| File name: | 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe |
| Full analysis: | https://app.any.run/tasks/ab59dc49-f73d-4f44-9745-c47cd6a2a11a |
| Verdict: | Malicious activity |
| Threats: | Chaos ransomware is a malware family known for its destructive capabilities and diverse variants. It first appeared in 2021 as a ransomware builder and later acted as a wiper. Unlike most ransomware strains that encrypt data to extort payment, early Chaos variants permanently corrupted files, while later versions adopted more conventional encryption techniques. |
| Analysis date: | January 08, 2025, 08:19:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 95BE77DAC172C472CBA318F9876EC444 |
| SHA1: | E24FC0A73FF5675A33DE6BF033B65FA4B139D85A |
| SHA256: | 2DD3144AB294D675EAE0290D5B2D385D4D7DDB36E0450B982358A1519BA19FB4 |
| SSDEEP: | 49152:Z1WDsGsL5TCvRc46CCGZuoKzzkvhctESbe7t0G8IfPIu3GTJ: |
MALICIOUS
Changes the autorun value in the registry
- svchost.exe (PID: 6436)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 3524)
Deletes shadow copies
- cmd.exe (PID: 4136)
- cmd.exe (PID: 6896)
Create files in the Startup directory
- svchost.exe (PID: 6436)
Steals credentials from Web Browsers
- svchost.exe (PID: 6436)
Actions looks like stealing of personal data
- svchost.exe (PID: 6436)
Modifies files in the Chrome extension folder
- svchost.exe (PID: 6436)
CHAOS has been detected (YARA)
- svchost.exe (PID: 6436)
SUSPICIOUS
Executable content was dropped or overwritten
- 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe (PID: 4428)
Reads security settings of Internet Explorer
- 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe (PID: 4428)
- svchost.exe (PID: 6436)
The process creates files with name similar to system file names
- 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe (PID: 4428)
Starts itself from another location
- 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe (PID: 4428)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 6436)
Reads the date of Windows installation
- svchost.exe (PID: 6436)
Executes as Windows Service
- wbengine.exe (PID: 5008)
- VSSVC.exe (PID: 6988)
- vds.exe (PID: 6420)
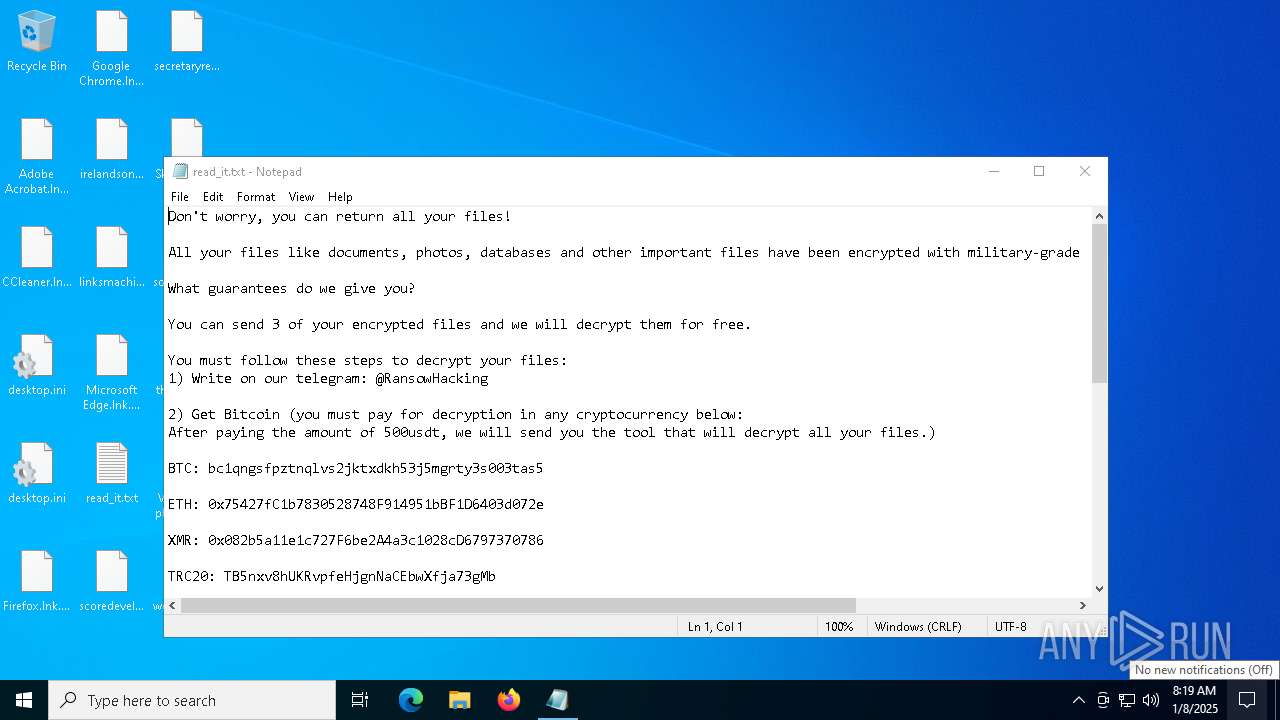
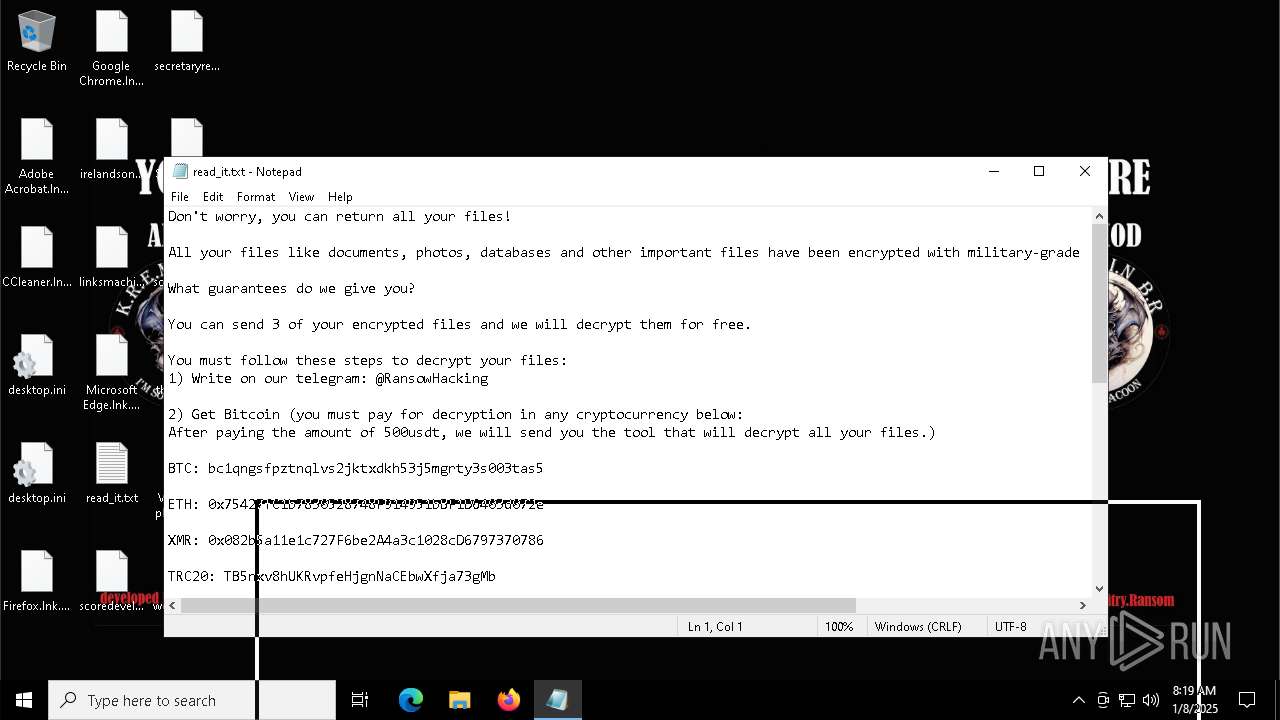
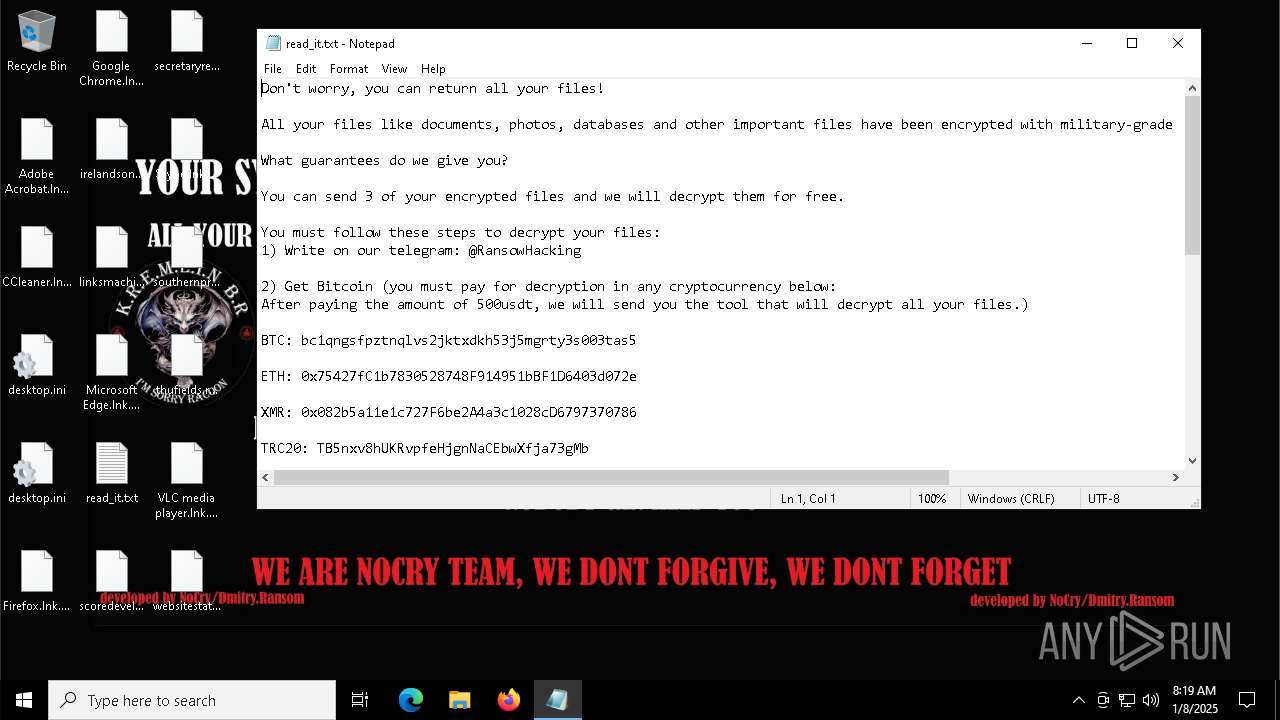
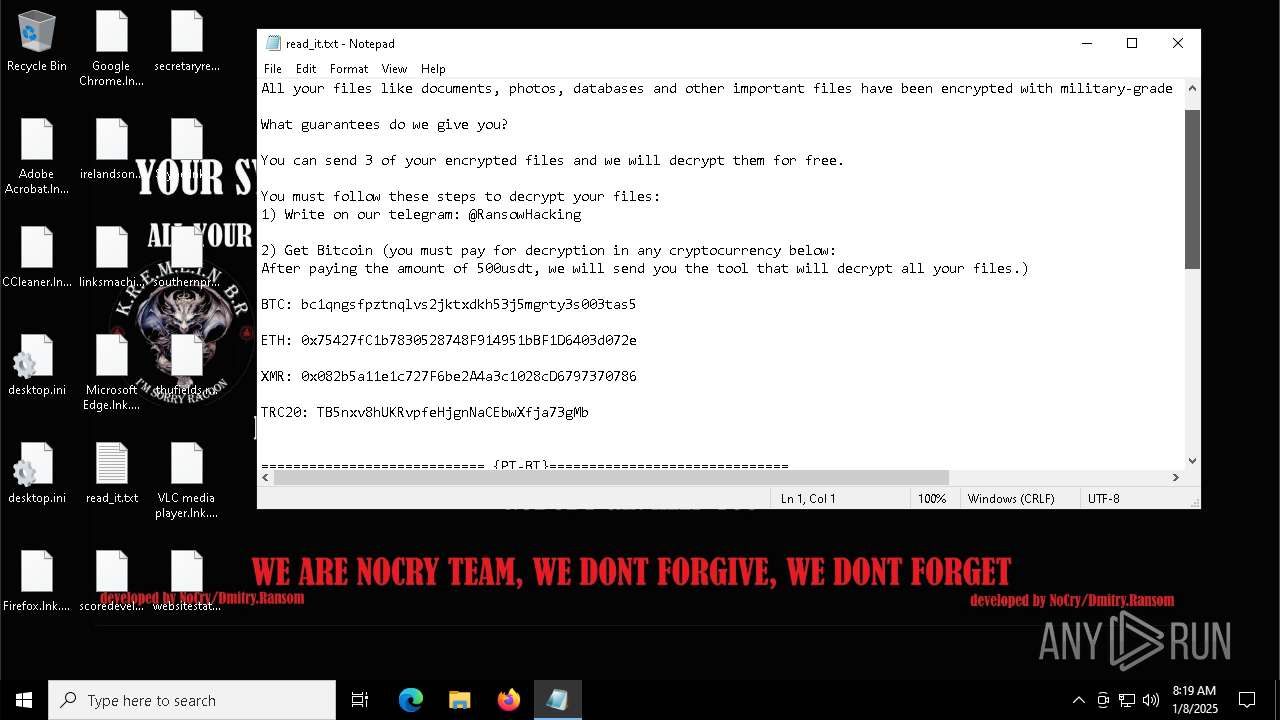
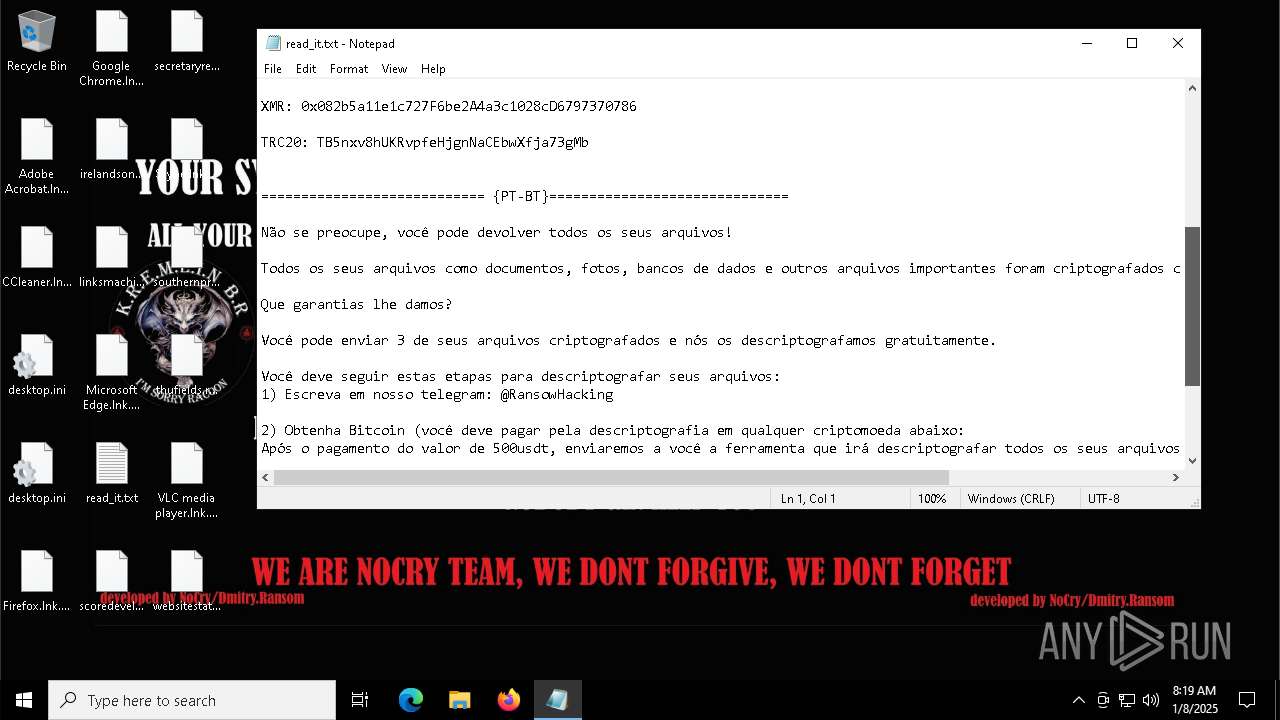
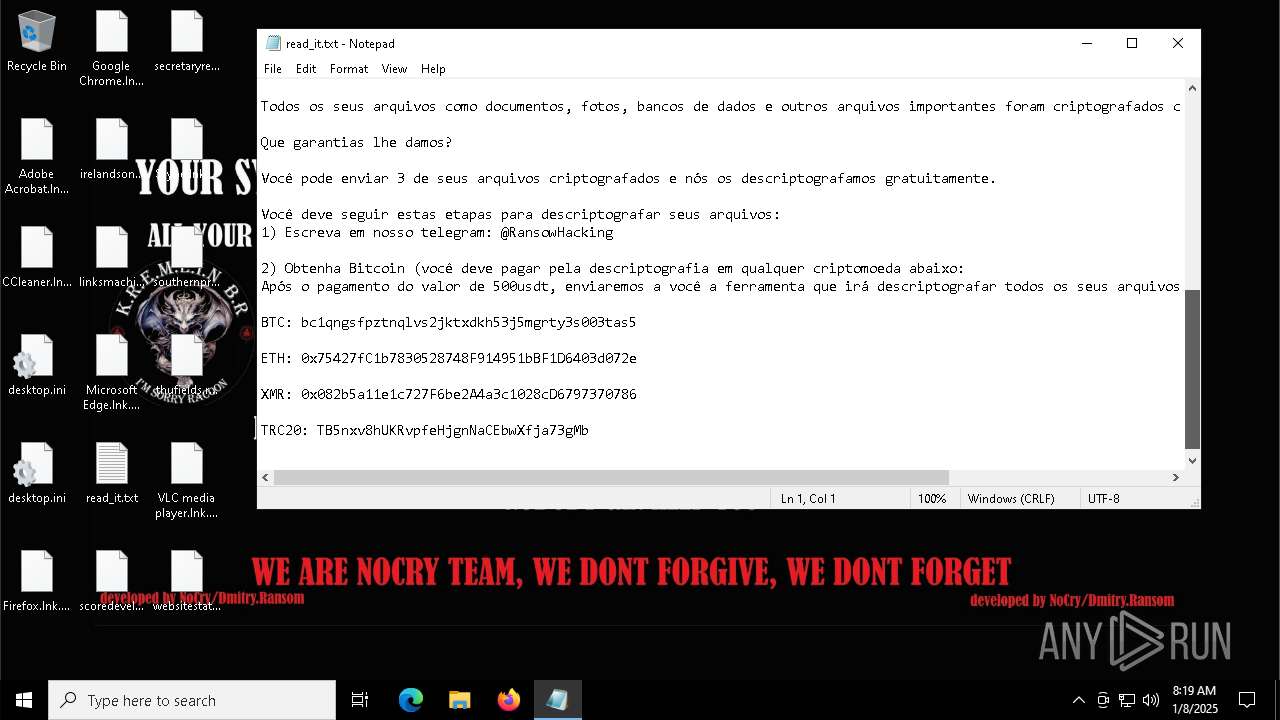
Start notepad (likely ransomware note)
- svchost.exe (PID: 6436)
Found regular expressions for crypto-addresses (YARA)
- svchost.exe (PID: 6436)
INFO
Reads the computer name
- 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe (PID: 4428)
- svchost.exe (PID: 6436)
Checks supported languages
- 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe (PID: 4428)
- svchost.exe (PID: 6436)
Reads the machine GUID from the registry
- 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe (PID: 4428)
- svchost.exe (PID: 6436)
Creates files or folders in the user directory
- 2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe (PID: 4428)
- svchost.exe (PID: 6436)
Process checks computer location settings
- svchost.exe (PID: 6436)
The process uses the downloaded file
- svchost.exe (PID: 6436)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7100)
Creates files in the program directory
- svchost.exe (PID: 6436)
Reads Microsoft Office registry keys
- svchost.exe (PID: 6436)
Create files in a temporary directory
- svchost.exe (PID: 6436)
Sends debugging messages
- wbadmin.exe (PID: 5548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:01:05 21:35:08+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 6600192 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x64d57e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | NoCry Hagnarock.exe |
| LegalCopyright: | |
| OriginalFileName: | NoCry Hagnarock.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
146
Monitored processes
18
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3524 | "C:\Windows\System32\cmd.exe" /C bcdedit /set {default} bootstatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4136 | "C:\Windows\System32\cmd.exe" /C wbadmin delete catalog -quiet | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | bcdedit /set {default} recoveryenabled no | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | "C:\Users\admin\AppData\Local\Temp\2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe" | C:\Users\admin\AppData\Local\Temp\2dd3144ab294d675eae0290d5b2d385d4d7ddb36e0450b982358a1519ba19fb4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 1 Version: 0.0.0.0 Modules
| |||||||||||||||
| 5000 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | "C:\WINDOWS\system32\wbengine.exe" | C:\Windows\System32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5236 | C:\WINDOWS\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5460 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | wbadmin delete catalog -quiet | C:\Windows\System32\wbadmin.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 874
Read events
4 837
Write events
19
Delete events
18
Modification events
| (PID) Process: | (6436) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | UpdateTask |
Value: C:\Users\admin\AppData\Roaming\svchost.exe | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Boot\Loader.efi | |||
| (PID) Process: | (4244) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Description |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
1
Suspicious files
536
Text files
873
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6436 | svchost.exe | C:\$WinREAgent\Backup\read_it.txt | text | |
MD5:3E2B5192E7CA51E0BD3FE0910B680EE6 | SHA256:897DA642F47D00BC703E62B3E9D451AB24AF1EC742DFE739C924A02A56988C61 | |||
| 6436 | svchost.exe | C:\$WinREAgent\RollbackInfo.ini | binary | |
MD5:D1457B72C3FB323A2671125AEF3EAB5D | SHA256:8A8DE823D5ED3E12746A62EF169BCF372BE0CA44F0A1236ABC35DF05D96928E1 | |||
| 6436 | svchost.exe | C:\Recovery\OEM\ResetConfig.xml.NoCry | binary | |
MD5:895E9EC5819D3DADBFE8B507DC9E0BE6 | SHA256:C7AD4BF69F72DCDE132ECC8B48A2A565B1E77D927A524F40202580323FC3EE78 | |||
| 6436 | svchost.exe | C:\found.000\dir0001.chk\read_it.txt | text | |
MD5:3E2B5192E7CA51E0BD3FE0910B680EE6 | SHA256:897DA642F47D00BC703E62B3E9D451AB24AF1EC742DFE739C924A02A56988C61 | |||
| 6436 | svchost.exe | C:\$WinREAgent\read_it.txt | text | |
MD5:3E2B5192E7CA51E0BD3FE0910B680EE6 | SHA256:897DA642F47D00BC703E62B3E9D451AB24AF1EC742DFE739C924A02A56988C61 | |||
| 6436 | svchost.exe | C:\found.000\dir0001.chk\WmiApRpl.ini | binary | |
MD5:D1457B72C3FB323A2671125AEF3EAB5D | SHA256:8A8DE823D5ED3E12746A62EF169BCF372BE0CA44F0A1236ABC35DF05D96928E1 | |||
| 6436 | svchost.exe | C:\$WinREAgent\Backup\ReAgent.xml.NoCry | binary | |
MD5:990D05D8C41AB88321AFB31F56A7CF53 | SHA256:EAA11661D8072B37521CFEC1F31E97691B1F2867346780EBF966EA46DCC69CB0 | |||
| 6436 | svchost.exe | C:\$WinREAgent\Rollback.xml | binary | |
MD5:D1457B72C3FB323A2671125AEF3EAB5D | SHA256:8A8DE823D5ED3E12746A62EF169BCF372BE0CA44F0A1236ABC35DF05D96928E1 | |||
| 6436 | svchost.exe | C:\Recovery\read_it.txt | text | |
MD5:3E2B5192E7CA51E0BD3FE0910B680EE6 | SHA256:897DA642F47D00BC703E62B3E9D451AB24AF1EC742DFE739C924A02A56988C61 | |||
| 6436 | svchost.exe | C:\Recovery\ReAgentOld.xml | binary | |
MD5:D1457B72C3FB323A2671125AEF3EAB5D | SHA256:8A8DE823D5ED3E12746A62EF169BCF372BE0CA44F0A1236ABC35DF05D96928E1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.21.245.134:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 92.123.53.223:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3608 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6868 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6868 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1684 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.21.245.134:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 92.123.53.223:80 | www.microsoft.com | AKAMAI-AS | BE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.21.245.21:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| unknown |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| unknown |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|