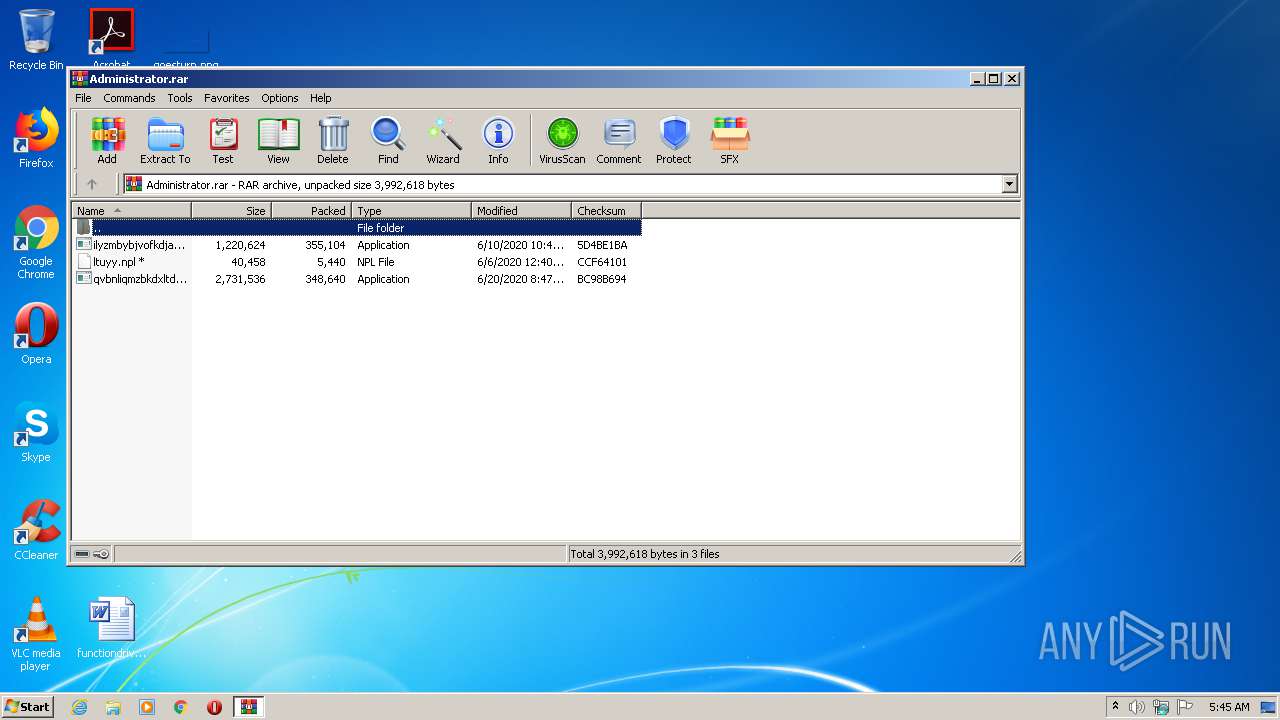
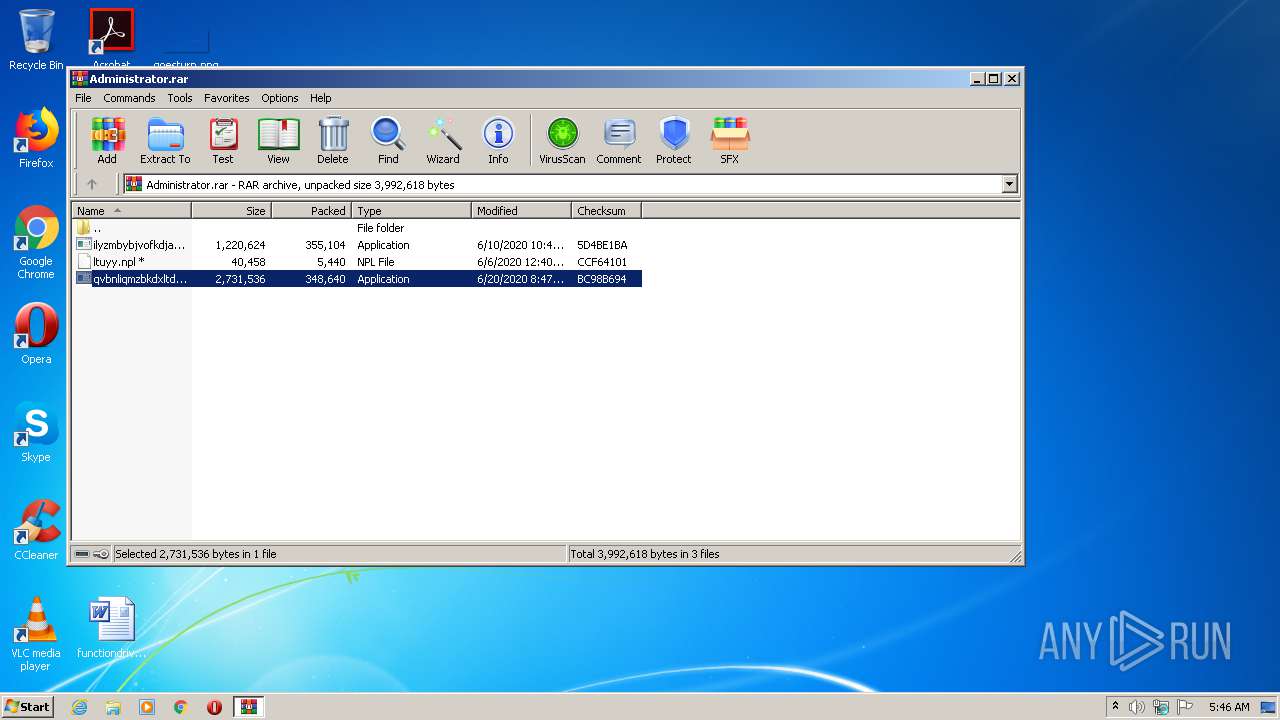
| File name: | Administrator.rar |
| Full analysis: | https://app.any.run/tasks/1768ffb8-a910-47c5-a41a-5e0bfd36f7c1 |
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | July 13, 2020, 04:45:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 54C7A7D2EB2FF91F1C613BC87DAFDB74 |
| SHA1: | C4EE79D08FB97325586E9EA63DD8F07229C453A3 |
| SHA256: | 2BECE5FF07E81901F7B289D12745998AB432D3C560F7CB0D107D3BB38040B386 |
| SSDEEP: | 12288:sTAzgBBLUTTrESsN734//nlSRwc/QeqDC10uQX7KRk78/jm6ZzCvT:sTReejq/nlSn/SO10uu7KRkg/HpCL |
MALICIOUS
Application was dropped or rewritten from another process
- qvbnliqmzbkdxltdpnncutkzsml.exe (PID: 2956)
- qvbnliqmzbkdxltdpnncutkzsml.exe (PID: 1456)
- ytfovlym.exe (PID: 2476)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3788)
QBOT was detected
- qvbnliqmzbkdxltdpnncutkzsml.exe (PID: 2956)
SUSPICIOUS
Executable content was dropped or overwritten
- qvbnliqmzbkdxltdpnncutkzsml.exe (PID: 2956)
- WinRAR.exe (PID: 184)
Creates files in the user directory
- qvbnliqmzbkdxltdpnncutkzsml.exe (PID: 2956)
Starts itself from another location
- qvbnliqmzbkdxltdpnncutkzsml.exe (PID: 2956)
Starts CMD.EXE for commands execution
- qvbnliqmzbkdxltdpnncutkzsml.exe (PID: 2956)
Application launched itself
- qvbnliqmzbkdxltdpnncutkzsml.exe (PID: 2956)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
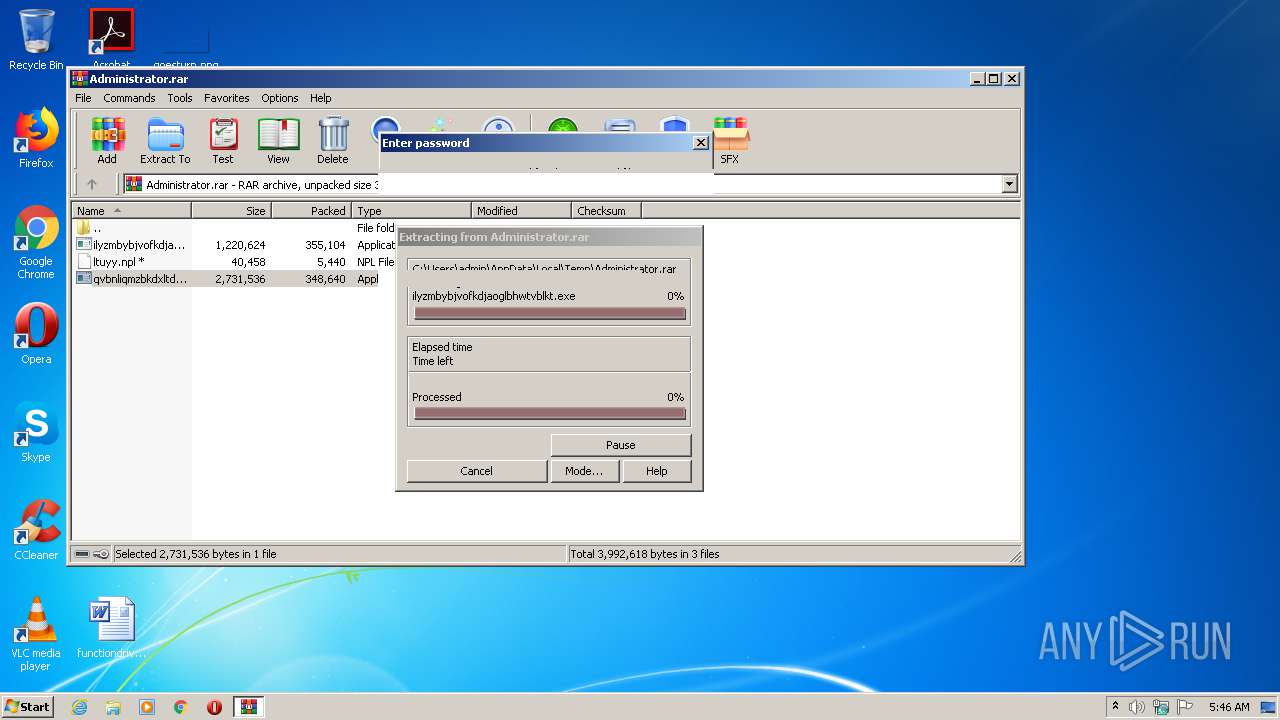
| 184 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Administrator.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1456 | C:\Users\admin\AppData\Local\Temp\Rar$EXb184.38730\qvbnliqmzbkdxltdpnncutkzsml.exe /C | C:\Users\admin\AppData\Local\Temp\Rar$EXb184.38730\qvbnliqmzbkdxltdpnncutkzsml.exe | — | qvbnliqmzbkdxltdpnncutkzsml.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SAM Lock Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | ping.exe -n 6 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | qvbnliqmzbkdxltdpnncutkzsml.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SAM Lock Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb184.38730\qvbnliqmzbkdxltdpnncutkzsml.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb184.38730\qvbnliqmzbkdxltdpnncutkzsml.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SAM Lock Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3788 | "C:\Windows\System32\cmd.exe" /c ping.exe -n 6 127.0.0.1 & type "C:\Windows\System32\calc.exe" > "C:\Users\admin\AppData\Local\Temp\Rar$EXb184.38730\qvbnliqmzbkdxltdpnncutkzsml.exe" | C:\Windows\System32\cmd.exe | — | qvbnliqmzbkdxltdpnncutkzsml.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
513
Read events
495
Write events
18
Delete events
0
Modification events
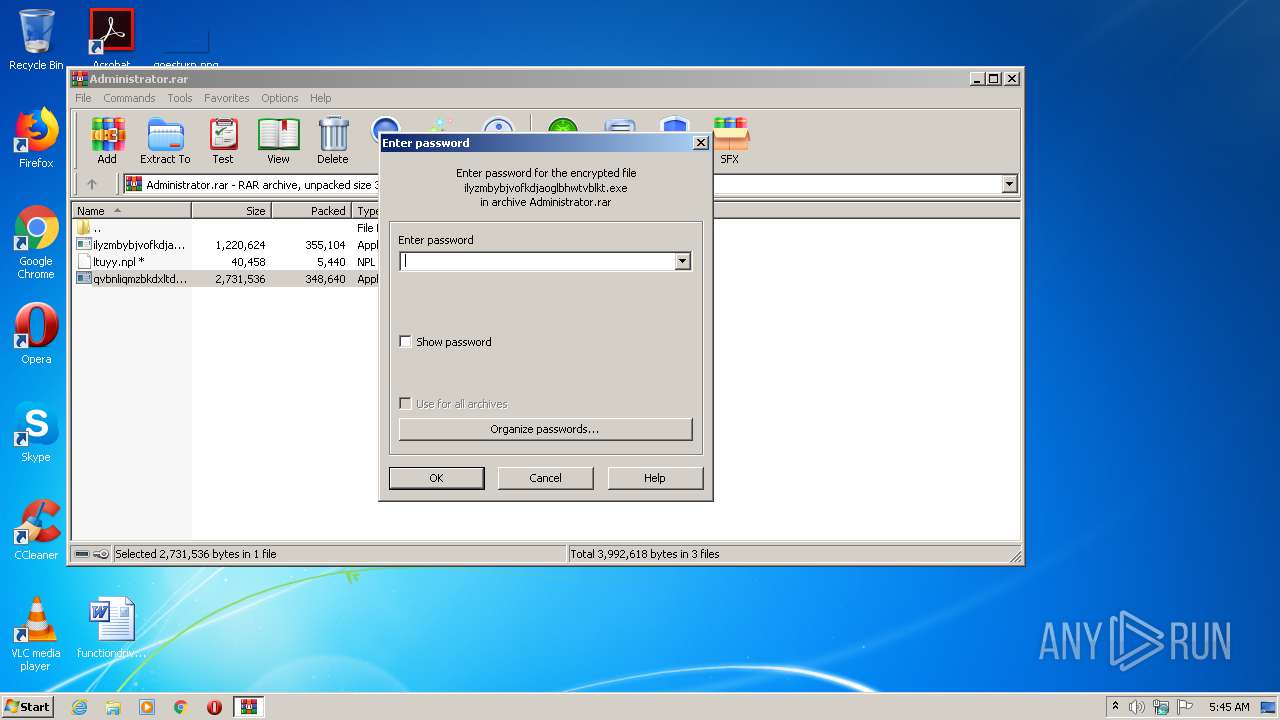
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Administrator.rar | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
Executable files
3
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb184.38730\ilyzmbybjvofkdjaoglbhwtvblkt.exe | executable | |
MD5:— | SHA256:— | |||
| 184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb184.38730\ltuyy.npl | text | |
MD5:— | SHA256:— | |||
| 2956 | qvbnliqmzbkdxltdpnncutkzsml.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.dat | binary | |
MD5:— | SHA256:— | |||
| 184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb184.38730\qvbnliqmzbkdxltdpnncutkzsml.exe | executable | |
MD5:— | SHA256:— | |||
| 2956 | qvbnliqmzbkdxltdpnncutkzsml.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report