| File name: | Test.txt |
| Full analysis: | https://app.any.run/tasks/4d22c3f6-c68a-4a22-82a1-5a616b3b8639 |
| Verdict: | Malicious activity |
| Threats: | Latrodectus is a malicious loader that is used by threat actors to gain a foothold on compromised devices and deploy additional malware. It has been associated with the IcedID trojan and has been used by APT groups in targeted attacks. The malware can gather system information, launch executables, and detect sandbox environments. It uses encryption and obfuscation to evade detection and can establish persistence on the infected device. |
| Analysis date: | June 02, 2025, 17:08:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 074C047917B763AE5924D45FF49EB4A7 |
| SHA1: | A9846472B008843558B2EE98A2F797E034161C54 |
| SHA256: | 282503621EF8F9F9585D39FD6A5F3726CC8E06B50FF5BD3B852CBCBBA8FF42AB |
| SSDEEP: | 3:BOn:o |
MALICIOUS
LATRODECTUS mutex has been found
- rundll32.exe (PID: 3140)
- rundll32.exe (PID: 5176)
LATRODECTUS has been detected
- rundll32.exe (PID: 3140)
- rundll32.exe (PID: 5176)
SUSPICIOUS
Executable content was dropped or overwritten
- AutoIt3.exe (PID: 6368)
- rundll32.exe (PID: 3140)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 5720)
- rundll32.exe (PID: 3140)
Detected use of alternative data streams (AltDS)
- rundll32.exe (PID: 3140)
Application launched itself
- rundll32.exe (PID: 3140)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 7632)
- rundll32.exe (PID: 5176)
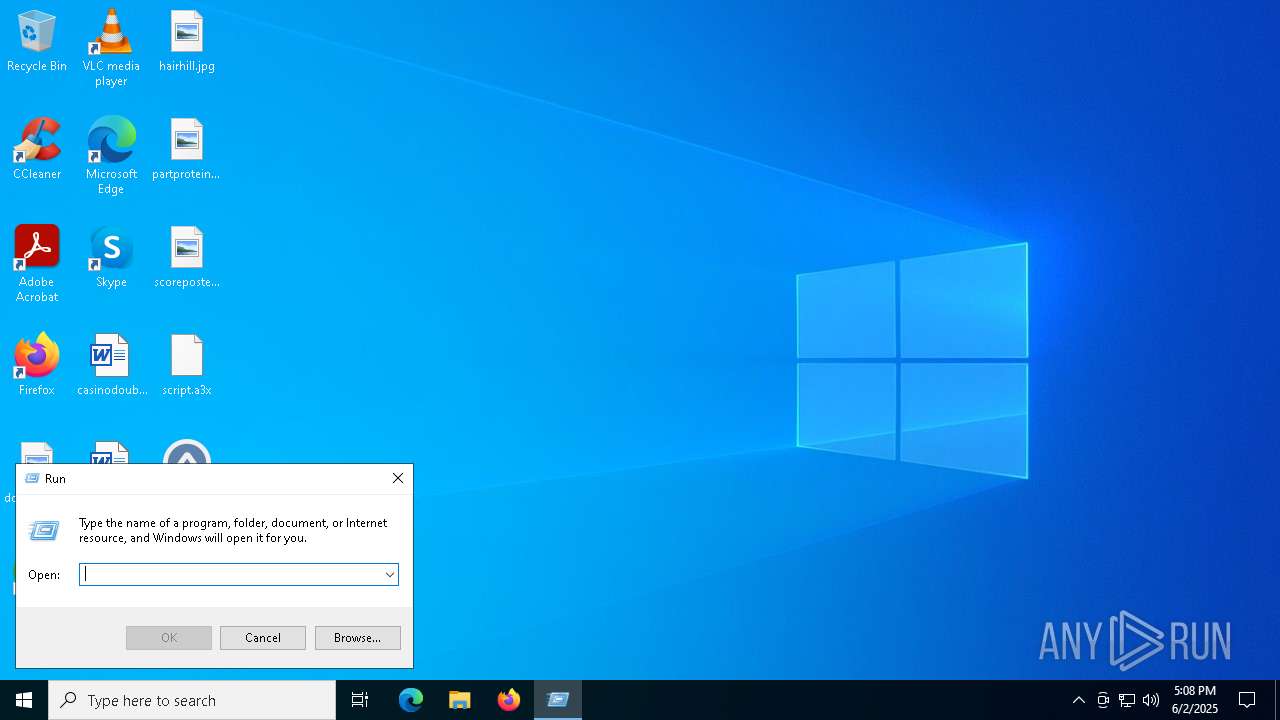
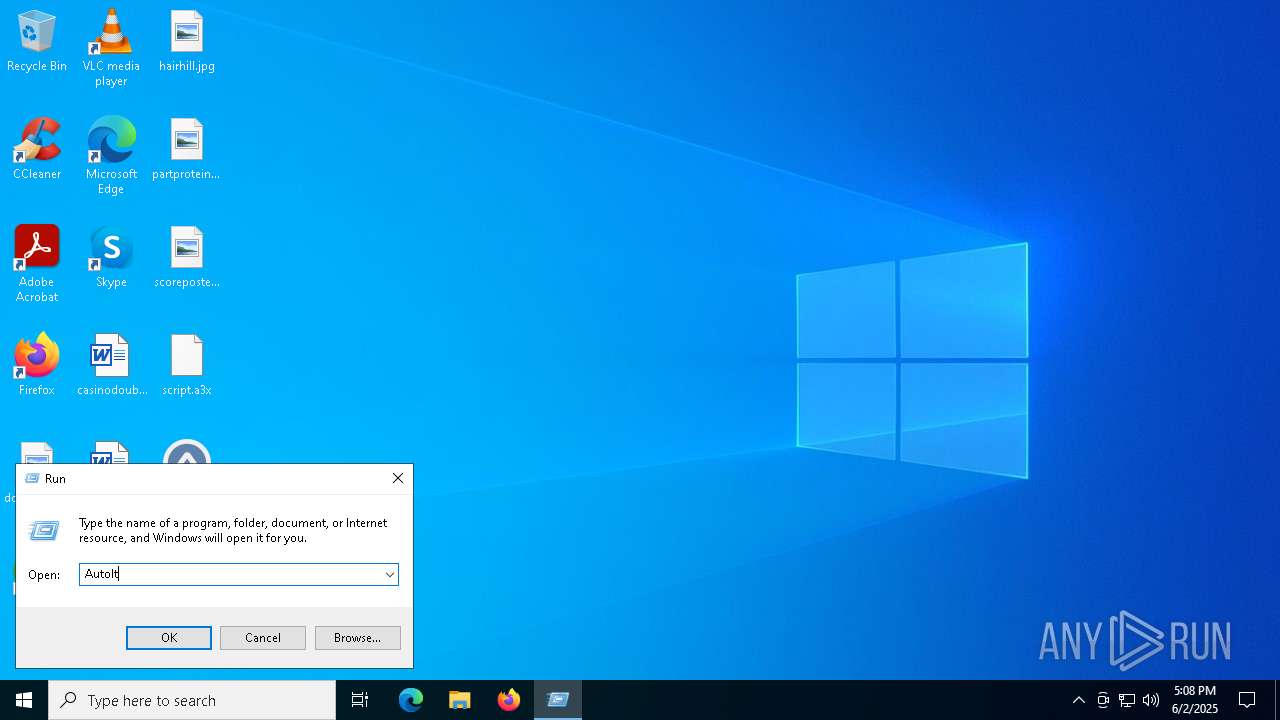
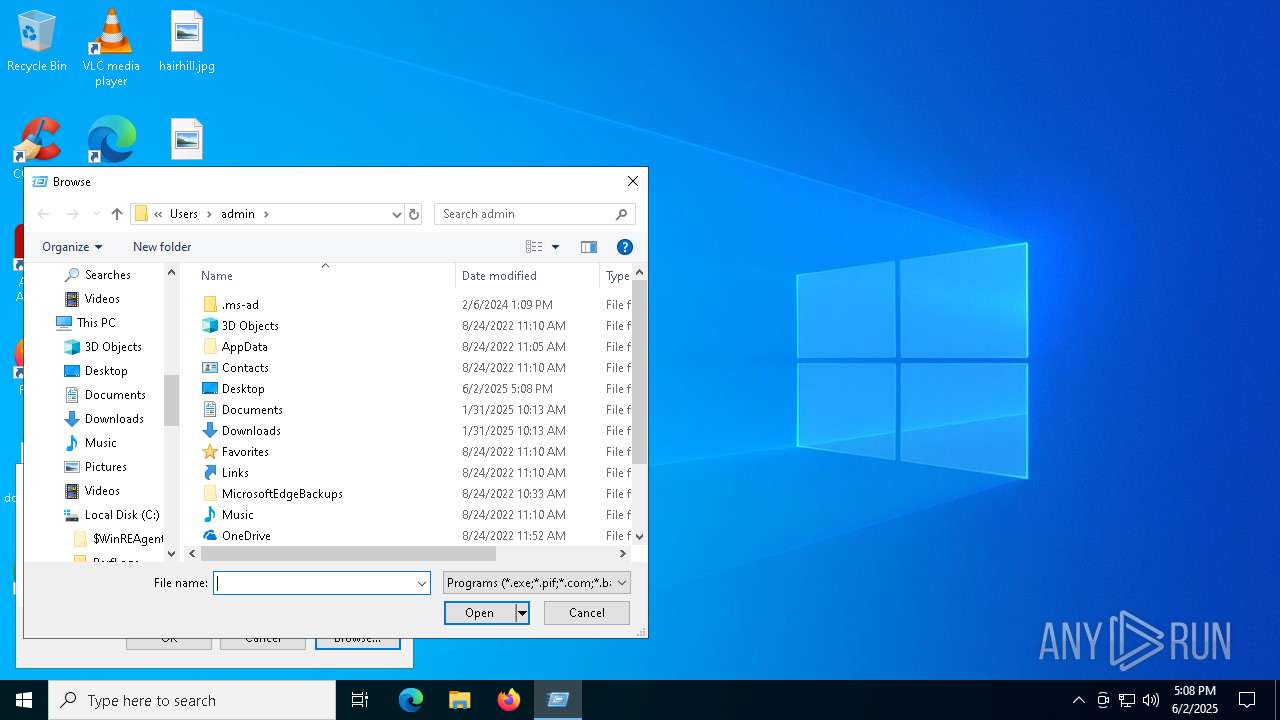
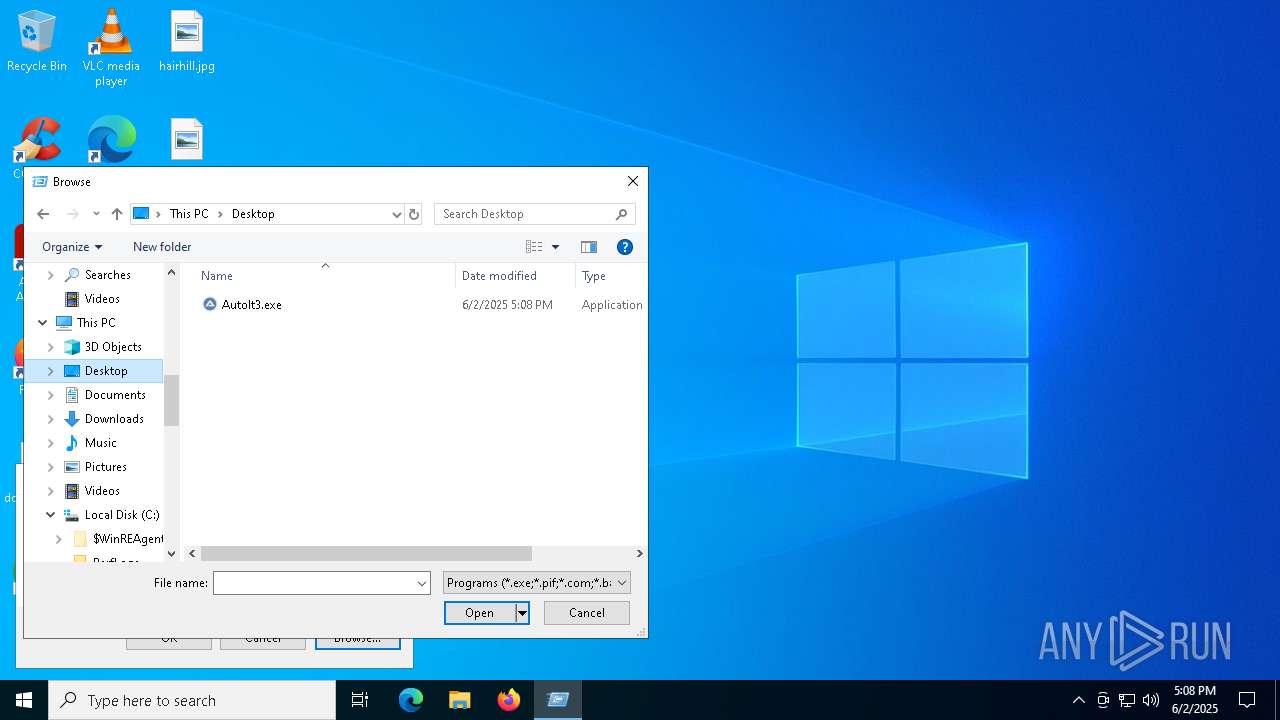
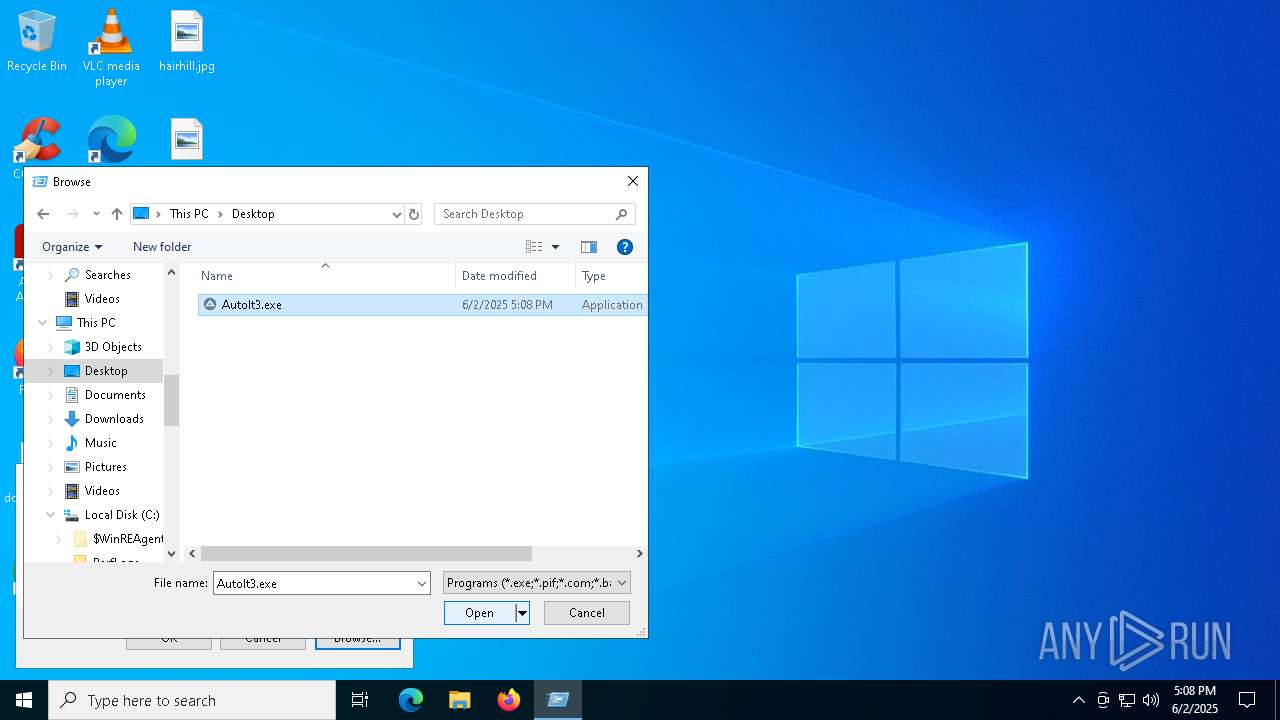
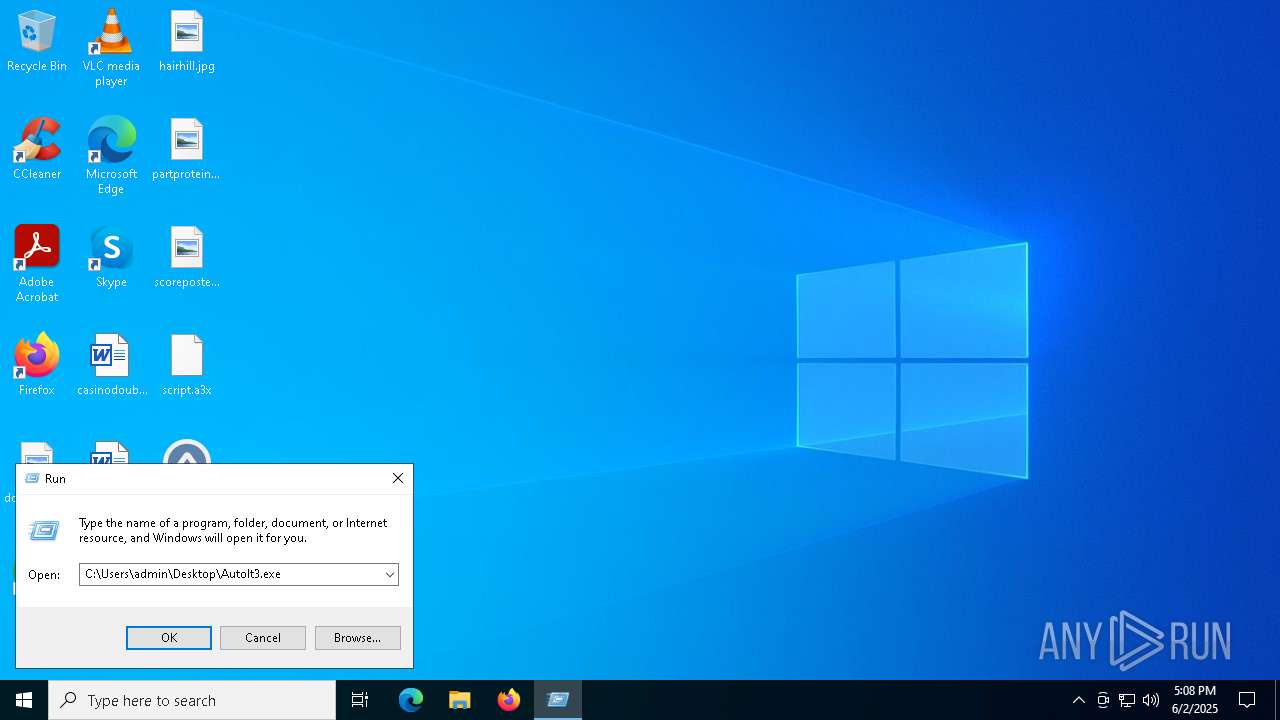
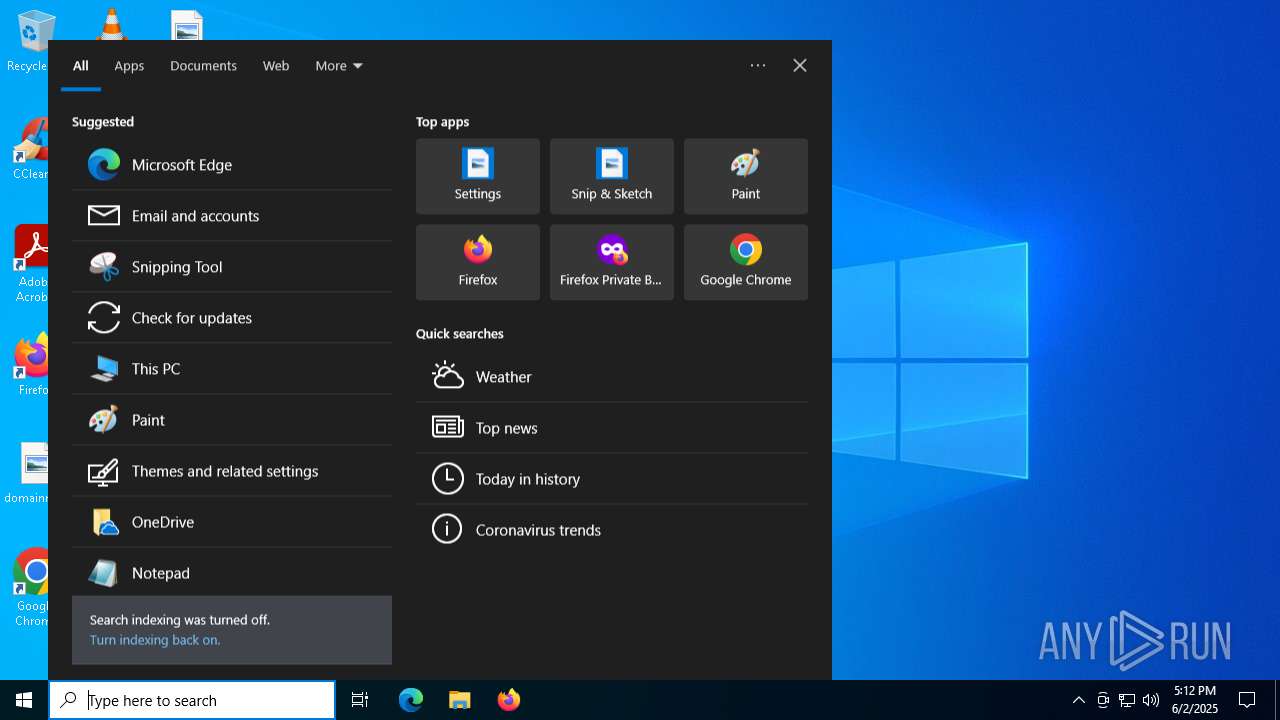
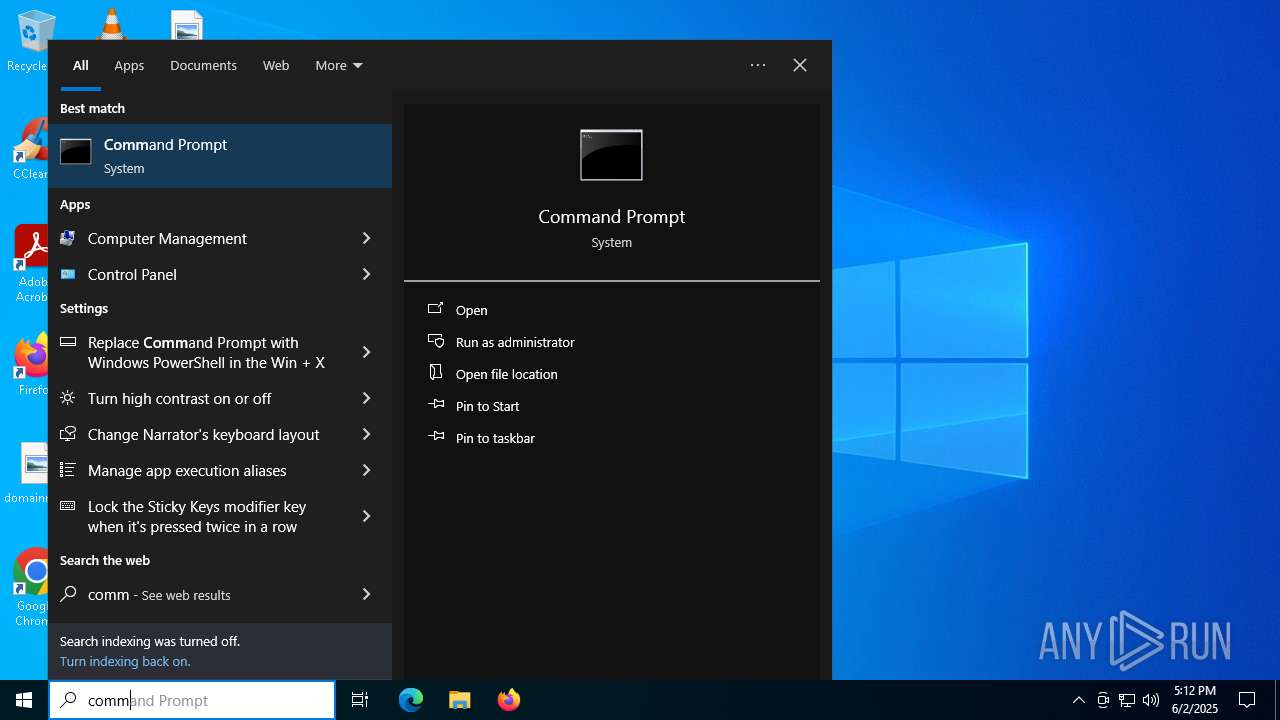
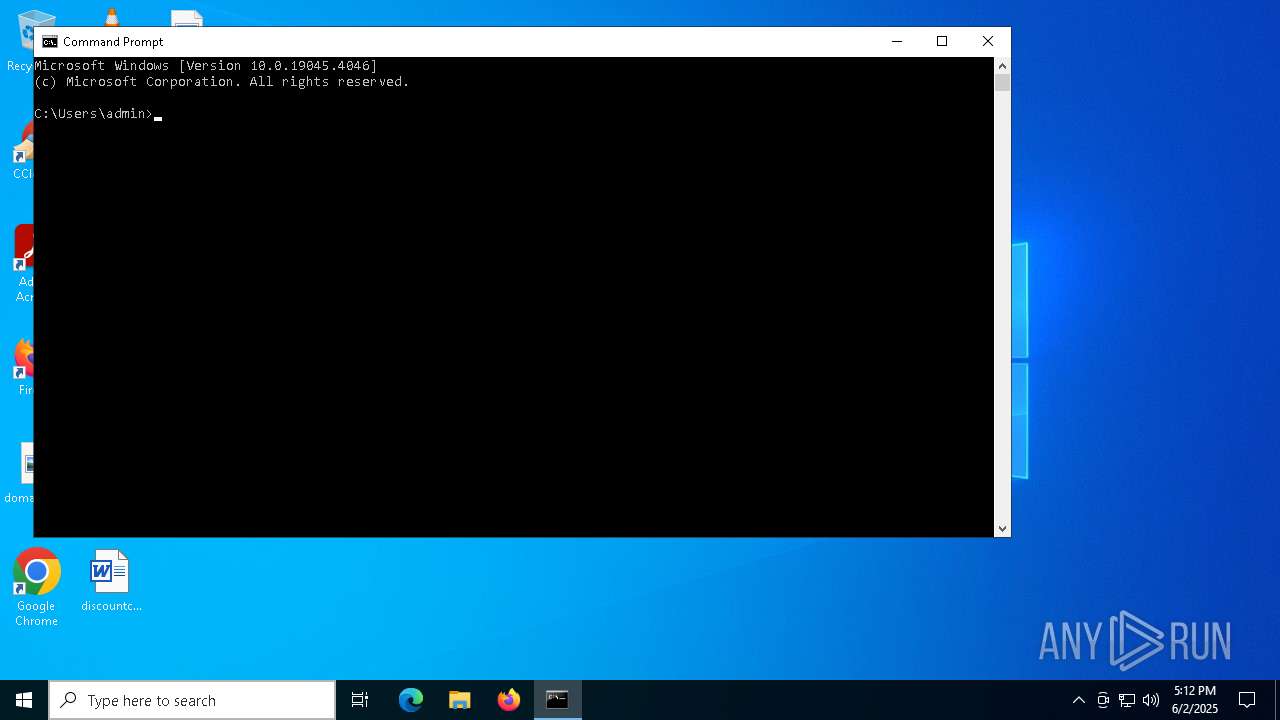
Manual execution by a user
- AutoIt3.exe (PID: 6368)
- cmd.exe (PID: 7764)
Reads mouse settings
- AutoIt3.exe (PID: 6368)
Creates files or folders in the user directory
- rundll32.exe (PID: 3140)
Create files in a temporary directory
- AutoIt3.exe (PID: 6368)
Checks supported languages
- AutoIt3.exe (PID: 6368)
The sample compiled with english language support
- AutoIt3.exe (PID: 6368)
- rundll32.exe (PID: 3140)
Checks proxy server information
- slui.exe (PID: 3996)
- rundll32.exe (PID: 5176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
143
Monitored processes
10
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3140 | rundll32.exe C:\Users\admin\AppData\Local\Temp\embedded.dll,WSPStartup | C:\Windows\System32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3996 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5176 | rundll32.exe "C:\Users\admin\AppData\Roaming\Custom_update\Update_28166db2.dll", WSPStartup | C:\Windows\System32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5720 | rundll32.exe C:\Users\admin\AppData\Local\Temp\embedded.dll,WSPStartup | C:\Windows\SysWOW64\rundll32.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6368 | "C:\Users\admin\Desktop\AutoIt3.exe" script.a3x | C:\Users\admin\Desktop\AutoIt3.exe | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 6824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7360 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
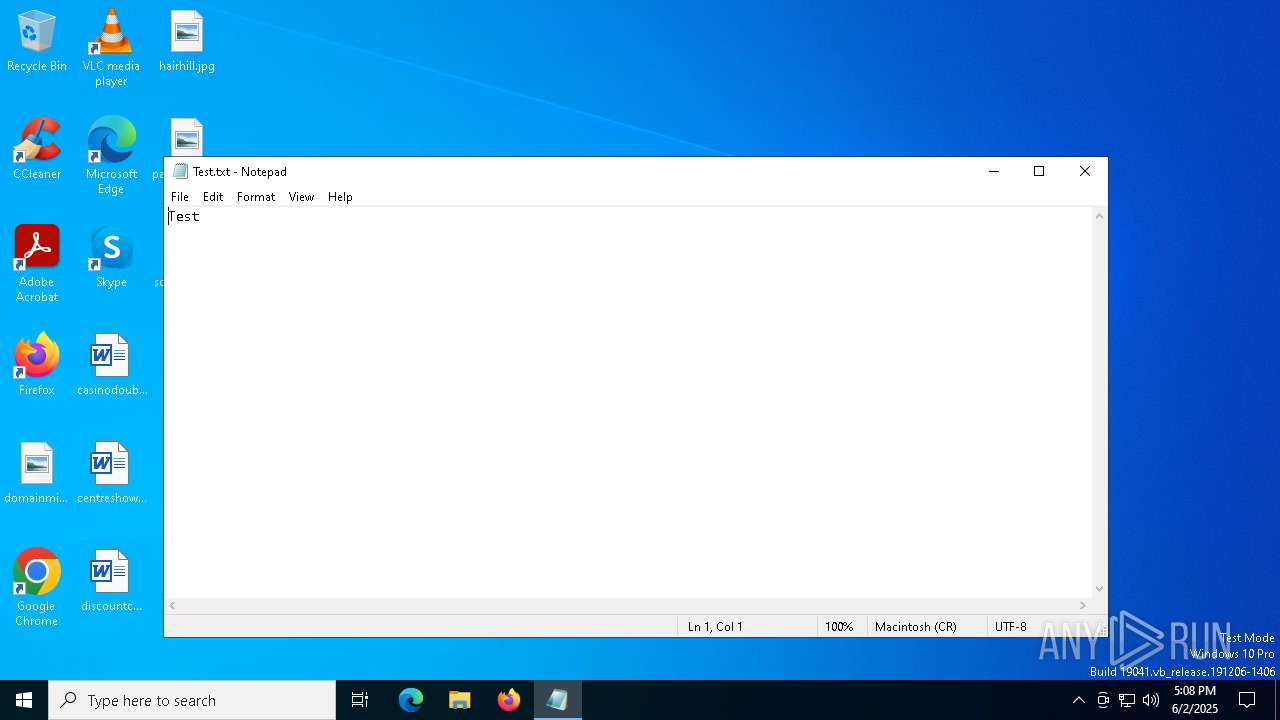
| 7632 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Test.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7764 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7792 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 116
Read events
2 113
Write events
3
Delete events
0
Modification events
| (PID) Process: | (5176) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5176) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5176) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6368 | AutoIt3.exe | C:\Users\admin\AppData\Local\Temp\embedded.dll | executable | |
MD5:2FEF1499B261440C18BA153CDCE17170 | SHA256:7A2FD36C4250B8F1601A540AE4654339B47F17C0CD03D64918EAF447306AA919 | |||
| 3140 | rundll32.exe | C:\Users\admin\AppData\Roaming\Custom_update\Update_28166db2.dll | executable | |
MD5:2FEF1499B261440C18BA153CDCE17170 | SHA256:7A2FD36C4250B8F1601A540AE4654339B47F17C0CD03D64918EAF447306AA919 | |||
| 6368 | AutoIt3.exe | C:\Users\admin\AppData\Local\Temp\autF5F1.tmp | binary | |
MD5:EE7095A4223AACDED556A390BBBB7527 | SHA256:97DD0476936155B2C6A35045289E9AC10EE78157A963EA17F157B44FF331E27B | |||
| 3140 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\embedded.dll:wtfbbq | executable | |
MD5:2FEF1499B261440C18BA153CDCE17170 | SHA256:7A2FD36C4250B8F1601A540AE4654339B47F17C0CD03D64918EAF447306AA919 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
32
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7572 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7504 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7572 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2924 | SearchApp.exe | 204.79.197.222:443 | fp.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2924 | SearchApp.exe | 92.123.104.59:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
daringdesigners.com |
| malicious |
dns.msftncsi.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |