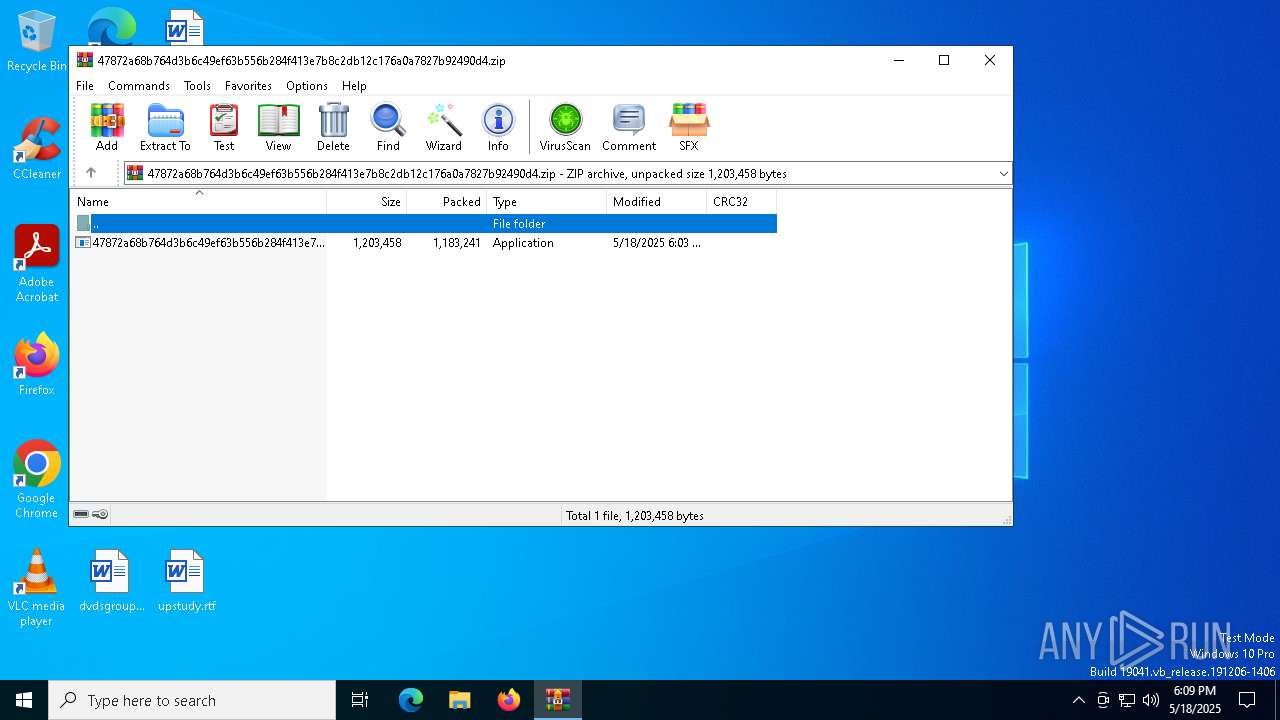
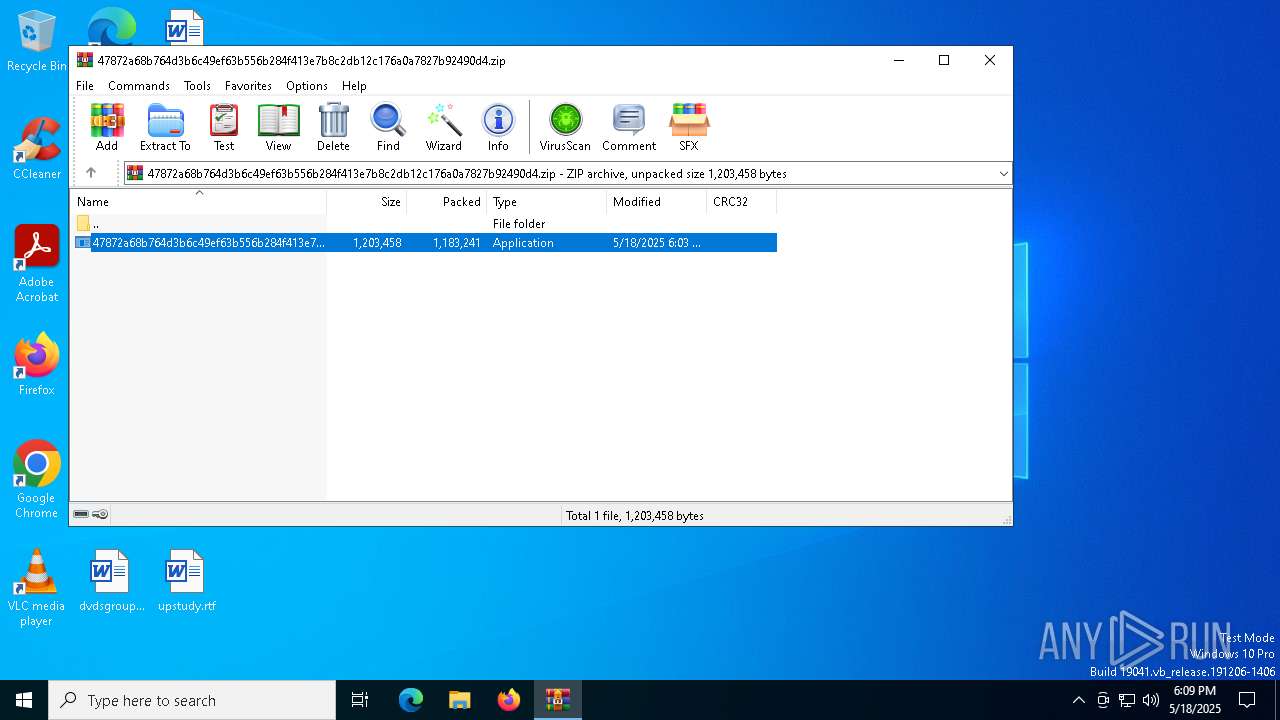
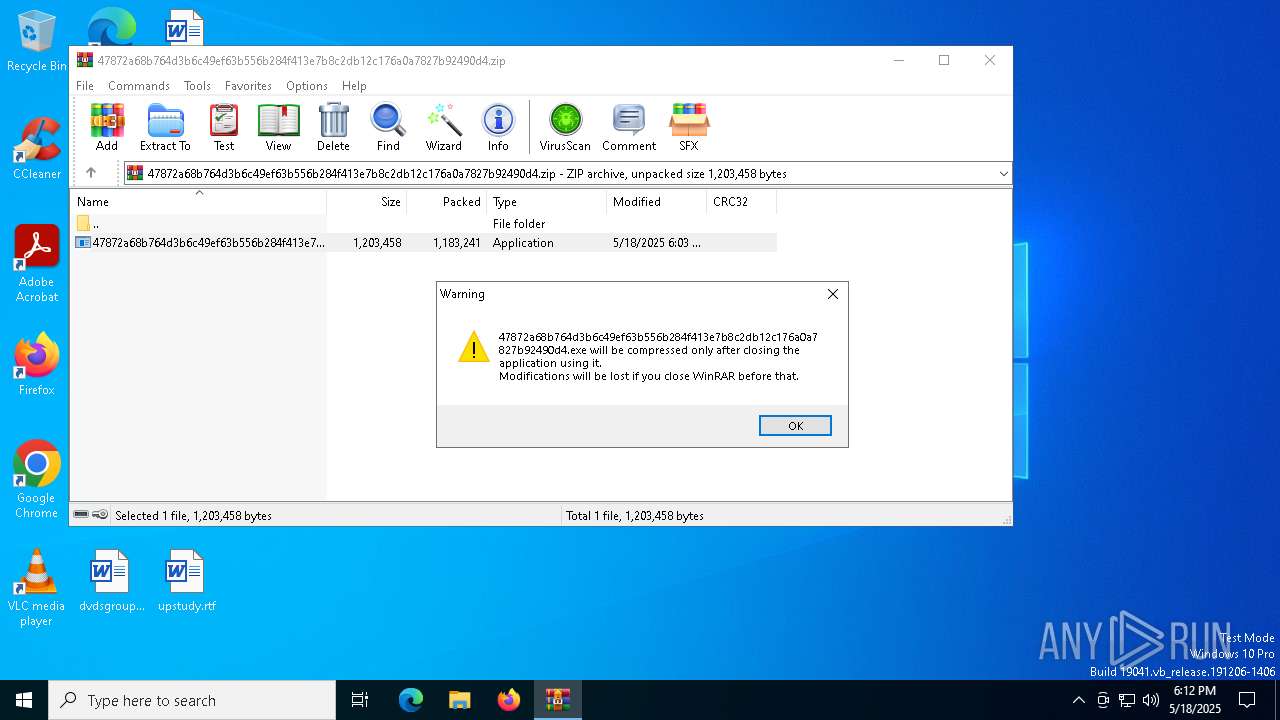
| File name: | 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.zip |
| Full analysis: | https://app.any.run/tasks/8ea03254-13d7-474b-b2e7-de206e6d7491 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 18, 2025, 18:09:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
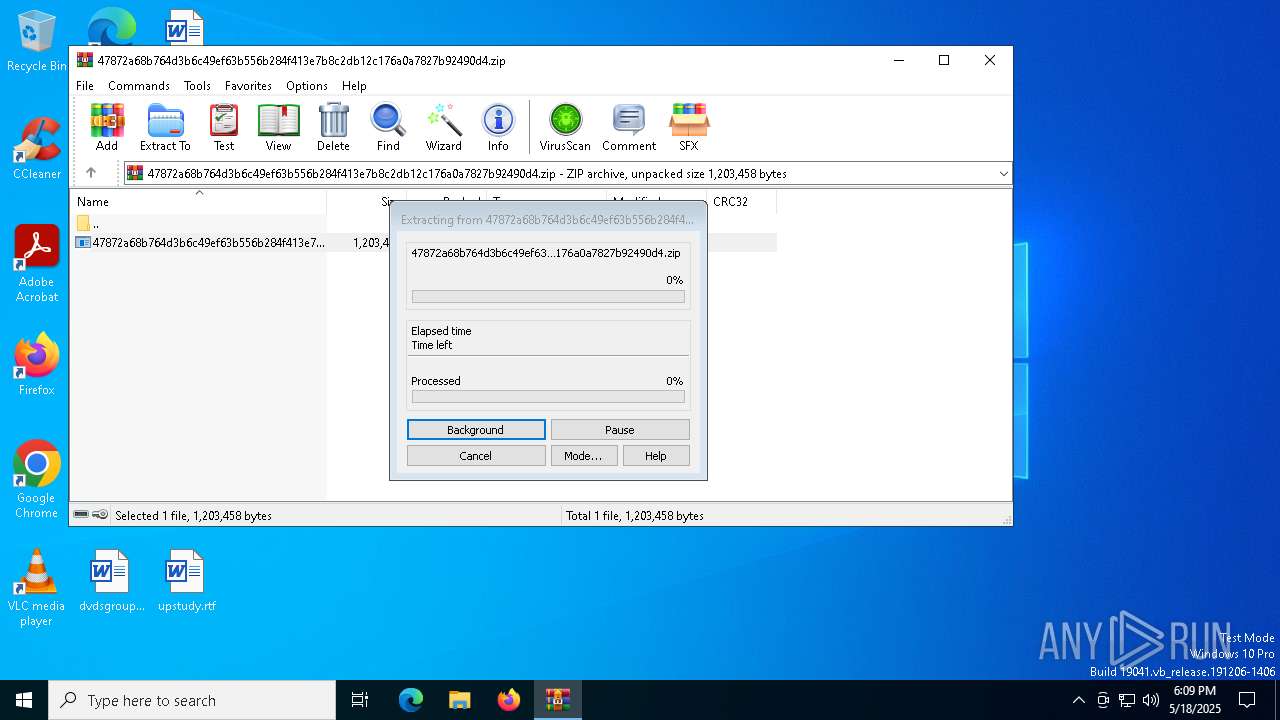
| MIME: | application/zip |
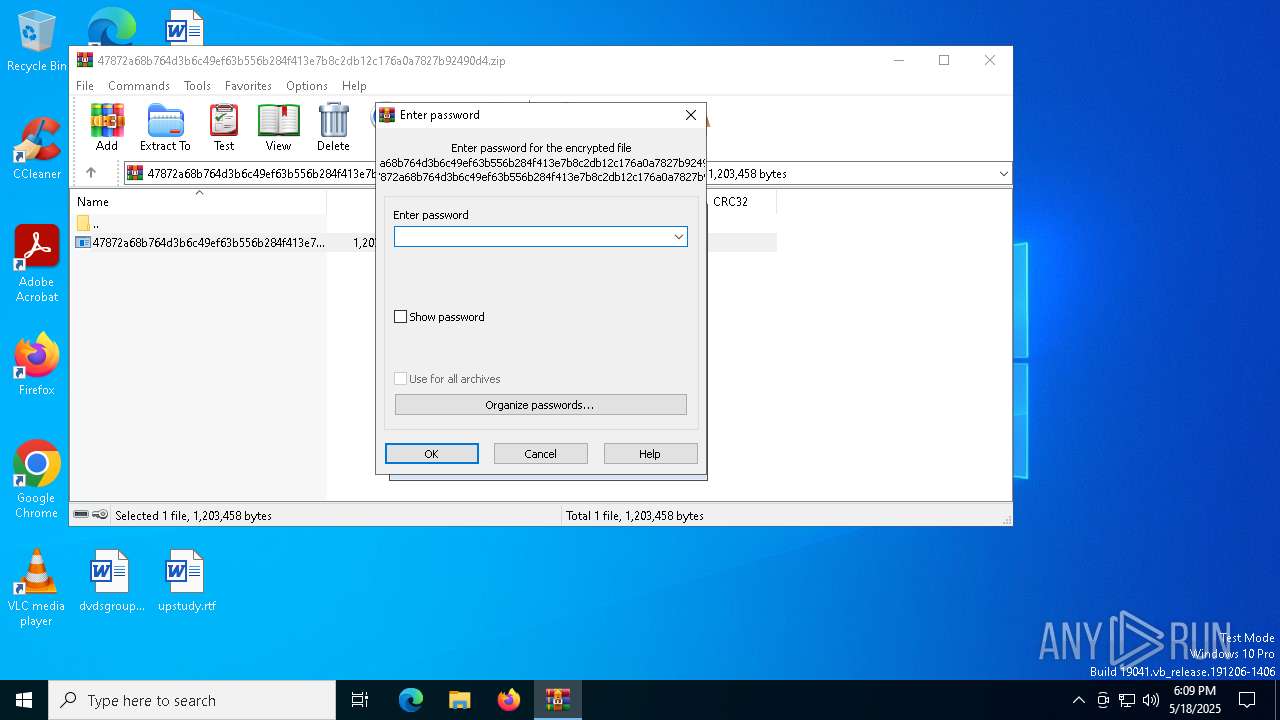
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 5337370A662F6680EF39691970407AF9 |
| SHA1: | 0C21578CEBCA71079C614B50B84E938B5CC3E6CC |
| SHA256: | 2EC7AF1F09FABF581D229CAAFAE8CA7872CCF64D70F67658E4E7E466CEBD0FC8 |
| SSDEEP: | 49152:PymE4lvZ5qlwlPUSLzhzILUlqqAM4QI+B4tdrCVnPislX9tMq1g64nC+RuSuY+HB:PY4VZjlM7LhqA9QPB4DCVnvN11SDsrVB |
MALICIOUS
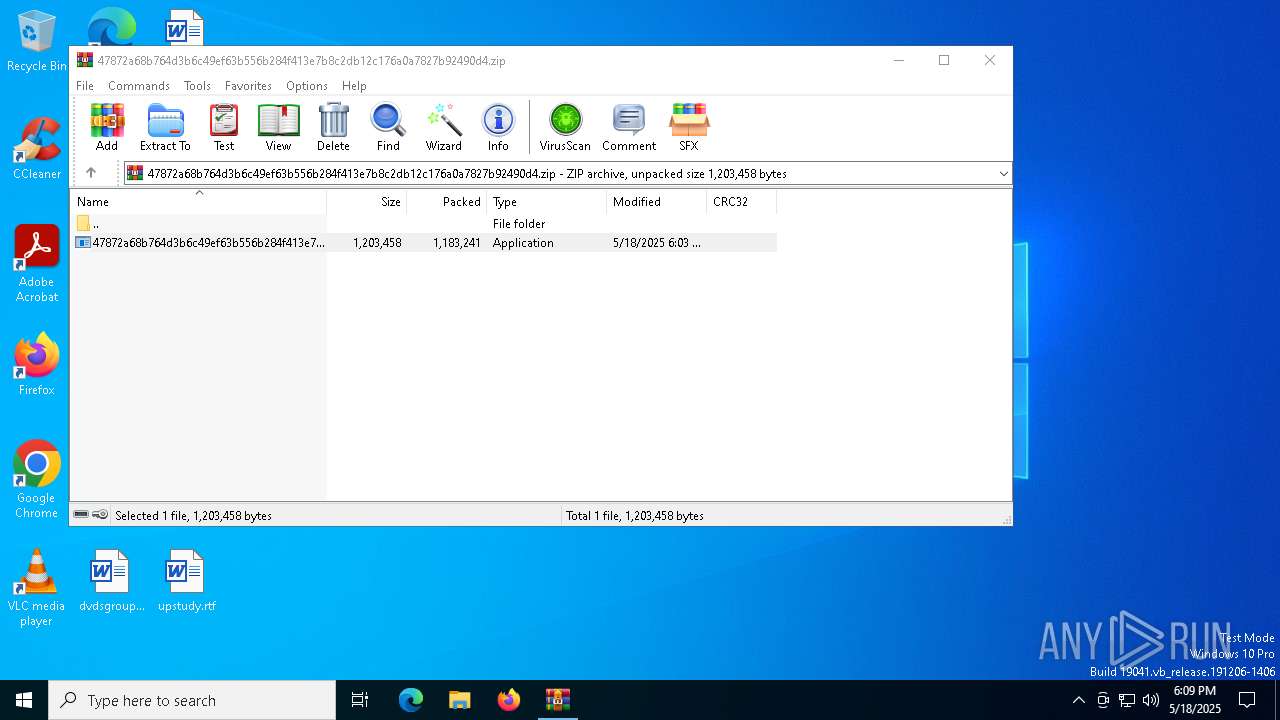
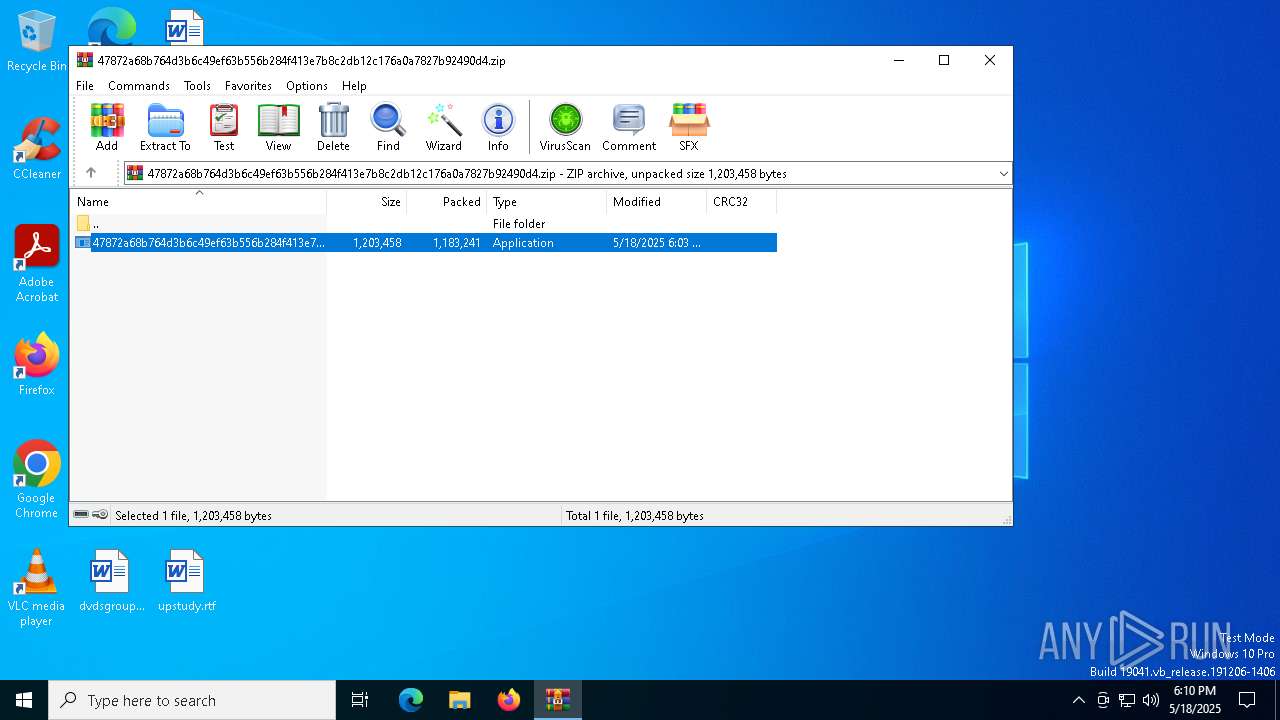
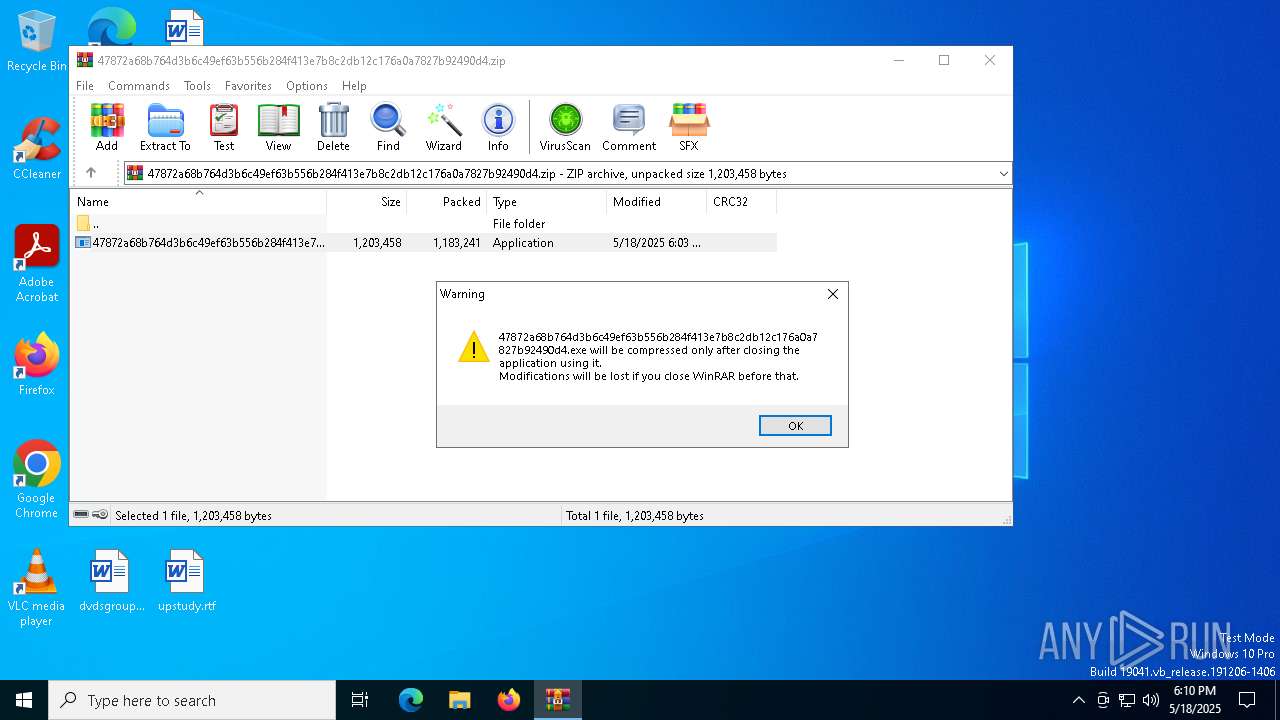
Generic archive extractor
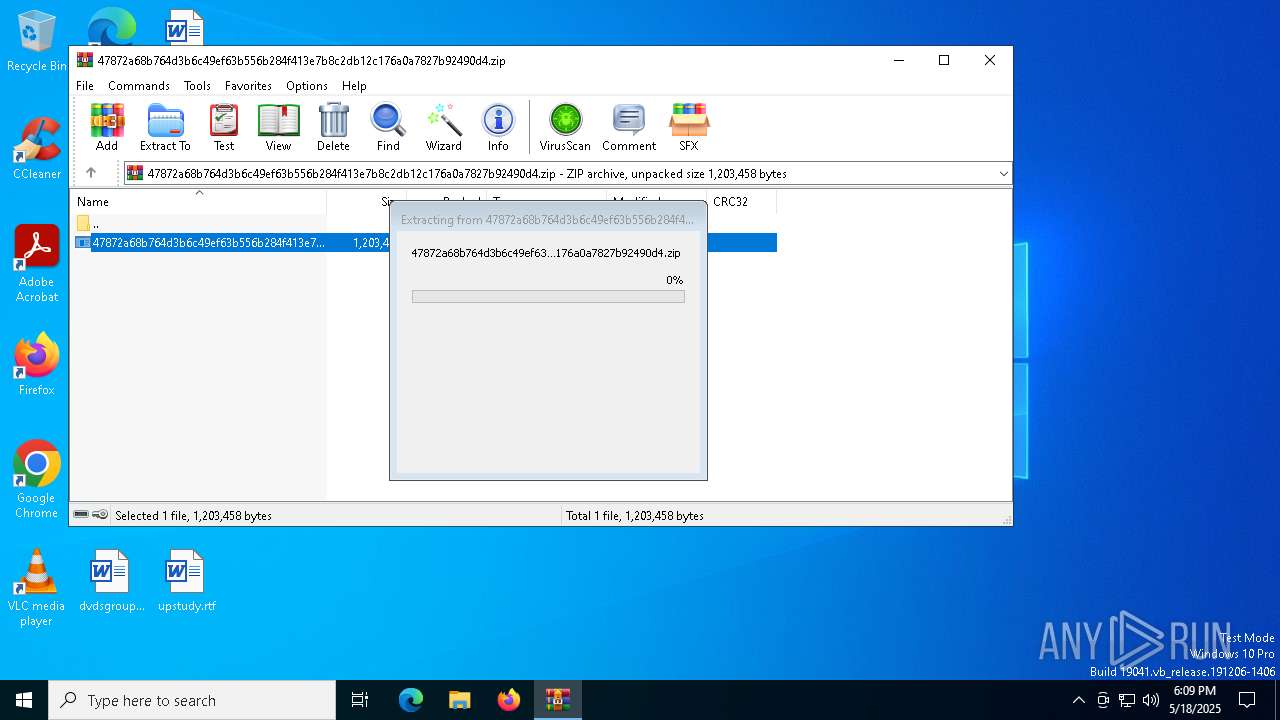
- WinRAR.exe (PID: 7504)
Actions looks like stealing of personal data
- Police.com (PID: 7204)
AutoIt loader has been detected (YARA)
- Police.com (PID: 7204)
LUMMA mutex has been found
- Police.com (PID: 7204)
Steals credentials from Web Browsers
- Police.com (PID: 7204)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7504)
- 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe (PID: 8100)
Executing commands from a ".bat" file
- 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe (PID: 8100)
Starts CMD.EXE for commands execution
- 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe (PID: 8100)
- cmd.exe (PID: 8148)
Get information on the list of running processes
- cmd.exe (PID: 8148)
Application launched itself
- cmd.exe (PID: 8148)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8148)
Starts application with an unusual extension
- cmd.exe (PID: 8148)
The executable file from the user directory is run by the CMD process
- Police.com (PID: 7204)
Starts the AutoIt3 executable file
- cmd.exe (PID: 8148)
There is functionality for taking screenshot (YARA)
- Police.com (PID: 7204)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Police.com (PID: 7204)
Searches for installed software
- Police.com (PID: 7204)
INFO
Create files in a temporary directory
- 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe (PID: 8100)
- extrac32.exe (PID: 7320)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7504)
Reads the computer name
- 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe (PID: 8100)
- extrac32.exe (PID: 7320)
- Police.com (PID: 7204)
Checks supported languages
- 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe (PID: 8100)
- extrac32.exe (PID: 7320)
- Police.com (PID: 7204)
Process checks computer location settings
- 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe (PID: 8100)
Creates a new folder
- cmd.exe (PID: 7316)
Reads mouse settings
- Police.com (PID: 7204)
Reads the software policy settings
- slui.exe (PID: 7688)
- Police.com (PID: 7204)
- slui.exe (PID: 7020)
Checks proxy server information
- slui.exe (PID: 7020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:18 18:03:12 |
| ZipCRC: | 0x9211f52d |
| ZipCompressedSize: | 1183241 |
| ZipUncompressedSize: | 1203458 |
| ZipFileName: | 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe |
Total processes
147
Monitored processes
17
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | cmd /c copy /b ..\Genius.mpg + ..\Statistics.mpg + ..\Gentle.mpg + ..\Prefers.mpg + ..\Pensions.mpg + ..\Instructor.mpg + ..\Small.mpg + ..\Rec.mpg T | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6068 | findstr "bdservicehost SophosHealth AvastUI AVGUI nsWscSvc ekrn" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7020 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7204 | Police.com T | C:\Users\admin\AppData\Local\Temp\497346\Police.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 7240 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7252 | findstr /V "checking" Realistic | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7272 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7316 | cmd /c md 497346 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 813
Read events
3 804
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.zip | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
20
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7320 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Fin | binary | |
MD5:09EA79C46A45F075FD10A0FF0521EFB9 | SHA256:0305EC11BC806F009002A53113BF1E32847FE87025614C57576F8E48A00DD61E | |||
| 7320 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Santa | binary | |
MD5:6DD20256C7FD89B4D9FA57FE6F8D8C24 | SHA256:841A8F9BF3E43E6DE831555C1A428369514A96FD769D79FCD64C89323A86D74B | |||
| 7504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7504.9708\47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe | executable | |
MD5:793CC97D16914EFC05E2573FB31616E5 | SHA256:47872A68B764D3B6C49EF63B556B284F413E7B8C2DB12C176A0A7827B92490D4 | |||
| 8100 | 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe | C:\Users\admin\AppData\Local\Temp\Rec.mpg | binary | |
MD5:4DDDB17822C57B52816E74E67C694DE6 | SHA256:261D1CB857B6F80D506079FDC877C0EB586D8289AC2E3F097AC5CB7D4B646E5B | |||
| 8100 | 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe | C:\Users\admin\AppData\Local\Temp\Prefers.mpg | binary | |
MD5:EF6BD4EDFF3BBEDBB98B61CCF1C0E1DF | SHA256:2138037A85499B271EB5AFB015CD37652FF8E6239AA0927B720141B194F752C9 | |||
| 8100 | 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe | C:\Users\admin\AppData\Local\Temp\Small.mpg | binary | |
MD5:5C75A958C80A283B6E6AD60C38DC9E46 | SHA256:DFEC60AD9A6CDEB14D78B9B424218E804F22AEC2A8F0F0B12B5A2D166E60F6B3 | |||
| 8100 | 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe | C:\Users\admin\AppData\Local\Temp\Dishes.mpg | compressed | |
MD5:2315EA1CFE6A661D27CF6BD1D8FF56A1 | SHA256:8D42625A02563B4B512DE1166888E69A4B4A3C55604EEA959DC9CCDAAB3D7E71 | |||
| 8100 | 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe | C:\Users\admin\AppData\Local\Temp\Genius.mpg | binary | |
MD5:9883842A781BA15AF904654D31BD4832 | SHA256:9CE0BC2F009A71AA620B2835A36DADD3D09FA5A0683FB36D5B3103331B277E9F | |||
| 8148 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Lithuania.mpg.bat | text | |
MD5:CFCF74C912478F52EEF5D109249AE0F2 | SHA256:2FD19D882075829554E6AF5C3454269320FD58F8E70279EB18FB0FF2928DC14A | |||
| 8100 | 47872a68b764d3b6c49ef63b556b284f413e7b8c2db12c176a0a7827b92490d4.exe | C:\Users\admin\AppData\Local\Temp\Lithuania.mpg | text | |
MD5:CFCF74C912478F52EEF5D109249AE0F2 | SHA256:2FD19D882075829554E6AF5C3454269320FD58F8E70279EB18FB0FF2928DC14A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7948 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7948 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4944 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
KkohxloJqyIpvzOKGSXHiPhpSSuH.KkohxloJqyIpvzOKGSXHiPhpSSuH |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
t.me |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7204 | Police.com | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |