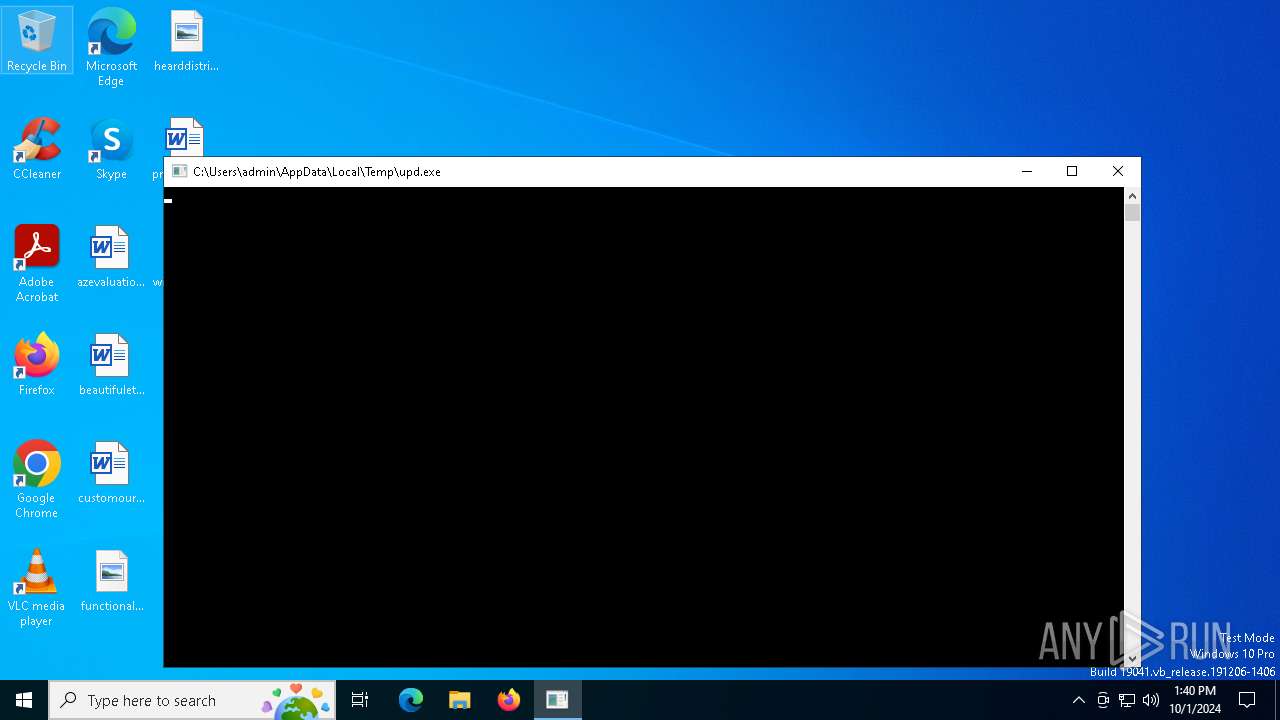
| File name: | upd.exe |
| Full analysis: | https://app.any.run/tasks/423b23d7-466a-4089-aa79-20a1e25714aa |
| Verdict: | Malicious activity |
| Threats: | MetaStealer is an info-stealing malware primarily targeting sensitive data like login credentials, payment details, and browser history. It typically infects systems via phishing emails or malicious downloads and can exfiltrate data to a command and control (C2) server. MetaStealer is known for its stealthy techniques, including evasion and persistence mechanisms, which make it difficult to detect. This malware has been actively used in various cyberattacks, particularly for financial theft and credential harvesting from individuals and organizations. |
| Analysis date: | October 01, 2024, 13:40:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A549BF16626F77D157EC22CF3DF30090 |
| SHA1: | 4BC271C9394746A18DCE93874623C505AC43E2A3 |
| SHA256: | 2C23D6102086BE047725664D1E28A1C4366D51AE476EA80416E599584E95D163 |
| SSDEEP: | 12288:yL43c0HNjo2bGydAnjXuUx0QDy7ZPwG0mb8aPnCPRjHo9Np9Ix6mrGdzt9:yL43FtjoWGydAn7uUx0Yy7ZPw |
MALICIOUS
REDLINE has been detected (SURICATA)
- MSBuild.exe (PID: 2932)
Connects to the CnC server
- MSBuild.exe (PID: 2932)
METASTEALER has been detected (SURICATA)
- MSBuild.exe (PID: 2932)
Stealers network behavior
- MSBuild.exe (PID: 2932)
REDLINE has been detected (YARA)
- MSBuild.exe (PID: 2932)
SUSPICIOUS
Executable content was dropped or overwritten
- upd.exe (PID: 4276)
Potential Corporate Privacy Violation
- MSBuild.exe (PID: 2932)
Checks for external IP
- svchost.exe (PID: 2256)
- MSBuild.exe (PID: 2932)
INFO
Checks supported languages
- upd.exe (PID: 4276)
- MSBuild.exe (PID: 2932)
Creates files or folders in the user directory
- upd.exe (PID: 4276)
Reads the computer name
- upd.exe (PID: 4276)
- MSBuild.exe (PID: 2932)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(2932) MSBuild.exe
C2 (1)185.215.113.22:80
Botnet@purple_dxxd
Options
ErrorMessage
Keys
XorAnacrustic
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:17 19:13:40+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 79360 |
| InitializedDataSize: | 346624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6e00a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.3.4 |
| ProductVersionNumber: | 0.0.3.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Shaping immersive experiences through visionary optics and digital innovation. |
| CompanyName: | ThinkVision Technologies Inc. |
| FileDescription: | ThinkVision Systems |
| FileVersion: | 0.0.3.4 |
| InternalName: | JackPeloci802Zachary.jar |
| LegalCopyright: | Copyright © 2026 |
| LegalTrademarks: | ThinkVision Technologies Trademark |
| OriginalFileName: | JackPeloci802Zachary.jar |
| ProductName: | ThinkVision OptiTech Suite |
| ProductVersion: | 0.0.3.4 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
131
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2932 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | upd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
RedLine(PID) Process(2932) MSBuild.exe C2 (1)185.215.113.22:80 Botnet@purple_dxxd Options ErrorMessage Keys XorAnacrustic | |||||||||||||||
| 4276 | "C:\Users\admin\AppData\Local\Temp\upd.exe" | C:\Users\admin\AppData\Local\Temp\upd.exe | explorer.exe | ||||||||||||
User: admin Company: ThinkVision Technologies Inc. Integrity Level: MEDIUM Description: ThinkVision Systems Exit code: 0 Version: 0.0.3.4 Modules
| |||||||||||||||
| 6568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | upd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 517
Read events
3 503
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2932) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4276 | upd.exe | C:\Users\admin\AppData\Roaming\msvcp110.dll | executable | |
MD5:3AB545CDAFDBB57BFA4F078F7AEB4FC6 | SHA256:BA7DA375D2C40AD31ACDA978D021A8F7AD32C4A95AB79E35097925B71D62F545 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
42
DNS requests
17
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1336 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4976 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5732 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5732 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2932 | MSBuild.exe | 185.215.113.22:80 | — | 1337team Limited | SC | malicious |
4324 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
8 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2932 | MSBuild.exe | 104.26.13.31:443 | api.ip.sb | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.ip.sb |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2932 | MSBuild.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
2932 | MSBuild.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
2932 | MSBuild.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer/MetaStealer Family Related (MC-NMF Authorization) |
2932 | MSBuild.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
2932 | MSBuild.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
2932 | MSBuild.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
2932 | MSBuild.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
3 ETPRO signatures available at the full report