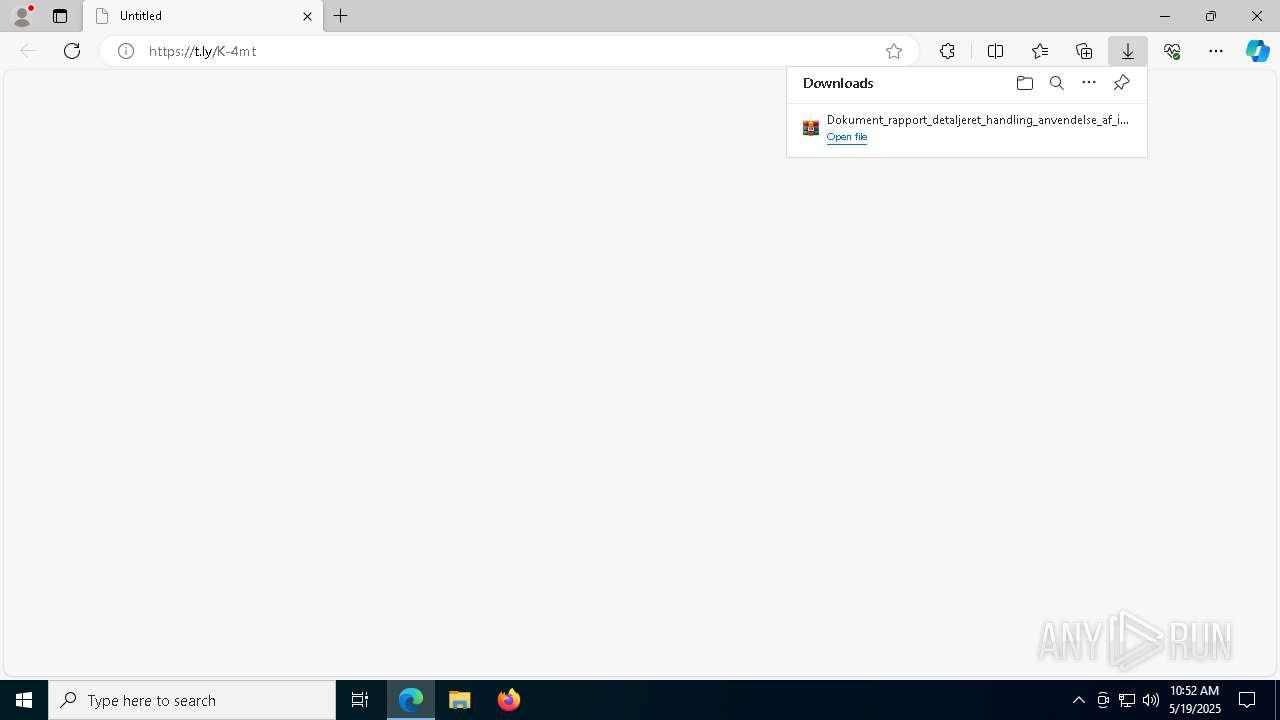
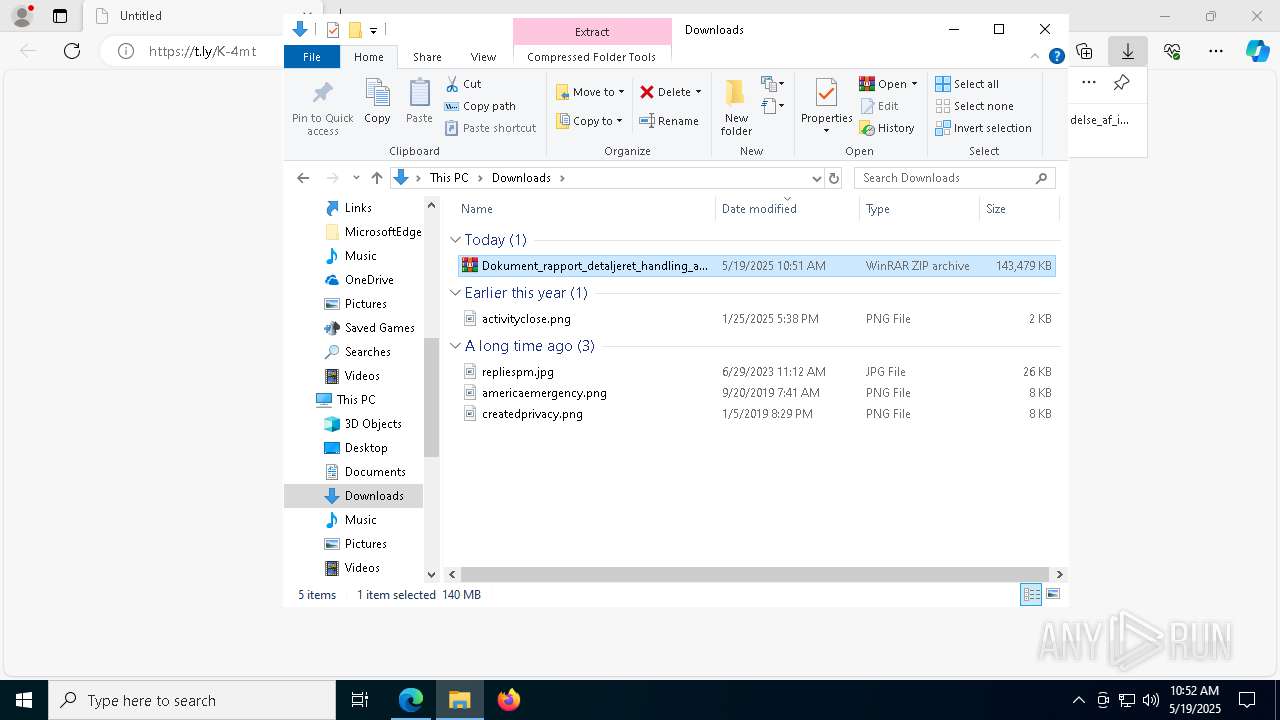
| URL: | https://t.ly/K-4mt |
| Full analysis: | https://app.any.run/tasks/65d5cd98-6af0-49e8-a7b6-a368292309fe |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 19, 2025, 10:50:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A785932690FB663C8BDA70CC9DFEEFF5 |
| SHA1: | 596B06B95483D1ABAE95C8CBCFCE023E8ACAE908 |
| SHA256: | 27E1C026BD76025AE6DDA4697043F473997C6B0146006BD9C5CD3EDCA3A854DA |
| SSDEEP: | 3:N8D5+:2t+ |
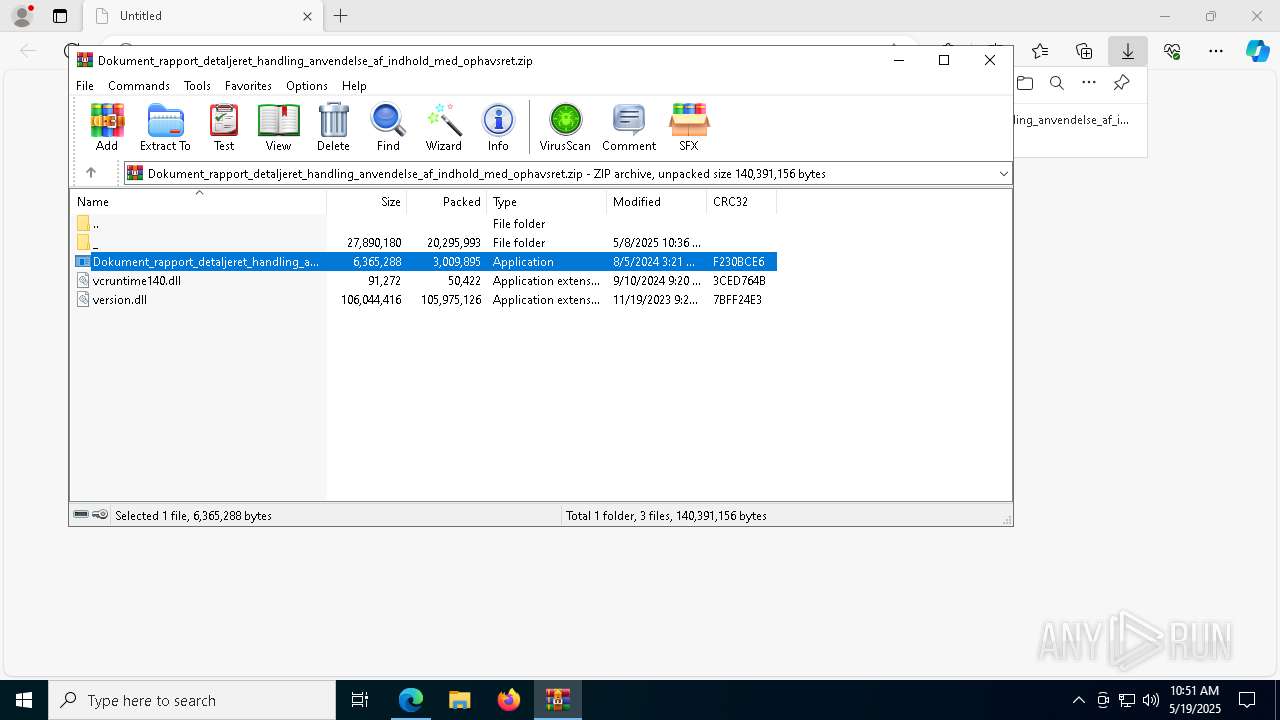
MALICIOUS
ASYNCRAT has been detected (SURICATA)
- RegAsm.exe (PID: 3992)
Suspicious browser debugging (Possible cookie theft)
- chrome.exe (PID: 1616)
- msedge.exe (PID: 9060)
SUSPICIOUS
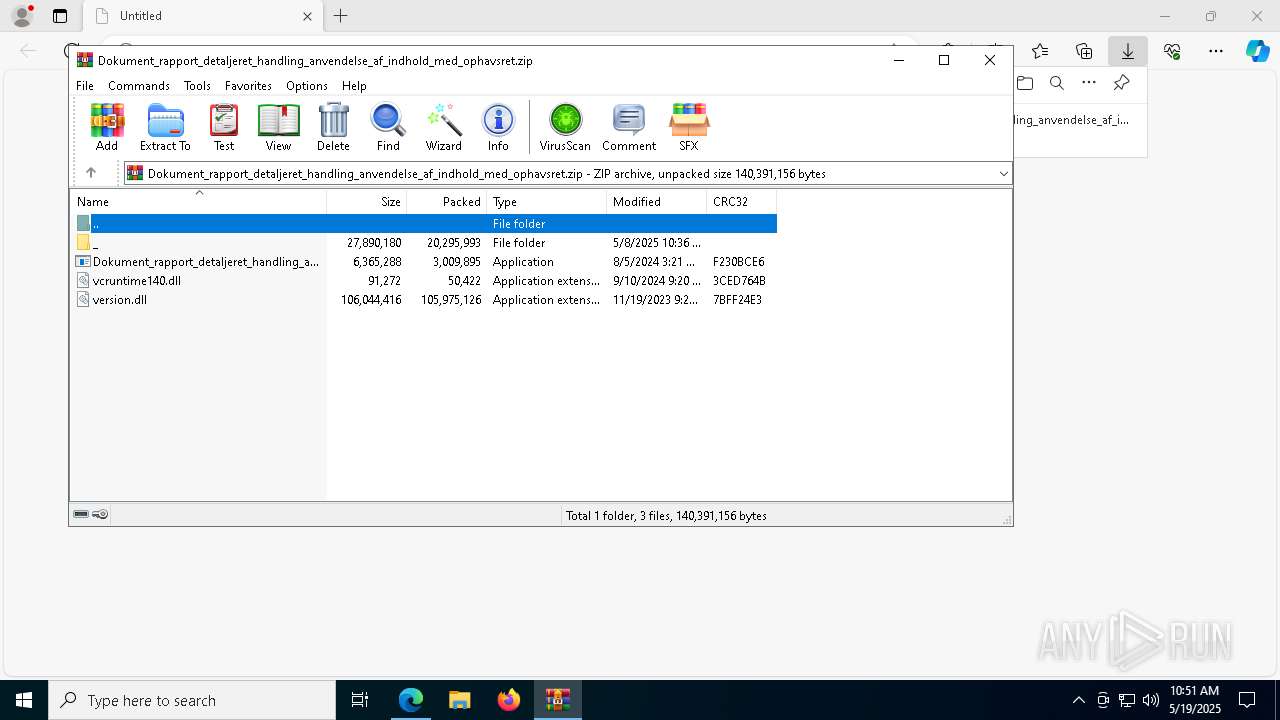
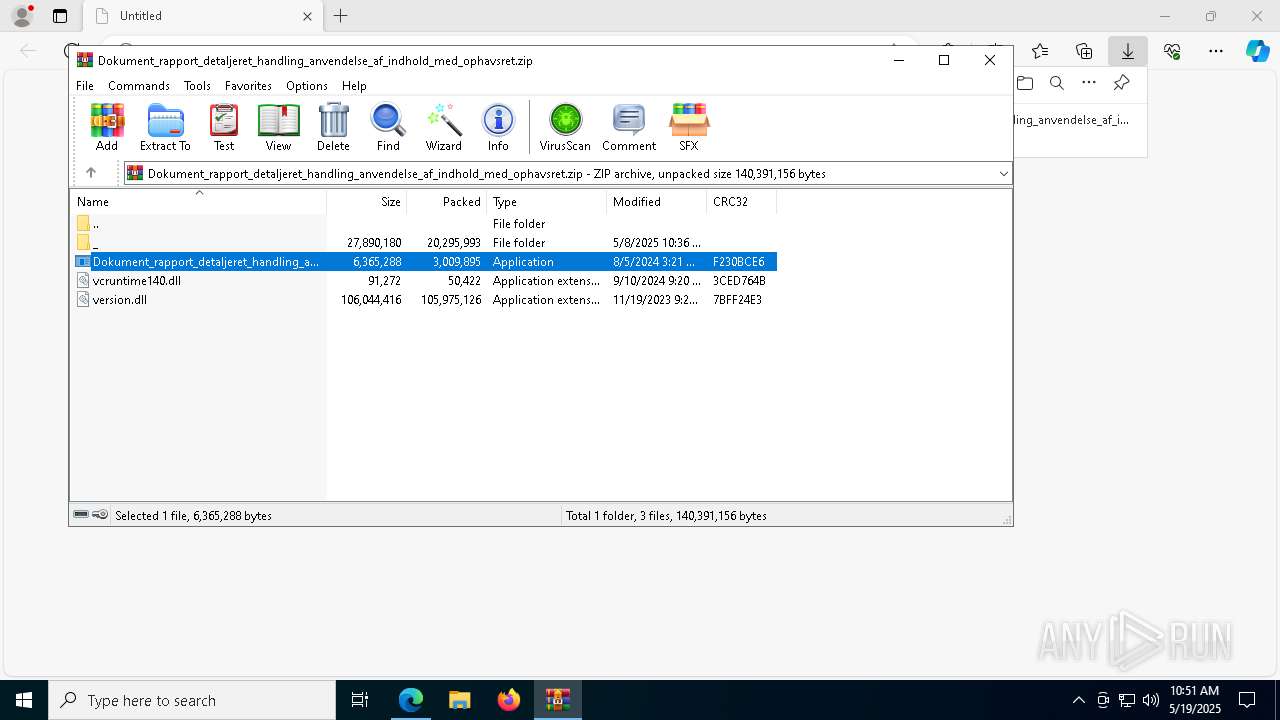
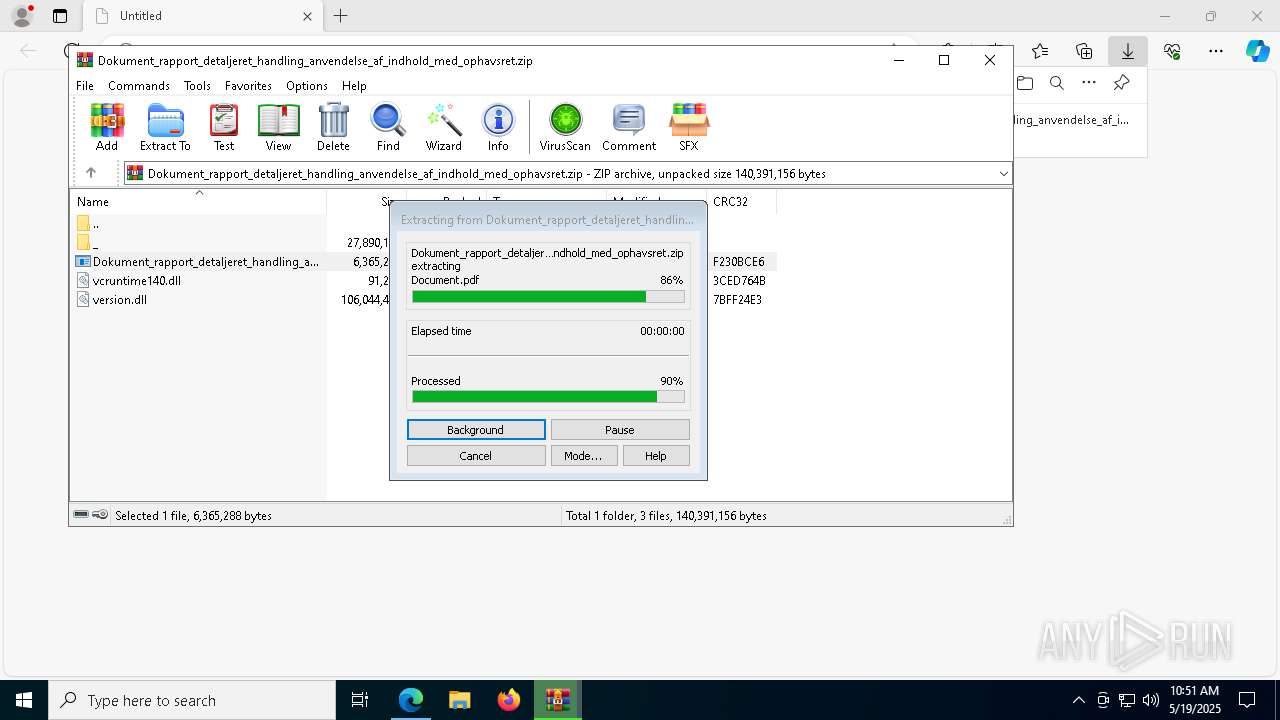
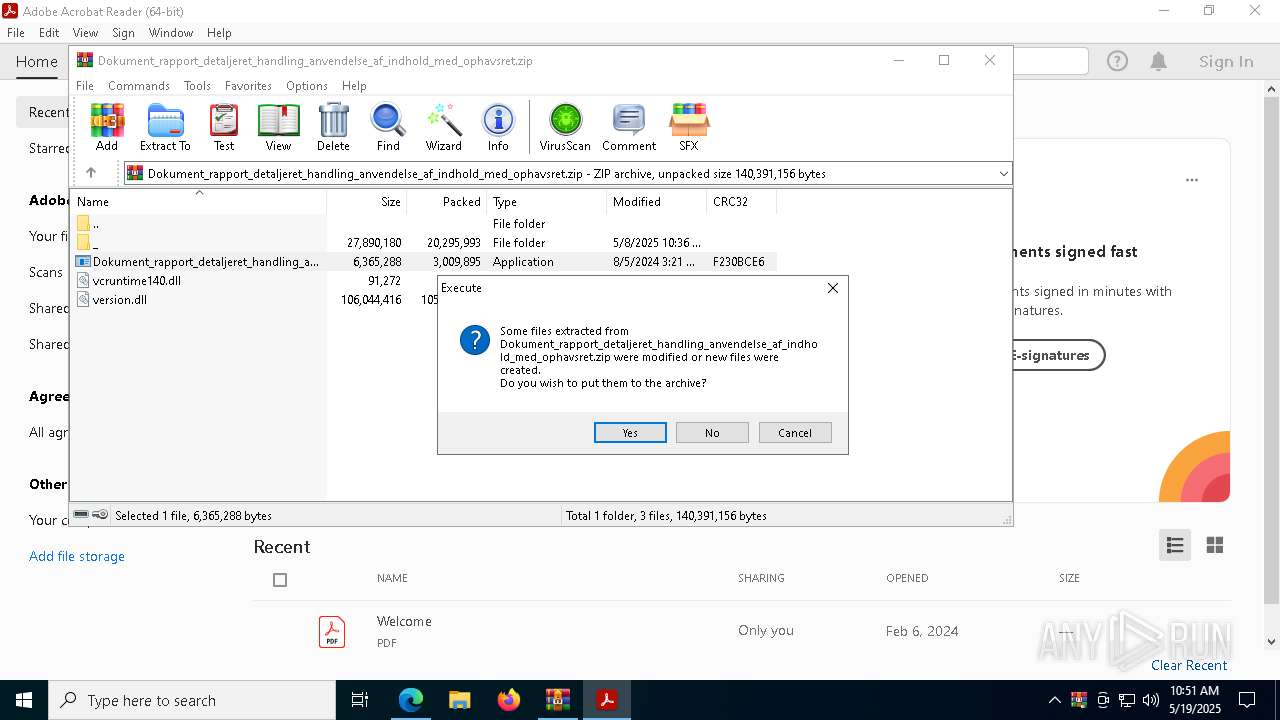
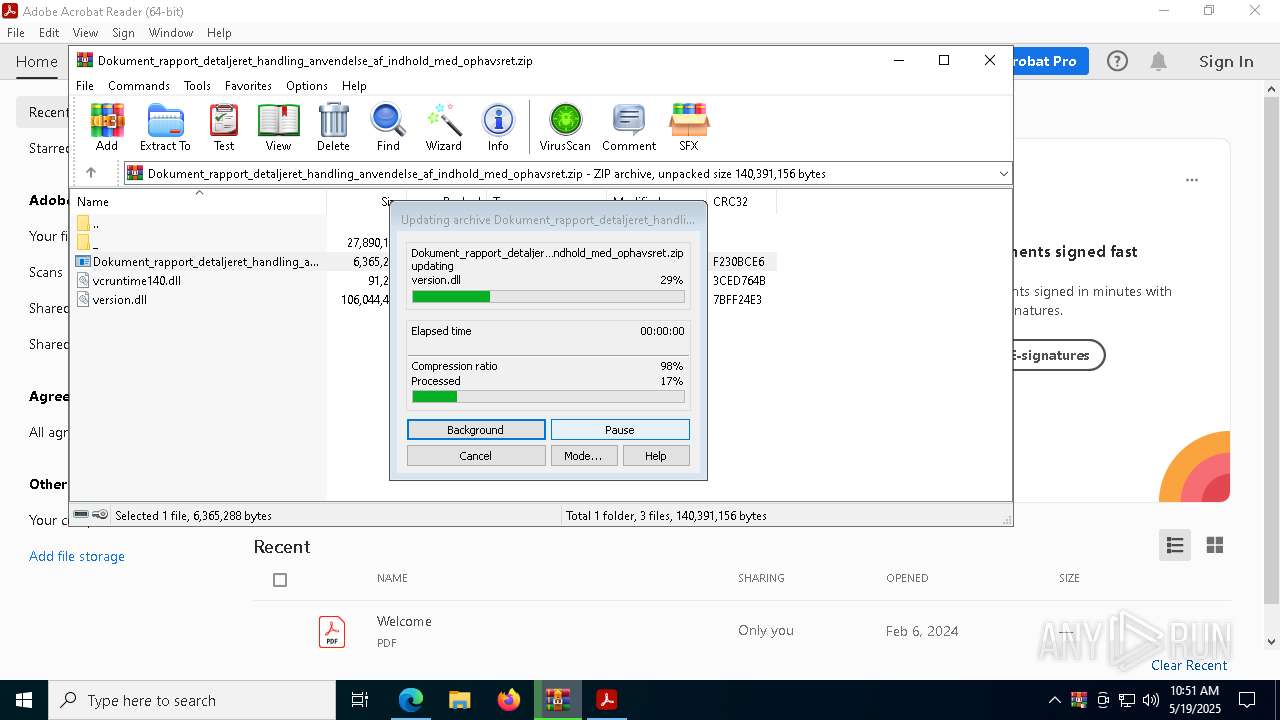
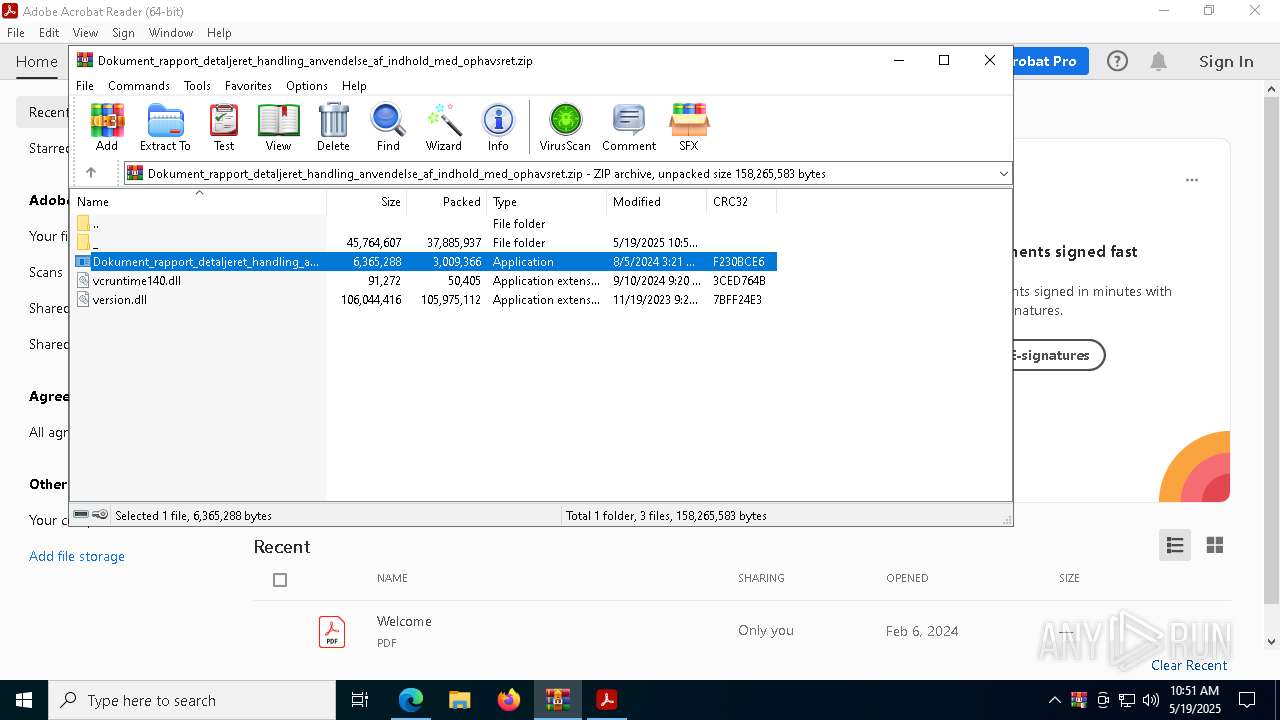
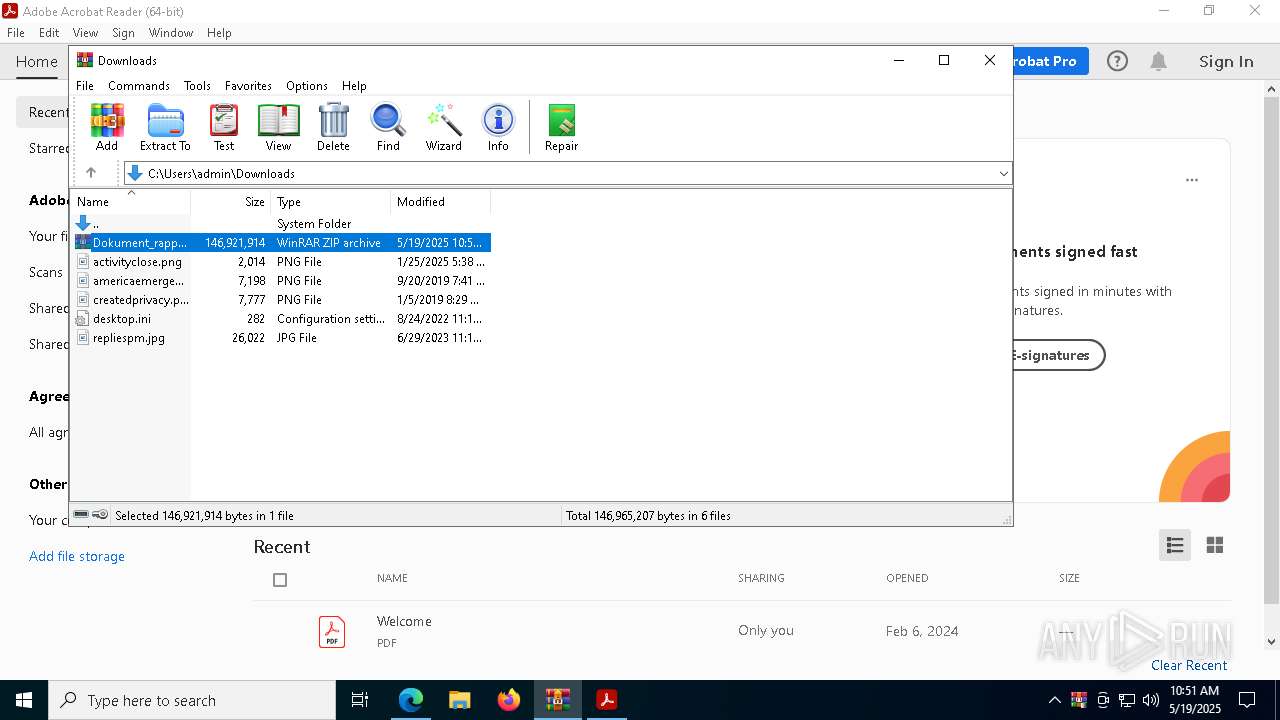
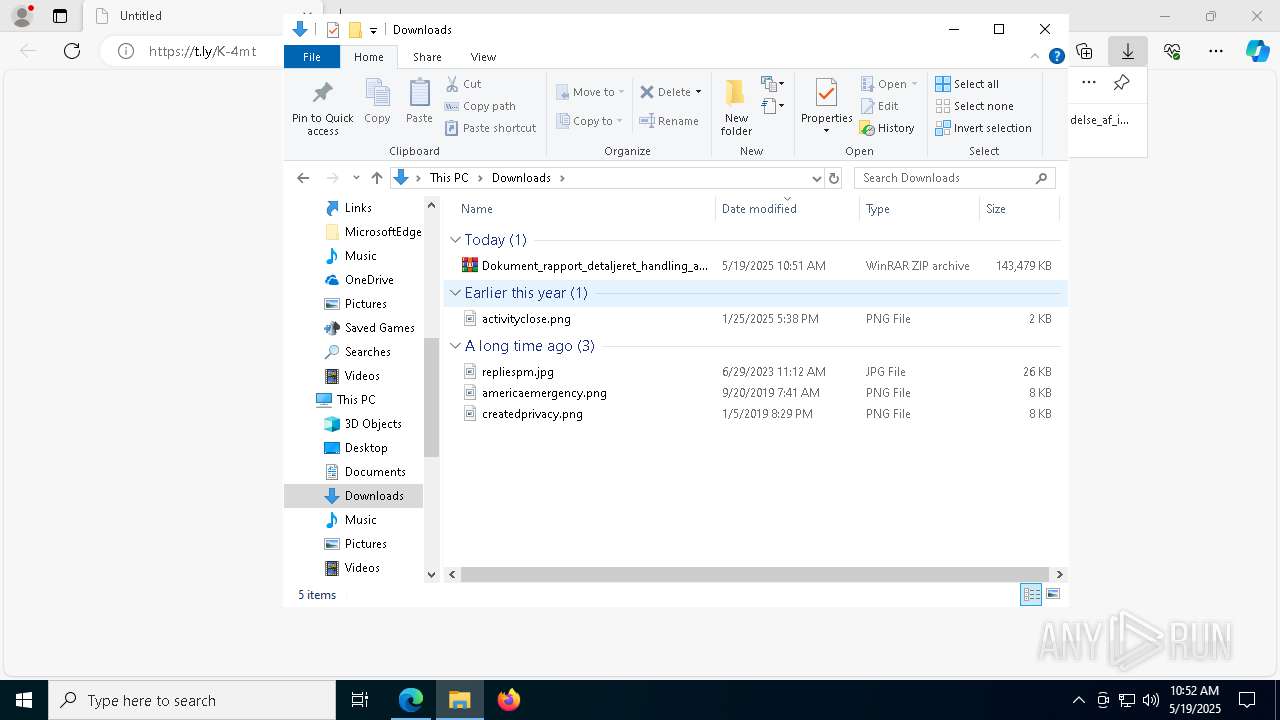
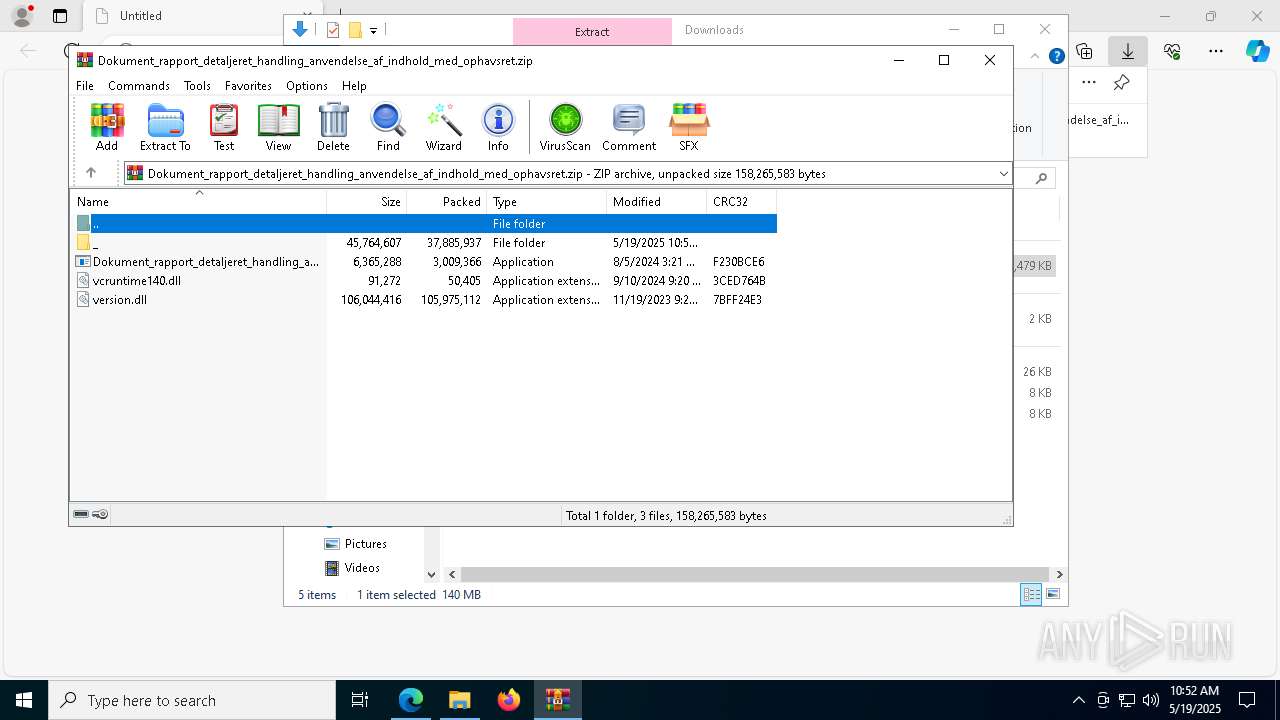
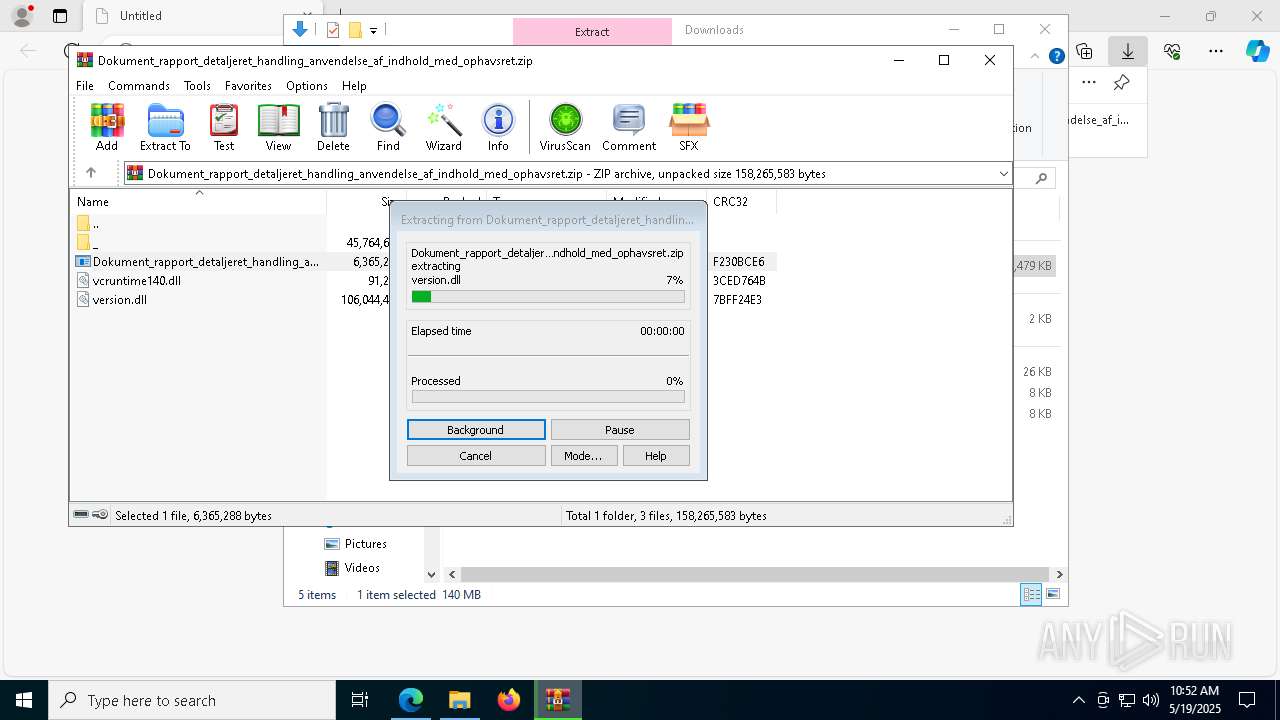
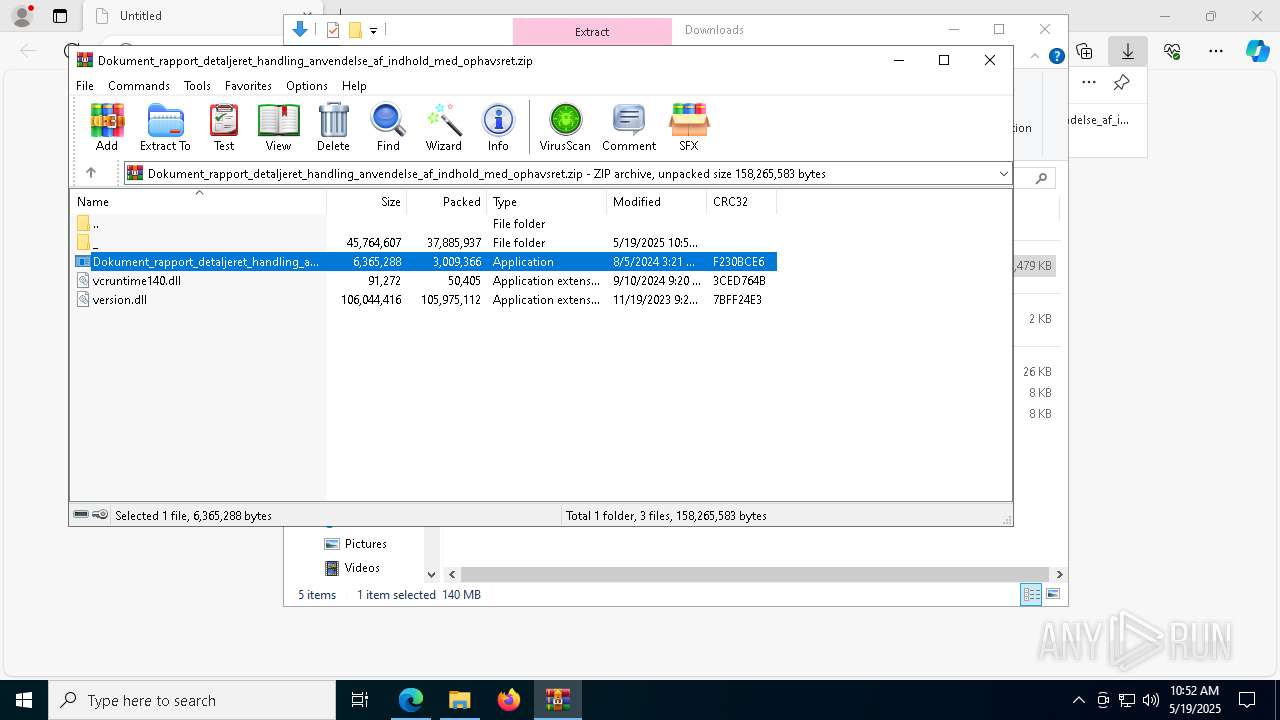
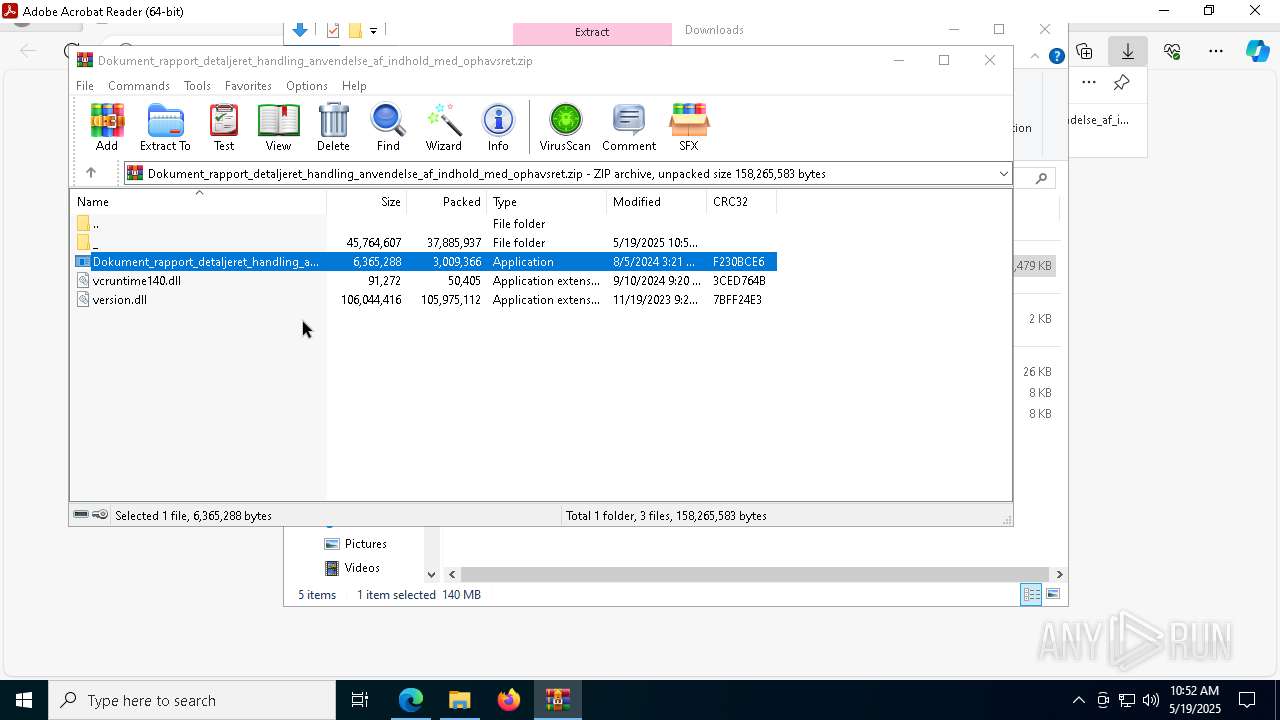
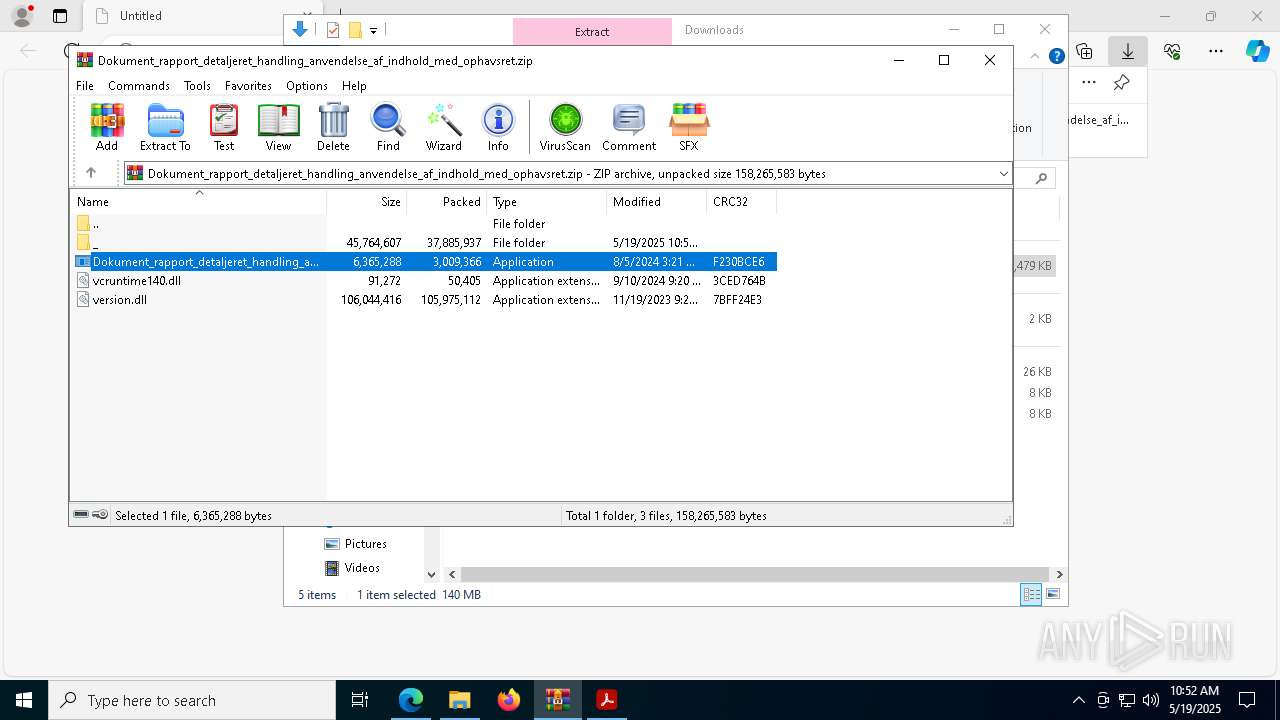
Starts CMD.EXE for commands execution
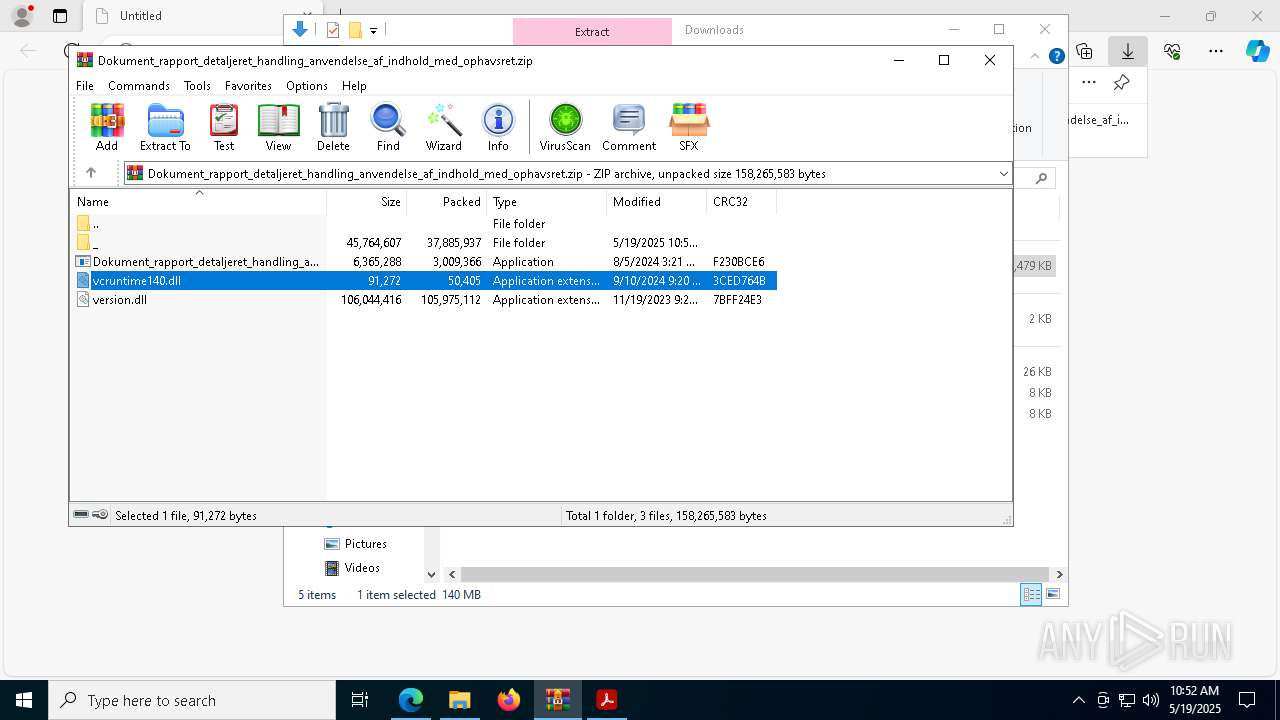
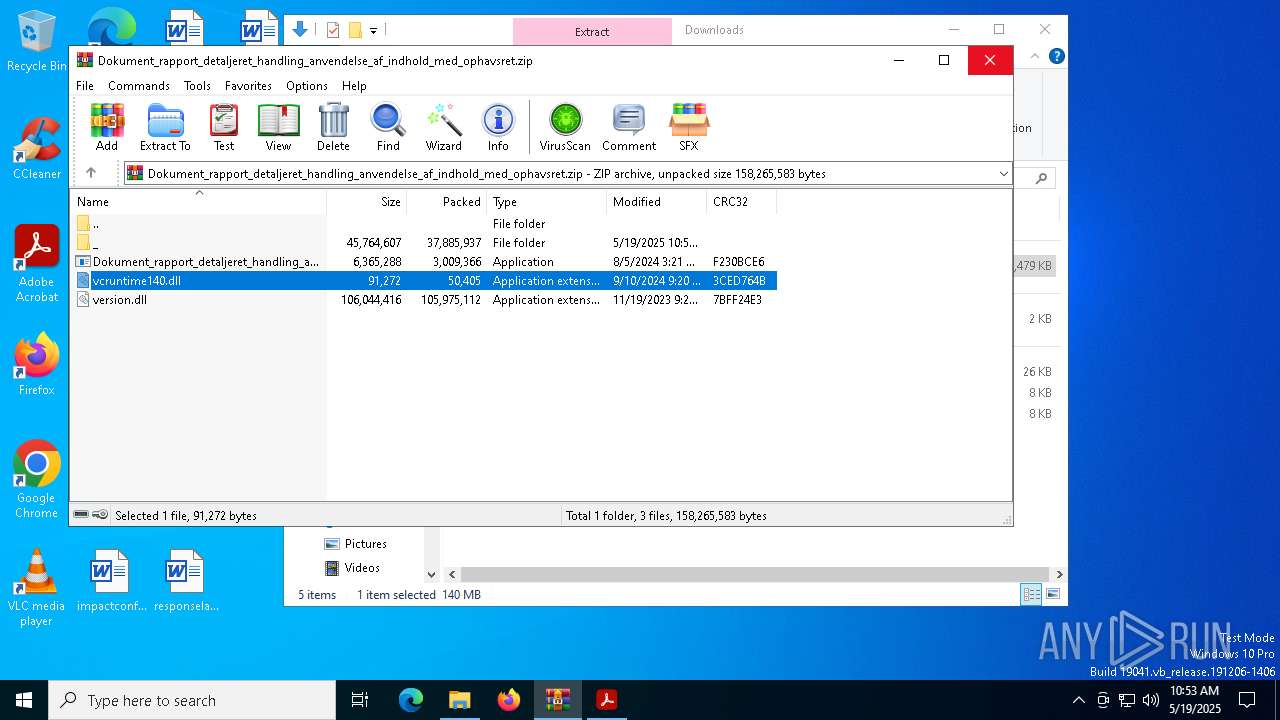
- Dokument_rapport_detaljeret_handling_anvendelse_af_indhold_med_ophavsret.exe (PID: 3768)
- Dokument_rapport_detaljeret_handling_anvendelse_af_indhold_med_ophavsret.exe (PID: 8412)
- svchost.exe (PID: 8376)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6740)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 2852)
- svchost.exe (PID: 8376)
- cmd.exe (PID: 7104)
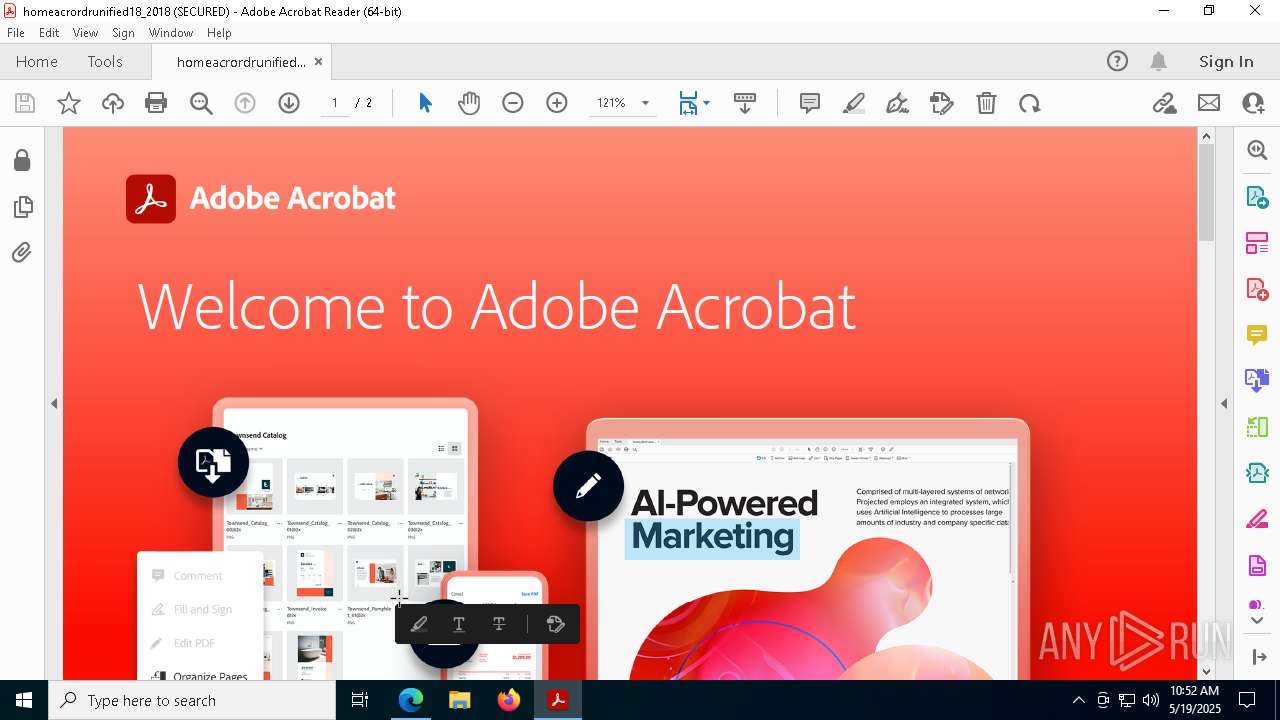
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 2852)
- cmd.exe (PID: 7104)
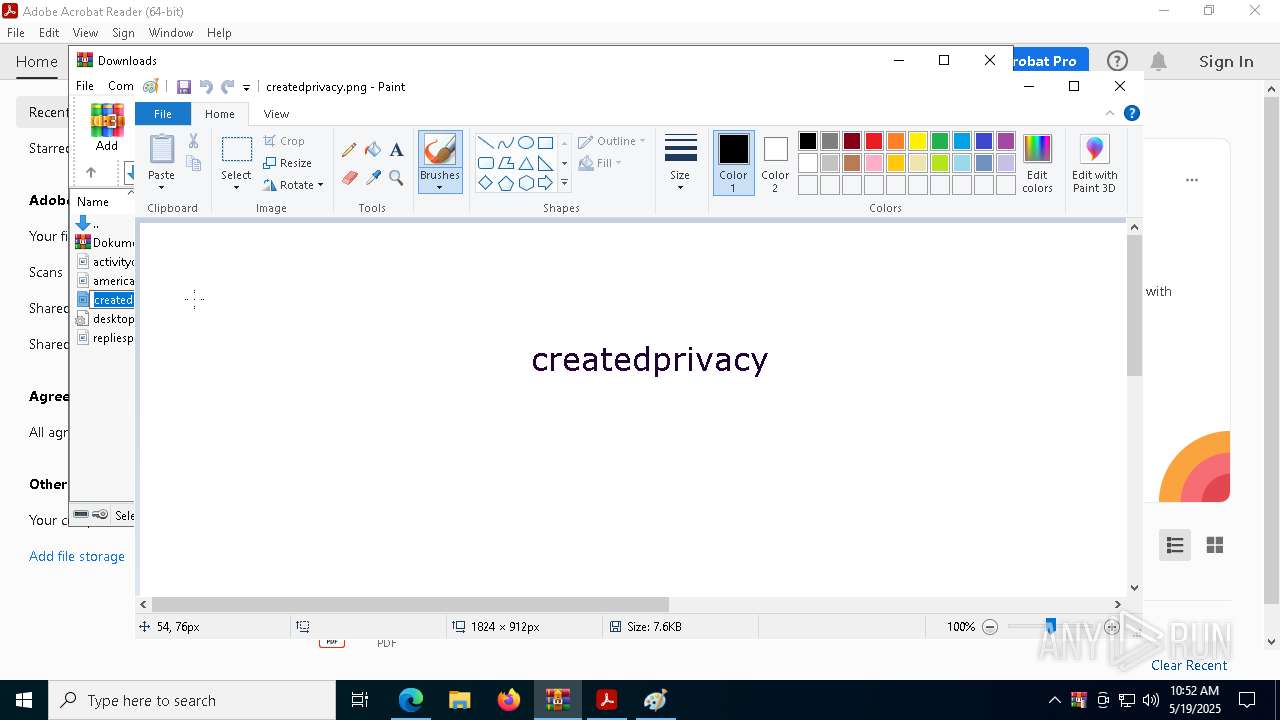
Process drops python dynamic module
- Images.png (PID: 5392)
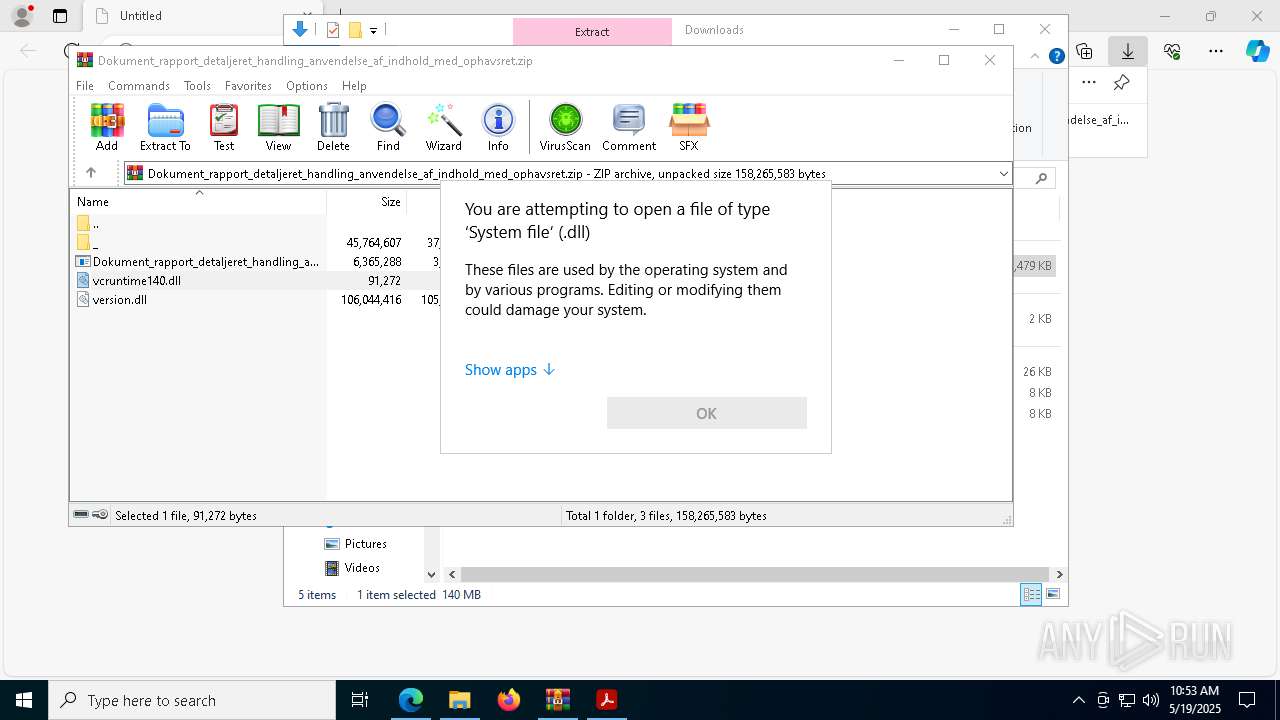
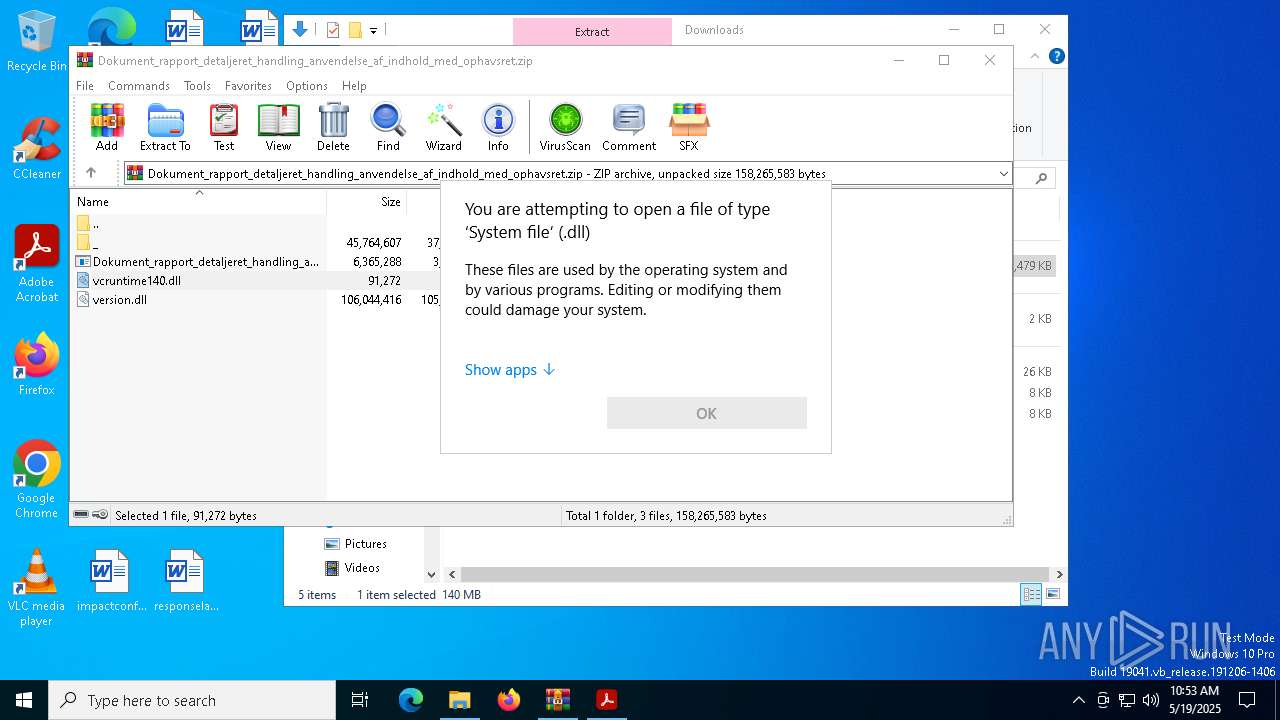
Process drops legitimate windows executable
- Images.png (PID: 5392)
- WinRAR.exe (PID: 8304)
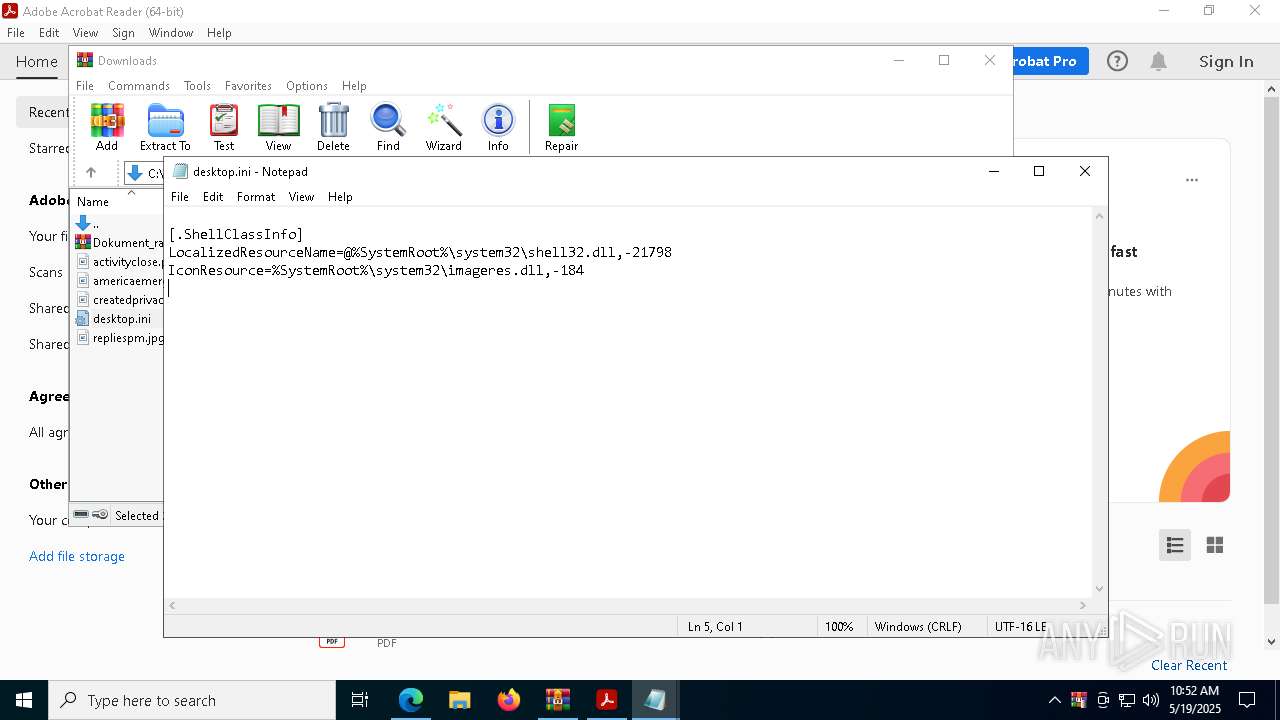
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 6740)
The executable file from the user directory is run by the CMD process
- Images.png (PID: 5392)
Starts application with an unusual extension
- cmd.exe (PID: 2852)
Executable content was dropped or overwritten
- Images.png (PID: 5392)
The process drops C-runtime libraries
- Images.png (PID: 5392)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 8376)
There is functionality for taking screenshot (YARA)
- Images.png (PID: 5392)
Get information on the list of running processes
- svchost.exe (PID: 8376)
Checks for external IP
- svchost.exe (PID: 2196)
Uses TASKKILL.EXE to kill process
- svchost.exe (PID: 8376)
Connects to unusual port
- RegAsm.exe (PID: 3992)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 9008)
- cmd.exe (PID: 8992)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 3992)
INFO
Checks supported languages
- identity_helper.exe (PID: 1532)
- Dokument_rapport_detaljeret_handling_anvendelse_af_indhold_med_ophavsret.exe (PID: 3768)
- Images.png (PID: 5392)
Application launched itself
- msedge.exe (PID: 976)
- AcroCEF.exe (PID: 7148)
- Acrobat.exe (PID: 208)
- AcroCEF.exe (PID: 8692)
- Acrobat.exe (PID: 2268)
- chrome.exe (PID: 1616)
- msedge.exe (PID: 9060)
Reads Environment values
- identity_helper.exe (PID: 1532)
Reads the computer name
- identity_helper.exe (PID: 1532)
- Images.png (PID: 5392)
Reads Microsoft Office registry keys
- msedge.exe (PID: 976)
Executable content was dropped or overwritten
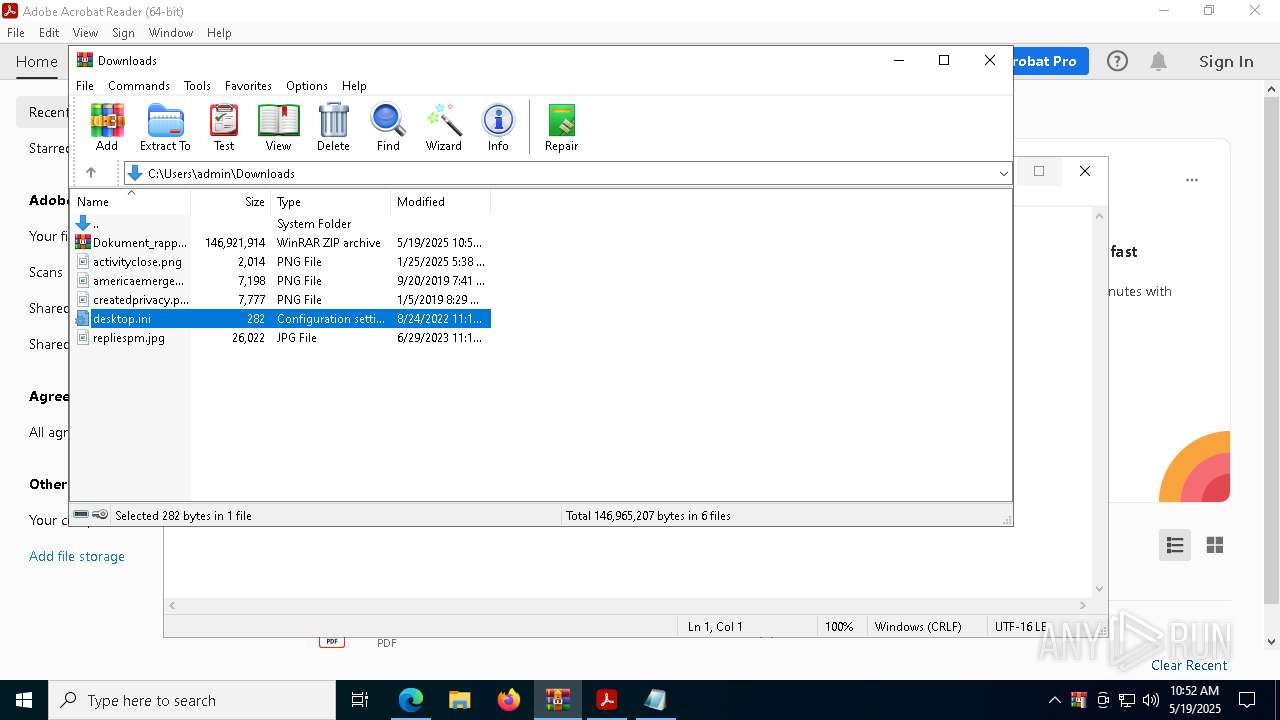
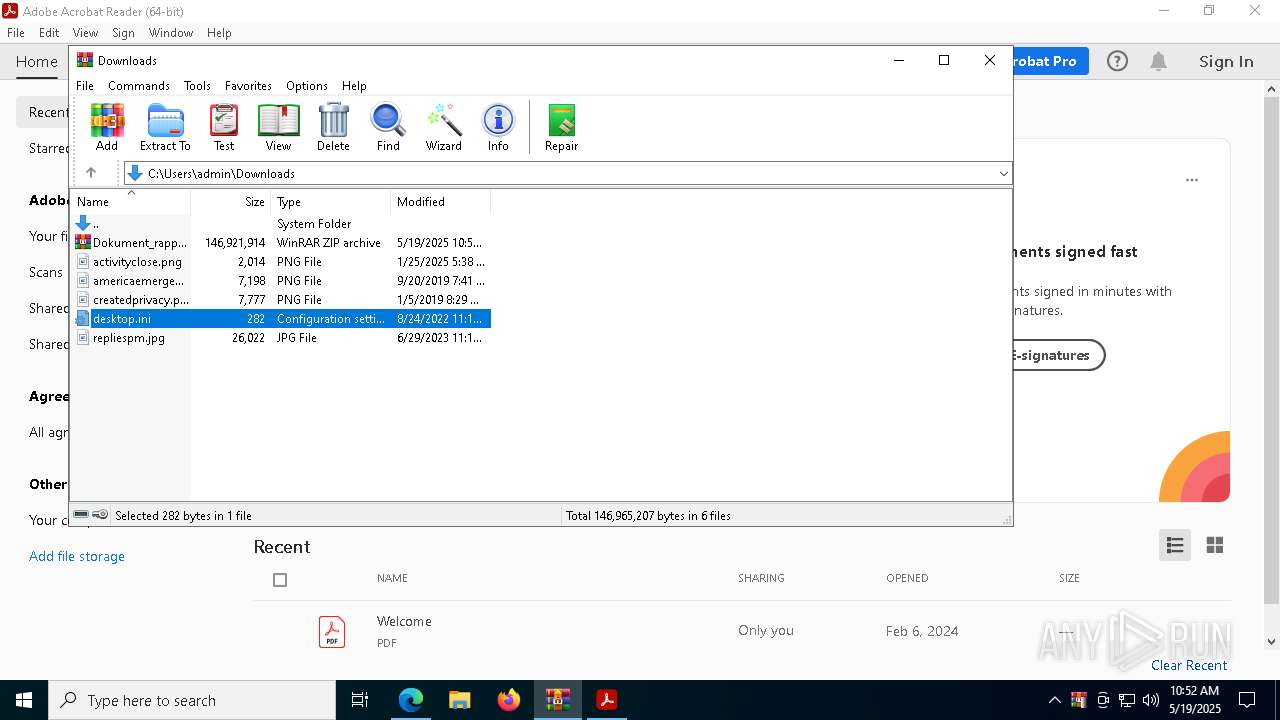
- WinRAR.exe (PID: 6740)
- msedge.exe (PID: 8912)
- WinRAR.exe (PID: 8304)
The sample compiled with english language support
- WinRAR.exe (PID: 6740)
- Images.png (PID: 5392)
- msedge.exe (PID: 8912)
- WinRAR.exe (PID: 8304)
Reads the software policy settings
- slui.exe (PID: 8024)
Create files in a temporary directory
- certutil.exe (PID: 856)
Reads the machine GUID from the registry
- Images.png (PID: 5392)
Python executable
- svchost.exe (PID: 8376)
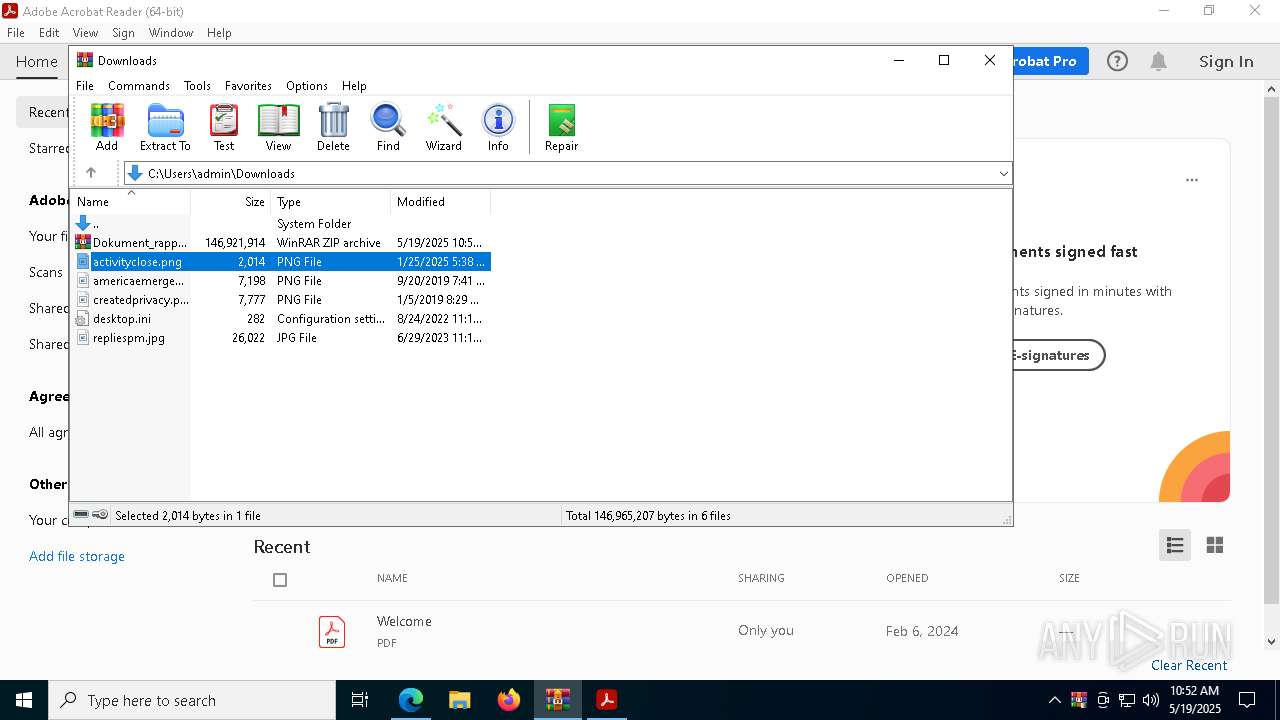
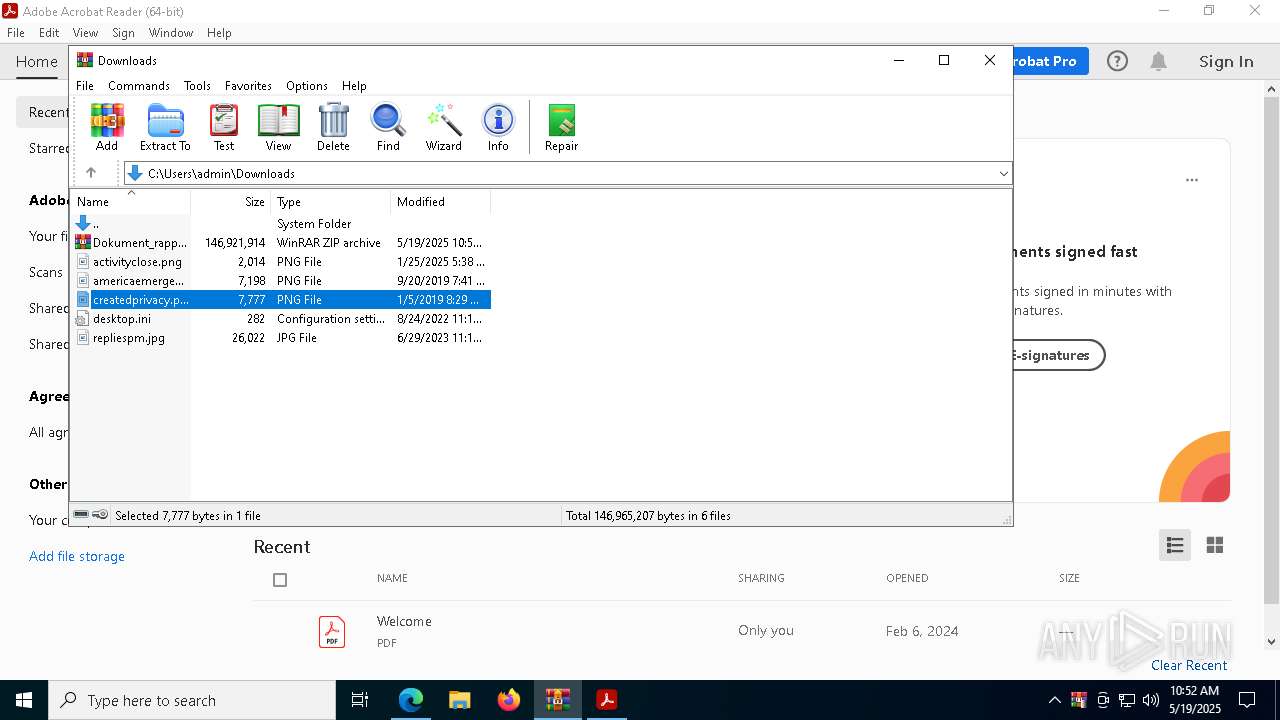
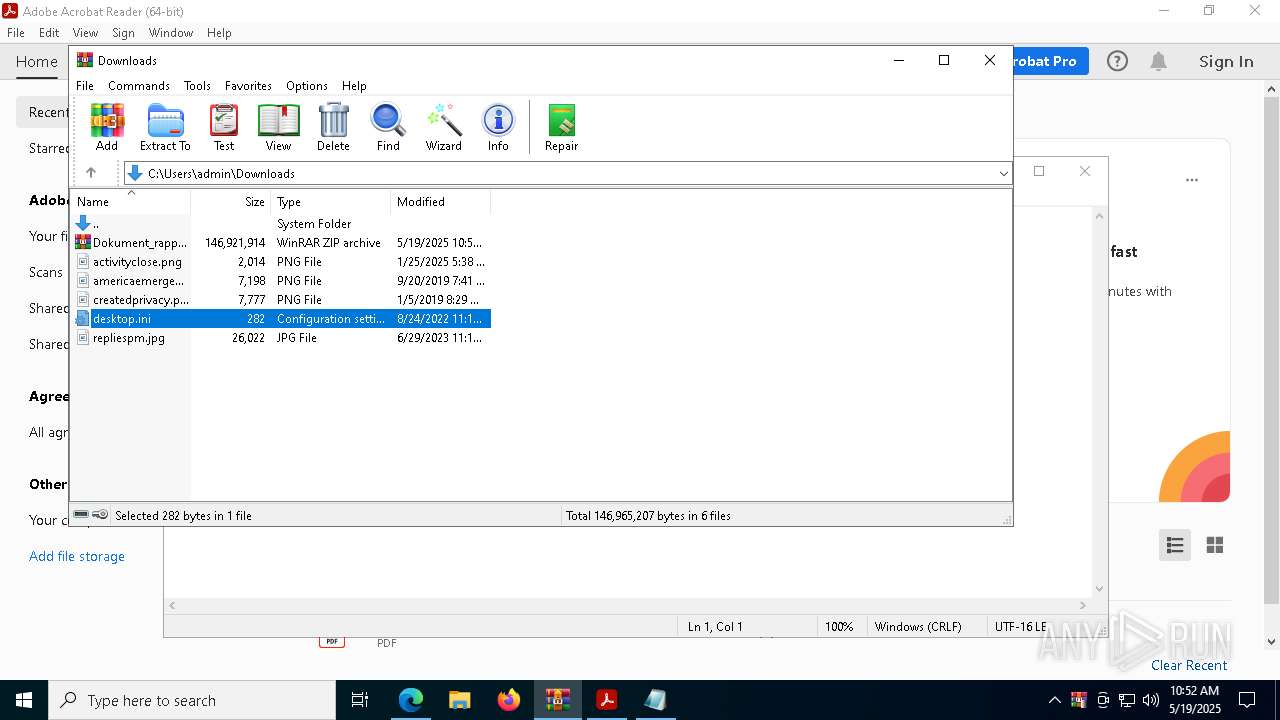
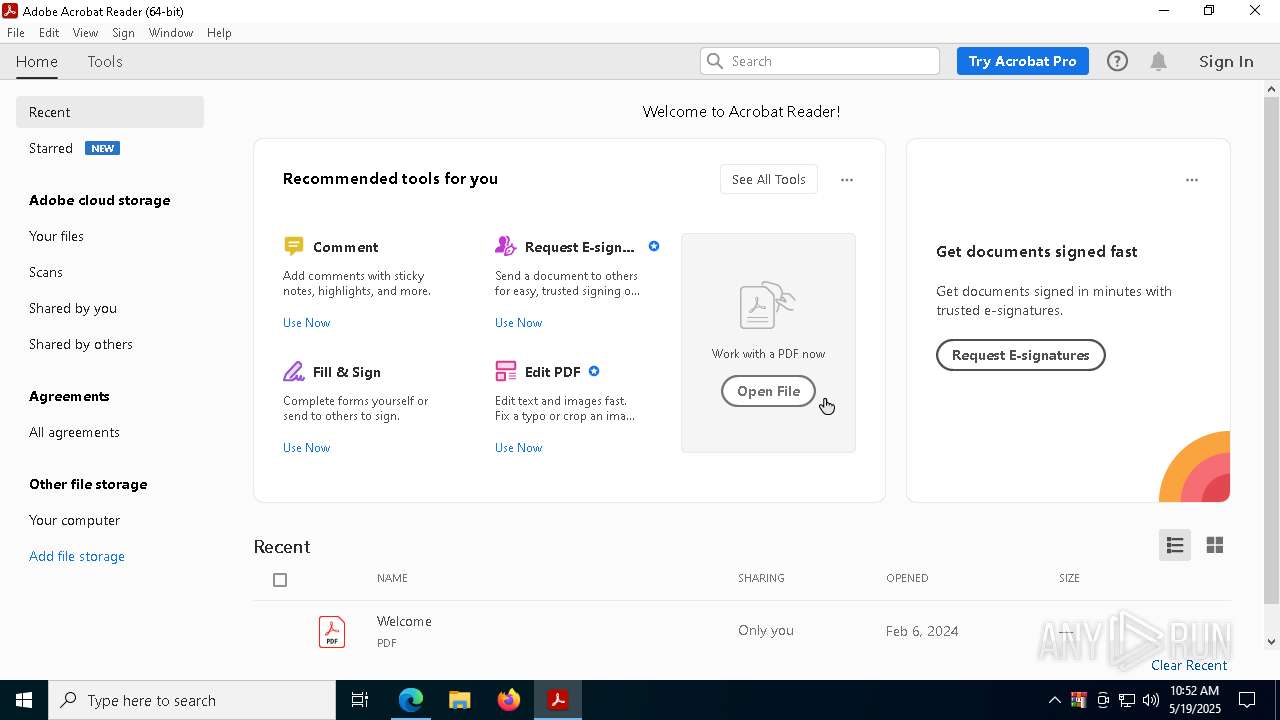
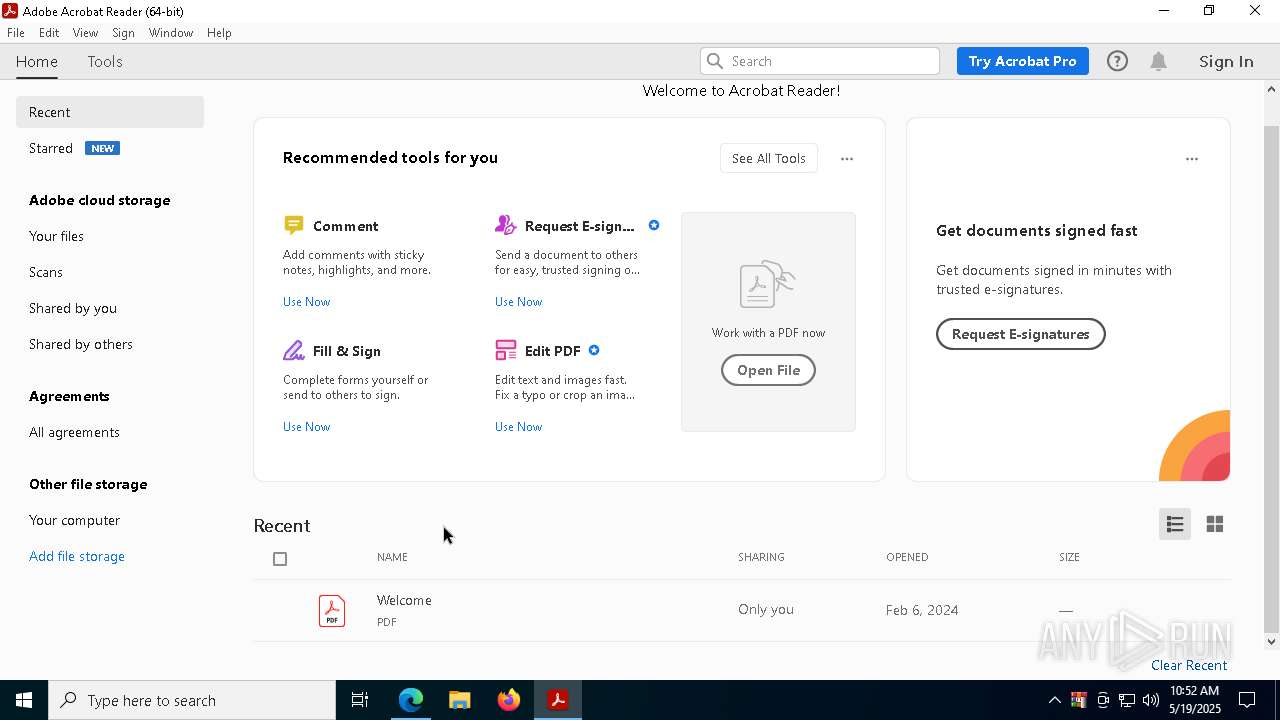
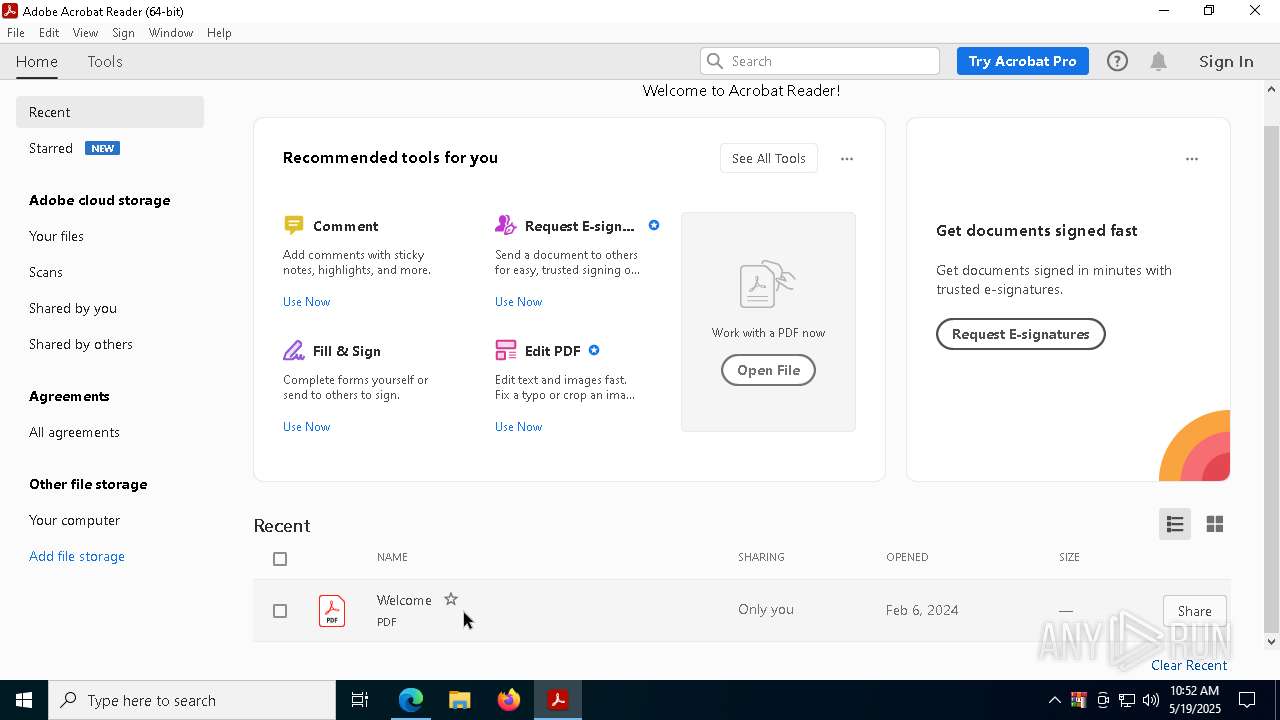
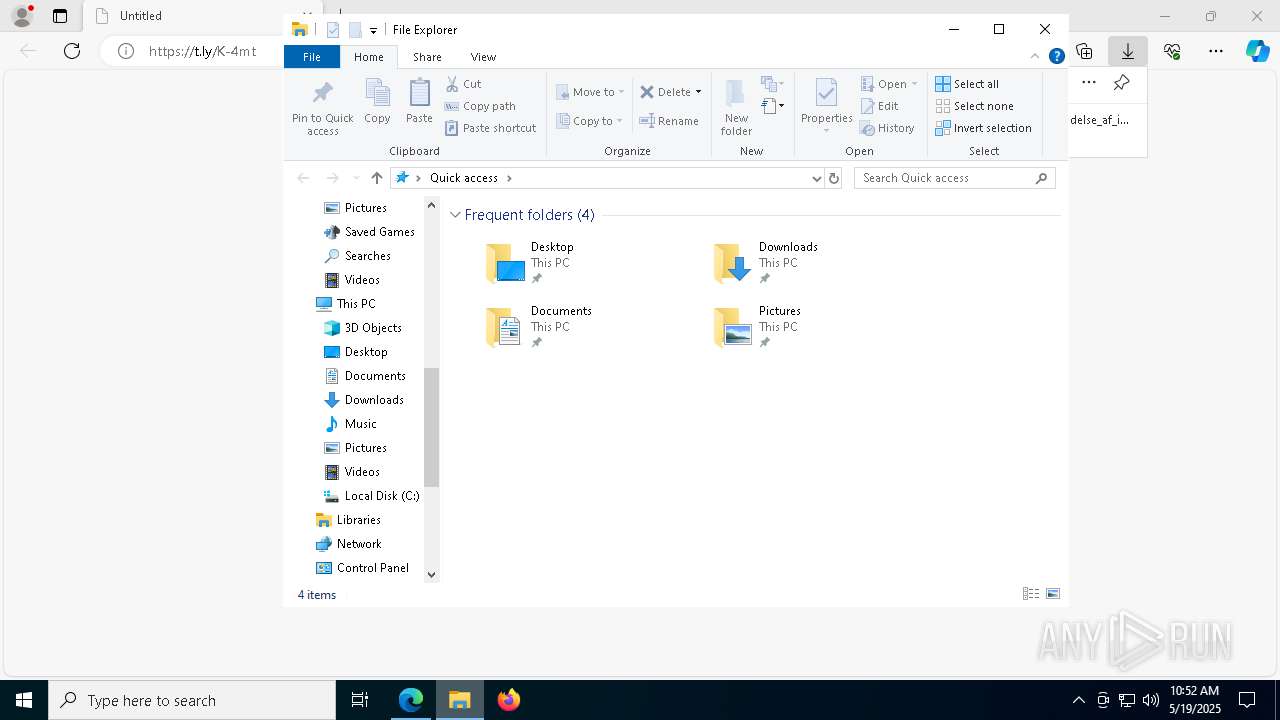
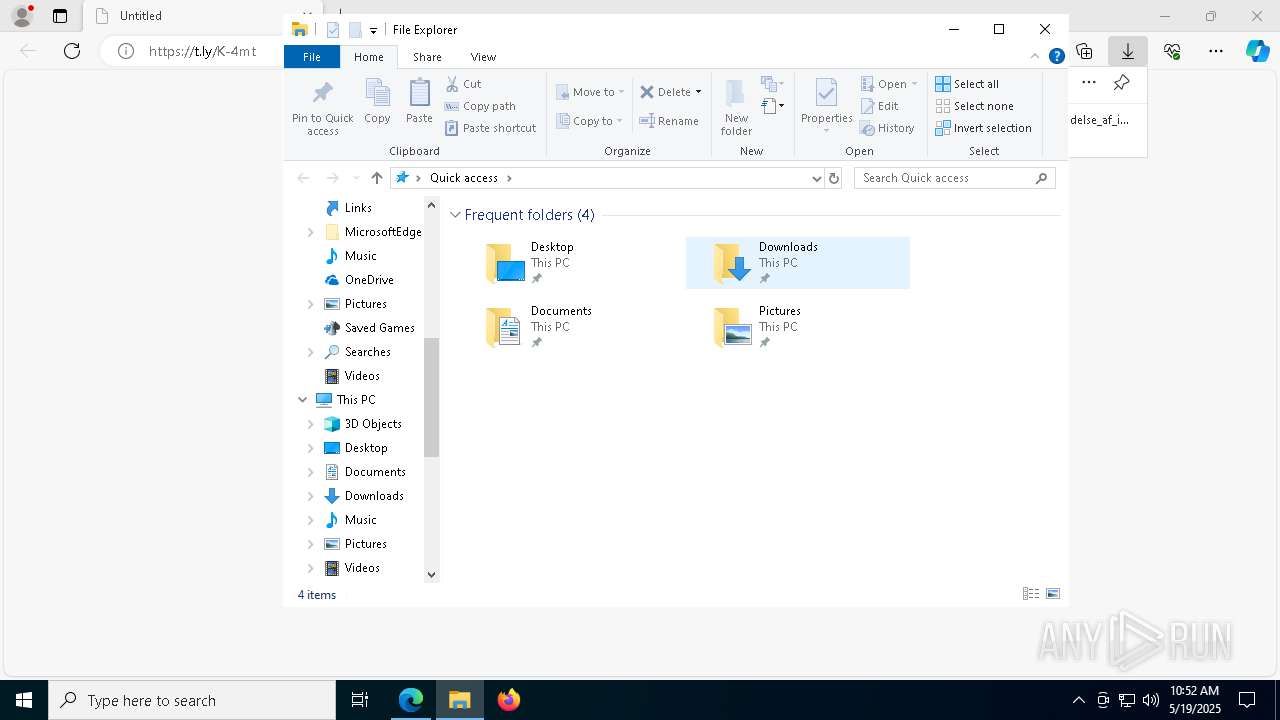
Manual execution by a user
- WinRAR.exe (PID: 8304)
Attempting to use instant messaging service
- svchost.exe (PID: 2196)
- svchost.exe (PID: 8376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
97
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
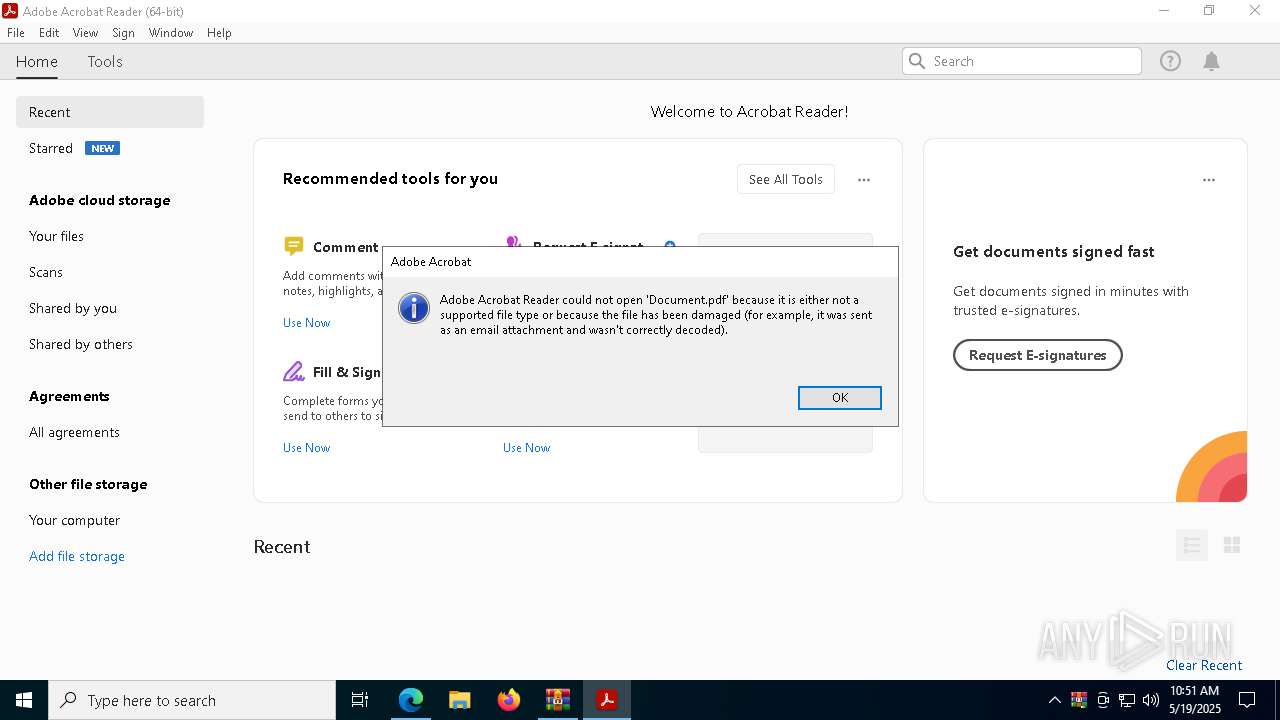
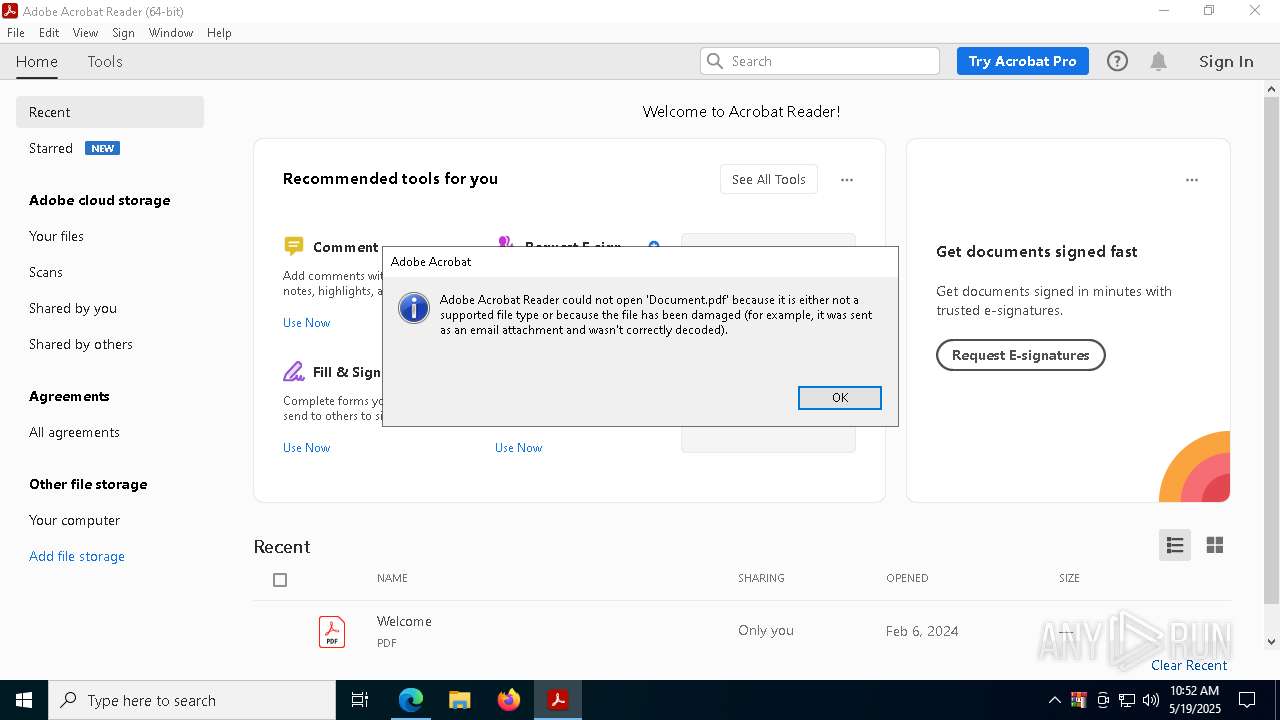
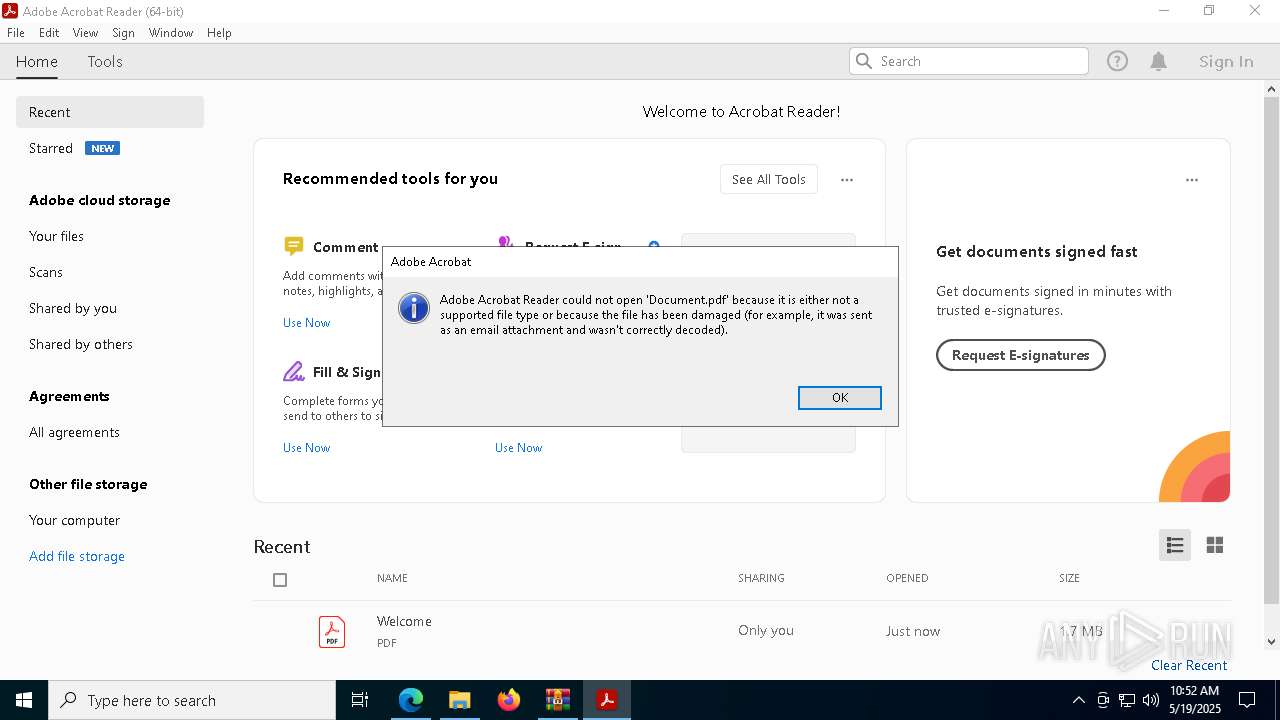
| 208 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" "C:\Users\admin\AppData\Local\Temp\Rar$EXa6740.20403\_\Document.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | cmd.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Exit code: 1 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 728 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2624 --field-trial-handle=1596,i,6039296075763727550,9671742827981305415,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 812 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2608 --field-trial-handle=1596,i,6039296075763727550,9671742827981305415,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 856 | certutil -decode Document.pdf Invoice.pdf | C:\Windows\SysWOW64\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2136 --field-trial-handle=1240,i,6007170412611382356,17036423341056933308,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | AcroCEF.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://t.ly/K-4mt" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=7104 --field-trial-handle=2408,i,18140028074347304226,14265670174031001334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6504 --field-trial-handle=2408,i,18140028074347304226,14265670174031001334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --remote-debugging-port=9923 "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --profile-directory=Default --remote-allow-origins=* --headless | C:\Program Files\Google\Chrome\Application\chrome.exe | — | svchost.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
46 315
Read events
46 001
Write events
295
Delete events
19
Modification events
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 29AD612F11942F00 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8EBD6A2F11942F00 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {11D99452-416A-4793-A7CA-4D985CD550BF} | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C8036FF6-67B4-40E4-A2F6-5AB1CB077F11} | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BA8A962F11942F00 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7B85B572-92AE-4846-8F94-B60D6E69E09D} | |||
Executable files
144
Suspicious files
999
Text files
1 472
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b46d.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b4ac.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b4ac.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b48c.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b4bb.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
70
DNS requests
68
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4068 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4068 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
960 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747700433&P2=404&P3=2&P4=WBy6BMRoxFu2oCg6Hl57eXmJUx%2bzgoPrEVg6Vs2vRM09S8jGnwpi227UCY1ELesGreimOkpLPAEuAbA4bCqH3g%3d%3d | unknown | — | — | whitelisted |
960 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747700433&P2=404&P3=2&P4=WBy6BMRoxFu2oCg6Hl57eXmJUx%2bzgoPrEVg6Vs2vRM09S8jGnwpi227UCY1ELesGreimOkpLPAEuAbA4bCqH3g%3d%3d | unknown | — | — | whitelisted |
960 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747700433&P2=404&P3=2&P4=WBy6BMRoxFu2oCg6Hl57eXmJUx%2bzgoPrEVg6Vs2vRM09S8jGnwpi227UCY1ELesGreimOkpLPAEuAbA4bCqH3g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
976 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7268 | msedge.exe | 104.20.6.133:443 | t.ly | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
t.ly |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
tailieuvp.thongbaotailieuvp.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7268 | msedge.exe | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (t .ly) |
7268 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .ly) |
7268 | msedge.exe | Misc activity | ET INFO Observed URL Shortening Service Domain (t .ly in TLS SNI) |
7268 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .ly) |
7268 | msedge.exe | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (t .ly) |
2196 | svchost.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (is .gd) |
2196 | svchost.exe | Misc activity | INFO [ANY.RUN] Possible short link service (is .gd) |
8376 | svchost.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |