| File name: | test.exe |
| Full analysis: | https://app.any.run/tasks/9d705aab-03e0-4536-8b16-46edba6bd93c |
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | October 04, 2022, 19:46:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 102F296D5E89F9B73143D702C7DD57D6 |
| SHA1: | E9C2399956813B4760988ACE3961CB9BC69A6D6A |
| SHA256: | 2BA23389994DE55B043894ACA4F56BD2B0330A14D542E9C57ABAA3C79157369E |
| SSDEEP: | 12288:O9HFJ9rJxRX1uVVjoaWSoynxdO1FVBaOiRZTERfIhNkNCCLo9Ek5C/h0:aZ1xuVVjfFoynPaVBUR8f+kN10EBS |
MALICIOUS
Changes the autorun value in the registry
- test.exe (PID: 1448)
- msdcsc.exe (PID: 2984)
Changes the login/logoff helper path in the registry
- test.exe (PID: 1448)
Drops executable file immediately after starts
- test.exe (PID: 1448)
DARKCOMET detected by memory dumps
- msdcsc.exe (PID: 2984)
SUSPICIOUS
Checks supported languages
- test.exe (PID: 1448)
- msdcsc.exe (PID: 2984)
- cmd.exe (PID: 2452)
- cmd.exe (PID: 3720)
Executable content was dropped or overwritten
- test.exe (PID: 1448)
Starts CMD.EXE for commands execution
- test.exe (PID: 1448)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2452)
- cmd.exe (PID: 3720)
Starts itself from another location
- test.exe (PID: 1448)
Reads the date of Windows installation
- test.exe (PID: 1448)
Reads the computer name
- msdcsc.exe (PID: 2984)
- test.exe (PID: 1448)
Drops a file with a compile date too recent
- test.exe (PID: 1448)
INFO
Checks supported languages
- attrib.exe (PID: 960)
- attrib.exe (PID: 3356)
- notepad.exe (PID: 2764)
- notepad.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DarkComet
(PID) Process(2984) msdcsc.exe
C2 (3)192.168.0.8:6969
rtts.ddns.net:6969
127.0.0.1:6969
Version#KCMDDC51#
MutexDC_MUTEX-CYNCSGL
sidVictim
FWB0
gencodeb7ladvSsUVqW
InstallTrue
COMBOPATH7
Install pathMSDCSC\msdcsc.exe
Registry keyMicroUpdate
Edit date2007-04-16
PersistanceTrue
MELT1
Change Date1
Directory attributesTrue
File attrubutesTrue
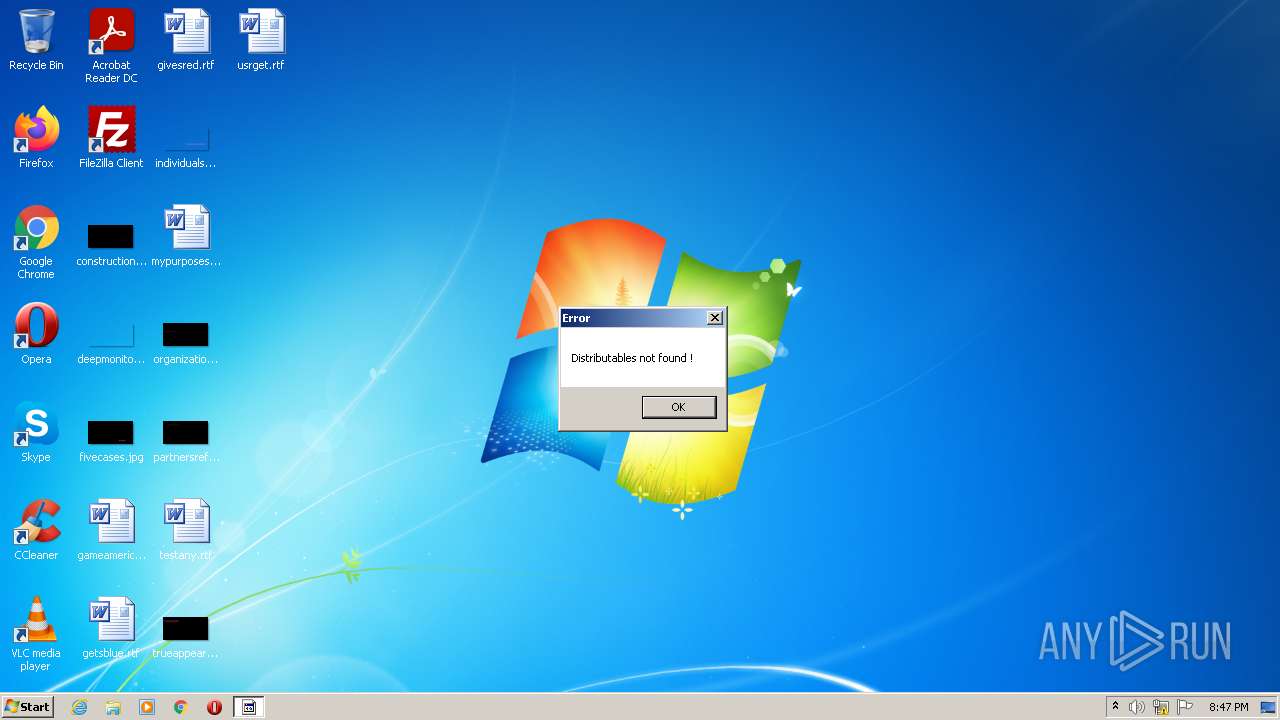
FAKEMSG1
MSGTITLEError
MSGCORE44697374726962757461626C6573206E6F7420666F756E642021
MSGICON0
SH11
SH41
CHIDEF1
CHIDED1
PERS1
Offline keyloggerTrue
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2012-Jun-07 15:59:53 |
| Detected languages: |
|
| Comments: | Remote Service Application |
| CompanyName: | Microsoft Corp. |
| FileDescription: | Remote Service Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | MSRSAAPP |
| LegalCopyright: | Copyright (C) 1999 |
| OriginalFilename: | MSRSAAP.EXE |
| ProductName: | Remote Service Application |
| ProductVersion: | 4, 0, 0, 0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 80 |
| e_cp: | 2 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | 15 |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | 26 |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 256 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 9 |
| TimeDateStamp: | 2012-Jun-07 15:59:53 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 579824 | 580096 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55342 |
.itext | 585728 | 6484 | 6656 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95375 |
.data | 593920 | 15676 | 15872 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.83487 |
.bss | 610304 | 29700 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.idata | 643072 | 16704 | 16896 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.26814 |
.tls | 663552 | 56 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rdata | 667648 | 24 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 671744 | 35548 | 35840 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.72501 |
.rsrc | 708608 | 17484 | 17920 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.44223 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.6633 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
2 | 2.80231 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4083 | 3.16951 | 524 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4084 | 3.32488 | 1020 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4085 | 3.46183 | 168 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
AVICAP32.DLL |
SHELL32.DLL |
SHFolder.dll |
URLMON.DLL |
WS2_32.DLL |
advapi32.dll |
advapi32.dll (#2) |
advapi32.dll (#3) |
comctl32.dll |
gdi32.dll |
Total processes
45
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | attrib "C:\Users\admin\AppData\Local\Temp\test.exe" +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1448 | "C:\Users\admin\AppData\Local\Temp\test.exe" | C:\Users\admin\AppData\Local\Temp\test.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2452 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\AppData\Local\Temp\test.exe" +s +h | C:\Windows\System32\cmd.exe | — | test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2764 | notepad | C:\Windows\system32\notepad.exe | — | msdcsc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\Documents\MSDCSC\msdcsc.exe" | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | test.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
DarkComet(PID) Process(2984) msdcsc.exe C2 (3)192.168.0.8:6969 rtts.ddns.net:6969 127.0.0.1:6969 Version#KCMDDC51# MutexDC_MUTEX-CYNCSGL sidVictim FWB0 gencodeb7ladvSsUVqW InstallTrue COMBOPATH7 Install pathMSDCSC\msdcsc.exe Registry keyMicroUpdate Edit date2007-04-16 PersistanceTrue MELT1 Change Date1 Directory attributesTrue File attrubutesTrue FAKEMSG1 MSGTITLEError MSGCORE44697374726962757461626C6573206E6F7420666F756E642021 MSGICON0 SH11 SH41 CHIDEF1 CHIDED1 PERS1 Offline keyloggerTrue | |||||||||||||||
| 3356 | attrib "C:\Users\admin\AppData\Local\Temp" +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3720 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\AppData\Local\Temp" +s +h | C:\Windows\System32\cmd.exe | — | test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3980 | notepad | C:\Windows\system32\notepad.exe | — | test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 817
Read events
1 743
Write events
74
Delete events
0
Modification events
| (PID) Process: | (1448) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicroUpdate |
Value: C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (1448) test.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | UserInit |
Value: C:\Windows\system32\userinit.exe,C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (1448) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1448) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1448) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1448) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1448) test.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2984) msdcsc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicroUpdate |
Value: C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (2984) msdcsc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1448 | test.exe | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
4
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | msdcsc.exe | 185.223.169.220:6969 | rtts.ddns.net | Andridan-Impex SRL | MD | unknown |
— | — | 192.168.100.180:49195 | — | — | — | malicious |
— | — | 185.223.169.220:6969 | rtts.ddns.net | Andridan-Impex SRL | MD | unknown |
— | — | 192.168.100.180:49895 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
rtts.ddns.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |