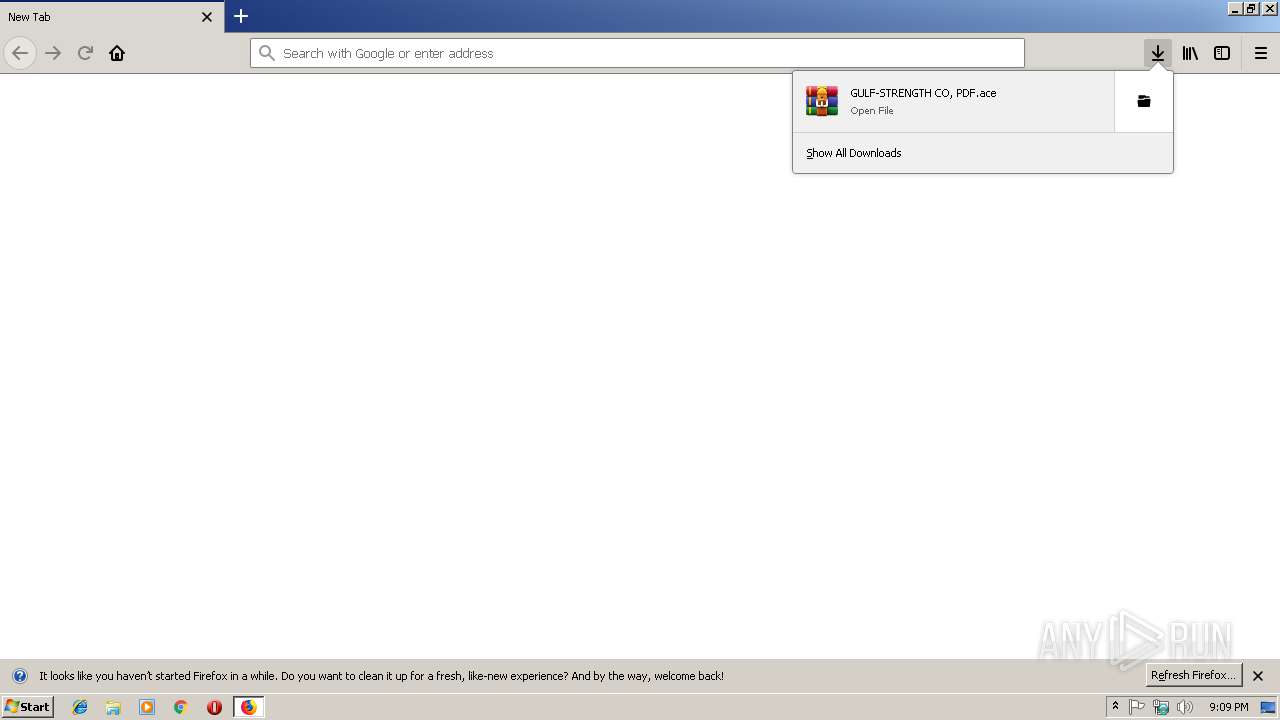
| URL: | https://onedrive.live.com/download?cid=9C2D3618603653D1&resid=9C2D3618603653D1%2113178&authkey=AGzWTvbOujj3WfQ |
| Full analysis: | https://app.any.run/tasks/7cc44f2e-93f1-4f3a-849c-05e5563f2d32 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | February 18, 2019, 21:09:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C9D064737533A710C399EAC9CC59C4DA |
| SHA1: | 7A2C8B0554A413C3276ADED491313EA74533BDDD |
| SHA256: | 2D8D5C18928D3000C02E5E457138E682D66822C1F7A9E927C2A8E0ABD0A4A9E0 |
| SSDEEP: | 3:N8Ck3CTwKblJUzYCDqg2UzYCA0LB1vpraxLF0:2CkST/ZXCBwCA0LfvpGxy |
MALICIOUS
FORMBOOK was detected
- firefox.exe (PID: 3032)
Application was dropped or rewritten from another process
- GULF-STRENGTH CO, PDF.exe (PID: 3944)
- GULF-STRENGTH CO, PDF.exe (PID: 3976)
Changes the autorun value in the registry
- wlanext.exe (PID: 2352)
Connects to CnC server
- firefox.exe (PID: 3032)
Formbook was detected
- wlanext.exe (PID: 2352)
- Firefox.exe (PID: 1252)
Actions looks like stealing of personal data
- wlanext.exe (PID: 2352)
Stealing of credential data
- wlanext.exe (PID: 2352)
SUSPICIOUS
Application launched itself
- GULF-STRENGTH CO, PDF.exe (PID: 3976)
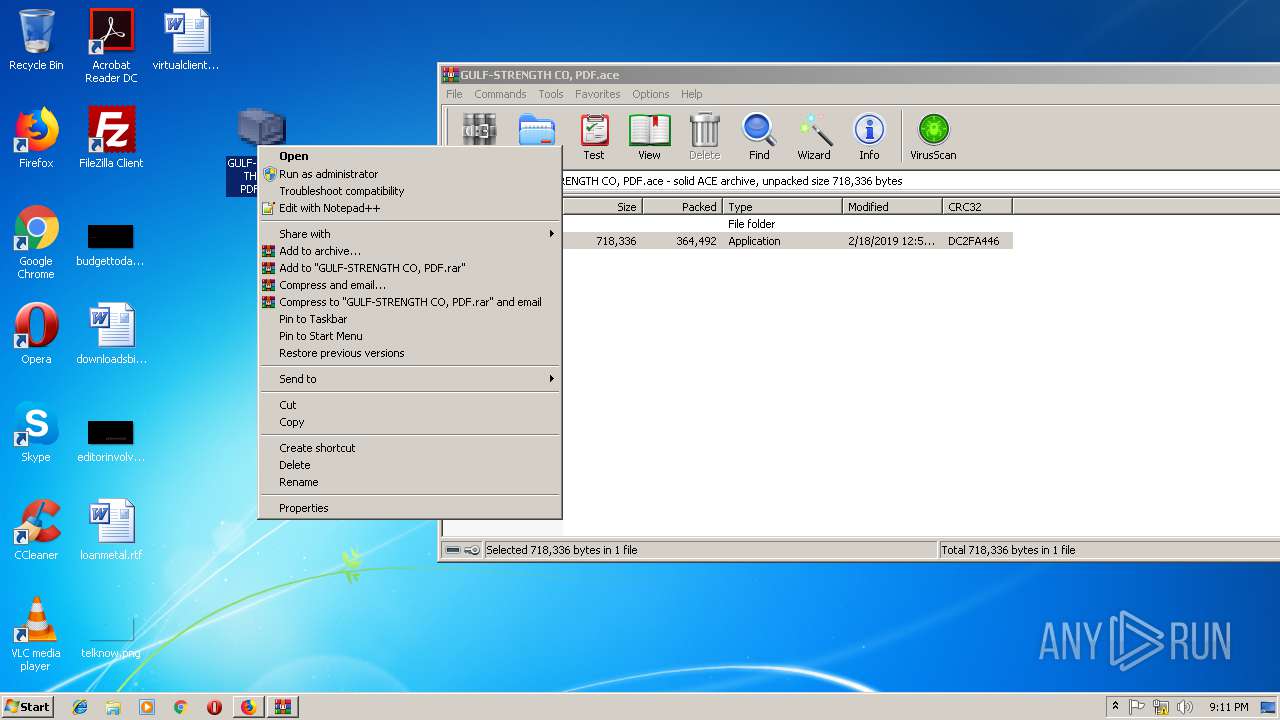
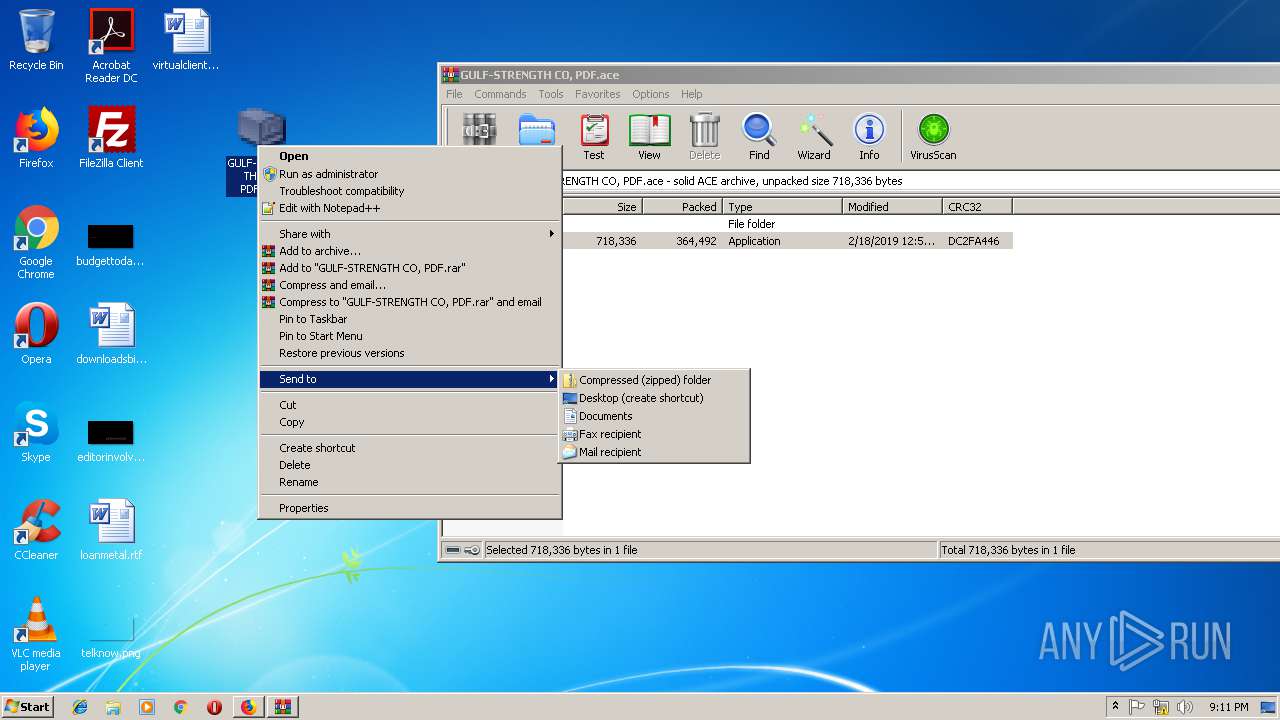
Executable content was dropped or overwritten
- WinRAR.exe (PID: 792)
- firefox.exe (PID: 3032)
Starts CMD.EXE for commands execution
- wlanext.exe (PID: 2352)
Creates files in the user directory
- wlanext.exe (PID: 2352)
Loads DLL from Mozilla Firefox
- wlanext.exe (PID: 2352)
INFO
Creates files in the user directory
- firefox.exe (PID: 3032)
- Firefox.exe (PID: 1252)
Application launched itself
- firefox.exe (PID: 3032)
Reads Internet Cache Settings
- firefox.exe (PID: 3032)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3032)
Reads settings of System Certificates
- firefox.exe (PID: 3032)
Reads CPU info
- firefox.exe (PID: 3032)
- firefox.exe (PID: 2728)
- firefox.exe (PID: 2888)
- firefox.exe (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
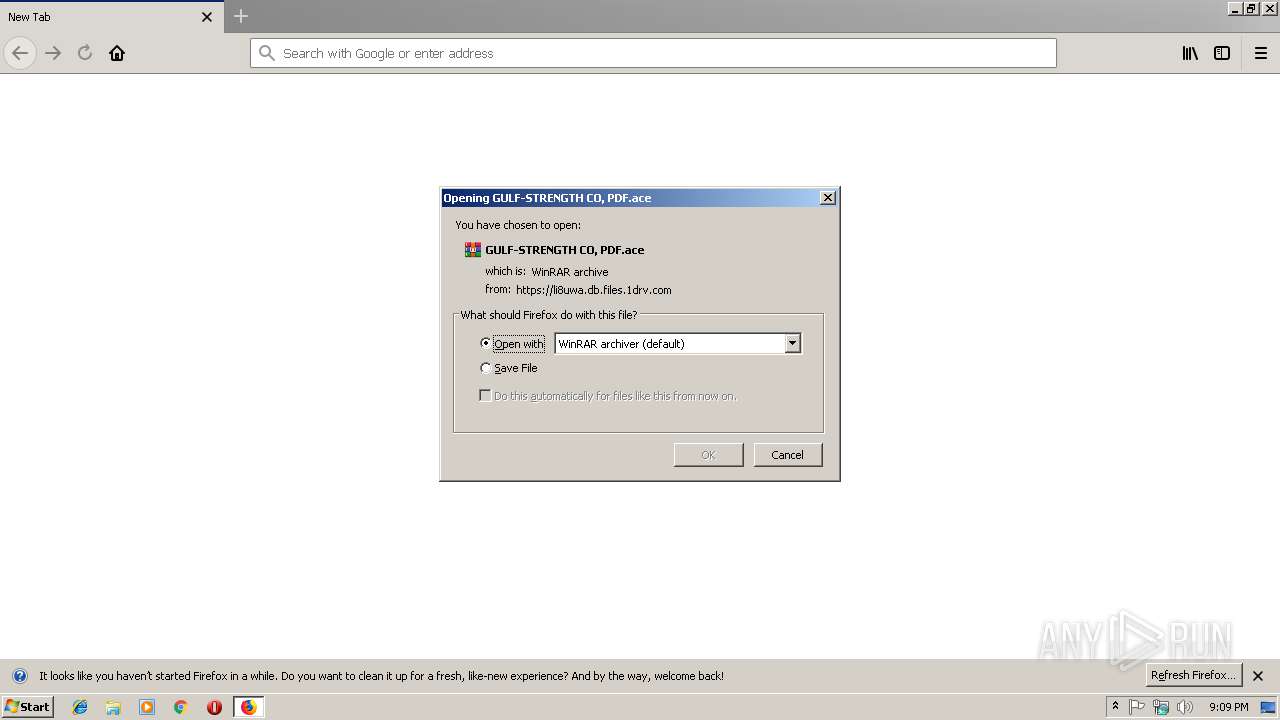
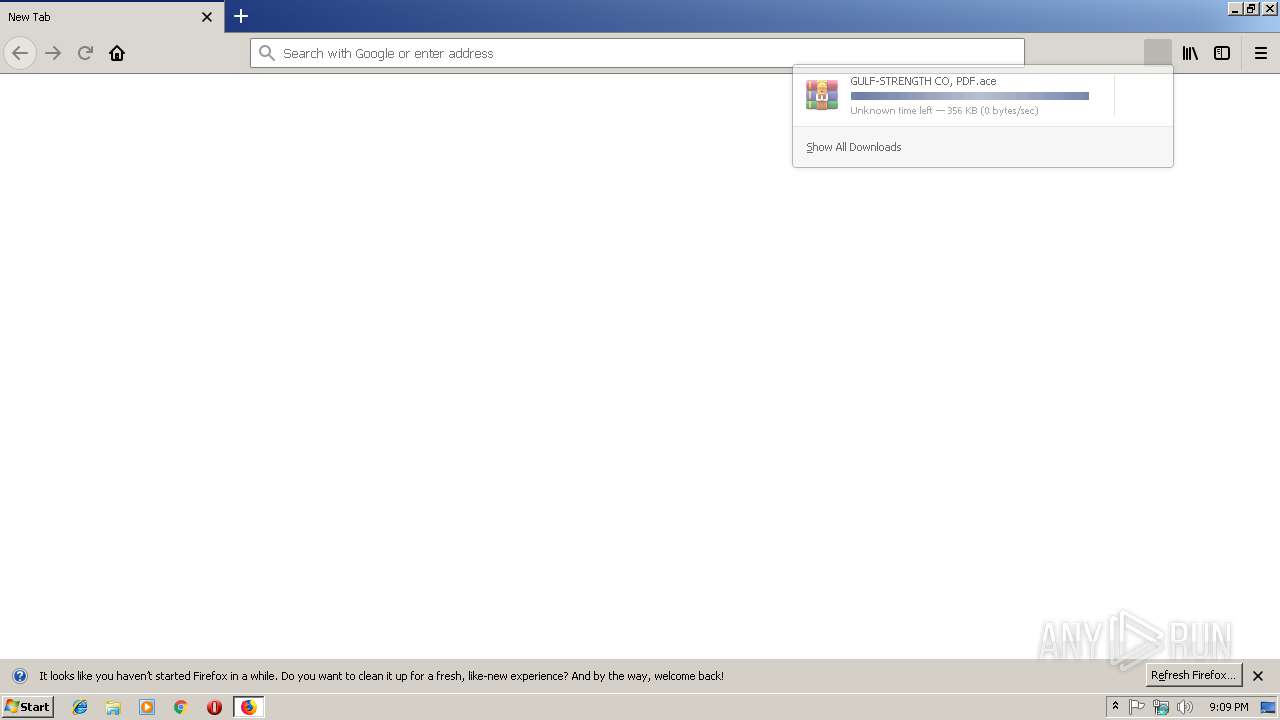
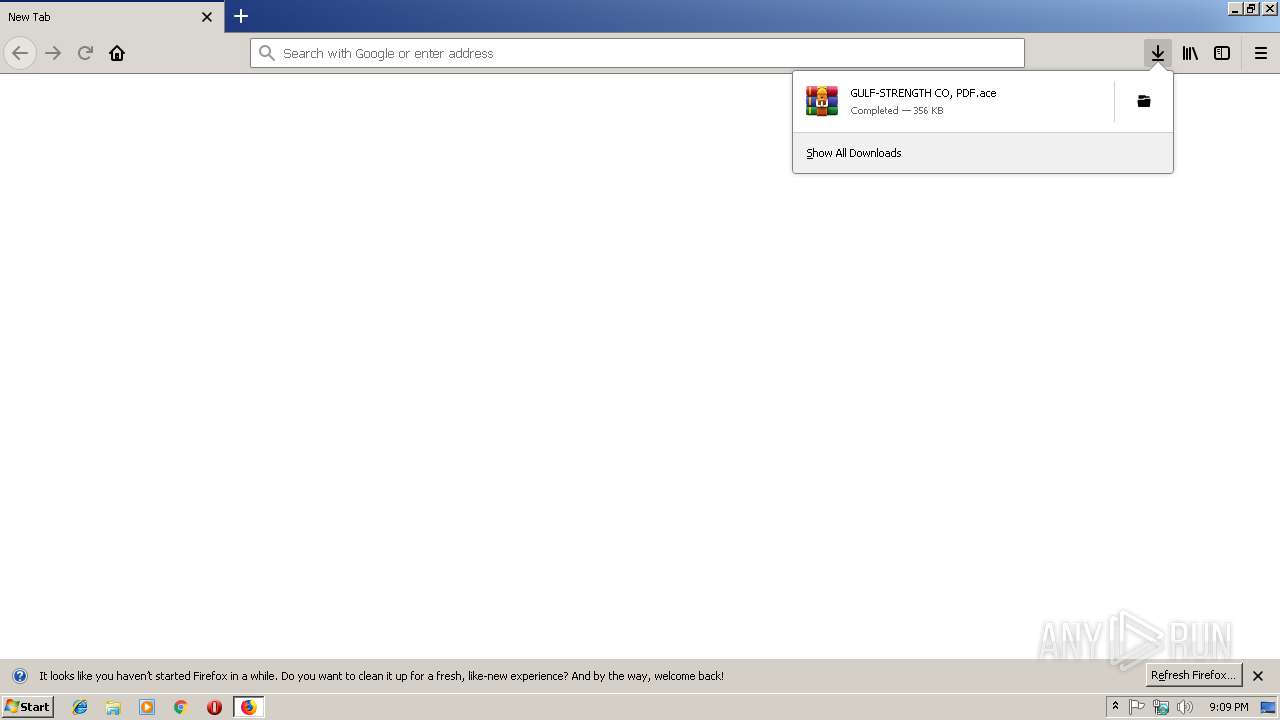
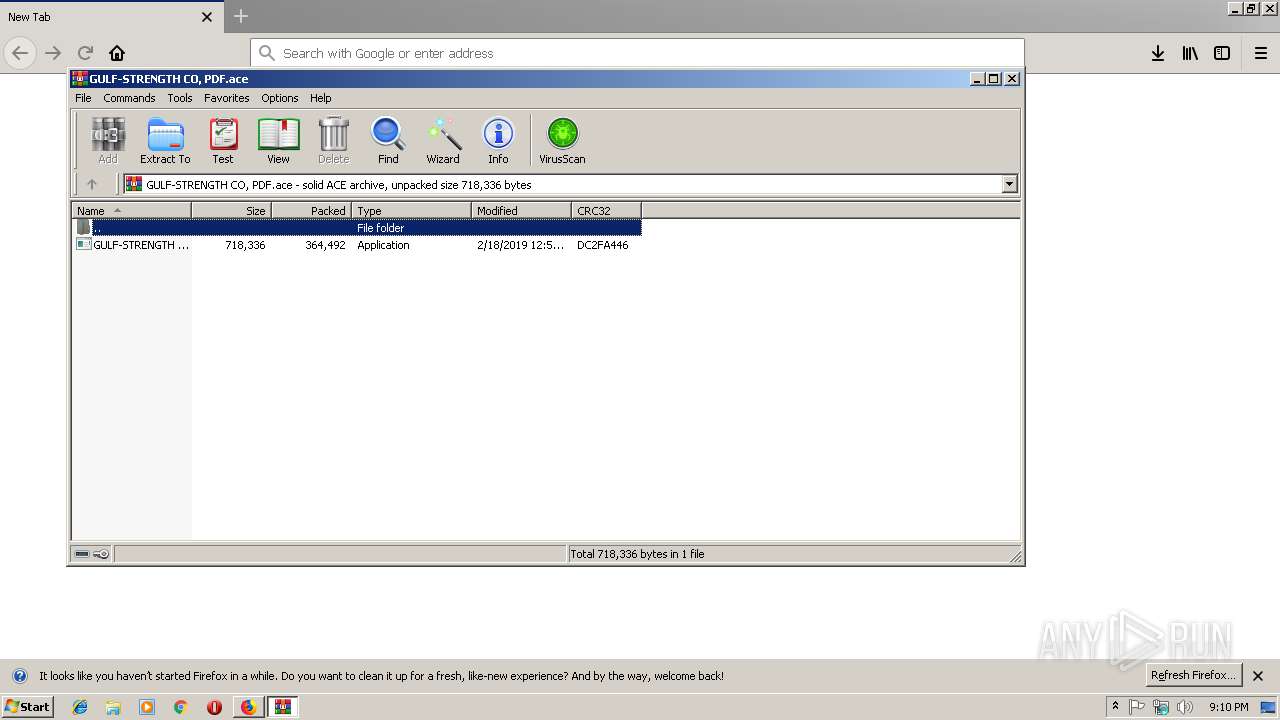
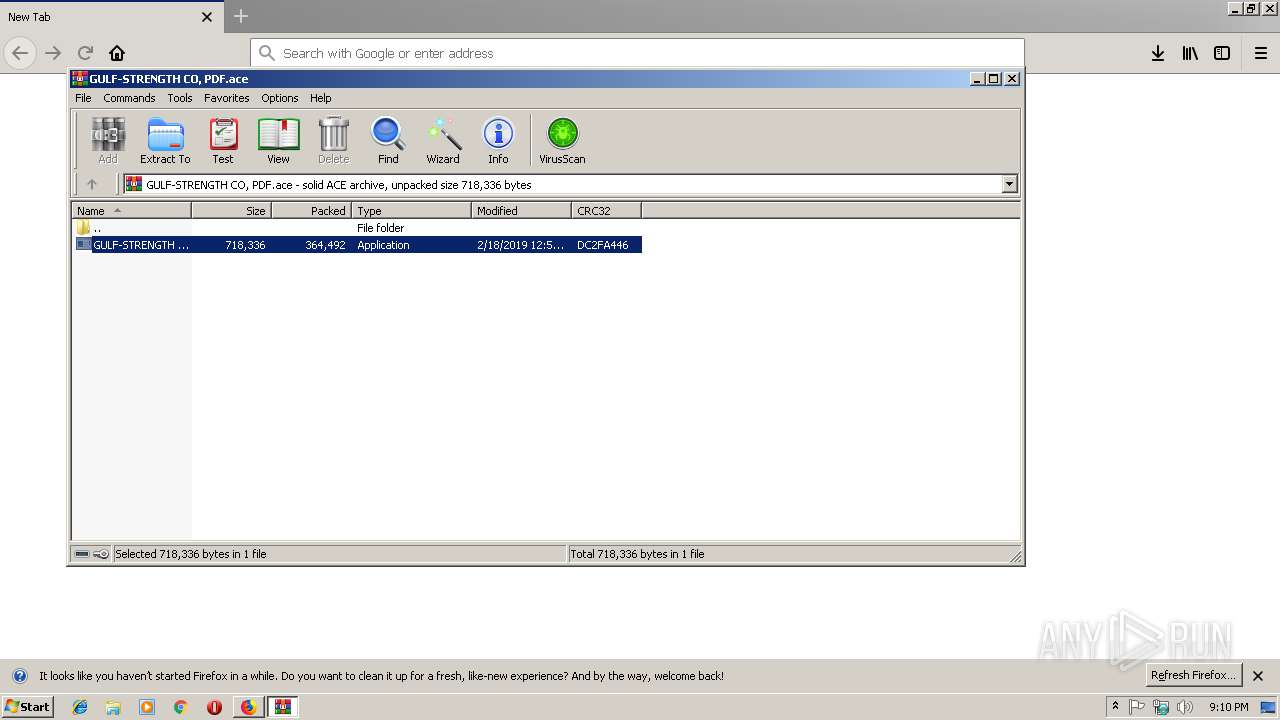
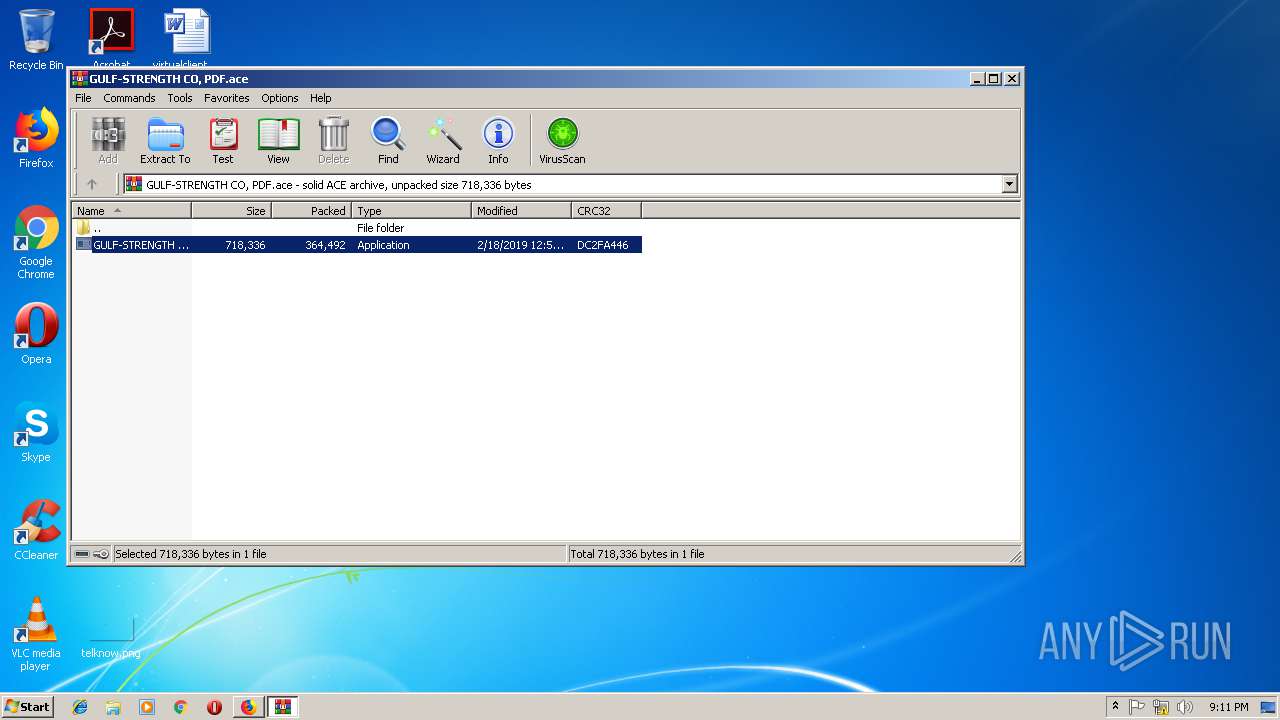
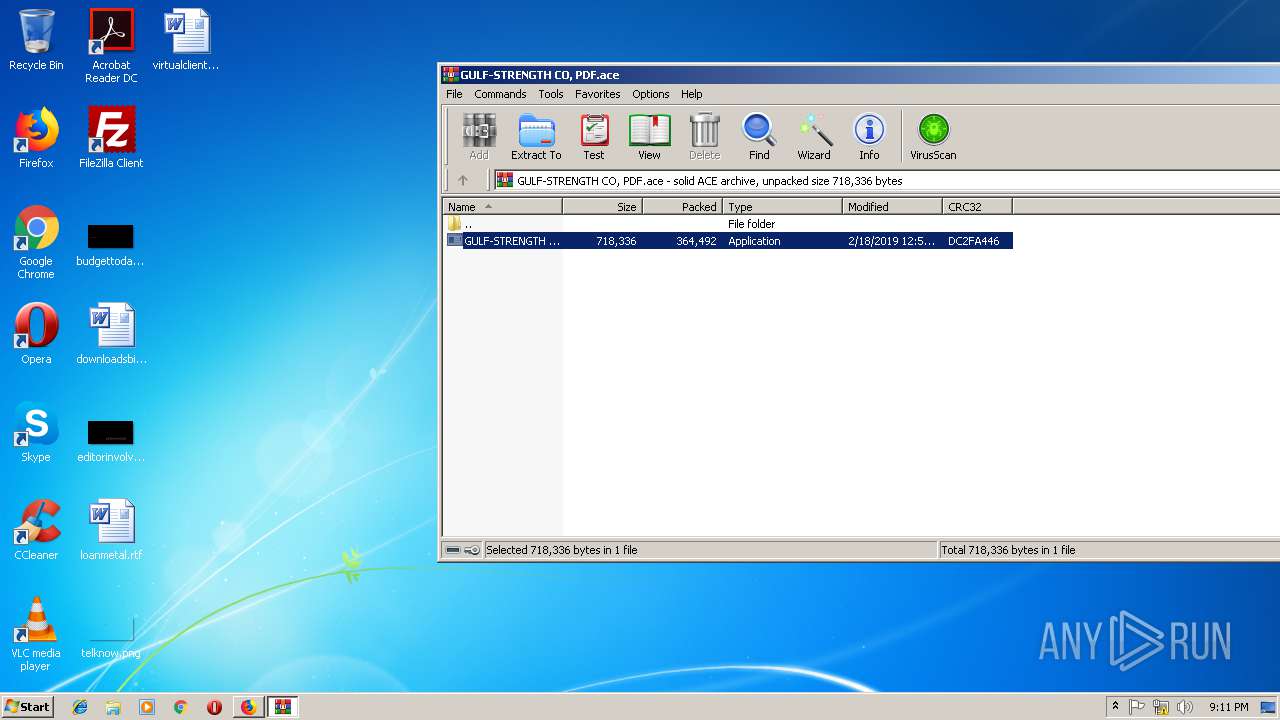
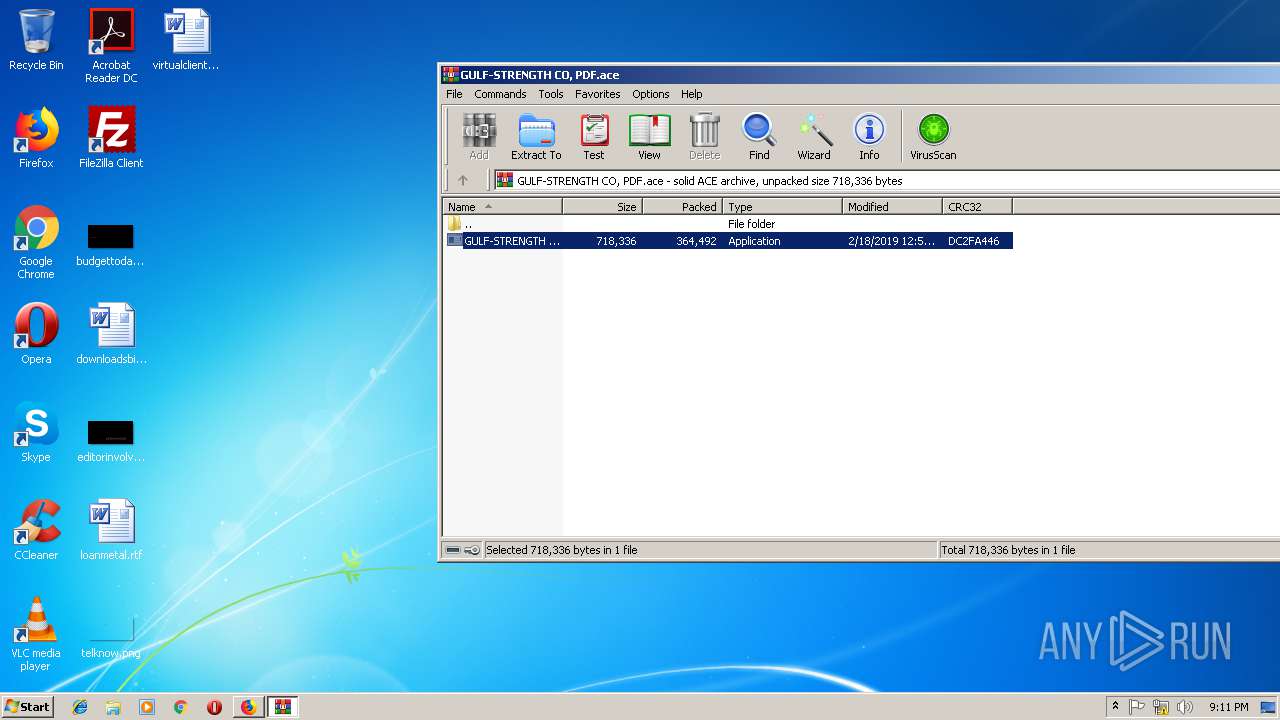
| 792 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\GULF-STRENGTH CO, PDF.ace" | C:\Program Files\WinRAR\WinRAR.exe | firefox.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wlanext.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2352 | "C:\Windows\System32\wlanext.exe" | C:\Windows\System32\wlanext.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wireless LAN 802.11 Extensibility Framework Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXa792.20929\GULF-STRENGTH CO, PDF.exe" | C:\Windows\System32\cmd.exe | — | wlanext.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3032.0.250934231\1907529621" -childID 1 -isForBrowser -prefsHandle 1444 -prefsLen 8310 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3032 "\\.\pipe\gecko-crash-server-pipe.3032" 1408 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3032.12.1014574154\1643815810" -childID 3 -isForBrowser -prefsHandle 2840 -prefsLen 12017 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3032 "\\.\pipe\gecko-crash-server-pipe.3032" 2956 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://onedrive.live.com/download?cid=9C2D3618603653D1&resid=9C2D3618603653D1%2113178&authkey=AGzWTvbOujj3WfQ | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3032.6.248971301\1058499419" -childID 2 -isForBrowser -prefsHandle 2476 -prefsLen 11442 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3032 "\\.\pipe\gecko-crash-server-pipe.3032" 2472 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3944 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa792.20929\GULF-STRENGTH CO, PDF.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa792.20929\GULF-STRENGTH CO, PDF.exe | — | GULF-STRENGTH CO, PDF.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa792.20929\GULF-STRENGTH CO, PDF.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa792.20929\GULF-STRENGTH CO, PDF.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 056
Read events
1 014
Write events
42
Delete events
0
Modification events
| (PID) Process: | (3032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.ace\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (792) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\GULF-STRENGTH CO, PDF.ace | |||
| (PID) Process: | (792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
3
Suspicious files
118
Text files
20
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
25
DNS requests
59
Threats
34
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3032 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3032 | firefox.exe | POST | 200 | 216.58.198.195:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3032 | firefox.exe | POST | — | 199.192.26.225:80 | http://www.ajexin.com/ho/ | US | — | — | malicious |
3032 | firefox.exe | POST | — | 199.192.26.225:80 | http://www.ajexin.com/ho/ | US | — | — | malicious |
3032 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3032 | firefox.exe | POST | 200 | 216.58.198.195:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3032 | firefox.exe | POST | 200 | 216.58.198.195:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3032 | firefox.exe | POST | — | 199.192.26.225:80 | http://www.ajexin.com/ho/ | US | — | — | malicious |
3032 | firefox.exe | POST | — | 199.192.26.225:80 | http://www.ajexin.com/ho/ | US | — | — | malicious |
3032 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3032 | firefox.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
3032 | firefox.exe | 52.89.32.107:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3032 | firefox.exe | 104.86.111.161:80 | detectportal.firefox.com | Akamai International B.V. | NL | whitelisted |
3032 | firefox.exe | 34.218.217.119:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3032 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3032 | firefox.exe | 13.107.42.12:443 | li8uwa.db.files.1drv.com | Microsoft Corporation | US | suspicious |
3032 | firefox.exe | 216.58.206.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3032 | firefox.exe | 216.58.198.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3032 | firefox.exe | 52.85.255.93:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3032 | firefox.exe | 52.32.77.100:443 | aus5.mozilla.org | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onedrive.live.com |
| shared |
detectportal.firefox.com |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
li8uwa.db.files.1drv.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
shavar.services.mozilla.com |
| whitelisted |
tracking-protection.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
3032 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
6 ETPRO signatures available at the full report