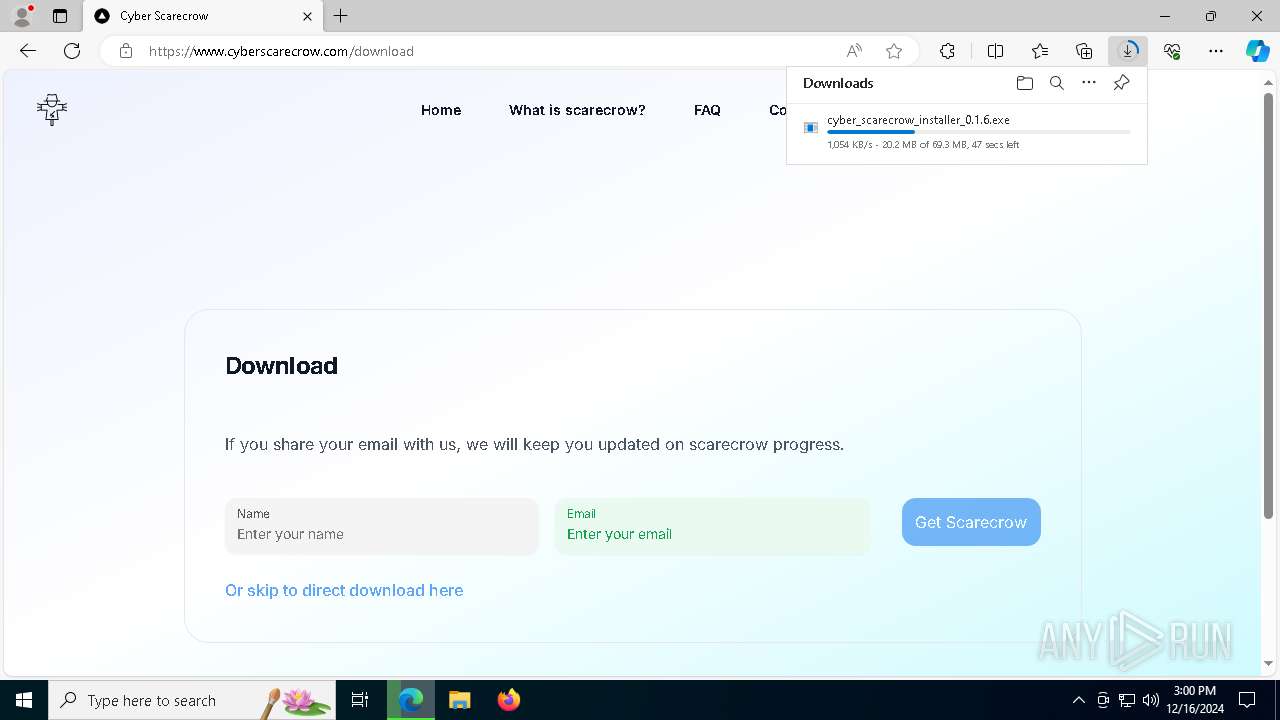
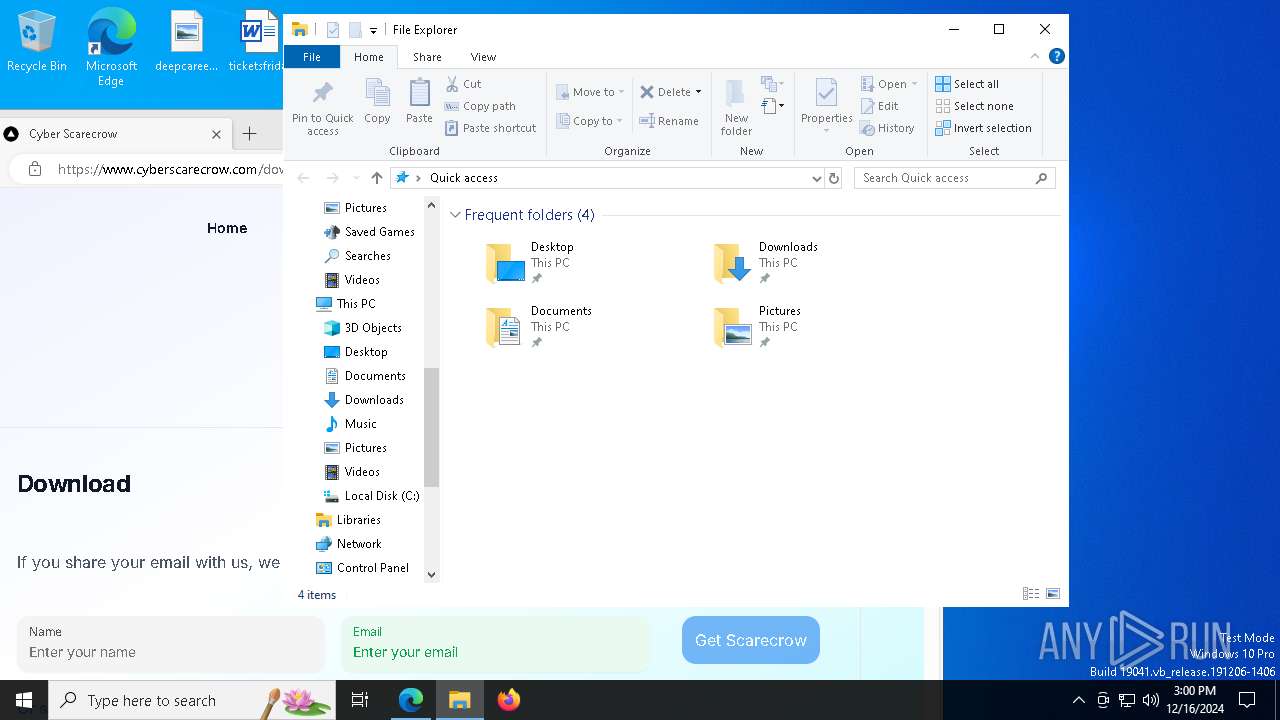
| URL: | https://www.cyberscarecrow.com/ |
| Full analysis: | https://app.any.run/tasks/72d8d67d-2481-4503-92c9-8abe61d2f707 |
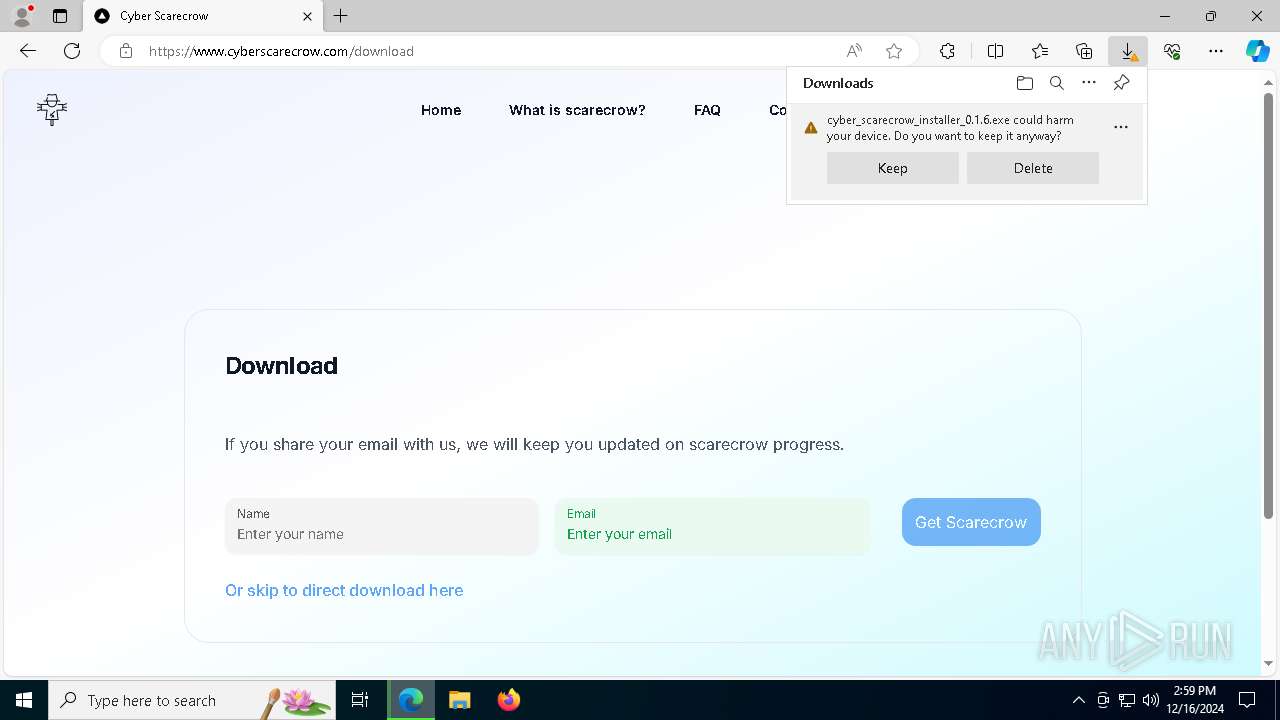
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 16, 2024, 14:59:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AC0929DEE128CBB6C6196AA7513E0172 |
| SHA1: | CF00A6D92C055717876967D7760EEEFAC056BC80 |
| SHA256: | 2D181EFF7CD9495A7C5B0C79A60BF4CA11EBBF55A73A460066CADFA56C595FB0 |
| SSDEEP: | 3:N8DSLzAXR+IK:2OLsh+IK |
MALICIOUS
Changes the autorun value in the registry
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 6948)
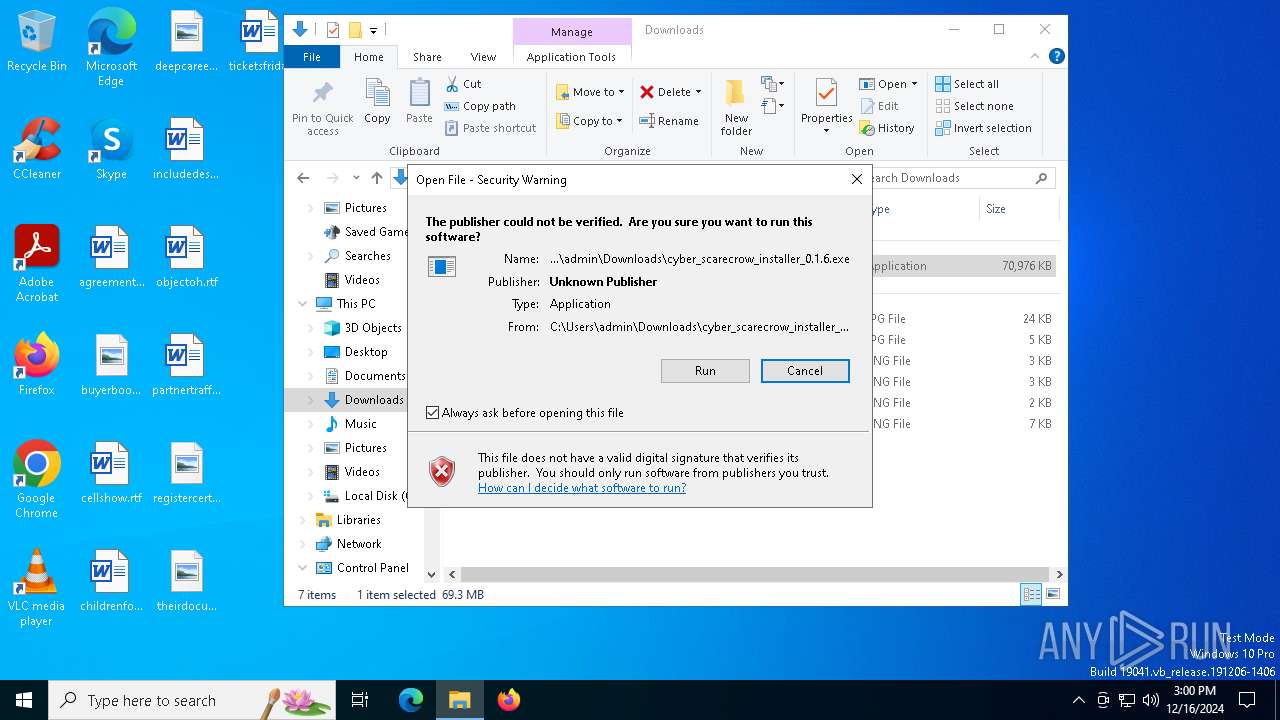
Executing a file with an untrusted certificate
- Full-Setup.exe (PID: 5920)
LUMMA mutex has been found
- Deck.com (PID: 2408)
Changes powershell execution policy (Bypass)
- Deck.com (PID: 2408)
Bypass execution policy to execute commands
- powershell.exe (PID: 7116)
SUSPICIOUS
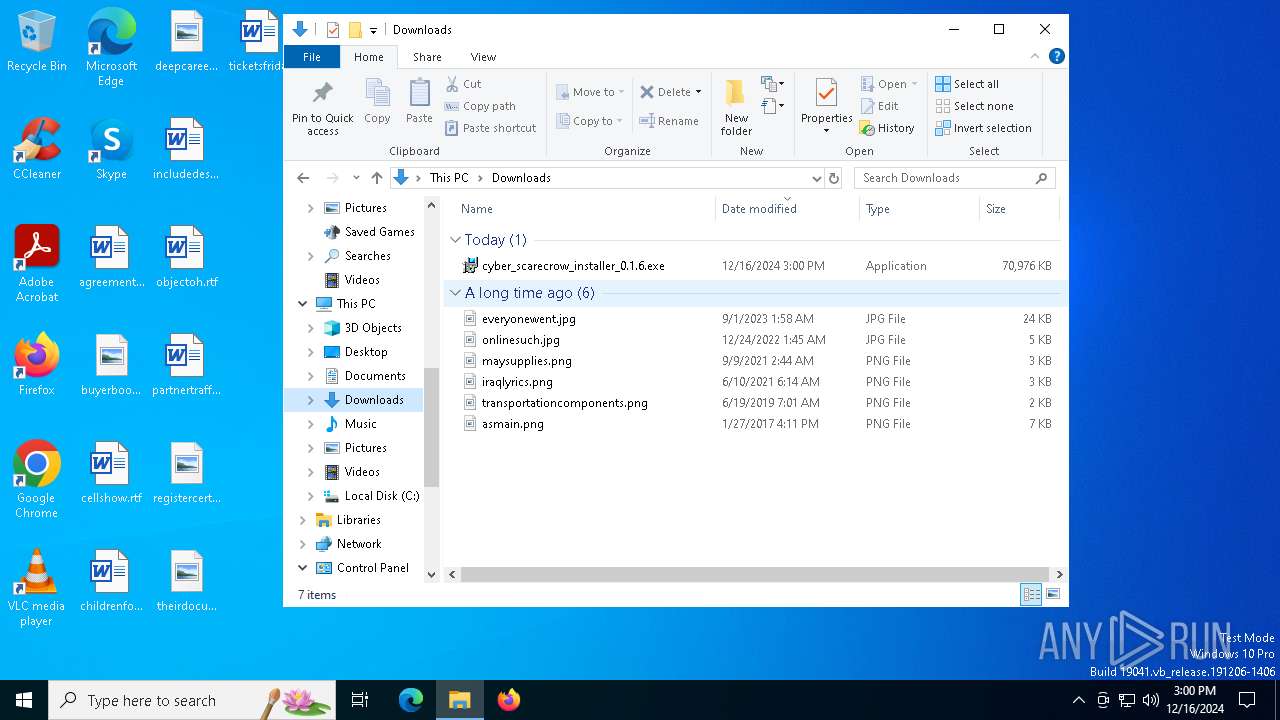
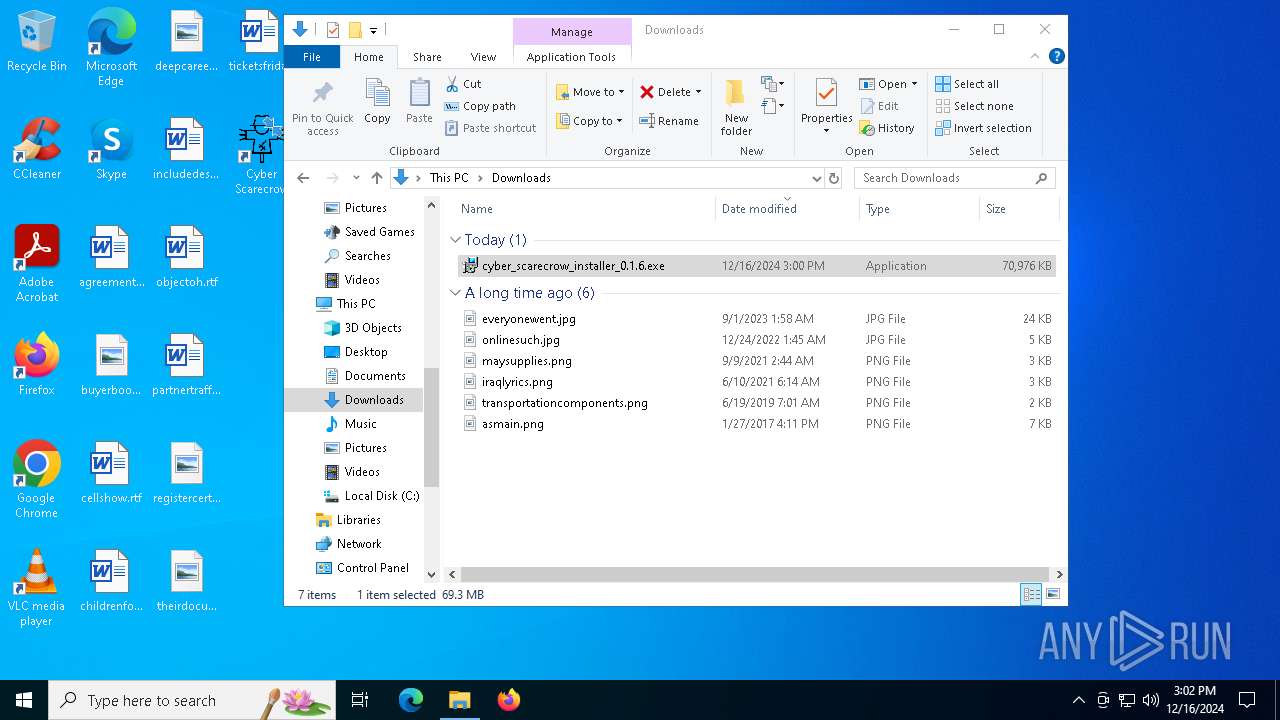
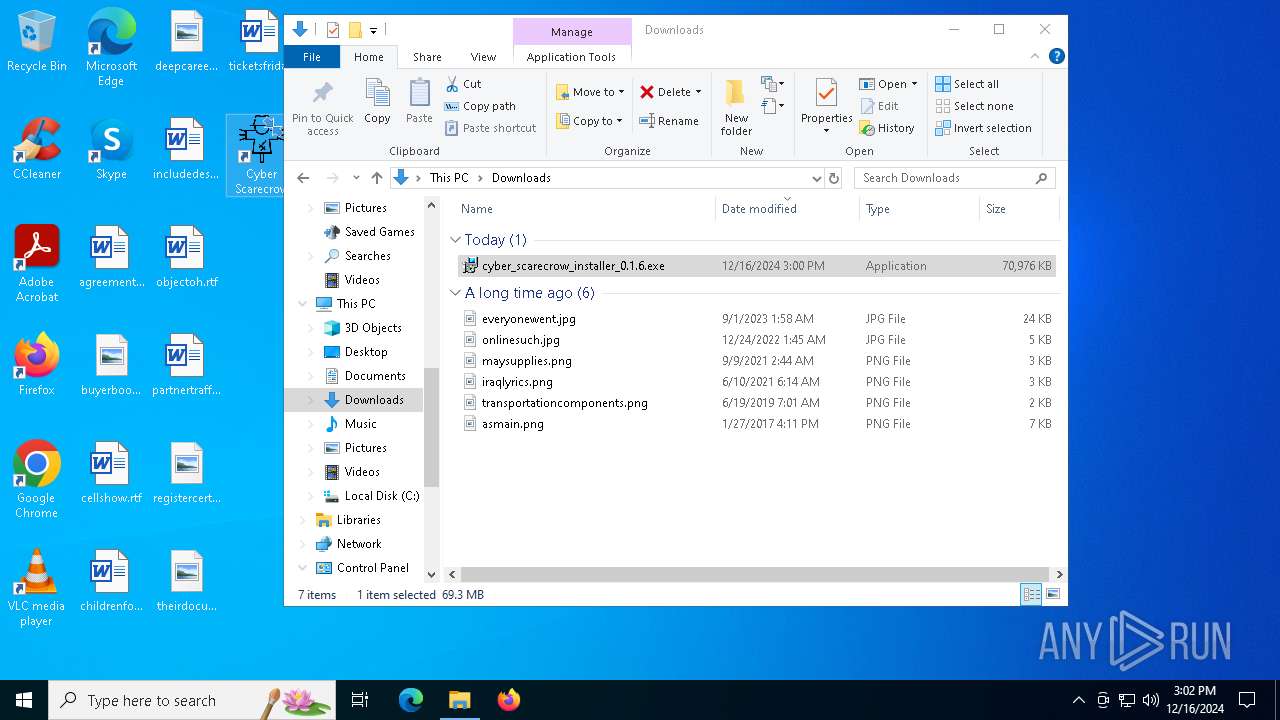
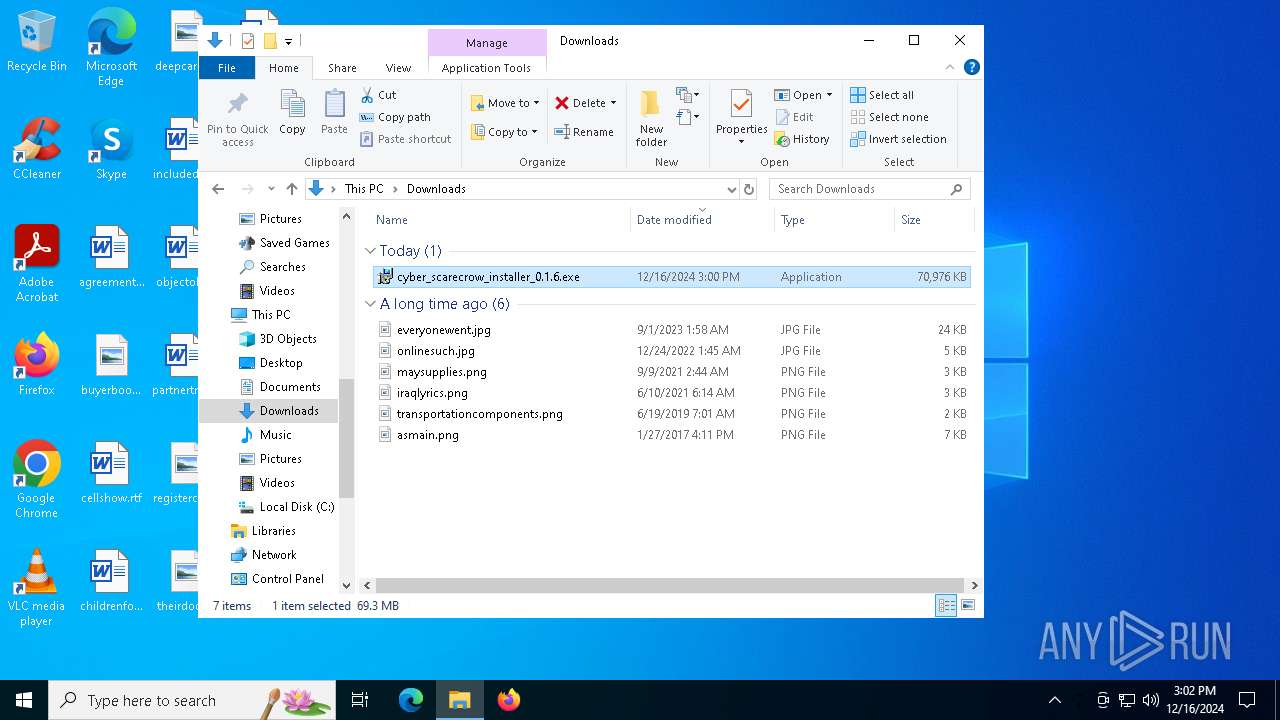
Executable content was dropped or overwritten
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- cyber_scarecrow_installer_VERSION.exe (PID: 6804)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 7084)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 6948)
- scarecrow_tray.exe (PID: 6568)
Process drops legitimate windows executable
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 7084)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 6948)
- msiexec.exe (PID: 5316)
Searches for installed software
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- cyber_scarecrow_installer_VERSION.exe (PID: 6804)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
Reads security settings of Internet Explorer
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
- Full-Setup.exe (PID: 5920)
Starts itself from another location
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
Executes as Windows Service
- VSSVC.exe (PID: 6728)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 6948)
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 6948)
- cyber_scarecrow_installer_VERSION.exe (PID: 6804)
Checks Windows Trust Settings
- msiexec.exe (PID: 5316)
The process drops C-runtime libraries
- msiexec.exe (PID: 5316)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5316)
Executing commands from ".cmd" file
- Full-Setup.exe (PID: 5920)
Starts CMD.EXE for commands execution
- Full-Setup.exe (PID: 5920)
- cmd.exe (PID: 396)
Get information on the list of running processes
- cmd.exe (PID: 396)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 396)
Application launched itself
- cmd.exe (PID: 396)
The executable file from the user directory is run by the CMD process
- Deck.com (PID: 2408)
Starts application with an unusual extension
- cmd.exe (PID: 396)
Starts the AutoIt3 executable file
- cmd.exe (PID: 396)
The process executes Powershell scripts
- Deck.com (PID: 2408)
Starts POWERSHELL.EXE for commands execution
- Deck.com (PID: 2408)
INFO
Application launched itself
- msedge.exe (PID: 6332)
- msedge.exe (PID: 3732)
Reads Environment values
- identity_helper.exe (PID: 1668)
- identity_helper.exe (PID: 1876)
Reads the computer name
- identity_helper.exe (PID: 1668)
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- identity_helper.exe (PID: 1876)
- cyber_scarecrow_installer_VERSION.exe (PID: 6804)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
- msiexec.exe (PID: 5316)
- msiexec.exe (PID: 6868)
- msiexec.exe (PID: 6772)
- scarecrow_tray.exe (PID: 6568)
- msiexec.exe (PID: 716)
Executable content was dropped or overwritten
- msedge.exe (PID: 6332)
- msiexec.exe (PID: 5316)
Checks supported languages
- identity_helper.exe (PID: 1668)
- identity_helper.exe (PID: 1876)
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- wixstdba.exe (PID: 7136)
- cyber_scarecrow_installer_VERSION.exe (PID: 6804)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 7084)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
- msiexec.exe (PID: 5316)
- msiexec.exe (PID: 6868)
- scarecrow_tray.exe (PID: 6568)
- ProcessHacker.exe (PID: 6676)
- msiexec.exe (PID: 716)
- msiexec.exe (PID: 6772)
- Full-Setup.exe (PID: 5920)
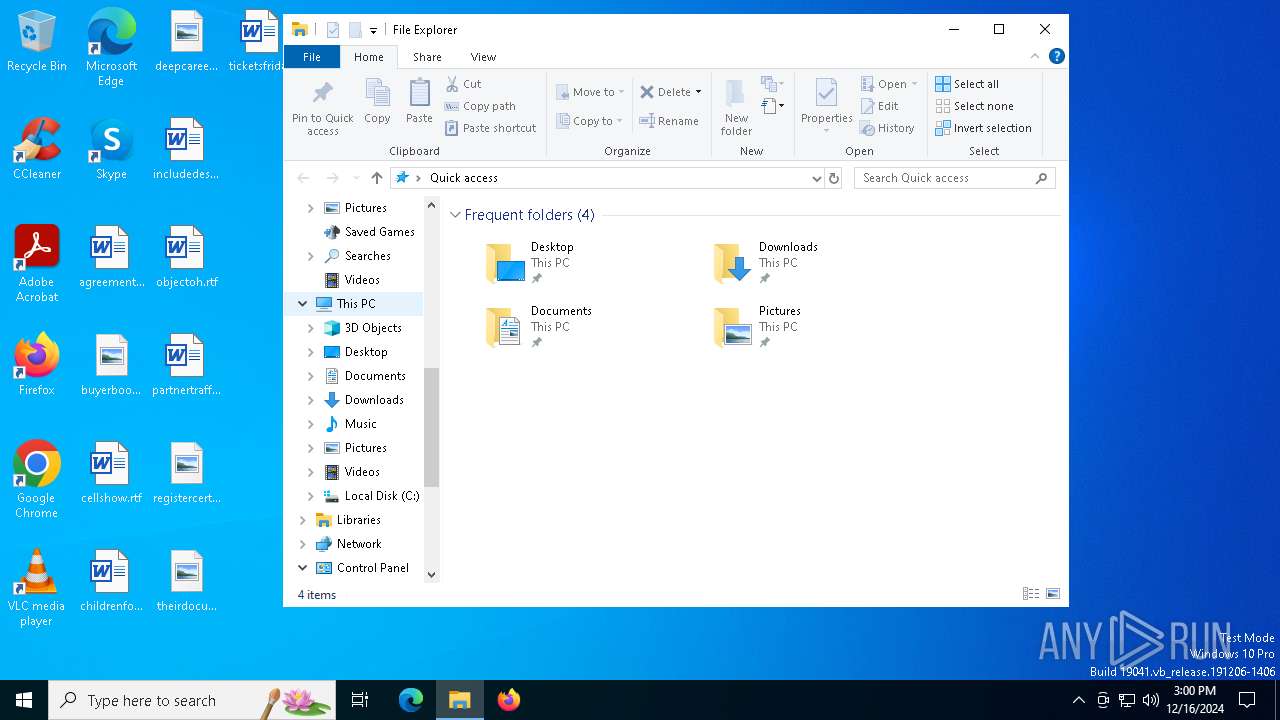
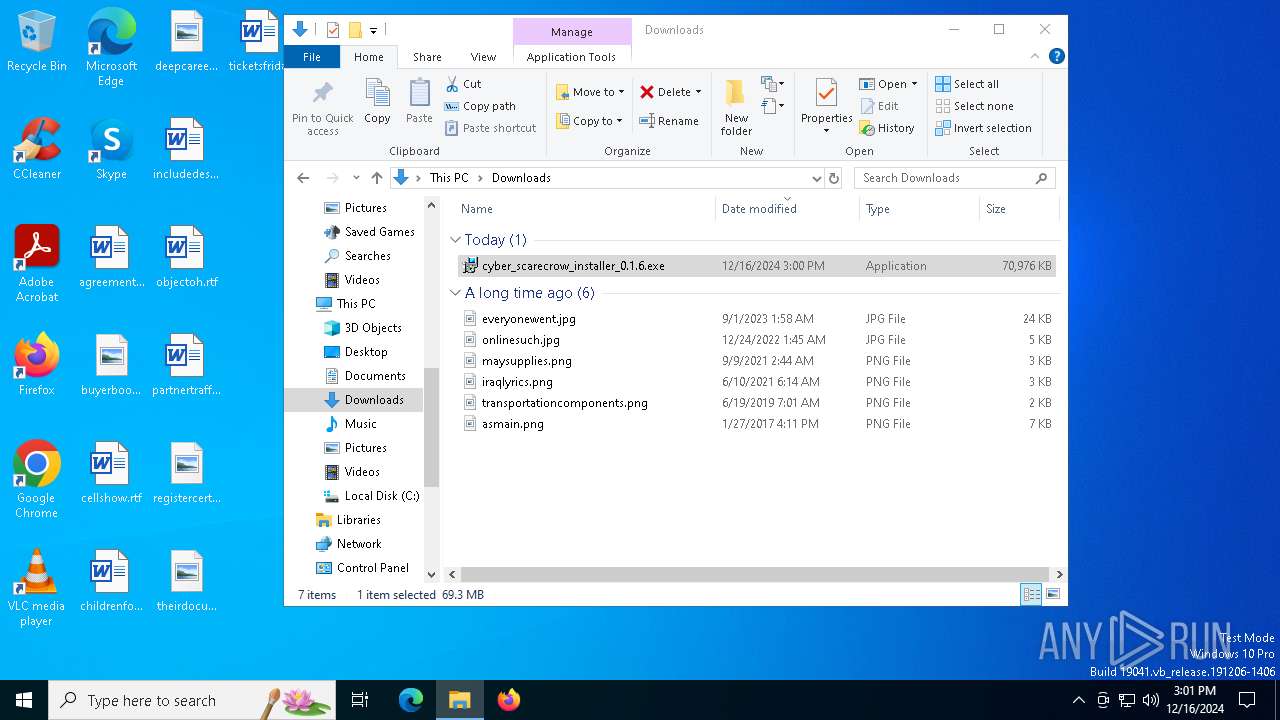
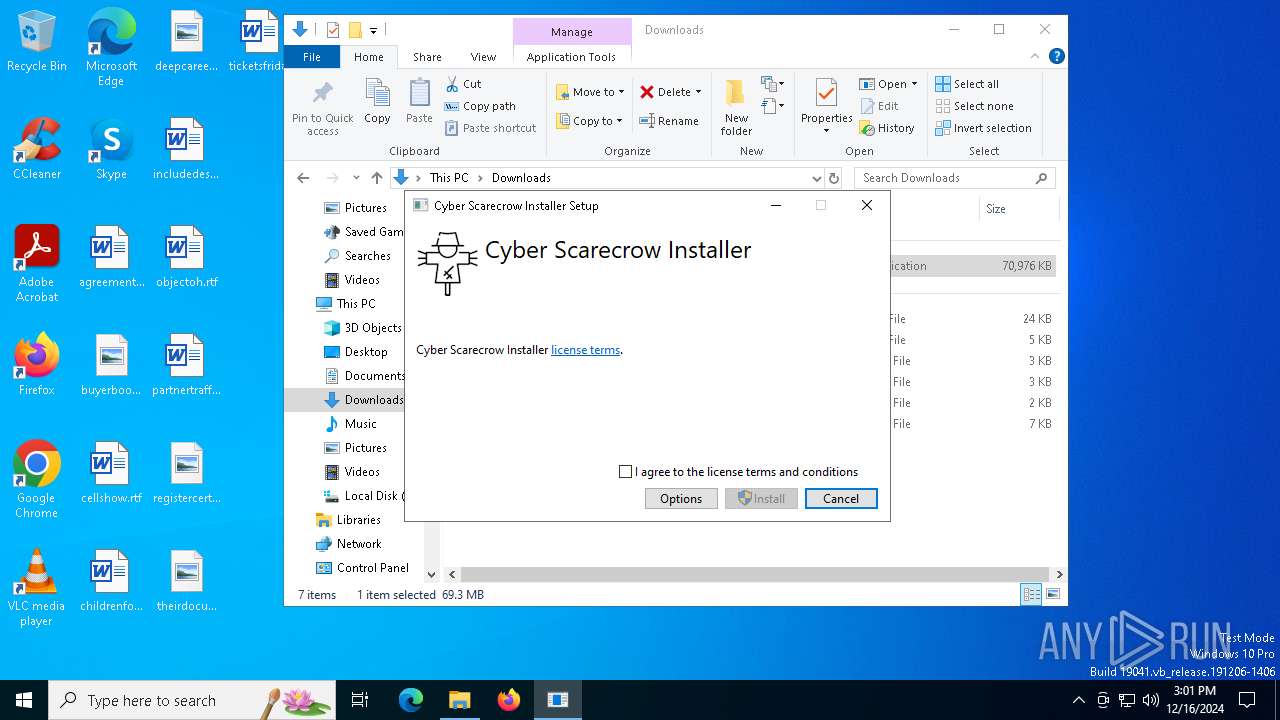
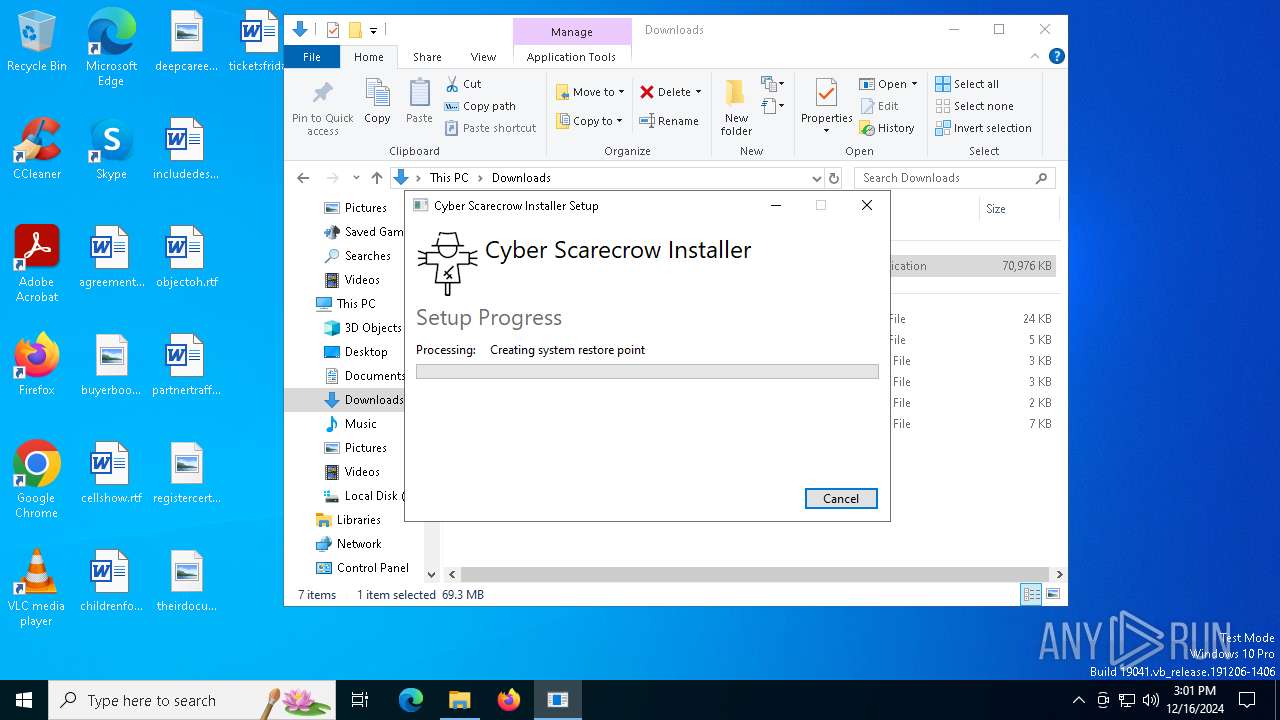
Manual execution by a user
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- scarecrow_tray.exe (PID: 7088)
- scarecrow_tray.exe (PID: 6568)
- Full-Setup.exe (PID: 5920)
The process uses the downloaded file
- msedge.exe (PID: 1296)
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
The sample compiled with english language support
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
- cyber_scarecrow_installer_VERSION.exe (PID: 6804)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 7084)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 6948)
- msiexec.exe (PID: 5316)
Create files in a temporary directory
- cyber_scarecrow_installer_0.1.6.exe (PID: 2324)
Manages system restore points
- SrTasks.exe (PID: 7000)
Reads the machine GUID from the registry
- cyber_scarecrow_installer_VERSION.exe (PID: 6804)
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 6948)
- msiexec.exe (PID: 5316)
Process checks computer location settings
- windowsdesktop-runtime-8.0.4-win-x64.exe (PID: 5972)
- scarecrow_tray.exe (PID: 6568)
Reads the software policy settings
- msiexec.exe (PID: 5316)
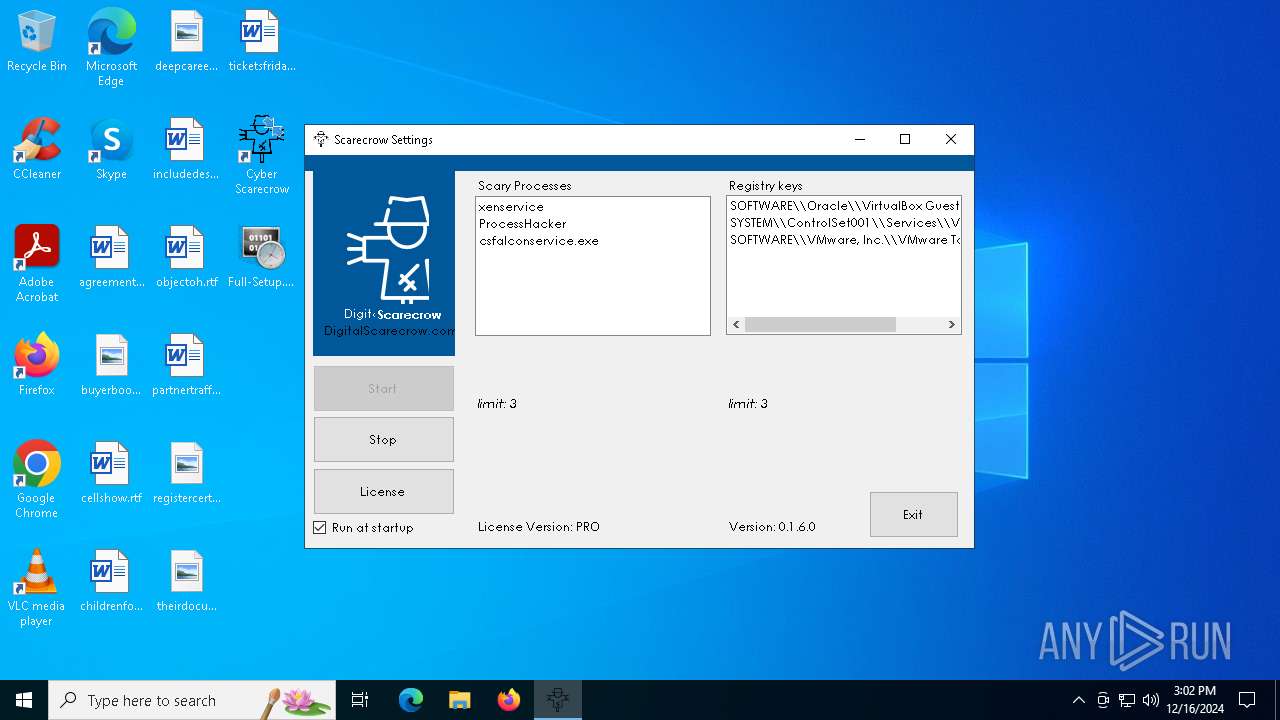
Sends debugging messages
- scarecrow_tray.exe (PID: 6568)
- xenservice.exe (PID: 4984)
- ProcessHacker.exe (PID: 6676)
- csfalconservice.exe.exe (PID: 6160)
Checks proxy server information
- scarecrow_tray.exe (PID: 6568)
Creates a software uninstall entry
- msiexec.exe (PID: 5316)
Creates a new folder
- cmd.exe (PID: 4336)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
112
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6544 --field-trial-handle=2272,i,6816670000879384849,4402314613703739810,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 396 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5720 --field-trial-handle=2272,i,6816670000879384849,4402314613703739810,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 396 | "C:\Windows\System32\cmd.exe" /c copy Helpful Helpful.cmd && Helpful.cmd | C:\Windows\SysWOW64\cmd.exe | — | Full-Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | C:\Windows\syswow64\MsiExec.exe -Embedding CD8D22F7593AC9D3E892B01EC2B519C0 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 748 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=6272 --field-trial-handle=2272,i,6816670000879384849,4402314613703739810,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1296 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4428 --field-trial-handle=2272,i,6816670000879384849,4402314613703739810,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5244 --field-trial-handle=2272,i,6816670000879384849,4402314613703739810,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1412 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7064 --field-trial-handle=2272,i,6816670000879384849,4402314613703739810,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1668 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5724 --field-trial-handle=2272,i,6816670000879384849,4402314613703739810,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4844 --field-trial-handle=2332,i,7765419575420960069,15358704752115235477,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
29 506
Read events
28 212
Write events
1 217
Delete events
77
Modification events
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FBE60DB7FA872F00 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B15A1EB7FA872F00 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2F4387AE-AC33-4F18-936A-B050A6BDFB0E} | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D3C20E5B-0E1A-4013-A719-223046432F4C} | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BFC8FD1A-5D02-41A6-9D74-F787BC0B7619} | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {88BCDFED-BC2A-4675-96D2-269F9C32BFA1} | |||
Executable files
536
Suspicious files
661
Text files
143
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136545.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF136555.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF136555.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136555.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136564.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
81
DNS requests
97
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3884 | svchost.exe | HEAD | 200 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
3884 | svchost.exe | GET | 206 | 151.101.86.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734861557&P2=404&P3=2&P4=IeGrv4H%2b7eLdX3XmEeOMmKL%2fIVYzqNA75Ygk1vwweTYtjblQiIIRngLeS%2bhzQuJO3oLLrpD8i%2fPNuSYiHF0uNg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6660 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6332 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6660 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6660 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6660 | msedge.exe | 23.36.77.235:443 | www.bing.com | Akamai International B.V. | NO | whitelisted |
6660 | msedge.exe | 23.36.76.202:443 | bzib.nelreports.net | Akamai International B.V. | NO | whitelisted |
6660 | msedge.exe | 76.76.21.98:443 | www.cyberscarecrow.com | AMAZON-02 | US | unknown |
6660 | msedge.exe | 13.107.246.74:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
716 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
www.cyberscarecrow.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
2408 | Deck.com | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
Process | Message |
|---|---|
scarecrow_tray.exe | info: Calling auto update service, https://update.digitalscarecrow.com/AutoUpdater.xml
|
scarecrow_tray.exe | info: Logfile: C:\Users\admin\AppData\Local\scarecrow\scarecrow_log.txt
|
scarecrow_tray.exe | info: Launching Scarecrow
|
scarecrow_tray.exe | info: Checking install ID
|
scarecrow_tray.exe | info: No install_id found, creating a new one: e052a06b-3189-4b0c-ab85-66b7777523b6
|
scarecrow_tray.exe | info: DeviceID is: EVWFRJP74TB5ARV5DP3VBDQ7NVN05JGYKR1VSJ2J2N5AKS6WYS00
|
scarecrow_tray.exe | info: Scarecrow_core:Scarecrow 0.1.6+2cd720c546bb6a127202a944985244701d90dbe6 Started
|
scarecrow_tray.exe | info: CWD: C:\Program Files\Cyber Scarecrow
|
scarecrow_tray.exe | info: EWD: C:\Program Files\Cyber Scarecrow
|
scarecrow_tray.exe | info: Registry key for autostart not found, creating and initialising it to default: 1
|