| File name: | RFQ2610204.exe |
| Full analysis: | https://app.any.run/tasks/9d74034a-2493-4df5-a129-53905c6e10eb |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 01, 2023, 02:33:03 |
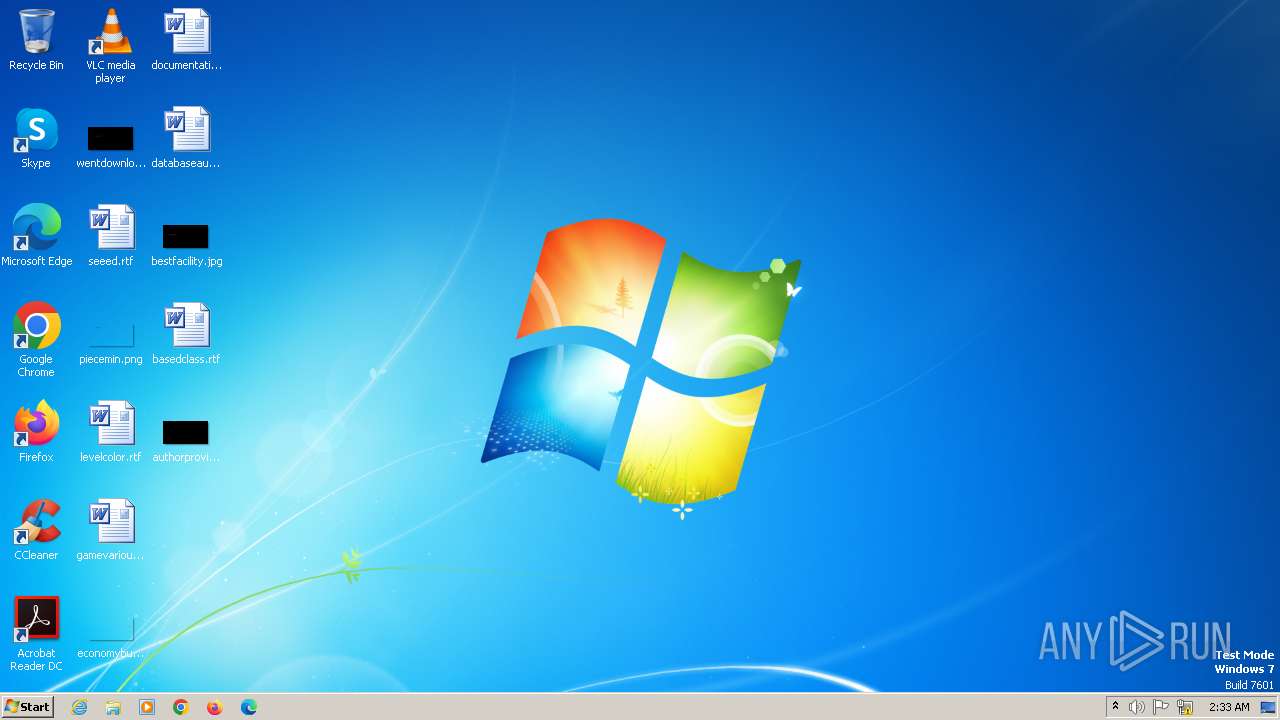
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 92A3BFC56047114BAF8E52D4C0A7DBE7 |
| SHA1: | B87AA007F7BAE56E8B34EBBCFC58D2FBBF0F25FE |
| SHA256: | 28F46D936DBF0C6A27993A483C00B6DBBE8A17F9751BE9B0EFB657D95B4D9400 |
| SSDEEP: | 98304:zm9yQmXXCplT/oqOVmAYvh1EYoSNXM31lCqVZJGoWrPCfOR4zNyVFX2aivO8l1xH:cc |
MALICIOUS
FORMBOOK has been detected (YARA)
- PATHPING.EXE (PID: 2380)
Connects to the CnC server
- explorer.exe (PID: 1944)
FORMBOOK has been detected (SURICATA)
- explorer.exe (PID: 1944)
Actions looks like stealing of personal data
- PATHPING.EXE (PID: 2380)
SUSPICIOUS
Reads the Internet Settings
- PATHPING.EXE (PID: 2380)
Process drops SQLite DLL files
- PATHPING.EXE (PID: 2380)
INFO
Checks supported languages
- RFQ2610204.exe (PID: 2672)
Reads the computer name
- RFQ2610204.exe (PID: 2672)
Reads the machine GUID from the registry
- RFQ2610204.exe (PID: 2672)
Manual execution by a user
- PATHPING.EXE (PID: 2380)
Checks proxy server information
- PATHPING.EXE (PID: 2380)
Create files in a temporary directory
- PATHPING.EXE (PID: 2380)
Creates files or folders in the user directory
- PATHPING.EXE (PID: 2380)
Drops the executable file immediately after the start
- PATHPING.EXE (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:30 19:00:36+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 1793948 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b7f96 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.74.213.30 |
| ProductVersionNumber: | 9.74.213.30 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | EGoKUi |
| FileDescription: | EaipU eYotOCUke eLEceREVOrI OQAm eEEpeQizema. |
| FileVersion: | 9.74.213.30 |
| InternalName: | EPeQOREo |
| LegalCopyright: | © 2023 EGoKUi. |
| OriginalFileName: | oAAKu |
| ProductName: | eJaJOnuR |
| ProductVersion: | 9.74.213.30 |
| Comments: | AAOEOKeu IruSOPUOai ADoFeJEvoP oKabeRIgaCa erIBiyI iGUuAHiwE areU. |
Total processes
35
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Windows\SYSWOW64\calc.exe" | C:\Windows\SysWOW64\calc.exe | — | RFQ2610204.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | PATHPING.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1944 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | "C:\Windows\SysWOW64\PATHPING.EXE" | C:\Windows\SysWOW64\PATHPING.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP PathPing Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\AppData\Local\Temp\RFQ2610204.exe" | C:\Users\admin\AppData\Local\Temp\RFQ2610204.exe | — | explorer.exe | |||||||||||
User: admin Company: EGoKUi Integrity Level: MEDIUM Description: EaipU eYotOCUke eLEceREVOrI OQAm eEEpeQizema. Exit code: 0 Version: 9.74.213.30 Modules
| |||||||||||||||
Total events
2 548
Read events
2 530
Write events
18
Delete events
0
Modification events
| (PID) Process: | (1944) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000088AF72B0747534094337F63DE35C94A000000000200000000001066000000010000200000003A7AE26404D75DF41C31FF40C5EA8CE90BAF74FA9E9BD7A9ACA34C7048350C1E000000000E8000000002000020000000BD2D56D46506C12C41A6A70B10E79EE53CB79EF36FD2BA8CDD2460CB8F4BE86A300000009B5D1418CBF2EB49F3C4BD4C21D58CA55B82FA3D3ED08AF0EF59D6C7ECAFC1055FA323A80FF7C154B1C9B60253392B6640000000DED9FDCC168073324C3013F1BB125E066EB1A2F09FD2C8E7CC7A793AA992E21EF1C942BF7294D04E036428704009B863B1CB981B97312E2530E3E816780CF7C9 | |||
| (PID) Process: | (2380) PATHPING.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2380) PATHPING.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2380) PATHPING.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2380) PATHPING.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2380) PATHPING.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2380) PATHPING.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2380) PATHPING.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2380) PATHPING.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000C1000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1944) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\156\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | PATHPING.EXE | C:\Users\admin\AppData\Local\Temp\vfit1b.zip | compressed | |
MD5:D71848944418C67F6EB230682F9A969A | SHA256:EFFF0464180FCB34EC33E7835086EA58ADC84BC3F0B08A7323EF1D58B258E59E | |||
| 2380 | PATHPING.EXE | C:\Users\admin\AppData\Local\Temp\sqlite3.dll | executable | |
MD5:87F9E5A6318AC1EC5EE05AA94A919D7A | SHA256:7705B87603E0D772E1753441001FCF1AC2643EE41BF14A8177DE2C056628665C | |||
| 2380 | PATHPING.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\K78MRVB5\sqlite-dll-win32-x86-3240000[1].zip | compressed | |
MD5:D71848944418C67F6EB230682F9A969A | SHA256:EFFF0464180FCB34EC33E7835086EA58ADC84BC3F0B08A7323EF1D58B258E59E | |||
| 2380 | PATHPING.EXE | C:\Users\admin\AppData\Local\Temp\31k67156 | binary | |
MD5:0F653EDF207BB943166A7EED331F14AD | SHA256:E4D518E335DF25562B0570F4F3FC6F39BF63F7D84805AECD485C5798671EA3D8 | |||
| 2380 | PATHPING.EXE | C:\Users\admin\AppData\Local\Temp\sqlite3.def | text | |
MD5:DF728FE35F4E5FE7A1DBFB2BC8C99972 | SHA256:82064FB9C414C8A50F090C6E8F9D17269B3F9B1B35E9EFE78C70ADBCB31929FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
22
DNS requests
4
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2380 | PATHPING.EXE | GET | 404 | 45.33.6.223:80 | http://www.sqlite.org/2016/sqlite-dll-win32-x86-3120000.zip | unknown | — | — | unknown |
2380 | PATHPING.EXE | GET | 200 | 45.33.6.223:80 | http://www.sqlite.org/2018/sqlite-dll-win32-x86-3240000.zip | unknown | compressed | 444 Kb | unknown |
1944 | explorer.exe | GET | 404 | 81.88.63.46:80 | http://www.schonbutter.com/8hbu/?zKGPv9z=k6PqWjfZ2TBXbNZy2eTjSpKKHwNEEaOkCBOE68ZOeGksEg+k9XEEIj5goUuK8/2Z6rScGLTitO6CpjzfEzh/Fp1MKTQk/N1bEiSXwxY=&qj_zl=DnwY3rzyELE | unknown | html | 203 b | unknown |
1944 | explorer.exe | POST | 405 | 91.195.240.19:80 | http://www.felizdiadamulher.com/8hbu/ | unknown | html | 154 b | unknown |
1944 | explorer.exe | POST | 405 | 91.195.240.19:80 | http://www.felizdiadamulher.com/8hbu/ | unknown | html | 154 b | unknown |
1944 | explorer.exe | POST | 405 | 91.195.240.19:80 | http://www.felizdiadamulher.com/8hbu/ | unknown | html | 154 b | unknown |
1944 | explorer.exe | POST | 405 | 91.195.240.19:80 | http://www.felizdiadamulher.com/8hbu/ | unknown | html | 154 b | unknown |
1944 | explorer.exe | POST | 405 | 91.195.240.19:80 | http://www.felizdiadamulher.com/8hbu/ | unknown | html | 154 b | unknown |
1944 | explorer.exe | GET | 200 | 91.195.240.19:80 | http://www.felizdiadamulher.com/8hbu/?zKGPv9z=tP74BpzBWZFxKKdw+sO4J59LmiFkU6CZ4uL300v5m0Jza2w0vib+Zyr/Oe2q/lydYdj5dwf5UbOVtIB9cs9ge2zne1zR2H1XjhWAOS0=&qj_zl=DnwY3rzyELE | unknown | html | 27.3 Kb | unknown |
1944 | explorer.exe | POST | 405 | 91.195.240.19:80 | http://www.felizdiadamulher.com/8hbu/ | unknown | html | 154 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1944 | explorer.exe | 81.88.63.46:80 | www.schonbutter.com | Register S.p.A. | IT | unknown |
2380 | PATHPING.EXE | 45.33.6.223:80 | www.sqlite.org | Linode, LLC | US | unknown |
1944 | explorer.exe | 91.195.240.19:80 | www.felizdiadamulher.com | SEDO GmbH | DE | unknown |
1944 | explorer.exe | 84.32.84.32:80 | www.victorviera.com | — | LT | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.schonbutter.com |
| unknown |
www.sqlite.org |
| whitelisted |
www.felizdiadamulher.com |
| unknown |
www.victorviera.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1944 | explorer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP header |
1944 | explorer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP header |
1944 | explorer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP header |
11 ETPRO signatures available at the full report