| download: | 1.msi |
| Full analysis: | https://app.any.run/tasks/8fe32ca8-179f-420d-8aaa-4b722670af60 |
| Verdict: | Malicious activity |
| Threats: | AZORult can steal banking information, including passwords and credit card details, as well as cryptocurrency. This constantly updated information stealer malware should not be taken lightly, as it continues to be an active threat. |
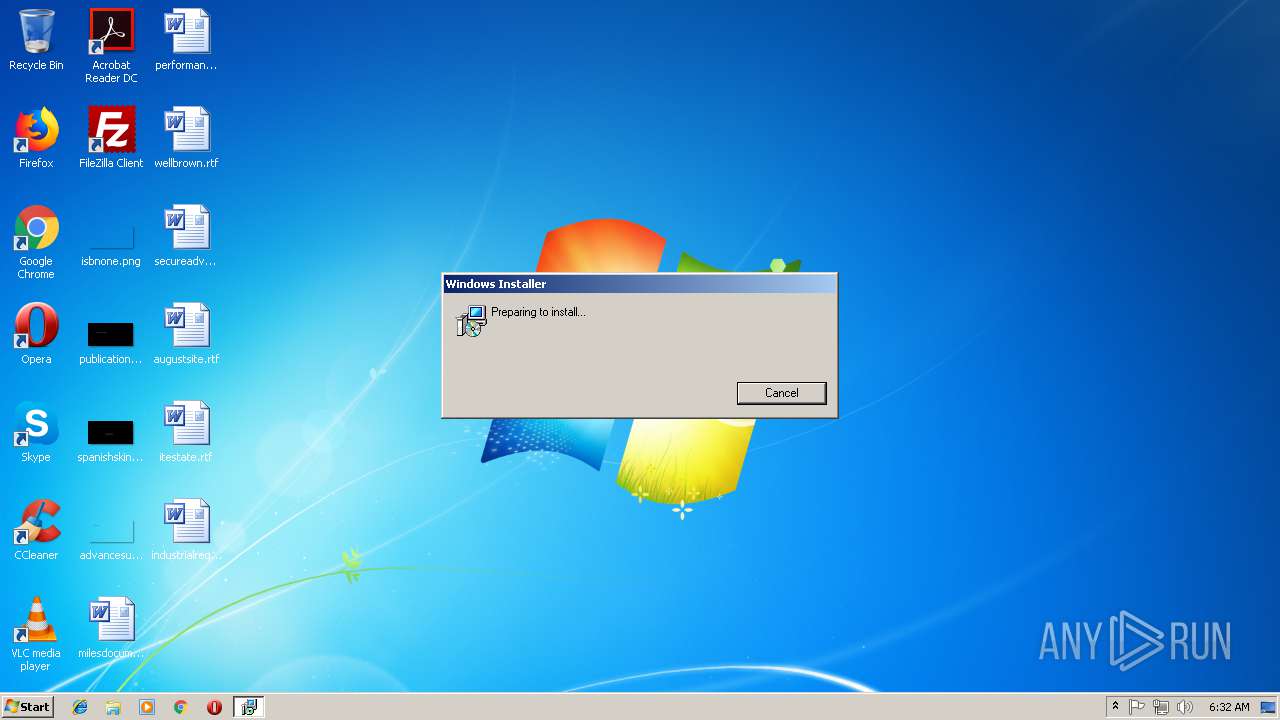
| Analysis date: | November 14, 2018, 06:32:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Last Printed: Fri Sep 21 10:56:09 2012, Create Time/Date: Fri Sep 21 10:56:09 2012, Name of Creating Application: Windows Installer, Title: Exe to msi converter free, Author: www.exetomsi.com, Template: ;0, Last Saved By: devuser, Revision Number: {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E}, Last Saved Time/Date: Tue May 21 12:56:44 2013, Number of Pages: 100, Number of Words: 0, Security: 0 |
| MD5: | 29C847988469FFE46C57162012E92055 |
| SHA1: | F0D27AC8154D413EA82AAFB867437F92272D908A |
| SHA256: | 2F23D2E3A86DDA161F027385710152684281DF3BACF6F67668B8D9DC9E31E165 |
| SSDEEP: | 6144:CE+fcaxUqZoIWyrzmvmJSmVWiH99x0QaKMIQFdushB4P0USdnxLf:CE+fcw5/gmJSgLx0QaKMI6DhB4rwV |
MALICIOUS
Actions looks like stealing of personal data
- MSI56C3.tmp (PID: 256)
- MSI56C3.tmp (PID: 2692)
Connects to CnC server
- MSI56C3.tmp (PID: 2692)
- MSI56C3.tmp (PID: 256)
AZORULT was detected
- MSI56C3.tmp (PID: 2692)
- MSI56C3.tmp (PID: 256)
SUSPICIOUS
Executable content was dropped or overwritten
- MSI56C3.tmp (PID: 256)
- MSI56C3.tmp (PID: 2692)
- msiexec.exe (PID: 2776)
Starts CMD.EXE for commands execution
- MSI56C3.tmp (PID: 2692)
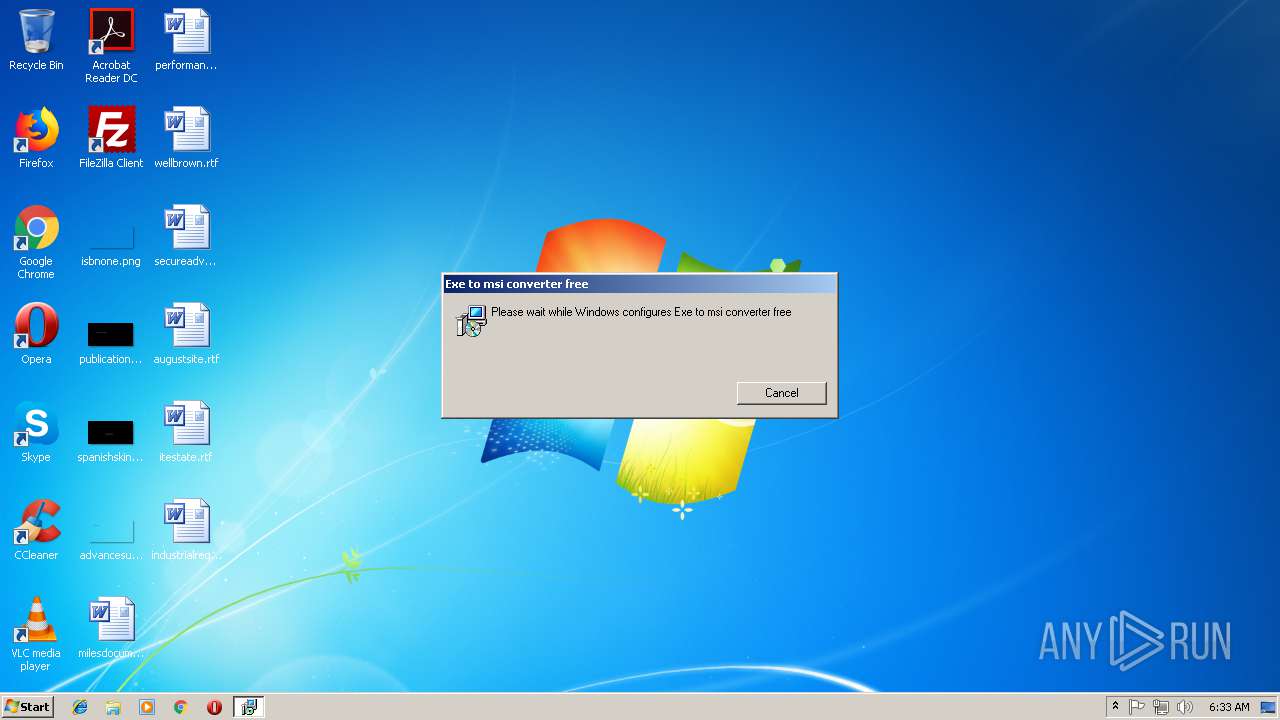
Drop ExeToMSI Application
- msiexec.exe (PID: 2776)
INFO
Creates or modifies windows services
- msiexec.exe (PID: 2776)
- vssvc.exe (PID: 3180)
Loads dropped or rewritten executable
- MSI56C3.tmp (PID: 256)
- MSI56C3.tmp (PID: 2692)
Application launched itself
- MSI56C3.tmp (PID: 256)
Application was dropped or rewritten from another process
- MSI56C3.tmp (PID: 2692)
- MSI56C3.tmp (PID: 256)
Starts application with an unusual extension
- MSI56C3.tmp (PID: 256)
- msiexec.exe (PID: 2776)
Searches for installed software
- msiexec.exe (PID: 2776)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LastPrinted: | 2012:09:21 09:56:09 |
| CreateDate: | 2012:09:21 09:56:09 |
| Software: | Windows Installer |
| Title: | Exe to msi converter free |
| Subject: | - |
| Author: | www.exetomsi.com |
| Keywords: | - |
| Comments: | - |
| Template: | ;0 |
| LastModifiedBy: | devuser |
| RevisionNumber: | {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E} |
| ModifyDate: | 2013:05:21 11:56:44 |
| Pages: | 100 |
| Words: | - |
| Security: | None |
Total processes
41
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Windows\Installer\MSI56C3.tmp" | C:\Windows\Installer\MSI56C3.tmp | msiexec.exe | ||||||||||||
User: admin Company: AI Internet Solutions LLC Integrity Level: MEDIUM Description: Xml Whenever Hemphill 80s Lifecycles Exit code: 0 Modules
| |||||||||||||||
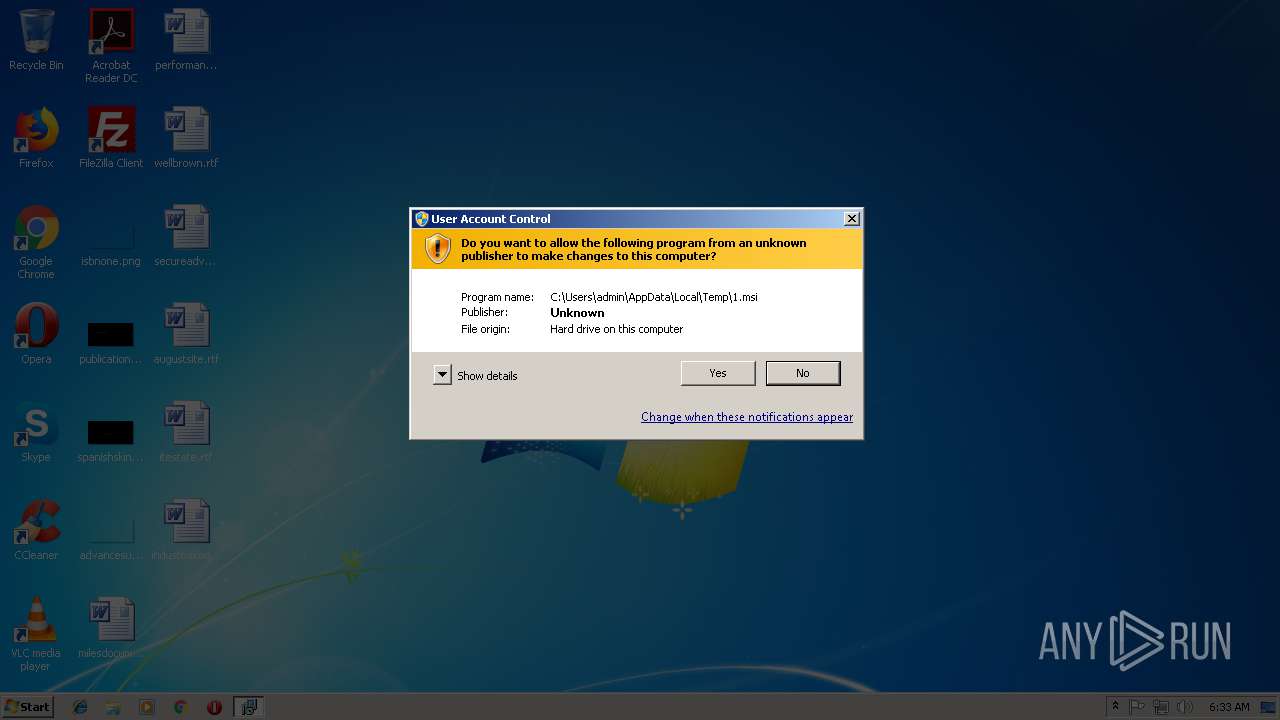
| 1308 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\1.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1960 | C:\Windows\system32\timeout.exe 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | "C:\Windows\Installer\MSI56C3.tmp" | C:\Windows\Installer\MSI56C3.tmp | MSI56C3.tmp | ||||||||||||
User: admin Company: AI Internet Solutions LLC Integrity Level: MEDIUM Description: Xml Whenever Hemphill 80s Lifecycles Exit code: 0 Modules
| |||||||||||||||
| 2776 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3360 | "C:\Windows\system32\cmd.exe" /c C:\Windows\system32\timeout.exe 3 & del "MSI56C3.tmp" | C:\Windows\system32\cmd.exe | — | MSI56C3.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3468 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000004E0" "00000060" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
931
Read events
730
Write events
189
Delete events
12
Modification events
| (PID) Process: | (2776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000008E0965DCE37BD401D80A0000C40D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000008E0965DCE37BD401D80A0000C40D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (2776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000522CC9DCE37BD401D80A0000C40D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AC8ECBDCE37BD401D80A0000580C0000E8030000010000000000000000000000135EEEC59C99644EB5C63F25BF956A8B0000000000000000 | |||
| (PID) Process: | (3180) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000223FDCDCE37BD4016C0C0000F0040000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3180) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000223FDCDCE37BD4016C0C0000240F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3180) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000223FDCDCE37BD4016C0C0000B40E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3180) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000223FDCDCE37BD4016C0C000098020000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3180) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000003066E3DCE37BD4016C0C0000240F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
98
Suspicious files
6
Text files
92
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2776 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3180 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2776 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF051A90F155324B62.TMP | — | |
MD5:— | SHA256:— | |||
| 2776 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3468 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 3468 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 3468 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
| 2776 | msiexec.exe | C:\Windows\Installer\5de29b.msi | executable | |
MD5:— | SHA256:— | |||
| 2776 | msiexec.exe | C:\Windows\Installer\5de29d.ipi | binary | |
MD5:— | SHA256:— | |||
| 2776 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{c5ee5e13-999c-4e64-b5c6-3f25bf956a8b}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
1
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
256 | MSI56C3.tmp | POST | 200 | 103.63.2.245:80 | http://sg-fujitsu.com/oshimili/index.php | HK | binary | 4.27 Mb | malicious |
2692 | MSI56C3.tmp | POST | 200 | 103.63.2.245:80 | http://sg-fujitsu.com/oshimili/index.php | HK | binary | 4.27 Mb | malicious |
256 | MSI56C3.tmp | POST | 200 | 103.63.2.245:80 | http://sg-fujitsu.com/oshimili/index.php | HK | text | 2 b | malicious |
2692 | MSI56C3.tmp | POST | 200 | 103.63.2.245:80 | http://sg-fujitsu.com/oshimili/index.php | HK | text | 2 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
256 | MSI56C3.tmp | 103.63.2.245:80 | sg-fujitsu.com | Guochao Group limited | HK | suspicious |
2692 | MSI56C3.tmp | 103.63.2.245:80 | sg-fujitsu.com | Guochao Group limited | HK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sg-fujitsu.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
256 | MSI56C3.tmp | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 5 |
256 | MSI56C3.tmp | A Network Trojan was detected | ET TROJAN AZORult Variant.4 Checkin M2 |
256 | MSI56C3.tmp | A Network Trojan was detected | MALWARE [PTsecurity] AZORult HTTP Header |
256 | MSI56C3.tmp | A Network Trojan was detected | MALWARE [PTsecurity] AZORult HTTP Header |
256 | MSI56C3.tmp | A Network Trojan was detected | MALWARE [PTsecurity] AZORult client request |
2692 | MSI56C3.tmp | A Network Trojan was detected | ET TROJAN AZORult Variant.4 Checkin M2 |
2692 | MSI56C3.tmp | A Network Trojan was detected | MALWARE [PTsecurity] AZORult client request |
2692 | MSI56C3.tmp | A Network Trojan was detected | MALWARE [PTsecurity] AZORult HTTP Header |
2692 | MSI56C3.tmp | A Network Trojan was detected | MALWARE [PTsecurity] AZORult HTTP Header |
2692 | MSI56C3.tmp | A Network Trojan was detected | MALWARE [PTsecurity] AZORult client request |
6 ETPRO signatures available at the full report