| File name: | tungtungtungsahur.exe |
| Full analysis: | https://app.any.run/tasks/23706160-7708-40b3-9be0-936b5f6e0c55 |
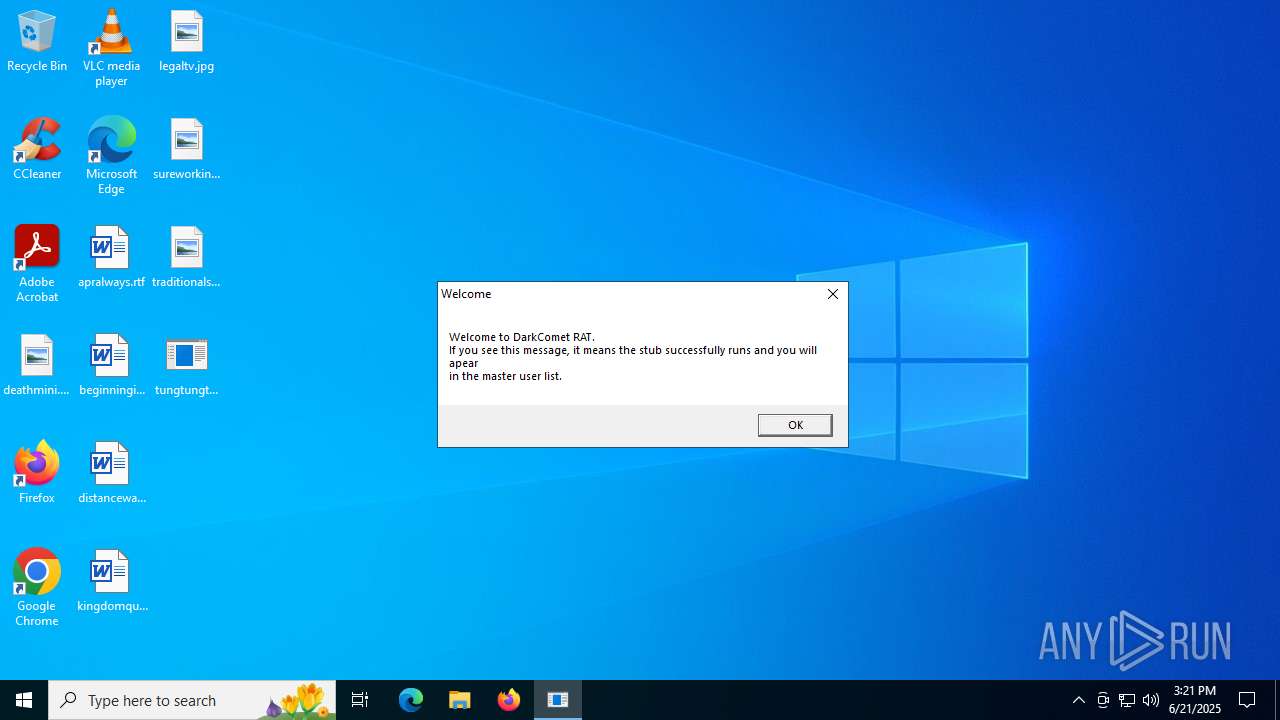
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | June 21, 2025, 15:21:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 9 sections |
| MD5: | 76E81931AE95D596646D9AE9D45B8C0C |
| SHA1: | D2FB26E3F321A26F159928F893E37EA533FB506C |
| SHA256: | 29CDE9F0B2B6F728DE46A83121A4A9470E992EC8804B821D1076E9B8438CC78E |
| SSDEEP: | 12288:S6/k564R2MsyHJGfN02XWDvQi4vGbN5Io1dxdffGslkqLznILa:S6/l4R2MsypGj9GH3ffGWkml |
MALICIOUS
Changes the login/logoff helper path in the registry
- tungtungtungsahur.exe (PID: 6852)
Changes the autorun value in the registry
- tungtungtungsahur.exe (PID: 6852)
DARKCOMET mutex has been found
- msdcsc.exe (PID: 5528)
- notepad.exe (PID: 5060)
- msdcsc.exe (PID: 6424)
Changes Security Center notification settings
- msdcsc.exe (PID: 5528)
- msdcsc.exe (PID: 6424)
DARKCOMET has been detected (YARA)
- msdcsc.exe (PID: 5528)
SUSPICIOUS
Executable content was dropped or overwritten
- tungtungtungsahur.exe (PID: 6852)
Start notepad (likely ransomware note)
- msdcsc.exe (PID: 5528)
- tungtungtungsahur.exe (PID: 6852)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 188)
- cmd.exe (PID: 3048)
There is functionality for taking screenshot (YARA)
- msdcsc.exe (PID: 5528)
There is functionality for communication over UDP network (YARA)
- msdcsc.exe (PID: 5528)
Starts itself from another location
- tungtungtungsahur.exe (PID: 6852)
Starts CMD.EXE for commands execution
- tungtungtungsahur.exe (PID: 6852)
Reads security settings of Internet Explorer
- tungtungtungsahur.exe (PID: 6852)
INFO
Checks supported languages
- tungtungtungsahur.exe (PID: 6852)
- msdcsc.exe (PID: 5528)
- msdcsc.exe (PID: 6424)
The sample compiled with english language support
- tungtungtungsahur.exe (PID: 6852)
Reads the computer name
- tungtungtungsahur.exe (PID: 6852)
- msdcsc.exe (PID: 5528)
- msdcsc.exe (PID: 6424)
Launching a file from a Registry key
- tungtungtungsahur.exe (PID: 6852)
Manual execution by a user
- msdcsc.exe (PID: 5528)
Compiled with Borland Delphi (YARA)
- msdcsc.exe (PID: 5528)
Process checks computer location settings
- tungtungtungsahur.exe (PID: 6852)
Reads the software policy settings
- slui.exe (PID: 3620)
Checks proxy server information
- slui.exe (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:07 15:59:53+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 586752 |
| InitializedDataSize: | 87552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8f888 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Remote Service Application |
| CompanyName: | Microsoft Corp. |
| FileDescription: | Remote Service Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | MSRSAAPP |
| LegalCopyright: | Copyright (C) 1999 |
| OriginalFileName: | MSRSAAP.EXE |
| ProductName: | Remote Service Application |
| ProductVersion: | 4, 0, 0, 0 |
Total processes
142
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\Desktop" +s +h | C:\Windows\SysWOW64\cmd.exe | — | tungtungtungsahur.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3048 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\Desktop\tungtungtungsahur.exe" +s +h | C:\Windows\SysWOW64\cmd.exe | — | tungtungtungsahur.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3820 | attrib "C:\Users\admin\Desktop" +s +h | C:\Windows\SysWOW64\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3960 | attrib "C:\Users\admin\Desktop\tungtungtungsahur.exe" +s +h | C:\Windows\SysWOW64\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5060 | notepad | C:\Windows\SysWOW64\notepad.exe | msdcsc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5528 | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 6408 | notepad | C:\Windows\SysWOW64\notepad.exe | — | tungtungtungsahur.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 48889856 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6424 | "C:\Users\admin\Documents\MSDCSC\msdcsc.exe" | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | tungtungtungsahur.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
5 034
Read events
5 020
Write events
14
Delete events
0
Modification events
| (PID) Process: | (6852) tungtungtungsahur.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicroUpdate |
Value: C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (6852) tungtungtungsahur.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | UserInit |
Value: C:\Windows\system32\userinit.exe,C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (5528) msdcsc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies |
| Operation: | write | Name: | NoControlPanel |
Value: 1 | |||
| (PID) Process: | (5528) msdcsc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (5528) msdcsc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 1 | |||
| (PID) Process: | (5528) msdcsc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (5528) msdcsc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusDisableNotify |
Value: 1 | |||
| (PID) Process: | (5528) msdcsc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesDisableNotify |
Value: 1 | |||
| (PID) Process: | (6424) msdcsc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (6424) msdcsc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6852 | tungtungtungsahur.exe | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | executable | |
MD5:76E81931AE95D596646D9AE9D45B8C0C | SHA256:29CDE9F0B2B6F728DE46A83121A4A9470E992EC8804B821D1076E9B8438CC78E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
77
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2028 | RUXIMICS.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2028 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2028 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2028 | RUXIMICS.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |