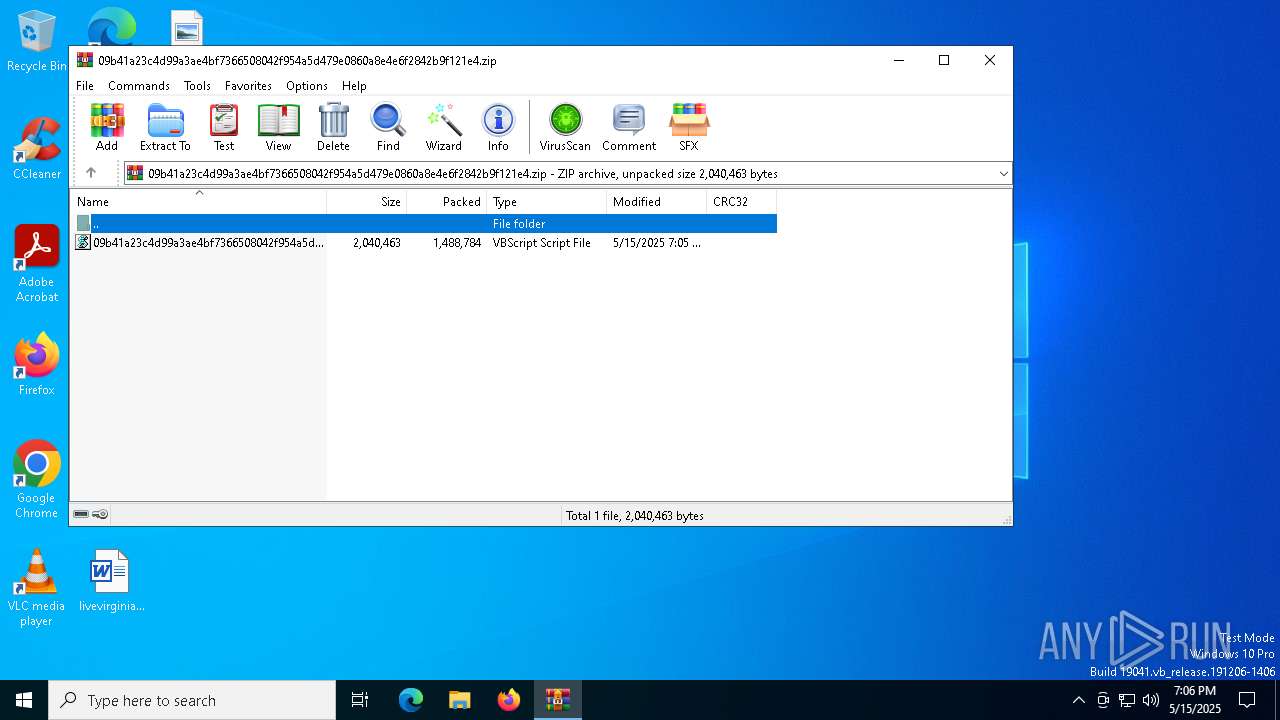
| File name: | 09b41a23c4d99a3ae4bf7366508042f954a5d479e0860a8e4e6f2842b9f121e4.zip |
| Full analysis: | https://app.any.run/tasks/8f67784c-1853-4111-85ad-d6d49c12f72d |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 15, 2025, 19:06:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
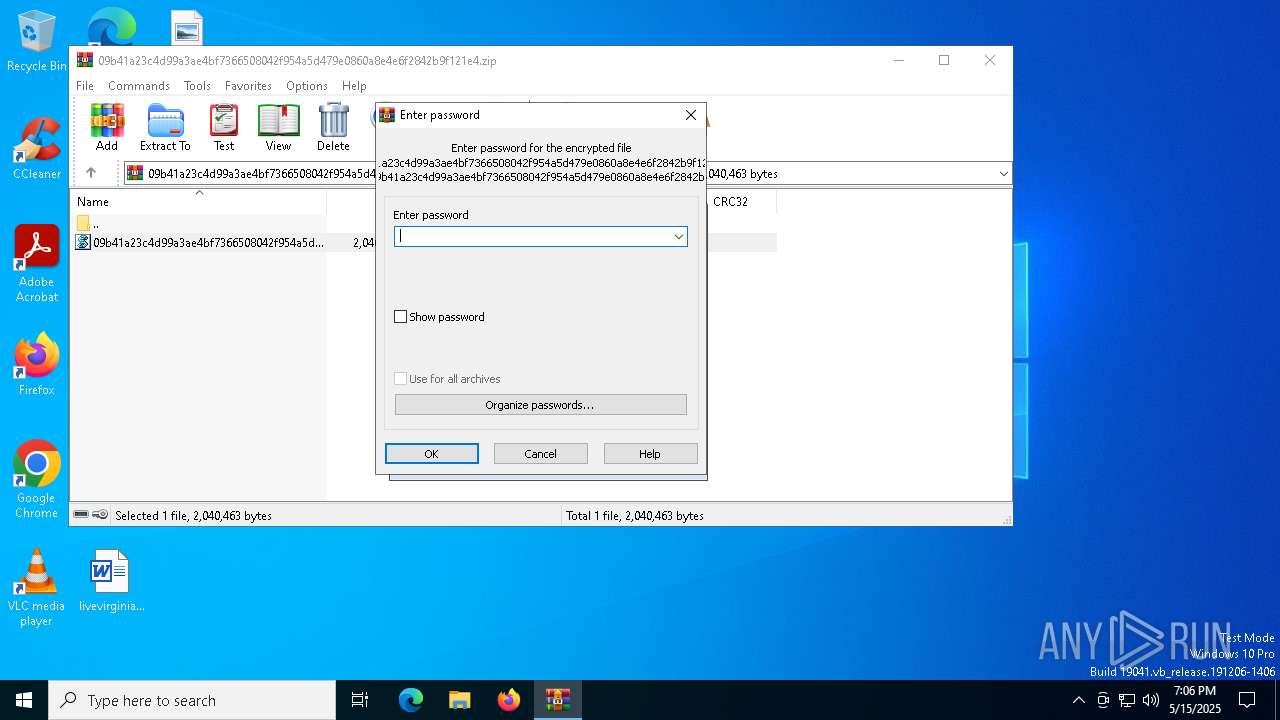
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 4BD37FC27E25FCE308CAC46117961937 |
| SHA1: | 2AE6B21BF8D13595ACED87A04D699EC822C2803B |
| SHA256: | 2FC2629C38FAD6FB576FA21AF73584672F66EF9445E730CF0C589211FF7817B4 |
| SSDEEP: | 49152:I5kkMVZghQNppM5OBEIT8TEo4SD2l1d7abh/CF4LXyOTtAcoYHAETG4CBLLnlIBA:b9mhQG4JYT+uI1duJCUXyOTtAc9gyGxn |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5452)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 1276)
Starts PowerShell from an unusual location
- wscript.exe (PID: 1276)
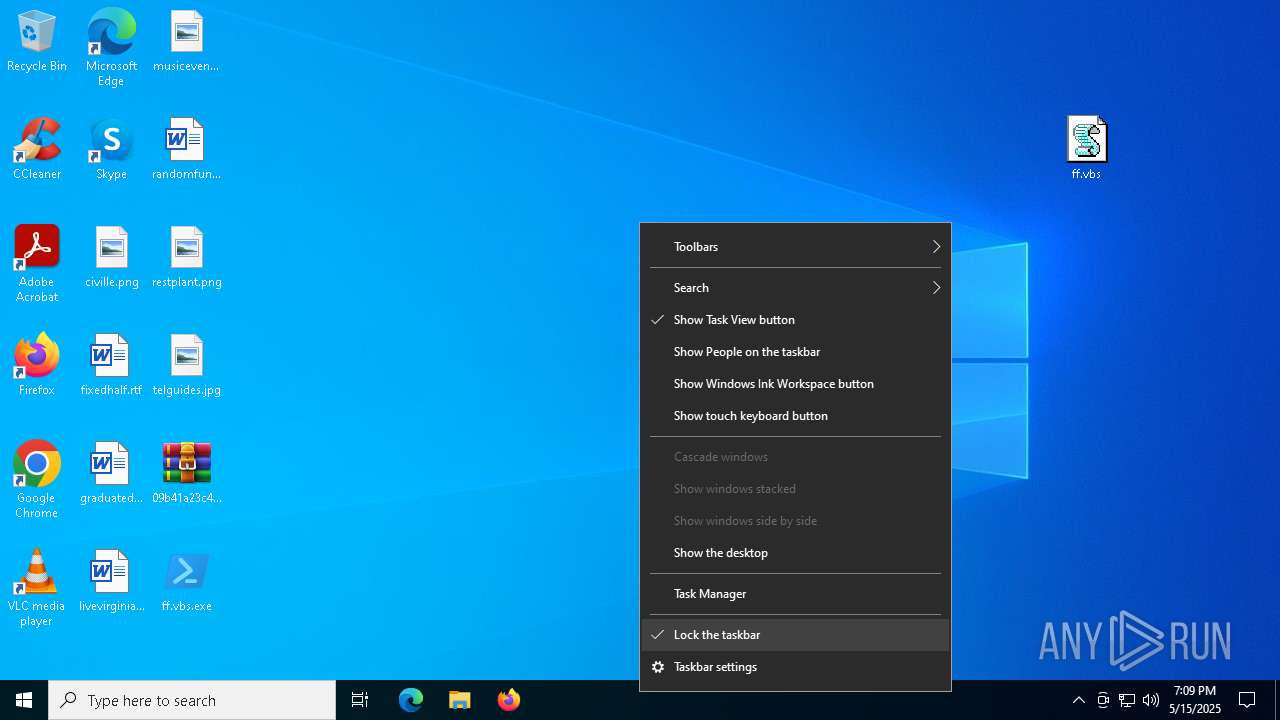
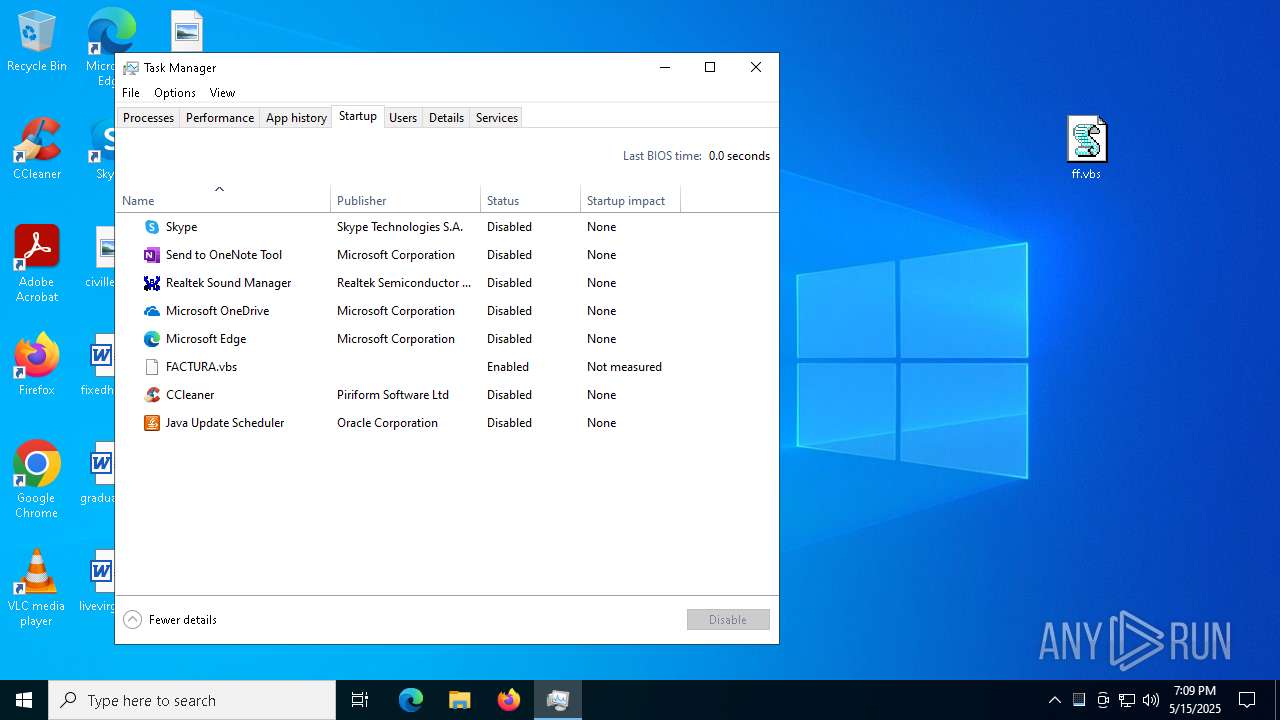
Create files in the Startup directory
- ff.vbs.exe (PID: 4988)
Steals credentials from Web Browsers
- InstallUtil.exe (PID: 6656)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 6656)
STORMKITTY has been detected (YARA)
- InstallUtil.exe (PID: 6656)
ASYNCRAT has been detected (MUTEX)
- InstallUtil.exe (PID: 6656)
SUSPICIOUS
Runs shell command (SCRIPT)
- wscript.exe (PID: 1276)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1276)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 1276)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 1276)
Executed via WMI
- cmd.exe (PID: 720)
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 1276)
Executable content was dropped or overwritten
- cmd.exe (PID: 720)
Process drops legitimate windows executable
- cmd.exe (PID: 720)
Renamed powershell base64 command
- ff.vbs.exe (PID: 4988)
Starts a Microsoft application from unusual location
- ff.vbs.exe (PID: 4988)
Reads security settings of Internet Explorer
- ff.vbs.exe (PID: 4988)
Uses base64 encoding (POWERSHELL)
- ff.vbs.exe (PID: 4988)
Reverses array data (POWERSHELL)
- ff.vbs.exe (PID: 4988)
Write to the desktop.ini file (may be used to cloak folders)
- InstallUtil.exe (PID: 6656)
Starts application with an unusual extension
- cmd.exe (PID: 5744)
- cmd.exe (PID: 4740)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 4740)
- cmd.exe (PID: 5744)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5744)
Possible usage of Discord/Telegram API has been detected (YARA)
- InstallUtil.exe (PID: 6656)
Starts CMD.EXE for commands execution
- InstallUtil.exe (PID: 6656)
Potential Corporate Privacy Violation
- InstallUtil.exe (PID: 6656)
The process connected to a server suspected of theft
- InstallUtil.exe (PID: 6656)
Checks for external IP
- svchost.exe (PID: 2196)
- InstallUtil.exe (PID: 6656)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- InstallUtil.exe (PID: 6656)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 6576)
- Taskmgr.exe (PID: 472)
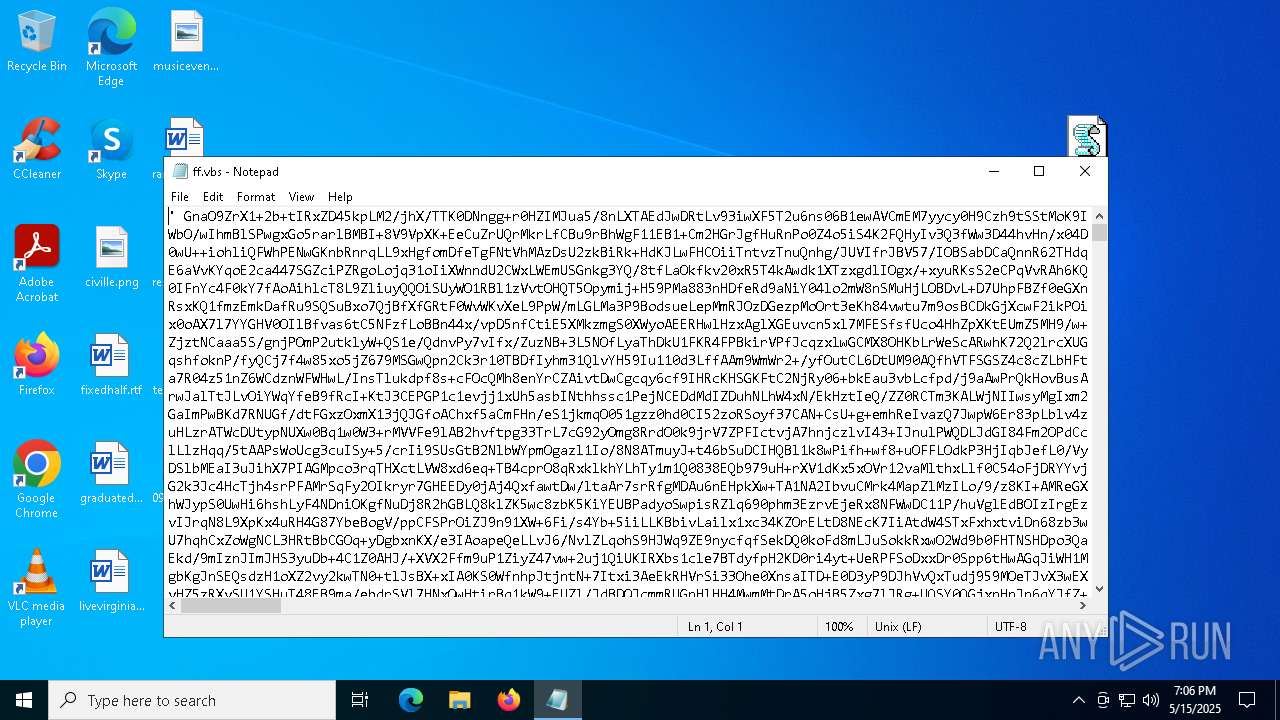
Manual execution by a user
- notepad.exe (PID: 6576)
- wscript.exe (PID: 1276)
- InstallUtil.exe (PID: 6656)
- Taskmgr.exe (PID: 780)
- Taskmgr.exe (PID: 472)
Checks supported languages
- ff.vbs.exe (PID: 4988)
- InstallUtil.exe (PID: 6656)
- chcp.com (PID: 5436)
- chcp.com (PID: 616)
The sample compiled with english language support
- cmd.exe (PID: 720)
Reads the machine GUID from the registry
- ff.vbs.exe (PID: 4988)
- InstallUtil.exe (PID: 6656)
Reads the computer name
- ff.vbs.exe (PID: 4988)
- InstallUtil.exe (PID: 6656)
Uses string replace method (POWERSHELL)
- ff.vbs.exe (PID: 4988)
Create files in a temporary directory
- ff.vbs.exe (PID: 4988)
- InstallUtil.exe (PID: 6656)
Found Base64 encoded access to processes via PowerShell (YARA)
- ff.vbs.exe (PID: 4988)
.NET Reactor protector has been detected
- ff.vbs.exe (PID: 4988)
Found Base64 encoded compression PowerShell classes (YARA)
- ff.vbs.exe (PID: 4988)
Found Base64 encoded reflection usage via PowerShell (YARA)
- ff.vbs.exe (PID: 4988)
Creates files or folders in the user directory
- ff.vbs.exe (PID: 4988)
- InstallUtil.exe (PID: 6656)
Reads the software policy settings
- slui.exe (PID: 6512)
- ff.vbs.exe (PID: 4988)
- slui.exe (PID: 6148)
- InstallUtil.exe (PID: 6656)
Found Base64 encoded text manipulation via PowerShell (YARA)
- ff.vbs.exe (PID: 4988)
Changes the display of characters in the console
- cmd.exe (PID: 5744)
- cmd.exe (PID: 4740)
Disables trace logs
- InstallUtil.exe (PID: 6656)
Reads CPU info
- InstallUtil.exe (PID: 6656)
Checks proxy server information
- InstallUtil.exe (PID: 6656)
- slui.exe (PID: 6148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
StormKitty
(PID) Process(6656) InstallUtil.exe
C2 (1)127.0.0.1
Ports (3)6606
7707
8808
Credentials
Protocoltelegram
URLnull
Token7505564427:AAFKINNdNepp05Fr2uKFA78xWEGn5_-5gqw
ChatId7629232865
Version
BotnetDefault
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE9jCCAt6gAwIBAgIQAKQXqY8ZdB/modqi69mWGTANBgkqhkiG9w0BAQ0FADAcMRowGAYDVQQDDBFXb3JsZFdpbmQgU3RlYWxlcjAgFw0yMTA3MTMwNDUxMDZaGA85OTk5MTIzMTIzNTk1OVowHDEaMBgGA1UEAwwRV29ybGRXaW5kIFN0ZWFsZXIwggIiMA0GCSqGSIb3DQEBAQUAA4ICDwAwggIKAoICAQCnRXYoxuLqqgXdcvIAYWb9DuVRl5ZpdpPfoIgmb7Y9A9AuiddKNm4is8EvIlEh98bQD4OB...
Server_SignatureJ7XpD4w+JaFzTixc0nCmiRA4ZP4bPCIpEYYGofNxvC1+0OsFQr56oTWwQMosnOTB64TZRGSdXVHKzjVchQf7X5Uwu/KQU61NPArjxWVScwKZXOGS4ZNzsWbrxgztkmlyRlQgvEq4rdFsqy1bfvHEoQ/s9aDXBNoLPPjJOexTRQSGuZYMpGSUD+ZUiVwPqqFWTb8KcjEMyABMeXGKfia2e9u8ePKpWv4HSiOfl6N47tTtIfN2FW/2mCX7BOnIZwCl3UxaQnITN812tHD1enX9TK86R91F02c0wabnf4oC07S3...
Keys
AESe5e3972eba013063607e705973dfdf80a8555bcfd8fe09651da2ab43b5773d9b
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:15 19:05:52 |
| ZipCRC: | 0xd89d7e9d |
| ZipCompressedSize: | 1488784 |
| ZipUncompressedSize: | 2040463 |
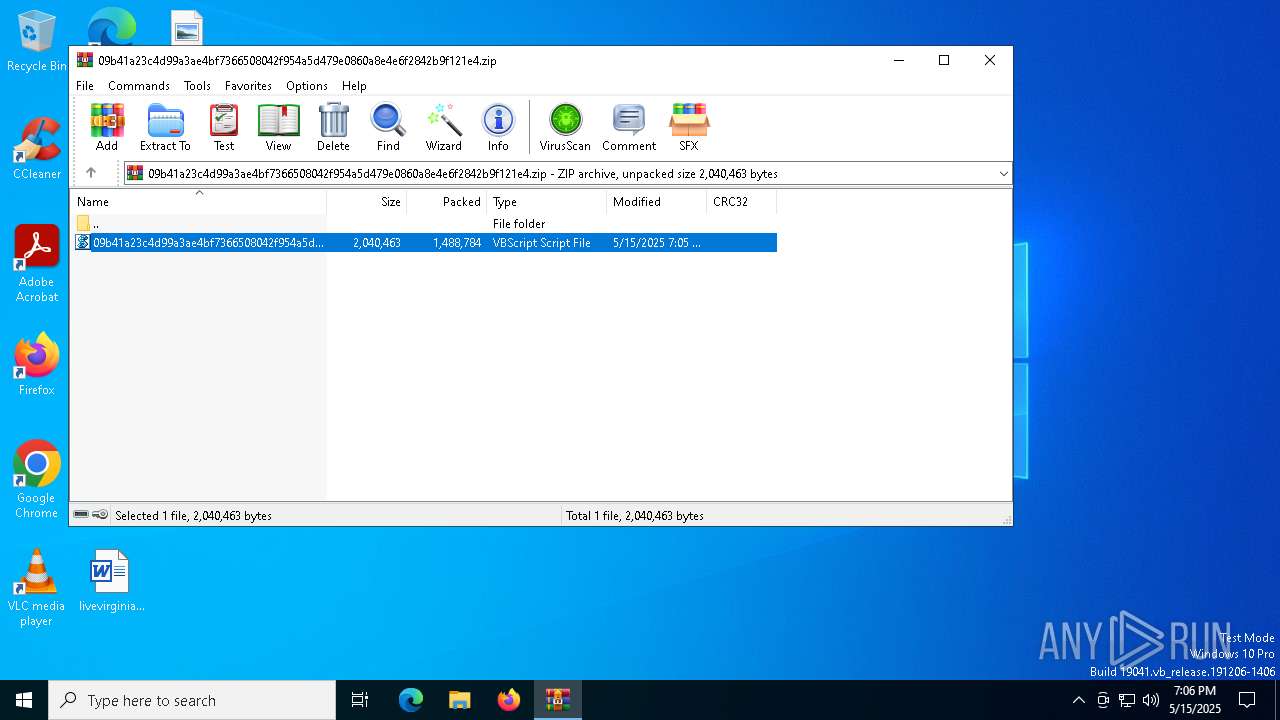
| ZipFileName: | 09b41a23c4d99a3ae4bf7366508042f954a5d479e0860a8e4e6f2842b9f121e4.vbs |
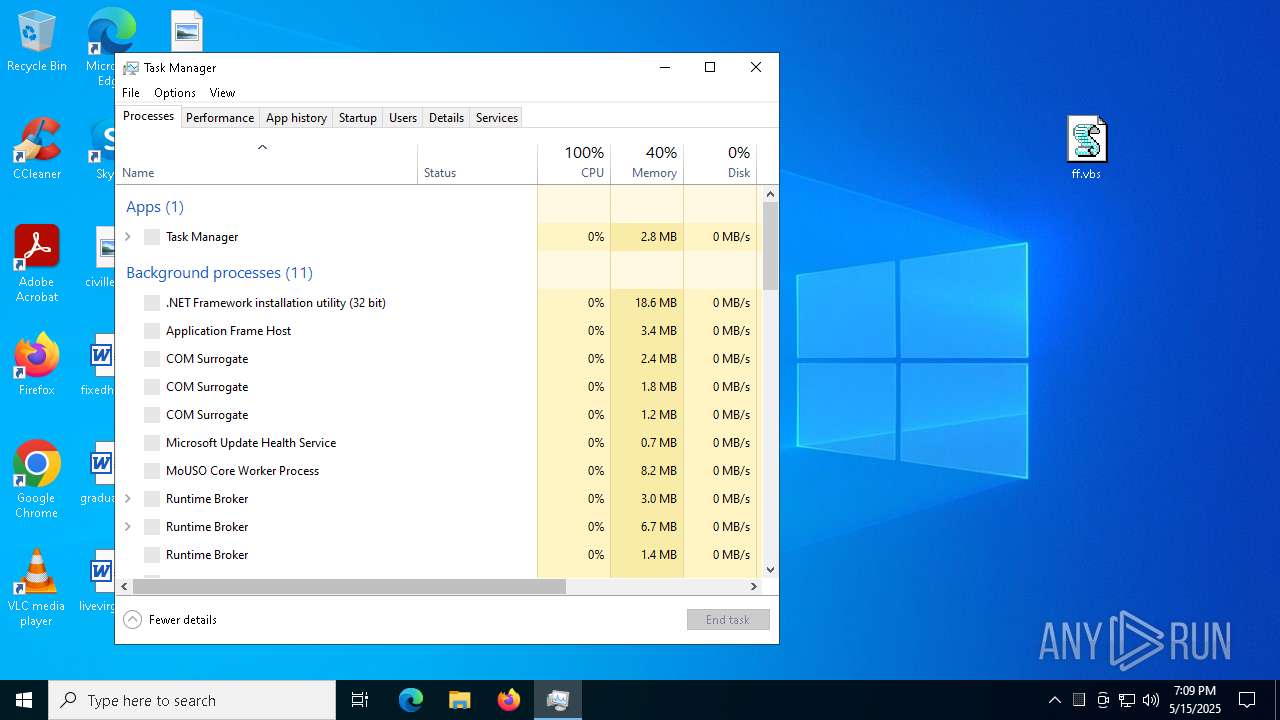
Total processes
155
Monitored processes
23
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | chcp 65001 | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | cmd /c copy "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Desktop\ff.vbs.exe" /Y | C:\Windows\System32\cmd.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\ff.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1804 | netsh wlan show profile | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3024 | netsh wlan show networks mode=bssid | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 201
Read events
14 155
Write events
45
Delete events
1
Modification events
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\09b41a23c4d99a3ae4bf7366508042f954a5d479e0860a8e4e6f2842b9f121e4.zip | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
1
Suspicious files
20
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 720 | cmd.exe | C:\Users\admin\Desktop\ff.vbs.exe | executable | |
MD5:6BB54B2D7A3D63578559239A79700EA3 | SHA256:870EDA04EA71CC066EC907F005E1D05CE592F04799C60E600E2CB986DC85B5EB | |||
| 4988 | ff.vbs.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gcvflb1i.kxq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6656 | InstallUtil.exe | C:\Users\admin\AppData\Local\e8fc6e80da8eaf83eefdbe730219a67f\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Downloads\desktop.ini | text | |
MD5:3A37312509712D4E12D27240137FF377 | SHA256:B029393EA7B7CF644FB1C9F984F57C1980077562EE2E15D0FFD049C4C48098D3 | |||
| 4988 | ff.vbs.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\FACTURA.vbs | text | |
MD5:D87C2A4D8C845086EA404A56C6A66886 | SHA256:7E38ADC308269BDA845CE259429F73A52AEC7735B14AA48A8D981A31384E9741 | |||
| 4988 | ff.vbs.exe | C:\Users\admin\AppData\Roaming\FACTURA.vbs | text | |
MD5:7367B824091F991503B1705B16522B9F | SHA256:09B41A23C4D99A3AE4BF7366508042F954A5D479E0860A8E4E6F2842B9F121E4 | |||
| 5452 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb5452.30679\09b41a23c4d99a3ae4bf7366508042f954a5d479e0860a8e4e6f2842b9f121e4.vbs | text | |
MD5:7367B824091F991503B1705B16522B9F | SHA256:09B41A23C4D99A3AE4BF7366508042F954A5D479E0860A8E4E6F2842B9F121E4 | |||
| 6656 | InstallUtil.exe | C:\Users\admin\AppData\Local\e8fc6e80da8eaf83eefdbe730219a67f\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Pictures\desktop.ini | text | |
MD5:29EAE335B77F438E05594D86A6CA22FF | SHA256:88856962CEF670C087EDA4E07D8F78465BEEABB6143B96BD90F884A80AF925B4 | |||
| 4988 | ff.vbs.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8E7D26D71A1CAF822C338431F0651251 | SHA256:495E7C4588626236C39124CCE568968E874BEDA950319BA391665B43DE111084 | |||
| 6656 | InstallUtil.exe | C:\Users\admin\AppData\Local\e8fc6e80da8eaf83eefdbe730219a67f\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Pictures\qcause.png | binary | |
MD5:7043249EE1EF094A7B2192E863D36CB4 | SHA256:7C97FAAEDCE480855C76C2909B1F168281FC8818B6F6B8A7CBF0914C222D8AA3 | |||
| 4988 | ff.vbs.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_retfrsen.5ly.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
35
DNS requests
24
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.16.155:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
920 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
920 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6656 | InstallUtil.exe | GET | 200 | 104.16.185.241:80 | http://icanhazip.com/ | unknown | — | — | whitelisted |
5380 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.16.155:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6656 | InstallUtil.exe | Attempted Information Leak | ET INFO IP Check Domain (icanhazip. com in HTTP Host) |
6656 | InstallUtil.exe | Potential Corporate Privacy Violation | ET INFO Observed Wifi Geolocation Domain (api .mylnikov .org in TLS SNI) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
6656 | InstallUtil.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
6656 | InstallUtil.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
6656 | InstallUtil.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
6656 | InstallUtil.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
6656 | InstallUtil.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Telegram |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |