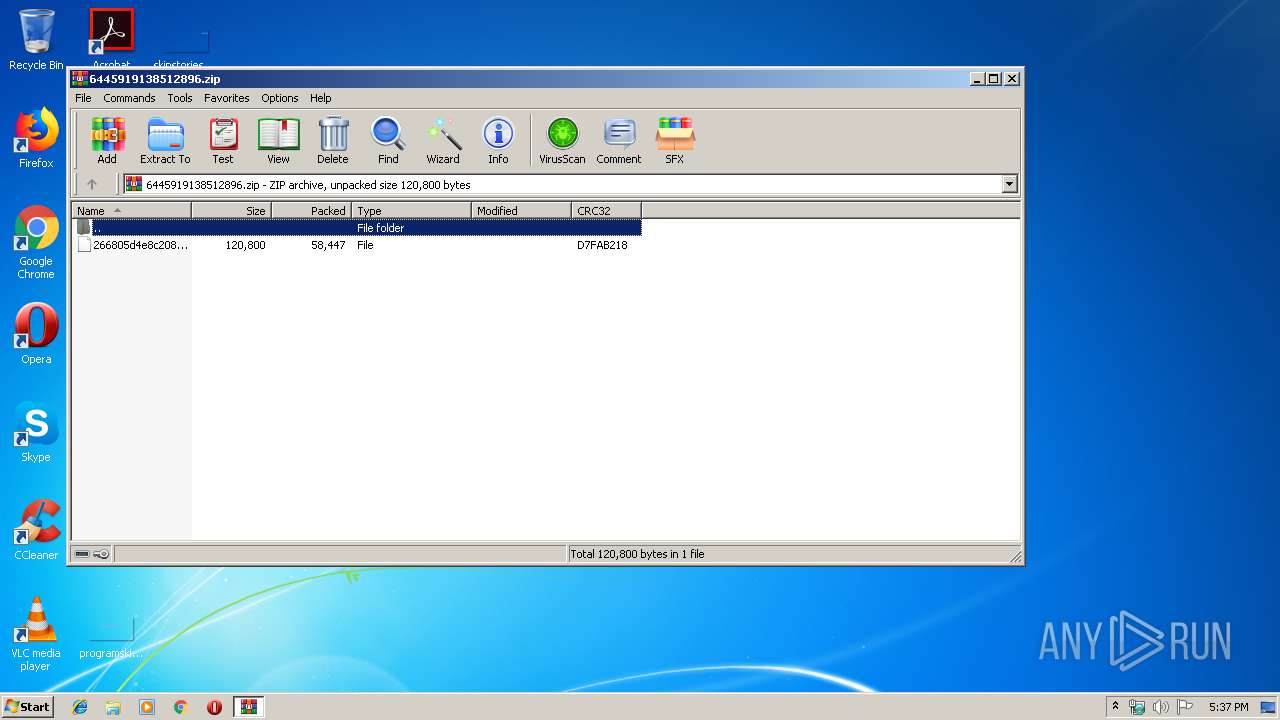
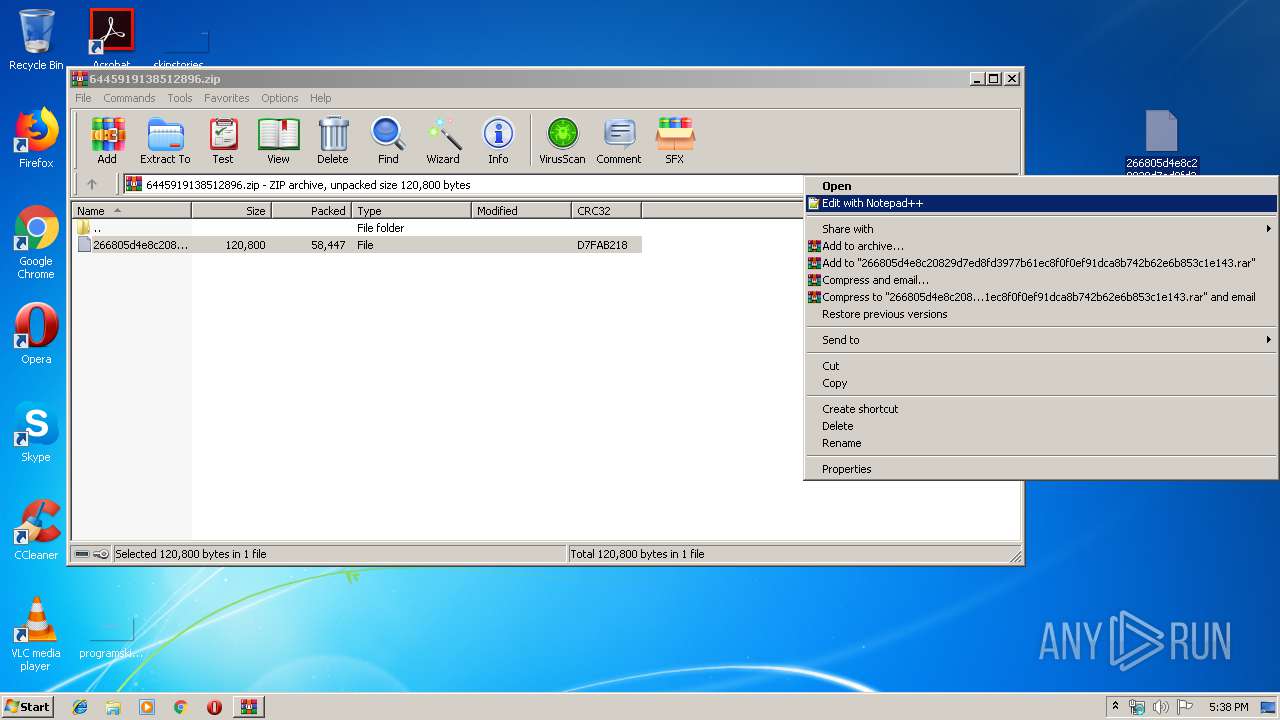
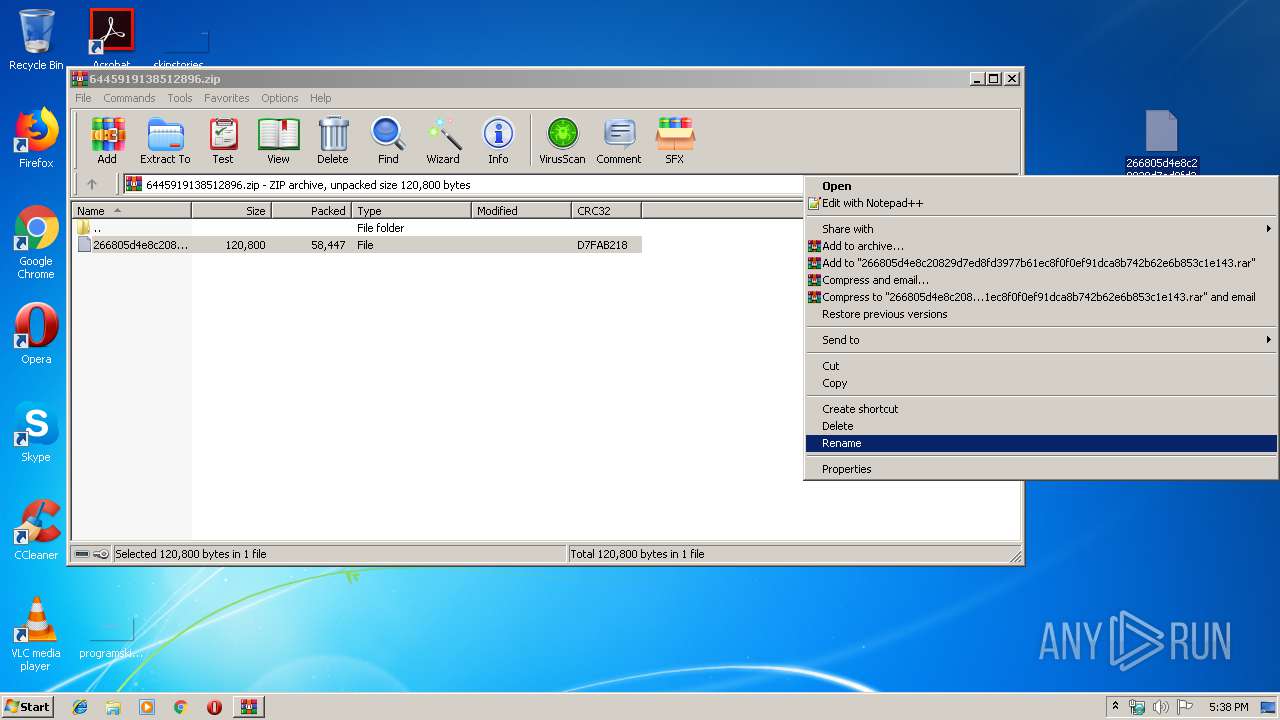
| File name: | 6445919138512896.zip |
| Full analysis: | https://app.any.run/tasks/79fc5871-729b-43a5-bacf-bfef26657fed |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | January 17, 2020, 17:37:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9F7D8B0E7999CD4998C8E32026B46A10 |
| SHA1: | 6A6AB852AC06530FBF78B88A9654F678D0FF33FB |
| SHA256: | 2E31F160A426AE27C1A371734A95E84E4E6267A56AB3955FC9783E49CDC56B80 |
| SSDEEP: | 1536:ejhDIKFHYuarqJbndD15nJligVvag4w2l9:0hkKF4wpnnJliavFQL |
MALICIOUS
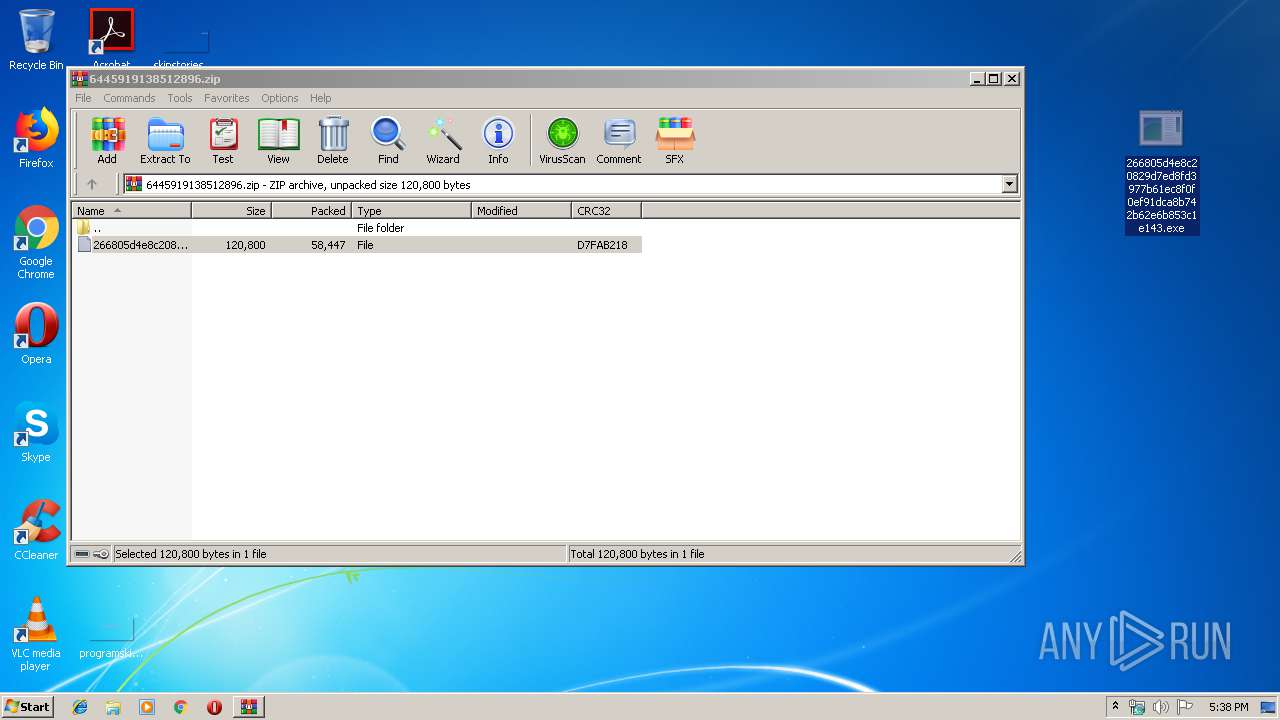
Application was dropped or rewritten from another process
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 2612)
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
Detected Pony/Fareit Trojan
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
Connects to CnC server
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
Actions looks like stealing of personal data
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
SUSPICIOUS
Changes tracing settings of the file or console
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
Creates files in the user directory
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
Starts CMD.EXE for commands execution
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
Connects to server without host name
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
Searches for installed software
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
Starts CMD.EXE for self-deleting
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 4048)
INFO
Manual execution by user
- 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe (PID: 2612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xd7fab218 |
| ZipCompressedSize: | 58447 |
| ZipUncompressedSize: | 120800 |
| ZipFileName: | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143 |
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2612 | "C:\Users\admin\Desktop\266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe" | C:\Users\admin\Desktop\266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 2684 | cmd.exe /c ping 127.0.0.1 & del /F /Q "C:\Users\admin\Desktop\266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe" | C:\Windows\system32\cmd.exe | — | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3900 | ping 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4048 | C:\Users\admin\Desktop\266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe dfsr | C:\Users\admin\Desktop\266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
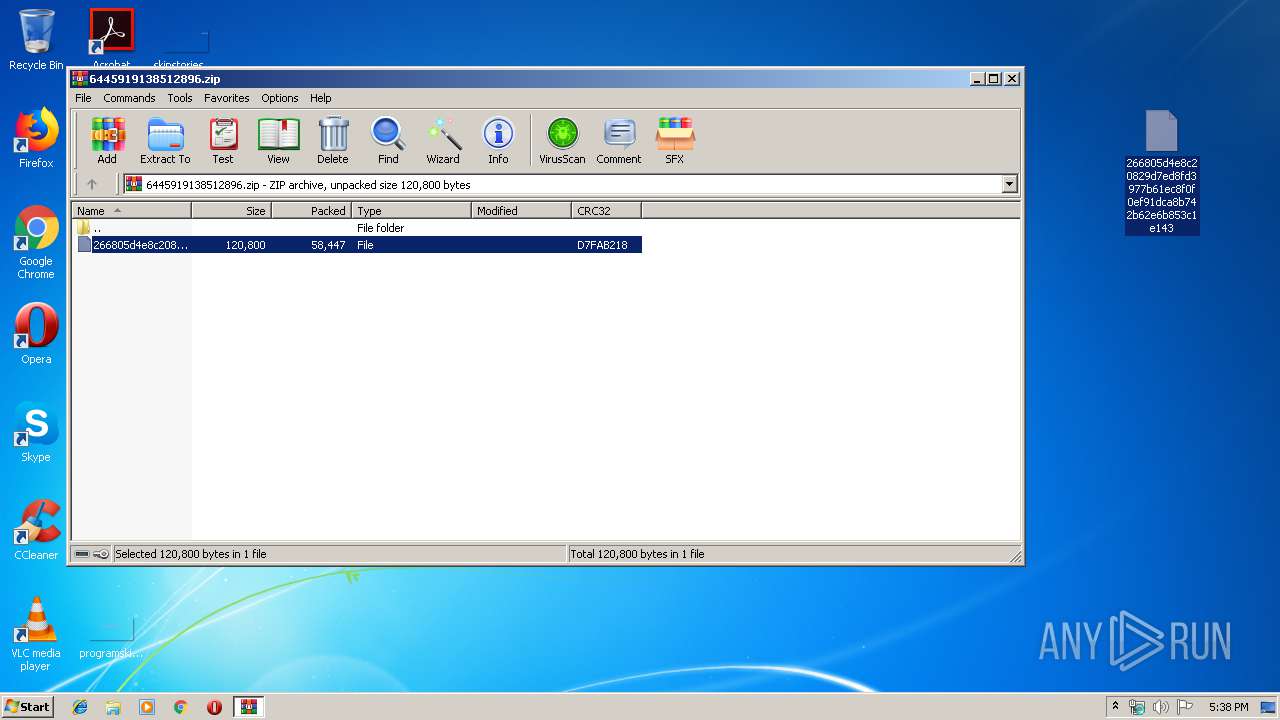
| 4056 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\6445919138512896.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
532
Read events
487
Write events
45
Delete events
0
Modification events
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\6445919138512896.zip | |||
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
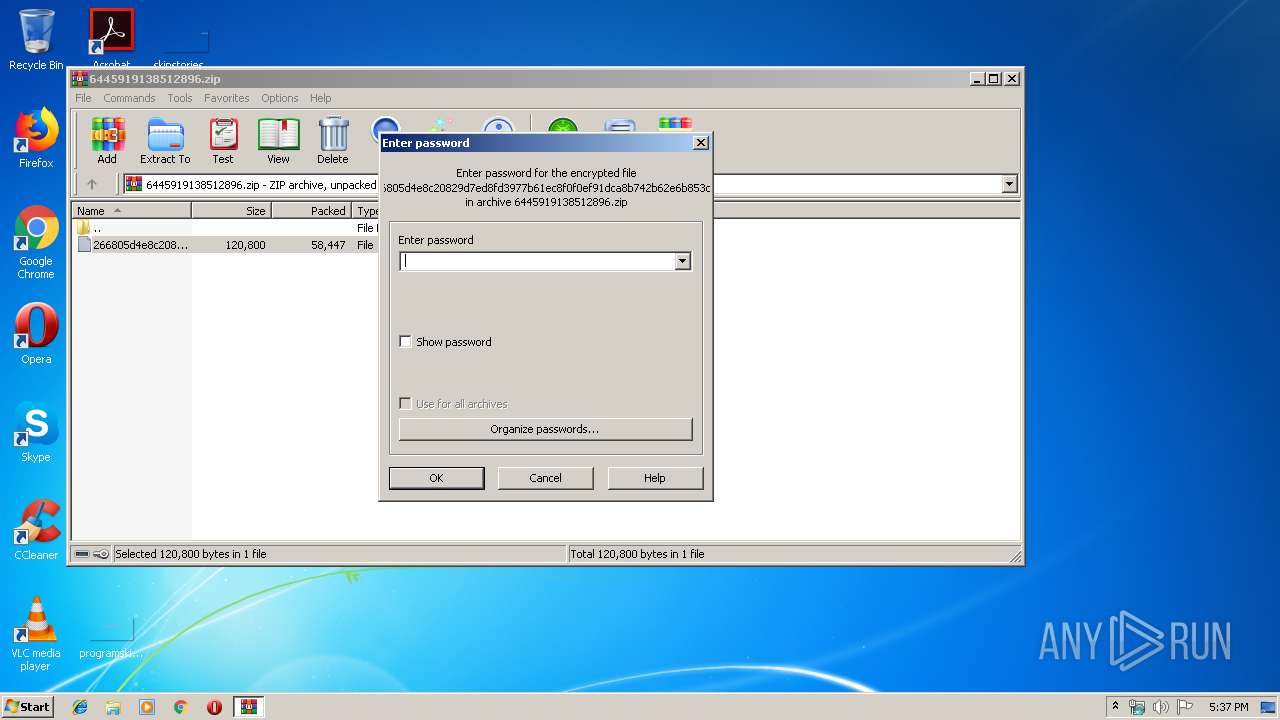
| (PID) Process: | (4056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
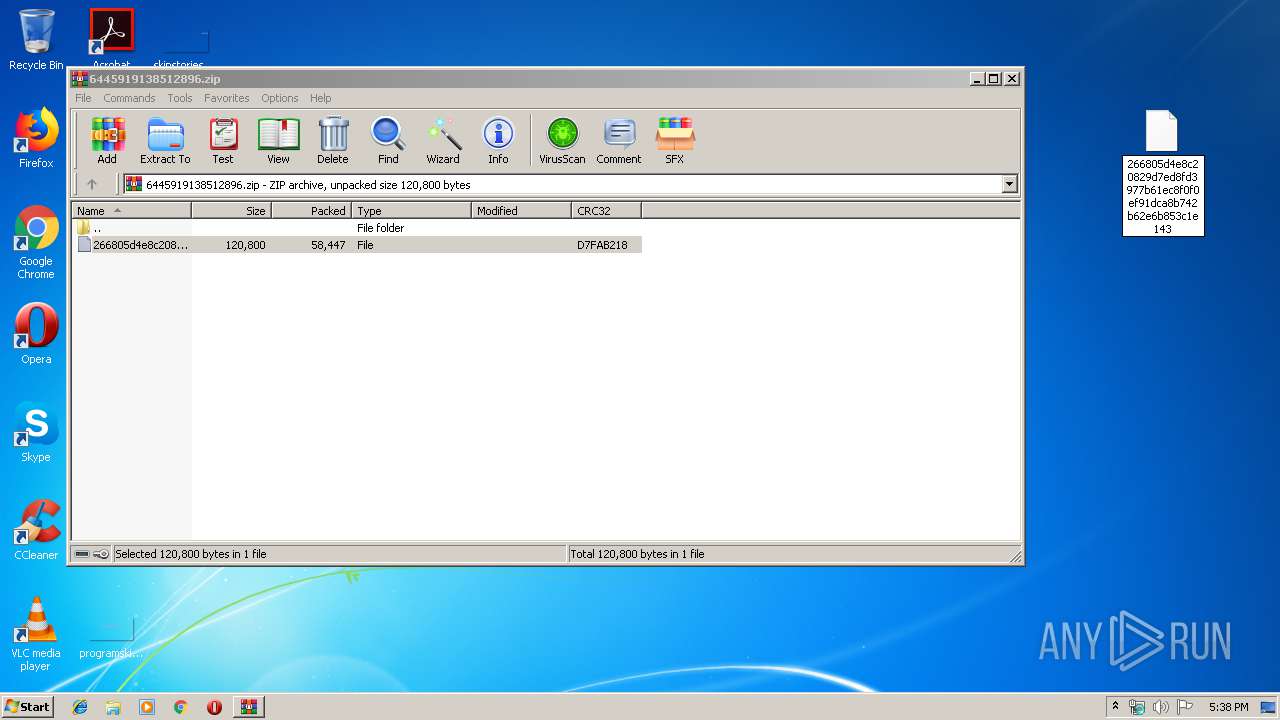
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4056 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4056.17831\266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143 | — | |
MD5:— | SHA256:— | |||
| 4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@blockcypher[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | GET | 200 | 195.123.220.107:80 | http://195.123.220.107/viewtopic.php?f576=0?f948=61646d696e?f783=555345522d5043 | NL | binary | 97.0 Kb | malicious |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | POST | — | 195.123.220.107:80 | http://195.123.220.107/p/g_38472341.php | NL | — | — | malicious |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | POST | — | 195.123.220.107:80 | http://195.123.220.107/p/g_38472341.php | NL | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 195.123.220.107:80 | — | ITL Company | NL | malicious |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | 104.16.54.3:443 | blockchain.info | Cloudflare Inc | US | shared |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | 195.123.220.107:80 | — | ITL Company | NL | malicious |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | 104.20.20.251:443 | api.blockcypher.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blockchain.info |
| shared |
api.blockcypher.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | A Network Trojan was detected | MALWARE [PTsecurity] RTM.Payload.xor |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony Downloader |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | A Network Trojan was detected | MALWARE [PTsecurity] Pony encrypted POST Data Request |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony Downloader |
4048 | 266805d4e8c20829d7ed8fd3977b61ec8f0f0ef91dca8b742b62e6b853c1e143.exe | A Network Trojan was detected | MALWARE [PTsecurity] Pony encrypted POST Data Request |