analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | COMPANY PROFILE.exe |
| Full analysis: | https://app.any.run/tasks/69a2bc47-7469-466a-8b0d-7beea7340274 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | June 19, 2019, 16:01:13 |
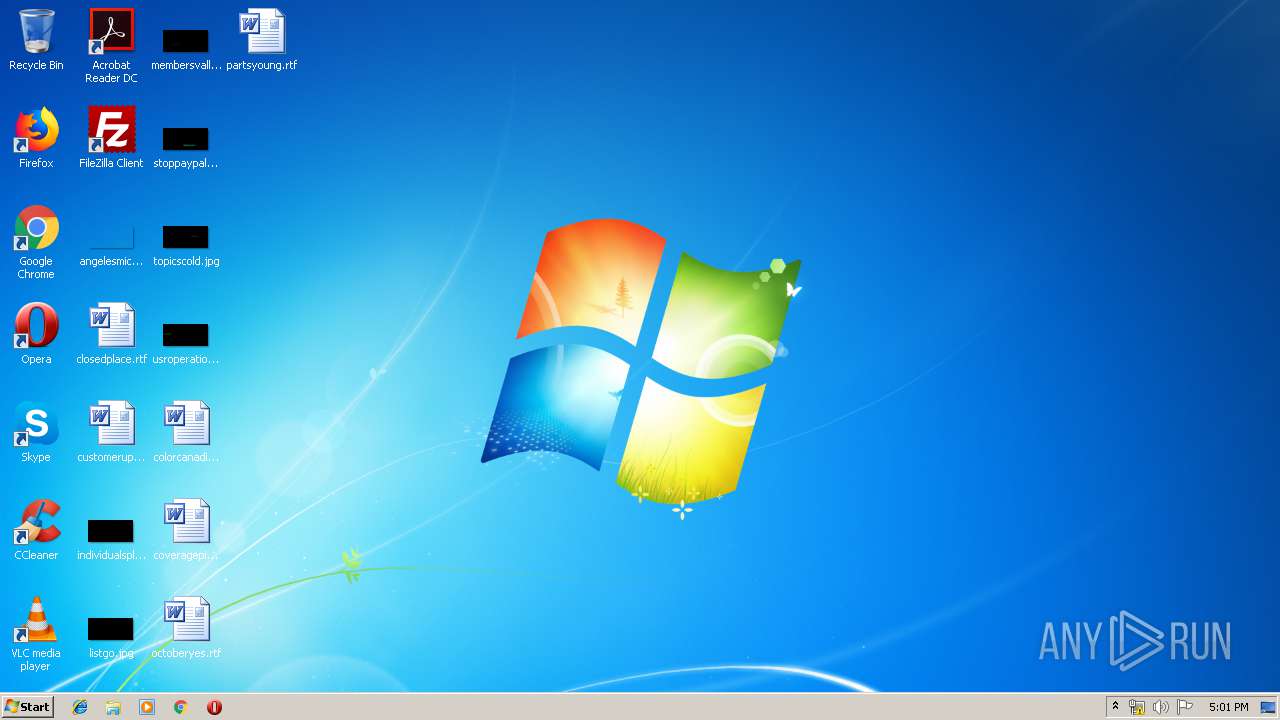
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 546E885B5FA21483C6AA7071CCF74790 |
| SHA1: | 571842D7197082420FDFDBFCA5A8C83E9EBC3754 |
| SHA256: | 2E800AC87E10F1DAACEE1FA4675D8297B7F3BEB06184C0539E5A49F2F5FEBF0F |
| SSDEEP: | 6144:d9hMeZGhba6GlONZT8yxjbxttGf6OtQ6ikagToO43dxORDuC9972IMeiVlakA5cv:+bapONhDbtHiviTgMOSB66estA |
MALICIOUS
Application was dropped or rewritten from another process
- vbc.exe (PID: 792)
- vbc.exe (PID: 1140)
- vbc.exe (PID: 3116)
- vbc.exe (PID: 1332)
- vbc.exe (PID: 3924)
- vbc.exe (PID: 544)
- vbc.exe (PID: 3264)
- vbc.exe (PID: 2984)
- vbc.exe (PID: 936)
- vbc.exe (PID: 4012)
- vbc.exe (PID: 1796)
- vbc.exe (PID: 2992)
- vbc.exe (PID: 3392)
- vbc.exe (PID: 1496)
- vbc.exe (PID: 3572)
- vbc.exe (PID: 4048)
- vbc.exe (PID: 760)
- vbc.exe (PID: 3780)
- vbc.exe (PID: 2960)
- vbc.exe (PID: 3152)
- vbc.exe (PID: 2608)
- vbc.exe (PID: 2104)
- vbc.exe (PID: 3948)
- vbc.exe (PID: 2268)
- vbc.exe (PID: 304)
- vbc.exe (PID: 3716)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 3608)
- vbc.exe (PID: 3064)
- vbc.exe (PID: 2128)
- vbc.exe (PID: 2436)
- vbc.exe (PID: 3328)
- vbc.exe (PID: 1024)
- vbc.exe (PID: 1232)
- vbc.exe (PID: 2812)
- vbc.exe (PID: 2112)
- vbc.exe (PID: 2036)
- vbc.exe (PID: 2756)
- vbc.exe (PID: 3816)
- vbc.exe (PID: 3548)
- vbc.exe (PID: 2900)
- vbc.exe (PID: 1820)
- vbc.exe (PID: 3872)
LOKIBOT was detected
- vbc.exe (PID: 1140)
- vbc.exe (PID: 1796)
- vbc.exe (PID: 3392)
- vbc.exe (PID: 3572)
- vbc.exe (PID: 2960)
- vbc.exe (PID: 2608)
- vbc.exe (PID: 304)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 3608)
- vbc.exe (PID: 2036)
- vbc.exe (PID: 3816)
- vbc.exe (PID: 2900)
Connects to CnC server
- vbc.exe (PID: 1140)
- vbc.exe (PID: 3116)
- vbc.exe (PID: 2984)
- vbc.exe (PID: 3924)
- vbc.exe (PID: 544)
- vbc.exe (PID: 1796)
- vbc.exe (PID: 3392)
- vbc.exe (PID: 3572)
- vbc.exe (PID: 760)
- vbc.exe (PID: 2960)
- vbc.exe (PID: 2608)
- vbc.exe (PID: 2104)
- vbc.exe (PID: 304)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 3608)
- vbc.exe (PID: 2436)
- vbc.exe (PID: 3328)
- vbc.exe (PID: 2812)
- vbc.exe (PID: 2036)
- vbc.exe (PID: 3816)
- vbc.exe (PID: 2900)
- vbc.exe (PID: 3872)
Detected artifacts of LokiBot
- vbc.exe (PID: 3116)
- vbc.exe (PID: 1140)
- vbc.exe (PID: 544)
- vbc.exe (PID: 2984)
- vbc.exe (PID: 3924)
- vbc.exe (PID: 1796)
- vbc.exe (PID: 3392)
- vbc.exe (PID: 3572)
- vbc.exe (PID: 760)
- vbc.exe (PID: 2960)
- vbc.exe (PID: 2608)
- vbc.exe (PID: 2104)
- vbc.exe (PID: 304)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 3608)
- vbc.exe (PID: 2436)
- vbc.exe (PID: 3328)
- vbc.exe (PID: 2812)
- vbc.exe (PID: 2036)
- vbc.exe (PID: 3816)
- vbc.exe (PID: 2900)
- vbc.exe (PID: 3872)
Actions looks like stealing of personal data
- vbc.exe (PID: 3116)
- vbc.exe (PID: 1140)
- vbc.exe (PID: 2984)
- vbc.exe (PID: 544)
- vbc.exe (PID: 3924)
- vbc.exe (PID: 1796)
- vbc.exe (PID: 3392)
- vbc.exe (PID: 3572)
- vbc.exe (PID: 760)
- vbc.exe (PID: 2960)
- vbc.exe (PID: 2104)
- vbc.exe (PID: 2608)
- vbc.exe (PID: 304)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 3608)
- vbc.exe (PID: 2436)
- vbc.exe (PID: 3328)
- vbc.exe (PID: 2812)
- vbc.exe (PID: 2036)
- vbc.exe (PID: 3816)
- vbc.exe (PID: 2900)
- vbc.exe (PID: 3872)
SUSPICIOUS
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3924)
- vbc.exe (PID: 1140)
- vbc.exe (PID: 3116)
- vbc.exe (PID: 544)
- vbc.exe (PID: 2984)
- vbc.exe (PID: 1796)
- vbc.exe (PID: 3392)
- vbc.exe (PID: 3572)
- vbc.exe (PID: 760)
- vbc.exe (PID: 2960)
- vbc.exe (PID: 2608)
- vbc.exe (PID: 2104)
- vbc.exe (PID: 304)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 3608)
- vbc.exe (PID: 2436)
- vbc.exe (PID: 3328)
- vbc.exe (PID: 2812)
- vbc.exe (PID: 2036)
- vbc.exe (PID: 3816)
- vbc.exe (PID: 2900)
- vbc.exe (PID: 3872)
Creates files in the user directory
- vbc.exe (PID: 1140)
- vbc.exe (PID: 3116)
- vbc.exe (PID: 544)
- vbc.exe (PID: 3924)
- vbc.exe (PID: 2984)
- vbc.exe (PID: 1796)
- vbc.exe (PID: 3392)
- vbc.exe (PID: 3572)
- vbc.exe (PID: 760)
- vbc.exe (PID: 2960)
- vbc.exe (PID: 2608)
- vbc.exe (PID: 2104)
- vbc.exe (PID: 304)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 3608)
- vbc.exe (PID: 2436)
- vbc.exe (PID: 3328)
- vbc.exe (PID: 2812)
- vbc.exe (PID: 2036)
- vbc.exe (PID: 3816)
- vbc.exe (PID: 2900)
- vbc.exe (PID: 3872)
Executable content was dropped or overwritten
- vbc.exe (PID: 1140)
Executes scripts
- COMPANY PROFILE.exe (PID: 3280)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x4466e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 238080 |
| CodeSize: | 272384 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2019:05:12 16:18:33+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-May-2019 14:18:33 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-May-2019 14:18:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00042674 | 0x00042800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.93603 |
.rsrc | 0x00046000 | 0x00039E58 | 0x0003A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.71697 |
.reloc | 0x00080000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
128 | 7.72475 | 237056 | Latin 1 / Western European | German - Germany | RT_HTML |
Imports
mscoree.dll |
Total processes
75
Monitored processes
44
Malicious processes
23
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3280 | "C:\Users\admin\AppData\Local\Temp\COMPANY PROFILE.exe" | C:\Users\admin\AppData\Local\Temp\COMPANY PROFILE.exe | — | explorer.exe |
User: admin Integrity Level: MEDIUM | ||||
| 1140 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | COMPANY PROFILE.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 3221225477 Version: 8.0.50727.5420 | ||||
| 792 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | COMPANY PROFILE.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 8.0.50727.5420 | ||||
| 3116 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | COMPANY PROFILE.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 3221225477 Version: 8.0.50727.5420 | ||||
| 1332 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | COMPANY PROFILE.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 8.0.50727.5420 | ||||
| 3924 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | COMPANY PROFILE.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 3221225477 Version: 8.0.50727.5420 | ||||
| 3264 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | COMPANY PROFILE.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 8.0.50727.5420 | ||||
| 2984 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | COMPANY PROFILE.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 3221225477 Version: 8.0.50727.5420 | ||||
| 936 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | COMPANY PROFILE.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 8.0.50727.5420 | ||||
| 544 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | COMPANY PROFILE.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 3221225477 Version: 8.0.50727.5420 | ||||
Total events
640
Read events
618
Write events
22
Delete events
0
Modification events
| (PID) Process: | (1140) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (3116) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (3924) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (2984) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (544) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (1796) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (3392) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (3572) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (760) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
| (PID) Process: | (2960) vbc.exe | Key: | HKEY_CURRENT_USER\������Д���������ќ�і�Е�Е�Я����Й���Й��я�� |
| Operation: | write | Name: | F63AAA |
Value: %APPDATA%\F63AAA\A71D80.exe | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
90
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1140 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 3116 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 3924 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 2984 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 544 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 1796 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 3392 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 3572 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 760 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 2960 | vbc.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
67
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1140 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
3924 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
3392 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
544 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
3116 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
544 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
1796 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
1796 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
3116 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
2984 | vbc.exe | POST | 302 | 208.91.198.102:80 | http://keralacabs.co.in/js/js/Panel/five/fre.php | US | html | 233 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
1796 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
2984 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
3392 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
544 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
3116 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
3924 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
1140 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
2960 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
760 | vbc.exe | 208.91.198.102:80 | keralacabs.co.in | PDR | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
keralacabs.co.in |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1140 | vbc.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
1140 | vbc.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
1140 | vbc.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
1140 | vbc.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
1140 | vbc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
1140 | vbc.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
1140 | vbc.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
1140 | vbc.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
1140 | vbc.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
1140 | vbc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
66 ETPRO signatures available at the full report