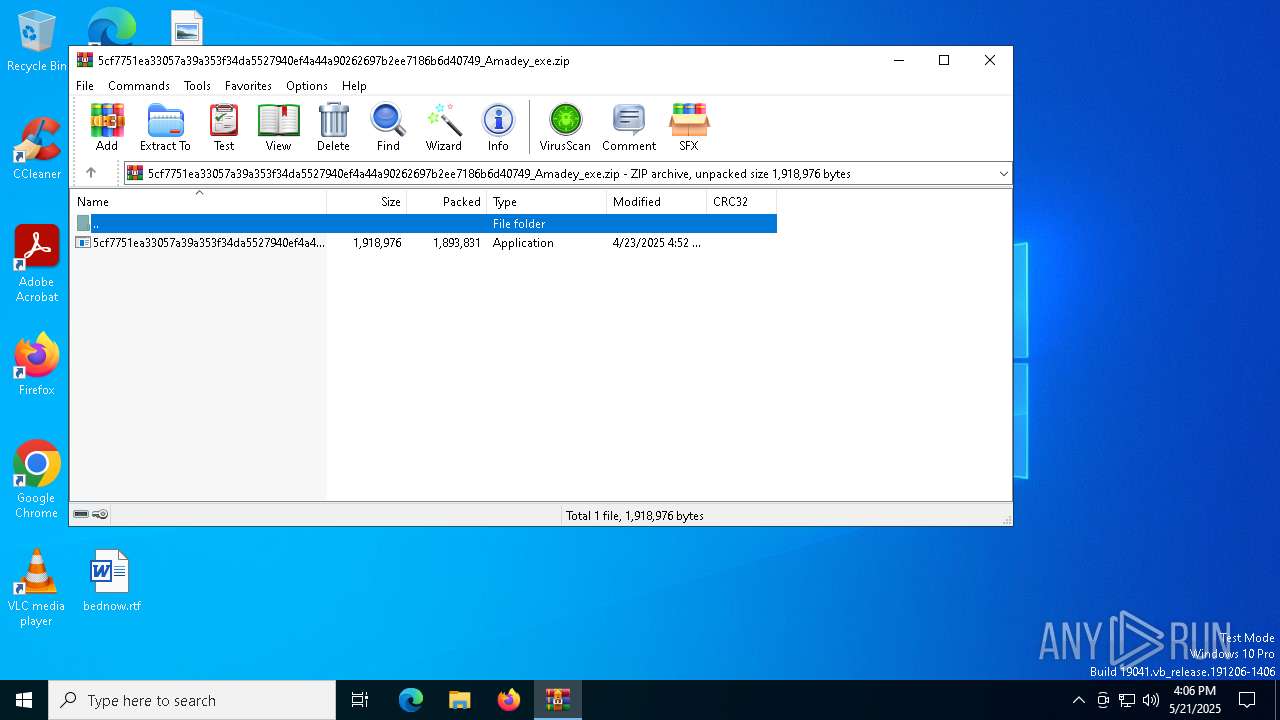
| File name: | 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749_Amadey_exe.zip |
| Full analysis: | https://app.any.run/tasks/06b5b263-1ab8-4446-93b4-f6ceb40ebc72 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 21, 2025, 16:05:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | C8FC0C2CA72E65DEFB2140324B89CB40 |
| SHA1: | 21E216ECAD4BB49575BB2C7D7173E8420CABAD6B |
| SHA256: | 2F09E92C63F1A0352C2E7FFD1664E5D0D661F4E35DB94C7F99908859B1CB3D47 |
| SSDEEP: | 98304:FrCnqH4I7anz+CPXBprtdPOPT1PZKML4b9V1ntHao/9HScg6IblASbKwxm+Sd9X7:MHCme0 |
MALICIOUS
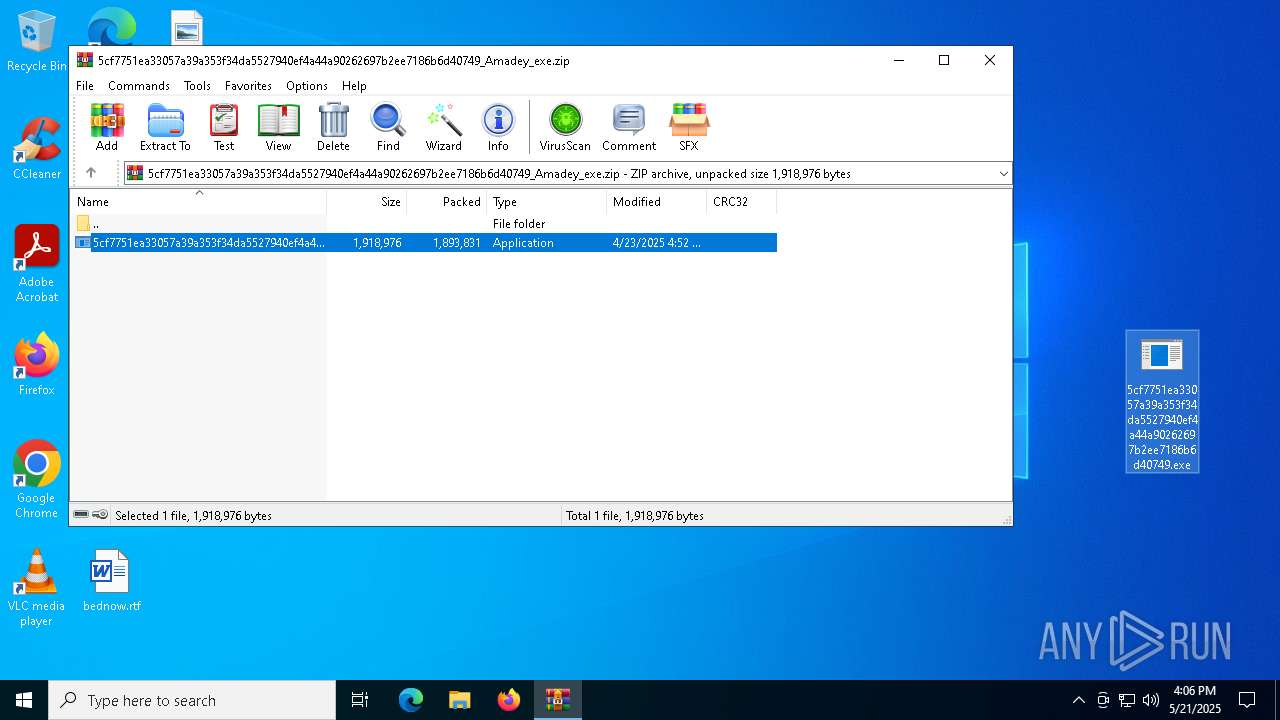
Generic archive extractor
- WinRAR.exe (PID: 4880)
AMADEY mutex has been found
- rapes.exe (PID: 7856)
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
- rapes.exe (PID: 6300)
AMADEY has been found (auto)
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
- WinRAR.exe (PID: 4880)
AMADEY has been detected (YARA)
- rapes.exe (PID: 7856)
SUSPICIOUS
Reads the BIOS version
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
- rapes.exe (PID: 7856)
- rapes.exe (PID: 6300)
Starts itself from another location
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
Reads security settings of Internet Explorer
- rapes.exe (PID: 7856)
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
Executable content was dropped or overwritten
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
There is functionality for enable RDP (YARA)
- rapes.exe (PID: 7856)
The process executes via Task Scheduler
- rapes.exe (PID: 6300)
INFO
Manual execution by a user
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4880)
Checks proxy server information
- rapes.exe (PID: 7856)
Create files in a temporary directory
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
Checks supported languages
- rapes.exe (PID: 7856)
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
- rapes.exe (PID: 6300)
Reads the computer name
- rapes.exe (PID: 7856)
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
Process checks computer location settings
- 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe (PID: 7672)
Themida protector has been detected
- rapes.exe (PID: 7856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(7856) rapes.exe
C2176.113.115.6
URLhttp://176.113.115.6/Ni9kiput/index.php
Version5.21
Options
Drop directorybb556cff4a
Drop namerapes.exe
Strings (125)lv:
msi
Kaspersky Lab
av:
|
#
"
\App
00000422
dm:
Powershell.exe
ProgramData\
ps1
rundll32
http://
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
5.21
dll
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
id:
VideoID
cred.dll|clip.dll|
0000043f
cmd
00000423
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
-executionpolicy remotesigned -File "
2022
------
2016
og:
\0000
CurrentBuild
2019
:::
S-%lu-
" && timeout 1 && del
ProductName
Panda Security
ESET
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/k
+++
?scr=1
Doctor Web
GET
SYSTEM\ControlSet001\Services\BasicDisplay\Video
/quiet
.jpg
vs:
sd:
rundll32.exe
"taskkill /f /im "
pc:
random
=
bb556cff4a
360TotalSecurity
<d>
wb
Content-Type: multipart/form-data; boundary=----
Startup
rapes.exe
Norton
176.113.115.6
&& Exit"
os:
https://
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
2025
Avira
%-lu
zip
POST
"
Content-Type: application/octet-stream
Rem
------
<c>
clip.dll
AVAST Software
\
shell32.dll
" && ren
e3
kernel32.dll
DefaultSettings.XResolution
d1
DefaultSettings.YResolution
r=
cred.dll
--
GetNativeSystemInfo
-%lu
ComputerName
&unit=
Keyboard Layout\Preload
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
ar:
Sophos
%USERPROFILE%
exe
e1
e2
st=s
Programs
0123456789
/Ni9kiput/index.php
un:
rb
bi:
abcdefghijklmnopqrstuvwxyz0123456789-_
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
cmd /C RMDIR /s/q
Bitdefender
-unicode-
AVG
WinDefender
&&
shutdown -s -t 0
Comodo
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
Main
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:04:23 16:52:24 |
| ZipCRC: | 0xbecbe1f6 |
| ZipCompressedSize: | 1893831 |
| ZipUncompressedSize: | 1918976 |
| ZipFileName: | 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe |
Total processes
133
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4880 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749_Amadey_exe.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6300 | "C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe" | C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7240 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7272 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7672 | "C:\Users\admin\Desktop\5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe" | C:\Users\admin\Desktop\5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7856 | "C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe" | C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe | 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
Amadey(PID) Process(7856) rapes.exe C2176.113.115.6 URLhttp://176.113.115.6/Ni9kiput/index.php Version5.21 Options Drop directorybb556cff4a Drop namerapes.exe Strings (125)lv: msi Kaspersky Lab av: | # " \App 00000422 dm: Powershell.exe ProgramData\ ps1 rundll32 http:// Content-Disposition: form-data; name="data"; filename=" SOFTWARE\Microsoft\Windows NT\CurrentVersion 5.21 dll SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders id: VideoID cred.dll|clip.dll| 0000043f cmd 00000423 SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName -executionpolicy remotesigned -File " 2022 ------ 2016 og: \0000 CurrentBuild 2019 ::: S-%lu- " && timeout 1 && del ProductName Panda Security ESET SOFTWARE\Microsoft\Windows\CurrentVersion\Run /k +++ ?scr=1 Doctor Web GET SYSTEM\ControlSet001\Services\BasicDisplay\Video /quiet .jpg vs: sd: rundll32.exe "taskkill /f /im " pc: random = bb556cff4a 360TotalSecurity <d> wb Content-Type: multipart/form-data; boundary=---- Startup rapes.exe Norton 176.113.115.6 && Exit" os: https:// SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce 2025 Avira %-lu zip POST "
Content-Type: application/octet-stream Rem ------ <c> clip.dll AVAST Software \ shell32.dll " && ren e3 kernel32.dll DefaultSettings.XResolution d1 DefaultSettings.YResolution r= cred.dll -- GetNativeSystemInfo -%lu ComputerName &unit= Keyboard Layout\Preload SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders ar: Sophos %USERPROFILE% exe e1 e2 st=s Programs 0123456789 /Ni9kiput/index.php un: rb bi: abcdefghijklmnopqrstuvwxyz0123456789-_ SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\ cmd /C RMDIR /s/q Bitdefender -unicode- AVG WinDefender && shutdown -s -t 0 Comodo 00000419 Content-Type: application/x-www-form-urlencoded /Plugins/ Main | |||||||||||||||
Total events
2 504
Read events
2 482
Write events
22
Delete events
0
Modification events
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749_Amadey_exe.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
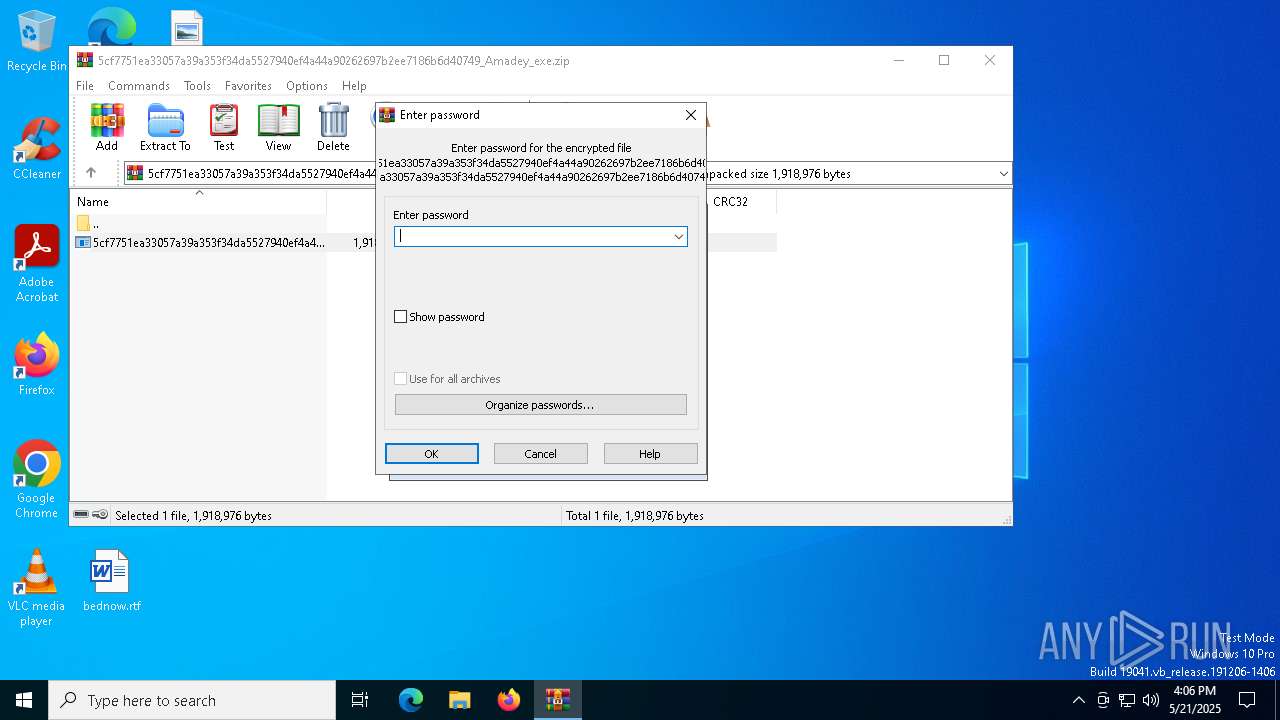
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7672 | 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe | C:\Windows\Tasks\rapes.job | binary | |
MD5:C8404DF444A6C2B6611E3EAB2870A5DF | SHA256:283C4AD413F7F440F466A9B2B1C044E696B6D68AB94AAAB7A80733D380733C5C | |||
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4880.38039\5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe | executable | |
MD5:0648029F0EB1CABA6FE73371623519AC | SHA256:5CF7751EA33057A39A353F34DA5527940EF4A44A90262697B2EE7186B6D40749 | |||
| 7672 | 5cf7751ea33057a39a353f34da5527940ef4a44a90262697b2ee7186b6d40749.exe | C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe | executable | |
MD5:0648029F0EB1CABA6FE73371623519AC | SHA256:5CF7751EA33057A39A353F34DA5527940EF4A44A90262697B2EE7186B6D40749 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8136 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8136 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |