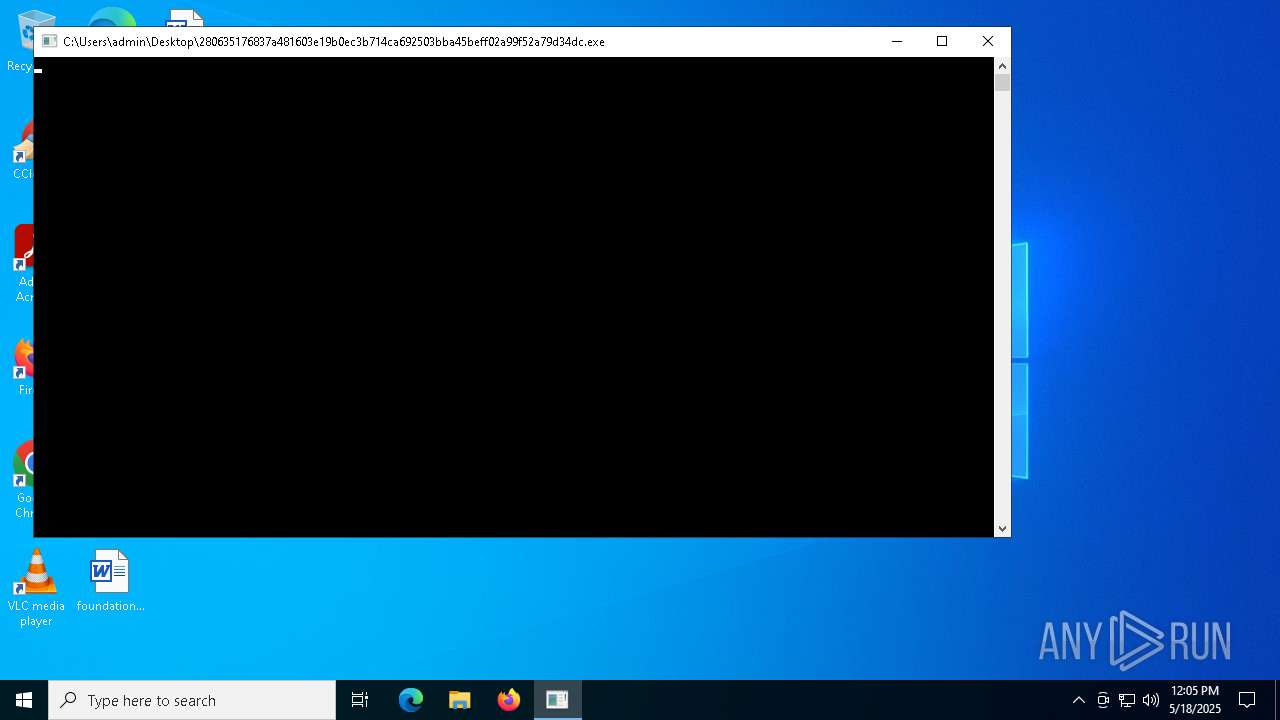
| File name: | 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc |
| Full analysis: | https://app.any.run/tasks/a4c39669-91e6-41d2-8efe-80bdea454740 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | May 18, 2025, 12:05:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 16 sections |
| MD5: | D6608289695FE7EE74DEB9906DAFA150 |
| SHA1: | 53FE6EDCF978642BF53C015F054EDF5122473CB0 |
| SHA256: | 280635176837A481603E19B0EC3B714CA692503BBA45BEFF02A99F52A79D34DC |
| SSDEEP: | 384:oq8Gt85tsovcB1oP42OphYsGvW1v0VoCCZKVDsIG2KZt9y+/F:oRGt0sQcB1oEYq1vHCG8 |
MALICIOUS
COBALTSTRIKE has been detected (YARA)
- 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe (PID: 6744)
SUSPICIOUS
Reads security settings of Internet Explorer
- 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe (PID: 6744)
Executes application which crashes
- 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe (PID: 6744)
INFO
Checks supported languages
- 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe (PID: 6744)
Reads the computer name
- 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe (PID: 6744)
Reads the machine GUID from the registry
- 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe (PID: 6744)
Checks proxy server information
- 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe (PID: 6744)
- slui.exe (PID: 1348)
Reads the software policy settings
- 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe (PID: 6744)
- slui.exe (PID: 1348)
Creates files or folders in the user directory
- WerFault.exe (PID: 896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
CobalStrike
(PID) Process(6744) 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe
C247.122.115.29:443/kunkun/jquery-3.3.2.slim.min.js
HeadersAccept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Referer: http://www.baidu.com/
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (Windows NT 6.3; Trident/7.0; rv:11.0) like Gecko
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:15 15:29:06+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.44 |
| CodeSize: | 7680 |
| InitializedDataSize: | 8704 |
| UninitializedDataSize: | 512 |
| EntryPoint: | 0x13f0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
125
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | C:\WINDOWS\system32\WerFault.exe -u -p 6744 -s 1516 | C:\Windows\System32\WerFault.exe | — | 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6744 | "C:\Users\admin\Desktop\280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe" | C:\Users\admin\Desktop\280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
CobalStrike(PID) Process(6744) 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe C247.122.115.29:443/kunkun/jquery-3.3.2.slim.min.js HeadersAccept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Referer: http://www.baidu.com/
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (Windows NT 6.3; Trident/7.0; rv:11.0) like Gecko | |||||||||||||||
Total events
8 472
Read events
8 472
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 896 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_280635176837a481_7735ecc3b23ffae9c0fe279db1f68dee3585_4c54f50f_02eaa88f-ac50-49f8-8f26-6c545eeb2b83\Report.wer | — | |
MD5:— | SHA256:— | |||
| 896 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WEREDEC.tmp.dmp | binary | |
MD5:69988D7A386E58A0CE0F1ABB188F86DF | SHA256:78515367F59FA4BB010E8F0E22C15E3EEA4DBEEC4E00ADD6C46D51F60FE72E52 | |||
| 896 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WEREEF7.tmp.WERInternalMetadata.xml | binary | |
MD5:BDD2C1F0BA8DDFCE2849C2FCEA71FDCC | SHA256:FD04A2AF728A46A62A0D402AD51CB4AEE08C6C2C139A0CECBC99C22F2D68F686 | |||
| 896 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WEREF17.tmp.xml | xml | |
MD5:5A74FC5C9EDFABE668608298666E8157 | SHA256:BFEF03D680DC9C331EBD0E15A2D39D0A954569C91C0044F368A493C0EDE54F8F | |||
| 896 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe.6744.dmp | binary | |
MD5:7C49071386DBC251557F949A68C97BD7 | SHA256:39BE63F9521999FBE039556034C572085450BB762F43BF8D6ABC6E38B7FB1D70 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
22
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6744 | 280635176837a481603e19b0ec3b714ca692503bba45beff02a99f52a79d34dc.exe | 47.122.115.29:443 | — | — | CN | unknown |
7020 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1348 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |