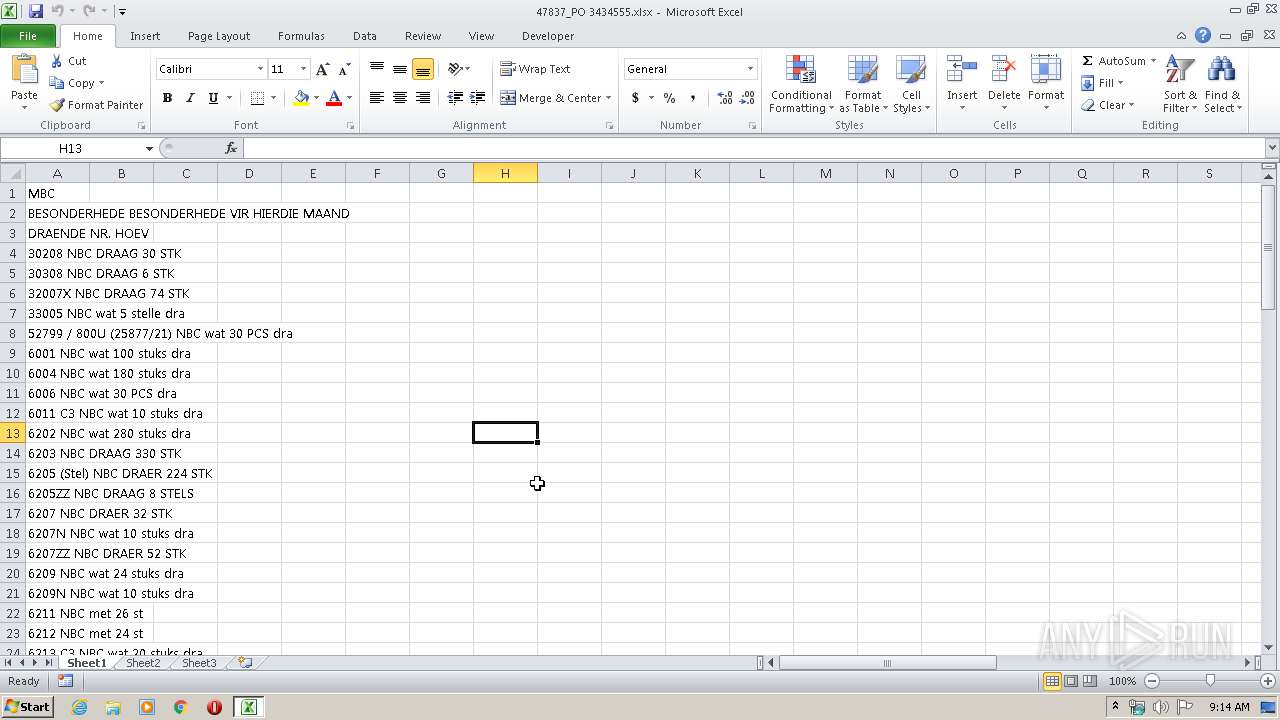
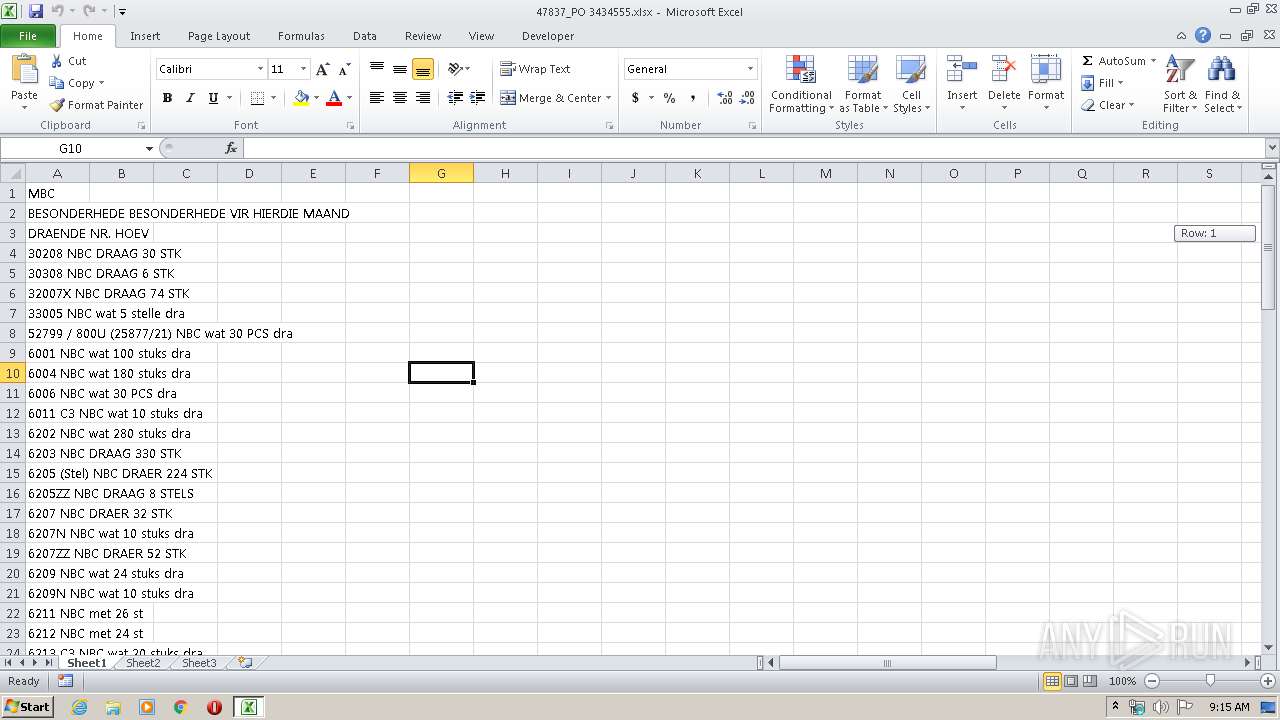
| File name: | 47837_PO 3434555.xlsx |
| Full analysis: | https://app.any.run/tasks/38c136f0-a4a5-4b34-9878-0598c343e5cf |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | March 31, 2020, 08:14:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 4783735BEDBB544C9CB47F837DFD2B99 |
| SHA1: | 2657D7030E0C5E7B9A516AA66EB20DE658472D3F |
| SHA256: | 29A75735E418508D7898026A11207F16DC8077BE25215366E97F38B5D487171E |
| SSDEEP: | 3072:86g7NHJFu2+IjGUMRPUEBvSQkjsPhqgFh/rZMmu0Ht4:FUHJI2+fUMRPUS3ZqgFbMmuet4 |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 1852)
Connects to CnC server
- explorer.exe (PID: 372)
Application was dropped or rewritten from another process
- uzmod035865.exe (PID: 1828)
- uzmod035865.exe (PID: 2952)
- 9rxd8fdj8-.exe (PID: 332)
- 9rxd8fdj8-.exe (PID: 1092)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 1852)
FORMBOOK was detected
- explorer.exe (PID: 372)
- audiodg.exe (PID: 3212)
- Firefox.exe (PID: 2392)
Changes the autorun value in the registry
- audiodg.exe (PID: 3212)
Actions looks like stealing of personal data
- audiodg.exe (PID: 3212)
Stealing of credential data
- audiodg.exe (PID: 3212)
SUSPICIOUS
Creates files in the user directory
- EQNEDT32.EXE (PID: 1852)
- audiodg.exe (PID: 3212)
Reads Internet Cache Settings
- EQNEDT32.EXE (PID: 1852)
Executed via COM
- EQNEDT32.EXE (PID: 1852)
- DllHost.exe (PID: 3076)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 1852)
- explorer.exe (PID: 372)
- DllHost.exe (PID: 3076)
Loads DLL from Mozilla Firefox
- audiodg.exe (PID: 3212)
Starts CMD.EXE for commands execution
- audiodg.exe (PID: 3212)
Creates files in the program directory
- DllHost.exe (PID: 3076)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 372)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2544)
Reads the hosts file
- audiodg.exe (PID: 3212)
Manual execution by user
- audiodg.exe (PID: 3212)
Creates files in the user directory
- Firefox.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:03:30 10:02:18 |
| ZipCRC: | 0x52547938 |
| ZipCompressedSize: | 402 |
| ZipUncompressedSize: | 1777 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | Modexcomm |
|---|
XML
| LastModifiedBy: | Modexcomm |
|---|---|
| CreateDate: | 2019:11:27 09:20:57Z |
| ModifyDate: | 2019:11:27 09:22:47Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
Total processes
48
Monitored processes
12
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Btz28\9rxd8fdj8-.exe" | C:\Program Files\Btz28\9rxd8fdj8-.exe | — | 9rxd8fdj8-.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Btz28\9rxd8fdj8-.exe" | C:\Program Files\Btz28\9rxd8fdj8-.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1688 | /c del "C:\Users\admin\AppData\Roaming\uzmod035865.exe" | C:\Windows\System32\cmd.exe | — | audiodg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\AppData\Roaming\uzmod035865.exe" | C:\Users\admin\AppData\Roaming\uzmod035865.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | audiodg.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2664 | "C:\Windows\System32\dwm.exe" | C:\Windows\System32\dwm.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\AppData\Roaming\uzmod035865.exe" | C:\Users\admin\AppData\Roaming\uzmod035865.exe | — | uzmod035865.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
646
Read events
573
Write events
62
Delete events
11
Modification events
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | &70 |
Value: 26373000F0090000010000000000000000000000 | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2544) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
4
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2544 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B26.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1852 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\uzmod035865.exe | executable | |
MD5:— | SHA256:— | |||
| 1852 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\uzmod03[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | audiodg.exe | C:\Users\admin\AppData\Roaming\NP218825\NP2logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Btz28\9rxd8fdj8-.exe | executable | |
MD5:— | SHA256:— | |||
| 3076 | DllHost.exe | C:\Program Files\Btz28\9rxd8fdj8-.exe | executable | |
MD5:— | SHA256:— | |||
| 2392 | Firefox.exe | C:\Users\admin\AppData\Roaming\NP218825\NP2logrf.ini | binary | |
MD5:— | SHA256:— | |||
| 3212 | audiodg.exe | C:\Users\admin\AppData\Roaming\NP218825\NP2logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 3212 | audiodg.exe | C:\Users\admin\AppData\Roaming\NP218825\NP2logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
| 3212 | audiodg.exe | C:\Users\admin\AppData\Roaming\NP218825\NP2logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
19
DNS requests
13
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
372 | explorer.exe | GET | — | 50.63.202.35:80 | http://www.providencetowing.com/d003/?jdGtQt20=FgBT/q131xChL6IhbsfR+Zedo2diRKmnyhR4STL/rDvqPn+nOxguib+Vs3hmrptKTo2PfQ==&TT=Ehd07BMX&sql=1 | US | — | — | malicious |
372 | explorer.exe | GET | — | 208.91.197.27:80 | http://www.meanfarmer.net/d003/?jdGtQt20=D6+ZTEX+THh+q6BQmfoR7t2E6lQU+QMiuSDHfYK9KlWfI+hFAmTpPmbHf4V0xdB3/GJ6pg==&TT=Ehd07BMX&sql=1 | US | — | — | malicious |
372 | explorer.exe | GET | 404 | 162.213.250.169:80 | http://www.allixanes.com/d003/?jdGtQt20=7S9Xc3sGxChIxZv47fz6yx4BXxrlFim44XUaTCbUQmOWkxaecQNY09egkhs3Saz/yWZEAQ==&TT=Ehd07BMX | US | html | 328 b | malicious |
1852 | EQNEDT32.EXE | GET | 200 | 162.214.75.129:80 | http://sylvaclouds.eu/uzmod03/uzmod03.exe | US | executable | 712 Kb | whitelisted |
372 | explorer.exe | POST | — | 50.63.202.35:80 | http://www.providencetowing.com/d003/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 50.63.202.35:80 | http://www.providencetowing.com/d003/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 50.63.202.35:80 | http://www.providencetowing.com/d003/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 208.91.197.27:80 | http://www.meanfarmer.net/d003/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 199.34.228.146:80 | http://www.tommymccarthycomedy.com/d003/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 92.43.218.161:80 | http://www.jedomproperties.com/d003/ | CH | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1852 | EQNEDT32.EXE | 162.214.75.129:80 | sylvaclouds.eu | Unified Layer | US | malicious |
372 | explorer.exe | 209.99.40.222:80 | www.usinamontealegre.com | Confluence Networks Inc | US | malicious |
372 | explorer.exe | 162.213.250.169:80 | www.allixanes.com | Namecheap, Inc. | US | malicious |
372 | explorer.exe | 208.91.197.27:80 | www.meanfarmer.net | Confluence Networks Inc | US | malicious |
372 | explorer.exe | 50.63.202.35:80 | www.providencetowing.com | GoDaddy.com, LLC | US | malicious |
372 | explorer.exe | 199.34.228.146:80 | www.tommymccarthycomedy.com | Weebly, Inc. | US | malicious |
372 | explorer.exe | 92.43.218.161:80 | www.jedomproperties.com | Webland AG | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sylvaclouds.eu |
| whitelisted |
www.usinamontealegre.com |
| malicious |
dns.msftncsi.com |
| shared |
www.0310100.com |
| unknown |
www.allixanes.com |
| malicious |
www.providencetowing.com |
| malicious |
www.meanfarmer.net |
| malicious |
www.fengxingyizhan.com |
| unknown |
www.tommymccarthycomedy.com |
| malicious |
www.ippuku.style |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1852 | EQNEDT32.EXE | A Network Trojan was detected | ET TROJAN Possible Malicious Macro DL EXE Feb 2016 |
1852 | EQNEDT32.EXE | A Network Trojan was detected | ET TROJAN Possible Malicious Macro EXE DL AlphaNumL |
1852 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
12 ETPRO signatures available at the full report