| File name: | Sample1.zip |
| Full analysis: | https://app.any.run/tasks/3d65522e-7653-4169-9d77-4a6351af037d |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | August 13, 2019, 13:25:03 |
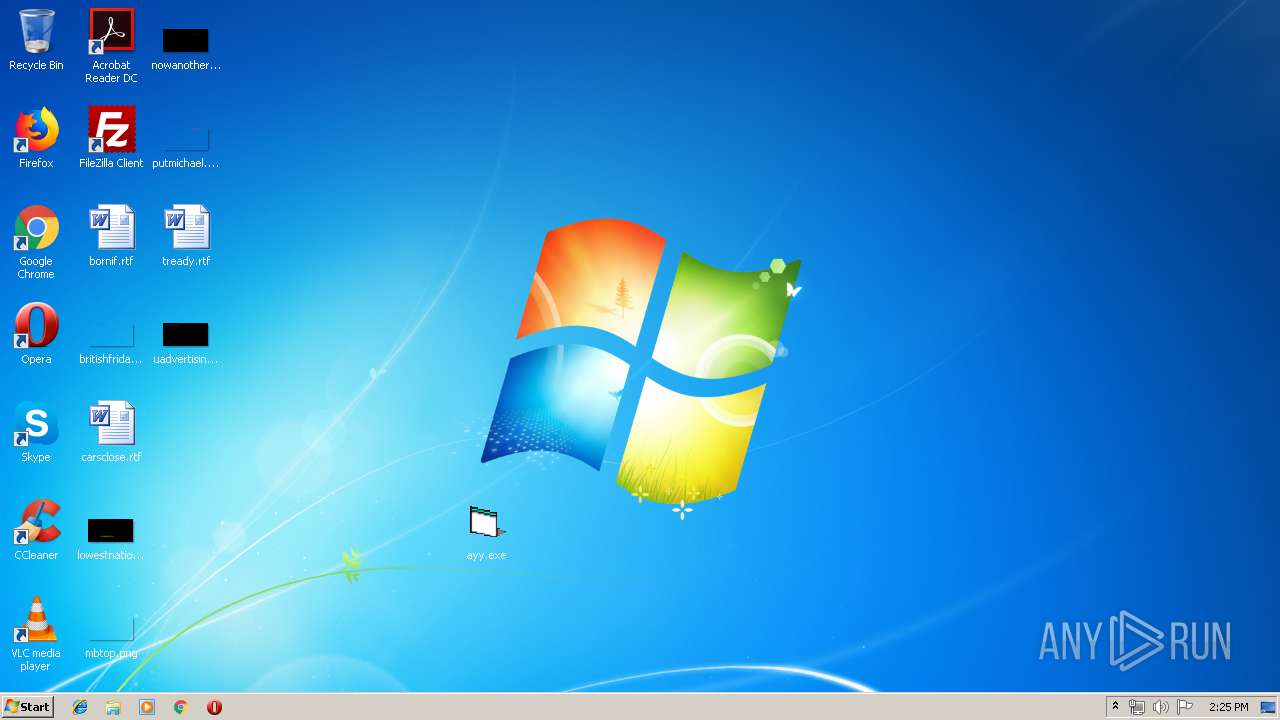
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
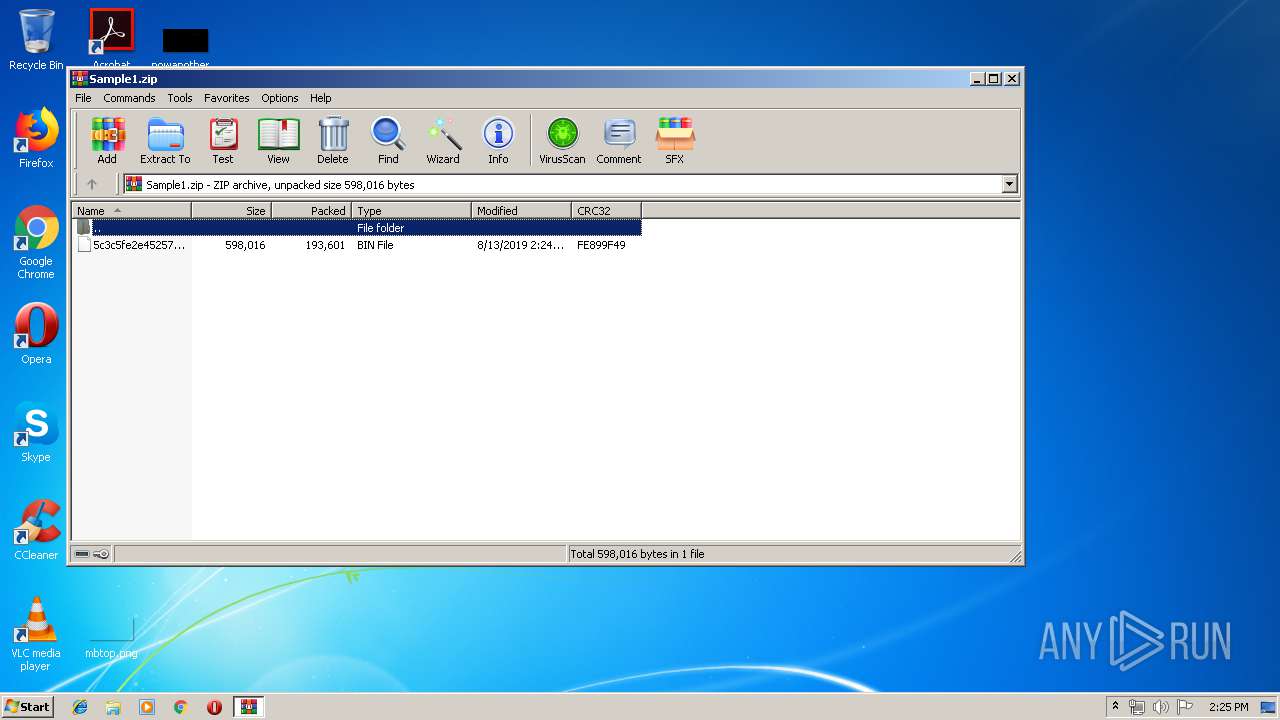
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 34FC60E24870CC6C2F61D75F9C7A83F2 |
| SHA1: | E8C0A565DAF1EB42AEE4477E19655C93F2239EBD |
| SHA256: | 291A41453681D5833D58C60A120A98744201A466A83F9F994E48CEF4C0C76197 |
| SSDEEP: | 3072:vYWXHU7NVDdN0qM/C3QCJmwcPFtE4CpxkrCNZjeQqzGFPCMO3W0slk6IxzCZe:vY5fdNbM/CACJ/SFtE4CpxkrCbjeh6FA |
MALICIOUS
Application was dropped or rewritten from another process
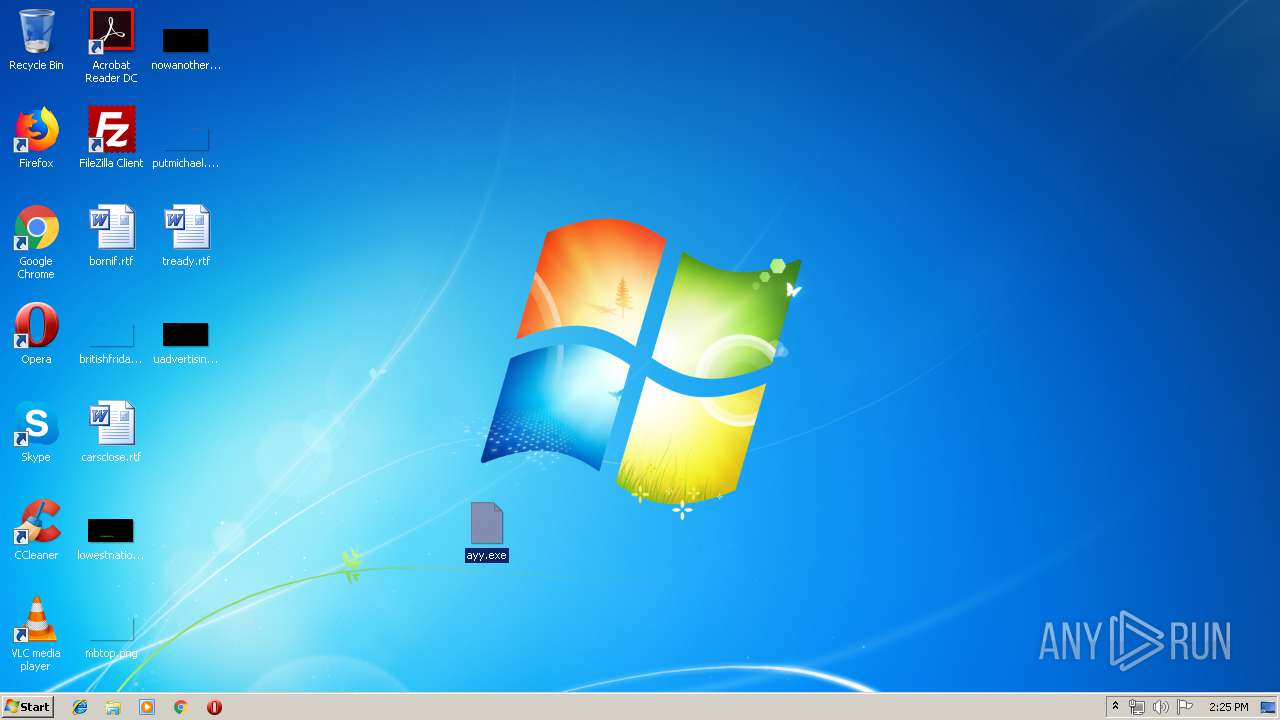
- ayy.exe (PID: 2312)
- ayy.exe (PID: 1212)
- ayy.exe (PID: 1996)
LOKIBOT was detected
- ayy.exe (PID: 1996)
Detected artifacts of LokiBot
- ayy.exe (PID: 1996)
Connects to CnC server
- ayy.exe (PID: 1996)
Actions looks like stealing of personal data
- ayy.exe (PID: 1996)
SUSPICIOUS
Application launched itself
- ayy.exe (PID: 2312)
- ayy.exe (PID: 1212)
Loads DLL from Mozilla Firefox
- ayy.exe (PID: 1996)
Executable content was dropped or overwritten
- ayy.exe (PID: 1996)
Creates files in the user directory
- ayy.exe (PID: 1996)
INFO
Manual execution by user
- ayy.exe (PID: 2312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:08:13 13:24:20 |
| ZipCRC: | 0xfe899f49 |
| ZipCompressedSize: | 193601 |
| ZipUncompressedSize: | 598016 |
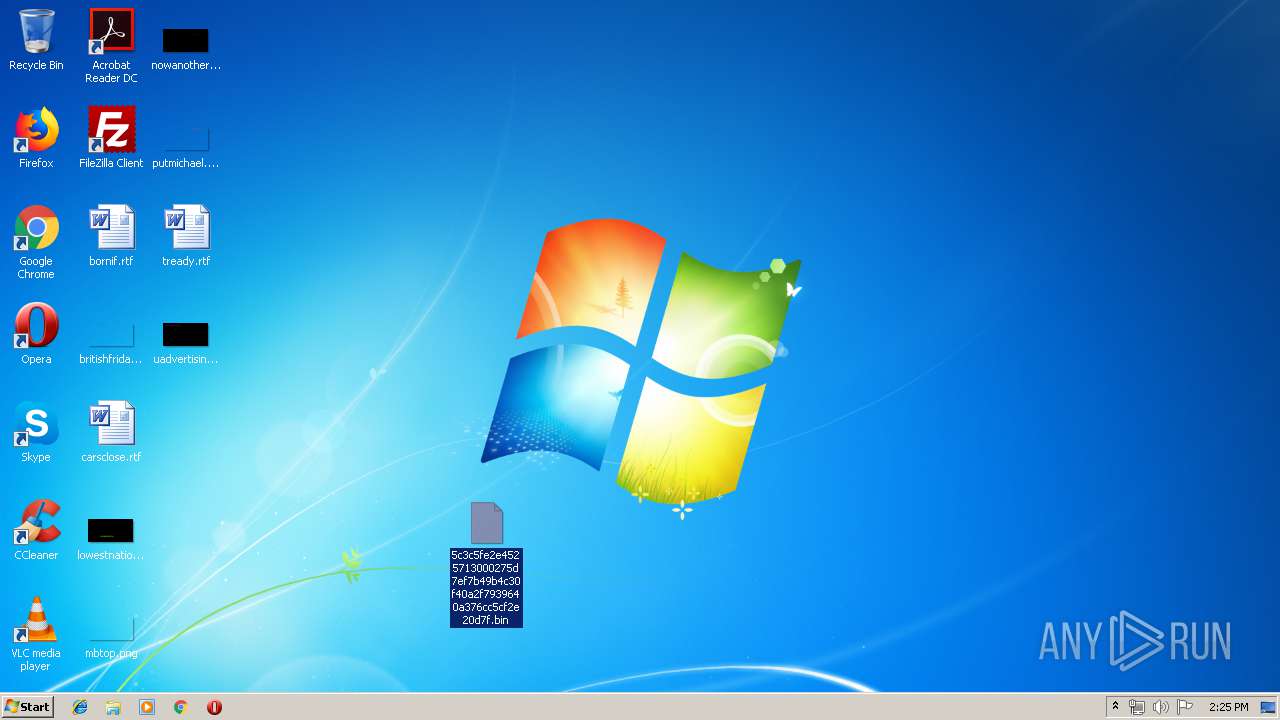
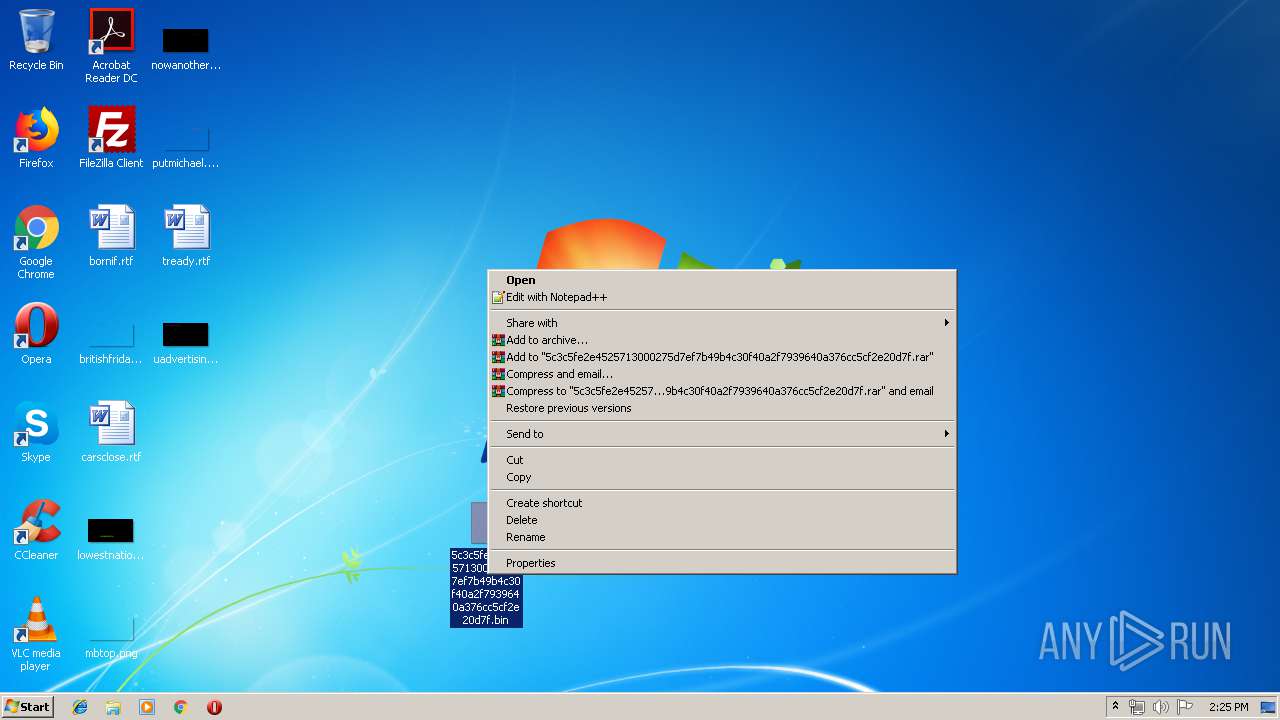
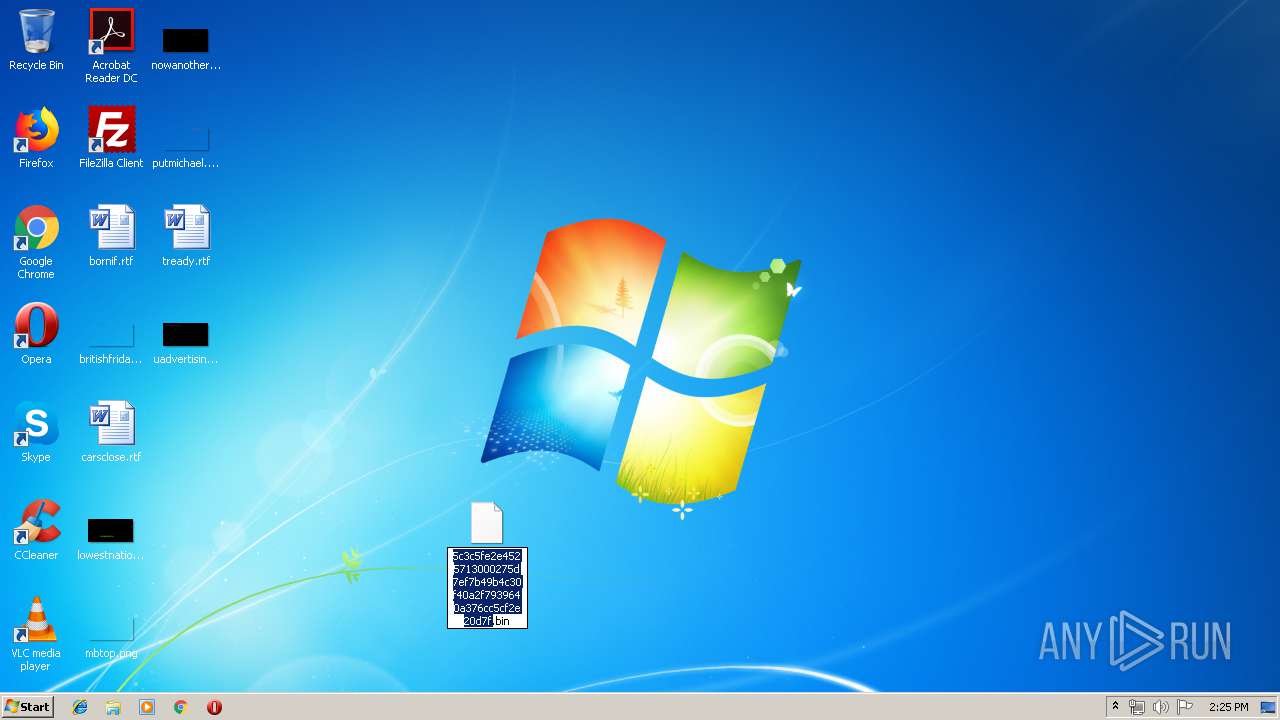
| ZipFileName: | 5c3c5fe2e4525713000275d7ef7b49b4c30f40a2f7939640a376cc5cf2e20d7f.bin |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1212 | "C:\Users\admin\Desktop\ayy.exe" | C:\Users\admin\Desktop\ayy.exe | — | ayy.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1996 | "C:\Users\admin\Desktop\ayy.exe" | C:\Users\admin\Desktop\ayy.exe | ayy.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\Desktop\ayy.exe" | C:\Users\admin\Desktop\ayy.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Sample1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
471
Read events
446
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sample1.zip | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
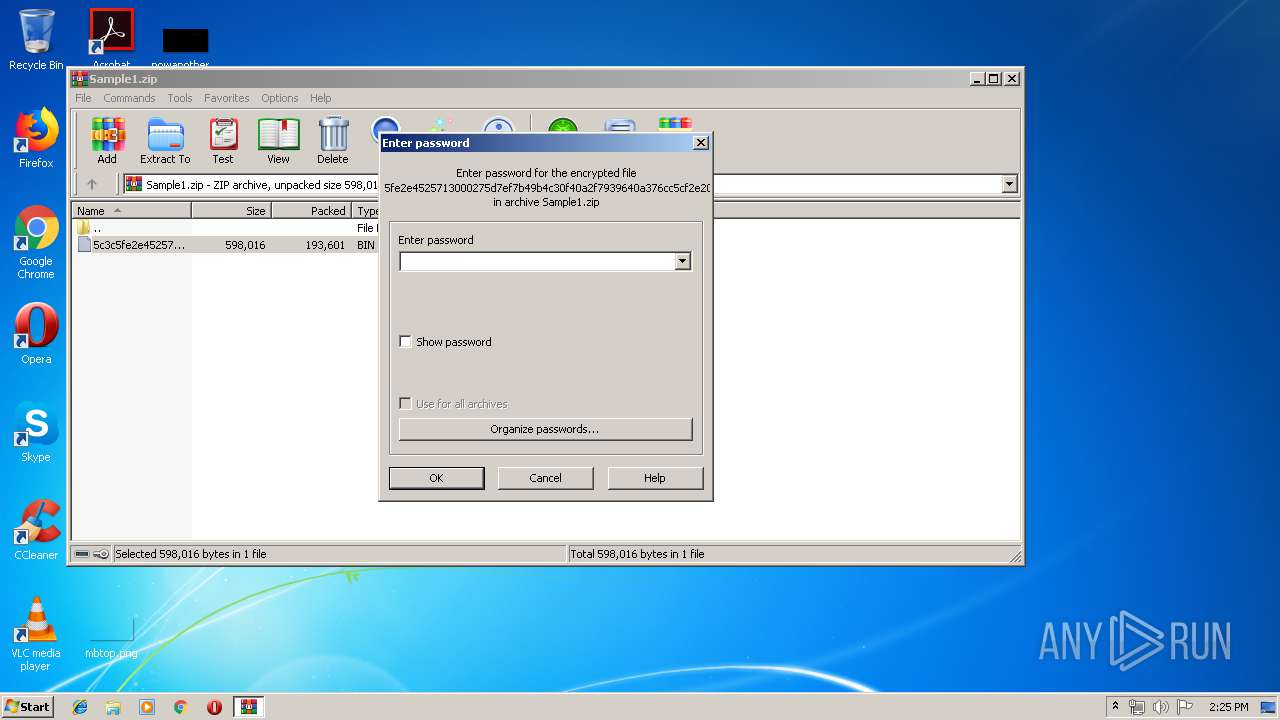
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1
Suspicious files
0
Text files
4
Unknown types
2
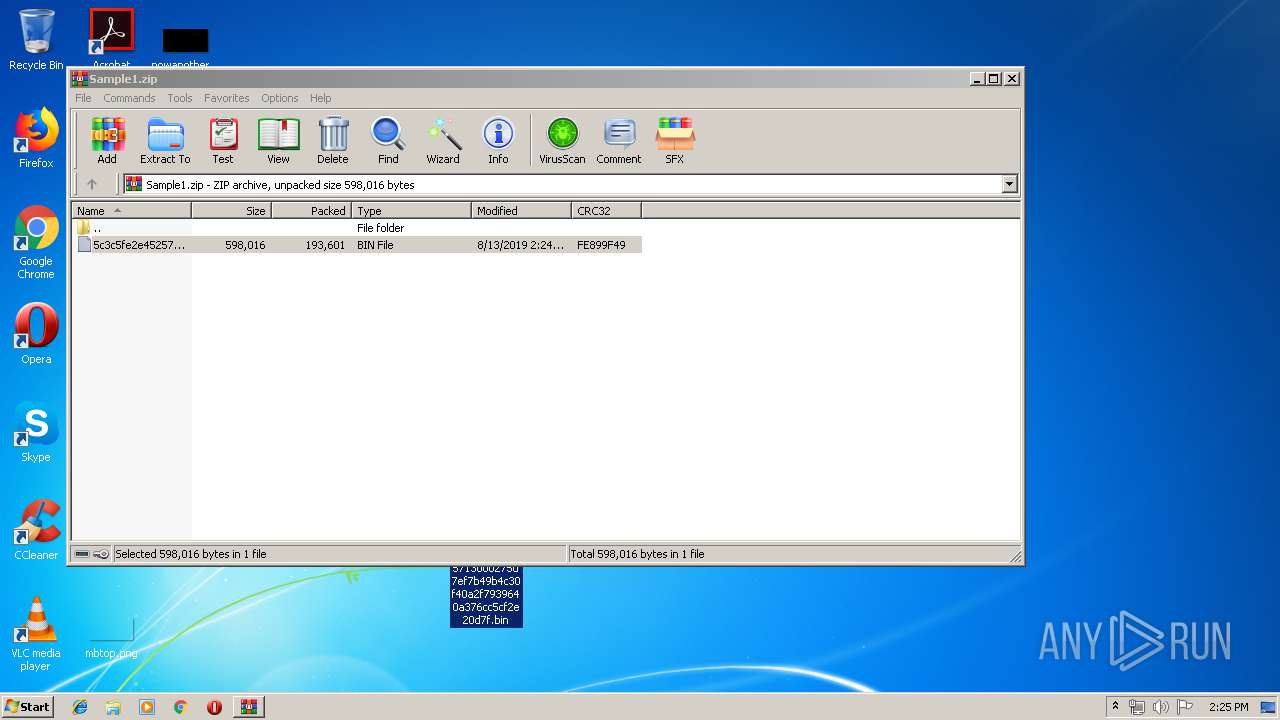
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2556.23008\5c3c5fe2e4525713000275d7ef7b49b4c30f40a2f7939640a376cc5cf2e20d7f.bin | — | |
MD5:— | SHA256:— | |||
| 1996 | ayy.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 1996 | ayy.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.hdb | text | |
MD5:— | SHA256:— | |||
| 1996 | ayy.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.exe | executable | |
MD5:— | SHA256:— | |||
| 2312 | ayy.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 1996 | ayy.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:18B8CFC0185C50383AAC0A4F30A9DAC8 | SHA256:913E8CED6A447FE791954D382ABA52D490513C5D2F689B391866C7E561F89A03 | |||
| 1212 | ayy.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
1
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1996 | ayy.exe | POST | — | 205.134.251.165:80 | http://chhaimaleresort.com.np/bag/five/fre.php | US | — | — | malicious |
1996 | ayy.exe | POST | — | 205.134.251.165:80 | http://chhaimaleresort.com.np/bag/five/fre.php | US | — | — | malicious |
1996 | ayy.exe | POST | — | 205.134.251.165:80 | http://chhaimaleresort.com.np/bag/five/fre.php | US | — | — | malicious |
1996 | ayy.exe | POST | — | 205.134.251.165:80 | http://chhaimaleresort.com.np/bag/five/fre.php | US | — | — | malicious |
1996 | ayy.exe | POST | — | 205.134.251.165:80 | http://chhaimaleresort.com.np/bag/five/fre.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1996 | ayy.exe | 205.134.251.165:80 | chhaimaleresort.com.np | InMotion Hosting, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chhaimaleresort.com.np |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1996 | ayy.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
1996 | ayy.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
1996 | ayy.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
1996 | ayy.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
1996 | ayy.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
1996 | ayy.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
1996 | ayy.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
1996 | ayy.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
1996 | ayy.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
1996 | ayy.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
5 ETPRO signatures available at the full report