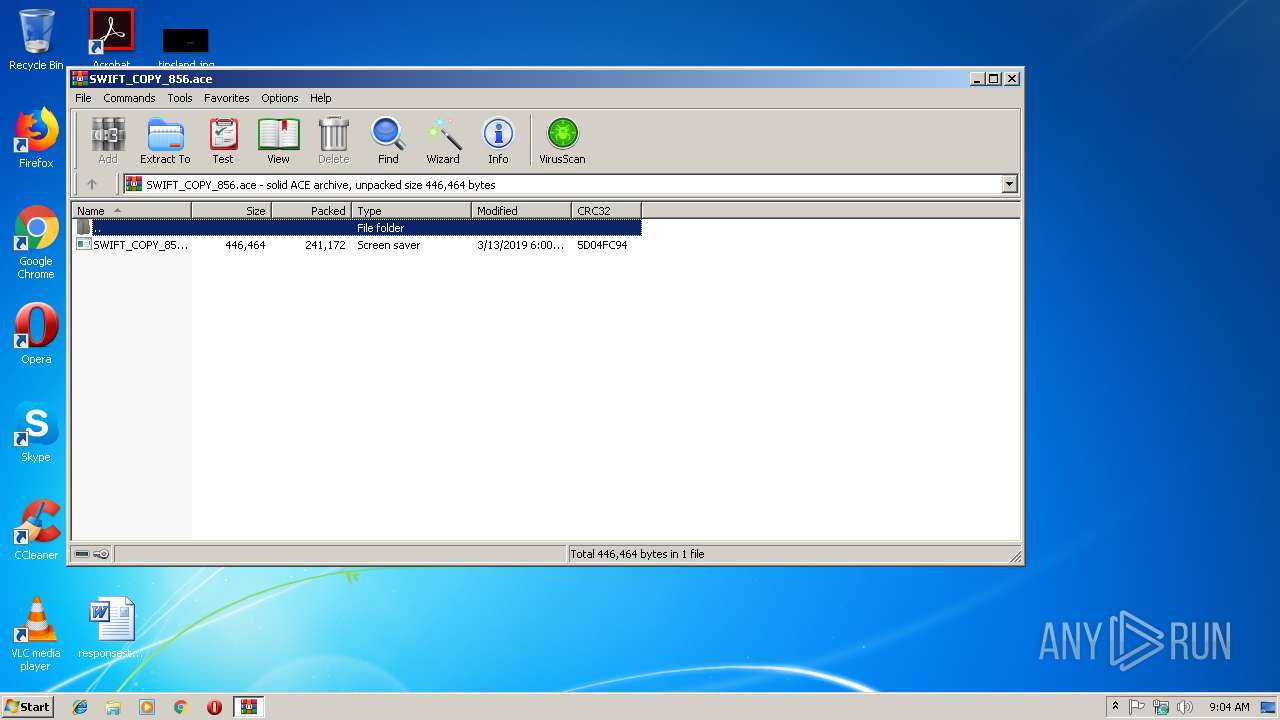
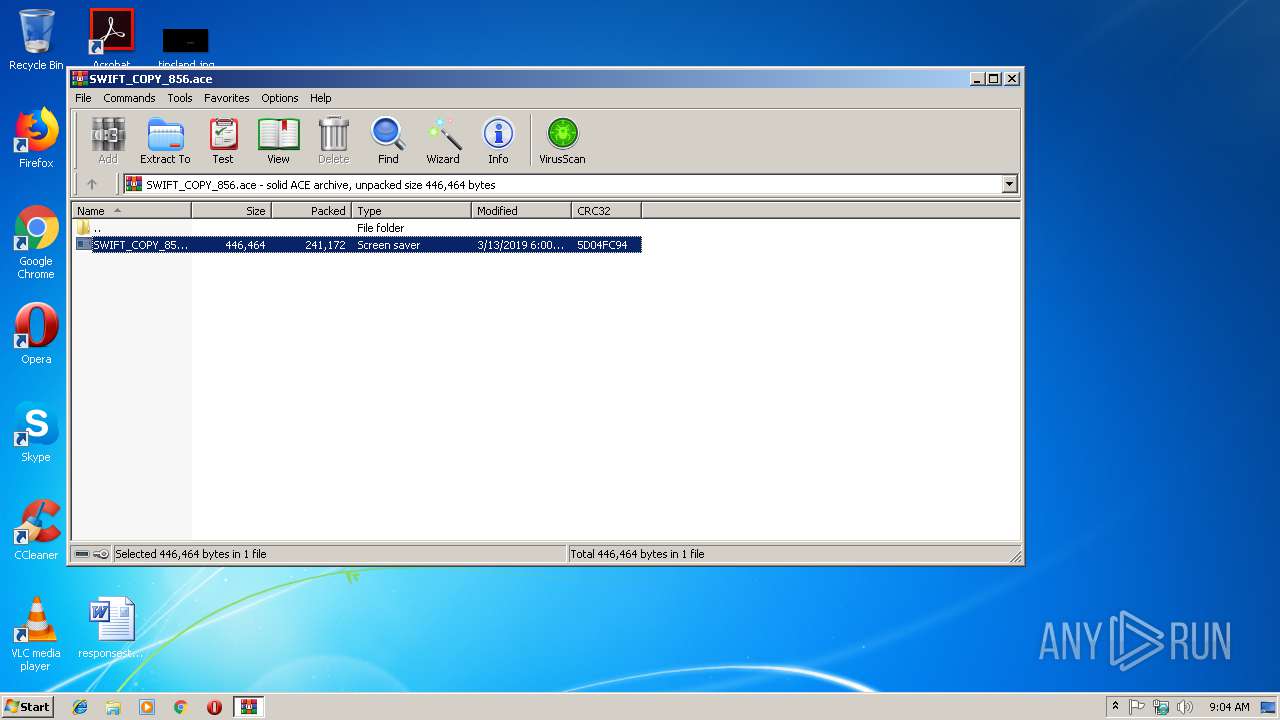
| File name: | SWIFT_COPY_856.ace |
| Full analysis: | https://app.any.run/tasks/e921c162-dc2d-4e41-ba29-7ad3b469b77b |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | March 14, 2019, 09:04:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | ACE archive data version 20, from Win/32, version 20 to extract, contains AV-String (unregistered), solid |
| MD5: | D42251C5A118B397951F53BA1B09E460 |
| SHA1: | F017D032784C73B6B94F5E646D1CB40CCB45EE58 |
| SHA256: | 2D1C8F574F21589BD55F6E822D78335F4FB96A7509148712E7067594E5215D1E |
| SSDEEP: | 6144:adnB4c0/qibum3dpg7cw8X04DqkjdD3ztNCZwb:XOi5W7Ok4DdjRzrCW |
MALICIOUS
Application was dropped or rewritten from another process
- SWIFT_COPY_856.scr (PID: 2848)
- SWIFT_COPY_856.scr (PID: 3356)
- SWIFT_COPY_856.scr (PID: 4044)
FORMBOOK was detected
- explorer.exe (PID: 284)
Formbook was detected
- rdpclip.exe (PID: 2624)
- Firefox.exe (PID: 2796)
Changes the autorun value in the registry
- rdpclip.exe (PID: 2624)
Actions looks like stealing of personal data
- rdpclip.exe (PID: 2624)
Connects to CnC server
- explorer.exe (PID: 284)
Stealing of credential data
- rdpclip.exe (PID: 2624)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2980)
Starts application with an unusual extension
- WinRAR.exe (PID: 2980)
- SWIFT_COPY_856.scr (PID: 2848)
- SWIFT_COPY_856.scr (PID: 3356)
Application launched itself
- SWIFT_COPY_856.scr (PID: 2848)
- SWIFT_COPY_856.scr (PID: 3356)
Starts CMD.EXE for commands execution
- rdpclip.exe (PID: 2624)
Creates files in the user directory
- rdpclip.exe (PID: 2624)
Loads DLL from Mozilla Firefox
- rdpclip.exe (PID: 2624)
INFO
Creates files in the user directory
- Firefox.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ace | | | ACE compressed archive (100) |
|---|
Total processes
37
Monitored processes
8
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | "C:\Windows\System32\rdpclip.exe" | C:\Windows\System32\rdpclip.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: RDP Clip Monitor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | rdpclip.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\Temp\Rar$DIa2980.26241\SWIFT_COPY_856.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIa2980.26241\SWIFT_COPY_856.scr | — | WinRAR.exe | |||||||||||
User: admin Company: NARA Integrity Level: MEDIUM Description: MOB Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\SWIFT_COPY_856.ace" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3356 | "C:\Users\admin\AppData\Local\Temp\Rar$DIa2980.26241\SWIFT_COPY_856.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIa2980.26241\SWIFT_COPY_856.scr | — | SWIFT_COPY_856.scr | |||||||||||
User: admin Company: NARA Integrity Level: MEDIUM Description: MOB Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3388 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$DIa2980.26241\SWIFT_COPY_856.scr" | C:\Windows\System32\cmd.exe | — | rdpclip.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4044 | "C:\Users\admin\AppData\Local\Temp\Rar$DIa2980.26241\SWIFT_COPY_856.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIa2980.26241\SWIFT_COPY_856.scr | — | SWIFT_COPY_856.scr | |||||||||||
User: admin Company: NARA Integrity Level: MEDIUM Description: MOB Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
482
Read events
446
Write events
36
Delete events
0
Modification events
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SWIFT_COPY_856.ace | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Count |
Value: 0 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Name |
Value: 542D4B42647265644B76737A7E794B566767537663764B5B7874767B4B43727A674B44405E5143485458474E482F2221397674721717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171700 | |||
Executable files
1
Suspicious files
73
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2980.26241\SWIFT_COPY_856.scr | executable | |
MD5:— | SHA256:— | |||
| 2796 | Firefox.exe | C:\Users\admin\AppData\Roaming\4NL07UBE\4NLlogrf.ini | binary | |
MD5:— | SHA256:— | |||
| 2624 | rdpclip.exe | C:\Users\admin\AppData\Roaming\4NL07UBE\4NLlogrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2624 | rdpclip.exe | C:\Users\admin\AppData\Roaming\4NL07UBE\4NLlogim.jpeg | image | |
MD5:— | SHA256:— | |||
| 3356 | SWIFT_COPY_856.scr | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 2848 | SWIFT_COPY_856.scr | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 2624 | rdpclip.exe | C:\Users\admin\AppData\Roaming\4NL07UBE\4NLlogrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
| 2624 | rdpclip.exe | C:\Users\admin\AppData\Roaming\4NL07UBE\4NLlogri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
26
DNS requests
16
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
284 | explorer.exe | GET | 301 | 104.154.23.229:80 | http://www.napalandman.net/pe/?PB=W9sGz4OoQAk2r1FrqsHeEjLoHC1tn2Jzv/4esmYgXyCsn5Vz0UO8gXGscJvcOIex5f8NfA==&00=Jz9L_rMX&sql=1 | US | — | — | malicious |
284 | explorer.exe | GET | — | 209.99.64.43:80 | http://www.tattoodedication.com/pe/?PB=N1ch3/b1sYv/hU9TQ/GnVRpLgi+LXR8/wLTAkNvEhxjgg7Ce3PifzJ3Q1qsWxN/ChGyUmg==&00=Jz9L_rMX&sql=1 | US | — | — | malicious |
284 | explorer.exe | GET | — | 88.214.207.96:80 | http://www.maccheronicini.com/pe/?PB=s1tnAVSUiInLtxGBFy8WOBpIfbg81+XIthL6ti59XpWaTbVwUAT653hwZKjmaJCHHyggRQ==&00=Jz9L_rMX&sql=1 | GB | — | — | malicious |
284 | explorer.exe | POST | — | 209.99.64.43:80 | http://www.tattoodedication.com/pe/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 209.99.64.43:80 | http://www.tattoodedication.com/pe/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 88.214.207.96:80 | http://www.maccheronicini.com/pe/ | GB | — | — | malicious |
284 | explorer.exe | POST | — | 88.214.207.96:80 | http://www.maccheronicini.com/pe/ | GB | — | — | malicious |
284 | explorer.exe | POST | — | 192.237.132.248:80 | http://www.thenorthernlightsmusic.com/pe/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 88.214.207.96:80 | http://www.maccheronicini.com/pe/ | GB | — | — | malicious |
284 | explorer.exe | GET | 301 | 192.237.132.248:80 | http://www.thenorthernlightsmusic.com/pe/?PB=TOfyfpYrAhc21K2hDYkifELHovYA4dP8aqEcz4CyRmzPSy/hDocWRtM9N9fSKe8LU0s6UA==&00=Jz9L_rMX&sql=1 | US | html | 209 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
284 | explorer.exe | 104.154.23.229:80 | www.napalandman.net | Google Inc. | US | malicious |
284 | explorer.exe | 213.186.33.5:80 | www.alexandre-allard.com | OVH SAS | FR | malicious |
284 | explorer.exe | 209.99.64.43:80 | www.tattoodedication.com | Confluence Networks Inc | US | malicious |
284 | explorer.exe | 88.214.207.96:80 | www.maccheronicini.com | NatCoWeb Corp. | GB | malicious |
284 | explorer.exe | 192.237.132.248:80 | www.thenorthernlightsmusic.com | Rackspace Ltd. | US | malicious |
284 | explorer.exe | 217.160.0.173:80 | www.lifemasterclass.info | 1&1 Internet SE | DE | malicious |
284 | explorer.exe | 23.20.239.12:80 | www.coffindepot.com | Amazon.com, Inc. | US | shared |
284 | explorer.exe | 45.192.106.247:80 | www.godspee.com | MacroLAN | ZA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hailougou.com |
| unknown |
www.alexandre-allard.com |
| malicious |
www.napalandman.net |
| malicious |
www.tattoodedication.com |
| malicious |
www.maccheronicini.com |
| malicious |
www.abetterupdates.win |
| unknown |
www.thenorthernlightsmusic.com |
| malicious |
www.lifemasterclass.info |
| malicious |
www.medi-strains.net |
| unknown |
www.godspee.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
21 ETPRO signatures available at the full report