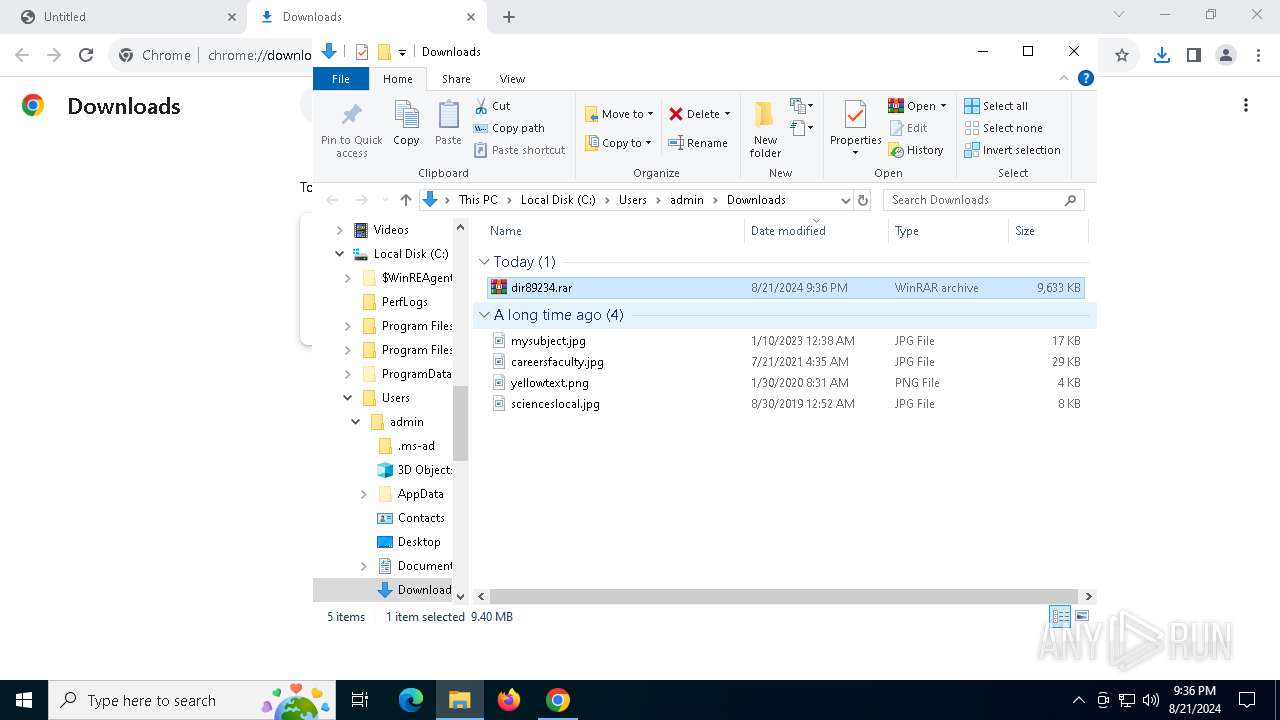
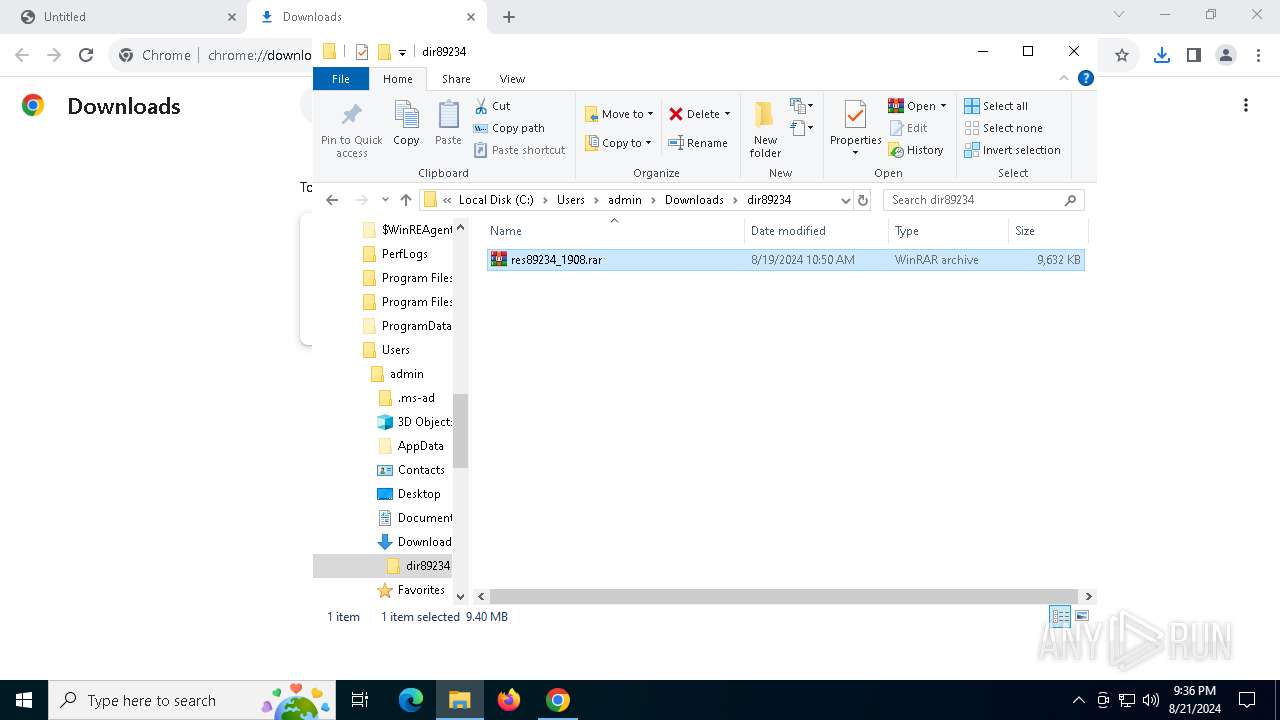
| URL: | https://emaratsec.com/wp-includes/assets/dir89234.rar |
| Full analysis: | https://app.any.run/tasks/3a679321-2dcb-42f8-ba5c-988f84b8b11f |
| Verdict: | Malicious activity |
| Threats: | PrivateLoader is a malware family that is specifically created to infect computer systems and drop additional malicious programs. It operates using a pay-per-install business model, which means that the individuals behind it are paid for each instance of successful deployment of different types of harmful programs, including trojans, stealers, and other ransomware. |
| Analysis date: | August 21, 2024, 21:35:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9192811D98BC76A4CFDB91759B67EEF6 |
| SHA1: | 7282FC3DB9F7E9B51BA8CB3ADFE705CA4DAF726E |
| SHA256: | 2FC512262E655C0EF93FB9855F2B74CAAEE7E5A56A7DB4C7B29726823BDD5F7A |
| SSDEEP: | 3:N8kURDKmUe2bWHNcXW+:2kURDbUfbWHNcXL |
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 8180)
- findstr.exe (PID: 1640)
Connects to the CnC server
- Preservation.pif (PID: 7324)
PRIVATELOADER has been detected (SURICATA)
- Preservation.pif (PID: 7324)
PRIVATELOADER has been detected (YARA)
- Preservation.pif (PID: 7324)
SUSPICIOUS
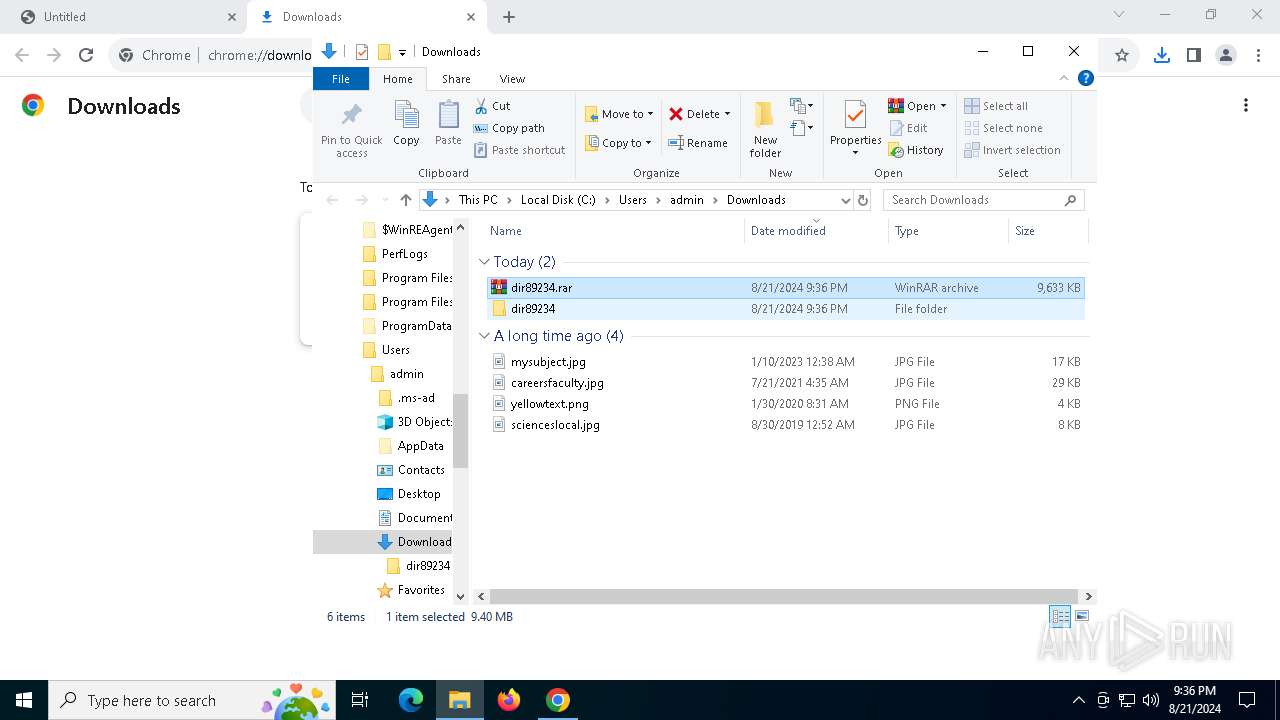
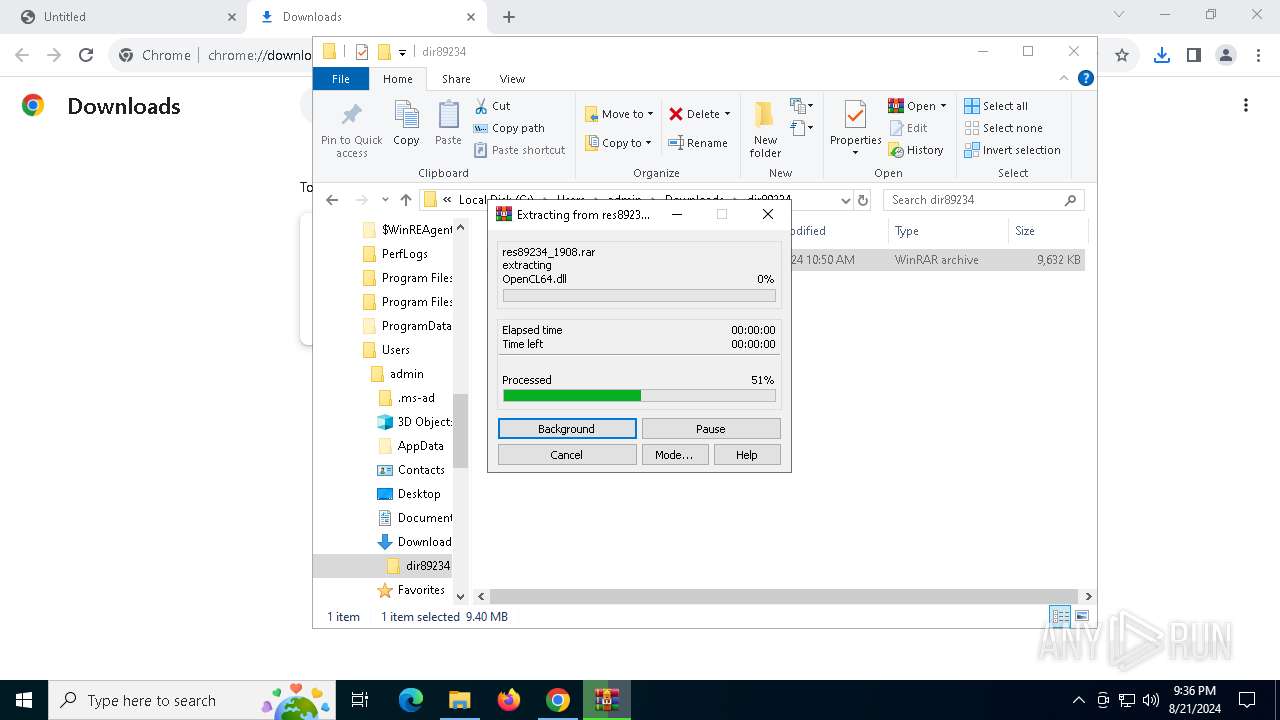
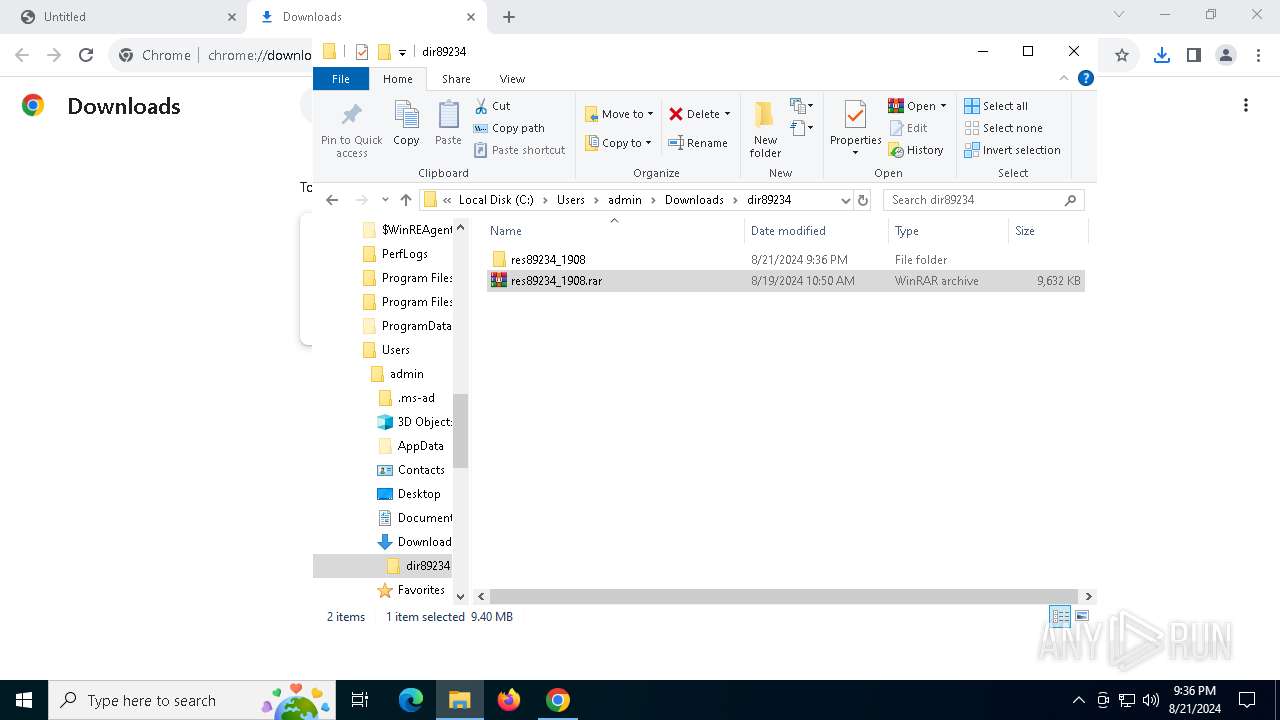
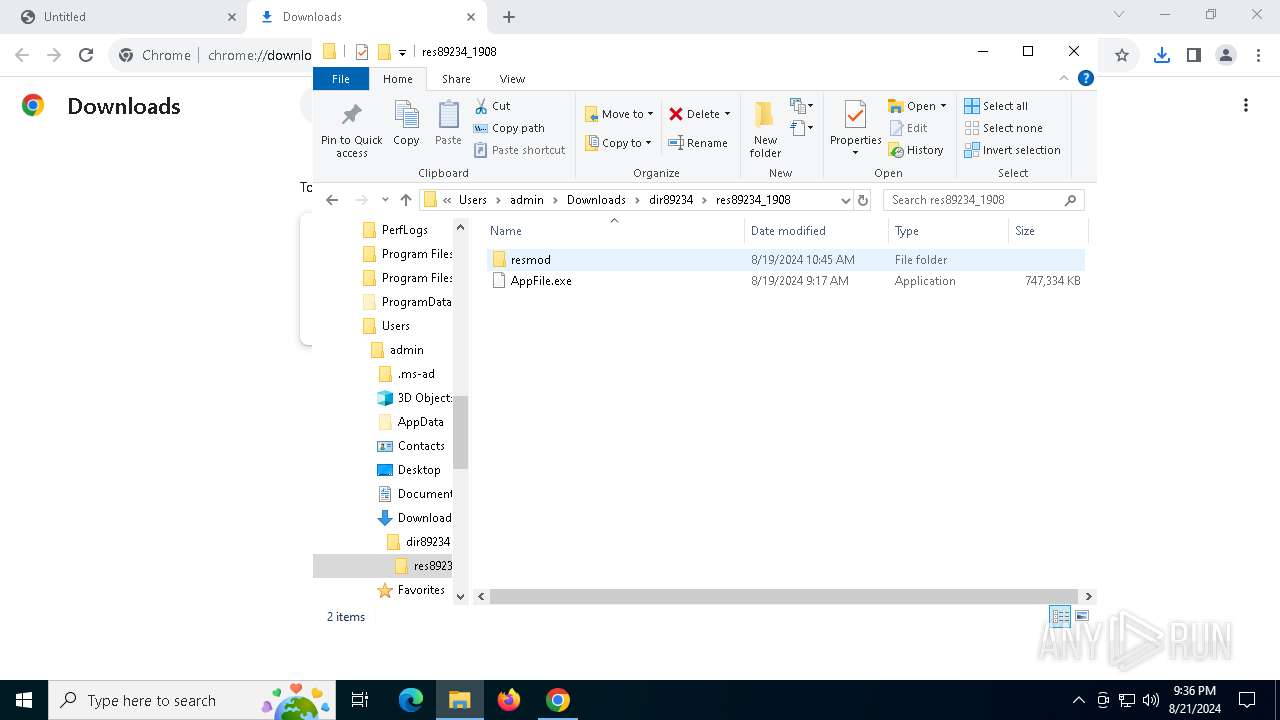
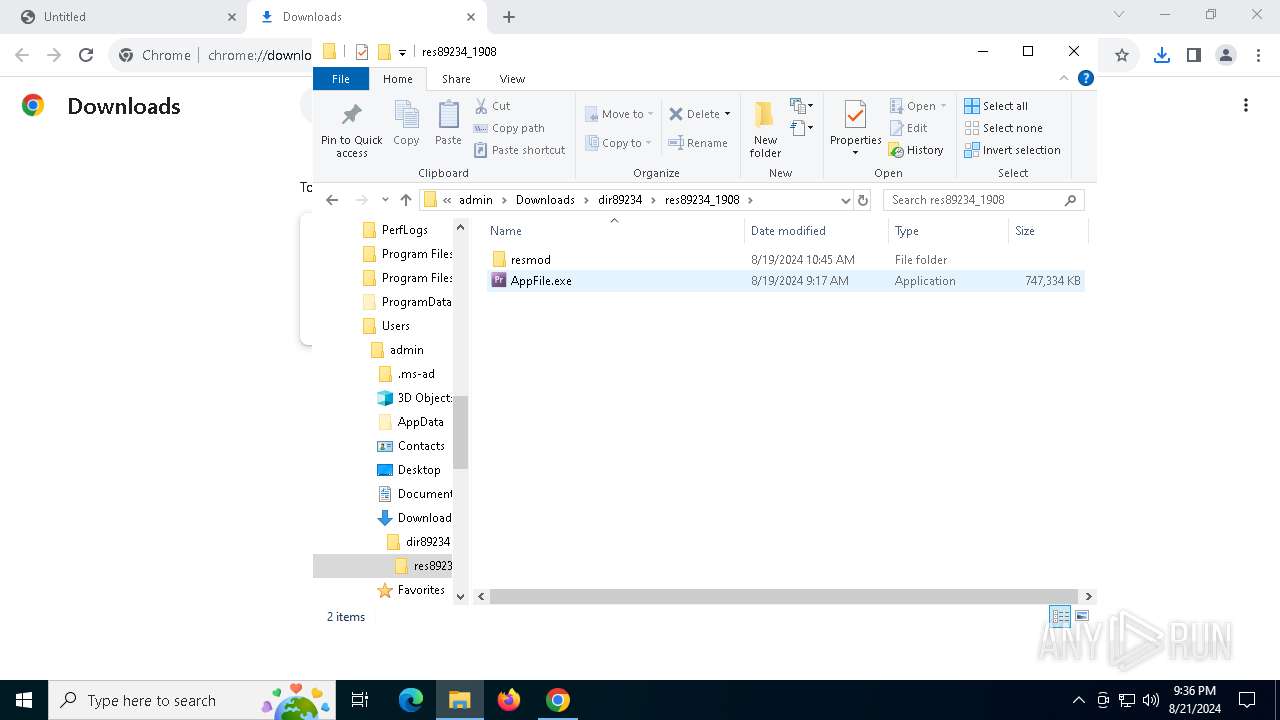
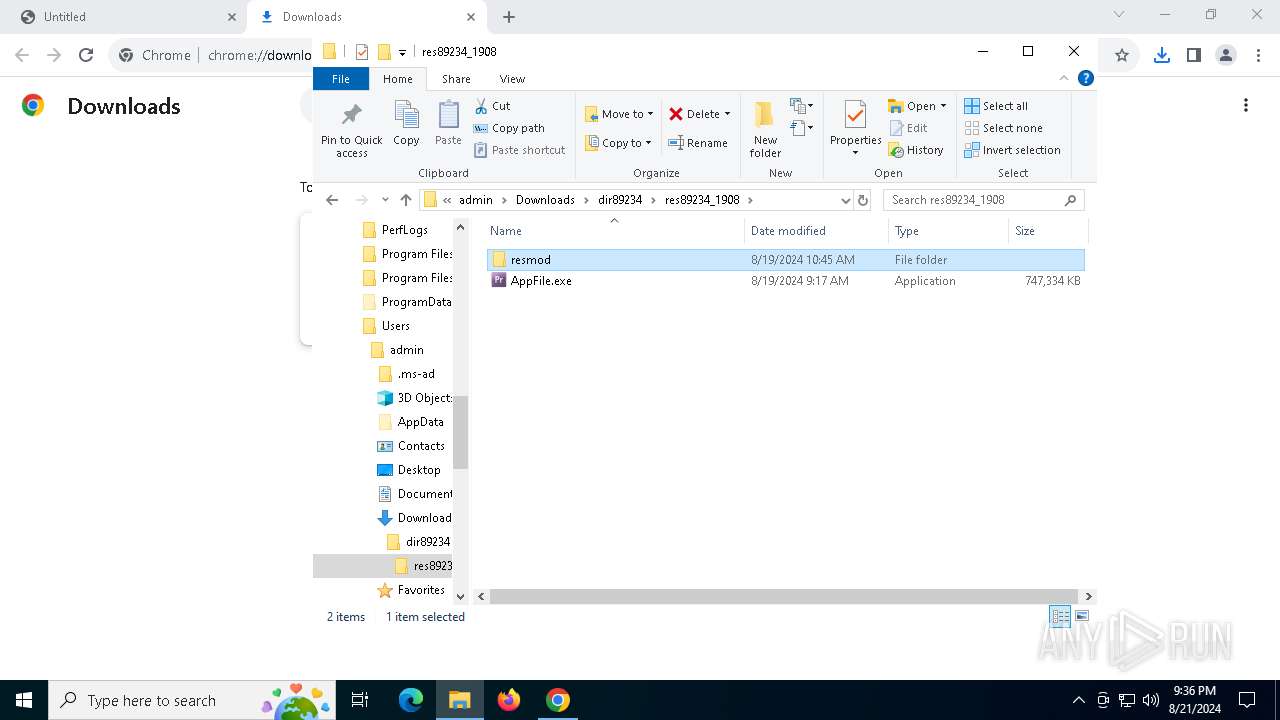
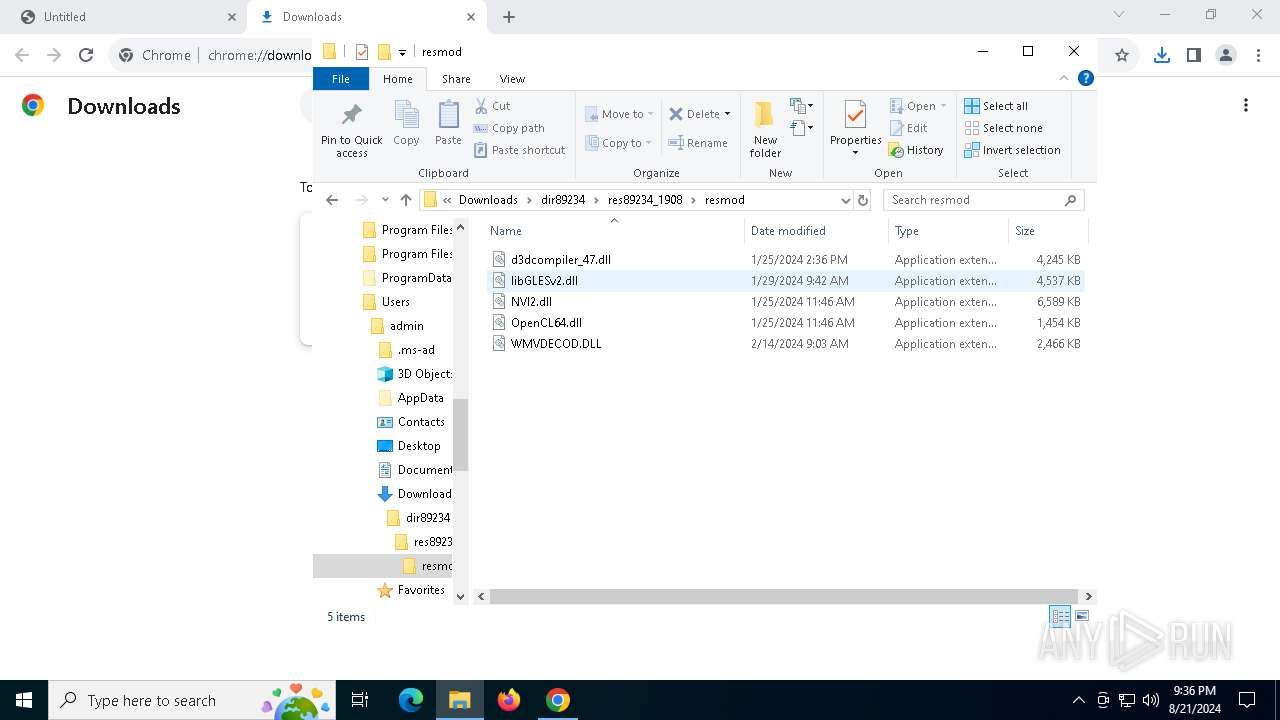
Process drops legitimate windows executable
- WinRAR.exe (PID: 7620)
Reads security settings of Internet Explorer
- AppFile.exe (PID: 8036)
Reads the date of Windows installation
- AppFile.exe (PID: 8036)
Starts CMD.EXE for commands execution
- AppFile.exe (PID: 8036)
- cmd.exe (PID: 8076)
Executing commands from ".cmd" file
- AppFile.exe (PID: 8036)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8076)
Get information on the list of running processes
- cmd.exe (PID: 8076)
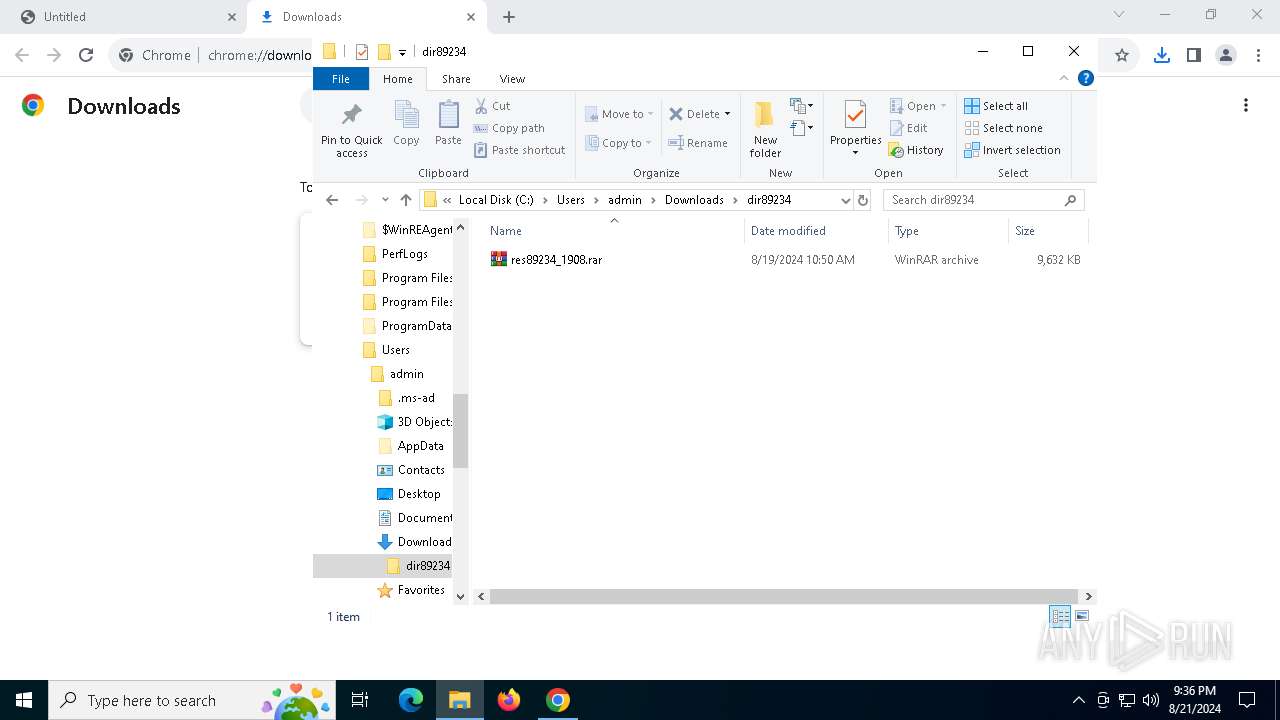
Drops the executable file immediately after the start
- cmd.exe (PID: 8076)
The executable file from the user directory is run by the CMD process
- Preservation.pif (PID: 32)
Application launched itself
- cmd.exe (PID: 8076)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 8076)
Executable content was dropped or overwritten
- cmd.exe (PID: 8076)
Starts application with an unusual extension
- cmd.exe (PID: 8076)
Checks for external IP
- Preservation.pif (PID: 7324)
- svchost.exe (PID: 2256)
Connects to the server without a host name
- Preservation.pif (PID: 7324)
INFO
Application launched itself
- chrome.exe (PID: 6560)
Manual execution by a user
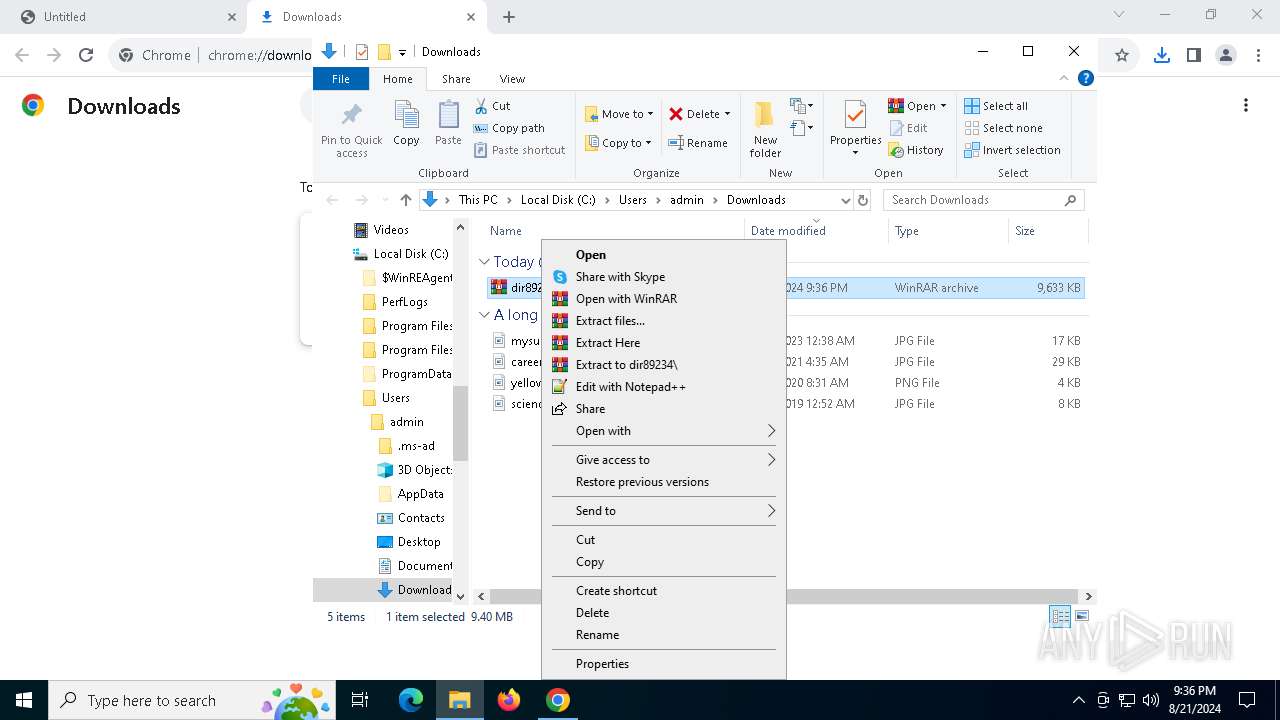
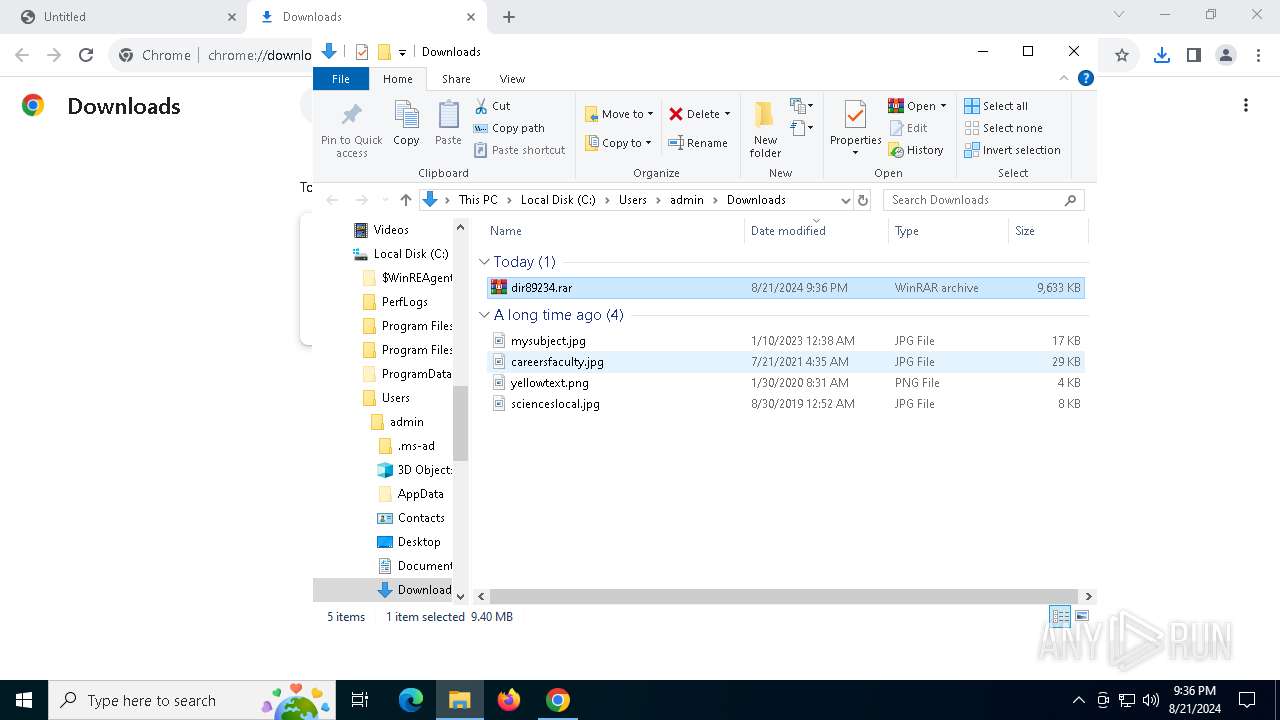
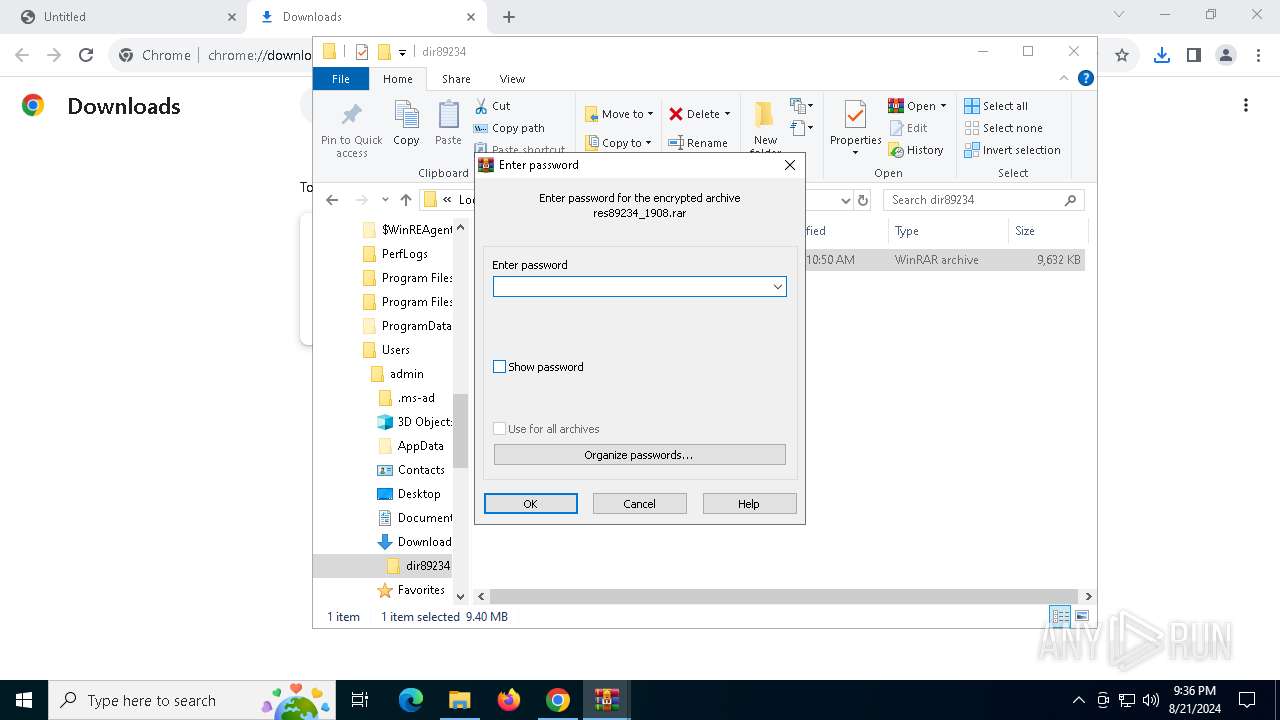
- WinRAR.exe (PID: 7508)
- AppFile.exe (PID: 8036)
- WinRAR.exe (PID: 7620)
- Preservation.pif (PID: 7324)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6560)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7620)
The process uses the downloaded file
- WinRAR.exe (PID: 7508)
- chrome.exe (PID: 7336)
Checks supported languages
- AppFile.exe (PID: 8036)
- Preservation.pif (PID: 32)
- Preservation.pif (PID: 7324)
Reads the computer name
- AppFile.exe (PID: 8036)
- Preservation.pif (PID: 32)
- Preservation.pif (PID: 7324)
Create files in a temporary directory
- AppFile.exe (PID: 8036)
Process checks computer location settings
- AppFile.exe (PID: 8036)
Reads mouse settings
- Preservation.pif (PID: 32)
Reads the software policy settings
- Preservation.pif (PID: 7324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
34
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | Preservation.pif B | C:\Users\admin\AppData\Local\Temp\21650\Preservation.pif | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 788 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3312 --field-trial-handle=1880,i,16741441605567024262,4453212698184408168,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1640 | findstr /I "avastui.exe avgui.exe bdservicehost.exe ekrn.exe nswscsvc.exe sophoshealth.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2388 | findstr /V "RefundAirplaneHuntingtonConstitutes" Ccd | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5496 --field-trial-handle=1880,i,16741441605567024262,4453212698184408168,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4276 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=840 --field-trial-handle=1880,i,16741441605567024262,4453212698184408168,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=5048 --field-trial-handle=1880,i,16741441605567024262,4453212698184408168,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
14 900
Read events
14 828
Write events
62
Delete events
10
Modification events
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
6
Suspicious files
131
Text files
33
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF11e5f8.TMP | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11e5f8.TMP | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:723783C35EAEEE1492EDB30847AE6750 | SHA256:C29323F784CF873BF34992E7A2B4630B19641BF42980109E31D5AF2D487DF6F8 | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\277652fc-5c8c-440e-8a5f-6079dab5810b.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
46
DNS requests
33
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4064 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6336 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7708 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
7480 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
7324 | Preservation.pif | GET | 200 | 195.10.205.48:80 | http://195.10.205.48/api/crazyfish.php | unknown | — | — | unknown |
7708 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/obk5vqrbqu6chkdcf4lvwshzsi_2024.8.20.2/jflhchccmppkfebkiaminageehmchikm_2024.08.20.02_all_acdysxsm3my4w2azgbkdkonfq4wa.crx3 | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/obk5vqrbqu6chkdcf4lvwshzsi_2024.8.20.2/jflhchccmppkfebkiaminageehmchikm_2024.08.20.02_all_acdysxsm3my4w2azgbkdkonfq4wa.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3840 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4200 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6812 | chrome.exe | 198.54.120.24:443 | emaratsec.com | NAMECHEAP-NET | US | unknown |
6560 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6812 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
6560 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3840 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6812 | chrome.exe | 142.250.185.68:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
emaratsec.com |
| unknown |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7324 | Preservation.pif | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain in TLS SNI (api .myip .com) |
7324 | Preservation.pif | A Network Trojan was detected | ET MALWARE PrivateLoader CnC Activity (GET) |
7324 | Preservation.pif | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
7324 | Preservation.pif | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |