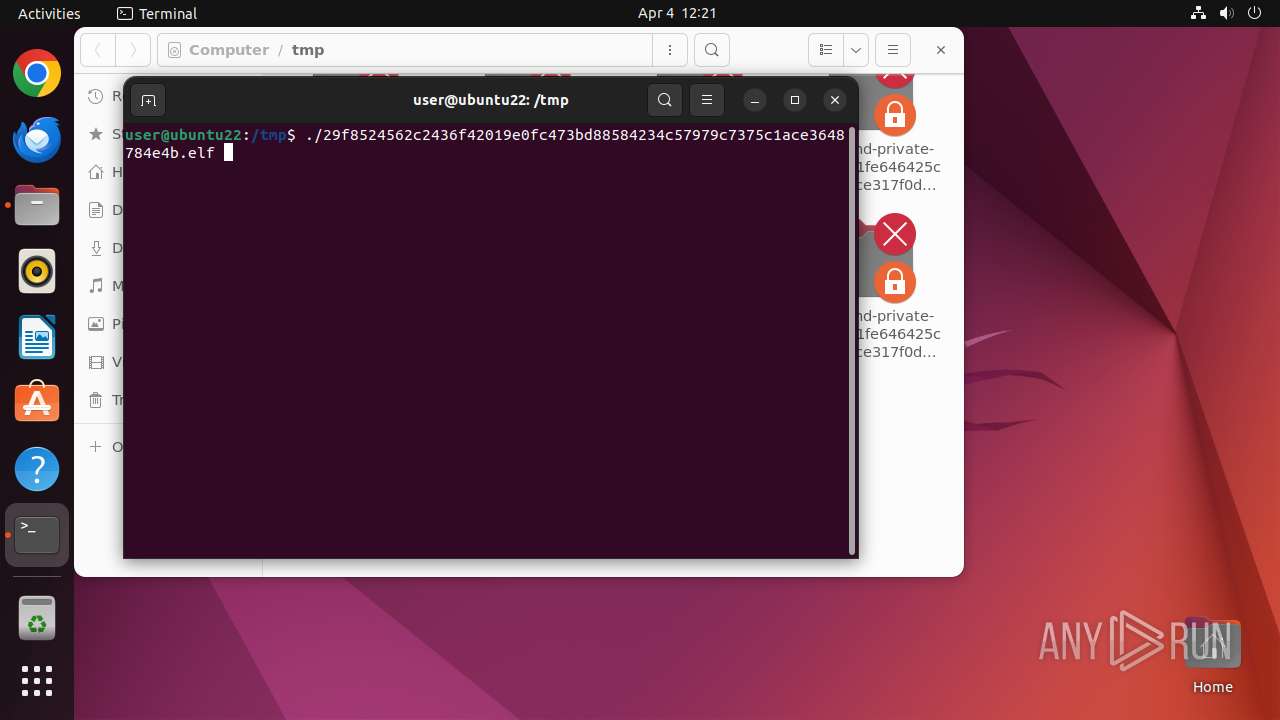
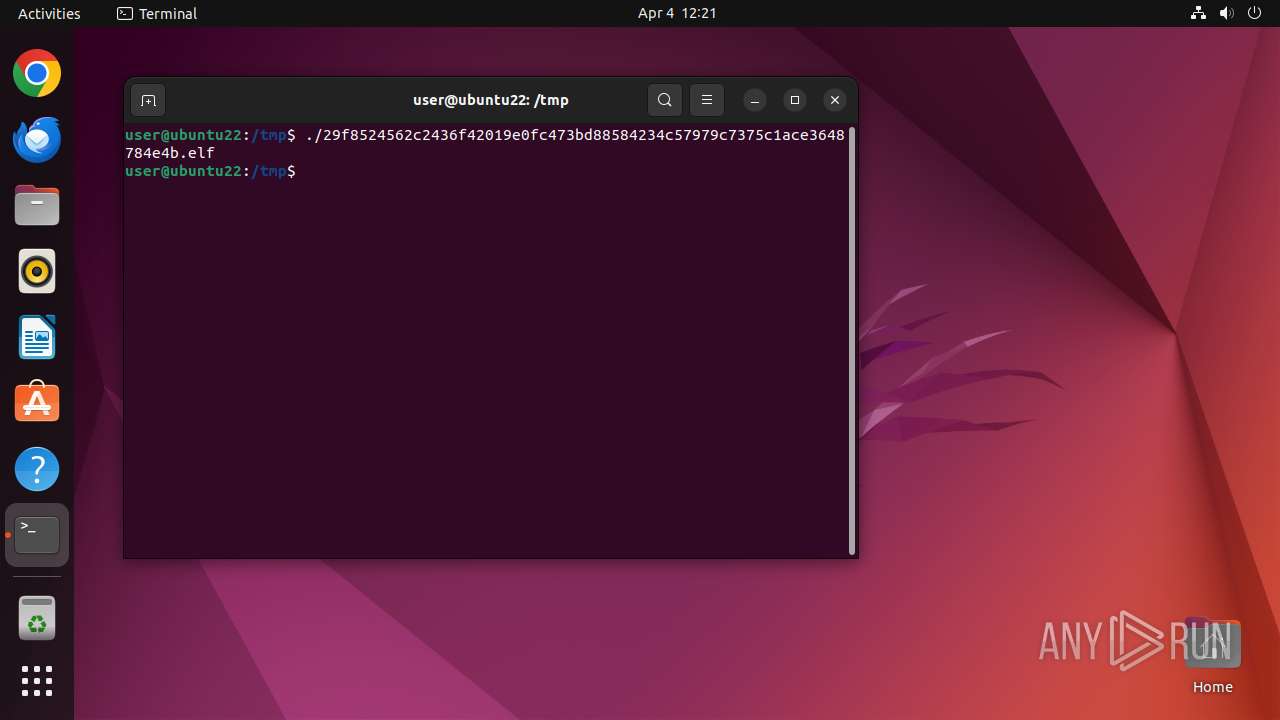
| File name: | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b |
| Full analysis: | https://app.any.run/tasks/ba96bc81-d8dd-4f34-b768-bcaaf6de64a0 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | April 04, 2025, 11:21:10 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MIME: | application/x-sharedlib |
| File info: | ELF 64-bit LSB shared object, x86-64, version 1 (SYSV), statically linked, no section header |
| MD5: | F6634E2FB7872BE767A2CB5B1DA04103 |
| SHA1: | 532037729F2DA9FC1341F744E5AFA2420BCFEBCA |
| SHA256: | 29F8524562C2436F42019E0FC473BD88584234C57979C7375C1ACE3648784E4B |
| SSDEEP: | 49152:cHO0kCVyoB79ZhZORj6g3//xCi2oOD9HXoLt5yHppHk0CeGzBmh/5iz7FF0UZgxI:cHdkCDnAReUXRhODJoL3yHppRCTm7W7F |
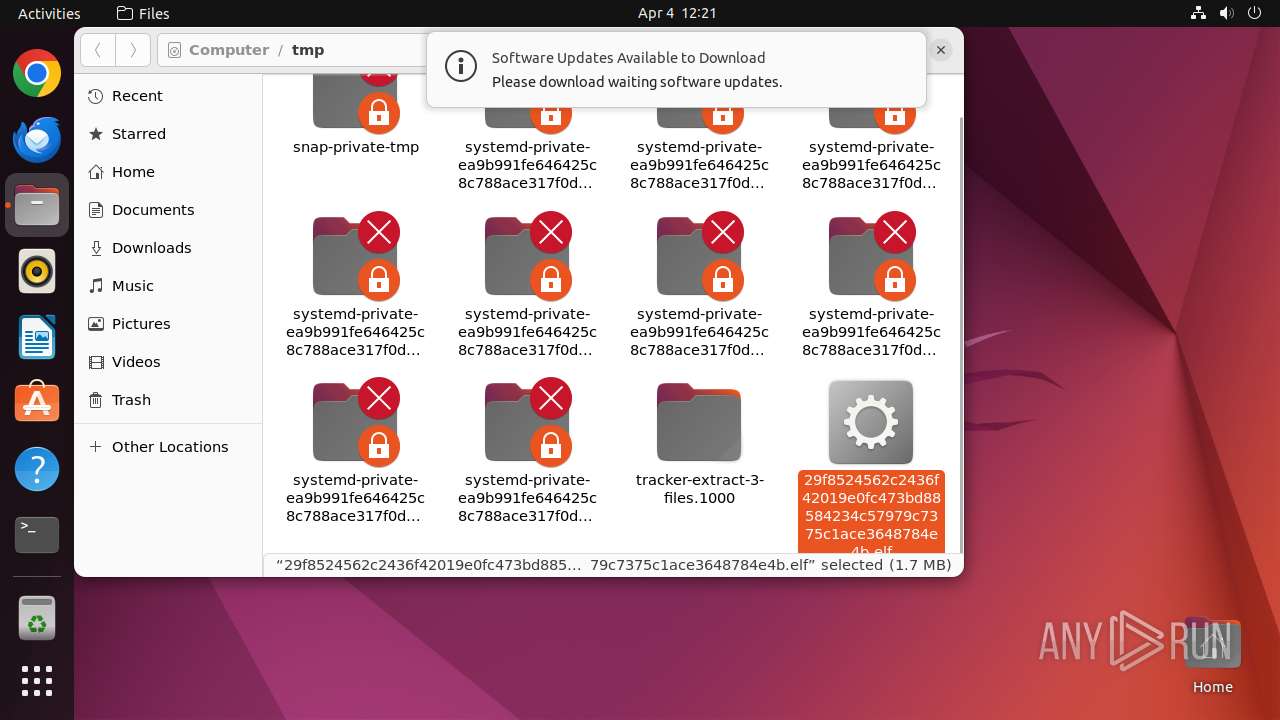
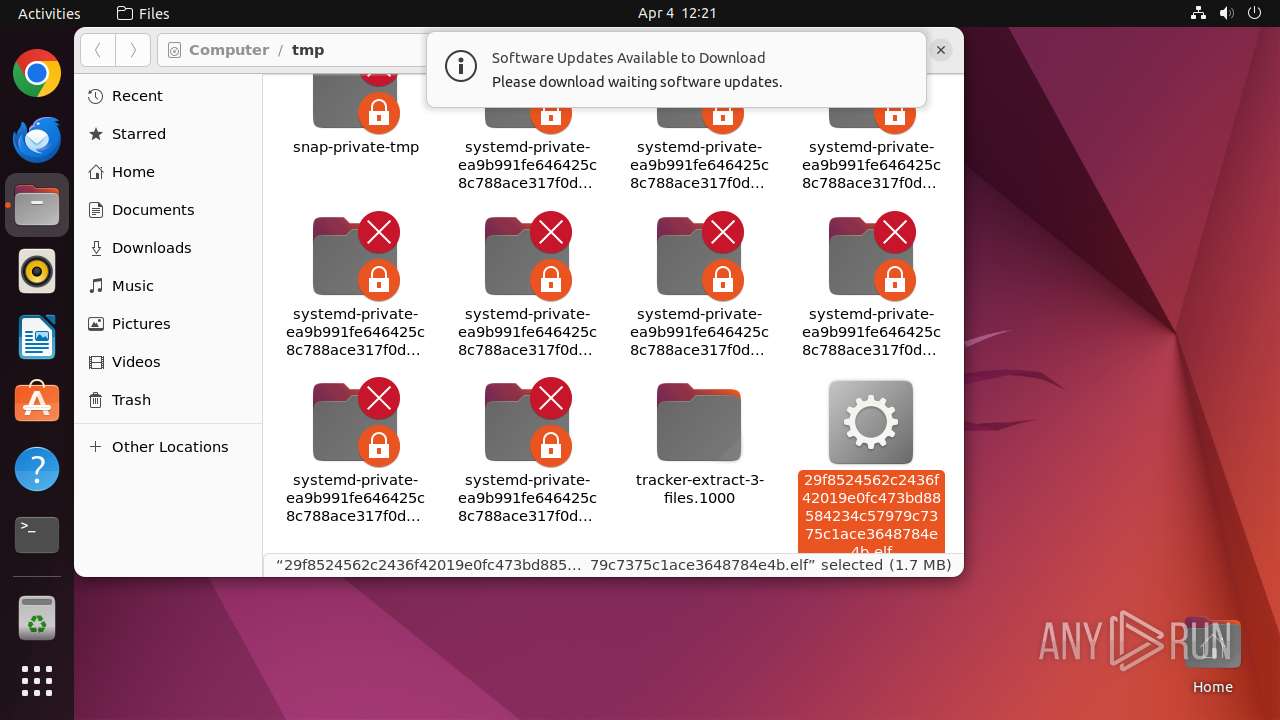
MALICIOUS
MINER has been detected (SURICATA)
- 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf (PID: 39557)
Connects to the CnC server
- 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf (PID: 39557)
SUSPICIOUS
Reads /proc/mounts (likely used to find writable filesystems)
- 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf (PID: 39556)
Reads passwd file
- crontab (PID: 39560)
- 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf (PID: 39557)
- crontab (PID: 39562)
Reads profile file
- nautilus (PID: 39489)
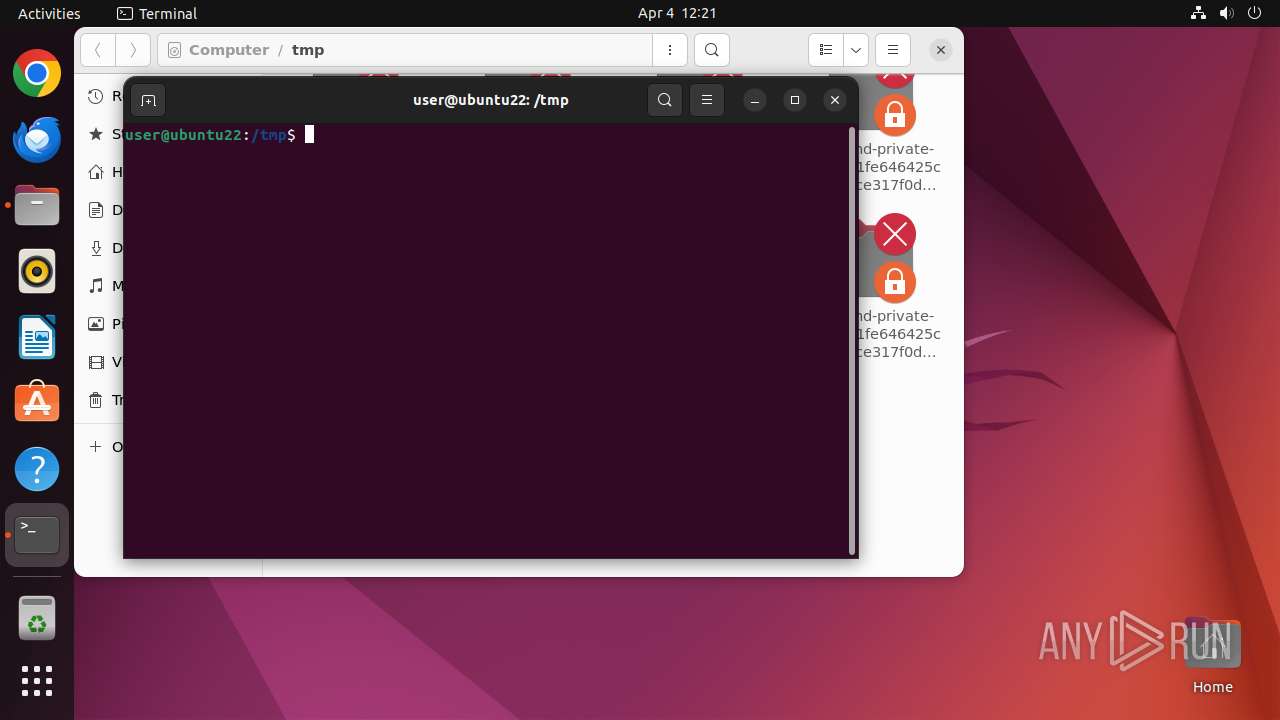
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 39532)
- sudo (PID: 39488)
Checks DMI information (probably VM detection)
- 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf (PID: 39556)
- udevadm (PID: 39576)
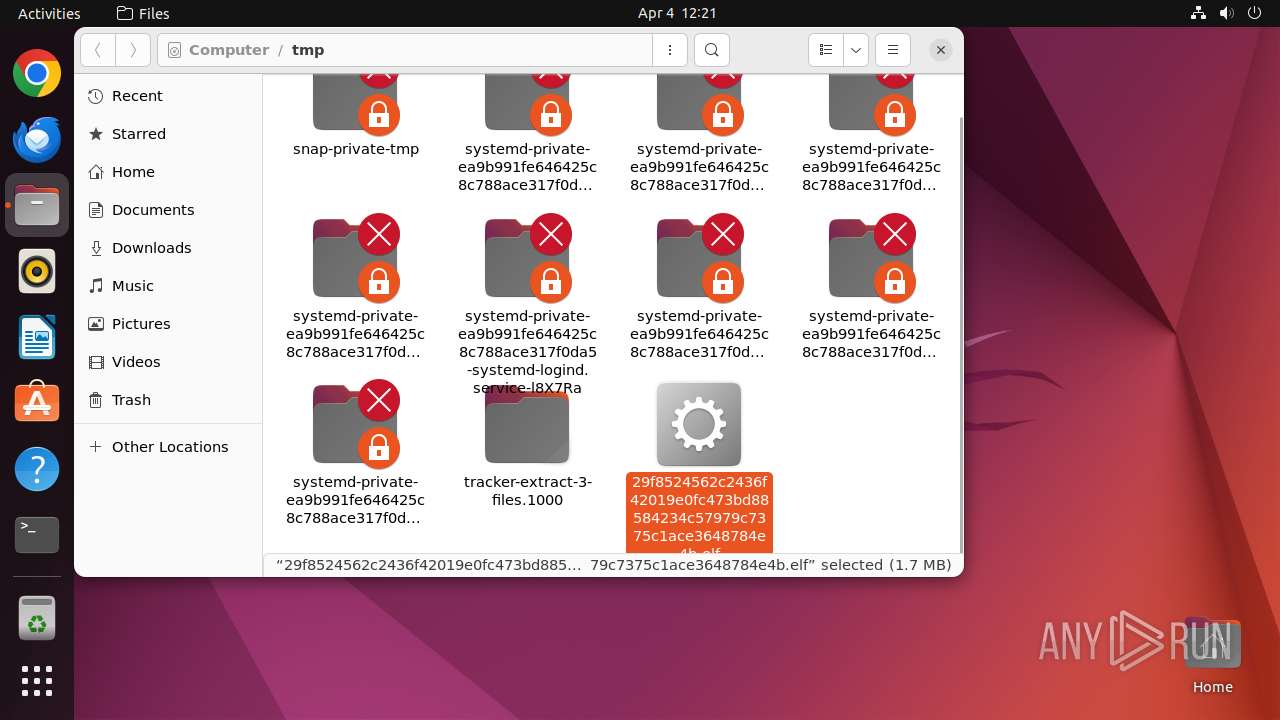
Modifies Cron jobs
- dash (PID: 39559)
Connects to unusual port
- 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf (PID: 39557)
Potential Corporate Privacy Violation
- 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf (PID: 39557)
Crypto Currency Mining Activity Detected
- 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf (PID: 39557)
INFO
Checks timezone
- crontab (PID: 39562)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (49.8) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Shared object file |
| CPUType: | AMD x86-64 |
Total processes
250
Monitored processes
32
Malicious processes
3
Suspicious processes
2
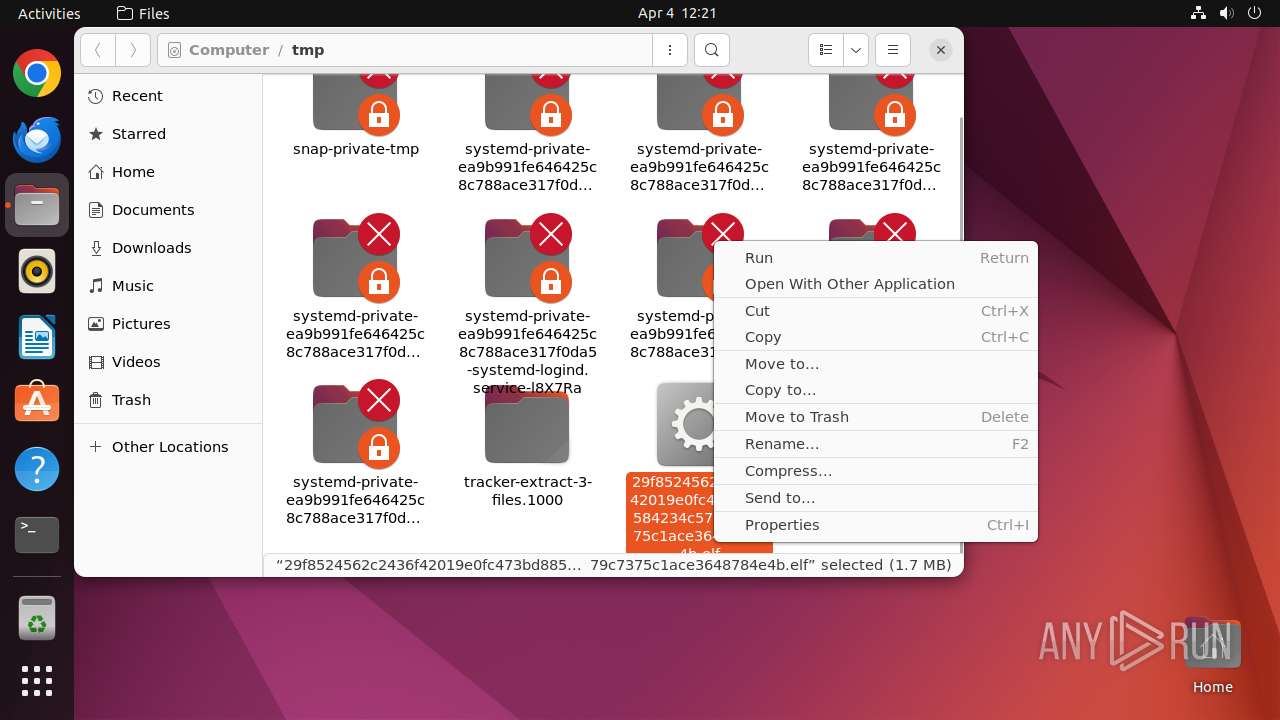
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
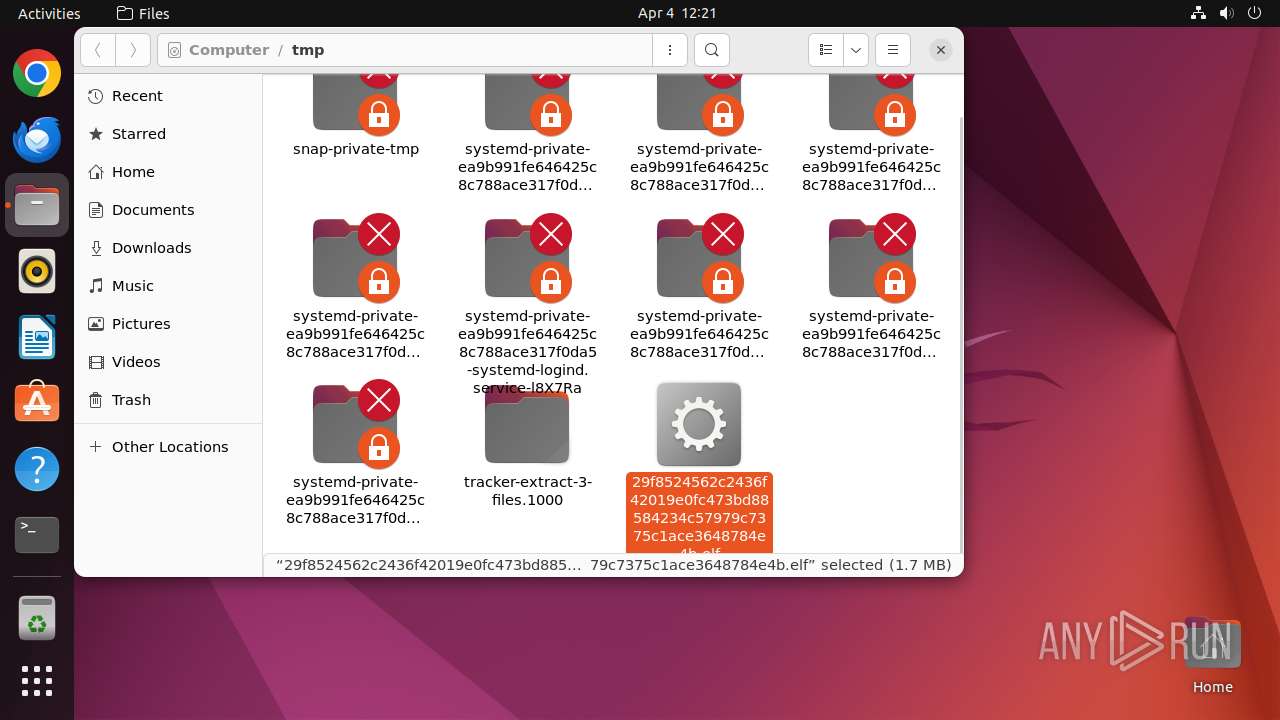
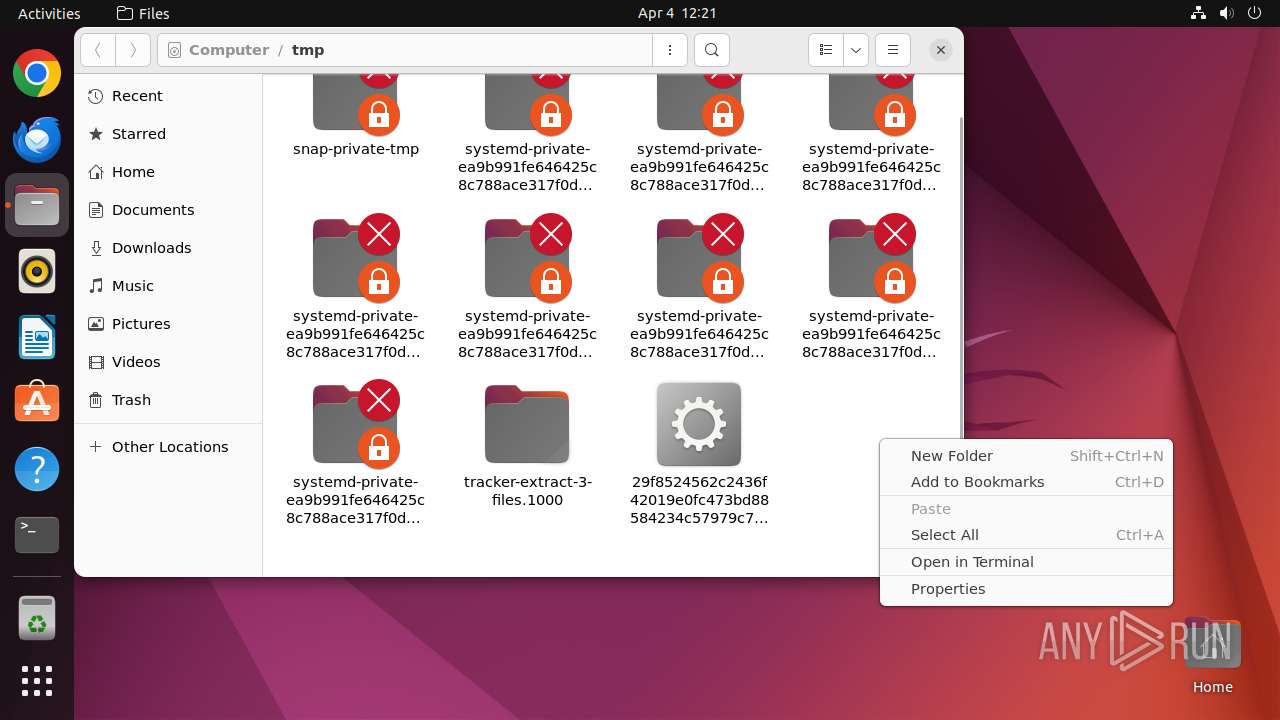
| 39487 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /tmp/29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b\.elf " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 9 | ||||
| 39488 | sudo -iu user nautilus /tmp/29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 39489 | nautilus /tmp/29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 9 | ||||
| 39490 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39508 | /lib/systemd/systemd-hostnamed | /usr/lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39511 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39516 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39518 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39532 | /usr/libexec/gnome-terminal-server | /usr/libexec/gnome-terminal-server | — | systemd |
User: user Integrity Level: UNKNOWN | ||||
| 39550 | bash | /usr/bin/bash | — | gnome-terminal-server |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39489 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | binary | |
MD5:— | SHA256:— | |||
| 39489 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm | binary | |
MD5:— | SHA256:— | |||
| 39562 | crontab | /var/spool/cron/crontabs/user | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
24
DNS requests
11
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.49:80 | — | Canonical Group Limited | GB | unknown |
— | — | 91.189.91.98:80 | — | Canonical Group Limited | US | unknown |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.96:80 | — | Canonical Group Limited | US | unknown |
— | — | 212.102.56.178:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
512 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | 51.158.108.203:853 | — | Online S.a.s. | FR | unknown |
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | 81.169.136.222:853 | — | Strato AG | DE | unknown |
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | 80.152.203.134:853 | — | Deutsche Telekom AG | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
6.100.168.192.in-addr.arpa |
| unknown |
x.2137gang.pl |
| unknown |
connectivity-check.ubuntu.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 344 |
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 211 |
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 38 |
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | Crypto Currency Mining Activity Detected | MINER [ANY.RUN] CoinMiner Agent CnC Initial Connection |
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
39557 | 29f8524562c2436f42019e0fc473bd88584234c57979c7375c1ace3648784e4b.elf | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |