| File name: | HelpPane.exe |
| Full analysis: | https://app.any.run/tasks/4f52e1cc-d7a2-4c95-aa7e-f055747f6066 |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | May 21, 2025, 23:13:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 6 sections |
| MD5: | 3E812DA254B43B5DD4887D361DC6C3C8 |
| SHA1: | 05B5405989A6668EEF63864A8592FC1BEE78FB17 |
| SHA256: | 2F16EFF9E255689457A7656D1A703FA370351AAFA62407F095F275182179ACC8 |
| SSDEEP: | 1536:cq478Oyoq66YwQQiEA5240bgfBukmld+4ghwVcl:cl8OyoD6YwL3A5sbgfBund+RhqY |
MALICIOUS
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7744)
- powershell.exe (PID: 2620)
Bypass execution policy to execute commands
- powershell.exe (PID: 2620)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 7744)
Changes settings for real-time protection
- powershell.exe (PID: 5360)
Changes Windows Defender settings
- cmd.exe (PID: 6492)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 5508)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7208)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 5596)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7260)
STEALER has been found (auto)
- powershell.exe (PID: 2620)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6872)
SUSPICIOUS
Starts a Microsoft application from unusual location
- HelpPane.exe (PID: 7500)
- HelpPane.exe (PID: 7424)
Reads security settings of Internet Explorer
- HelpPane.exe (PID: 7500)
- StartMenuExperienceHost.exe (PID: 8092)
Possibly malicious use of IEX has been detected
- HelpPane.exe (PID: 7500)
Process drops legitimate windows executable
- HelpPane.exe (PID: 7500)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 8092)
- SearchApp.exe (PID: 7488)
Starts POWERSHELL.EXE for commands execution
- HelpPane.exe (PID: 7500)
- powershell.exe (PID: 7744)
- cmd.exe (PID: 6492)
Application launched itself
- powershell.exe (PID: 7744)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 7744)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 7744)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7744)
Base64-obfuscated command line is found
- powershell.exe (PID: 7744)
Executing commands from a ".bat" file
- powershell.exe (PID: 2620)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 6492)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2620)
Script disables Windows Defender's behavior monitoring
- cmd.exe (PID: 6492)
Script disables Windows Defender's IPS
- cmd.exe (PID: 6492)
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 5244)
- cmd.exe (PID: 6492)
- powershell.exe (PID: 6752)
Modifies existing scheduled task
- schtasks.exe (PID: 5596)
- schtasks.exe (PID: 7196)
- schtasks.exe (PID: 2852)
- schtasks.exe (PID: 3008)
- schtasks.exe (PID: 4964)
Executable content was dropped or overwritten
- powershell.exe (PID: 2620)
- HelpPane.exe (PID: 7500)
Connects to unusual port
- Steanings.exe (PID: 6068)
INFO
Reads the computer name
- HelpPane.exe (PID: 7500)
- TextInputHost.exe (PID: 8088)
- SearchApp.exe (PID: 7488)
- StartMenuExperienceHost.exe (PID: 8092)
Checks supported languages
- HelpPane.exe (PID: 7500)
- StartMenuExperienceHost.exe (PID: 8092)
- TextInputHost.exe (PID: 8088)
- SearchApp.exe (PID: 7488)
Process checks computer location settings
- HelpPane.exe (PID: 7500)
- StartMenuExperienceHost.exe (PID: 8092)
- SearchApp.exe (PID: 7488)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 7488)
Checks proxy server information
- SearchApp.exe (PID: 7488)
- powershell.exe (PID: 2620)
Found Base64 encoded file access via PowerShell (YARA)
- HelpPane.exe (PID: 7500)
- powershell.exe (PID: 7744)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- HelpPane.exe (PID: 7500)
- powershell.exe (PID: 7744)
Found Base64 encoded JSON usage via PowerShell (YARA)
- HelpPane.exe (PID: 7500)
- powershell.exe (PID: 7744)
Reads the software policy settings
- SearchApp.exe (PID: 7488)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2620)
Reads Environment values
- SearchApp.exe (PID: 7488)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2620)
Disables trace logs
- powershell.exe (PID: 2620)
The executable file from the user directory is run by the Powershell process
- Steanings.exe (PID: 6068)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2093:10:01 23:23:37+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 18944 |
| InitializedDataSize: | 93696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2200a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.0.19041.3758 |
| ProductVersionNumber: | 10.0.19041.3758 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Microsoft Help and Support |
| CompanyName: | Microsoft Corporation |
| FileDescription: | HelpPane.exe |
| FileVersion: | 10.0.19041.3758 |
| InternalName: | LoadMe.exe |
| LegalCopyright: | Microsoft Corporation. All rights reserved. |
| LegalTrademarks: | Microsoft Corporation |
| OriginalFileName: | LoadMe.exe |
| ProductName: | Microsoft Windows Operating System |
| ProductVersion: | 10.0.19041.3758 |
| AssemblyVersion: | 10.0.19041.3758 |
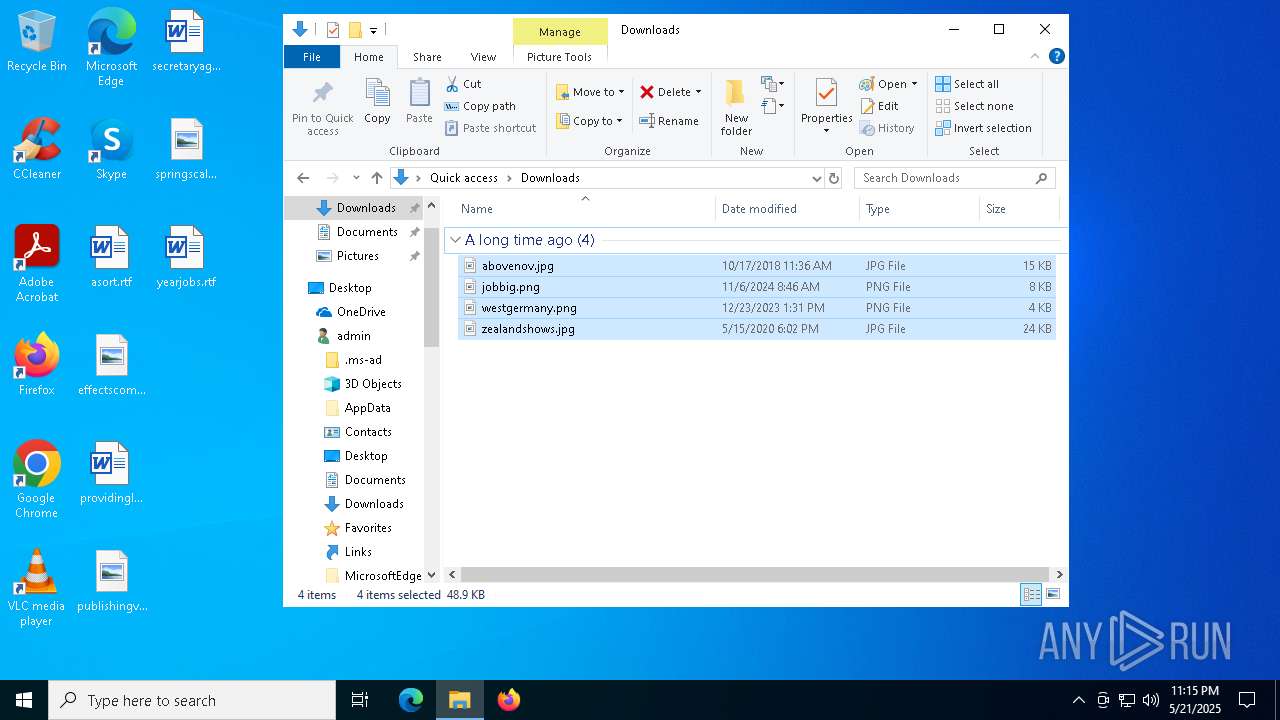
Total processes
201
Monitored processes
68
Malicious processes
4
Suspicious processes
6
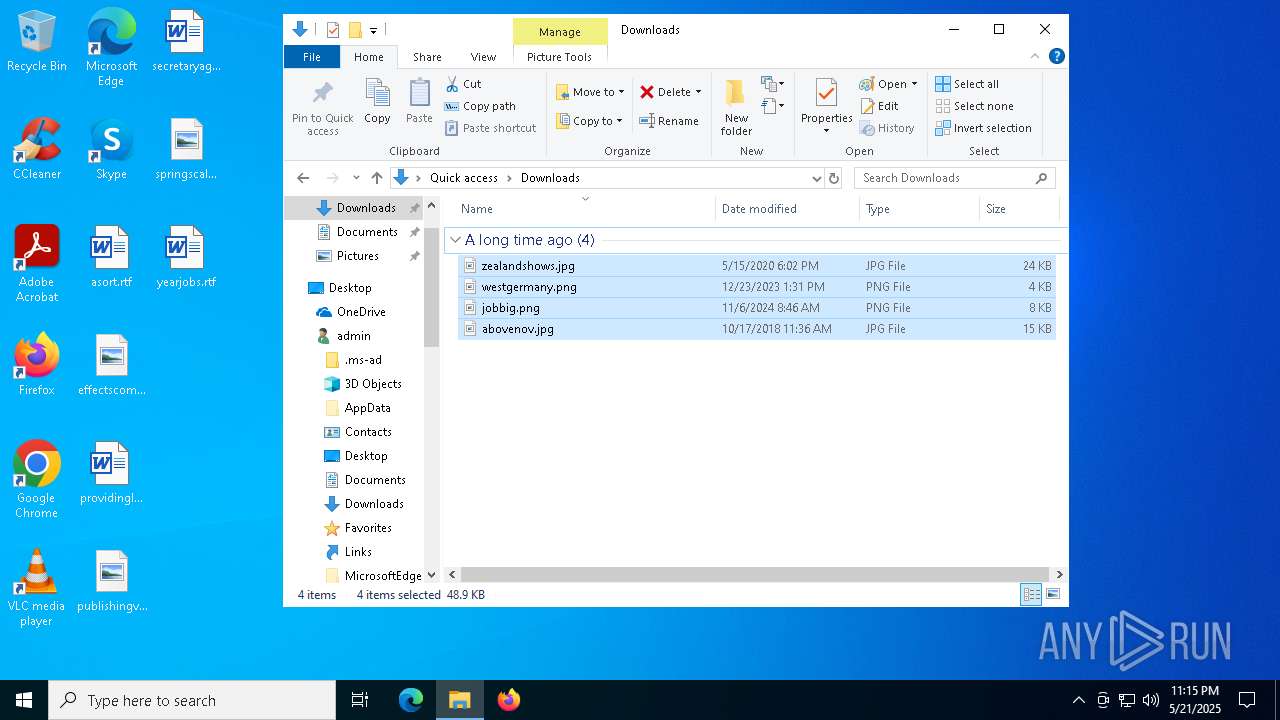
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | reg delete "HKLM\Software\Policies\Microsoft\Windows Defender" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender" /v "DisableAntiSpyware" /t REG_DWORD /d "1" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 740 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\SpyNet" /v "SubmitSamplesConsent" /t REG_DWORD /d "2" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | reg add "HKLM\System\CurrentControlSet\Services\WdFilter" /v "Start" /t REG_DWORD /d "4" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableRealtimeMonitoring" /t REG_DWORD /d "1" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | reg add "HKLM\System\CurrentControlSet\Control\WMI\Autologger\DefenderAuditLogger" /v "Start" /t REG_DWORD /d "0" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | reg delete "HKCR\Directory\shellex\ContextMenuHandlers\EPP" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2388 | powershell.exe -command "Set-MpPreference -HighThreatDefaultAction 6 -Force" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | reg delete "HKCR\*\shellex\ContextMenuHandlers\EPP" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
108 449
Read events
108 338
Write events
101
Delete events
10
Modification events
| (PID) Process: | (7500) HelpPane.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\PushNotifications |
| Operation: | write | Name: | ToastEnabled |
Value: 0 | |||
| (PID) Process: | (7500) HelpPane.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Defender Security Center\Notifications |
| Operation: | write | Name: | DisableEnhancedNotifications |
Value: 1 | |||
| (PID) Process: | (7500) HelpPane.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | HideExclusionsFromLocalAdmins |
Value: 1 | |||
| (PID) Process: | (7716) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8092) StartMenuExperienceHost.exe | Key: | \REGISTRY\A\{043b0682-9ef5-e770-630d-e6e16c9cc131}\LocalState\DataCorruptionRecovery |
| Operation: | write | Name: | InitializationAttemptCount |
Value: 0100000045B2220CA6CADB01 | |||
| (PID) Process: | (8092) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (8092) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_AppUsageData |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (8092) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_TargetedContentTiles |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (7312) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31181478 | |||
| (PID) Process: | (7312) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: 209697100 | |||
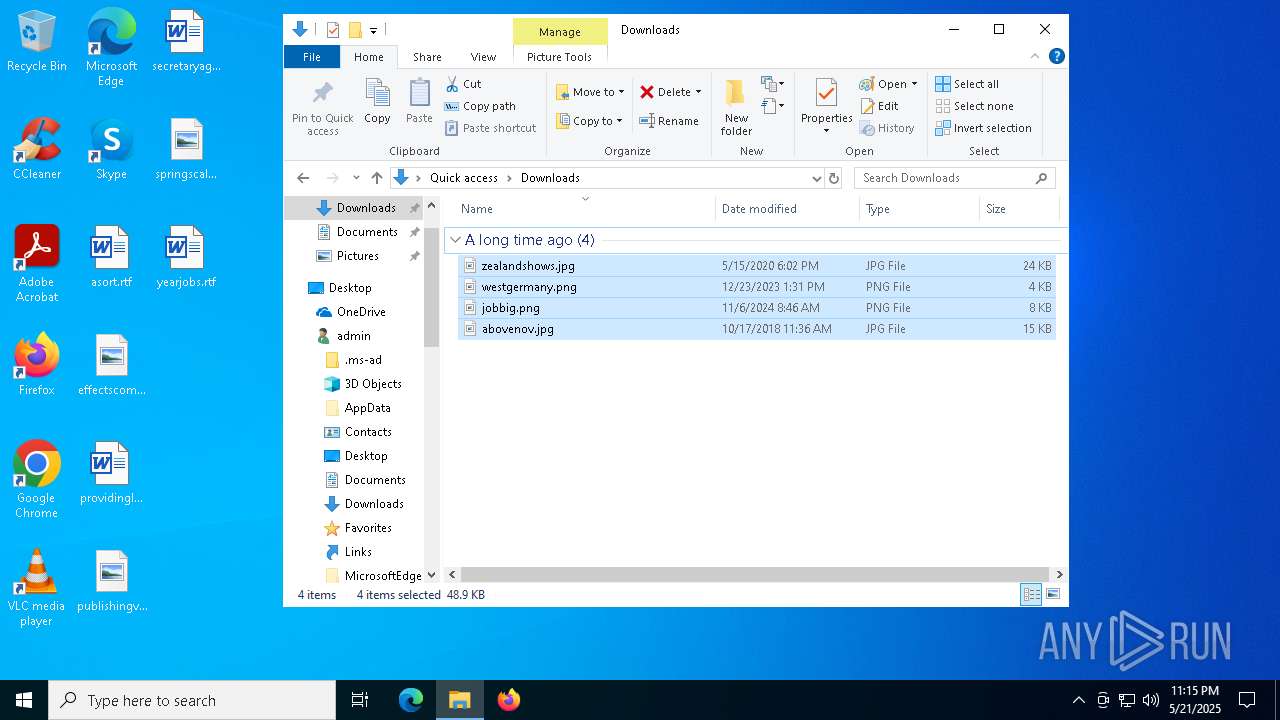
Executable files
4
Suspicious files
36
Text files
62
Unknown types
0
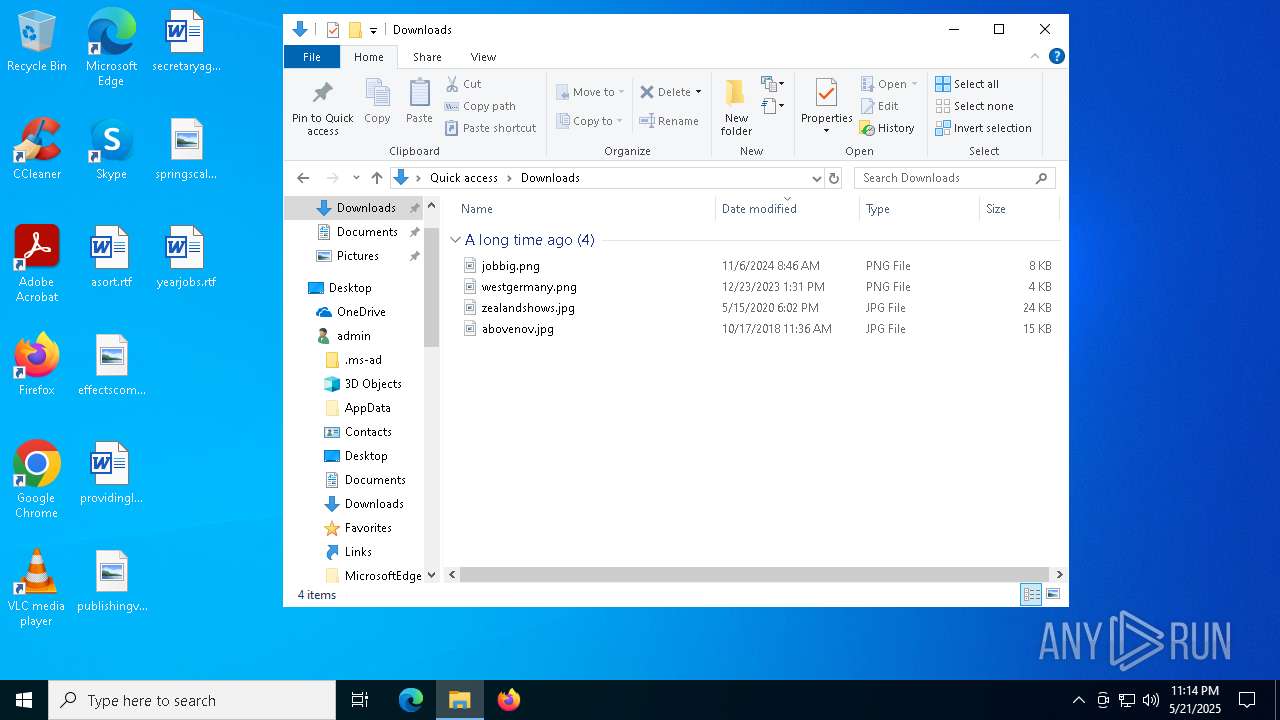
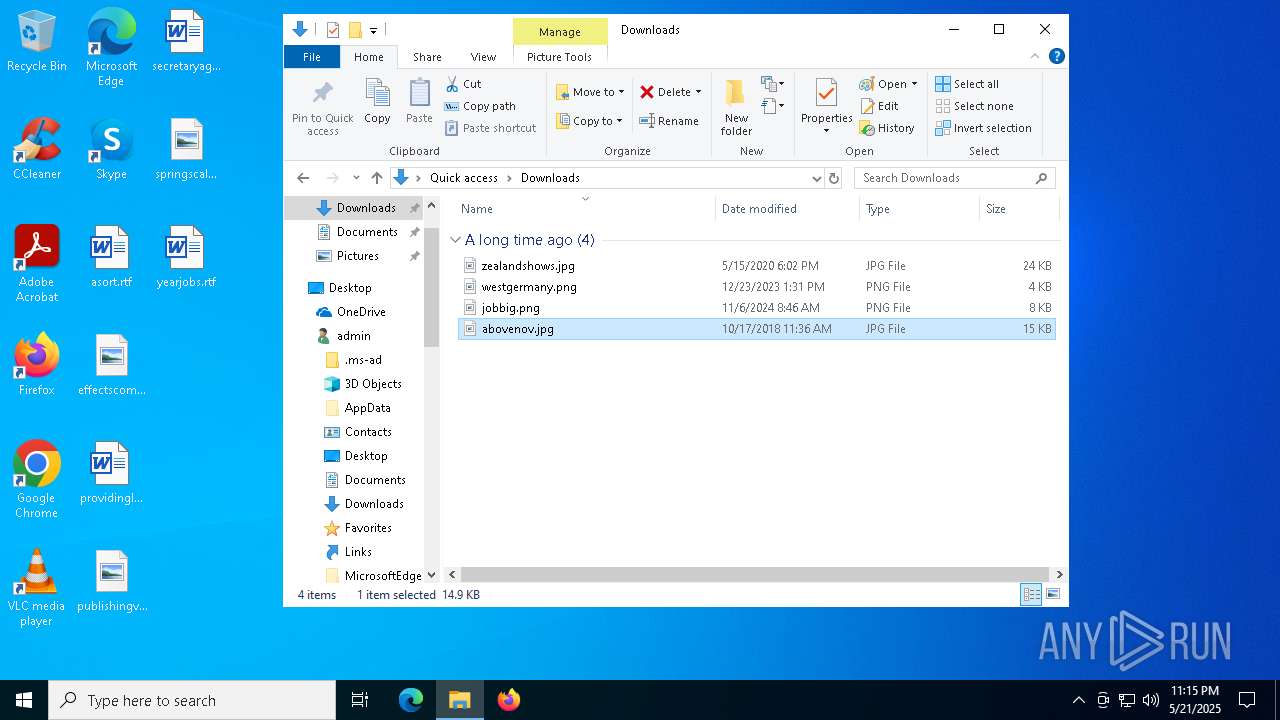
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7312 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:1EEB9D78F112FDF684B3A323BB6D4621 | SHA256:7614CD26D26B07D14441027333612E0E6D063701ECBD33E64820E89AB6350AC3 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:6E1A83FEED2AD48BADD808AA33A9222E | SHA256:17F9C2503F8181535B78A486E47961670E04A428D73668CB06105A3ADE835287 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\bcb8z_DwCpe1HdPp8ojCiJyyJ1I[1].css | text | |
MD5:F1416C376D017BBCA974F4059E969FB6 | SHA256:5B2FA01BCA2B9751B7DC673C3D12BF1C03158A0178B8950A8F8E899E0A3F0B45 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\FgBbpIj0thGWZOh_xFnM9i4O7ek[1].css | text | |
MD5:908111EB0FFB1360D5DD61279C21703E | SHA256:1ED87CF425DED994B05A842271AB4D28A76F399E571688CF2E7B186F70DC3059 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:A11DBBC1BDD8C31BAB492486346C148E | SHA256:C0D216745B268FCAAD0B19712FF57A42B6068072B2AEDCB94D300855DFBFC681 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\-M-8YWX0KlEtdAHVrkTvKQHOghs[1].js | binary | |
MD5:32EE4742328DFB725F3A96641B93B344 | SHA256:061E63AF37D22CCEF7FB5BB9BEABA0DF2F36B64F985BB8A408638846C895D0A7 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\4T9MTY6fJXfwgP6tkOp3zg-9zrY.br[1].js | binary | |
MD5:D26161F0515FEF29C16179B89AD302A6 | SHA256:FDFED0755EA02BD6290A6700ED75AE0B6BC046B1185FB8C37E37ED19E4CFC2A2 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\-iNIzuEypRdgRJ6xnyVHizZ3bpM.br[1].js | binary | |
MD5:E86ABEFE45E62F7E2F865D8A344D0B6F | SHA256:5D54790C856CE13811590E18AC3B0ACEEFEFB61258852490F4C5C60748365E89 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\49fXb98w6kC7-SmXtvaoVNlvMDI.br[1].js | binary | |
MD5:76F9882485239F1413F9FBCFC9CF7339 | SHA256:554383BE05ABA627985DBA632BB3F3884D0D30B7F7B2793954A10B36E4FA20D8 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\NajusmjIqB4kdLn9FmVxeS4xi2o[1].css | text | |
MD5:73D1CEBD8E3B6C7246F422D624EDF803 | SHA256:0674786CF9978A1F9065F57D98E986070C7CBB5177F154F40E8A924C0E0C13F2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
32
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7488 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7096 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7096 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.119.109.218:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7488 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |