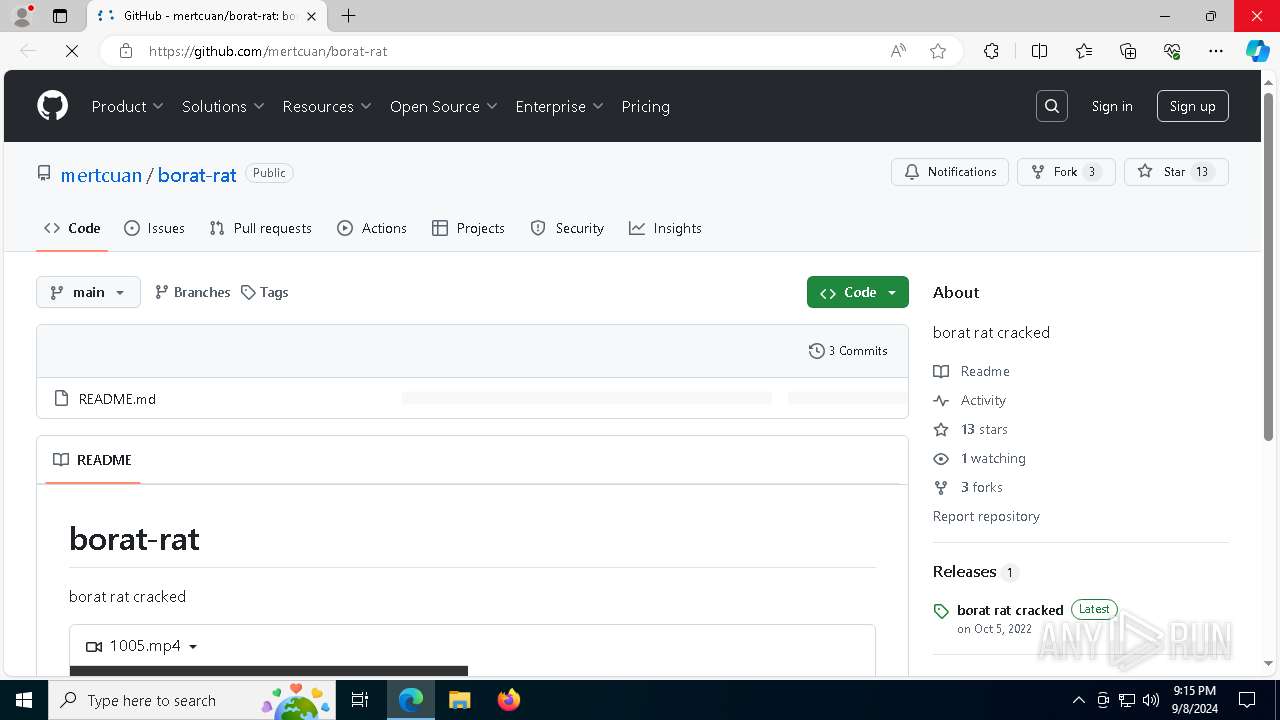
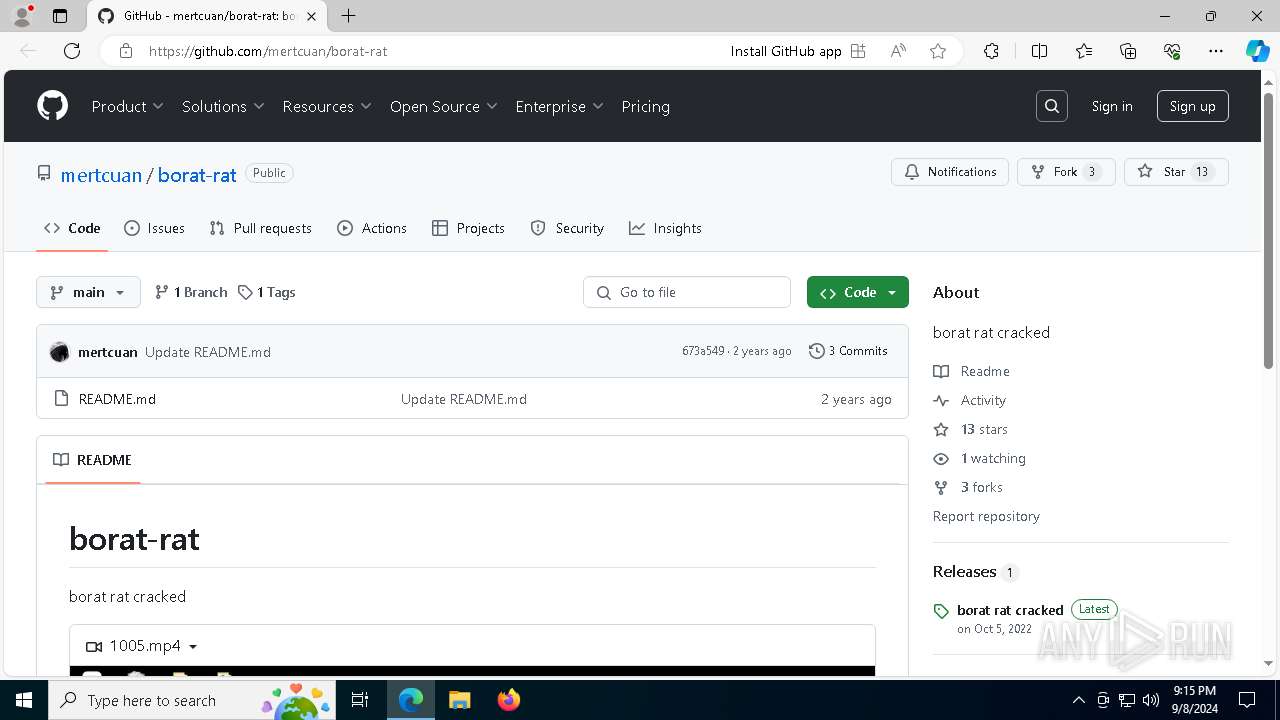
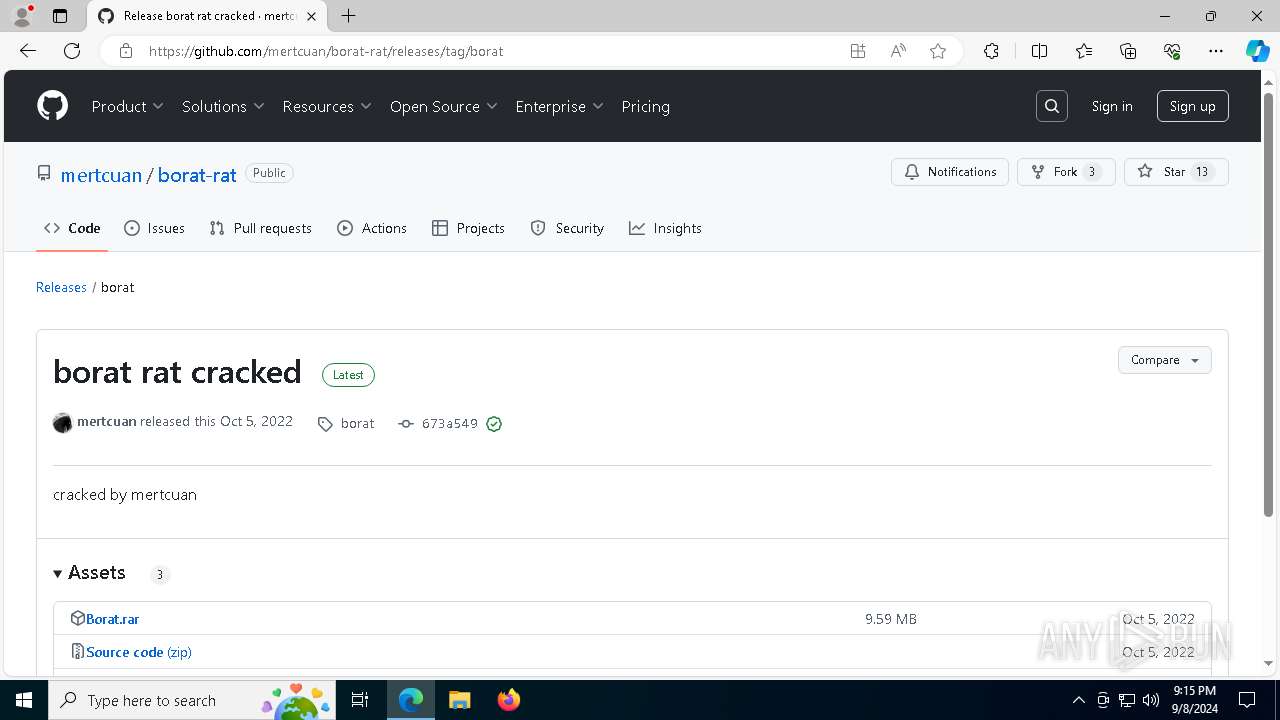
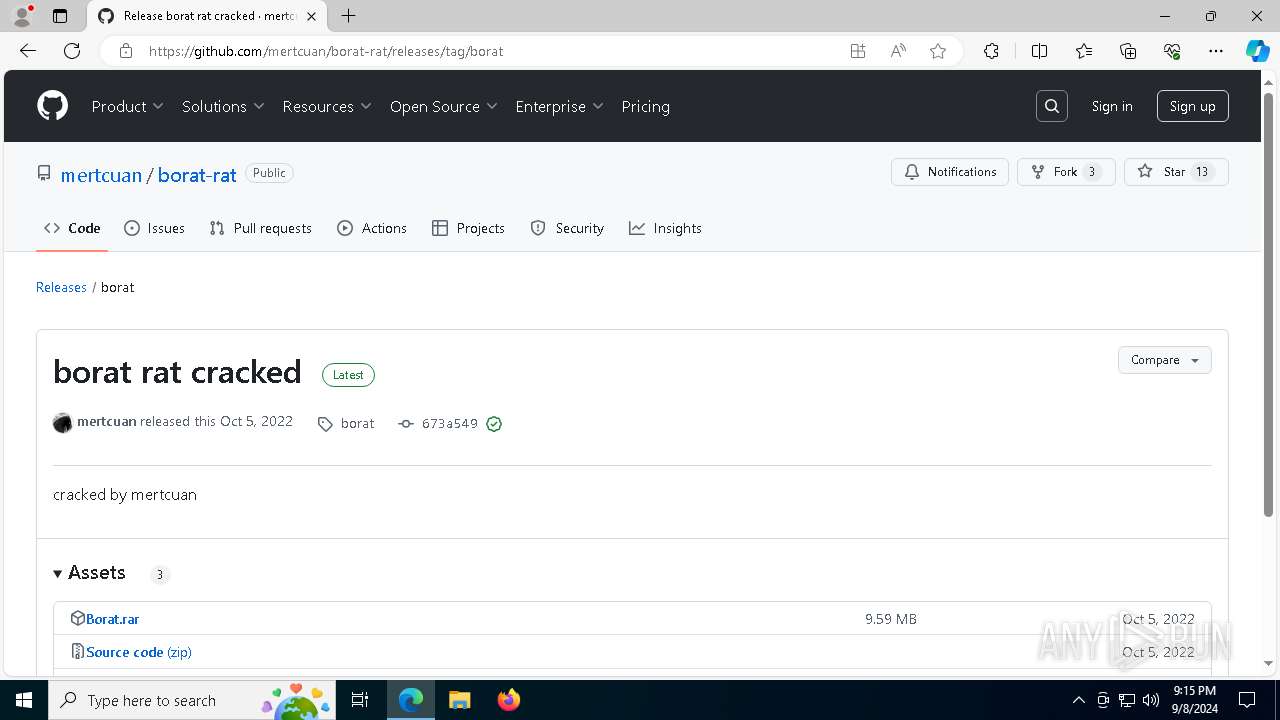
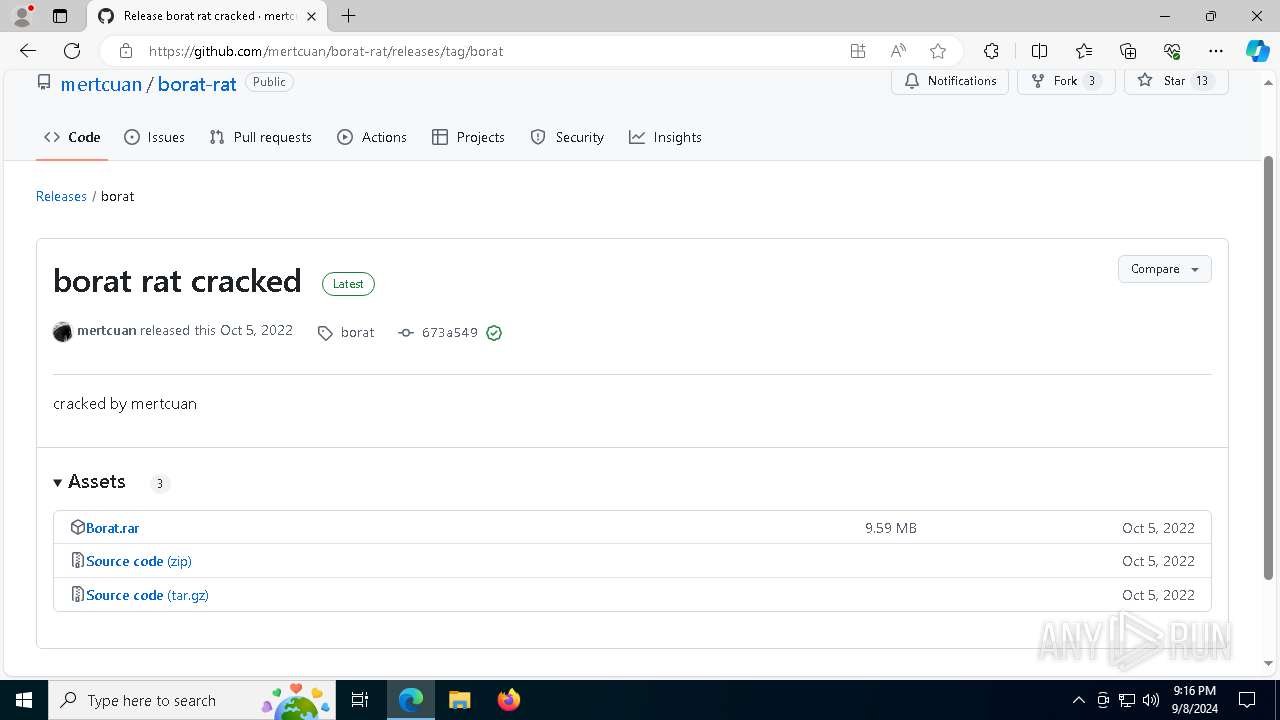
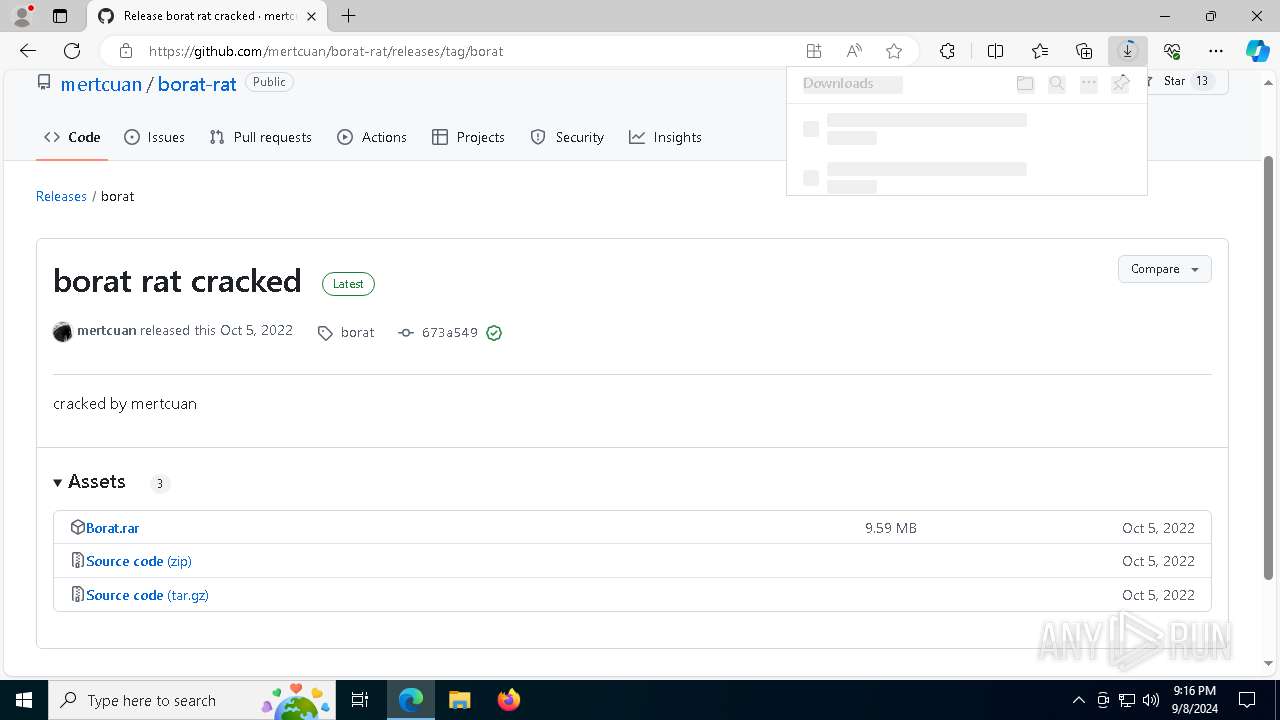
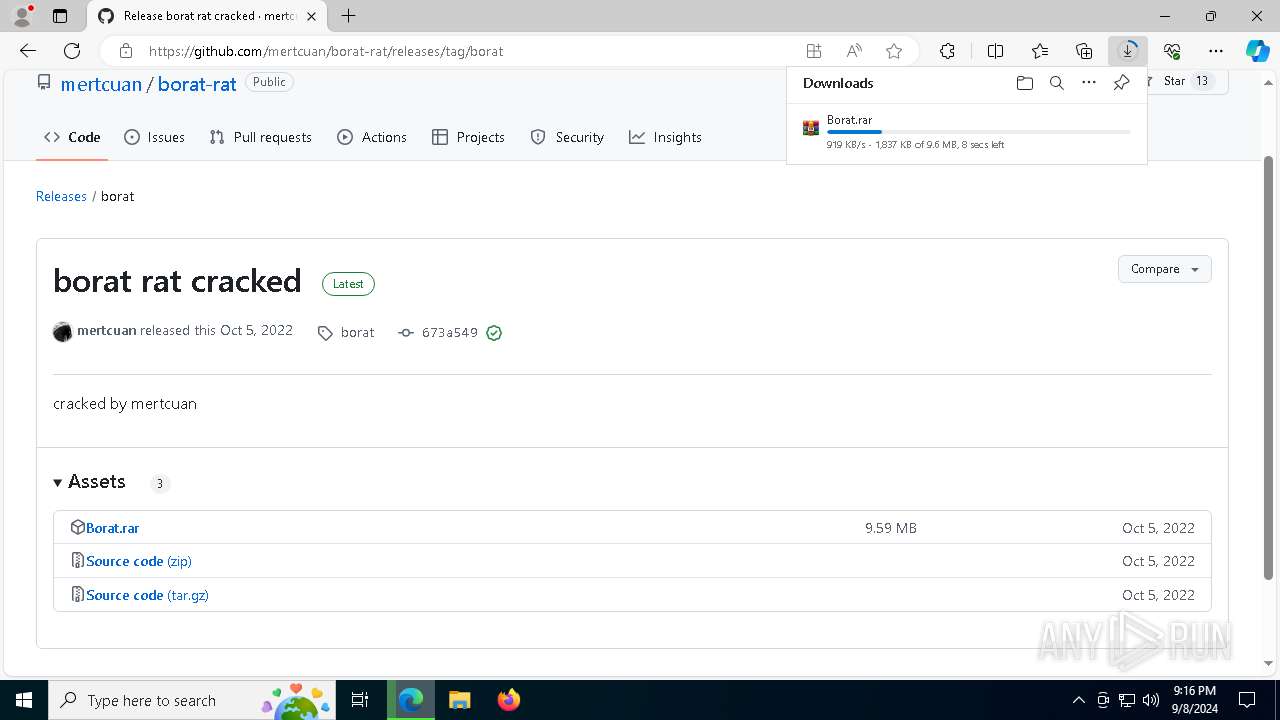
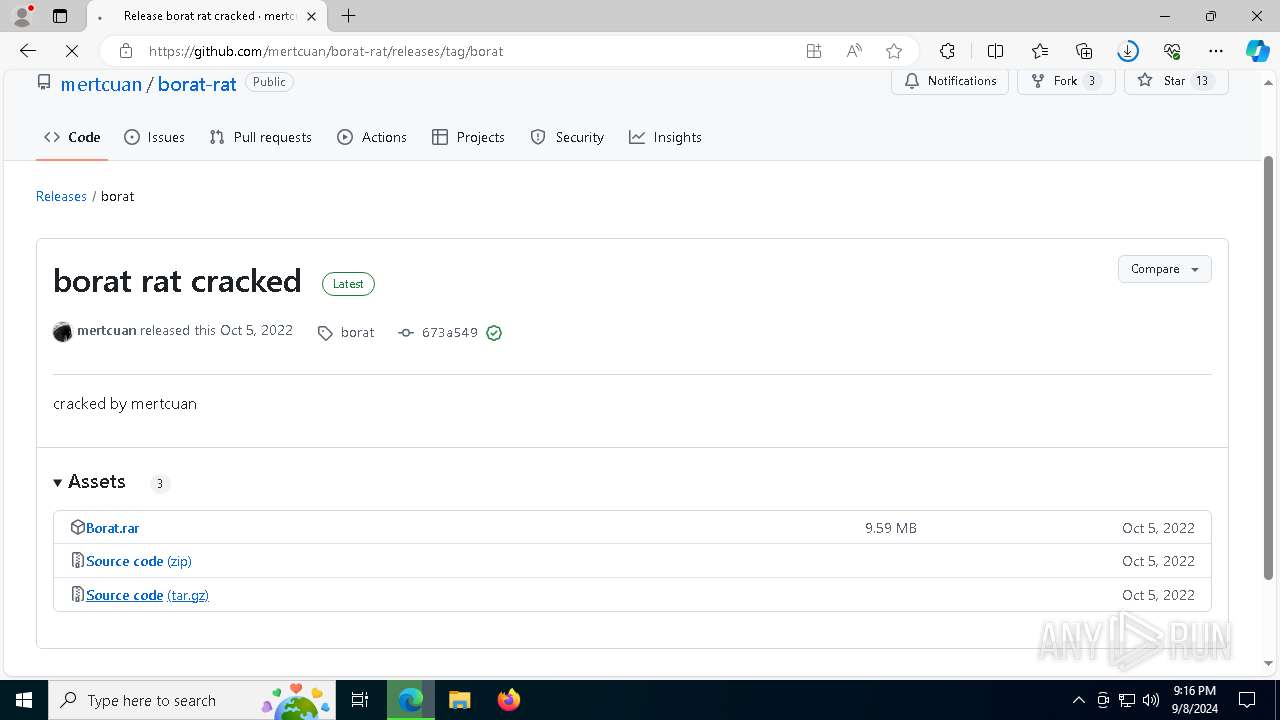
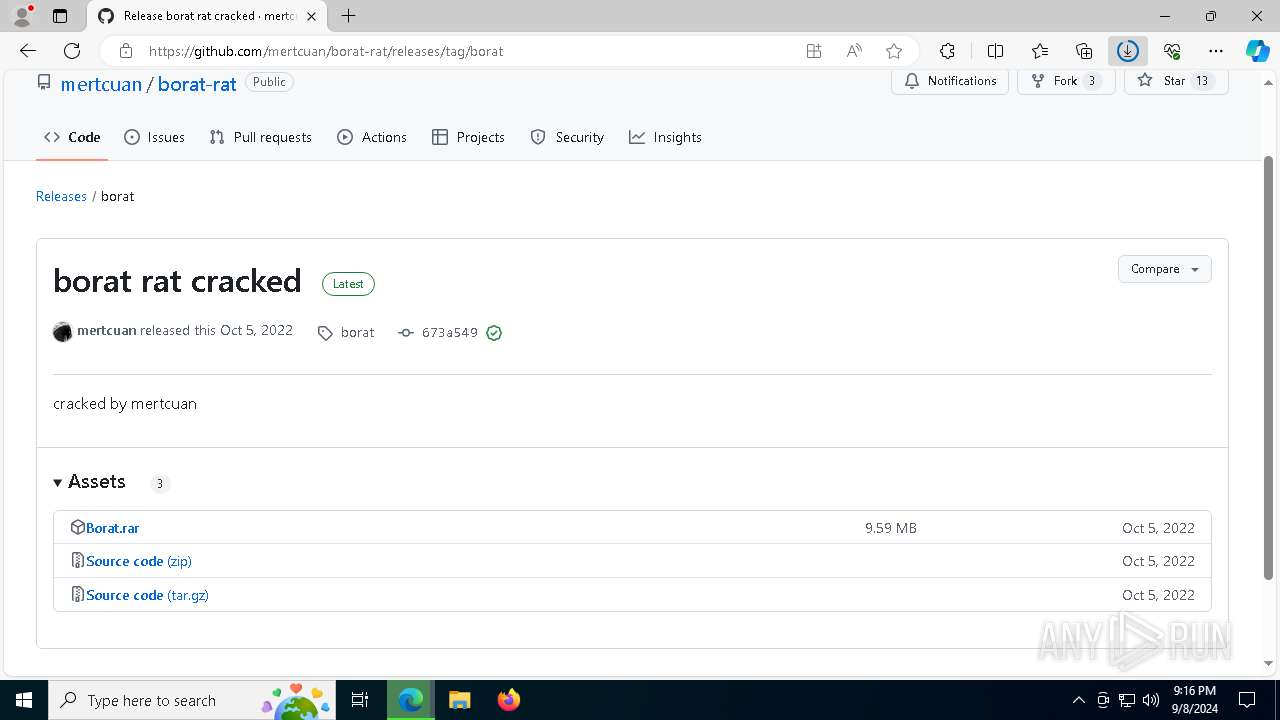
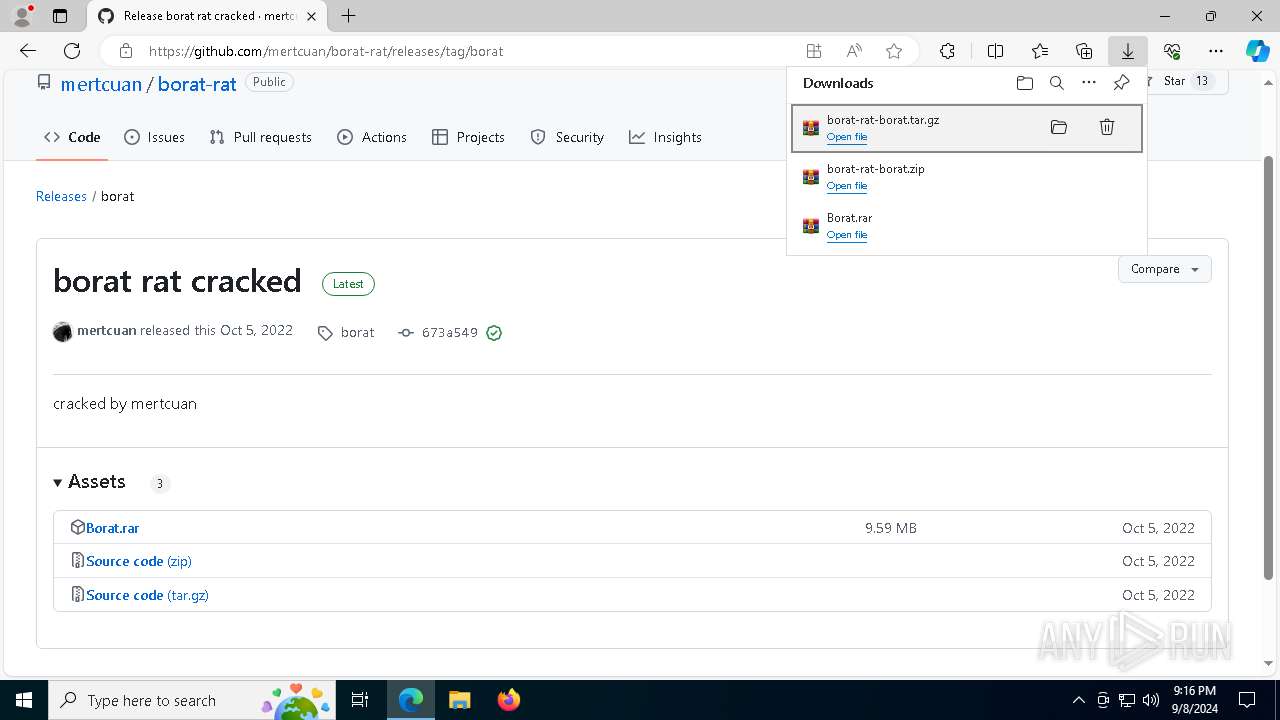
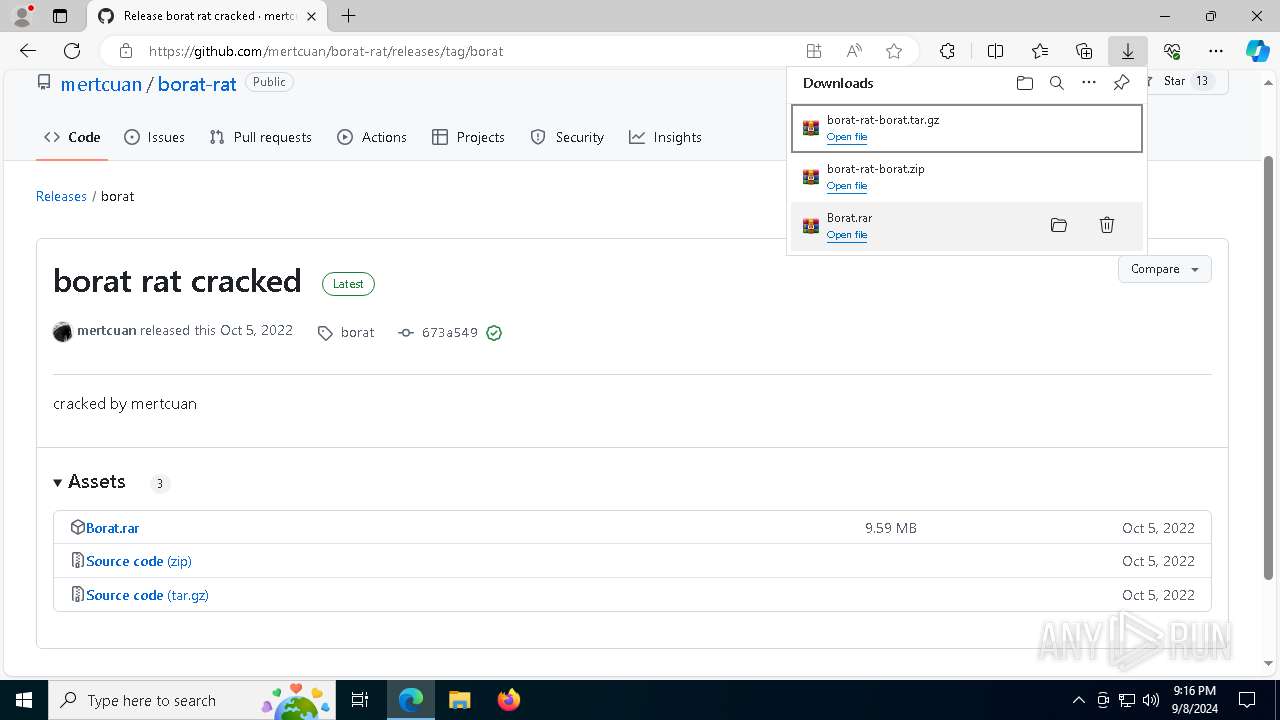
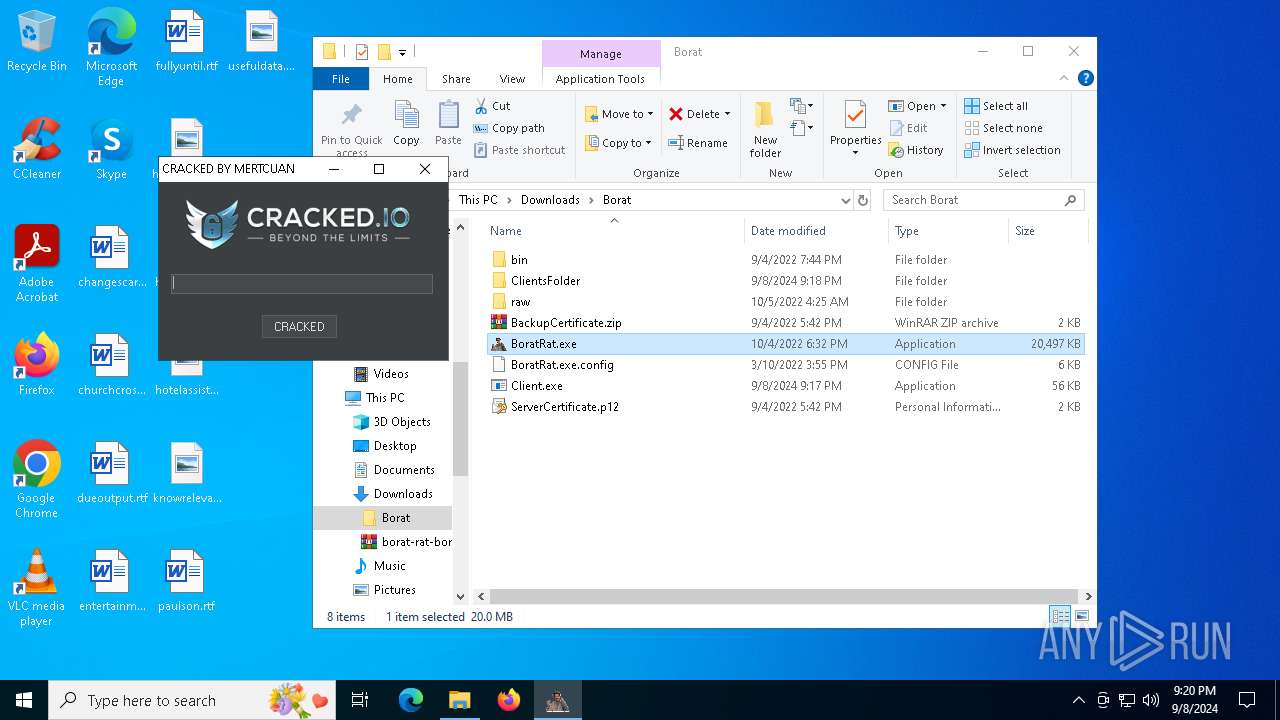
| URL: | https://github.com/mertcuan/borat-rat |
| Full analysis: | https://app.any.run/tasks/024c5f11-ba1a-4f53-8da9-d09535a38b1e |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
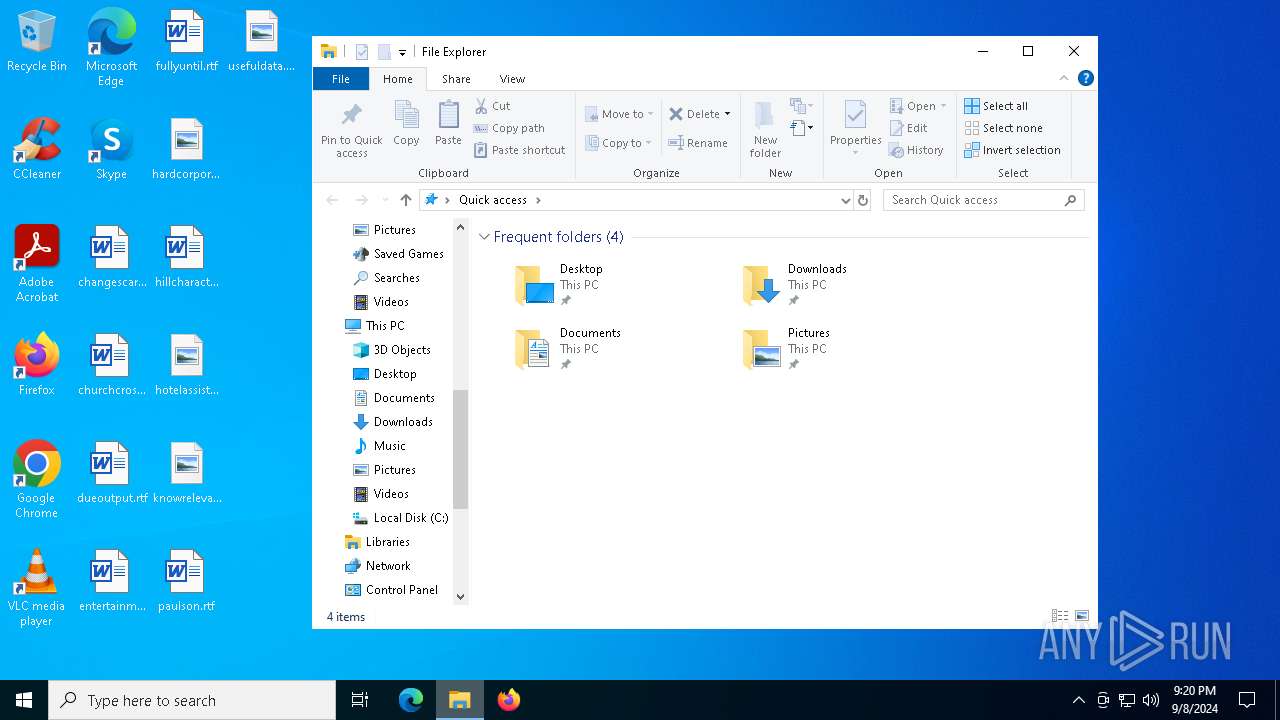
| Analysis date: | September 08, 2024, 21:15:26 |
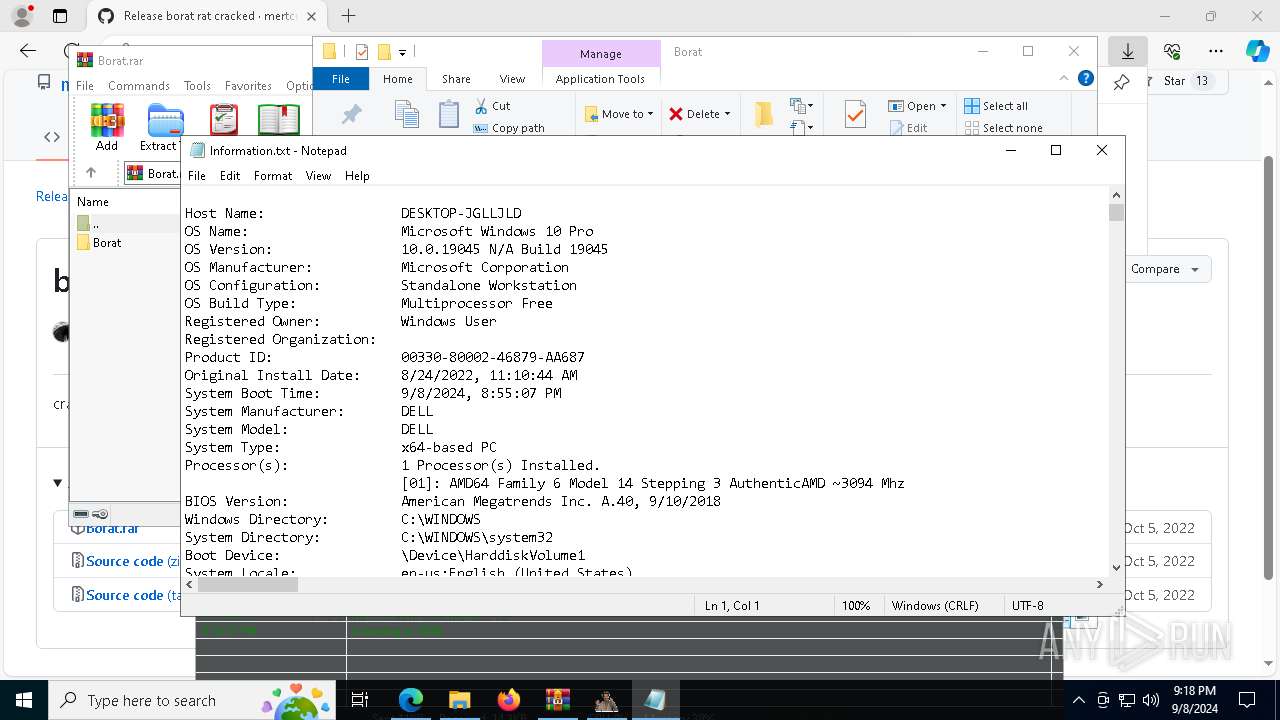
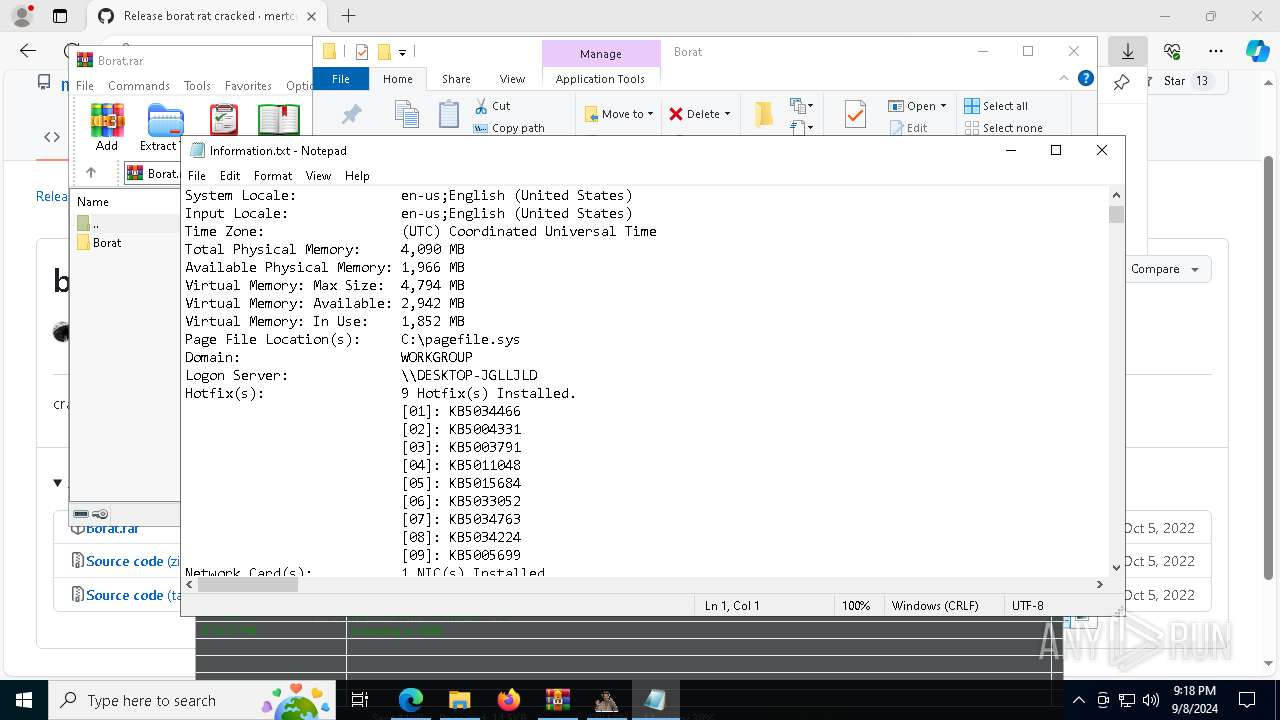
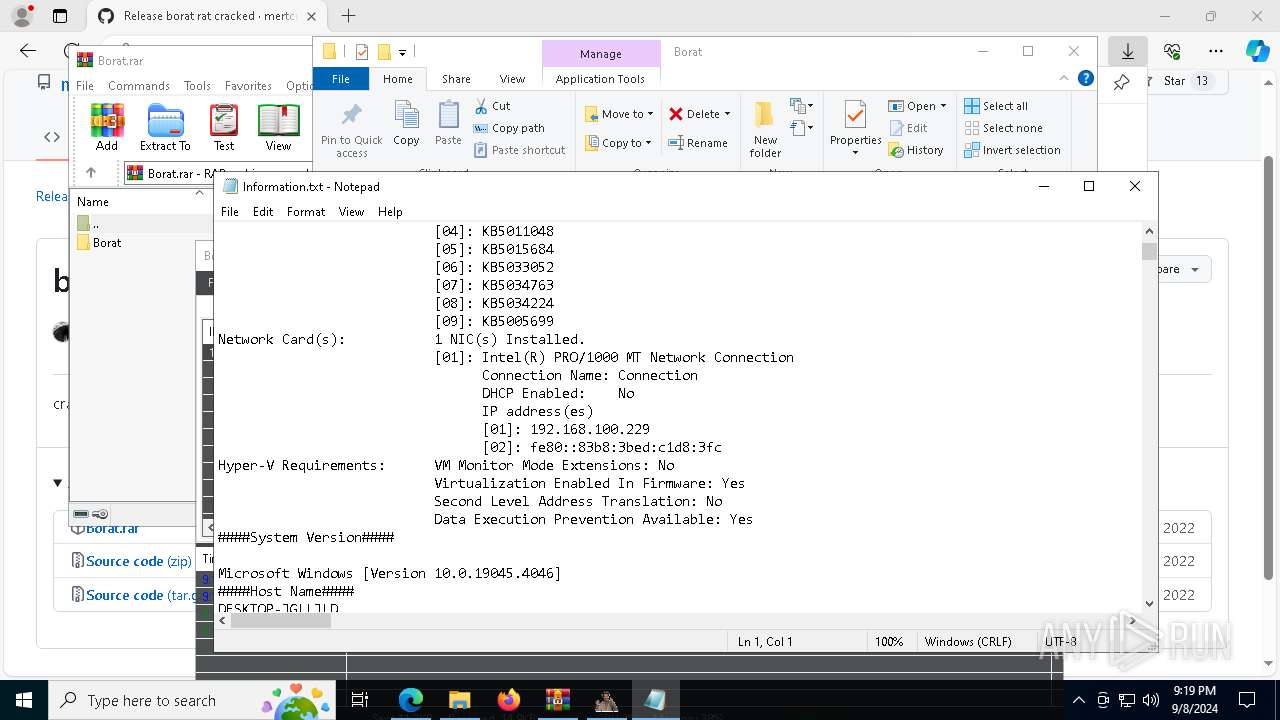
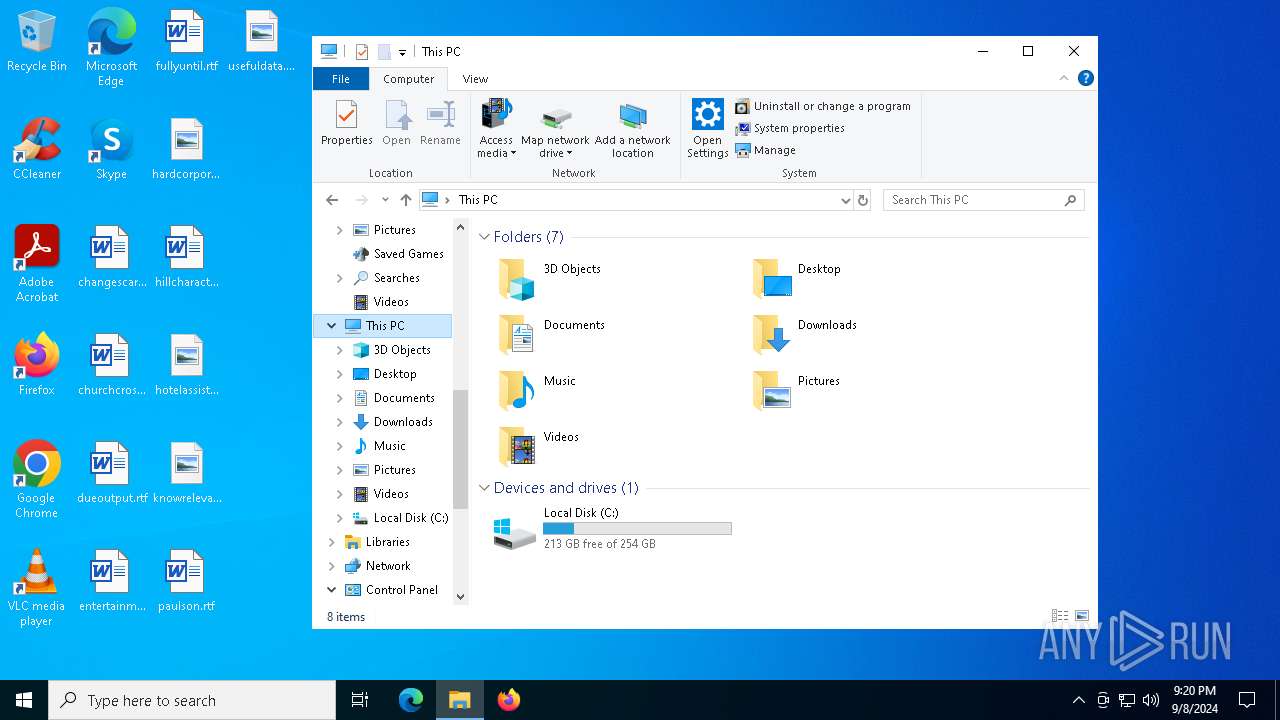
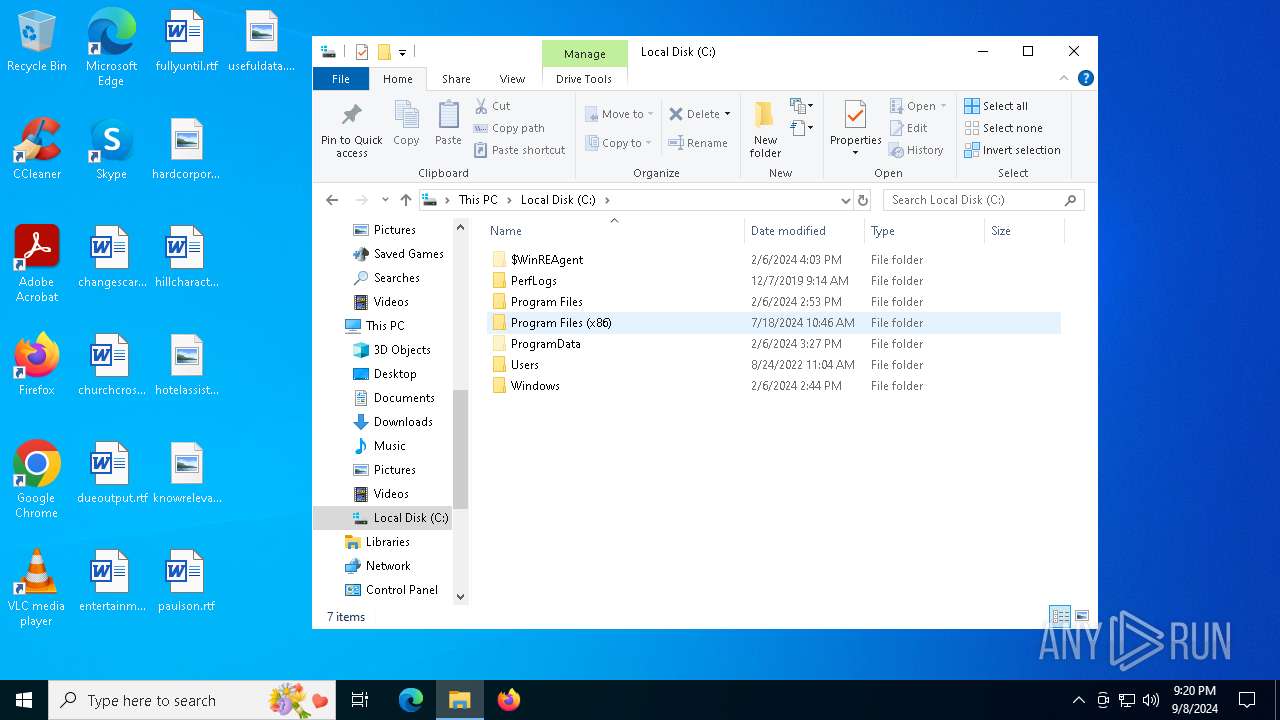
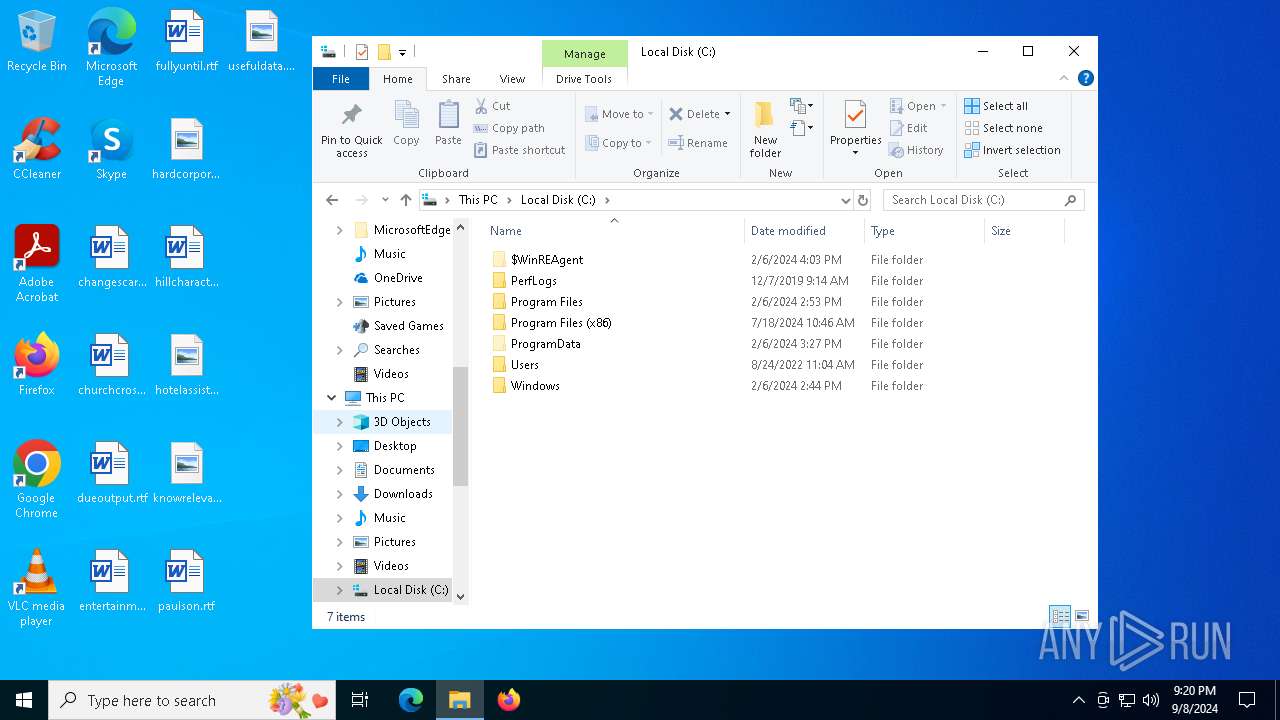
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9EEE1E46659D0A468ACC942A1480D960 |
| SHA1: | 16E06E465E29492973CCE55C3ABB477235C83C19 |
| SHA256: | 2BDA73160A1CBE4448104D6E3C004094AEAC6328B4CEB81BAC626673BE39750A |
| SSDEEP: | 3:N8tEd4FtsqER:2uuFSqER |
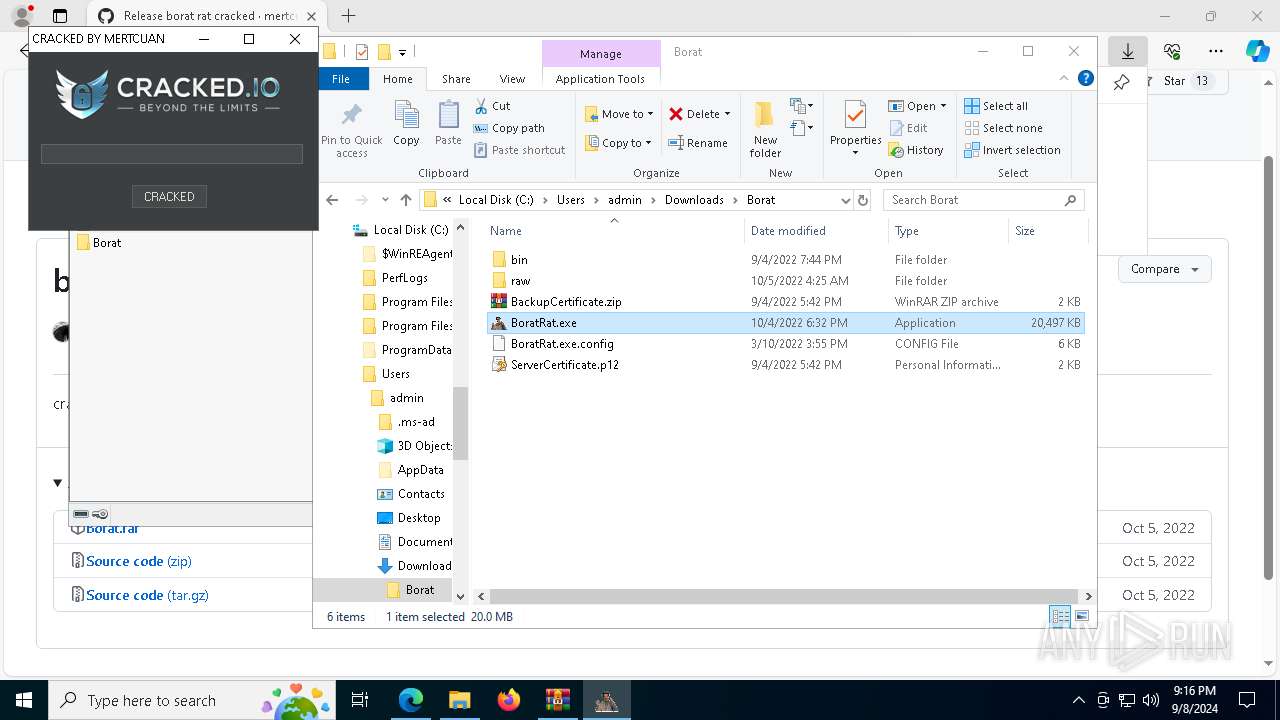
MALICIOUS
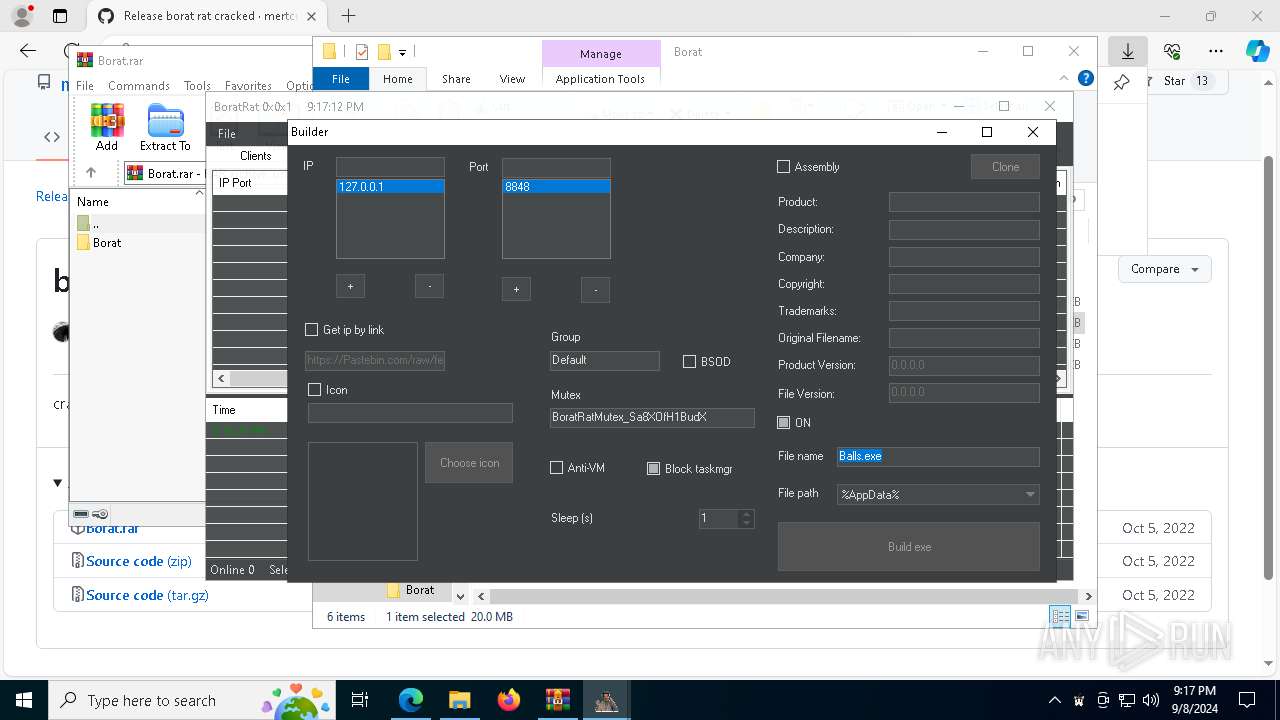
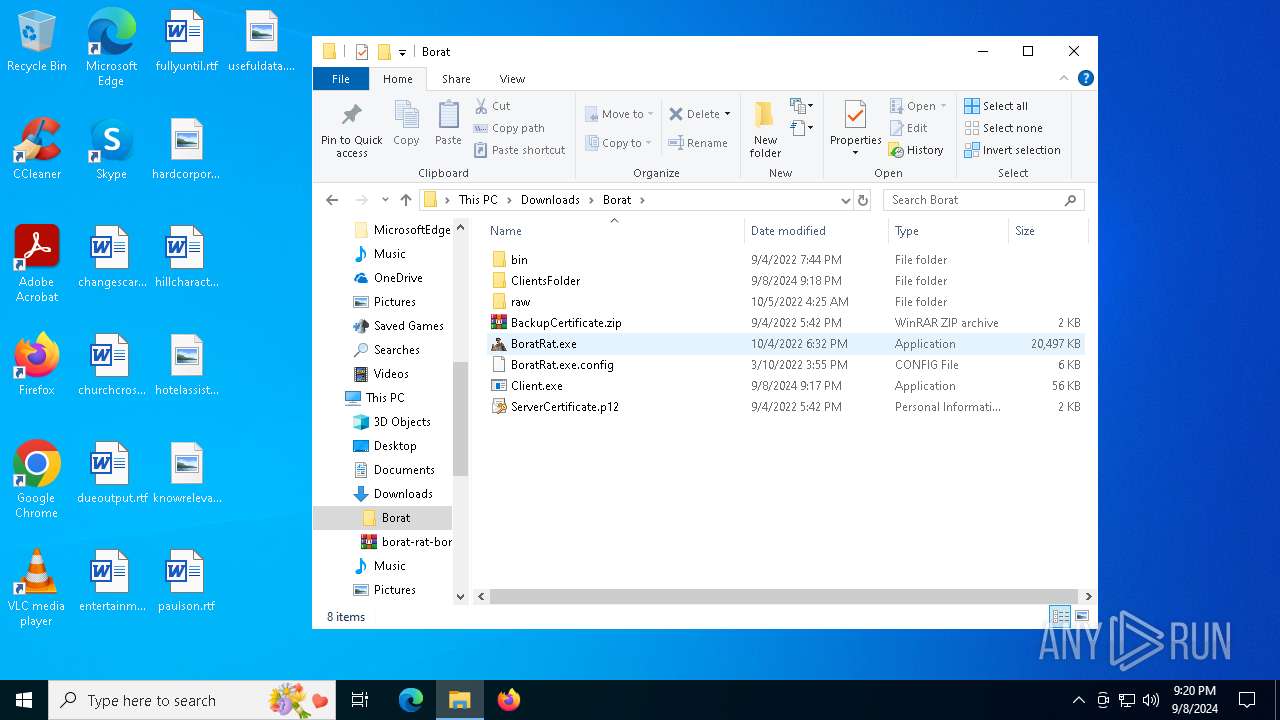
ASYNCRAT has been detected (YARA)
- BoratRat.exe (PID: 2136)
- Balls.exe (PID: 7472)
BORAT mutex has been found
- Client.exe (PID: 4056)
- Balls.exe (PID: 7472)
- Balls.exe (PID: 6024)
Changes the autorun value in the registry
- Client.exe (PID: 4056)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 5588)
- net.exe (PID: 7852)
- net.exe (PID: 4072)
- net.exe (PID: 1964)
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 5588)
- net.exe (PID: 1064)
- net.exe (PID: 964)
SUSPICIOUS
The process creates files with name similar to system file names
- WinRAR.exe (PID: 1020)
Reads security settings of Internet Explorer
- BoratRat.exe (PID: 2136)
- Balls.exe (PID: 7472)
- GameBar.exe (PID: 6000)
- StartMenuExperienceHost.exe (PID: 4080)
- BoratRat.exe (PID: 1664)
The process checks if it is being run in the virtual environment
- BoratRat.exe (PID: 2136)
- BoratRat.exe (PID: 1664)
Executable content was dropped or overwritten
- BoratRat.exe (PID: 2136)
- Client.exe (PID: 4056)
Creates file in the systems drive root
- BoratRat.exe (PID: 2136)
Executing commands from a ".bat" file
- Client.exe (PID: 4056)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5112)
The executable file from the user directory is run by the CMD process
- Balls.exe (PID: 7472)
Starts CMD.EXE for commands execution
- Balls.exe (PID: 7472)
- Client.exe (PID: 4056)
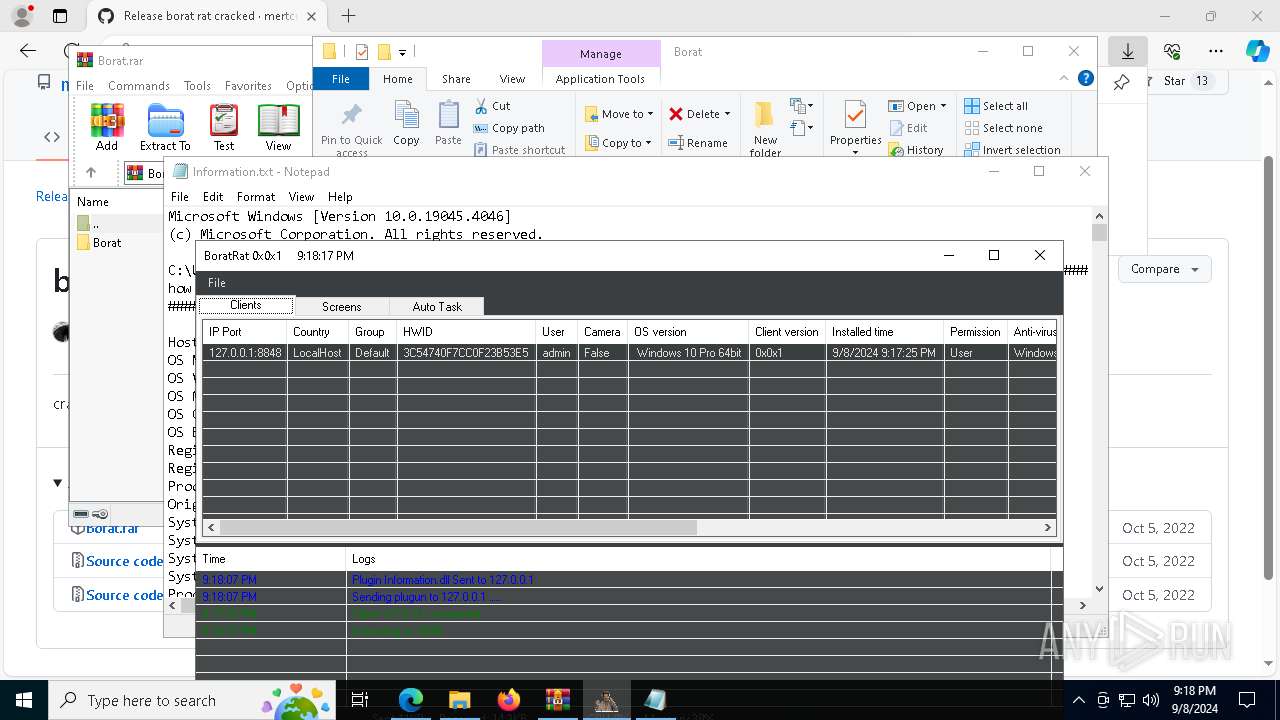
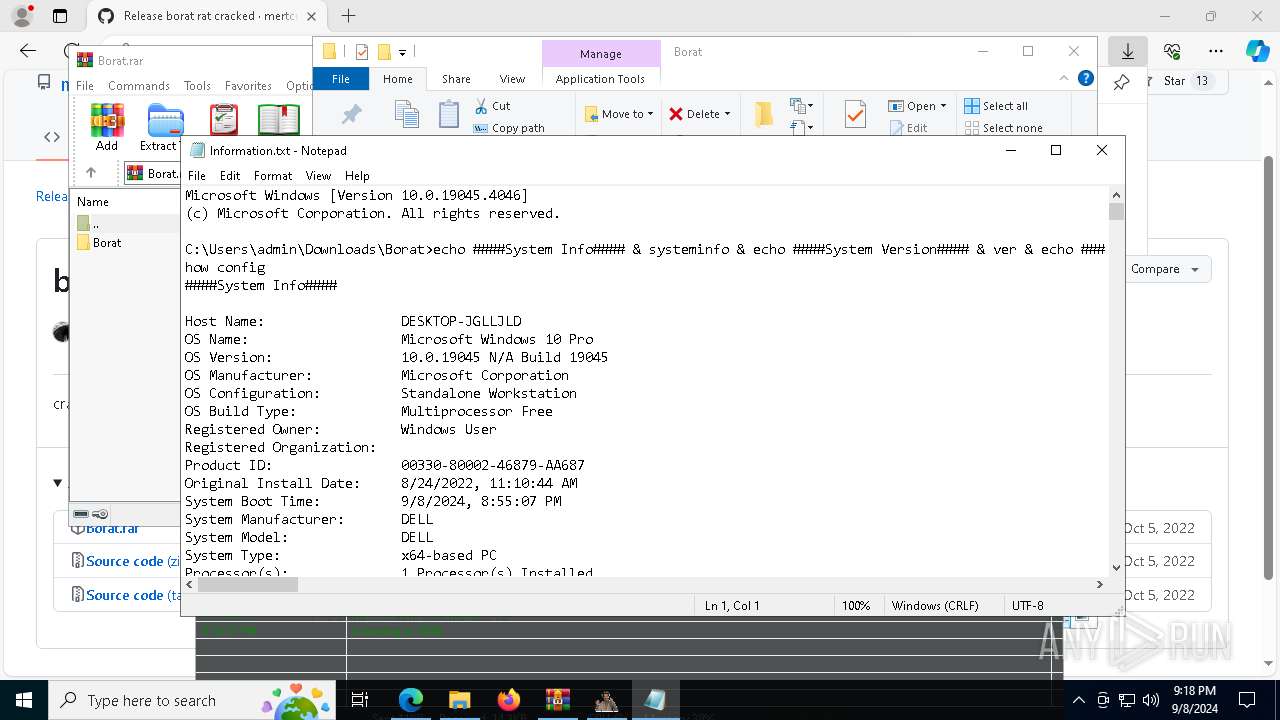
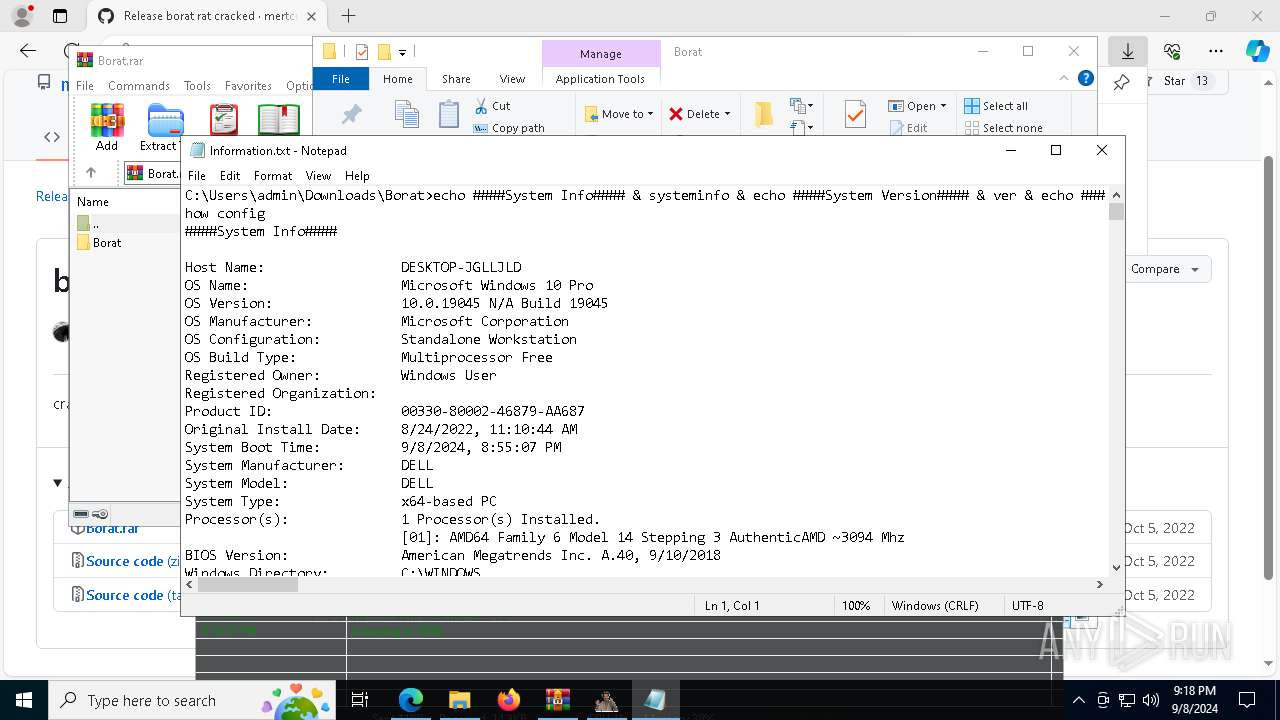
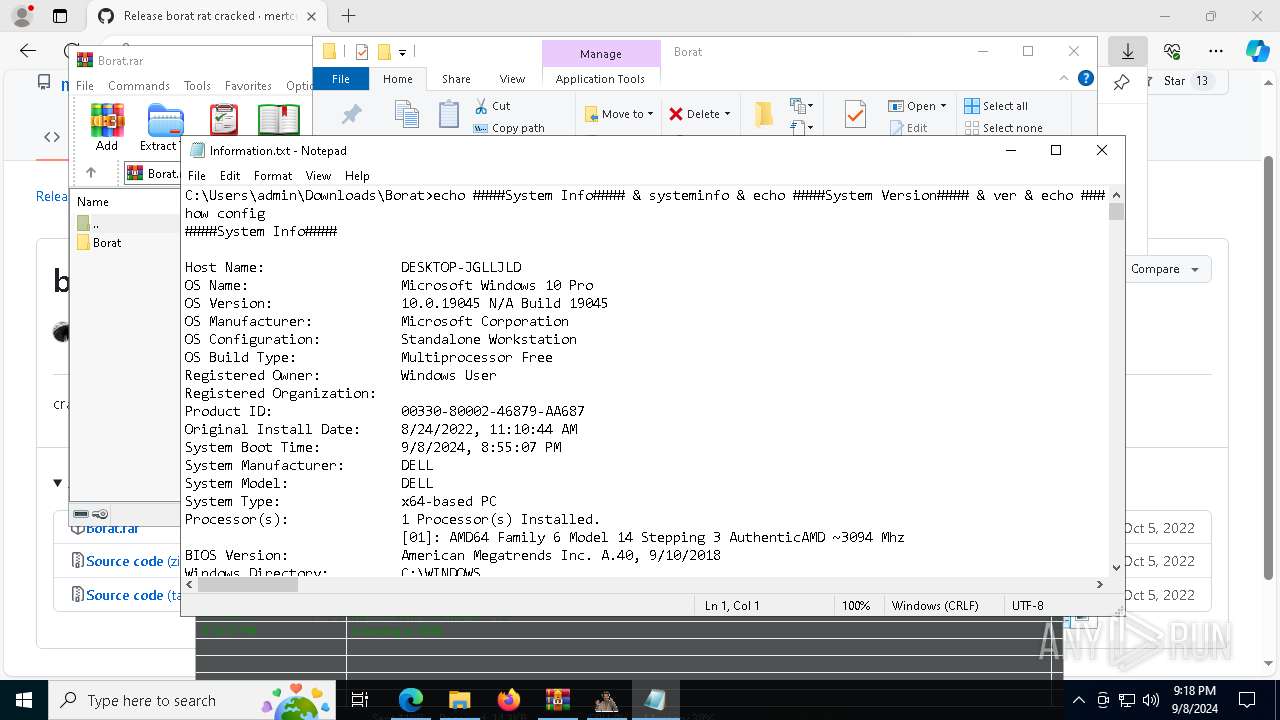
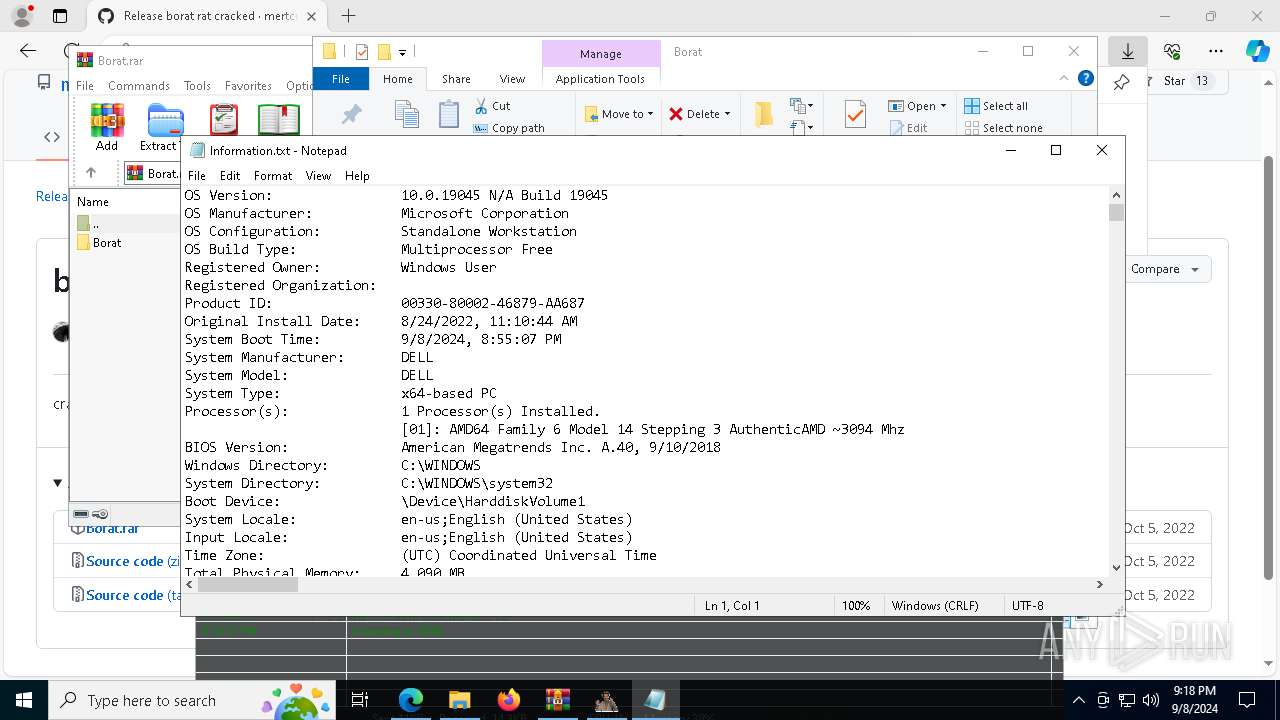
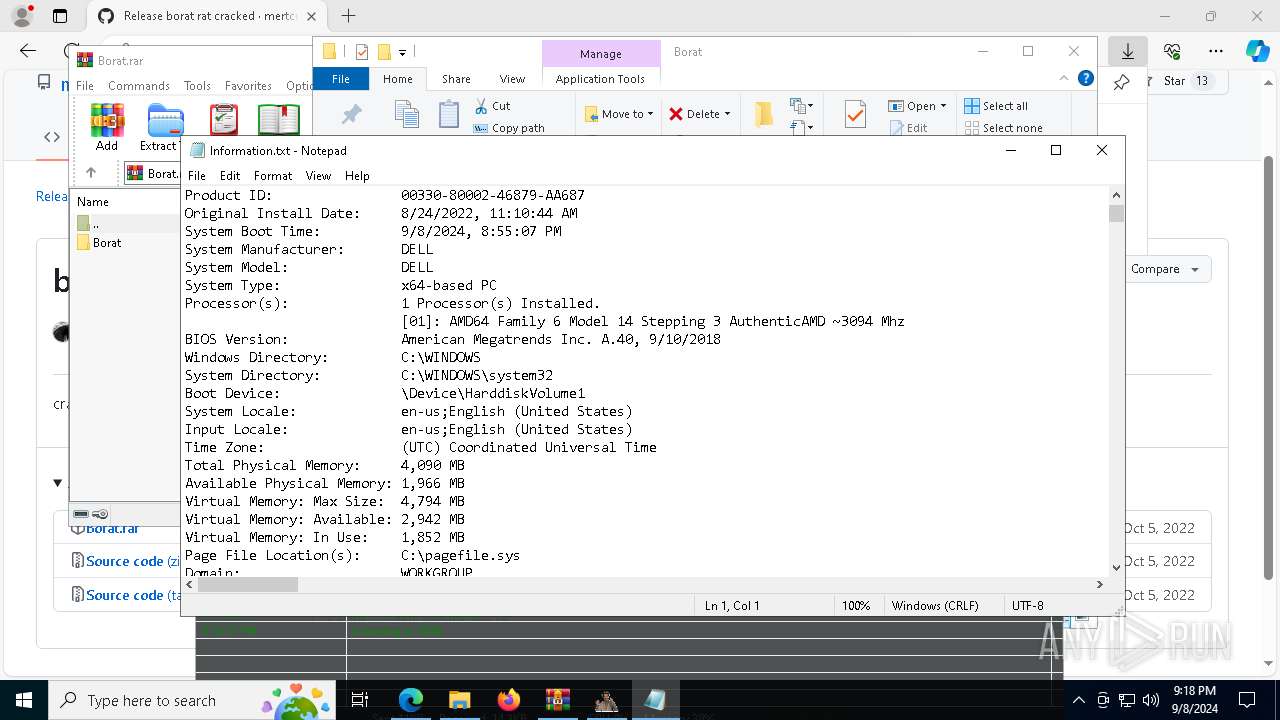
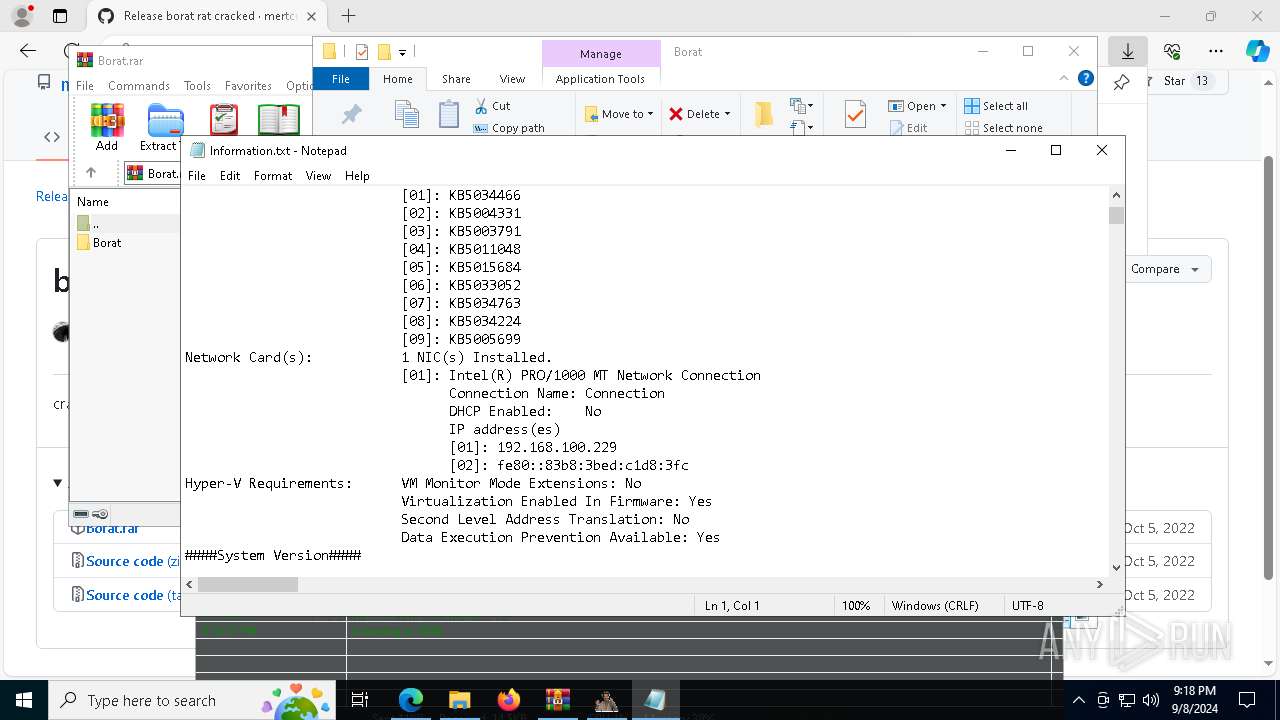
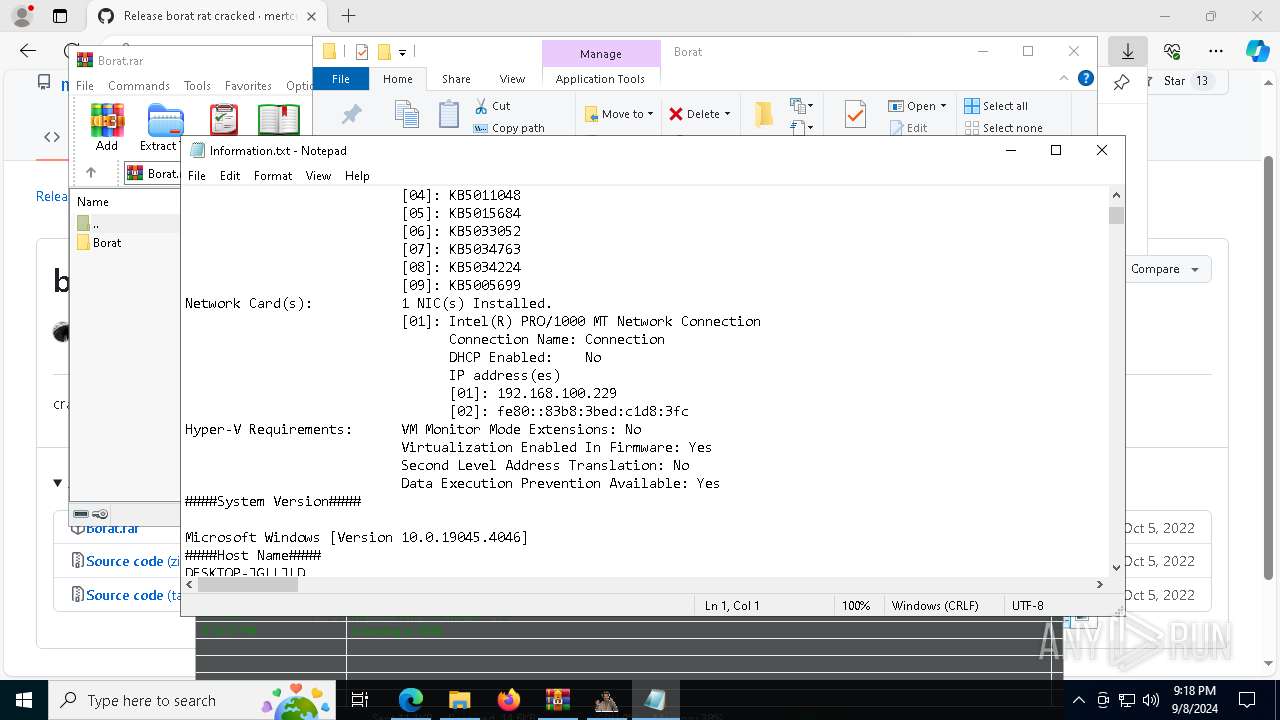
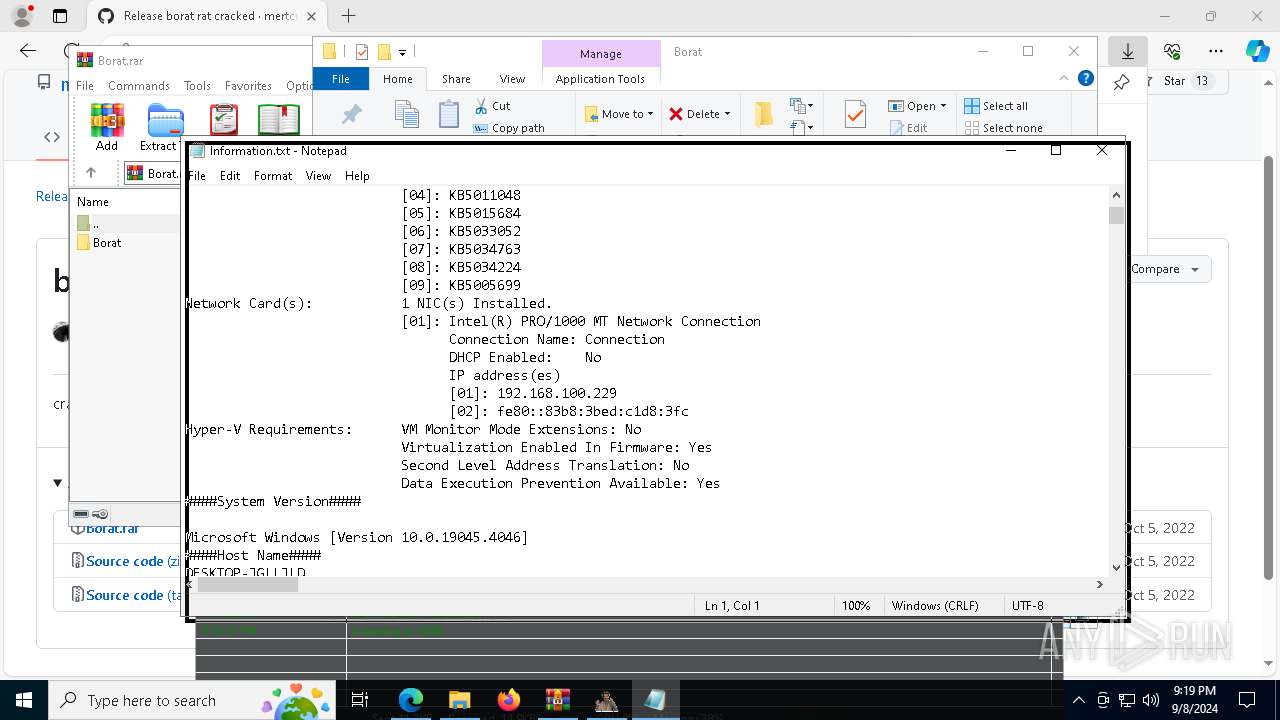
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 5588)
Uses WMIC.EXE to obtain local storage devices information
- cmd.exe (PID: 5588)
Uses QUSER.EXE to read information about current user sessions
- query.exe (PID: 4284)
Uses WMIC.EXE to obtain commands that are run when users log in
- cmd.exe (PID: 5588)
Get information on the list of running processes
- cmd.exe (PID: 5588)
Process uses ARP to discover network configuration
- cmd.exe (PID: 5588)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 5588)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 5588)
Starts SC.EXE for service management
- cmd.exe (PID: 5588)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 5588)
Reads the date of Windows installation
- BoratRat.exe (PID: 2136)
- Balls.exe (PID: 7472)
- StartMenuExperienceHost.exe (PID: 4080)
- SearchApp.exe (PID: 5980)
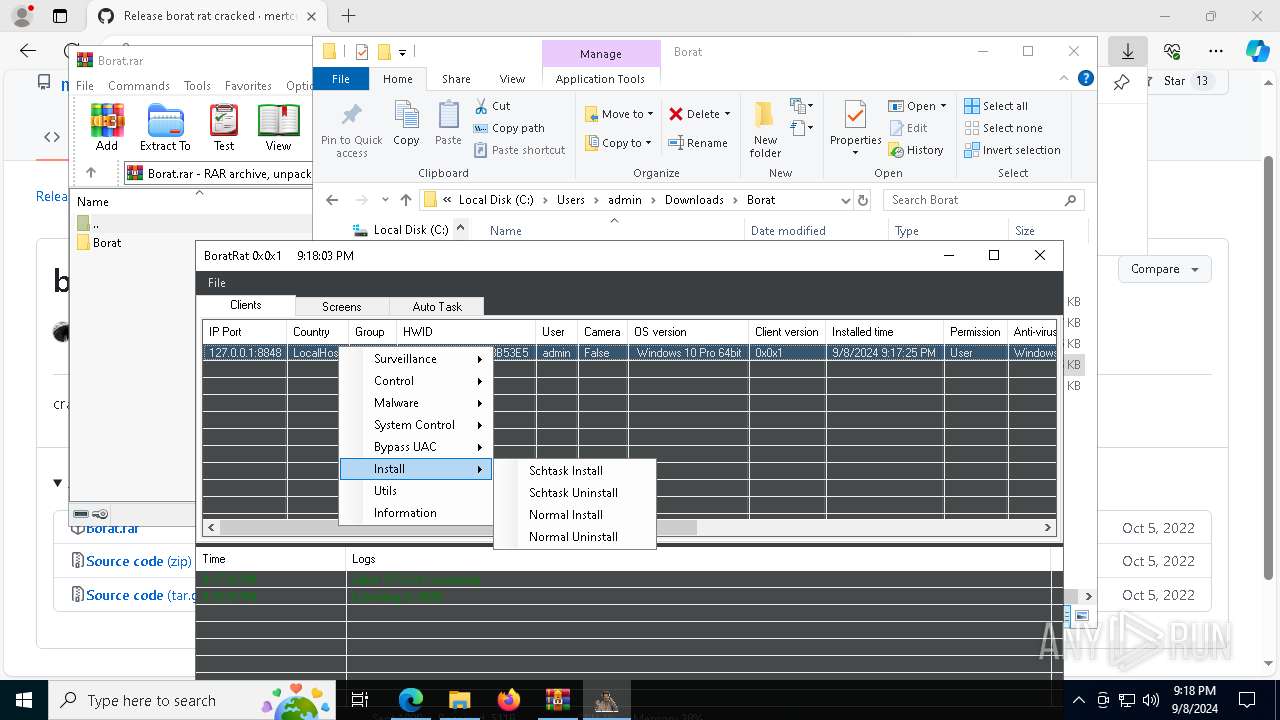
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 6772)
The system shut down or reboot
- cmd.exe (PID: 6276)
INFO
Checks supported languages
- identity_helper.exe (PID: 3908)
- BoratRat.exe (PID: 2136)
- Client.exe (PID: 4056)
- Balls.exe (PID: 7472)
- PLUGScheduler.exe (PID: 6772)
- StartMenuExperienceHost.exe (PID: 4080)
- GameBar.exe (PID: 6000)
- SearchApp.exe (PID: 5980)
- Balls.exe (PID: 6024)
- BoratRat.exe (PID: 1664)
Reads Environment values
- identity_helper.exe (PID: 3908)
- Balls.exe (PID: 7472)
- BoratRat.exe (PID: 2136)
- BoratRat.exe (PID: 1664)
- Balls.exe (PID: 6024)
- SearchApp.exe (PID: 5980)
The process uses the downloaded file
- msedge.exe (PID: 6876)
- msedge.exe (PID: 4004)
- WinRAR.exe (PID: 1020)
- msedge.exe (PID: 5064)
- msedge.exe (PID: 5720)
- BoratRat.exe (PID: 2136)
- explorer.exe (PID: 6984)
- Balls.exe (PID: 7472)
- BoratRat.exe (PID: 1664)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5720)
- explorer.exe (PID: 6984)
Reads the computer name
- identity_helper.exe (PID: 3908)
- BoratRat.exe (PID: 2136)
- Client.exe (PID: 4056)
- Balls.exe (PID: 7472)
- PLUGScheduler.exe (PID: 6772)
- GameBar.exe (PID: 6000)
- StartMenuExperienceHost.exe (PID: 4080)
- SearchApp.exe (PID: 5980)
- Balls.exe (PID: 6024)
- BoratRat.exe (PID: 1664)
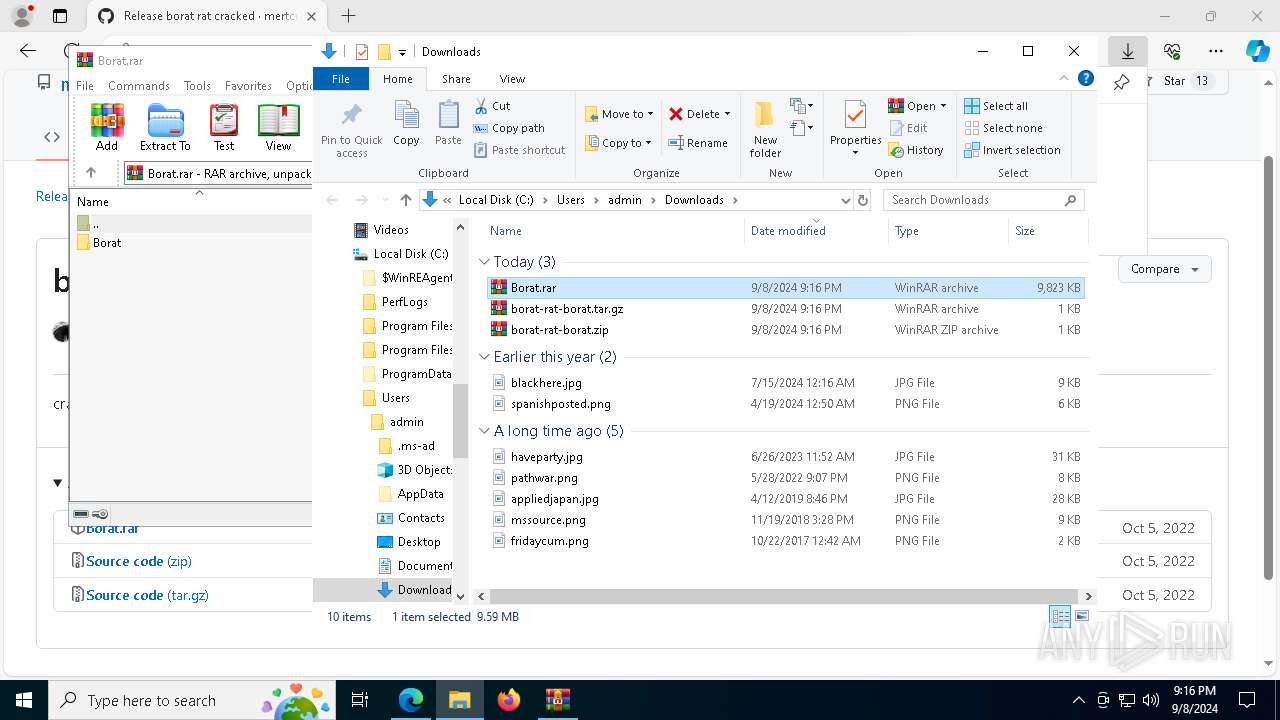
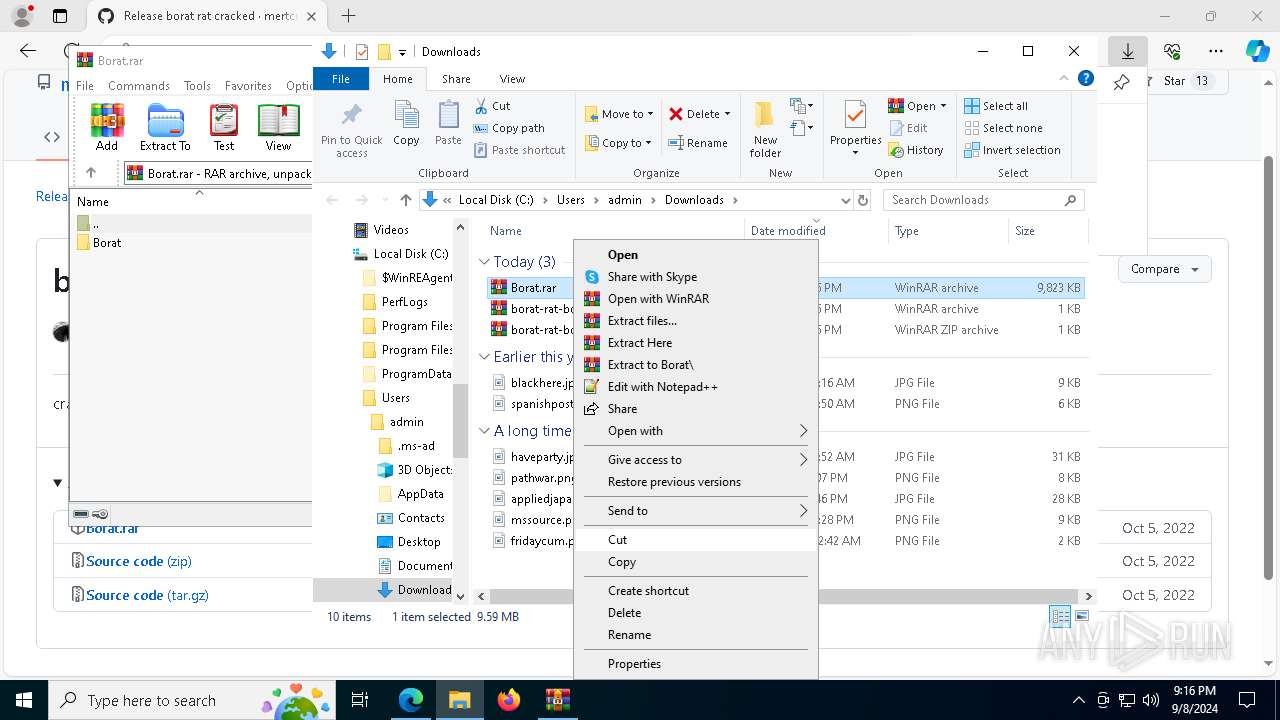
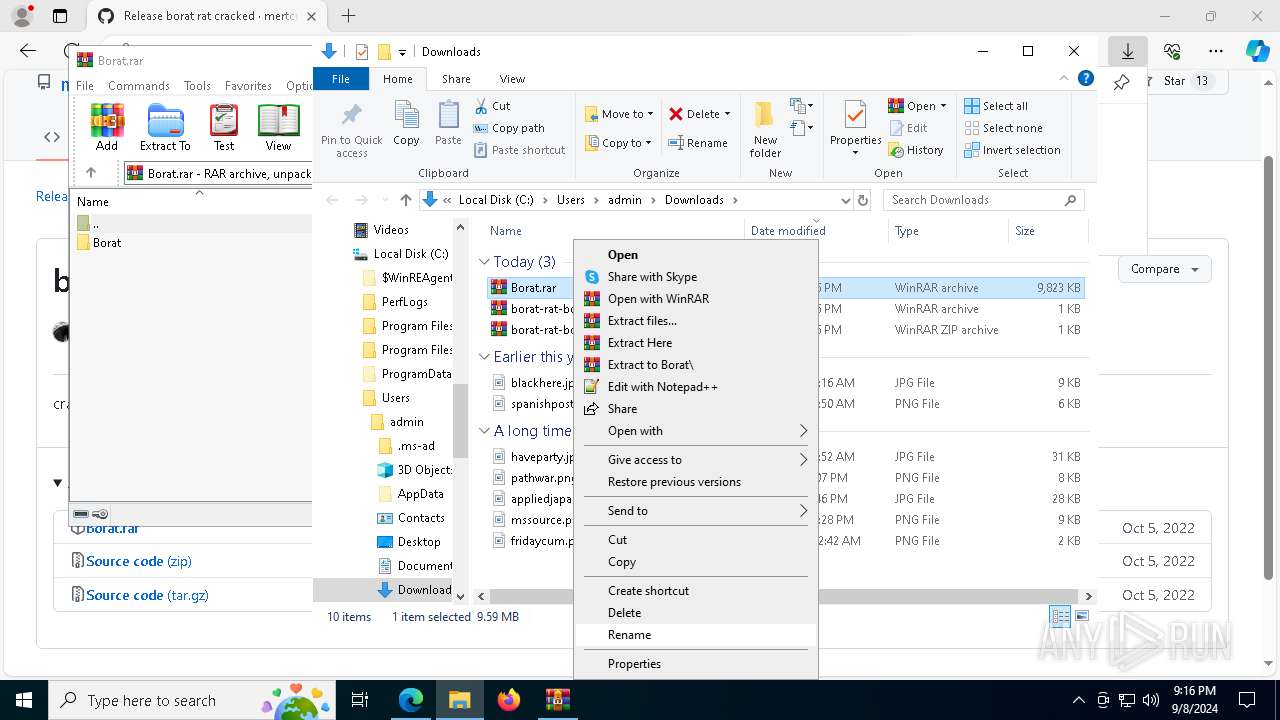
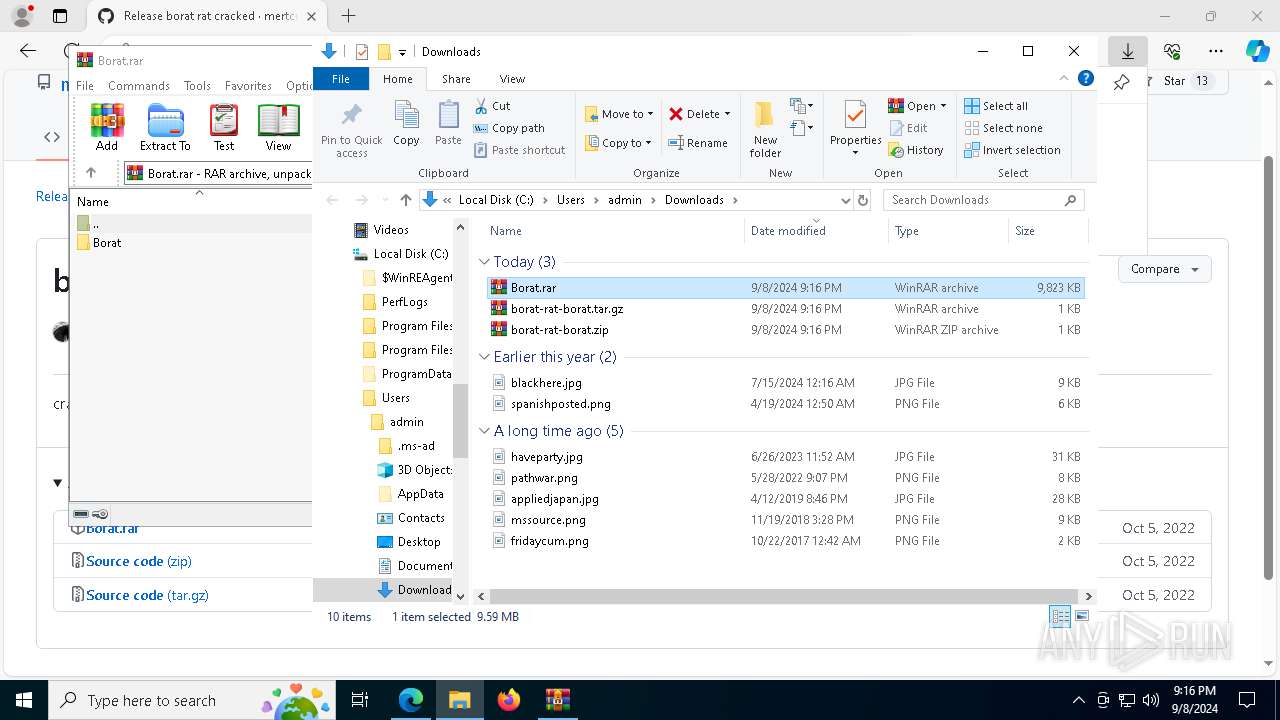
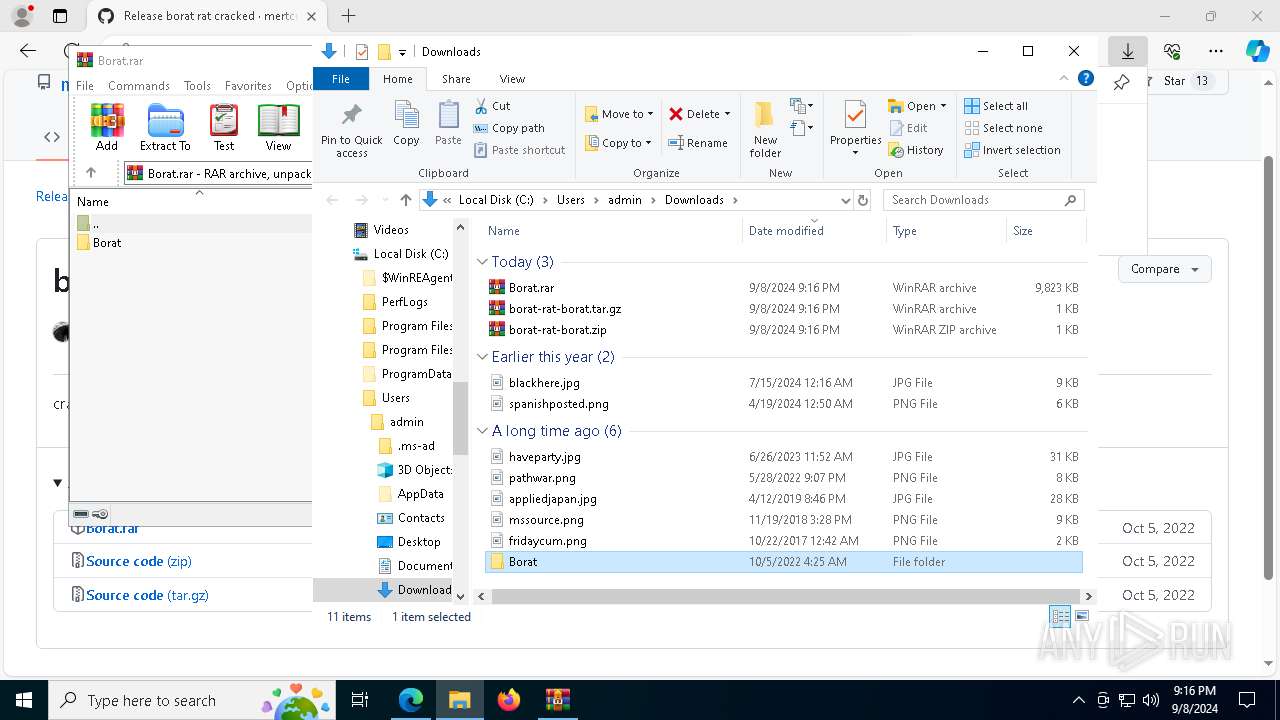
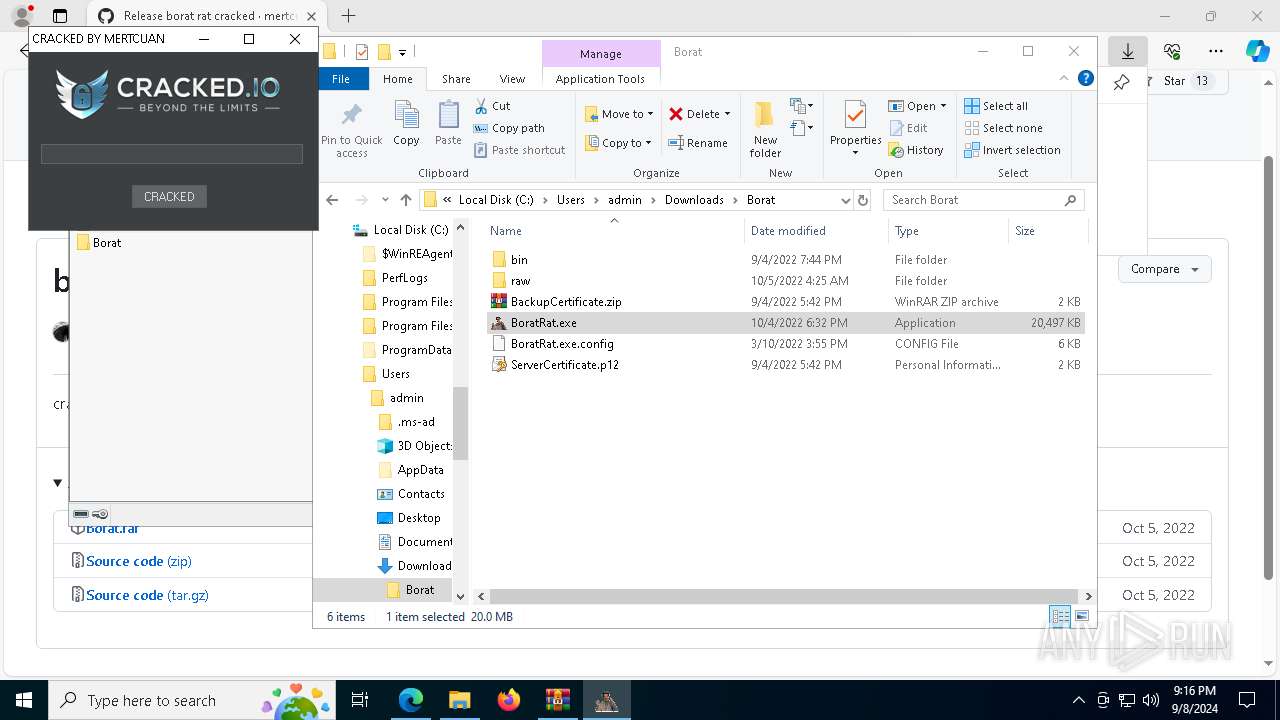
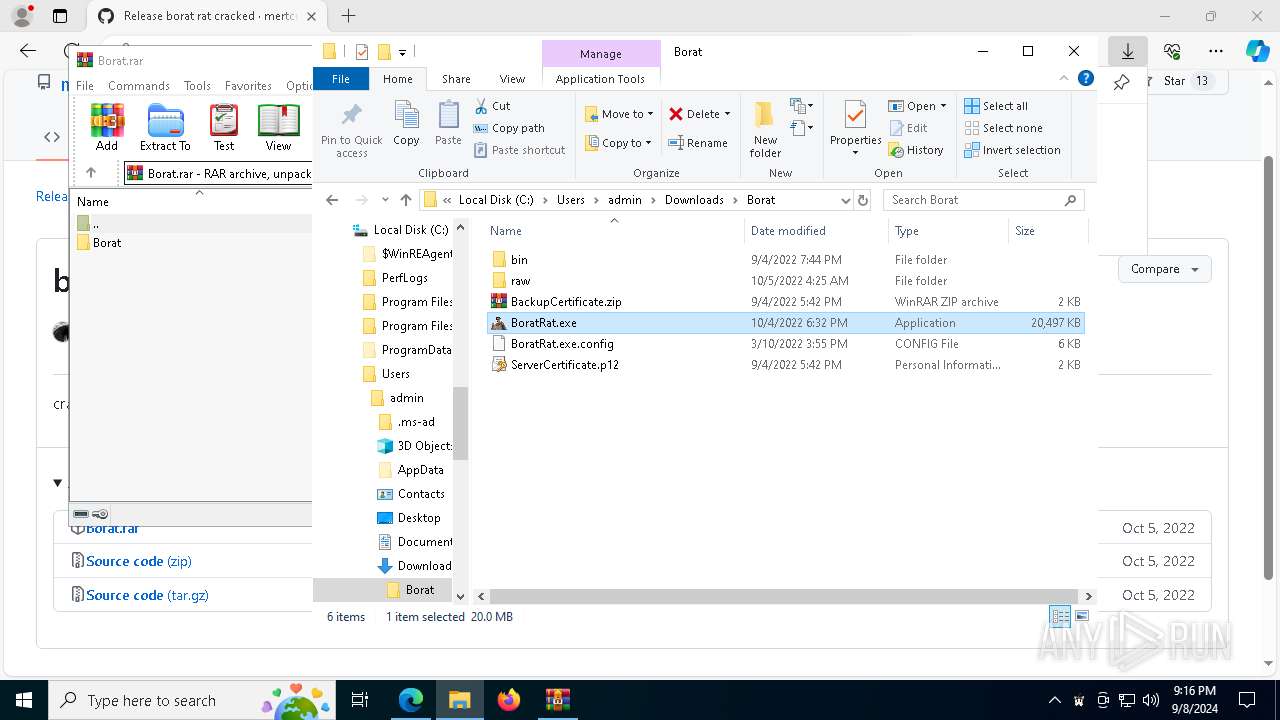
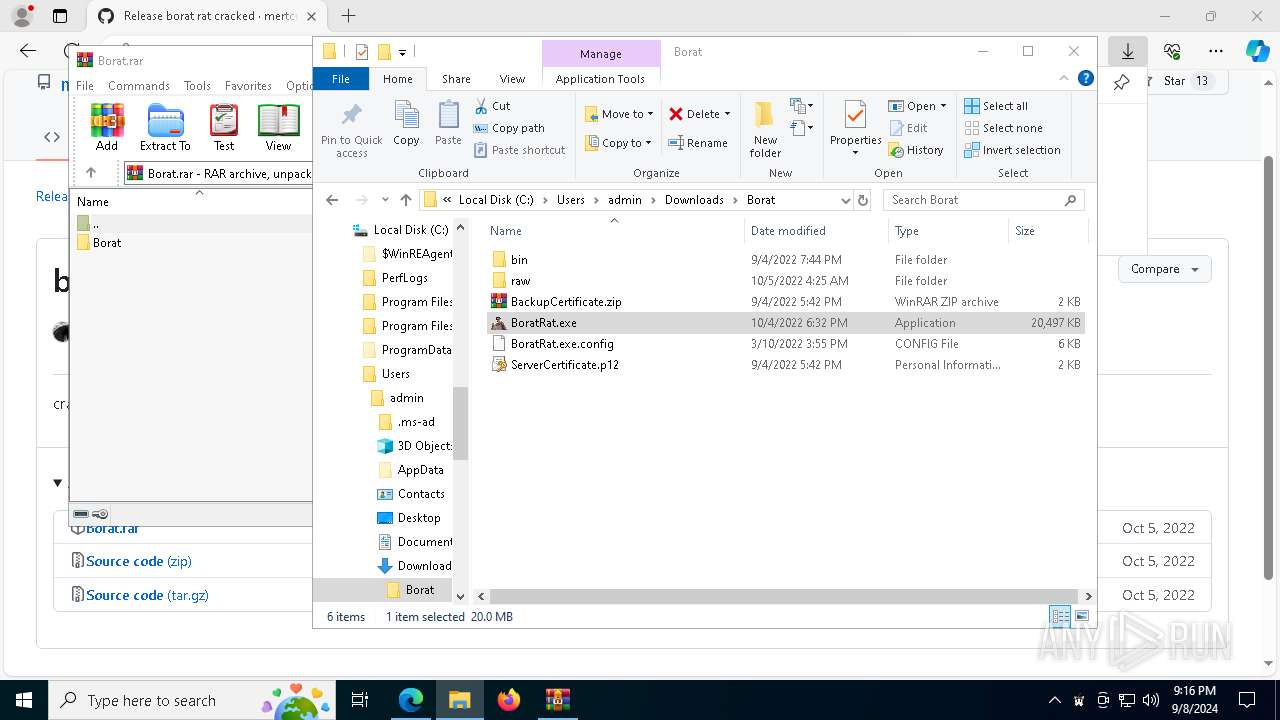
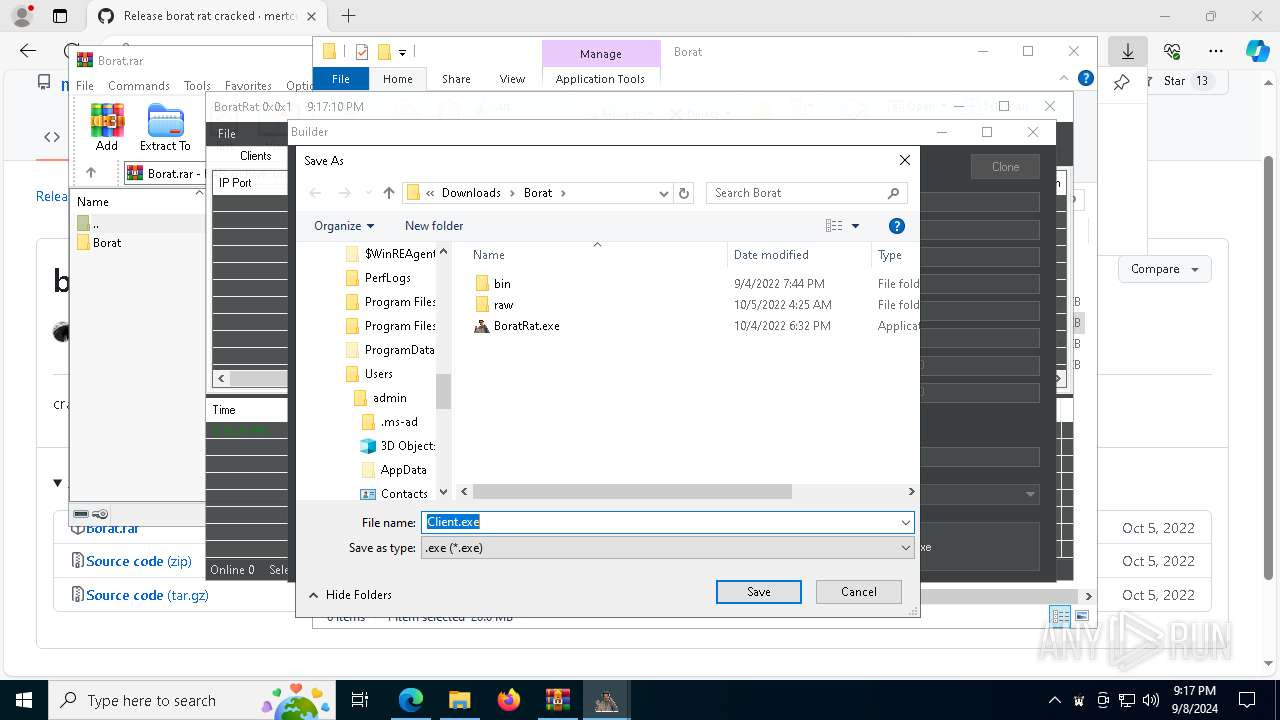
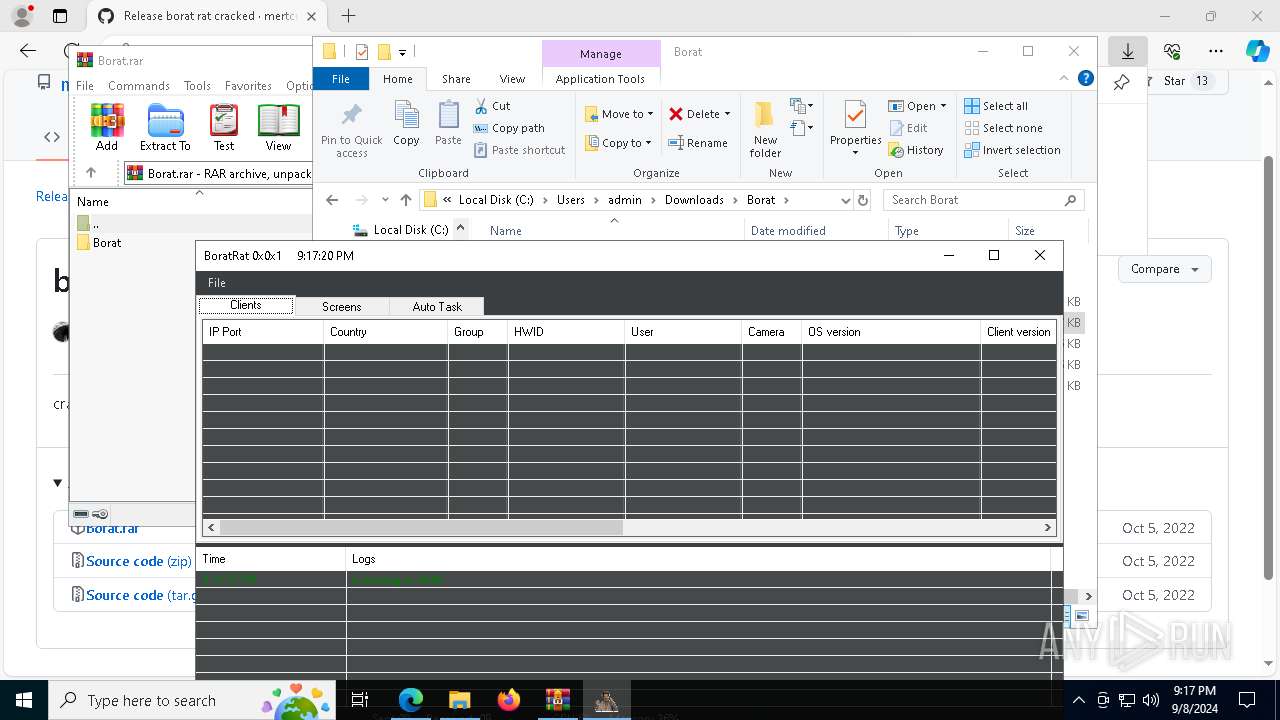
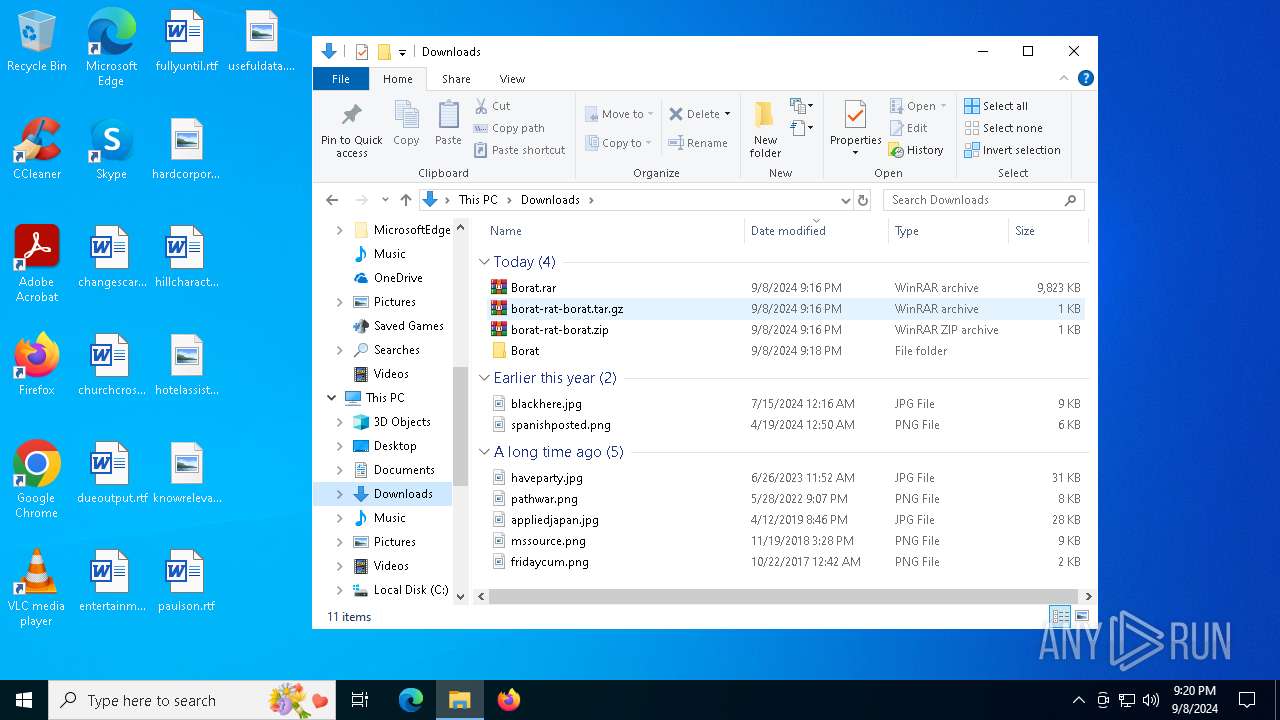
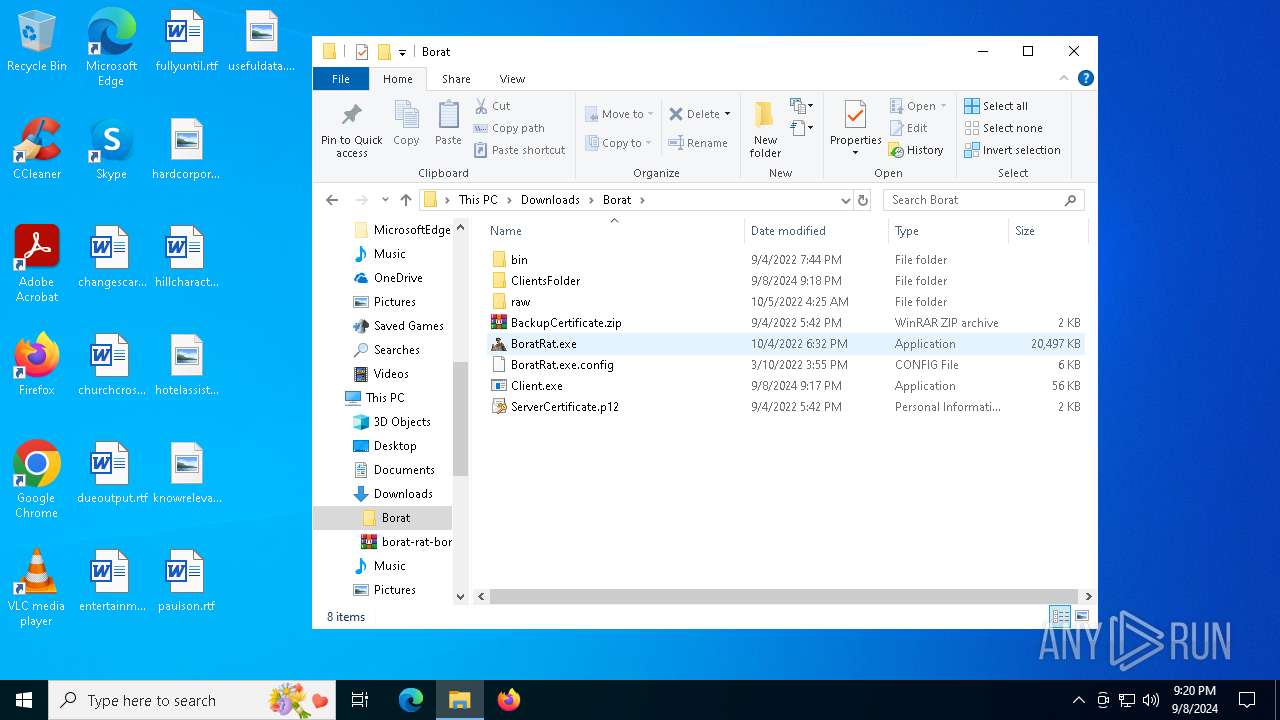
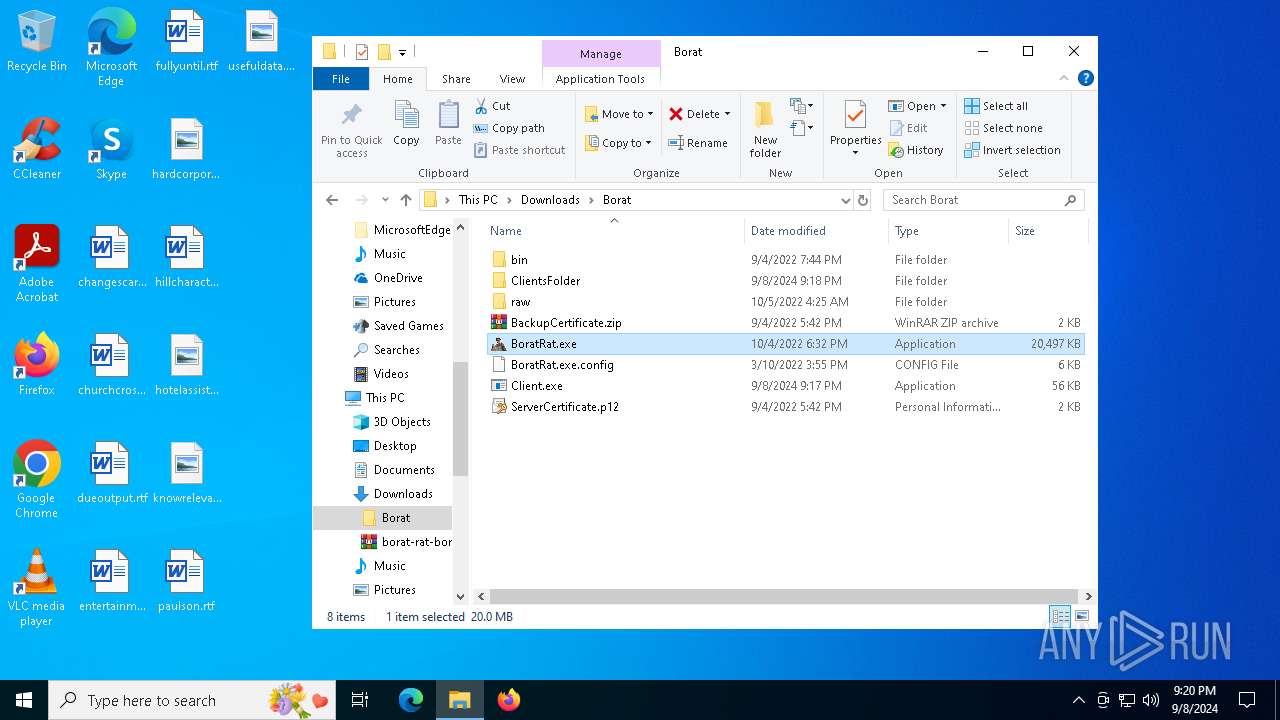
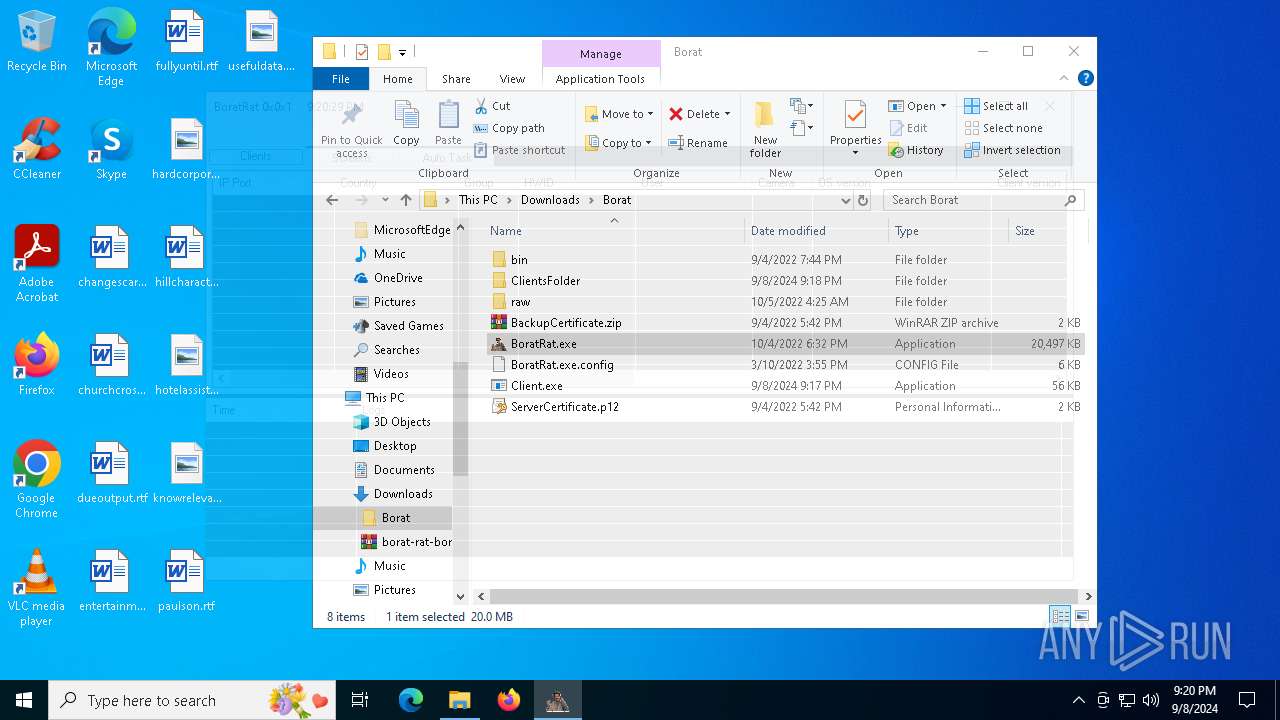
Manual execution by a user
- WinRAR.exe (PID: 1020)
- BoratRat.exe (PID: 2136)
- Client.exe (PID: 4056)
- Balls.exe (PID: 6024)
- BoratRat.exe (PID: 1664)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1020)
Reads the machine GUID from the registry
- BoratRat.exe (PID: 2136)
- Client.exe (PID: 4056)
- Balls.exe (PID: 7472)
- SearchApp.exe (PID: 5980)
- Balls.exe (PID: 6024)
- BoratRat.exe (PID: 1664)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- BoratRat.exe (PID: 2136)
Creates files or folders in the user directory
- Client.exe (PID: 4056)
- BoratRat.exe (PID: 2136)
- dllhost.exe (PID: 5244)
- dllhost.exe (PID: 1240)
- BoratRat.exe (PID: 1664)
Create files in a temporary directory
- Client.exe (PID: 4056)
Application launched itself
- msedge.exe (PID: 5720)
Reads the software policy settings
- Balls.exe (PID: 7472)
- SearchApp.exe (PID: 5980)
- Balls.exe (PID: 6024)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7488)
- WMIC.exe (PID: 4576)
- explorer.exe (PID: 6984)
- dllhost.exe (PID: 5244)
- dllhost.exe (PID: 1240)
- notepad.exe (PID: 6160)
Reads the time zone
- net1.exe (PID: 1292)
- net1.exe (PID: 4280)
Process checks computer location settings
- BoratRat.exe (PID: 2136)
- Balls.exe (PID: 7472)
- StartMenuExperienceHost.exe (PID: 4080)
- SearchApp.exe (PID: 5980)
Creates files in the program directory
- PLUGScheduler.exe (PID: 6772)
Checks proxy server information
- SearchApp.exe (PID: 5980)
Sends debugging messages
- StartMenuExperienceHost.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
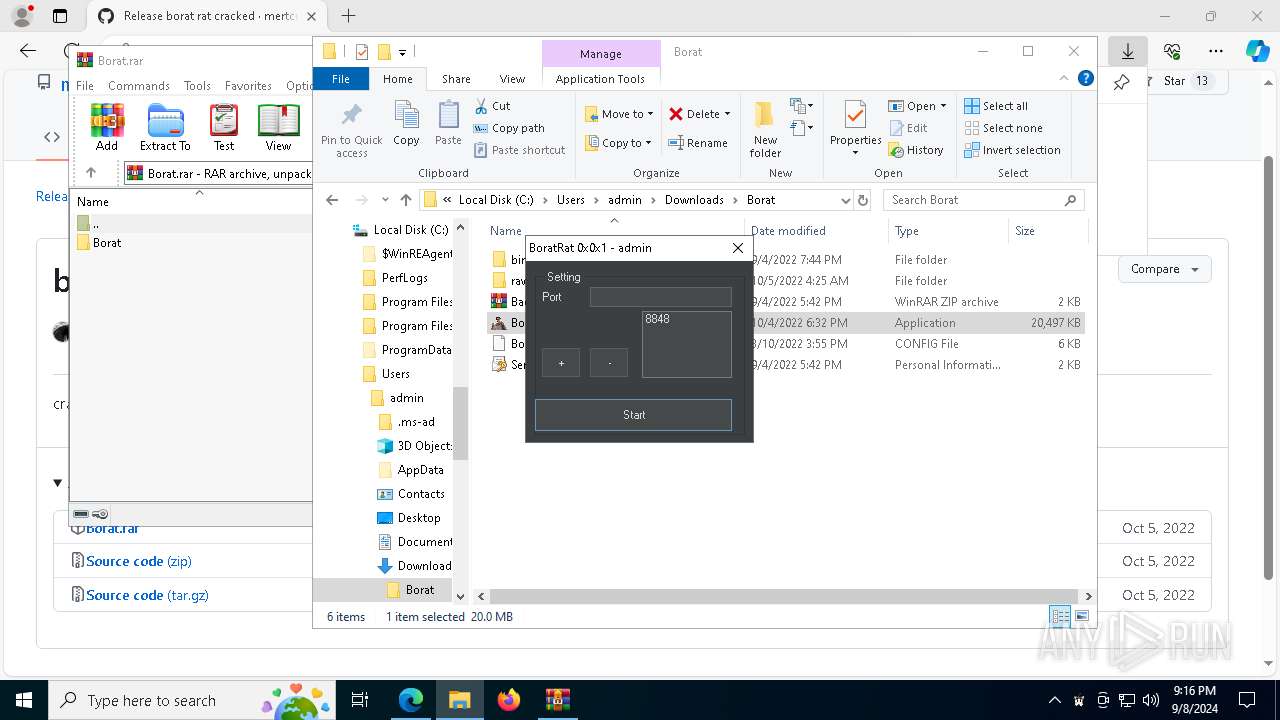
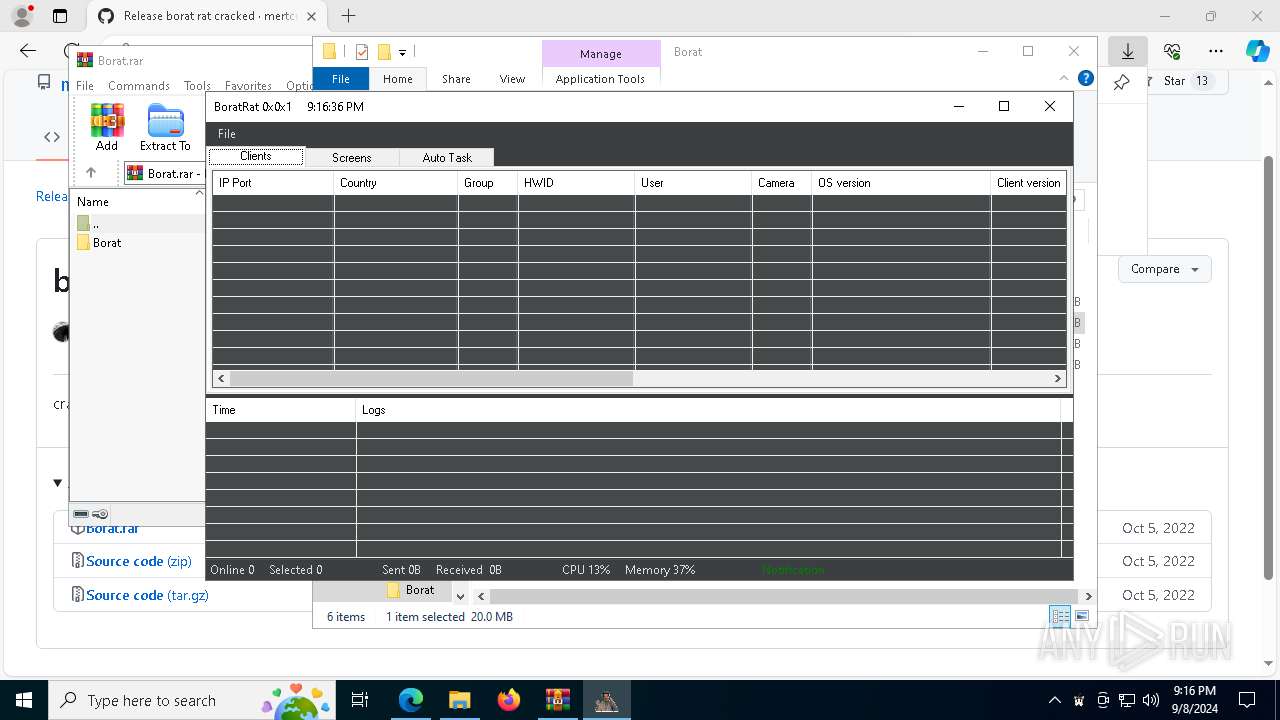
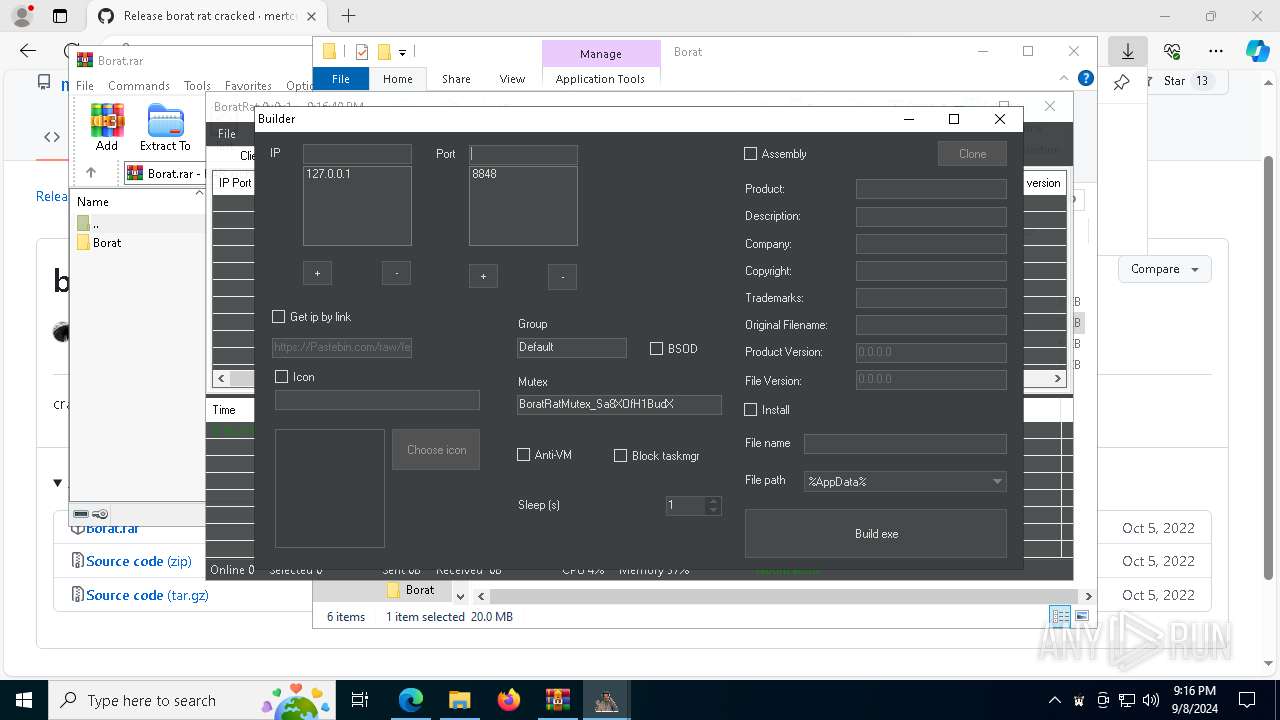
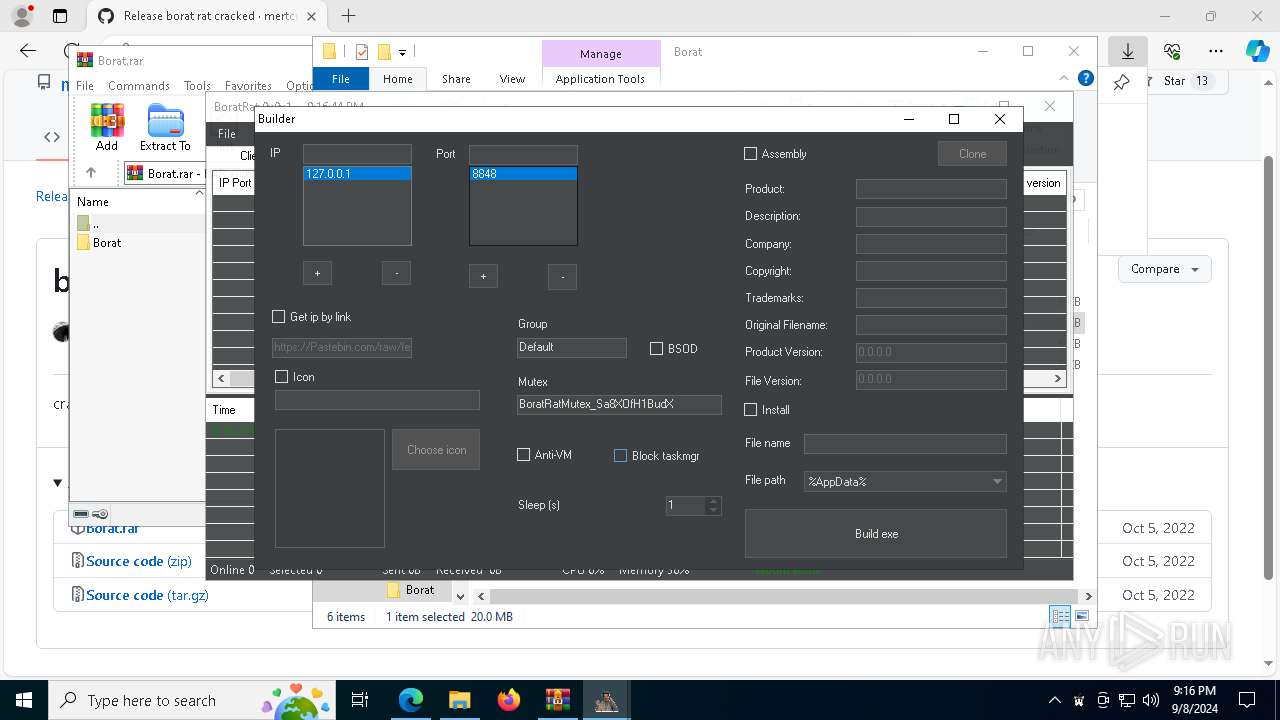
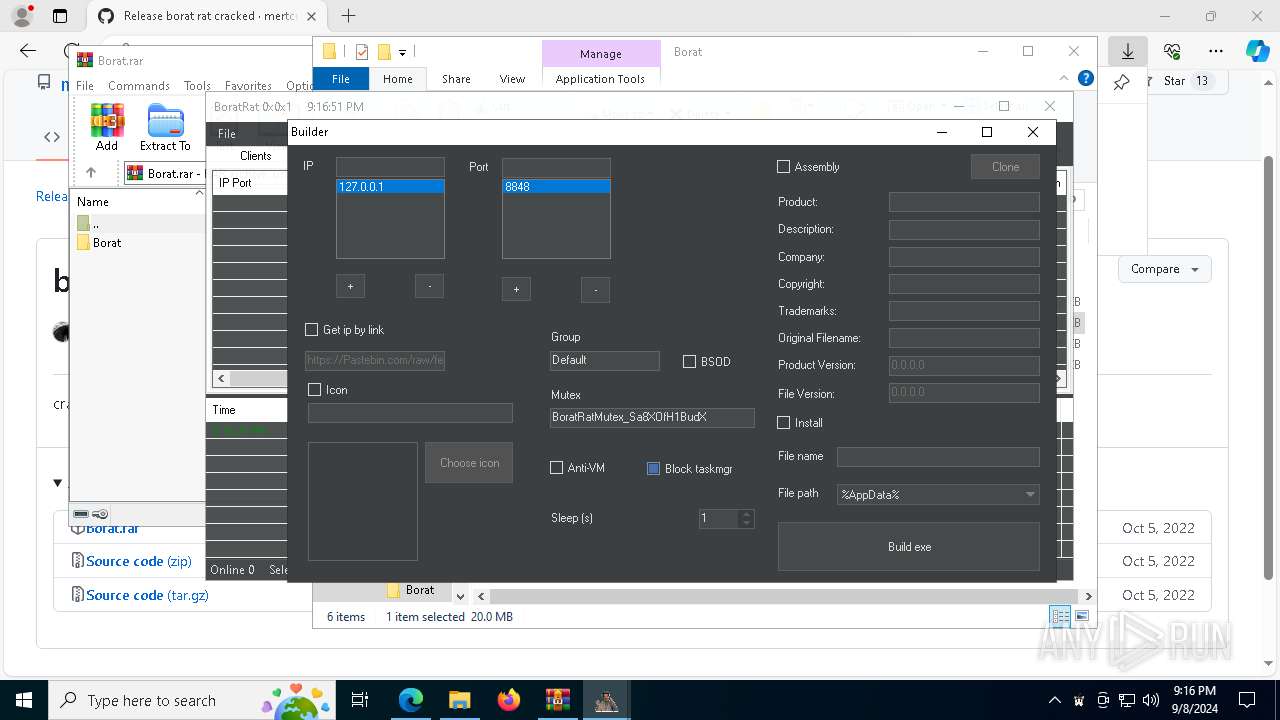
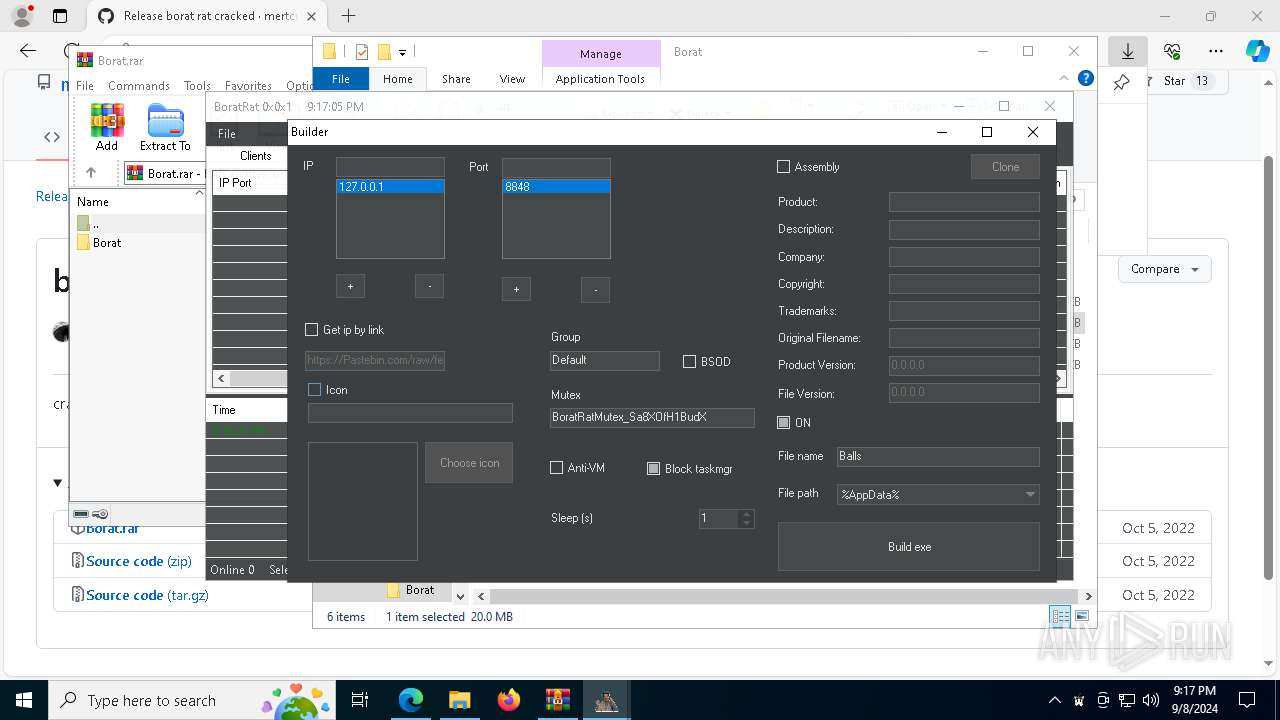
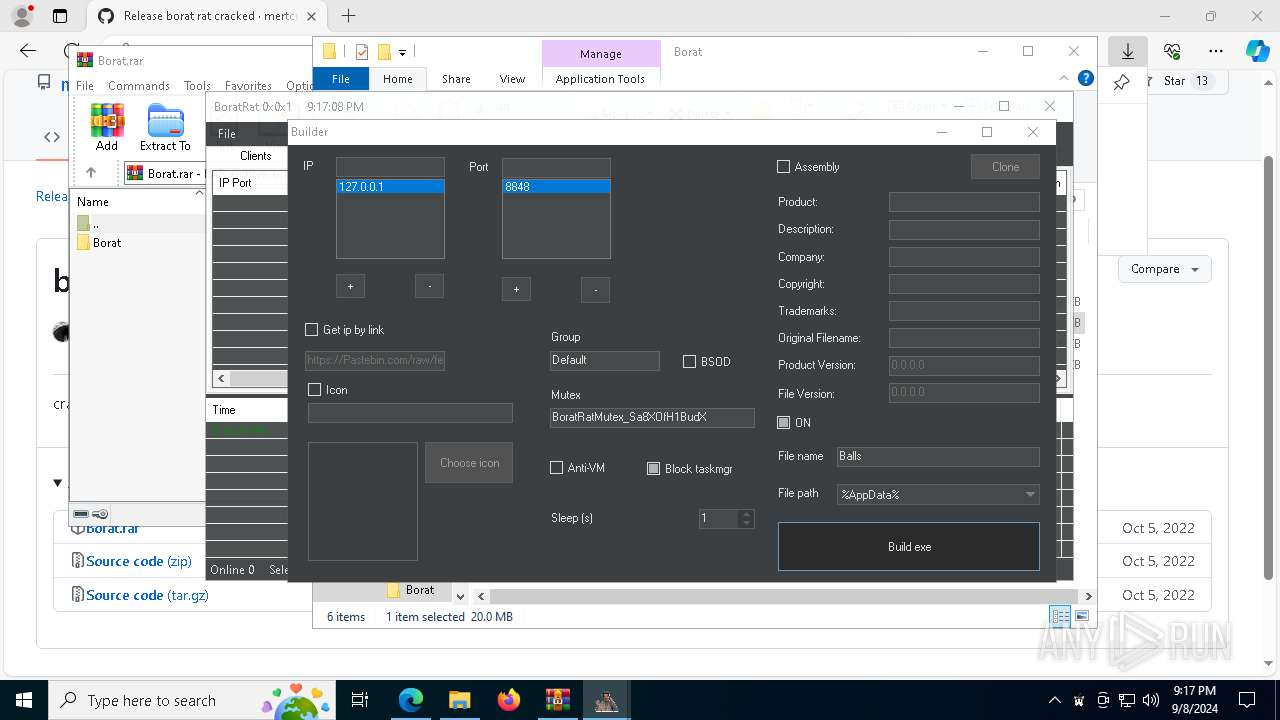
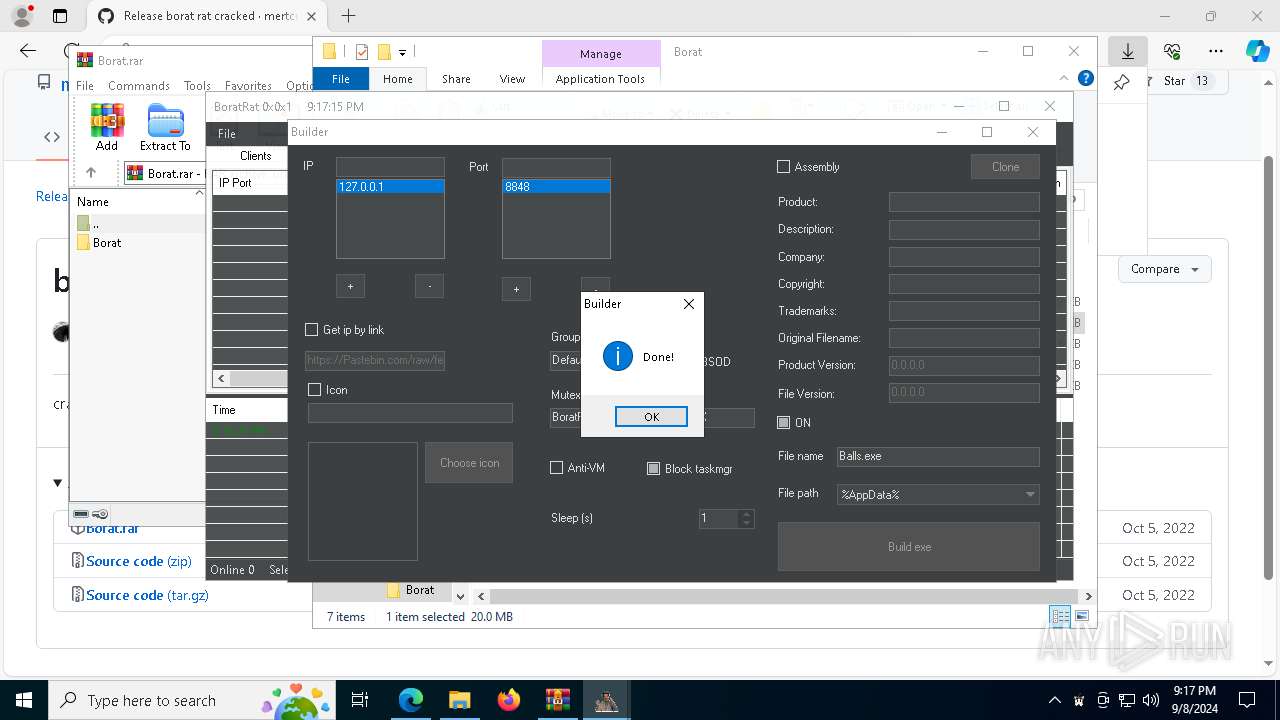
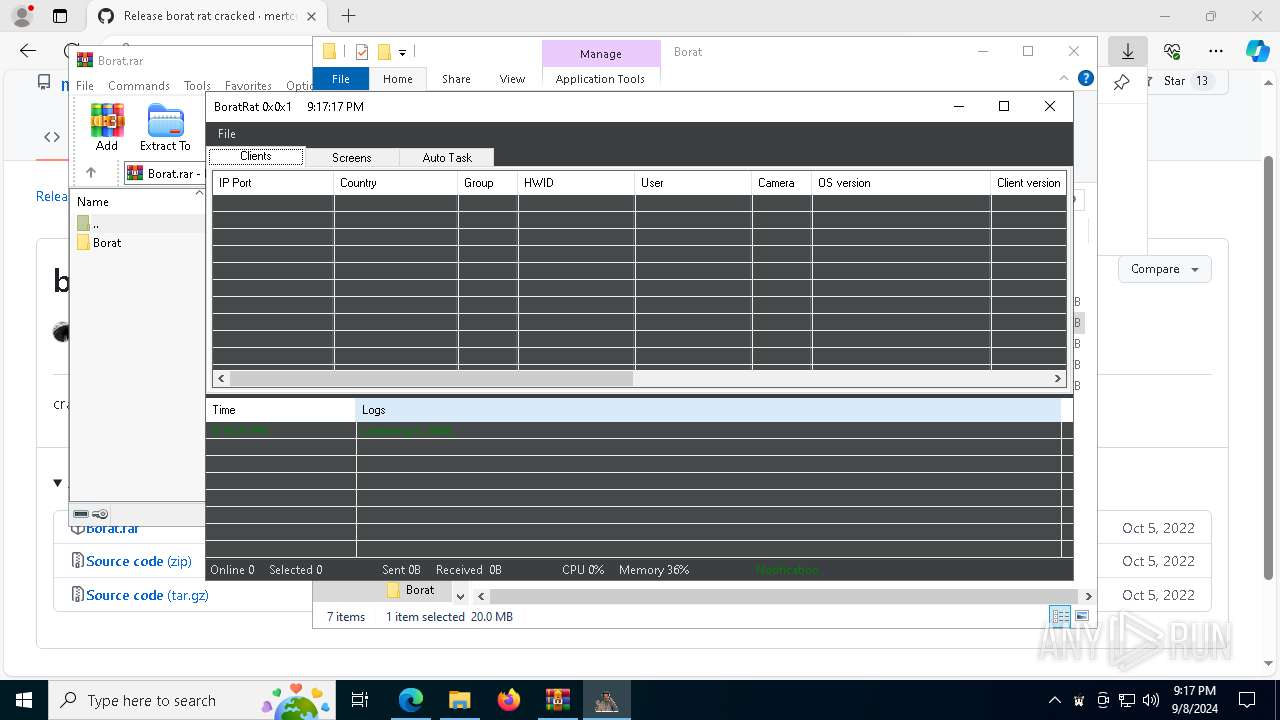
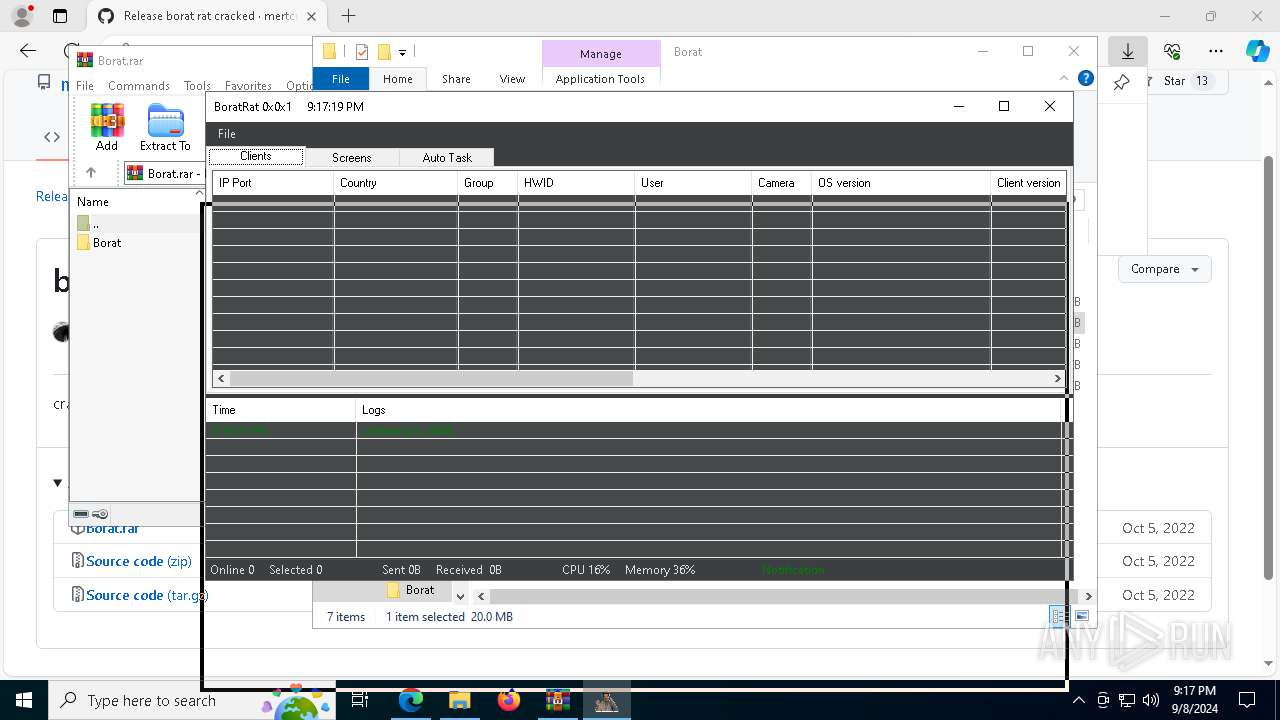
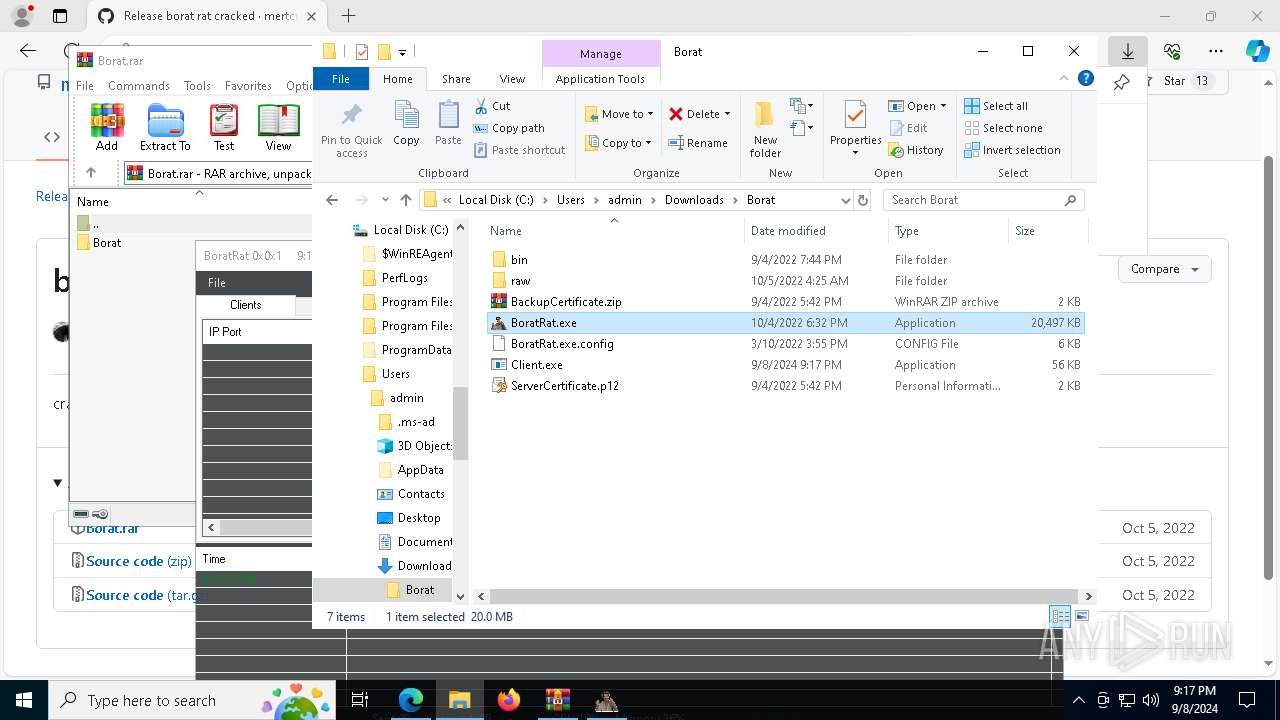
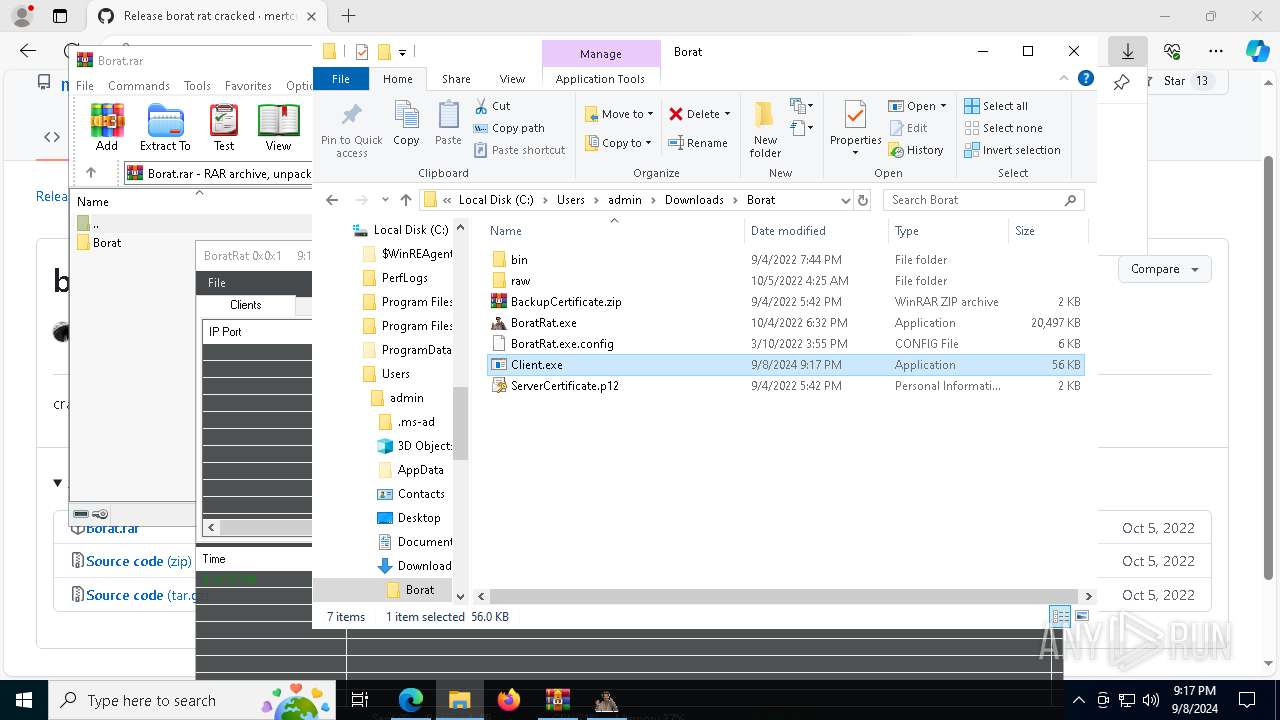
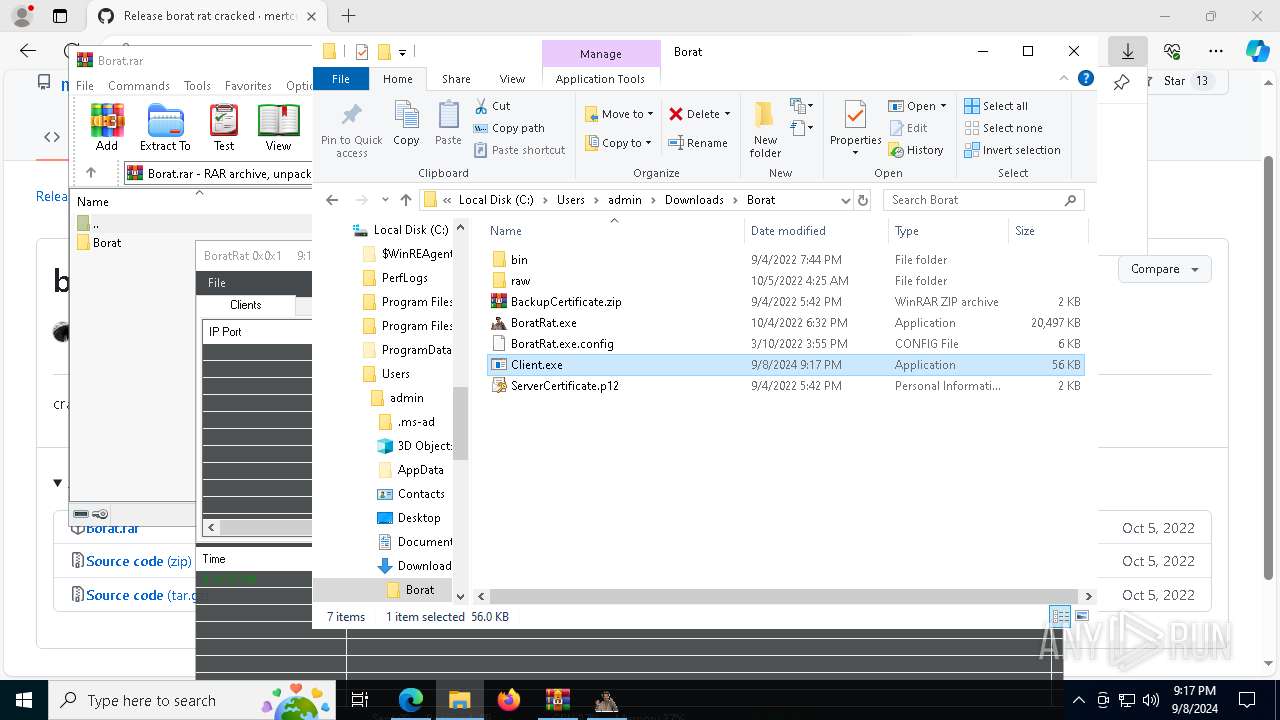
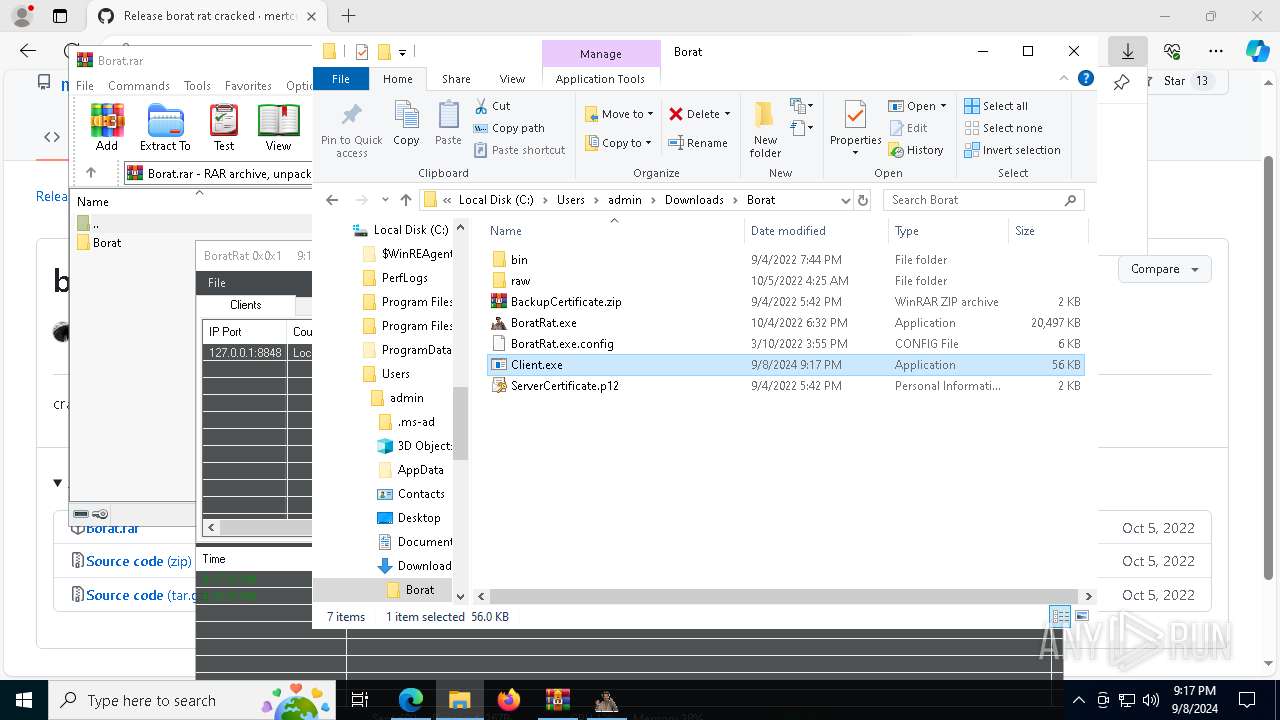
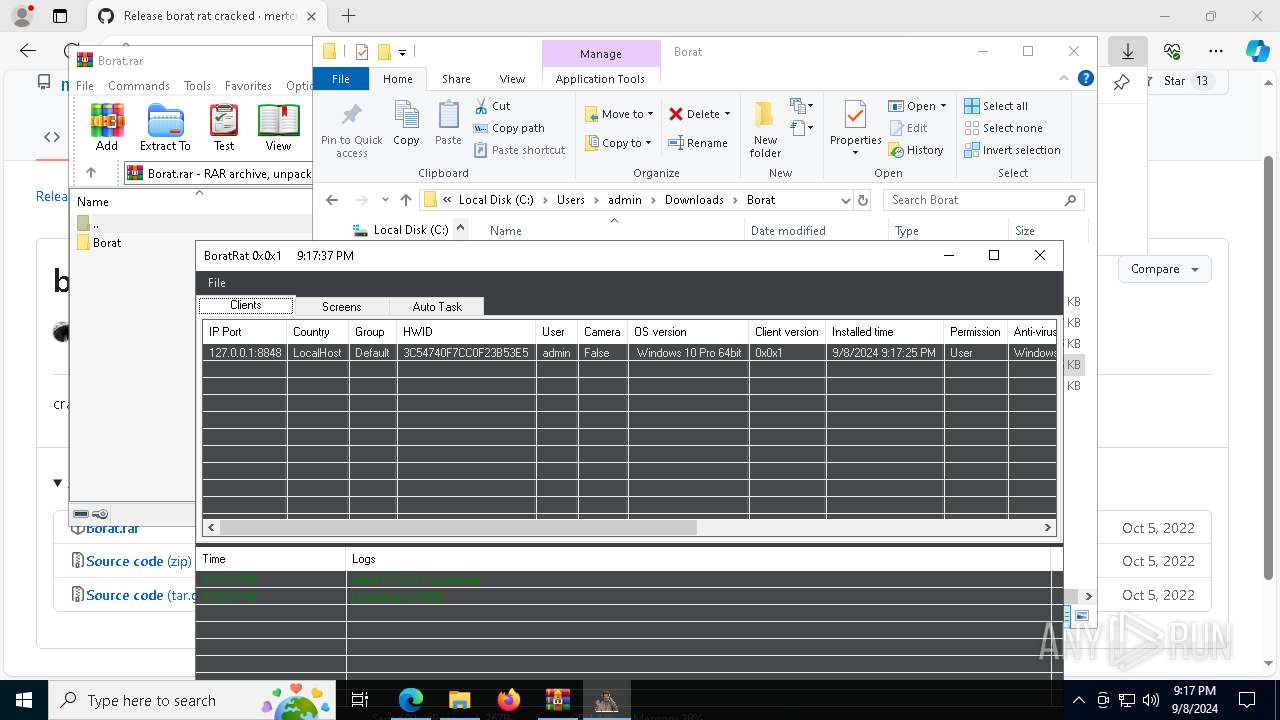
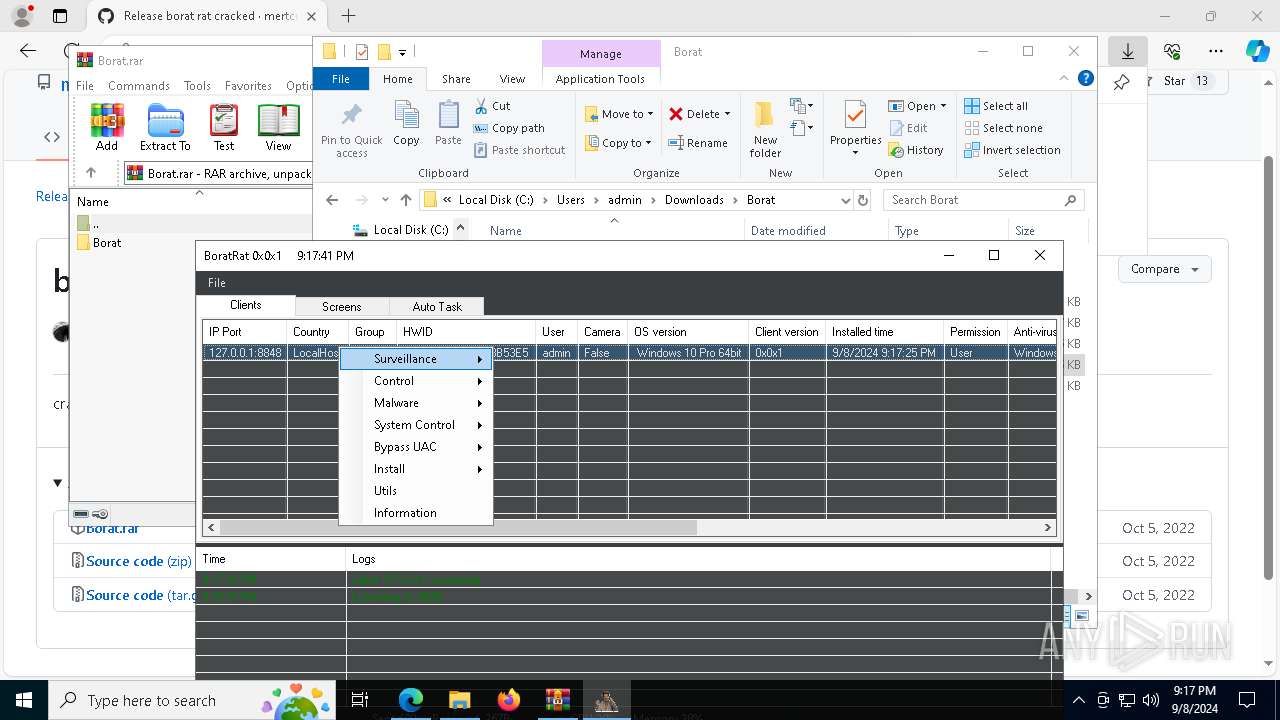
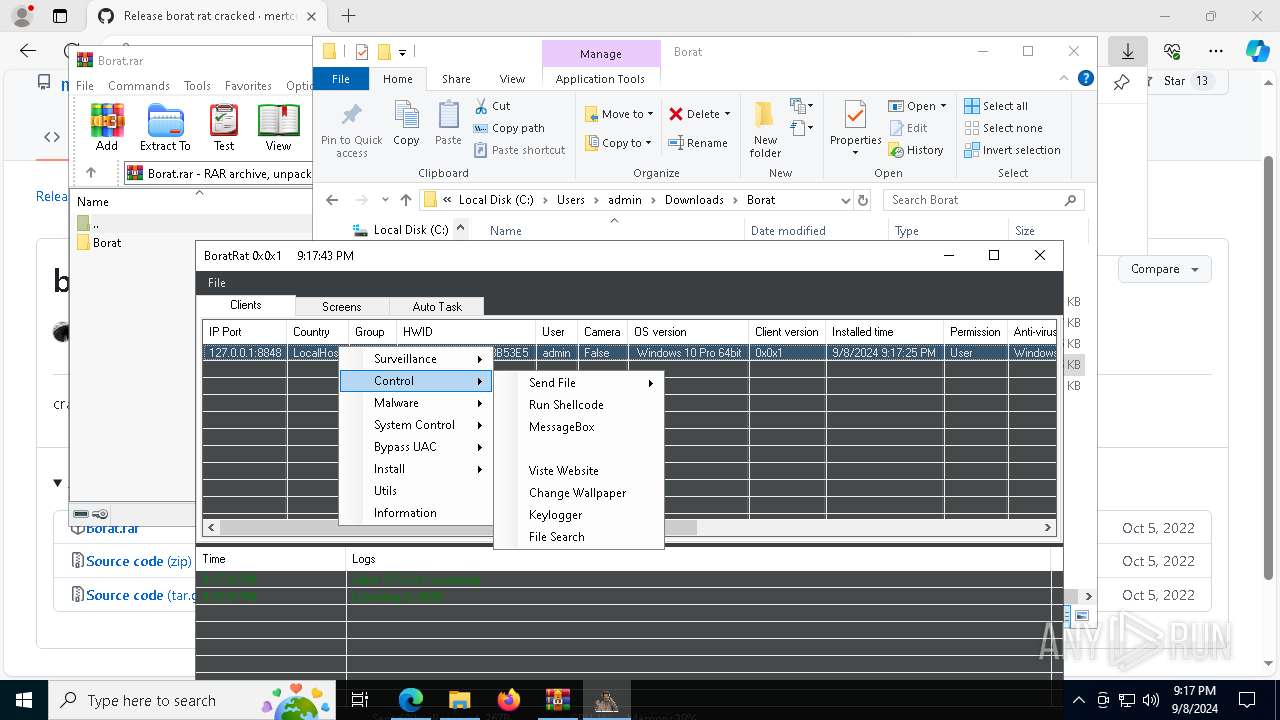
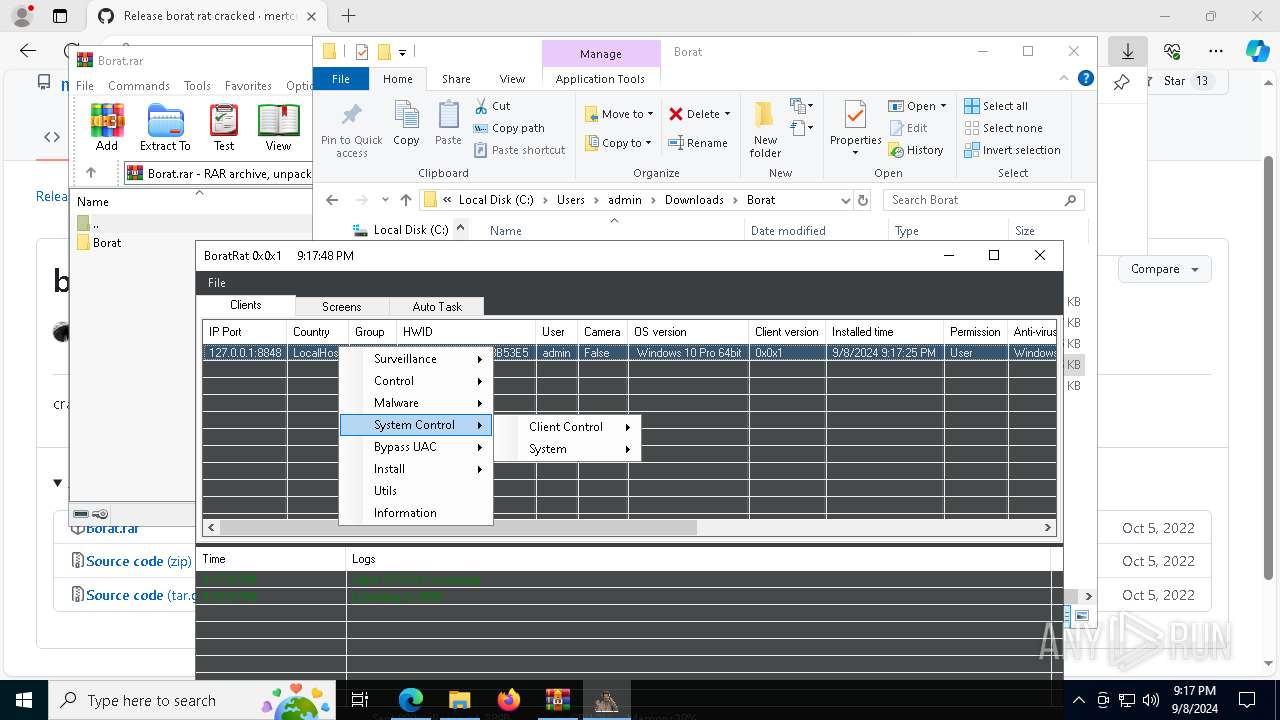
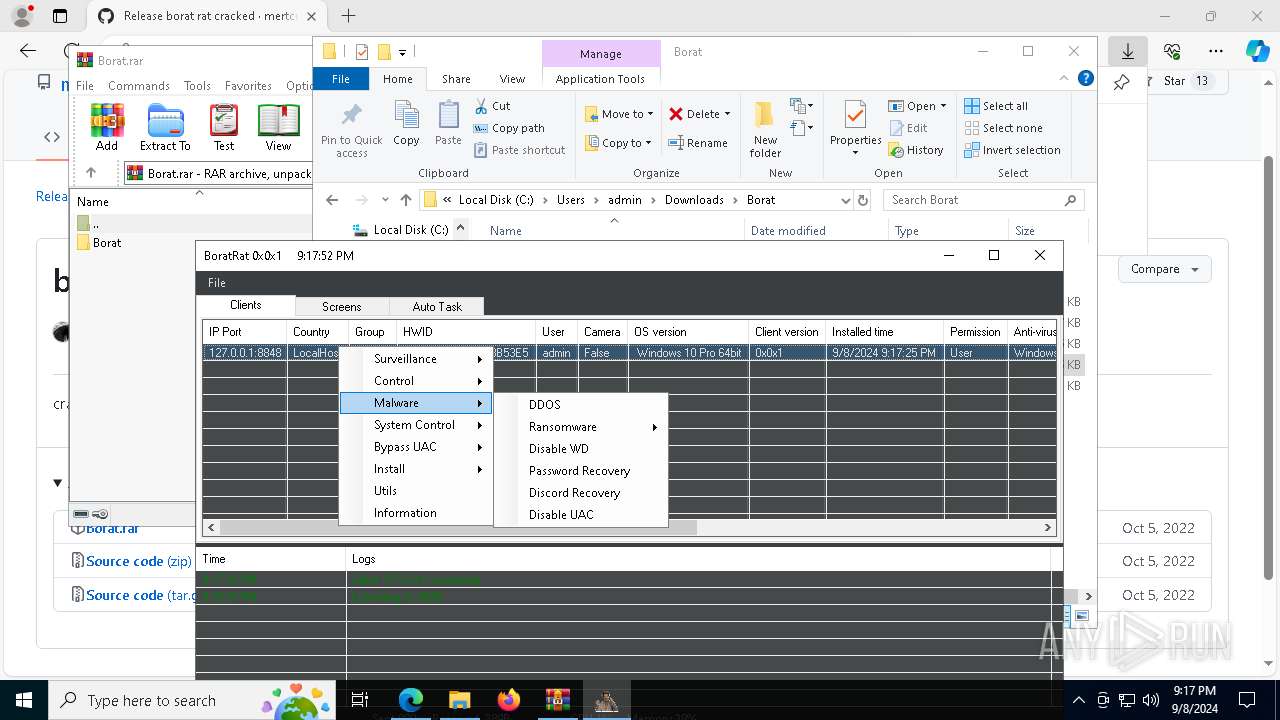
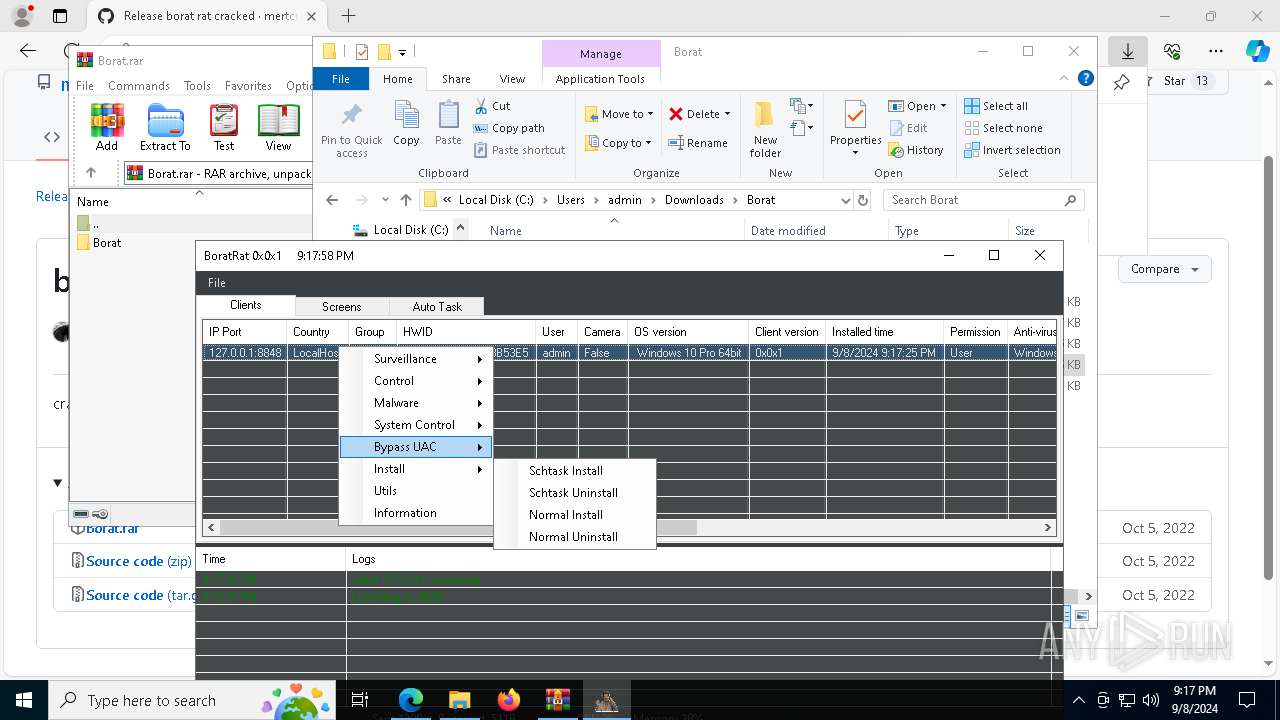
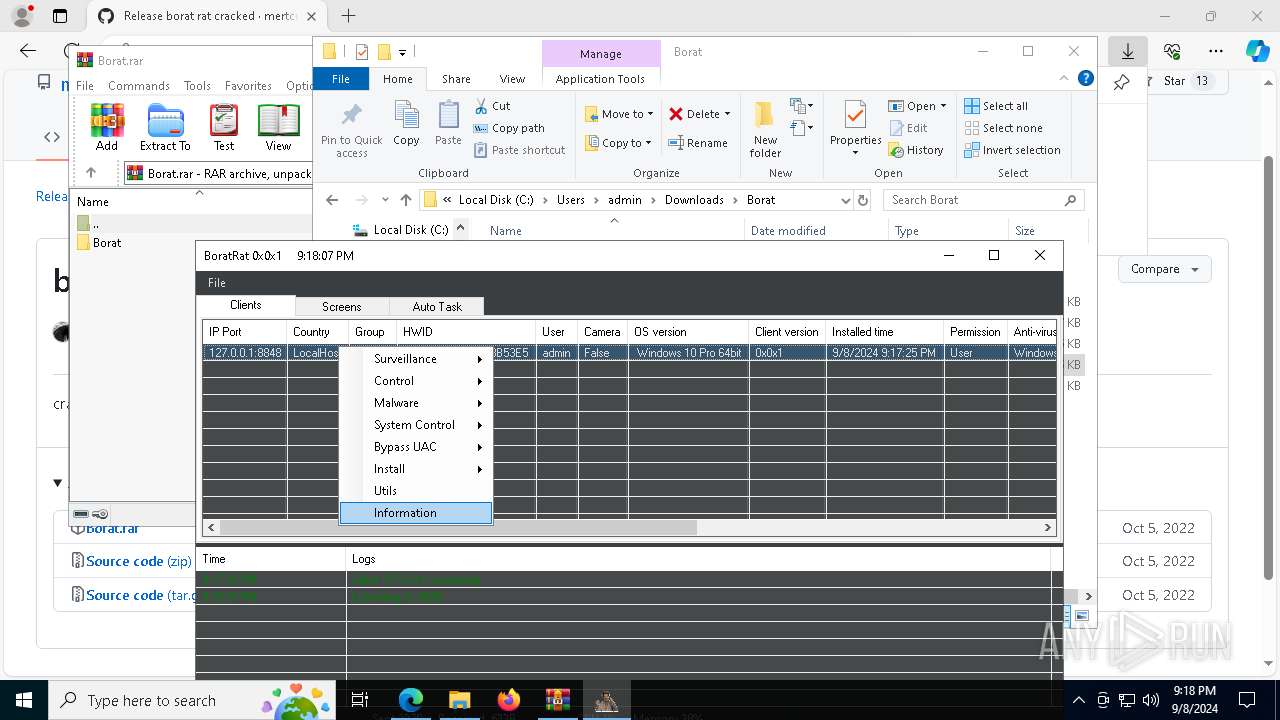
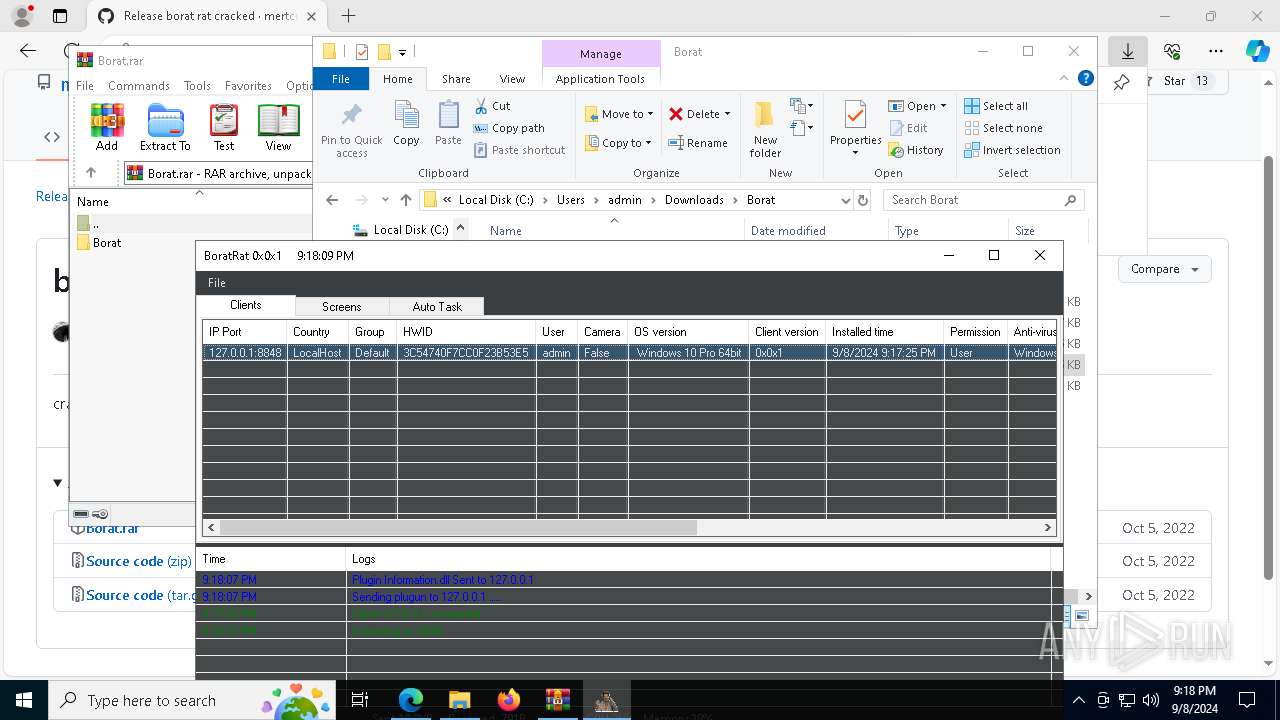
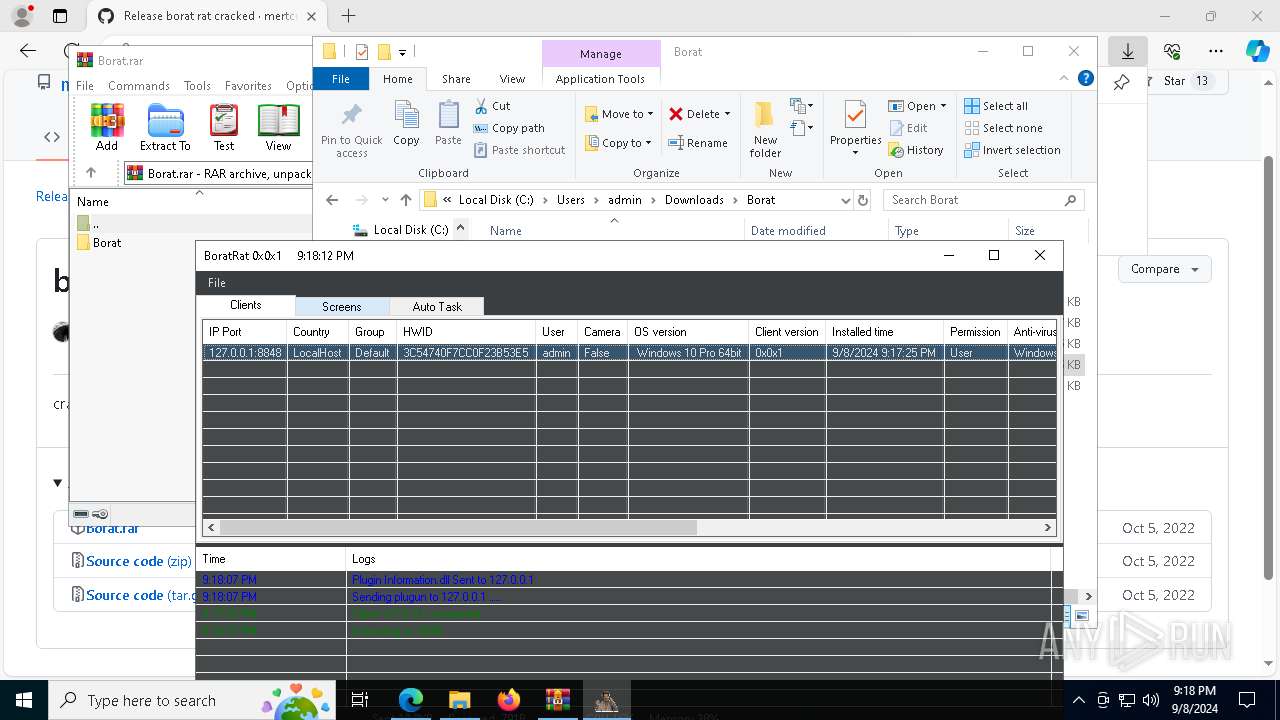
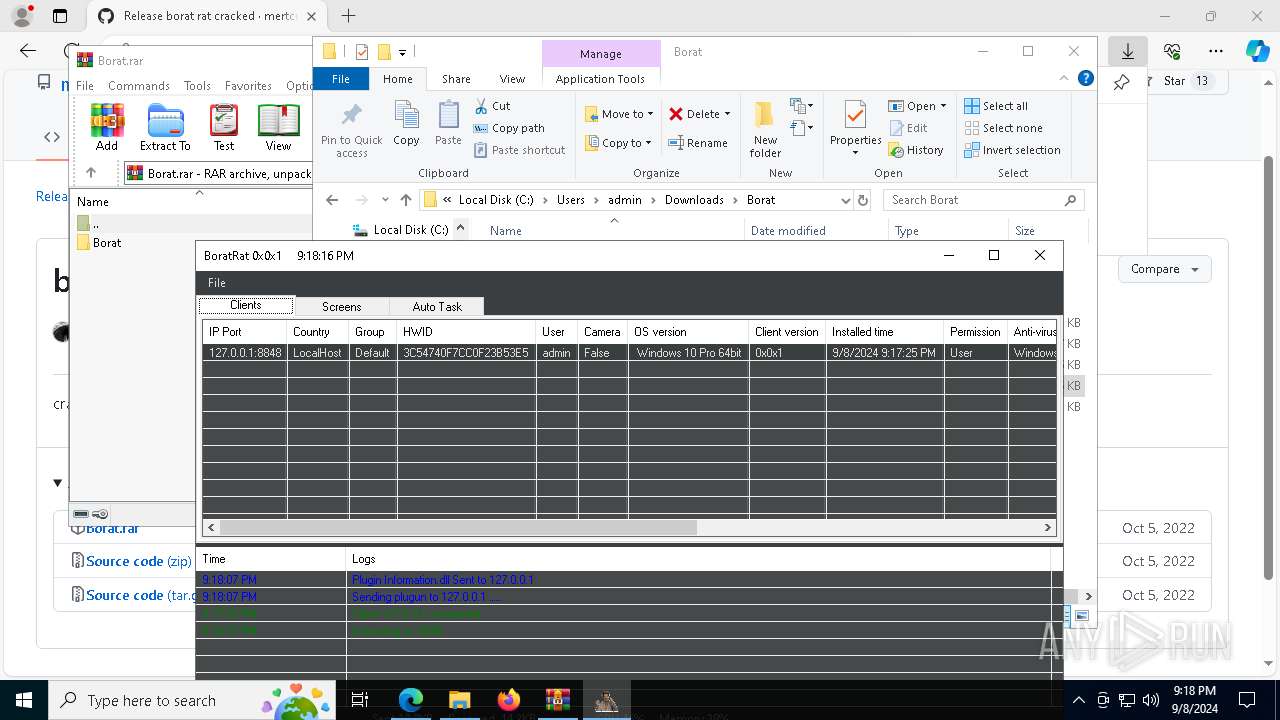
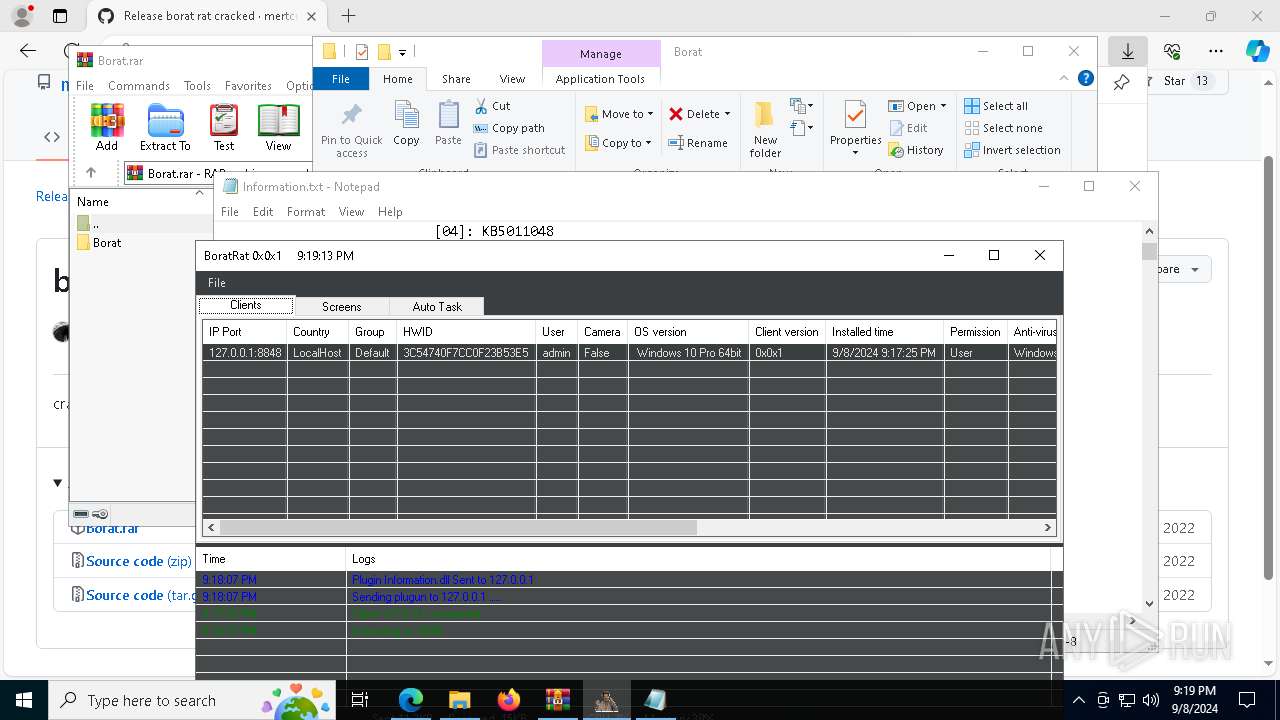
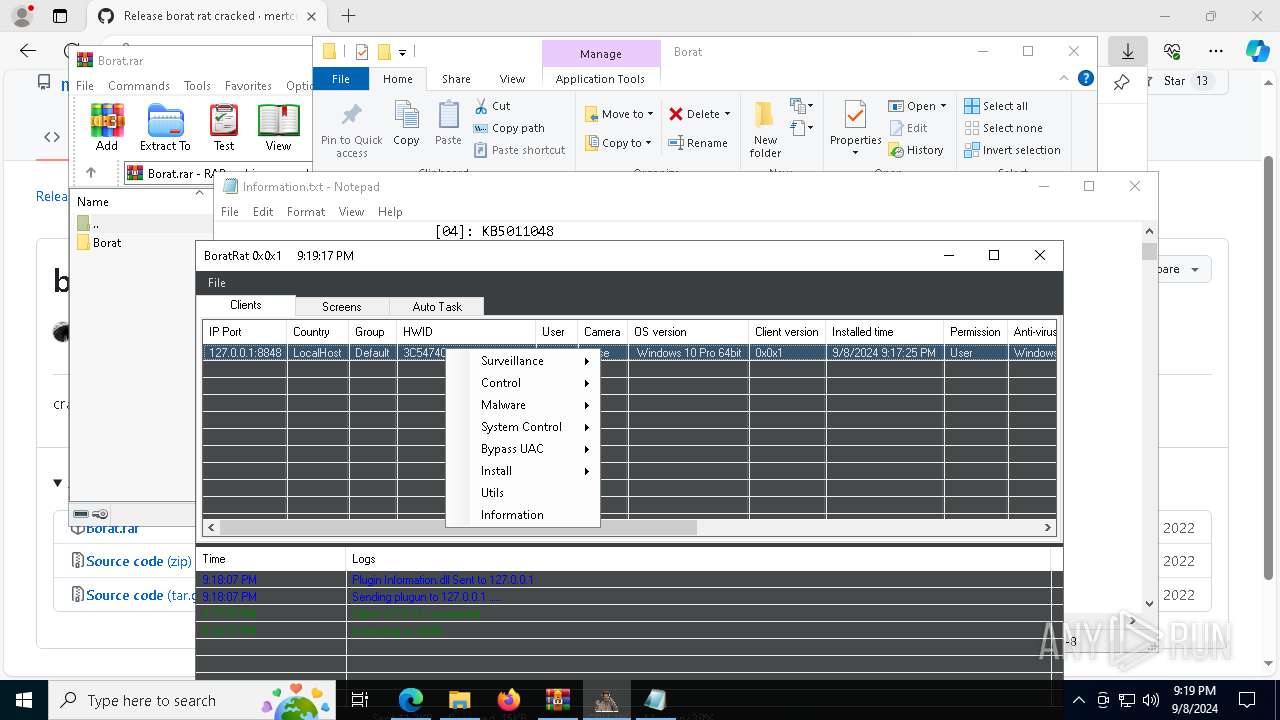
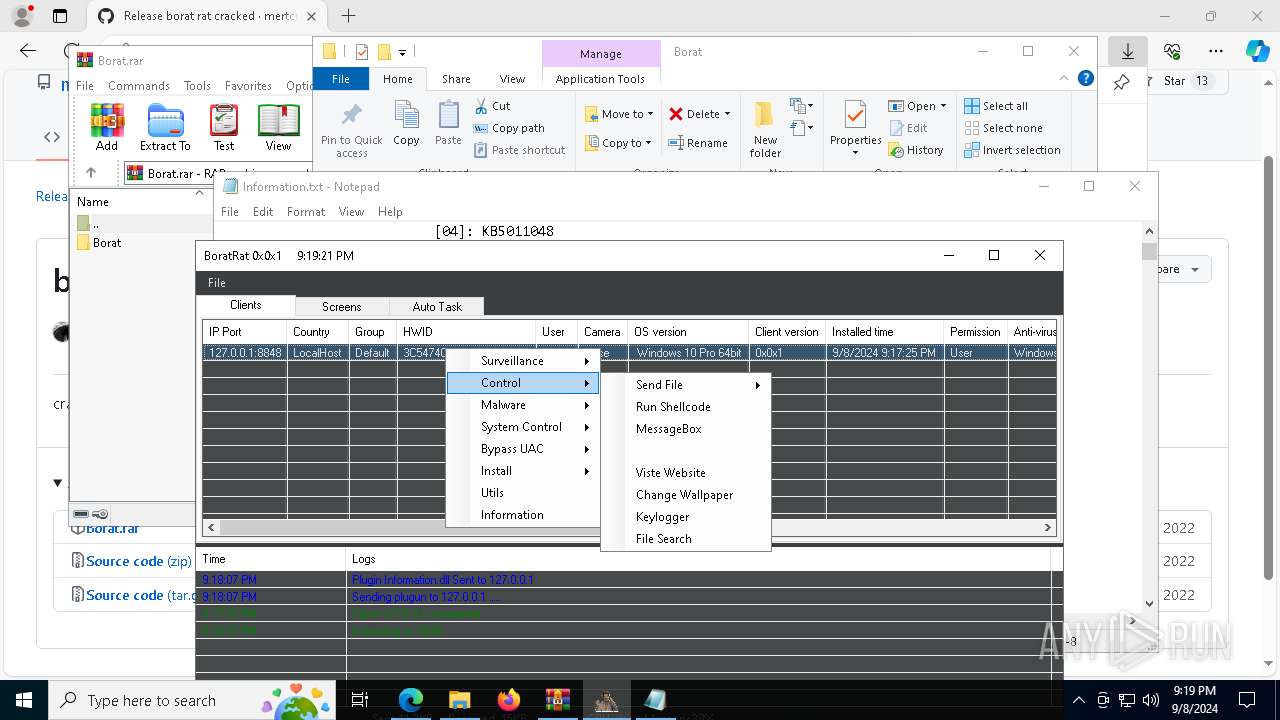
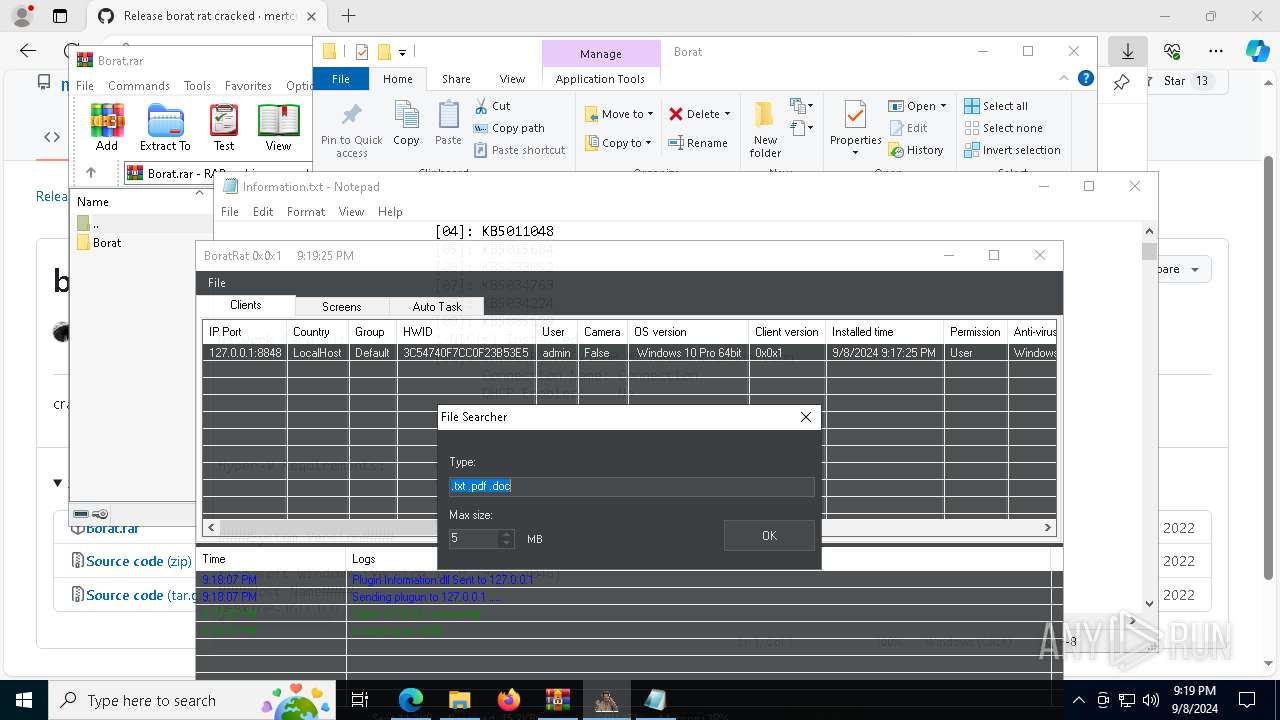
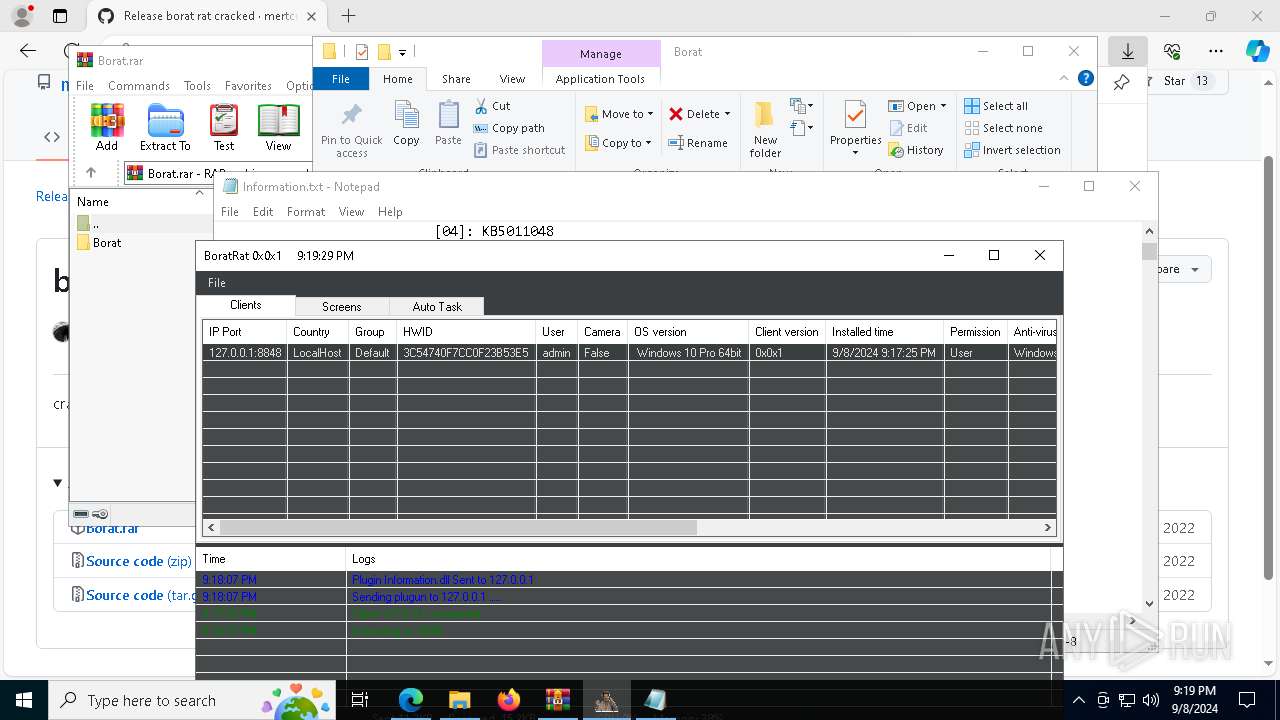
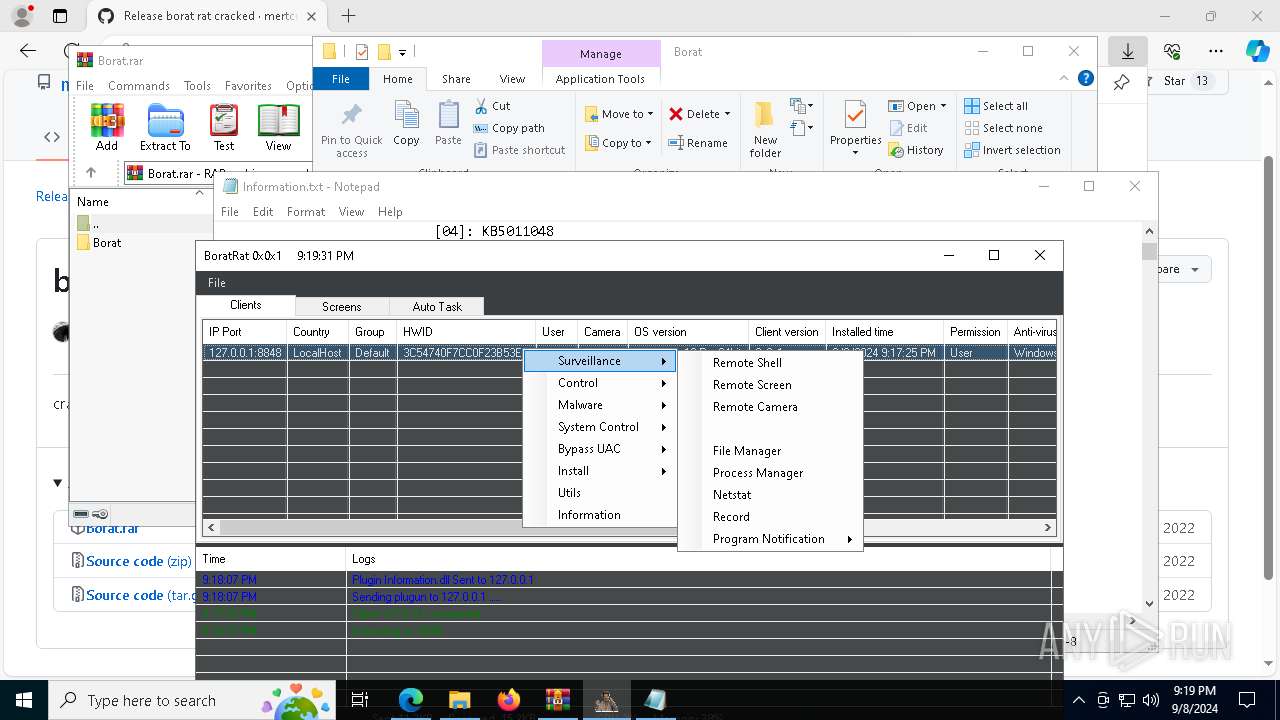
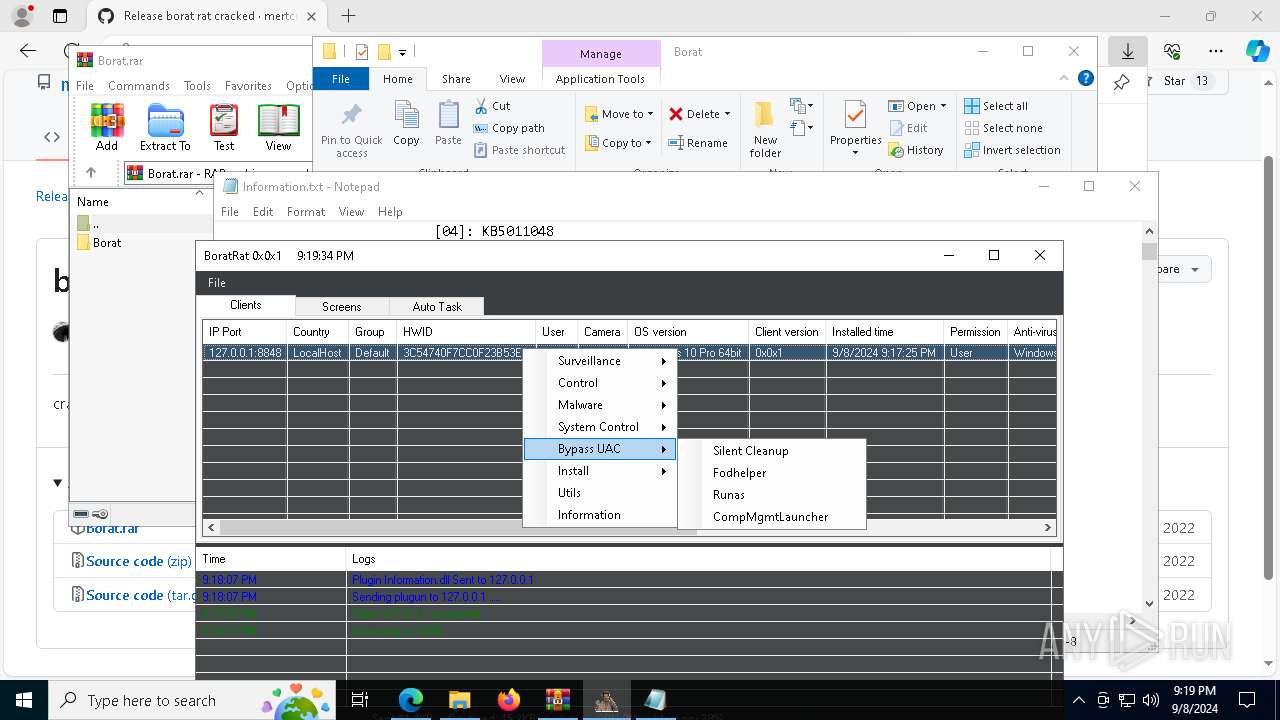
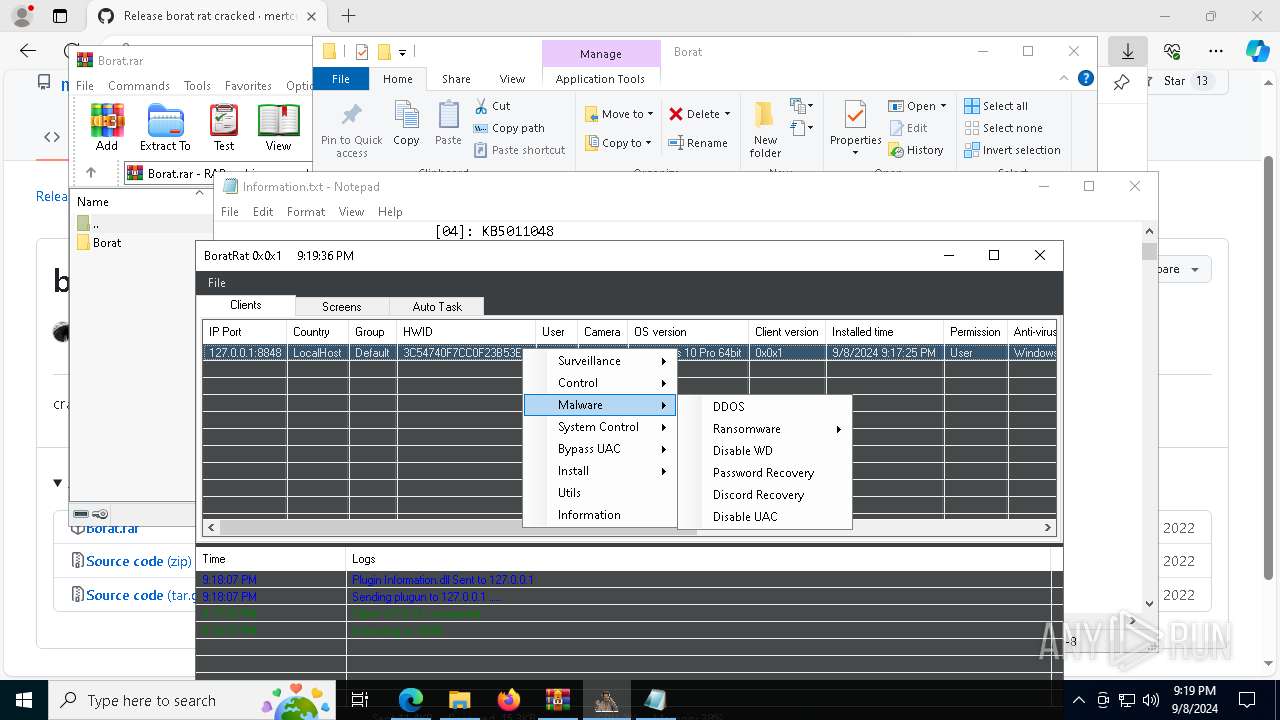
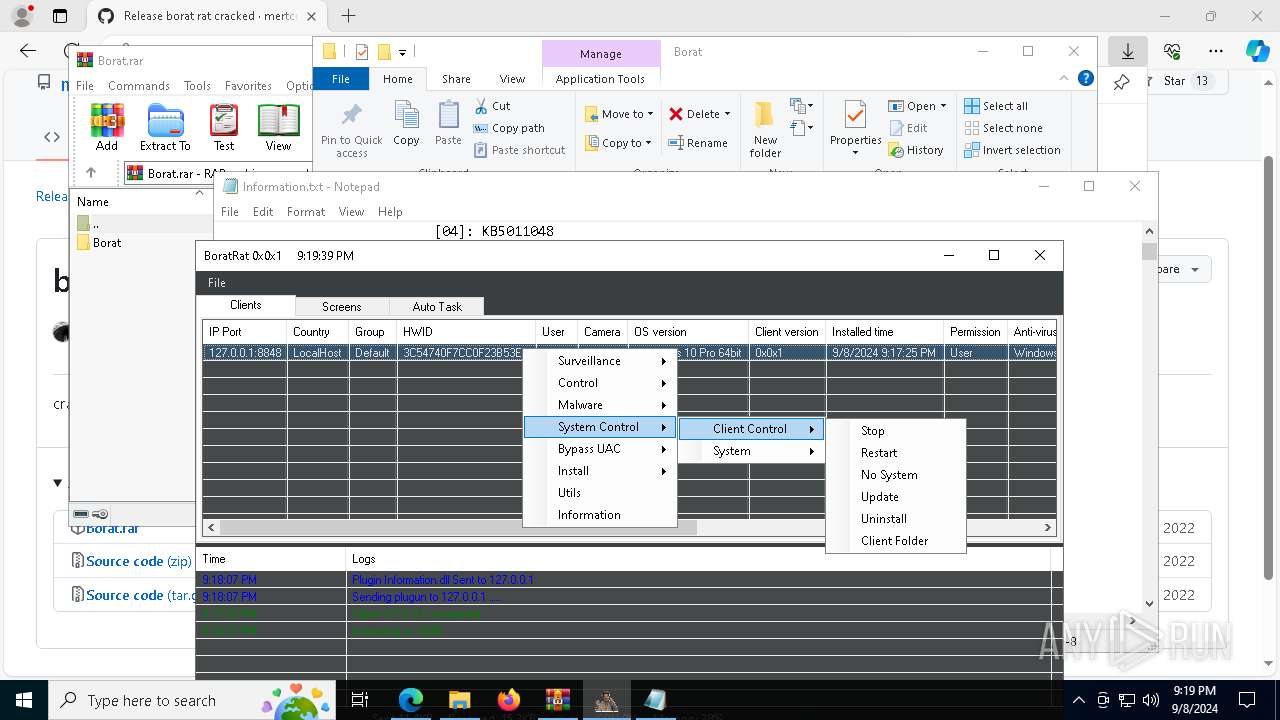
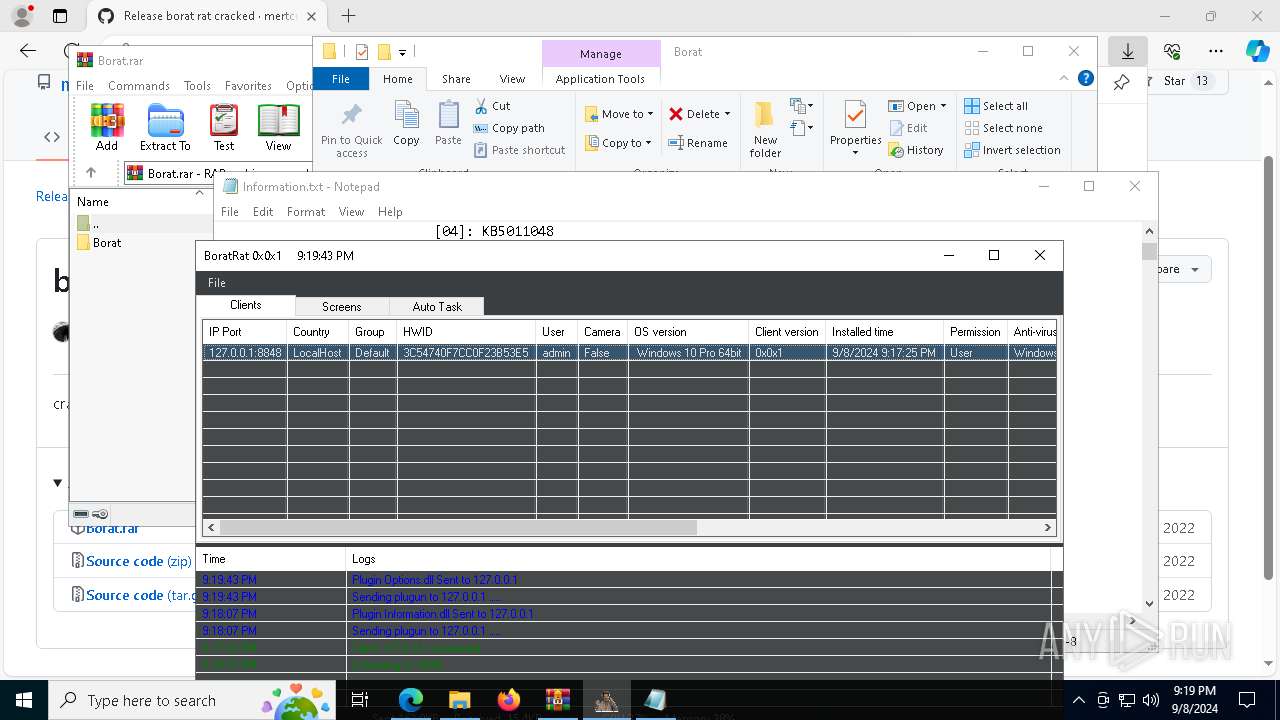
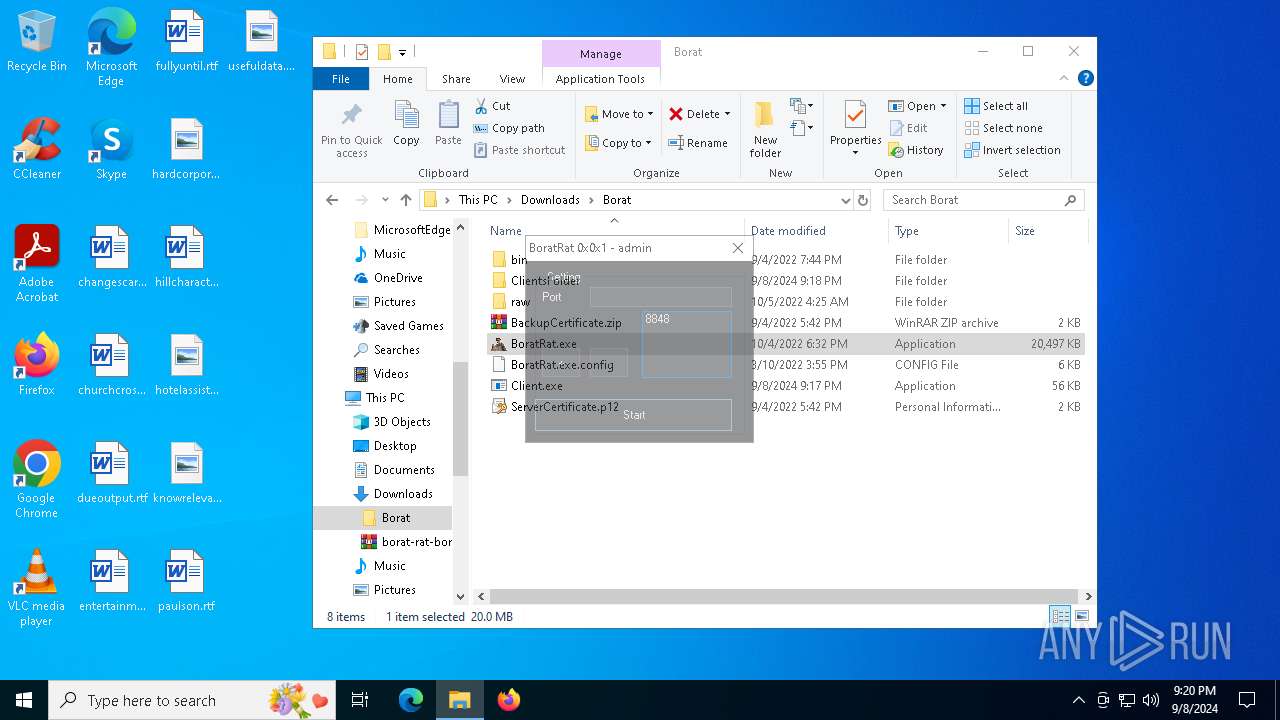
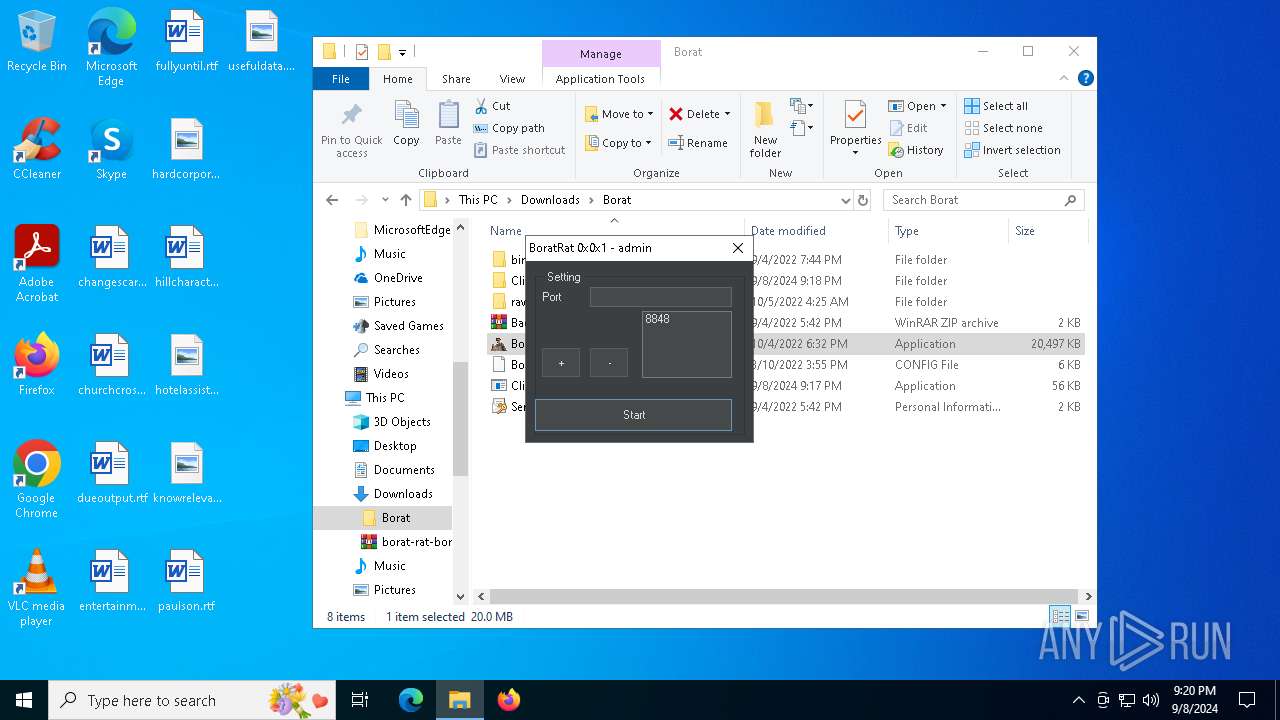
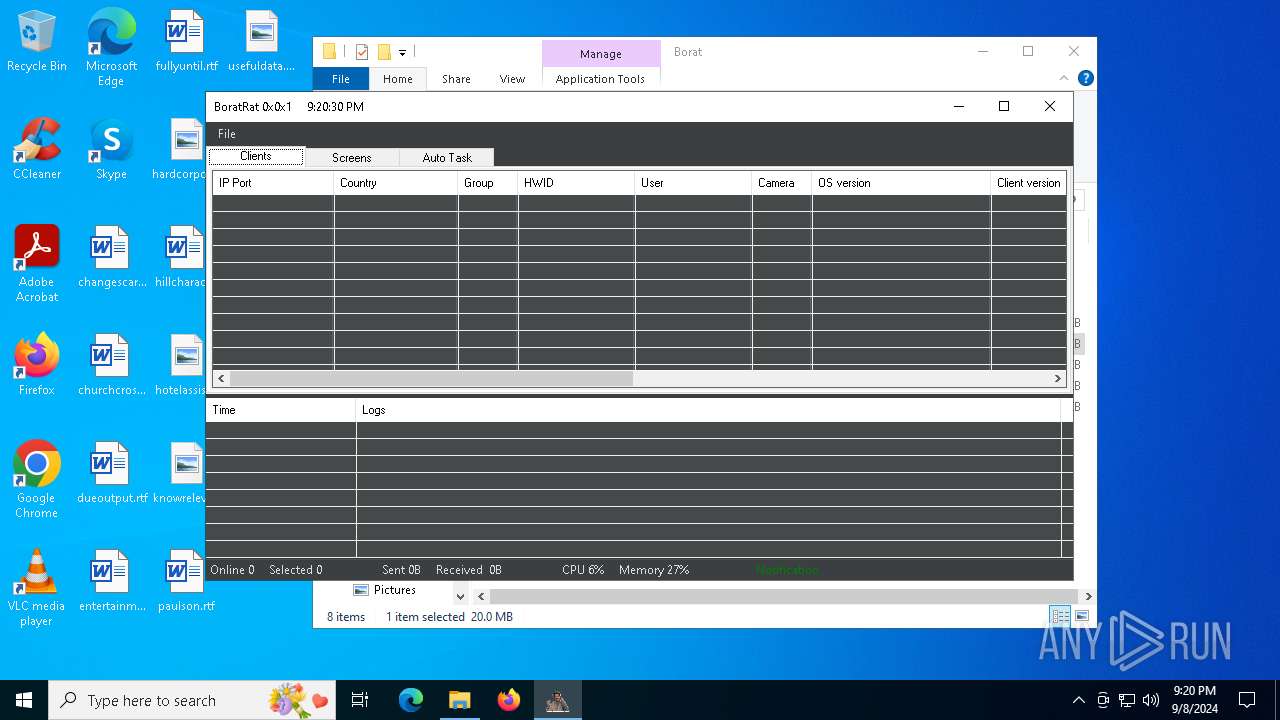
AsyncRat
(PID) Process(7472) Balls.exe
C2 (1)127.0.0.1
Ports (1)8848
Version0x0x1
Options
AutoRuntrue
MutexBoratRatMutex_Sa8XOfH1BudX
InstallFolder%AppData%
Certificates
Cert1MIICPTCCAaagAwIBAgIVAOBn4LGl7BufH3AY6NsdG2+okhltMA0GCSqGSIb3DQEBDQUAMG4xGDAWBgNVBAMMD0JvcmF0UmF0IFNlcnZlcjEVMBMGA1UECwwMU2E4WE9mSDFCdWRYMSEwHwYDVQQKDBhCb3JhdFJhdCBCeSBTYThYT2ZIMUJ1ZFgxCzAJBgNVBAcMAlNIMQswCQYDVQQGEwJDTjAeFw0yMTExMjMxNzQyNTFaFw0zMjA5MDExNzQyNTFaMBMxETAPBgNVBAMMCEJvcmF0UmF0MIGfMA0GCSqG...
Server_SignaturelYAoPlLsM4bgLJda+Dxyvc99HtNWNBxokWiEcX9ZrdHYvTPaz2nBDATFDot/U+P7utdRSl90JbEIyiLgR/xVtUm3J0H8p0hENz7npmRbNZUOpjBc3ksjJ4wmqhKzAagIaCXaooMCqkzTz6palinh2trIf7CgdlDoIMUEOq6h4kY=
Keys
AESafb57aefce5736a4dded095fe005cd7a4c965f265b47435bf5117cf62f28aef2
SaltBor@tRAT584
Total processes
272
Monitored processes
112
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6960 --field-trial-handle=2356,i,14805975419533480610,18209674110088587824,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 964 | net localgroup administrators | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
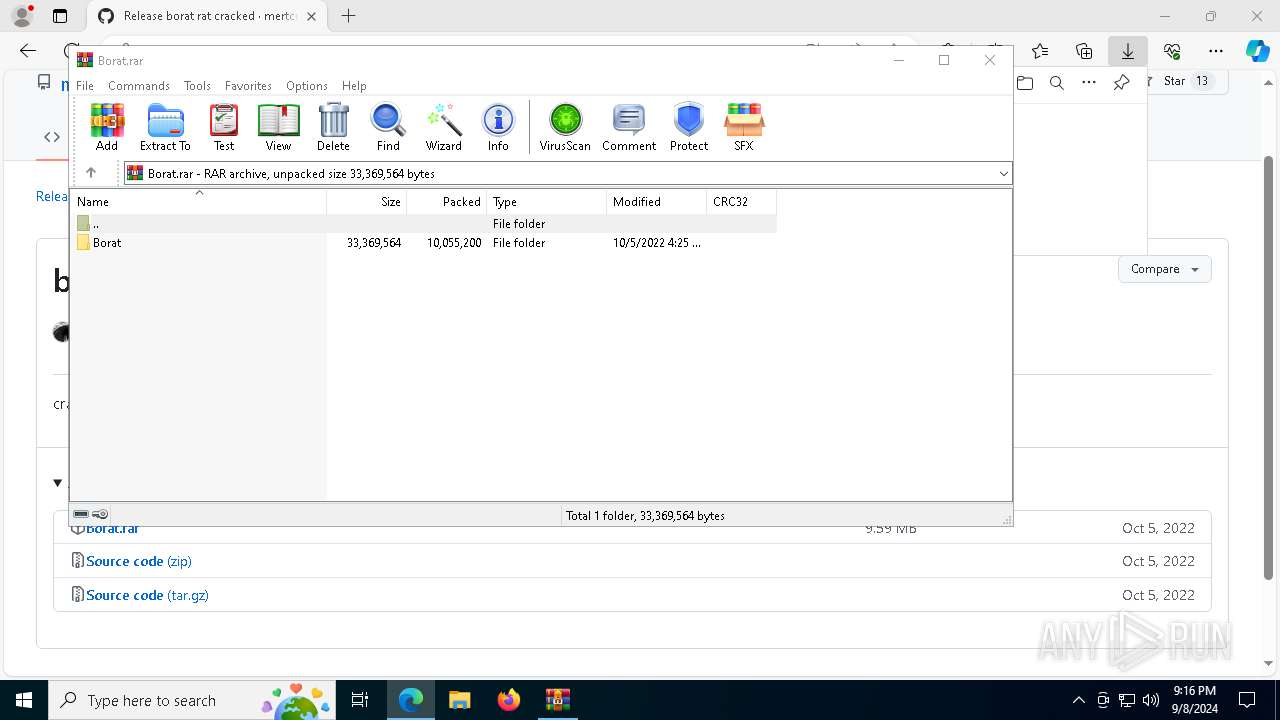
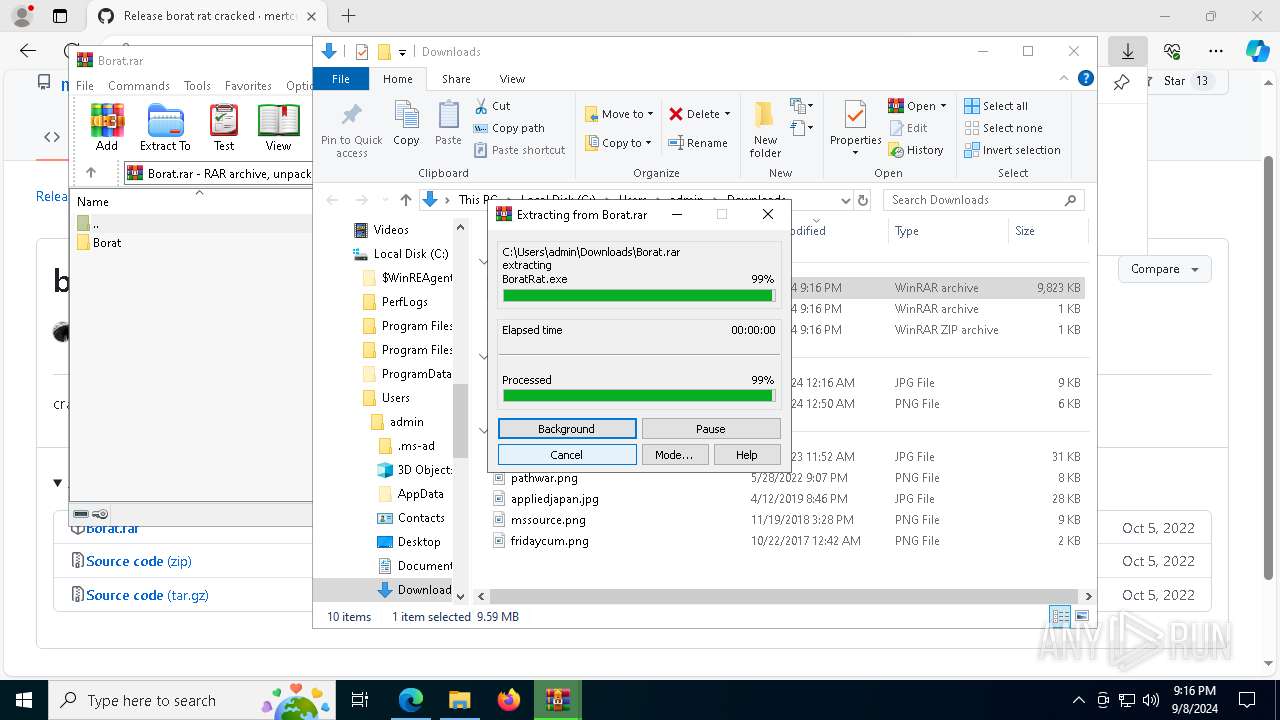
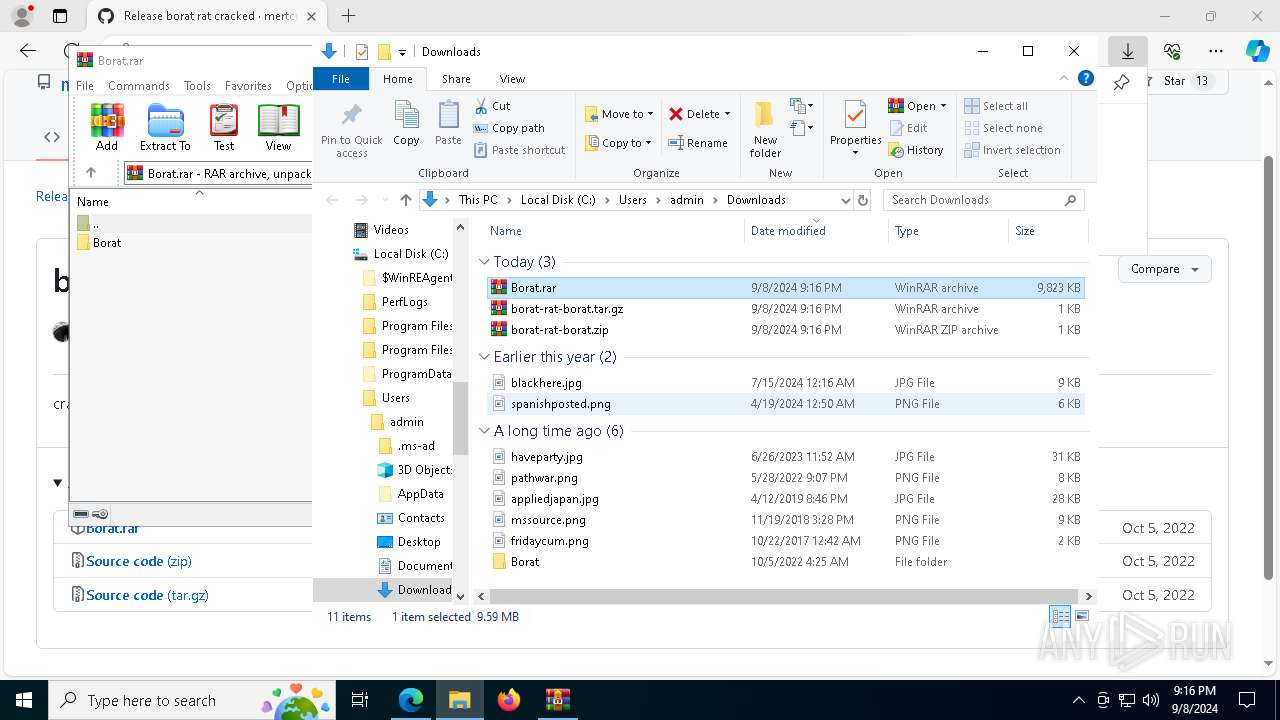
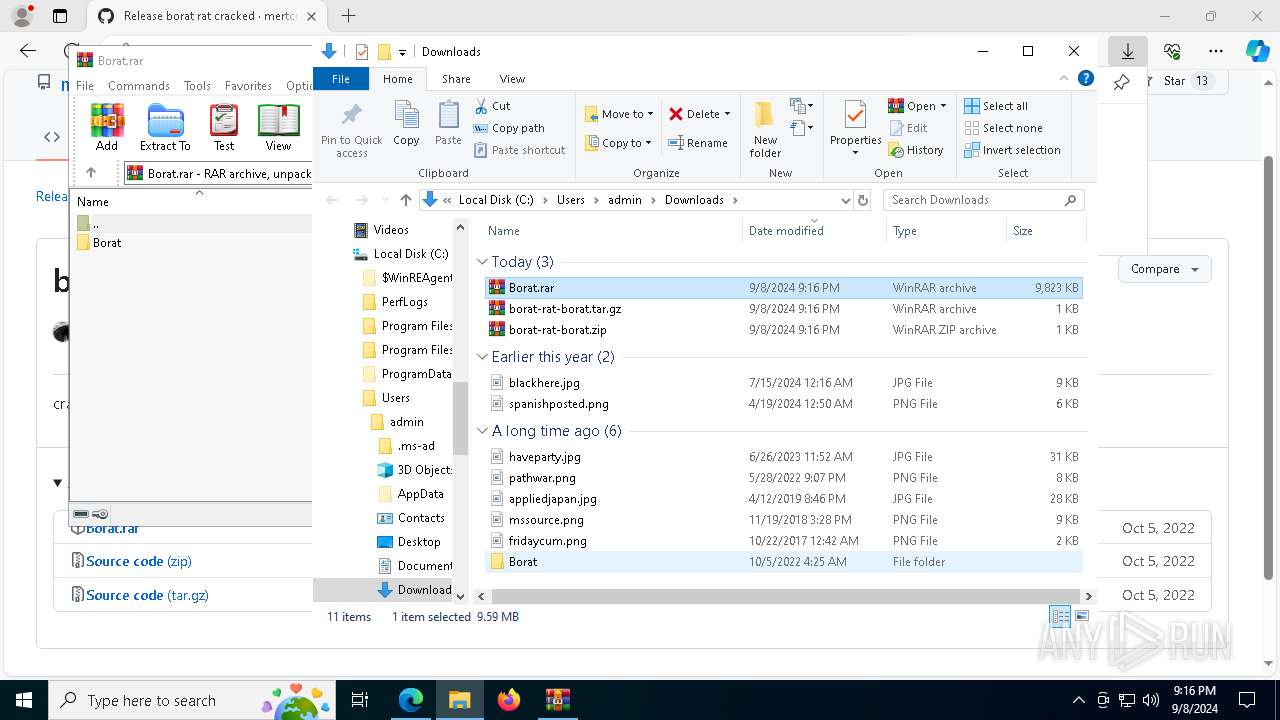
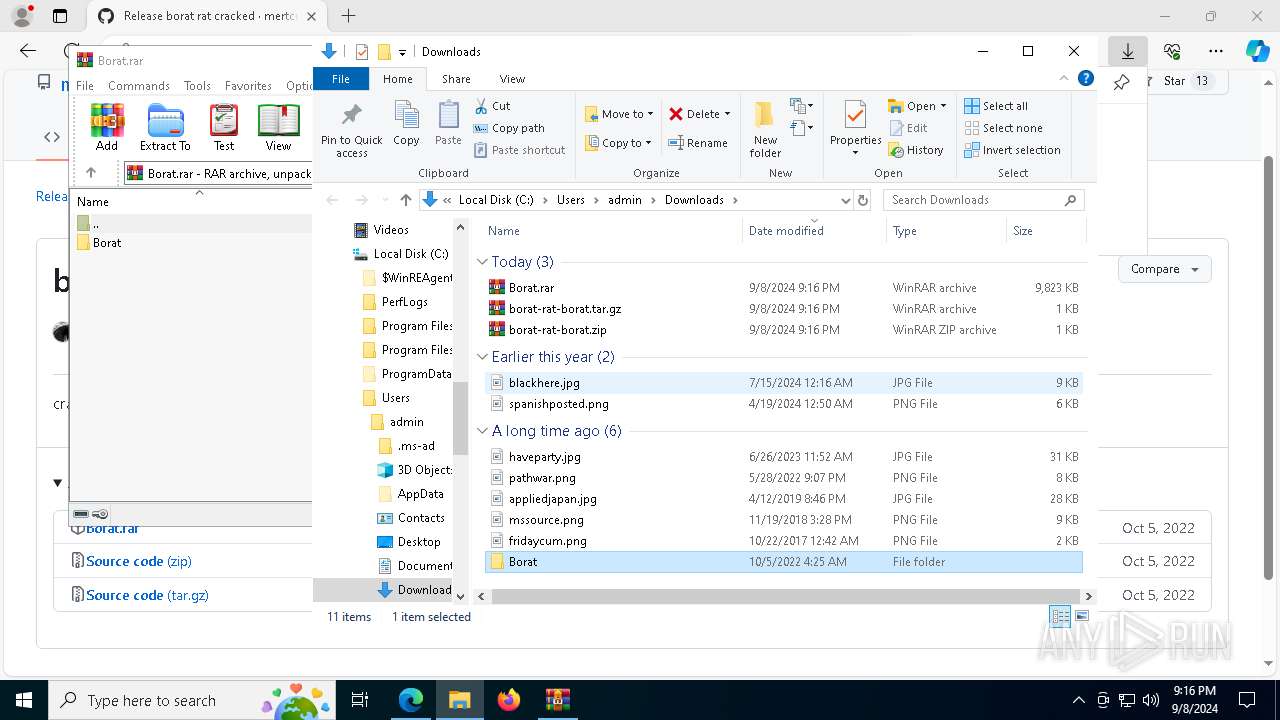
| 1020 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Borat.rar" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1064 | net localgroup | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | C:\WINDOWS\system32\net1 user guest | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
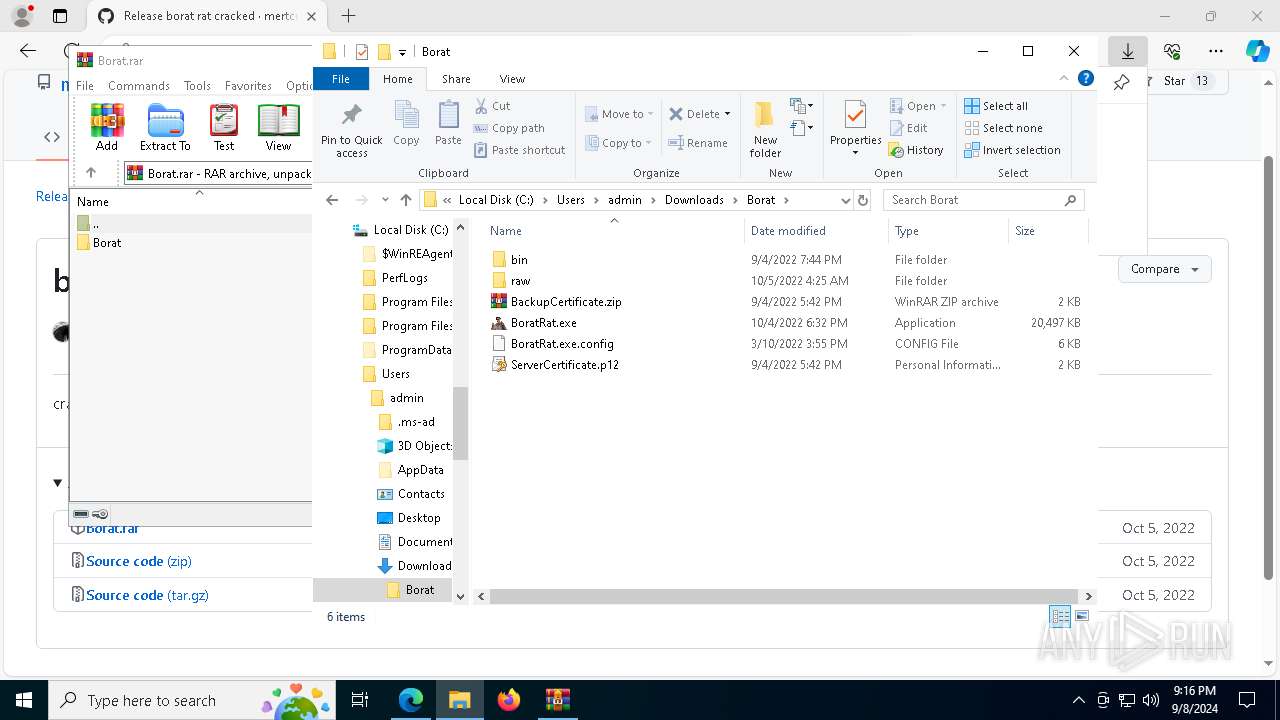
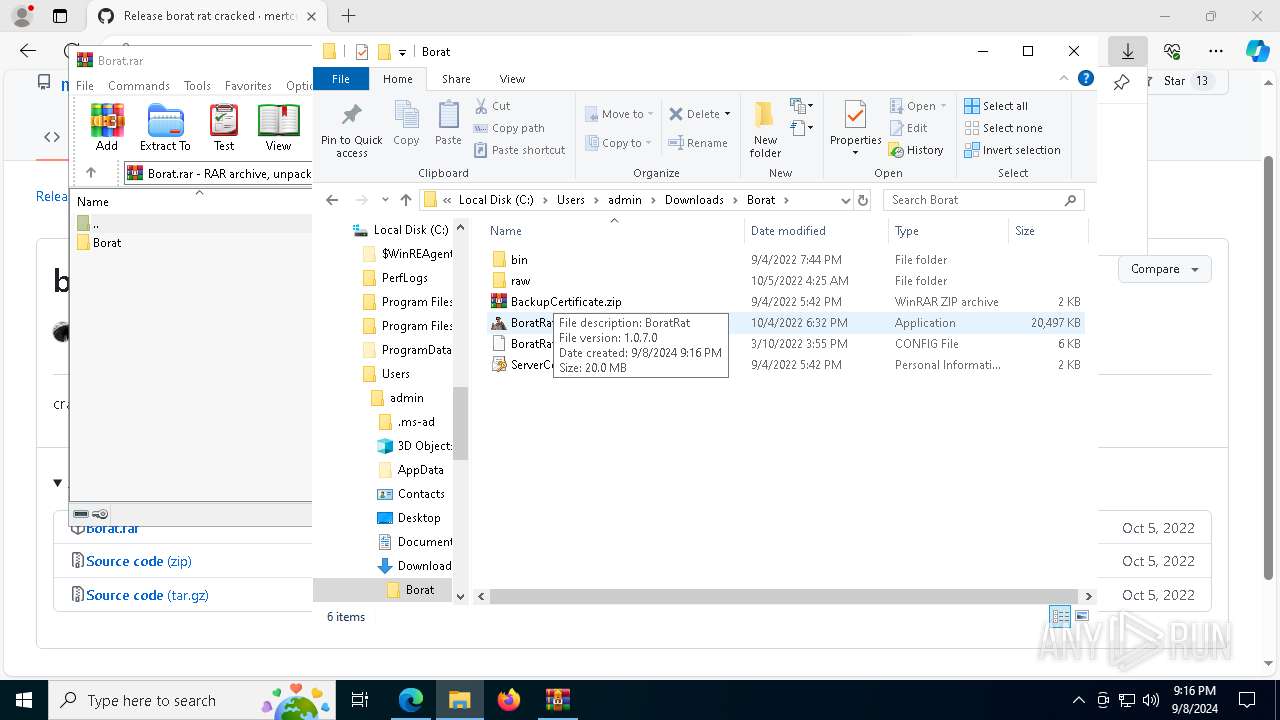
| 1664 | "C:\Users\admin\Downloads\Borat\BoratRat.exe" | C:\Users\admin\Downloads\Borat\BoratRat.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: BoratRat Version: 1.0.7.0 Modules
| |||||||||||||||
| 1964 | net user administrator | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1984 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2876 --field-trial-handle=2356,i,14805975419533480610,18209674110088587824,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
48 378
Read events
48 175
Write events
194
Delete events
9
Modification events
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D22CAE6C38802F00 | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 36B6B86C38802F00 | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656132 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {021396C6-D241-49EF-9617-CF96CF68F33E} | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656132 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D49D30FD-747B-4A94-B646-42910453D510} | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656132 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A4EF4188-F9A7-4A32-A64C-5E28EE8704D0} | |||
| (PID) Process: | (5720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656132 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {98BC1942-69DB-4EE6-84BF-119D14710F75} | |||
Executable files
31
Suspicious files
663
Text files
364
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12bcc0.TMP | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12bce0.TMP | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12bce0.TMP | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF12bd5d.TMP | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12bce0.TMP | — | |
MD5:— | SHA256:— | |||
| 5720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
103
DNS requests
103
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2092 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726166710&P2=404&P3=2&P4=g%2bvblwZyfmKicOplAzdEO4bV6Nq%2f9AiMPslNyUdhL5sOLcky9vaGEOdW4FRAvhPLeBMHe1TtFg0Ldr1Gu%2bdf5A%3d%3d | unknown | — | — | whitelisted |
2108 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726166710&P2=404&P3=2&P4=g%2bvblwZyfmKicOplAzdEO4bV6Nq%2f9AiMPslNyUdhL5sOLcky9vaGEOdW4FRAvhPLeBMHe1TtFg0Ldr1Gu%2bdf5A%3d%3d | unknown | — | — | whitelisted |
2092 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726166710&P2=404&P3=2&P4=nkMSt%2bfFdXJWggsR%2b216xXDTygUP5Qp4MN%2bykXkIvEIbNDkujWOj%2b3AVkczPmdRC5B4CS0gOFLzMVJ6CVRg6QQ%3d%3d | unknown | — | — | whitelisted |
7776 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ea79963f-51af-4930-ab74-50e807a8950b?P1=1726209880&P2=404&P3=2&P4=jPEo5cNyo0JVcf%2fqhk%2fdnDgnQ9FI5v%2fmrNlD%2flLNTqkeMUYMeU8NtUkPDIGlnJG1oIARwBuSXqgZzVHxD4uVZw%3d%3d | unknown | — | — | whitelisted |
2092 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/33525f64-900e-472b-82f7-b2841f9be572?P1=1726386325&P2=404&P3=2&P4=eUFfbbwdkKo4ZFQZ9BbpONxwqAqmx%2f1KqrxCVHpHuT1Oe4EaB2Ji15SvpREB8zIK%2bktX00tY25fY%2bpwtwDFRiA%3d%3d | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726166710&P2=404&P3=2&P4=g%2bvblwZyfmKicOplAzdEO4bV6Nq%2f9AiMPslNyUdhL5sOLcky9vaGEOdW4FRAvhPLeBMHe1TtFg0Ldr1Gu%2bdf5A%3d%3d | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726166710&P2=404&P3=2&P4=g%2bvblwZyfmKicOplAzdEO4bV6Nq%2f9AiMPslNyUdhL5sOLcky9vaGEOdW4FRAvhPLeBMHe1TtFg0Ldr1Gu%2bdf5A%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
568 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6380 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2108 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2108 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |