| File name: | SOA.pdf.bat |
| Full analysis: | https://app.any.run/tasks/5e26d1ac-17de-41c1-a596-0e3fcdebb56e |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | July 17, 2019, 14:54:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6EAB03997C07F74AA977917C0D8E038C |
| SHA1: | 84D1D2E6131F903F0B08FE4545DC746D64801F46 |
| SHA256: | 2866D79409E6B305539194B47B96F63E53F84C1CC74496E7083E009F9F11205E |
| SSDEEP: | 6144:OAufG3kHFAs8EHyThqRjnwPeiCQs9N9KBPLUeJcXPayPyM9zr6D:OnG3kHys5mqRjnwP3CQs9N0BDZal |
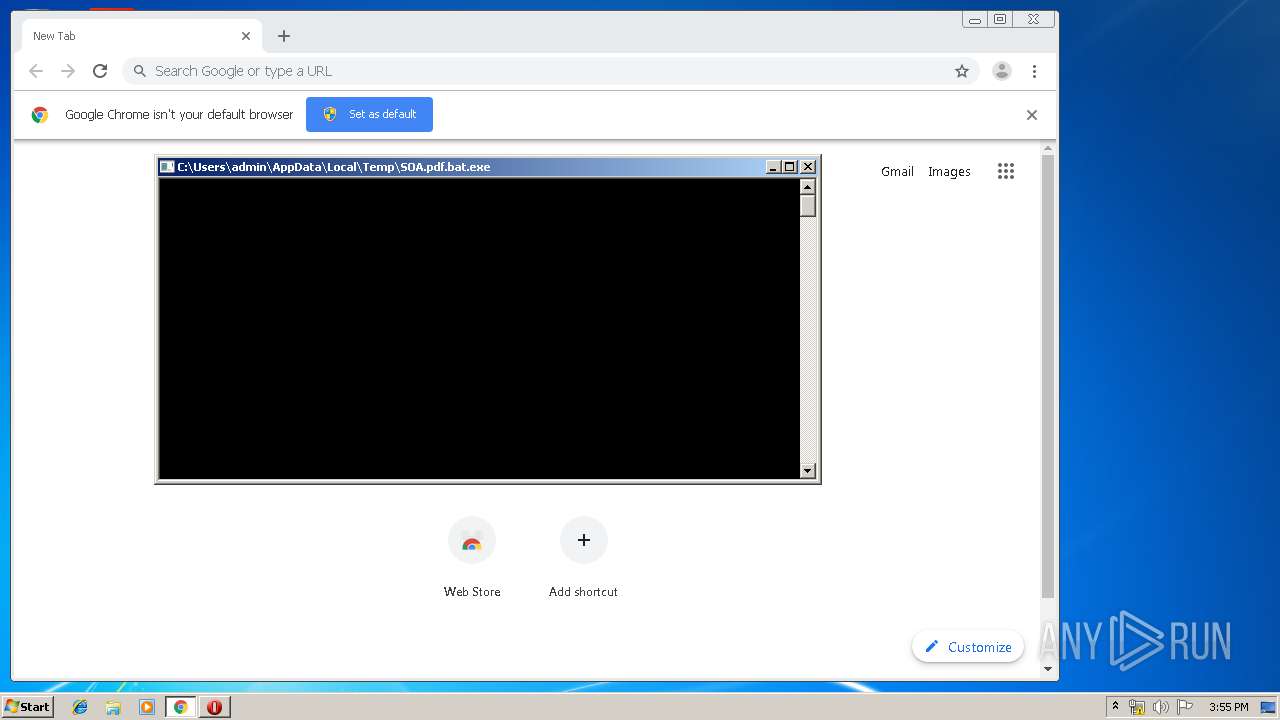
MALICIOUS
Changes the autorun value in the registry
- SOA.pdf.bat.exe (PID: 2600)
AGENTTESLA was detected
- SOA.pdf.bat.exe (PID: 2600)
Actions looks like stealing of personal data
- SOA.pdf.bat.exe (PID: 2600)
Changes settings of System certificates
- SOA.pdf.bat.exe (PID: 2600)
SUSPICIOUS
Application launched itself
- SOA.pdf.bat.exe (PID: 3784)
Creates files in the user directory
- SOA.pdf.bat.exe (PID: 2600)
Executable content was dropped or overwritten
- SOA.pdf.bat.exe (PID: 2600)
Uses REG.EXE to modify Windows registry
- SOA.pdf.bat.exe (PID: 2600)
Adds / modifies Windows certificates
- SOA.pdf.bat.exe (PID: 2600)
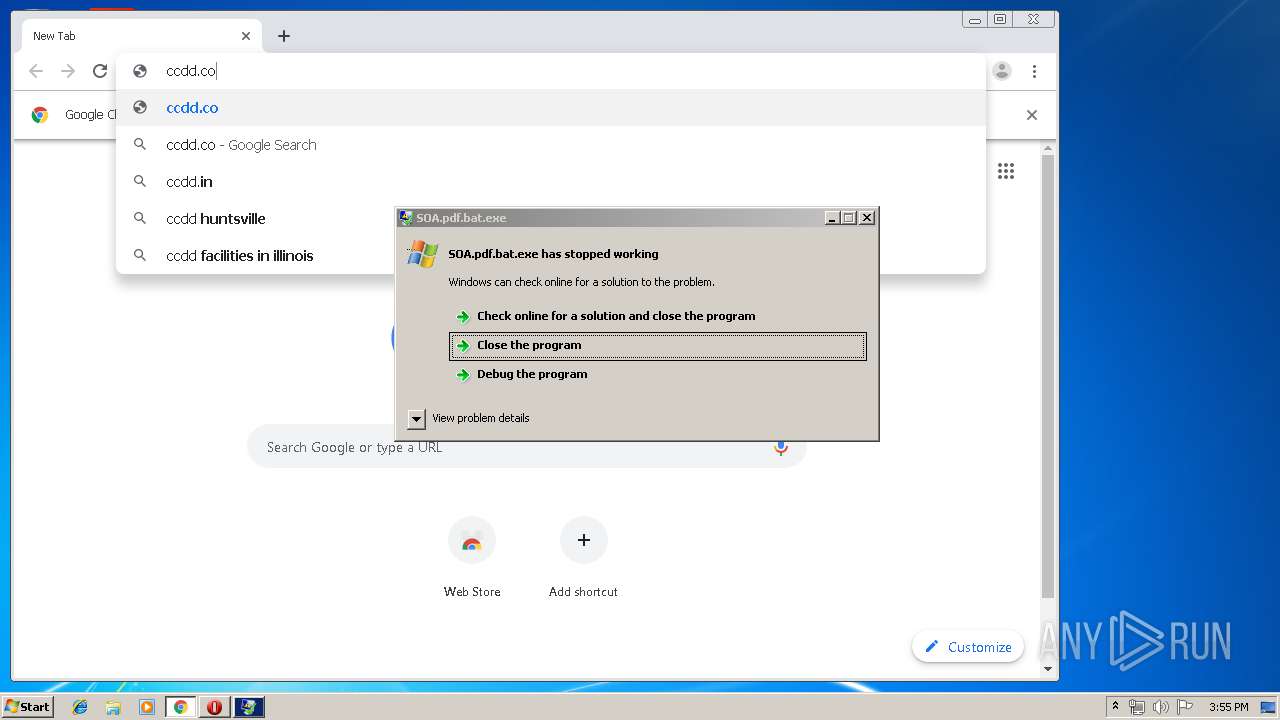
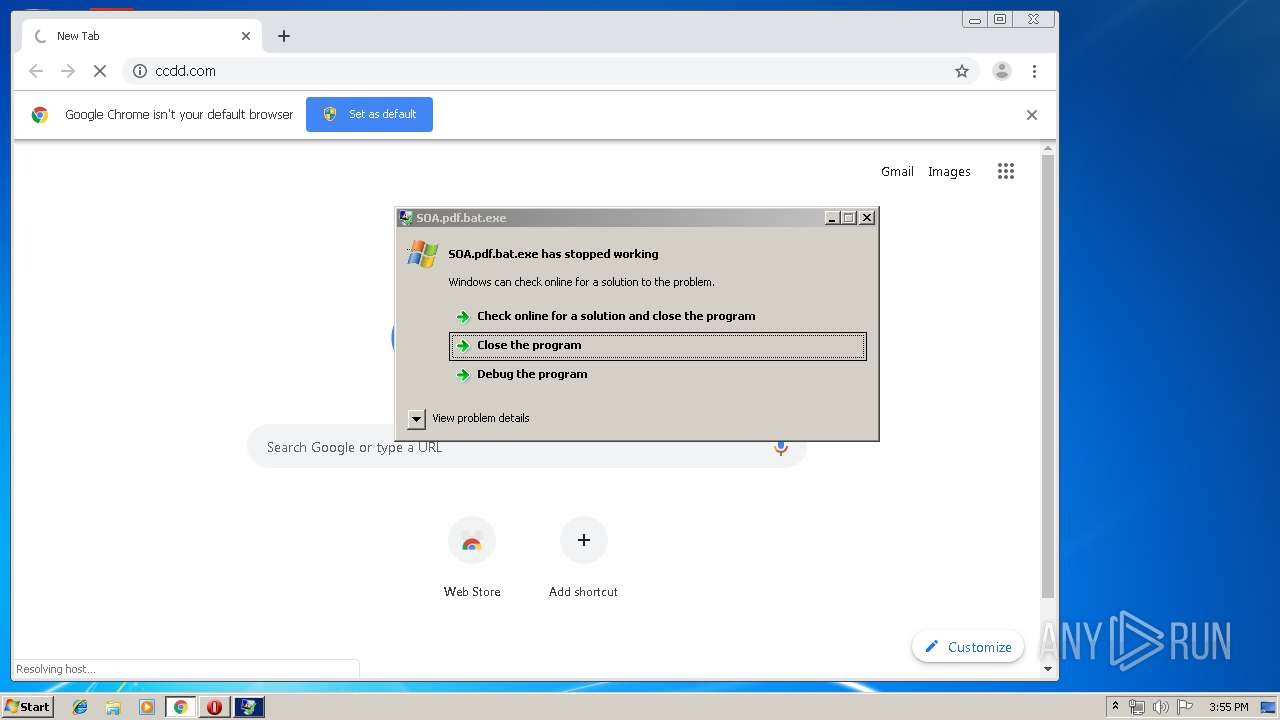
Modifies files in Chrome extension folder
- chrome.exe (PID: 3864)
INFO
Creates files in the user directory
- opera.exe (PID: 3792)
Application launched itself
- chrome.exe (PID: 3864)
Manual execution by user
- chrome.exe (PID: 3864)
- opera.exe (PID: 3792)
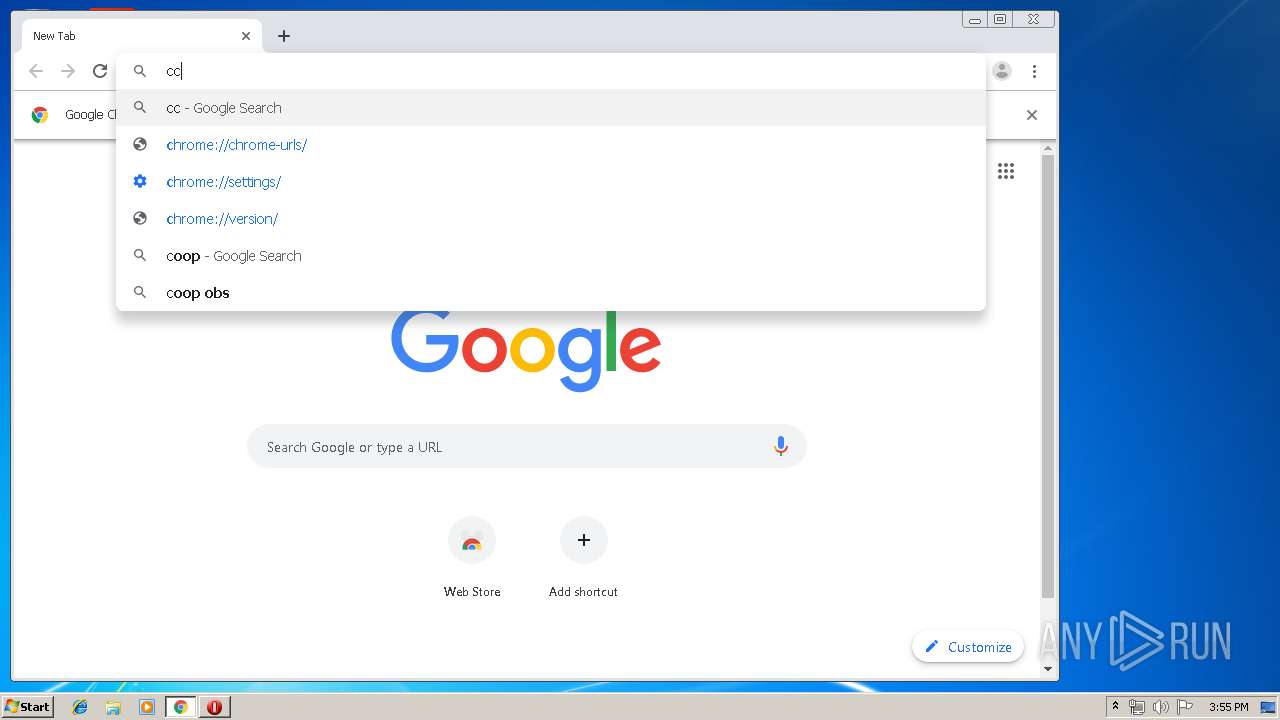
Application was crashed
- SOA.pdf.bat.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:08:05 13:45:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 491520 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11d0 |
| OSVersion: | 4 |
| ImageVersion: | 1.8 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.8.0.4 |
| ProductVersionNumber: | 1.8.0.4 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | FIVEPART10 |
| FileDescription: | Subpunctuation2 |
| ProductName: | Muisca1 |
| FileVersion: | 1.08.0004 |
| ProductVersion: | 1.08.0004 |
| InternalName: | TROUBLEMAKER2 |
| OriginalFileName: | TROUBLEMAKER2.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Aug-2010 11:45:43 |
| Detected languages: |
|
| CompanyName: | FIVEPART10 |
| FileDescription: | Subpunctuation2 |
| ProductName: | Muisca1 |
| FileVersion: | 1.08.0004 |
| ProductVersion: | 1.08.0004 |
| InternalName: | TROUBLEMAKER2 |
| OriginalFilename: | TROUBLEMAKER2.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-Aug-2010 11:45:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00077E94 | 0x00078000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.80835 |
.data | 0x00079000 | 0x00001550 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0007B000 | 0x00002D12 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.76 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.38524 | 640 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 4.94522 | 7336 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 4.9521 | 3240 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
66
Monitored processes
30
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3658747340089153625 --mojo-platform-channel-handle=3620 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9366019749458667784 --mojo-platform-channel-handle=3608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3427888333794985787 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18133479694826085835 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14203242186110562333 --mojo-platform-channel-handle=4048 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6288425048175604183 --mojo-platform-channel-handle=3336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17314658441961051459 --mojo-platform-channel-handle=3484 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10255317983053276543 --mojo-platform-channel-handle=3368 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6595292371593182606,7432573509825094099,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4078706299610238758 --mojo-platform-channel-handle=3588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ec4a9d0,0x6ec4a9e0,0x6ec4a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
489
Read events
355
Write events
129
Delete events
5
Modification events
| (PID) Process: | (3792) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3792) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3864-13207848891536500 |
Value: 259 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
1
Suspicious files
67
Text files
143
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4C76.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4CC5.tmp | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7cc05ebc-00a8-476a-87a4-27165fd122ef.tmp | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3792 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe4d60.TMP | text | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
71
DNS requests
32
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
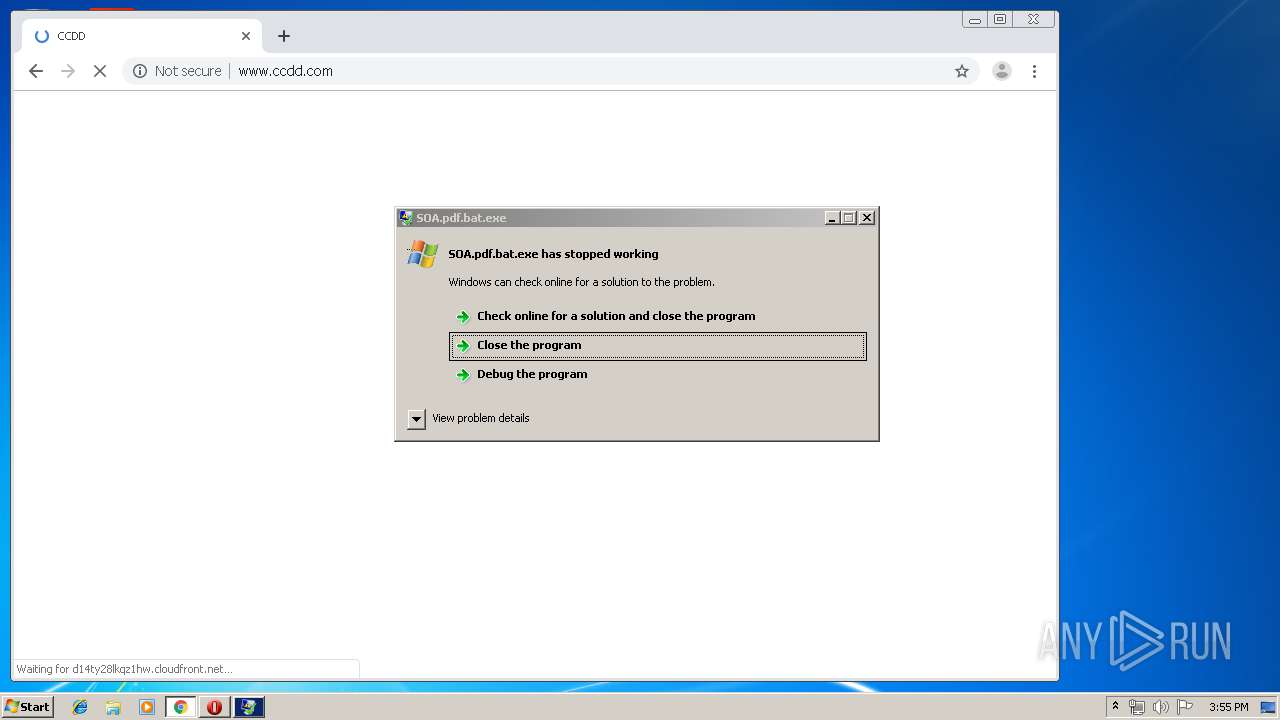
3216 | chrome.exe | GET | 200 | 13.250.27.157:80 | http://www.ccdd.com/ | SG | html | 6.19 Kb | malicious |
3216 | chrome.exe | GET | 301 | 198.61.166.45:80 | http://ccdd.com/ | US | html | 302 b | unknown |
3216 | chrome.exe | GET | 200 | 13.225.84.159:80 | http://d2wvwvig0d1mx7.cloudfront.net/static/min/core.min.css | US | text | 21.6 Kb | whitelisted |
3216 | chrome.exe | GET | 200 | 13.225.84.159:80 | http://d2wvwvig0d1mx7.cloudfront.net/static/min/core.min.js | US | text | 64.3 Kb | whitelisted |
3216 | chrome.exe | GET | 200 | 13.225.84.225:80 | http://d14ty28lkqz1hw.cloudfront.net/data/org/15139/theme/21066/css/easyResponsiveTabs.css | US | text | 898 b | malicious |
3216 | chrome.exe | GET | 200 | 13.225.84.225:80 | http://d14ty28lkqz1hw.cloudfront.net/data/org/15139/theme/21066/css/offcanvas.css | US | text | 770 b | malicious |
3216 | chrome.exe | GET | 200 | 13.225.84.225:80 | http://d14ty28lkqz1hw.cloudfront.net/data/org/15139/theme/21066/css/chosen.min.css | US | text | 2.21 Kb | malicious |
3216 | chrome.exe | GET | 200 | 13.225.84.225:80 | http://d14ty28lkqz1hw.cloudfront.net/data/org/15139/theme/21066/css/foundation.min.css | US | text | 11.7 Kb | malicious |
3216 | chrome.exe | GET | 200 | 13.225.84.225:80 | http://d14ty28lkqz1hw.cloudfront.net/data/org/15139/theme/21066/css/site.css | US | text | 10.5 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3792 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3216 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3216 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 172.217.16.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 216.58.207.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2600 | SOA.pdf.bat.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |