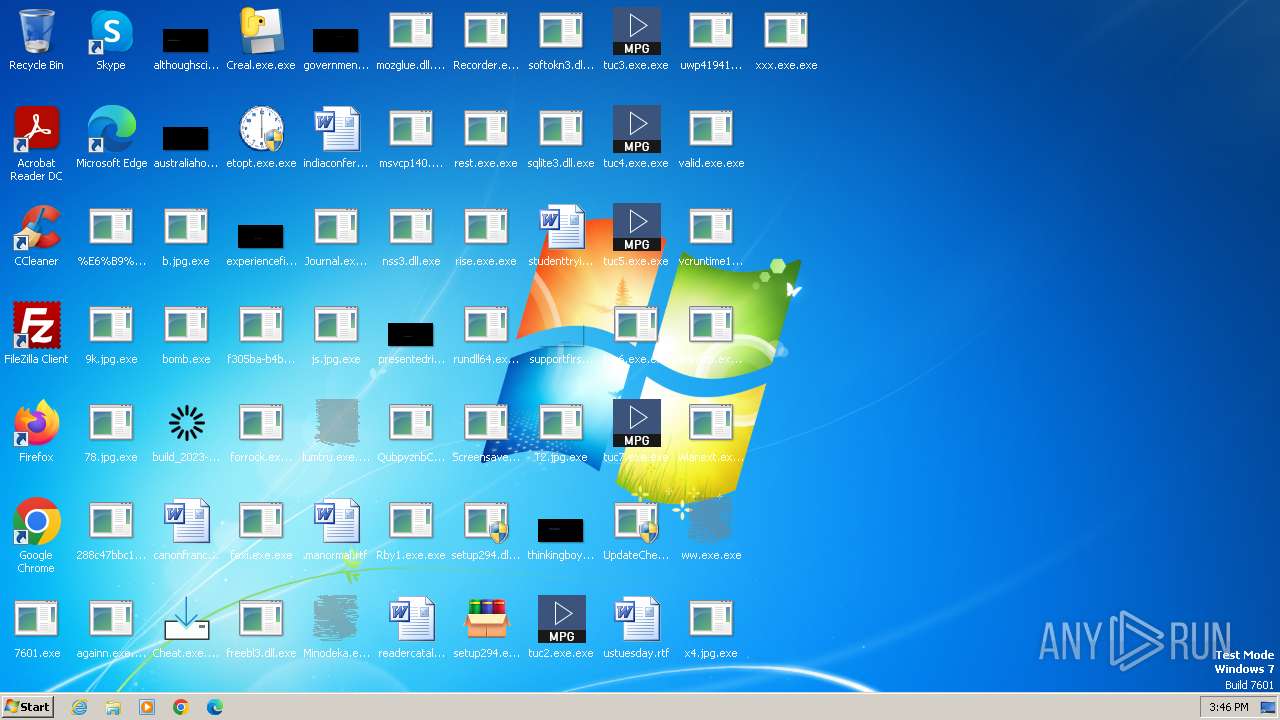
| File name: | bomb.exe |
| Full analysis: | https://app.any.run/tasks/f34b3e65-77d0-46bf-8b13-351b452bfff7 |
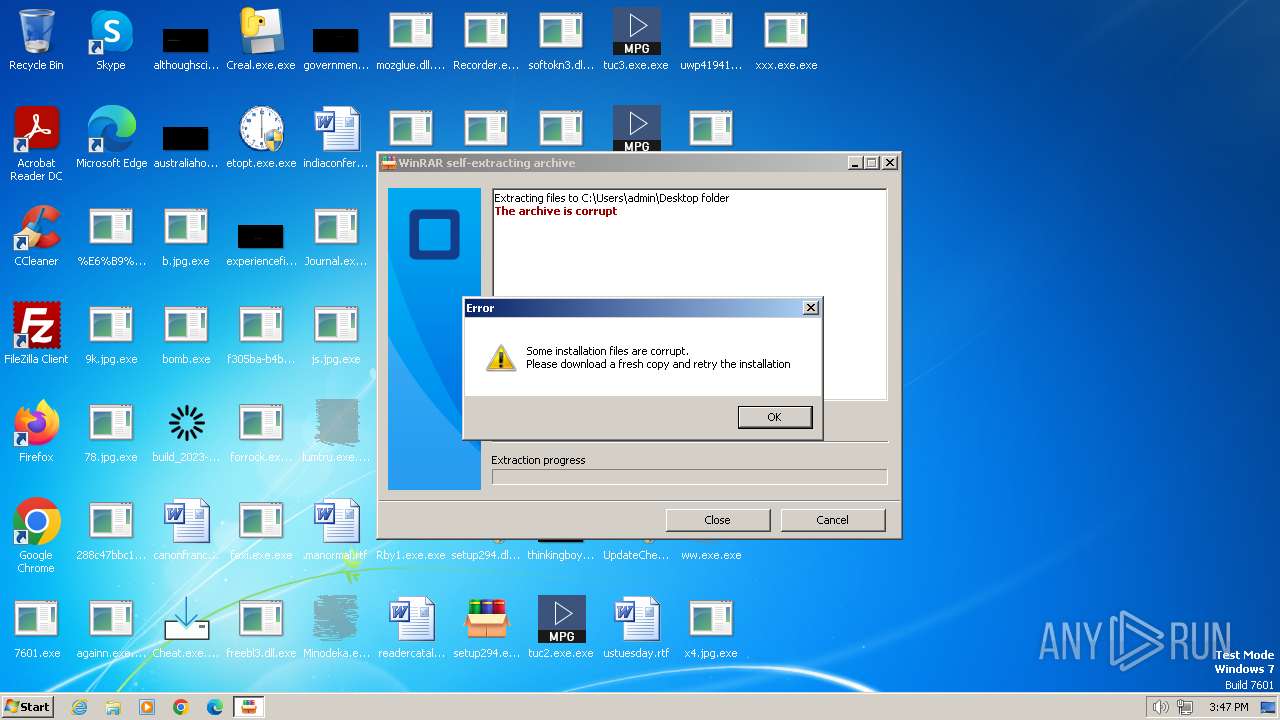
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
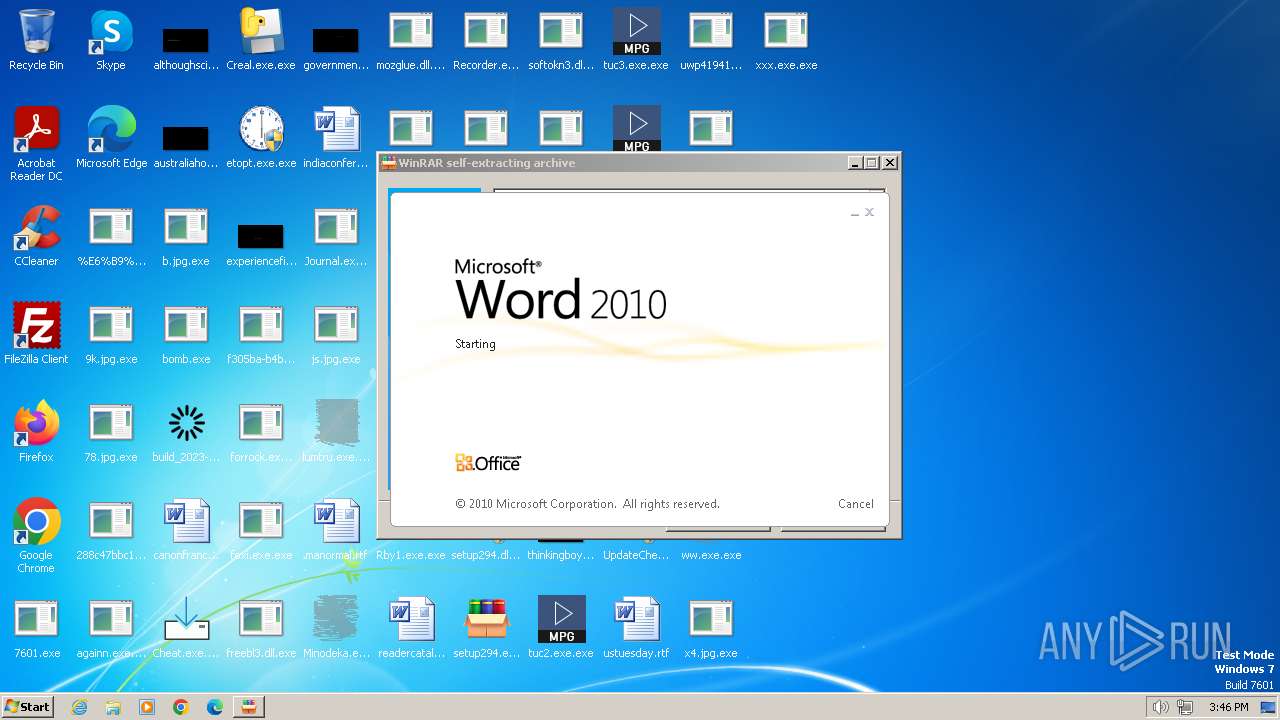
| Analysis date: | December 27, 2023, 15:45:08 |
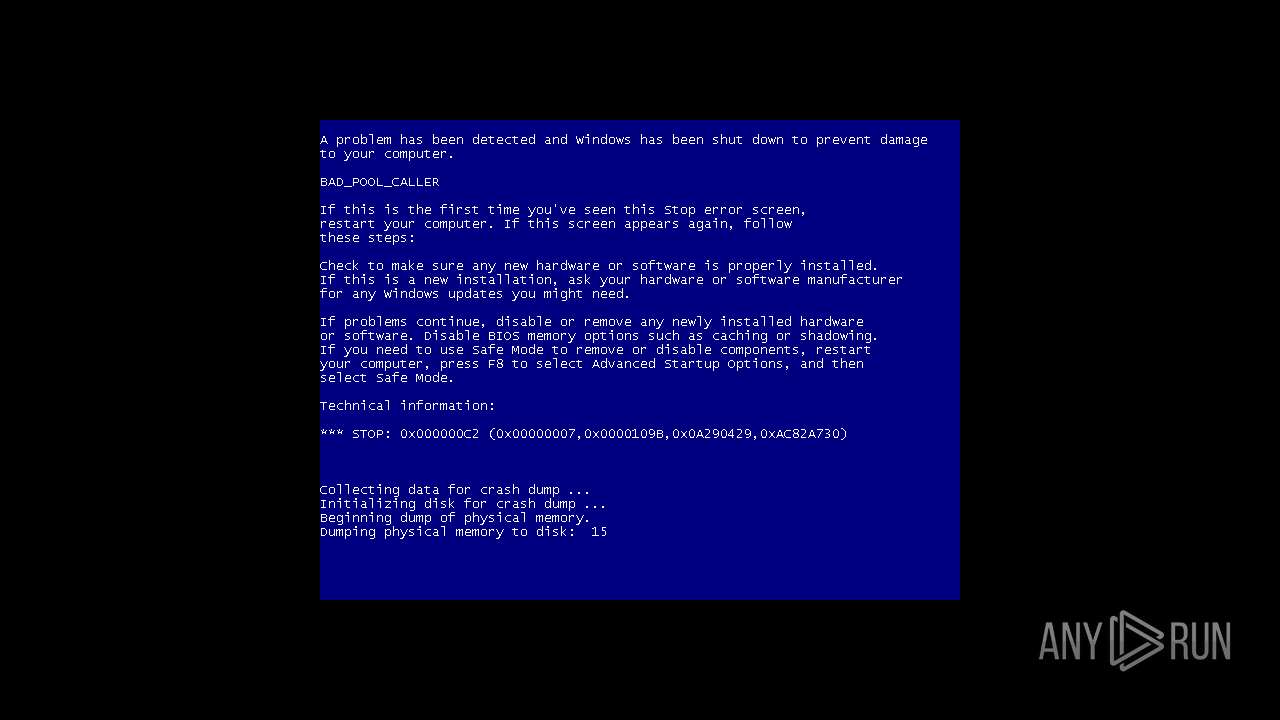
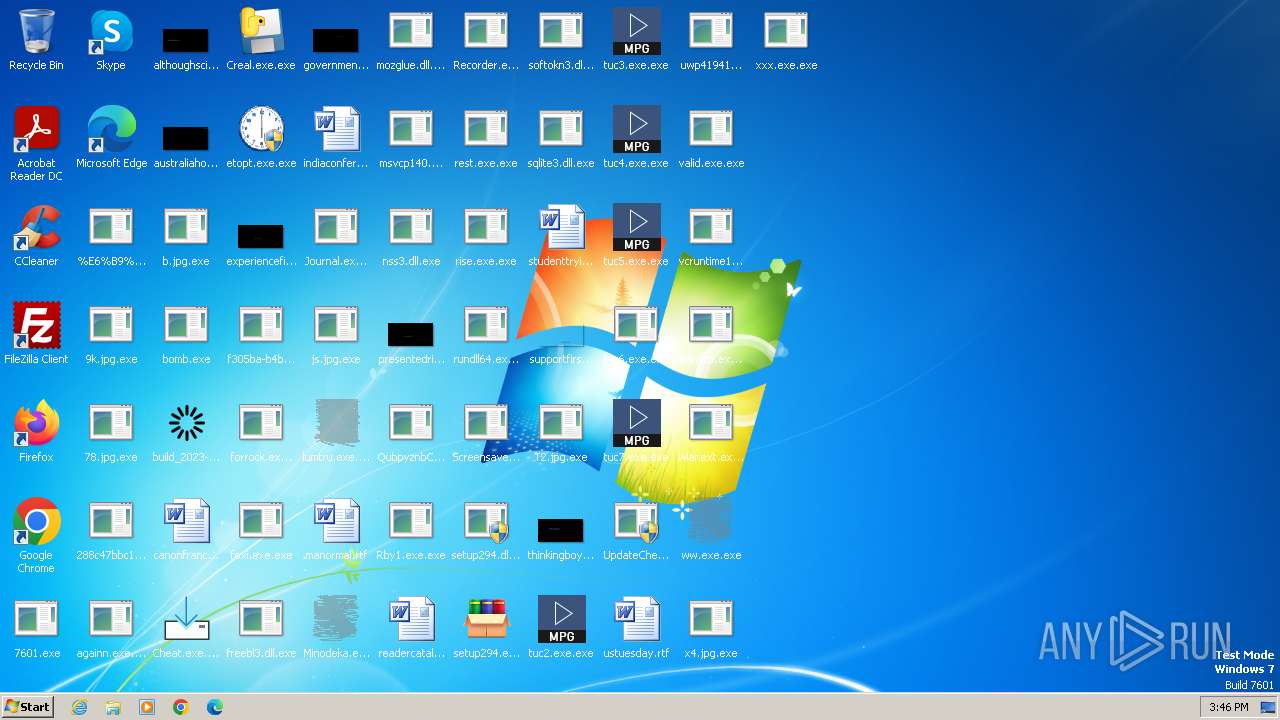
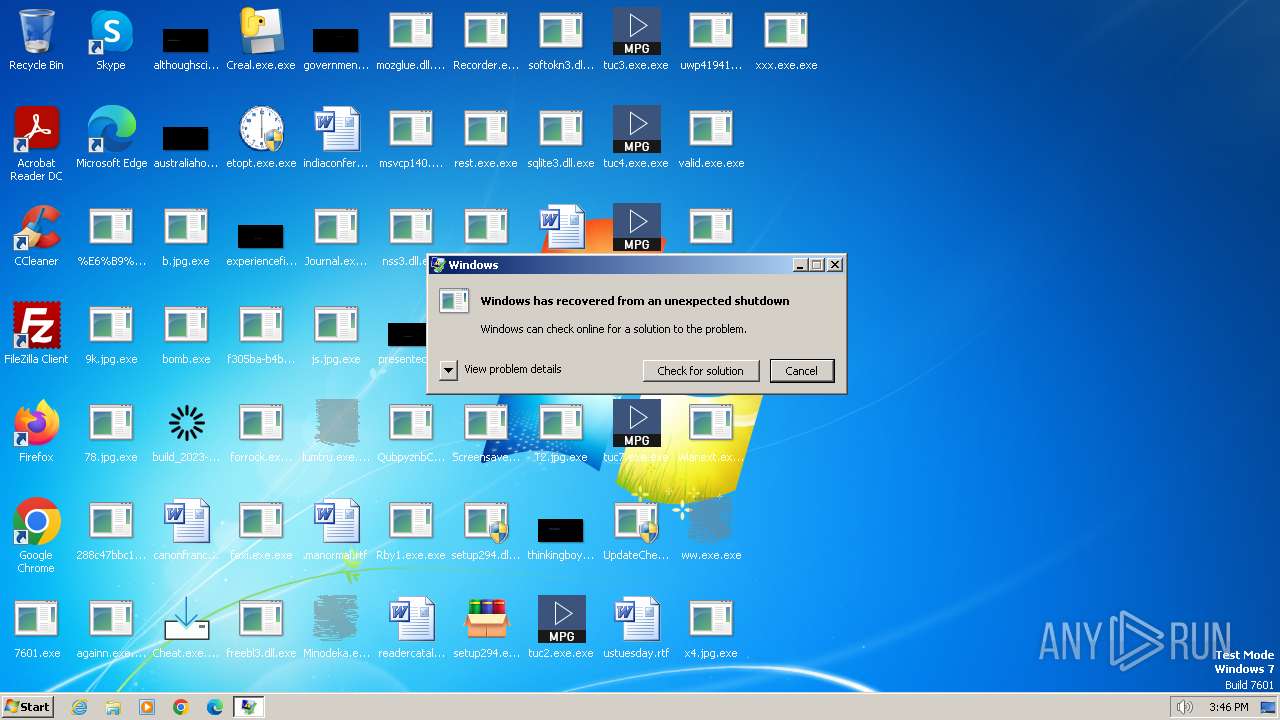
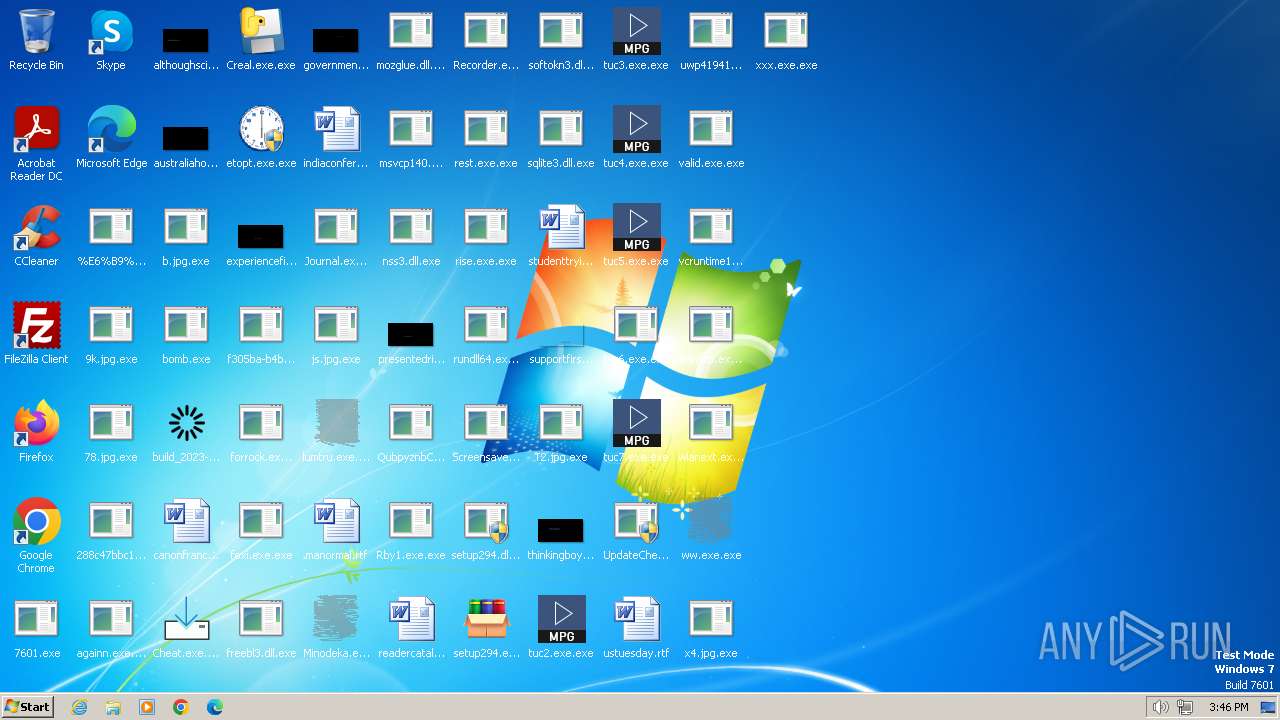
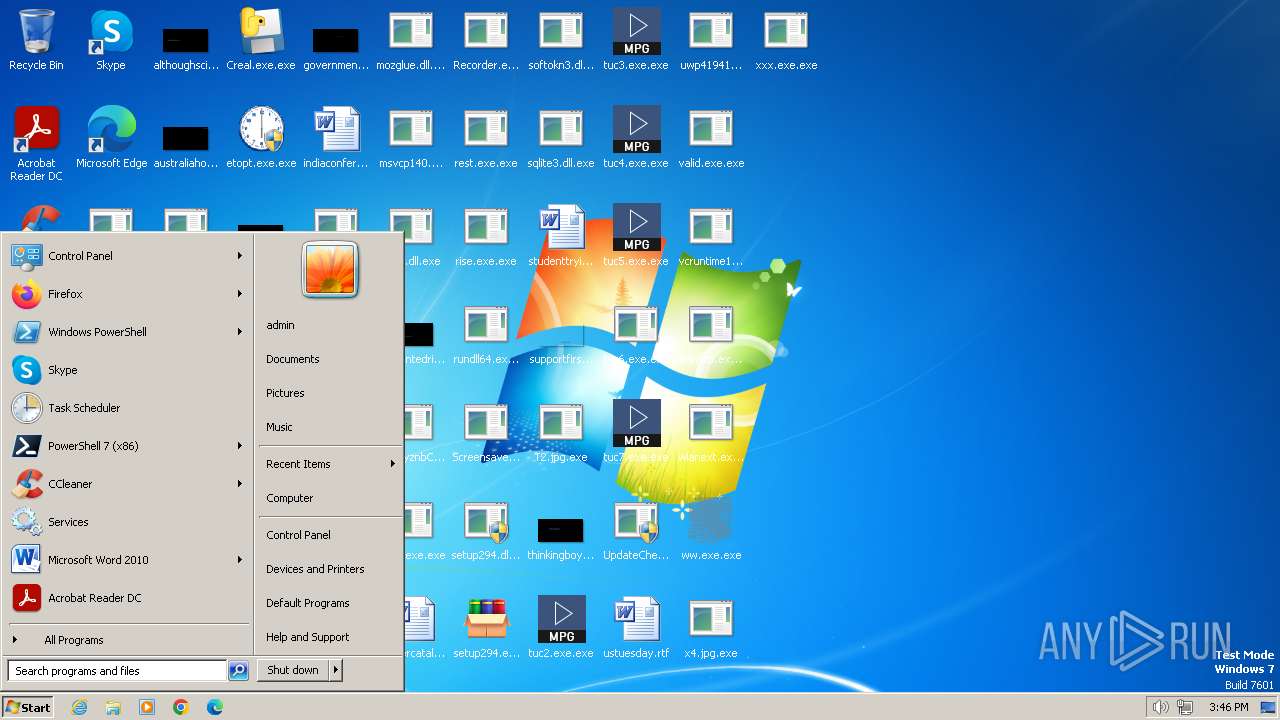
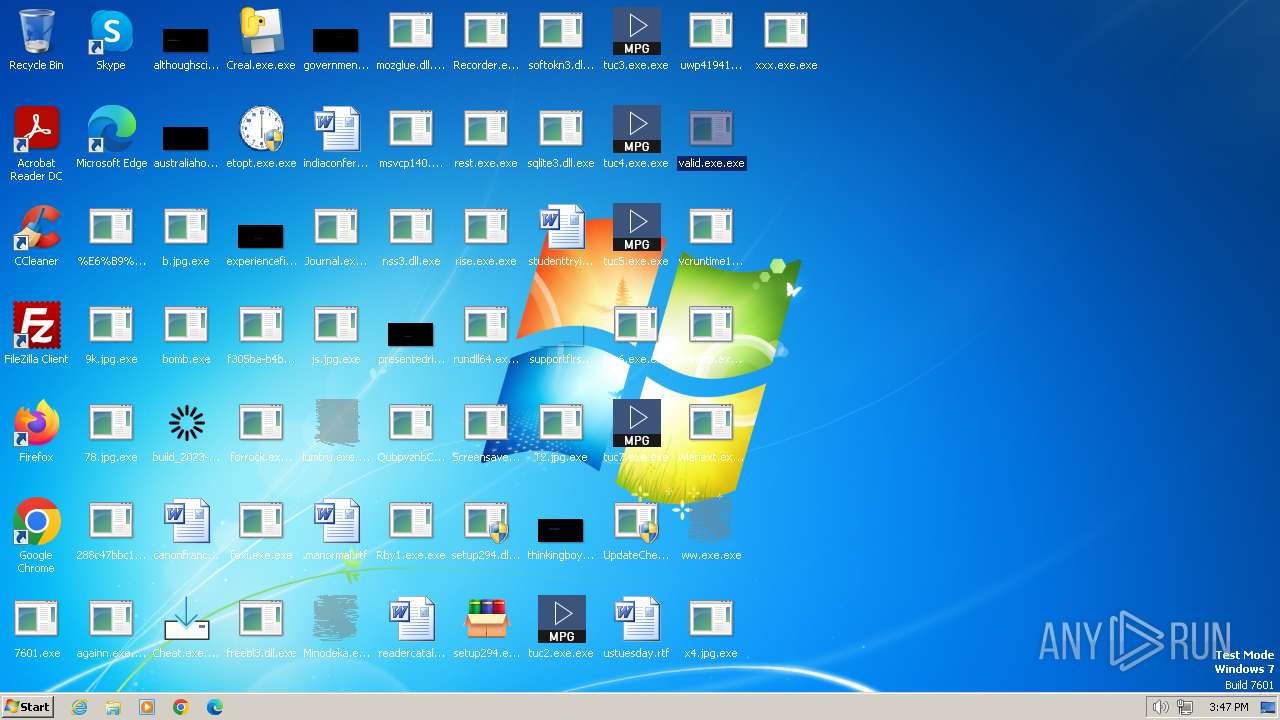
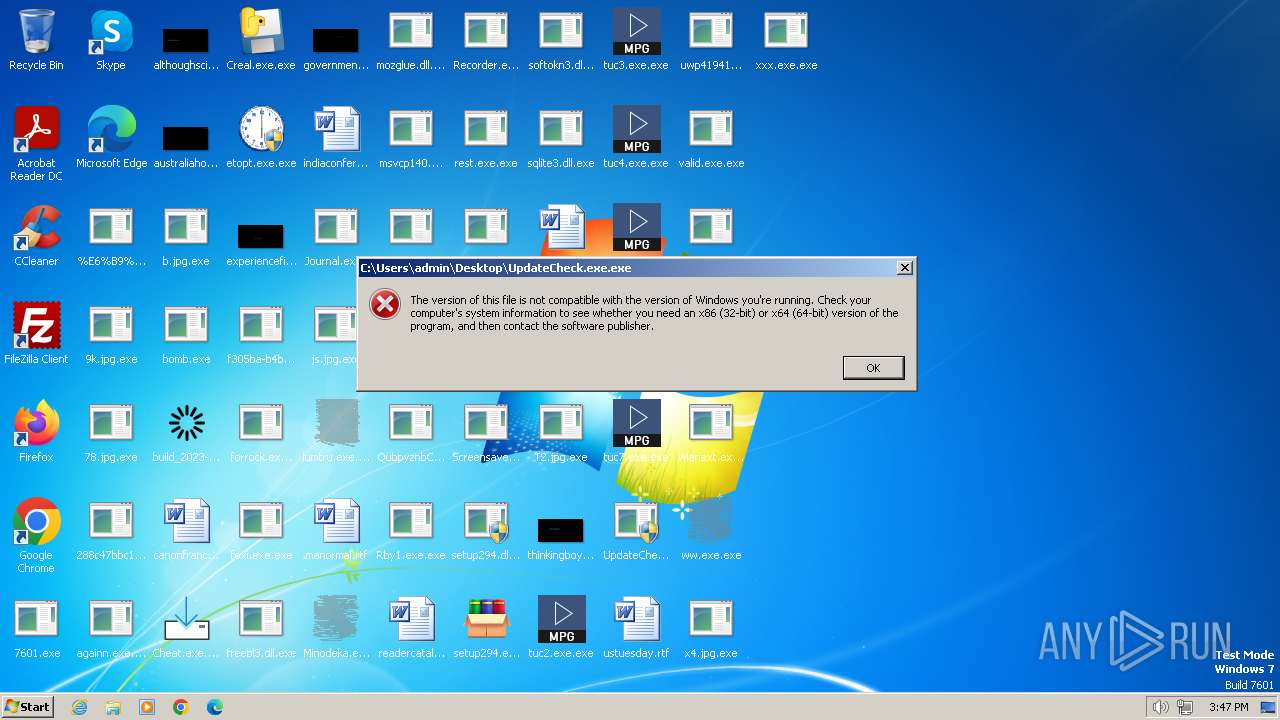
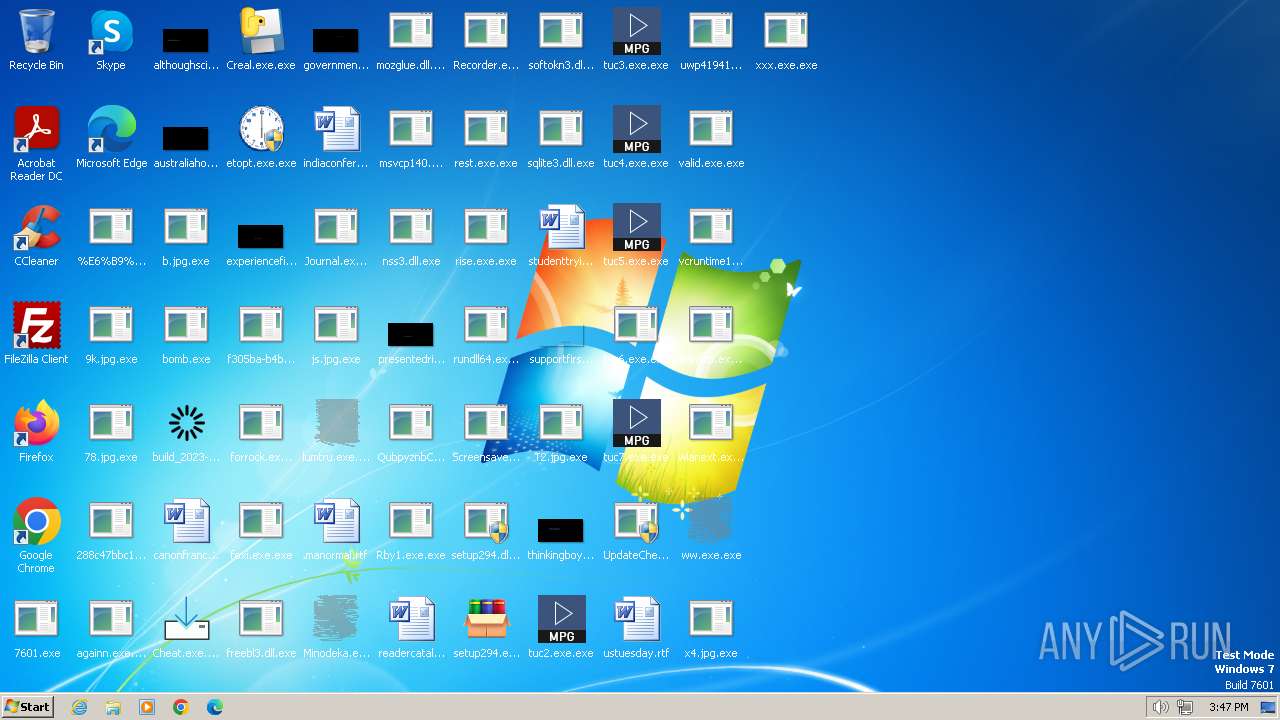
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 59985F4F4E615DDF93EE1DAEAD705F4A |
| SHA1: | DE311E3B268F3D298B9DFEFCB7F816166B7349ED |
| SHA256: | 27AE22ABC89641E340B7E4261632F4689490C44854C4023E564675F18FCE5925 |
| SSDEEP: | 192:5RDRWMWZCWfmYsQrl+SDN+QhtdVr1MeiOLU87glpp/bI6J4ILjyeoIw:JY9DN+cBwOLU870NJ3xoI |
MALICIOUS
METASPLOIT has been detected (SURICATA)
- bomb.exe (PID: 2040)
KELIHOS has been detected (SURICATA)
- bomb.exe (PID: 2040)
Adds path to the Windows Defender exclusion list
- WinScp.exe.exe (PID: 2484)
- Rby1.exe.exe (PID: 3884)
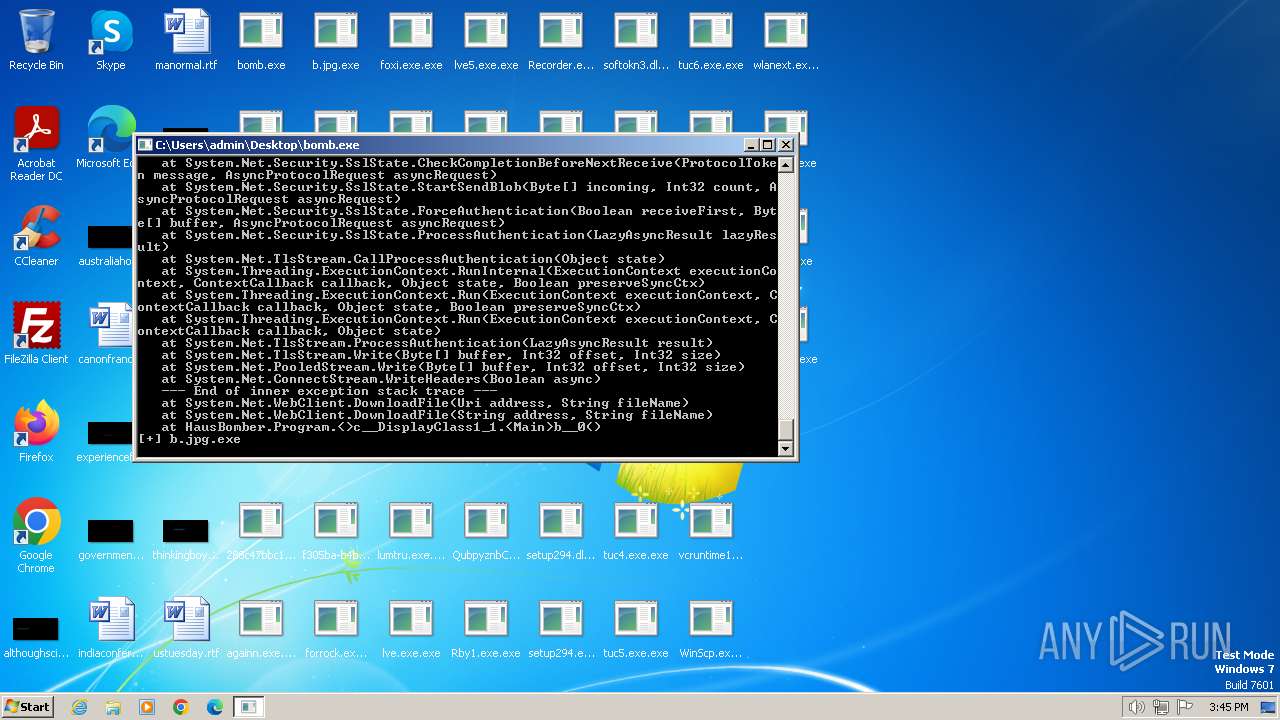
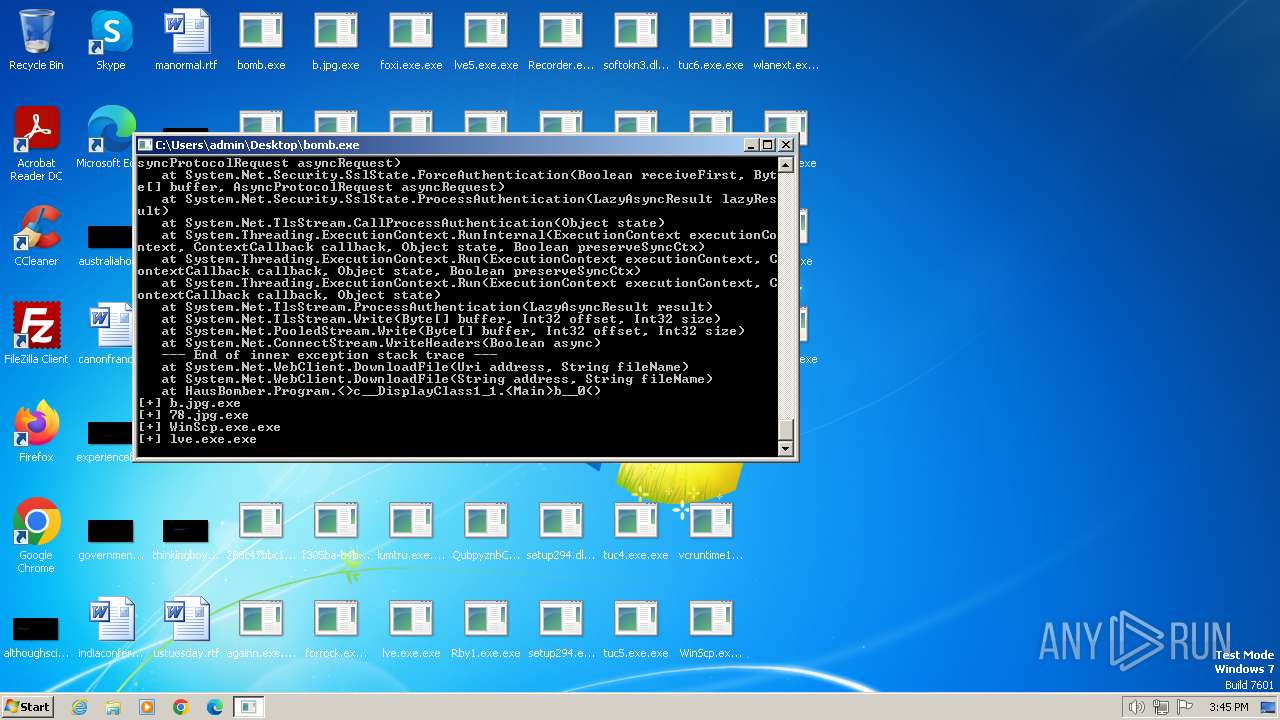
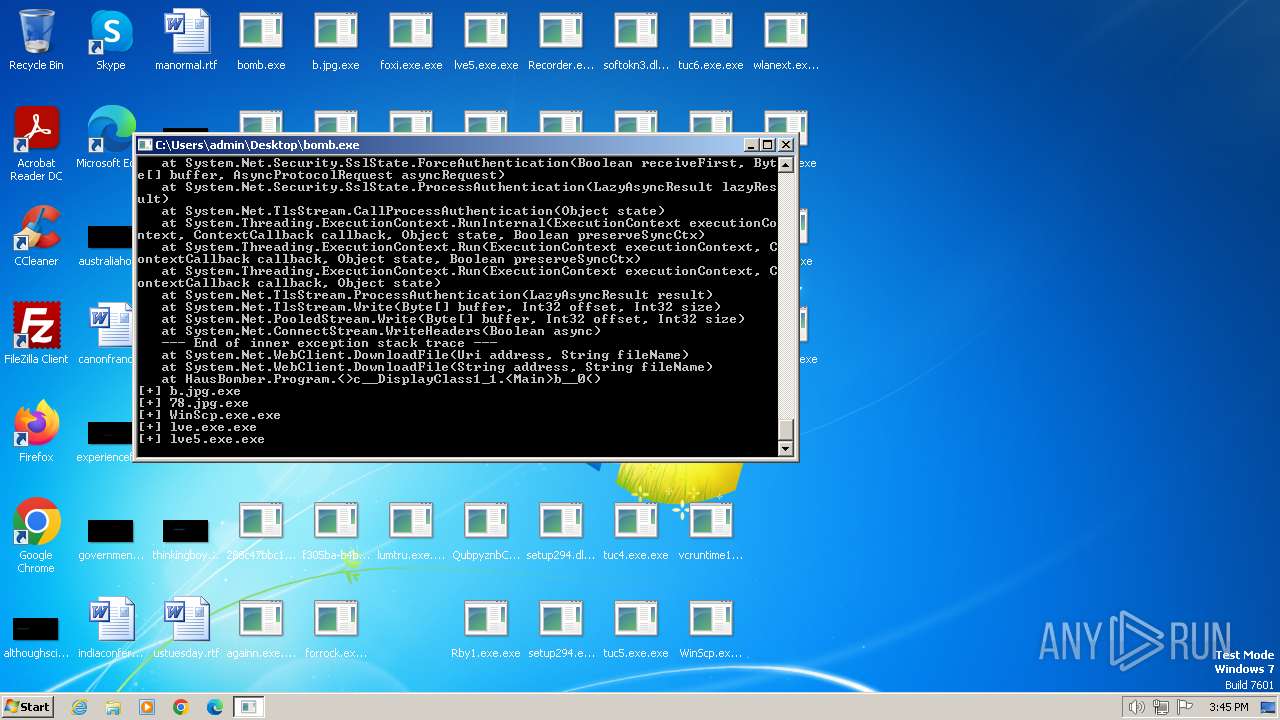
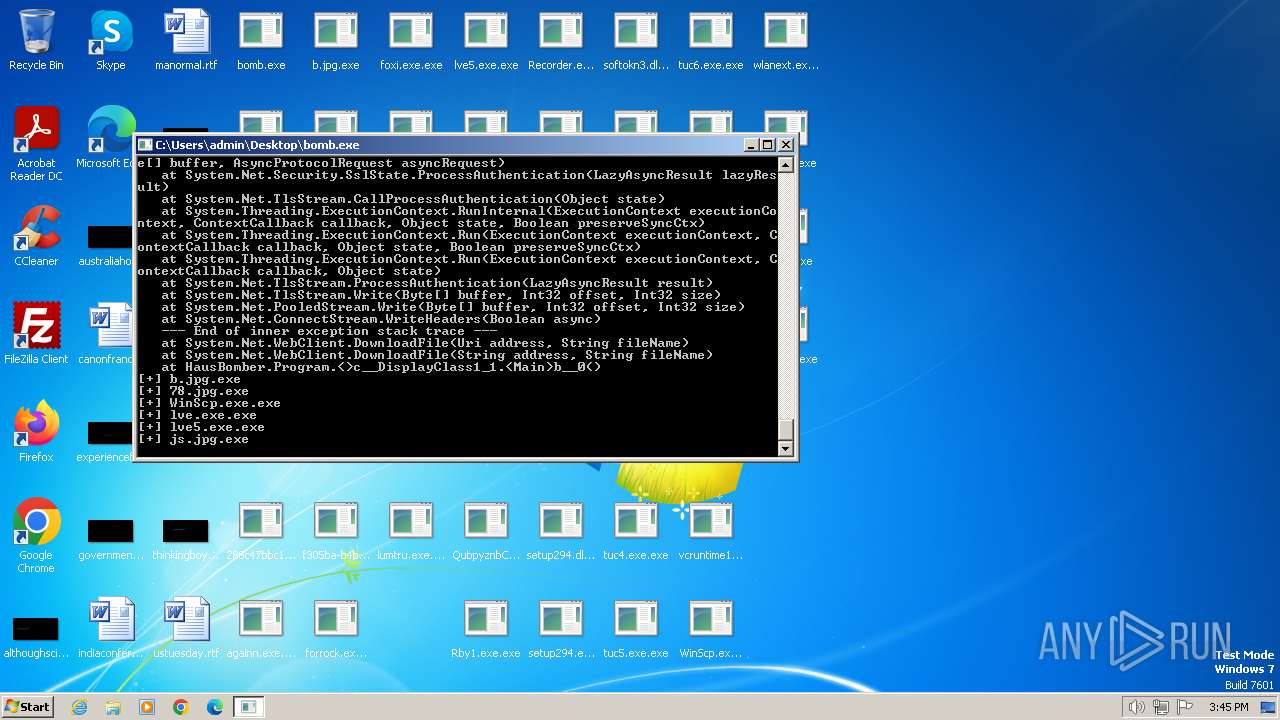
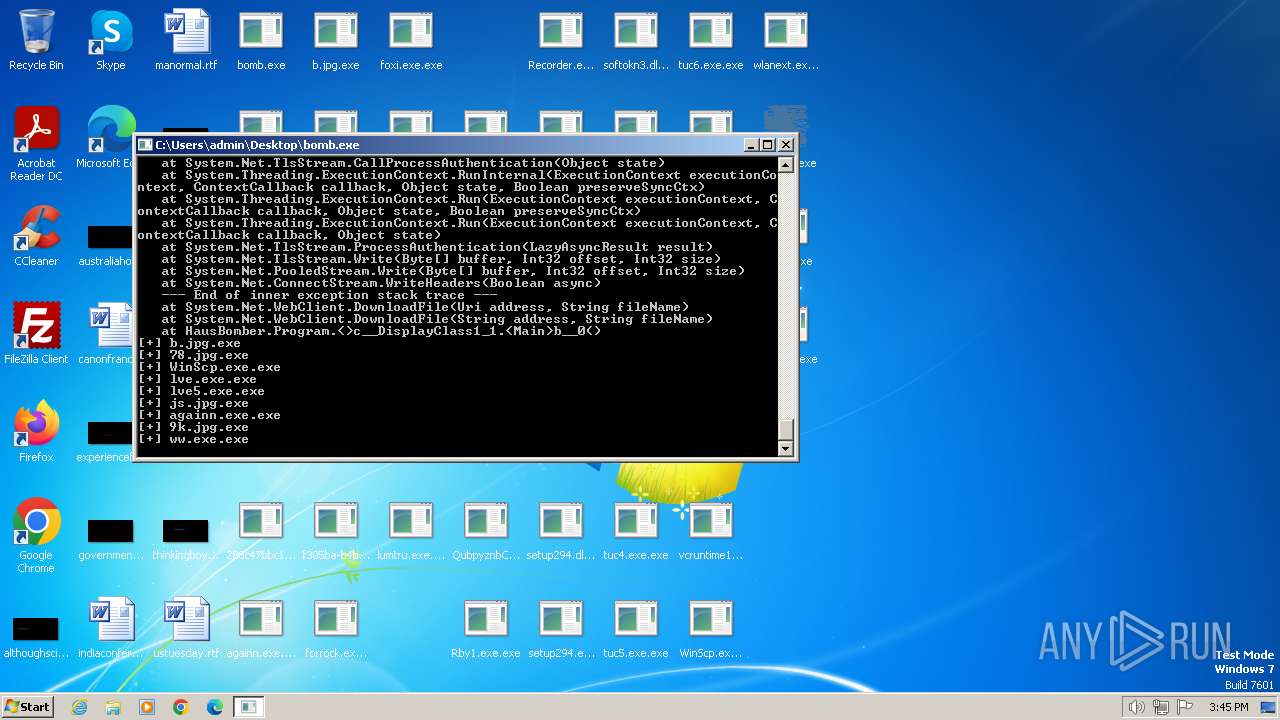
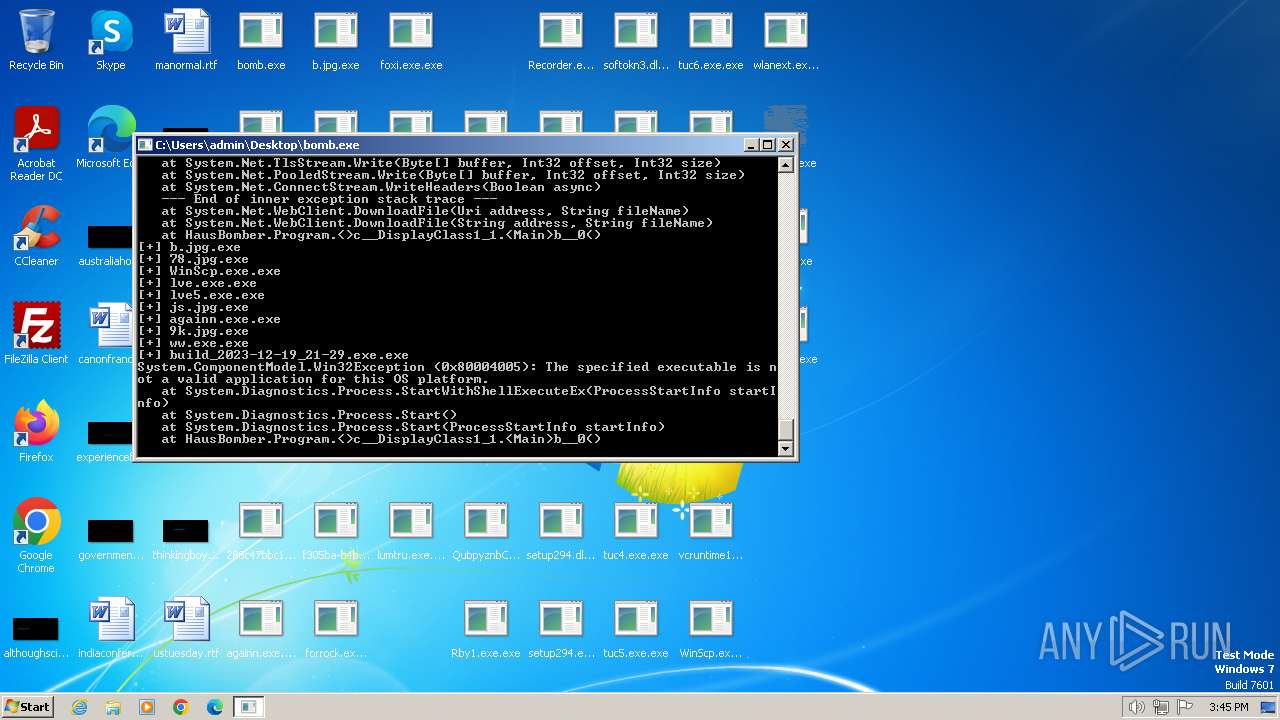
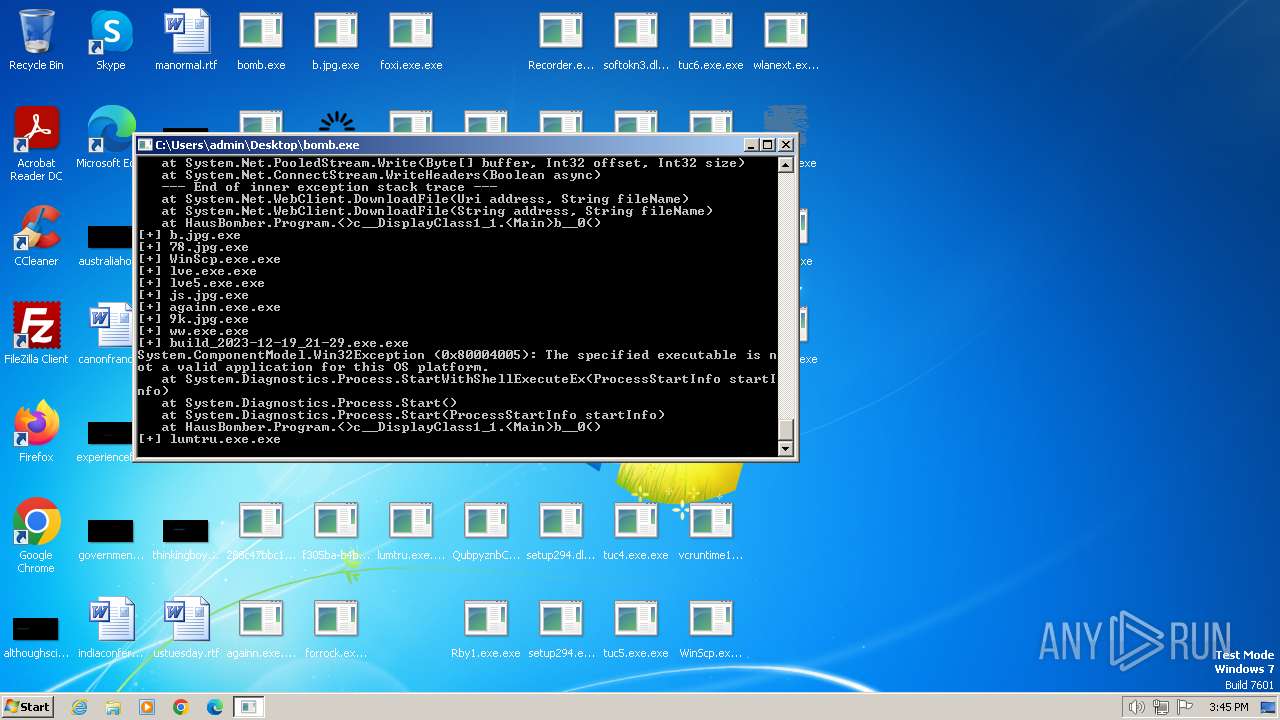
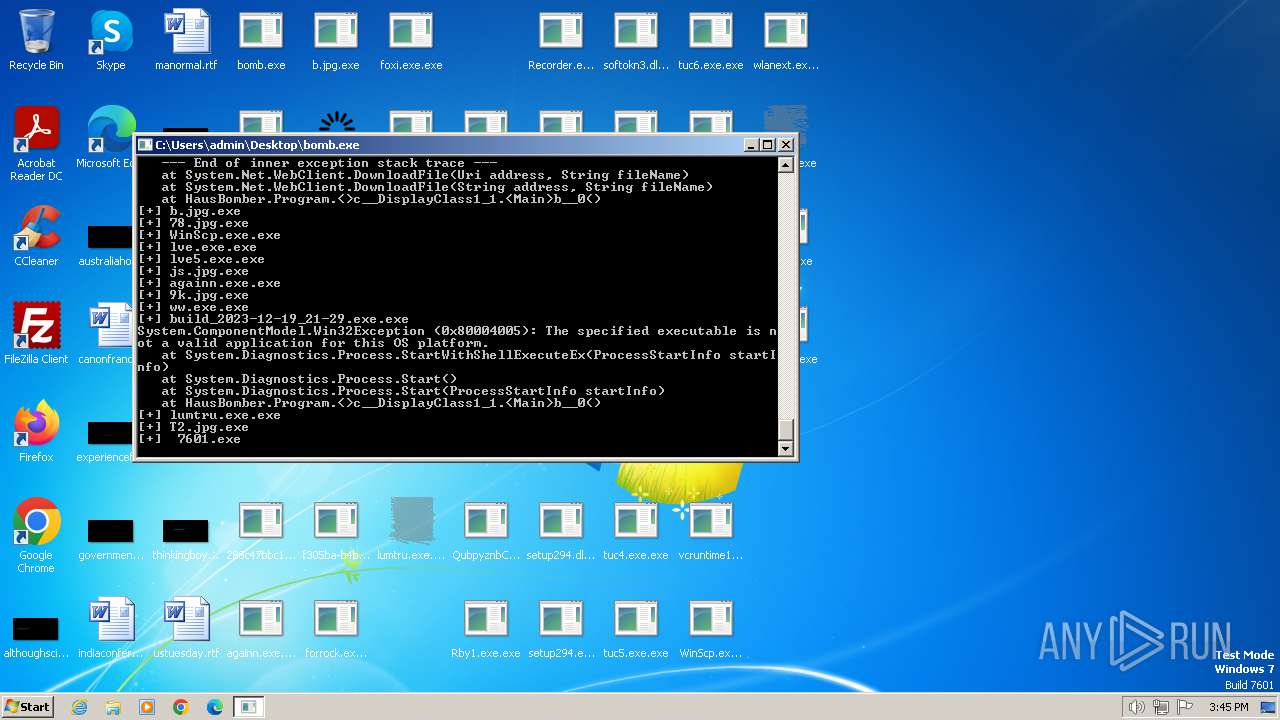
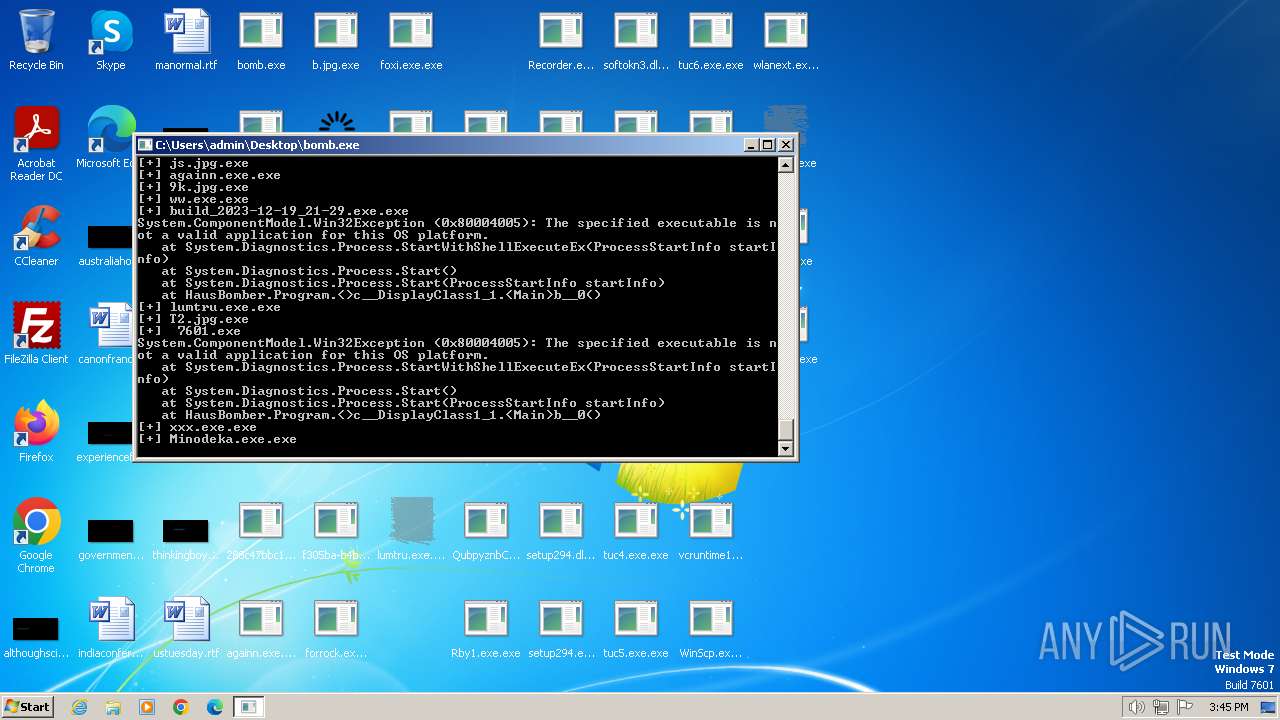
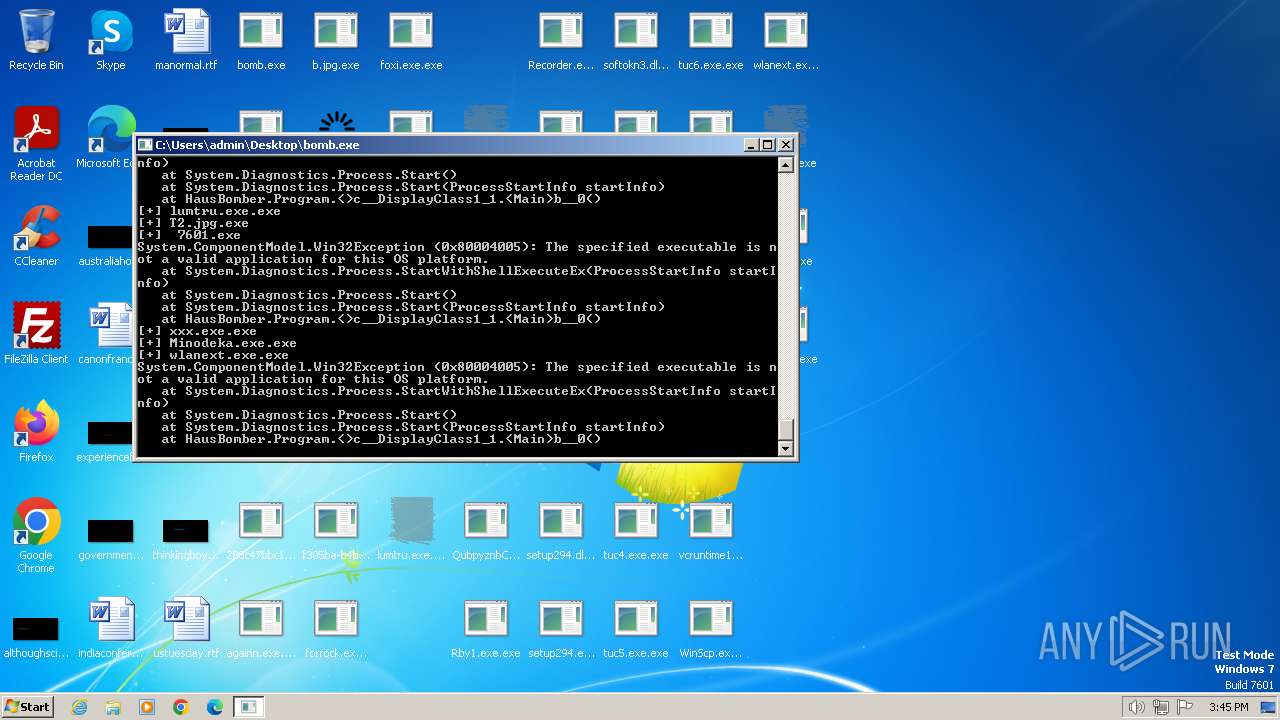
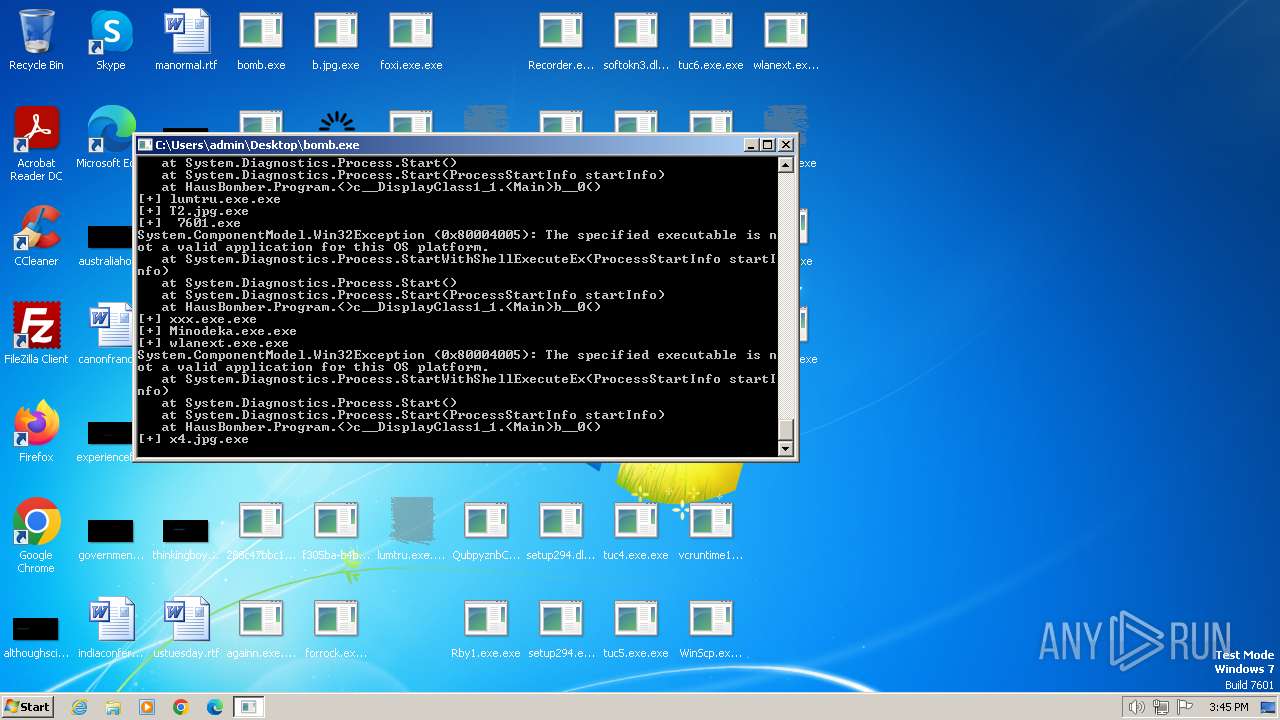
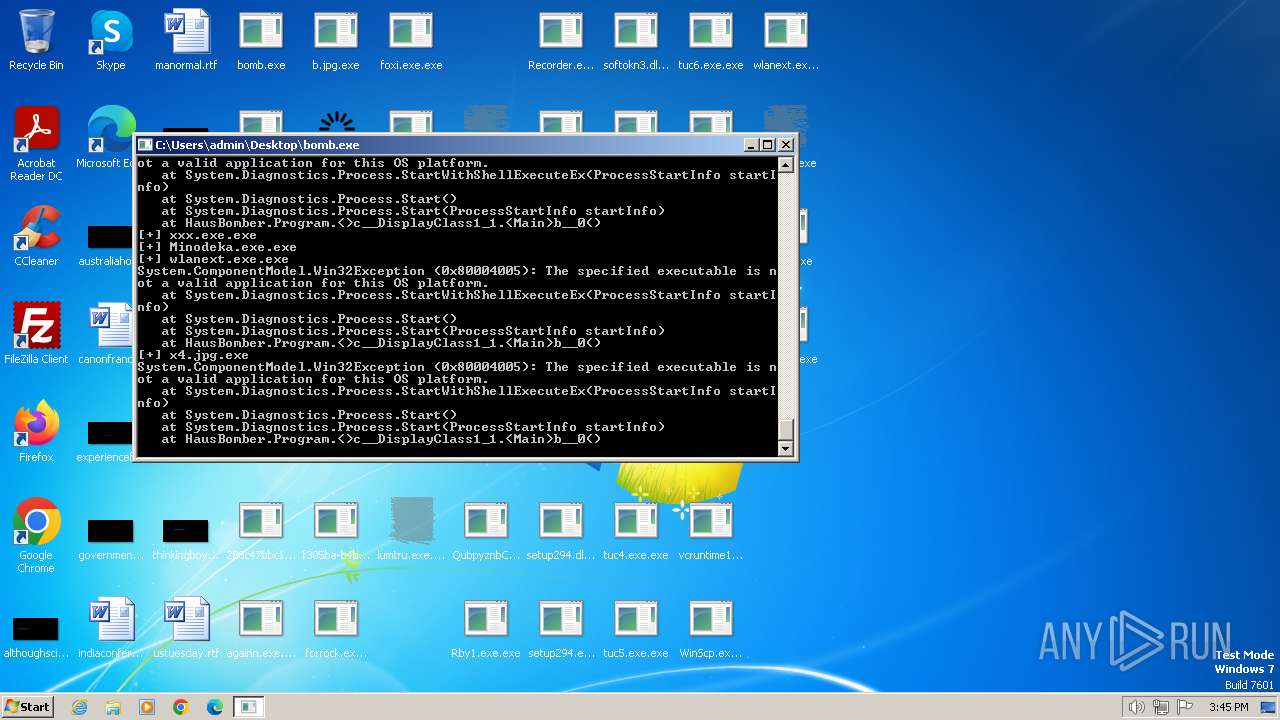
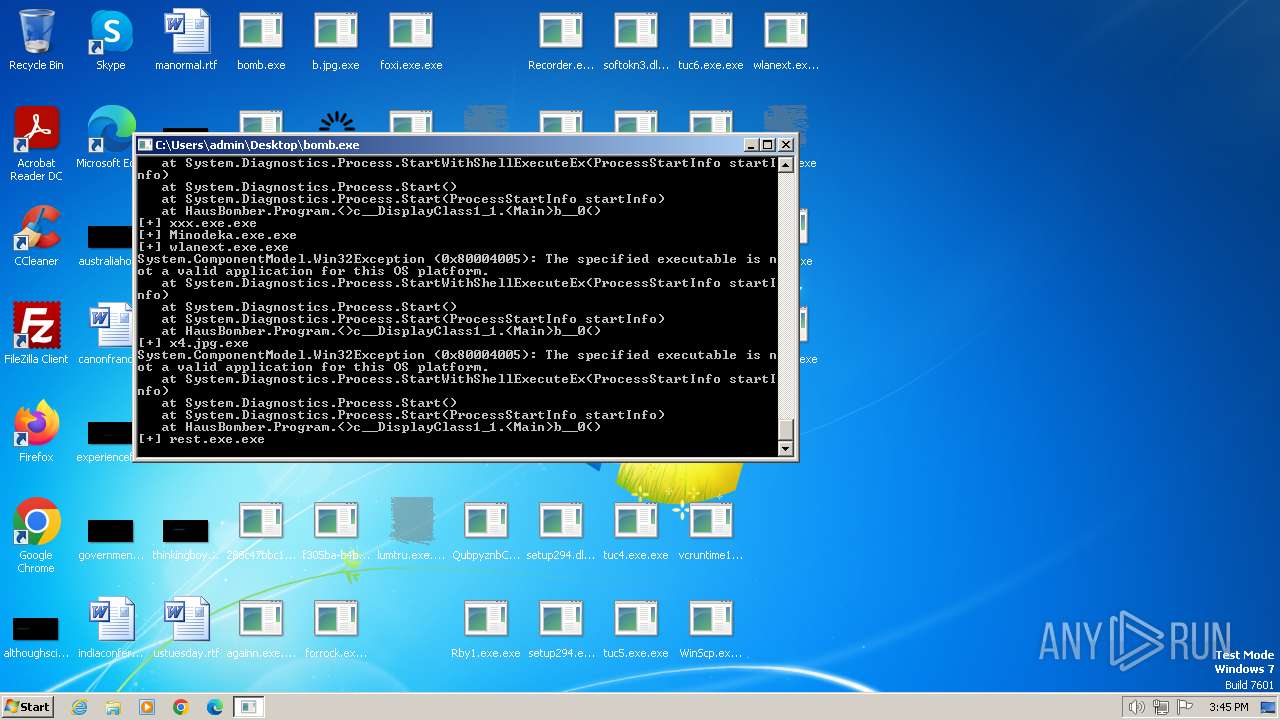
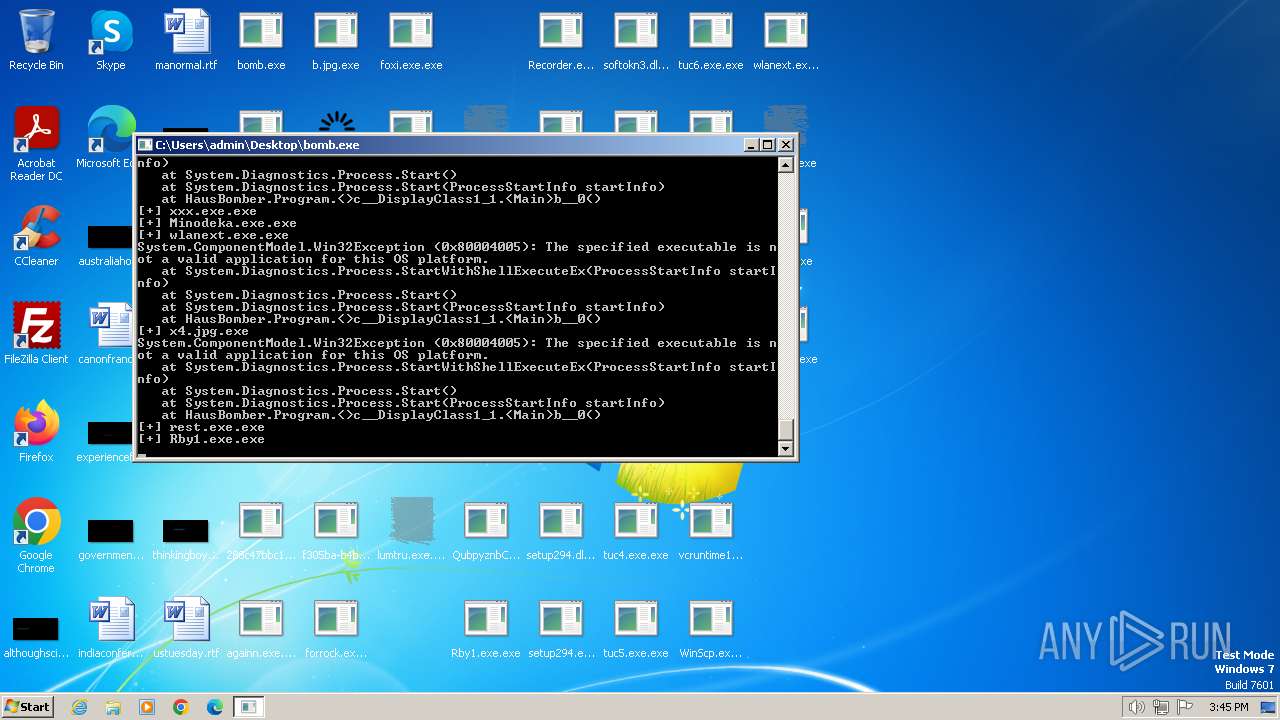
HAUSBOMBER has been detected (YARA)
- bomb.exe (PID: 2040)
Connects to the CnC server
- lve.exe.exe (PID: 2660)
- rest.exe.exe (PID: 3636)
PURPLEFOX has been detected (SURICATA)
- lve.exe.exe (PID: 2660)
LUMMA has been detected (SURICATA)
- lumtru.exe.exe (PID: 3028)
Create files in the Startup directory
- xxx.exe.exe (PID: 2652)
- rest.exe.exe (PID: 3636)
- InstallUtil.exe (PID: 1888)
Risepro uses scheduled tasks to run itself
- cmd.exe (PID: 3684)
- cmd.exe (PID: 3744)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3684)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 3744)
Actions looks like stealing of personal data
- lumtru.exe.exe (PID: 3028)
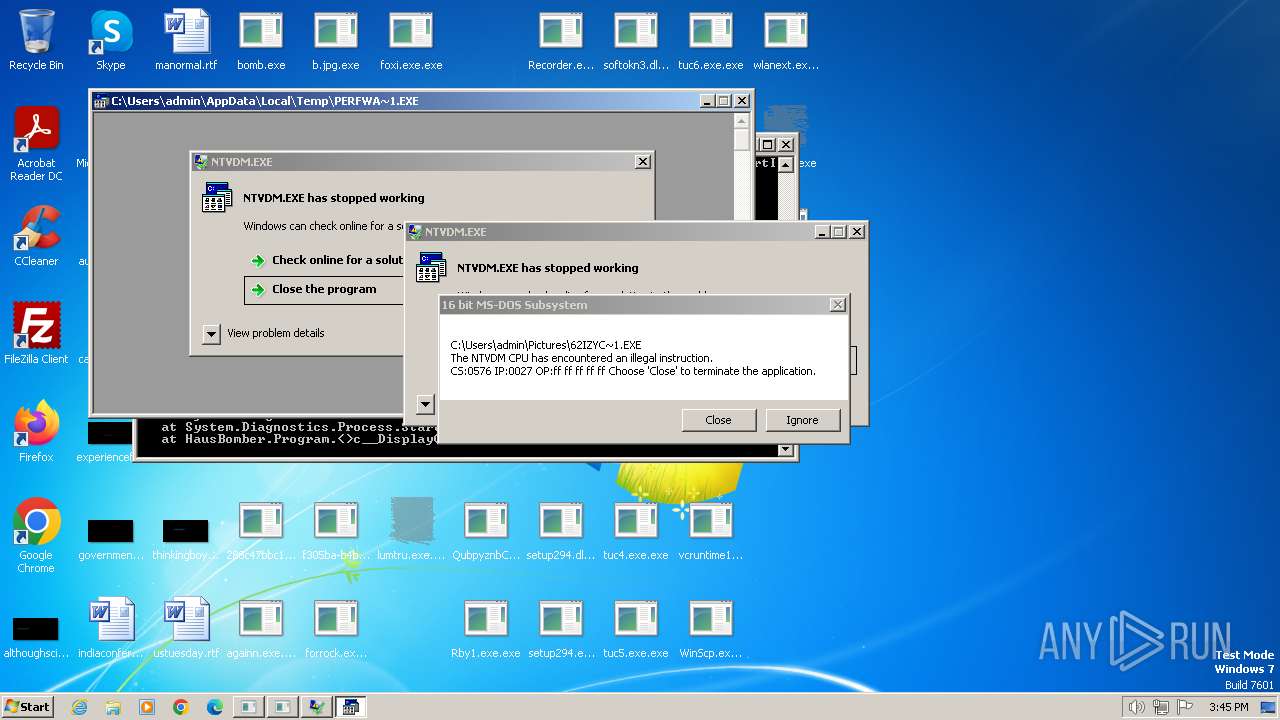
UAC/LUA settings modification
- Rby1.exe.exe (PID: 3884)
NITOL has been detected (YARA)
- lve.exe.exe (PID: 2660)
RISEPRO has been detected (SURICATA)
- rest.exe.exe (PID: 3636)
SUSPICIOUS
Reads the Internet Settings
- bomb.exe (PID: 2040)
- WinScp.exe.exe (PID: 2484)
- POWERSHELL.exe (PID: 2316)
- Rby1.exe.exe (PID: 3884)
- InstallUtil.exe (PID: 1888)
- powershell.exe (PID: 2136)
- f305ba-b4b69ab5.exe.exe (PID: 2336)
- 1IE77zf7.exe (PID: 2904)
- 3Az54zw.exe (PID: 2060)
Connects to unusual port
- bomb.exe (PID: 2040)
- Screensaver.exe.exe (PID: 1656)
- lve.exe.exe (PID: 2660)
- build_2023-12-19_21-29.exe.exe (PID: 1484)
- againn.exe.exe (PID: 2496)
- Minodeka.exe.exe (PID: 3240)
- RegAsm.exe (PID: 3104)
- rest.exe.exe (PID: 3636)
Reads settings of System Certificates
- bomb.exe (PID: 2040)
- InstallUtil.exe (PID: 1888)
- f305ba-b4b69ab5.exe.exe (PID: 2336)
Connects to the server without a host name
- bomb.exe (PID: 2040)
- WinScp.exe.exe (PID: 2484)
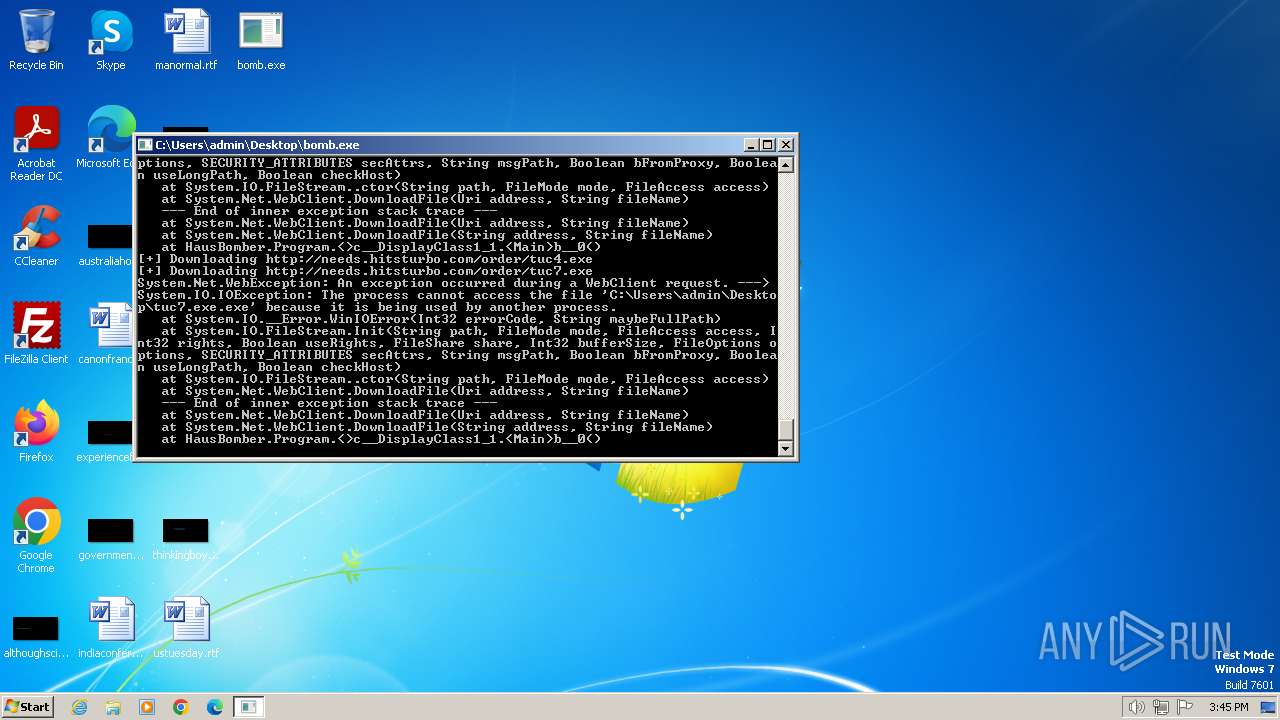
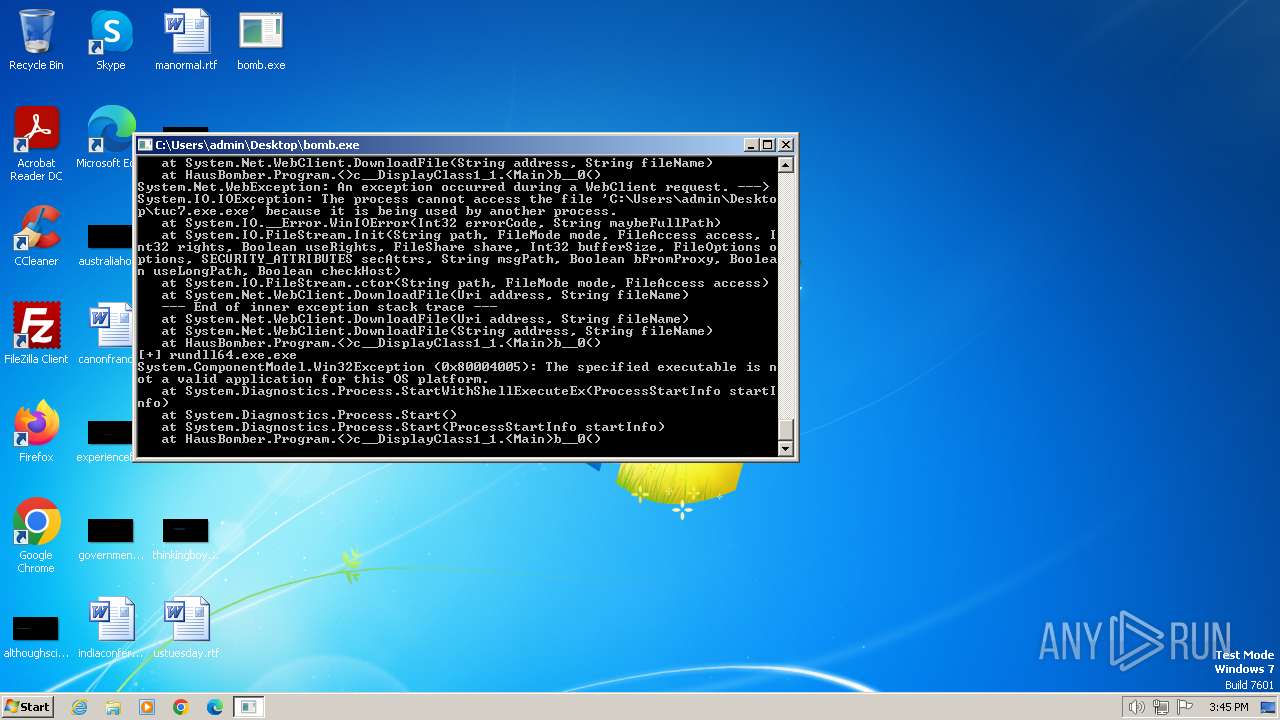
Process requests binary or script from the Internet
- bomb.exe (PID: 2040)
Starts POWERSHELL.EXE for commands execution
- WinScp.exe.exe (PID: 2484)
- Rby1.exe.exe (PID: 3884)
Script adds exclusion path to Windows Defender
- WinScp.exe.exe (PID: 2484)
- Rby1.exe.exe (PID: 3884)
Starts CMD.EXE for commands execution
- rest.exe.exe (PID: 3636)
Reads security settings of Internet Explorer
- WinScp.exe.exe (PID: 2484)
Reads browser cookies
- lumtru.exe.exe (PID: 3028)
Checks Windows Trust Settings
- WinScp.exe.exe (PID: 2484)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2136)
Searches for installed software
- lumtru.exe.exe (PID: 3028)
INFO
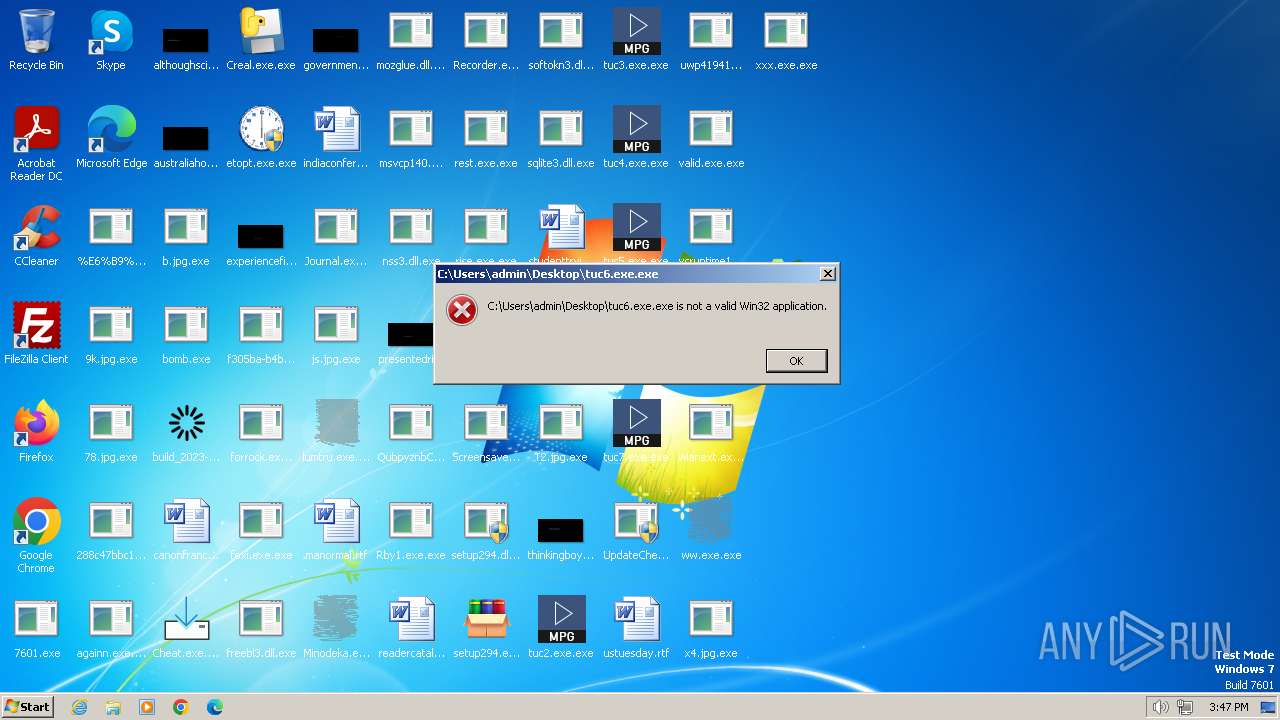
Checks supported languages
- bomb.exe (PID: 2040)
- Screensaver.exe.exe (PID: 1656)
- rundll64.exe.exe (PID: 1924)
- lve.exe.exe (PID: 2660)
- WinScp.exe.exe (PID: 2484)
- lve5.exe.exe (PID: 2488)
- againn.exe.exe (PID: 2496)
- ww.exe.exe (PID: 2964)
- build_2023-12-19_21-29.exe.exe (PID: 1484)
- lumtru.exe.exe (PID: 3028)
- xxx.exe.exe (PID: 2652)
- Minodeka.exe.exe (PID: 3240)
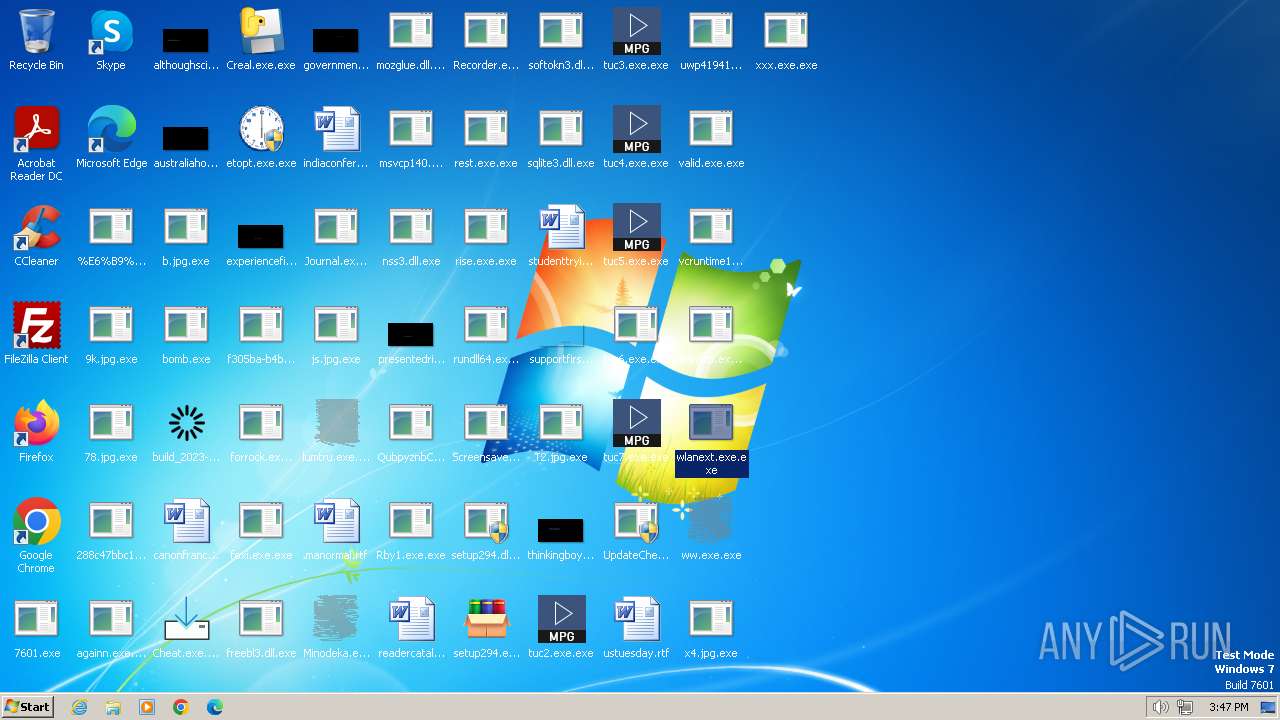
- wlanext.exe.exe (PID: 3328)
- rest.exe.exe (PID: 3636)
- RegAsm.exe (PID: 3104)
- Rby1.exe.exe (PID: 3884)
- InstallUtil.exe (PID: 1888)
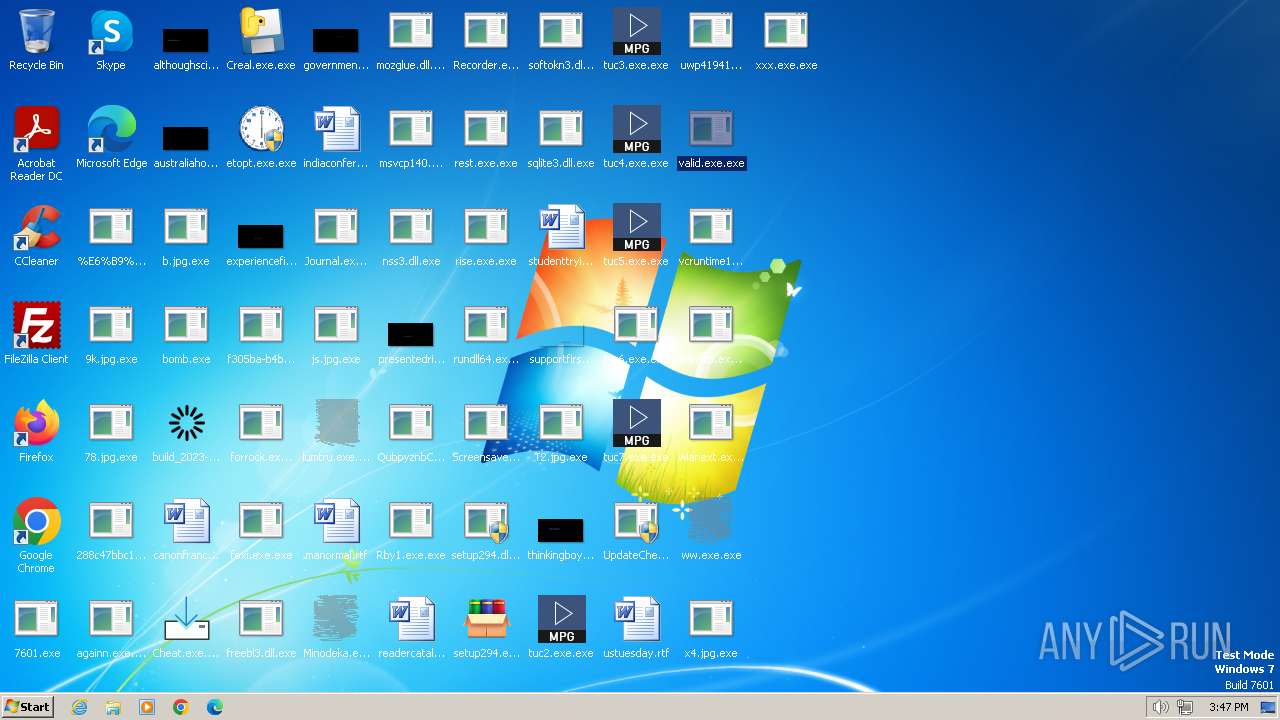
- valid.exe.exe (PID: 1556)
- ww7qm33.exe (PID: 560)
- 1IE77zf7.exe (PID: 2904)
- f305ba-b4b69ab5.exe.exe (PID: 2336)
- 3Az54zw.exe (PID: 2060)
- 4Oa386lk.exe (PID: 568)
Reads the machine GUID from the registry
- bomb.exe (PID: 2040)
- againn.exe.exe (PID: 2496)
- build_2023-12-19_21-29.exe.exe (PID: 1484)
- WinScp.exe.exe (PID: 2484)
- xxx.exe.exe (PID: 2652)
- Minodeka.exe.exe (PID: 3240)
- wlanext.exe.exe (PID: 3328)
- RegAsm.exe (PID: 3104)
- rest.exe.exe (PID: 3636)
- Rby1.exe.exe (PID: 3884)
- InstallUtil.exe (PID: 1888)
- f305ba-b4b69ab5.exe.exe (PID: 2336)
Reads the computer name
- bomb.exe (PID: 2040)
- rundll64.exe.exe (PID: 1924)
- WinScp.exe.exe (PID: 2484)
- lve.exe.exe (PID: 2660)
- build_2023-12-19_21-29.exe.exe (PID: 1484)
- againn.exe.exe (PID: 2496)
- lumtru.exe.exe (PID: 3028)
- xxx.exe.exe (PID: 2652)
- RegAsm.exe (PID: 3104)
- Minodeka.exe.exe (PID: 3240)
- wlanext.exe.exe (PID: 3328)
- rest.exe.exe (PID: 3636)
- lve5.exe.exe (PID: 2488)
- Rby1.exe.exe (PID: 3884)
- InstallUtil.exe (PID: 1888)
- 1IE77zf7.exe (PID: 2904)
- 3Az54zw.exe (PID: 2060)
- f305ba-b4b69ab5.exe.exe (PID: 2336)
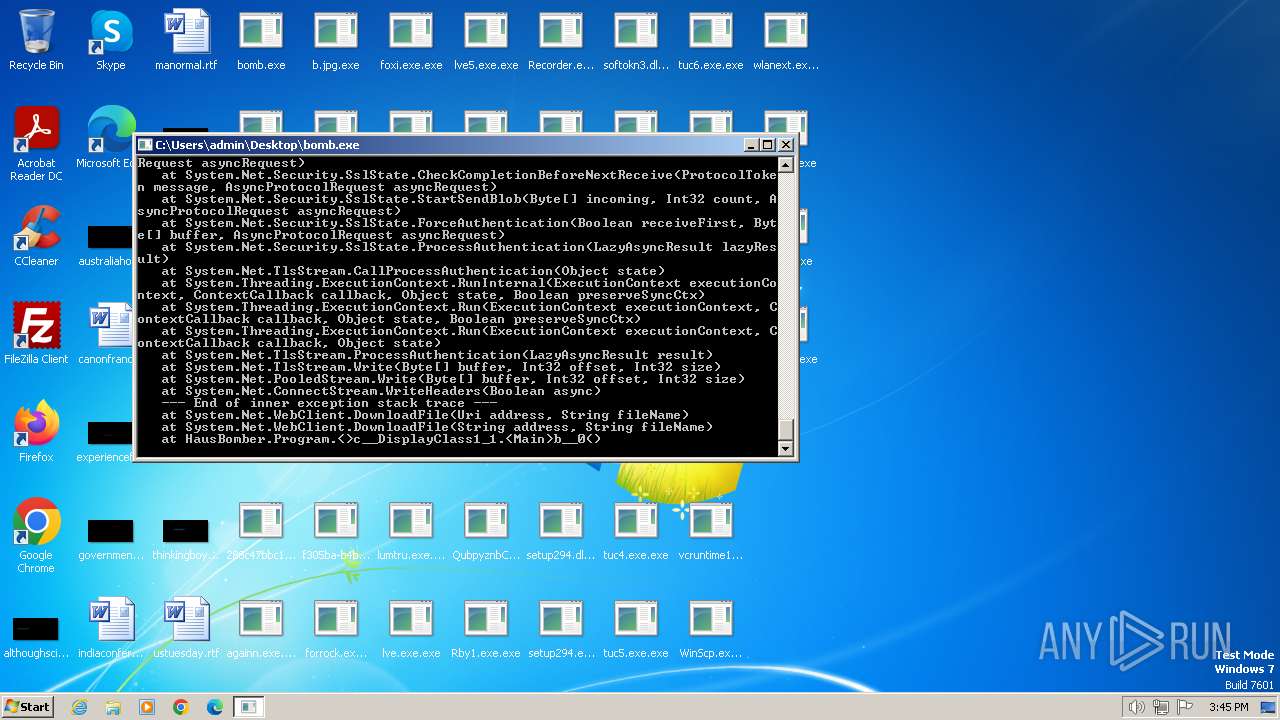
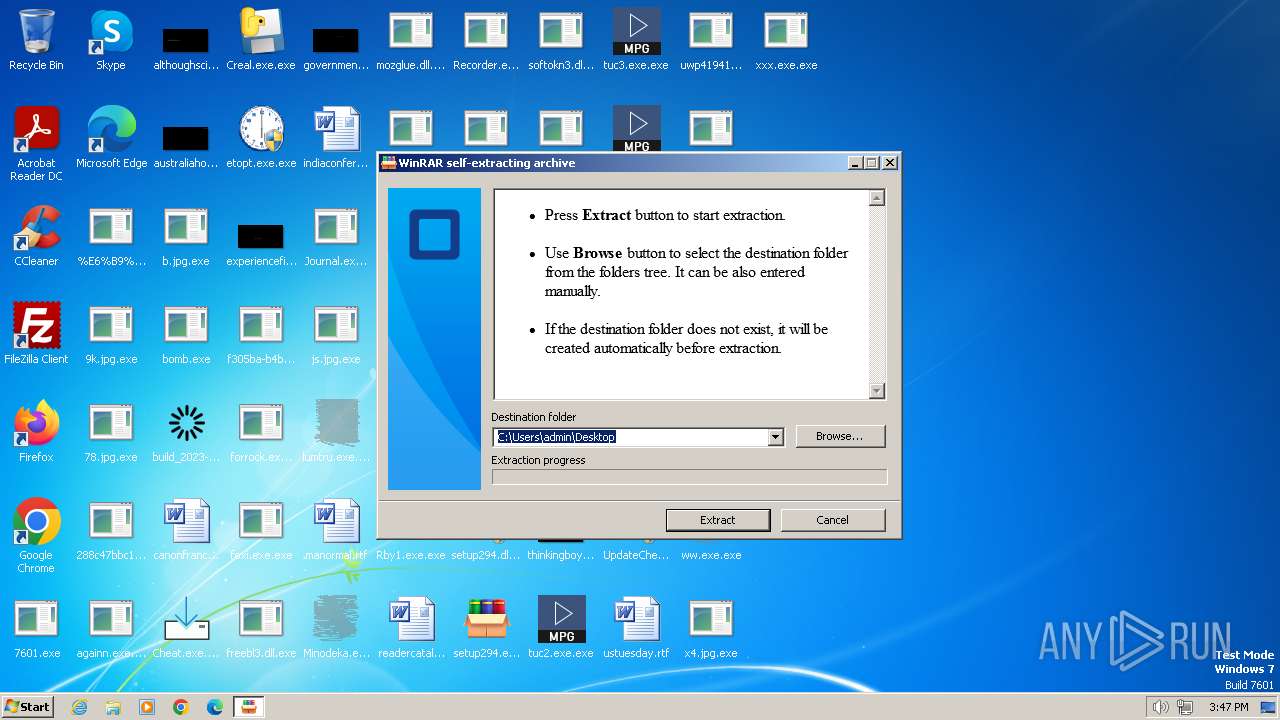
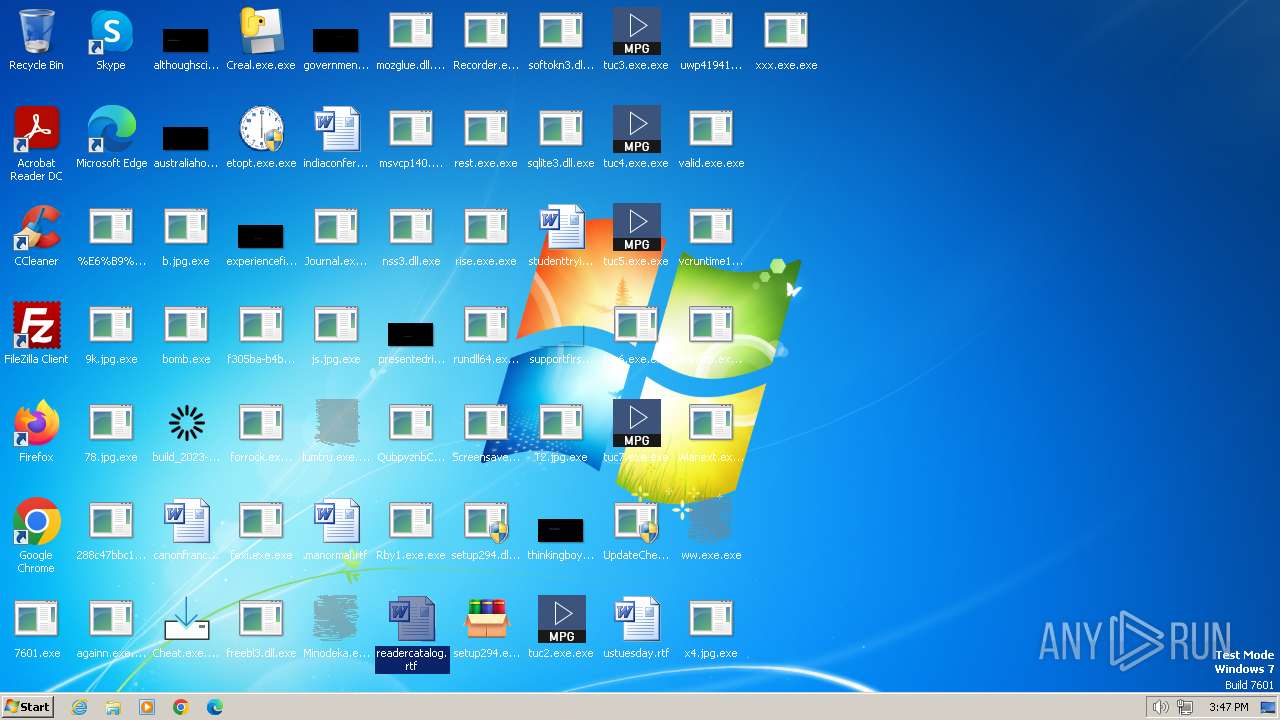
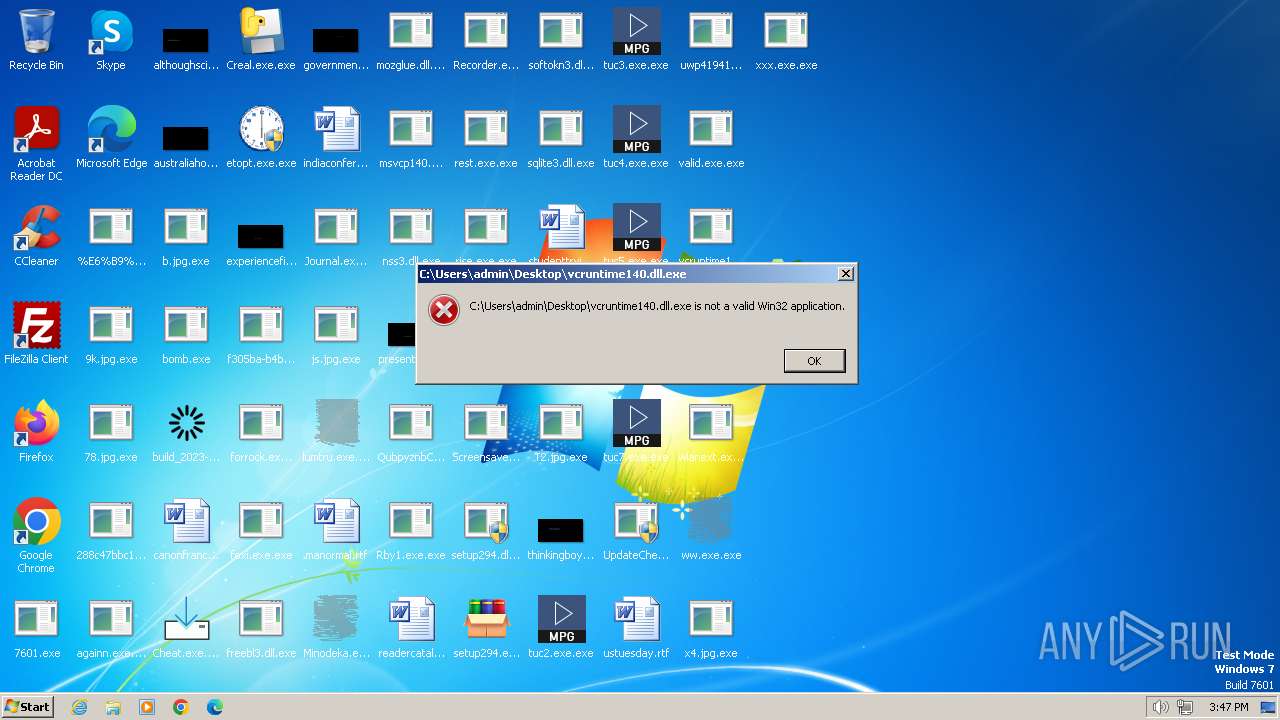
Process drops legitimate windows executable
- bomb.exe (PID: 2040)
- valid.exe.exe (PID: 1556)
Reads Environment values
- bomb.exe (PID: 2040)
- WinScp.exe.exe (PID: 2484)
- rest.exe.exe (PID: 3636)
- InstallUtil.exe (PID: 1888)
- f305ba-b4b69ab5.exe.exe (PID: 2336)
Create files in a temporary directory
- bomb.exe (PID: 2040)
- WinScp.exe.exe (PID: 2484)
- rest.exe.exe (PID: 3636)
- f305ba-b4b69ab5.exe.exe (PID: 2336)
- valid.exe.exe (PID: 1556)
- ww7qm33.exe (PID: 560)
Drops the executable file immediately after the start
- bomb.exe (PID: 2040)
- lve.exe.exe (PID: 2660)
- lve5.exe.exe (PID: 2488)
- rest.exe.exe (PID: 3636)
- valid.exe.exe (PID: 1556)
- ww7qm33.exe (PID: 560)
Reads CPU info
- lve.exe.exe (PID: 2660)
The process drops Mozilla's DLL files
- bomb.exe (PID: 2040)
Creates files or folders in the user directory
- xxx.exe.exe (PID: 2652)
- InstallUtil.exe (PID: 1888)
- rest.exe.exe (PID: 3636)
The process drops C-runtime libraries
- bomb.exe (PID: 2040)
Creates files in the program directory
- rest.exe.exe (PID: 3636)
Process checks are UAC notifies on
- Rby1.exe.exe (PID: 3884)
Reads mouse settings
- 1IE77zf7.exe (PID: 2904)
- 3Az54zw.exe (PID: 2060)
Application launched itself
- msedge.exe (PID: 2780)
- msedge.exe (PID: 920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2095:12:30 16:34:12+01:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 9728 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4432 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | bomb.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | bomb.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
100
Monitored processes
45
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ww7qm33.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ww7qm33.exe | — | valid.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
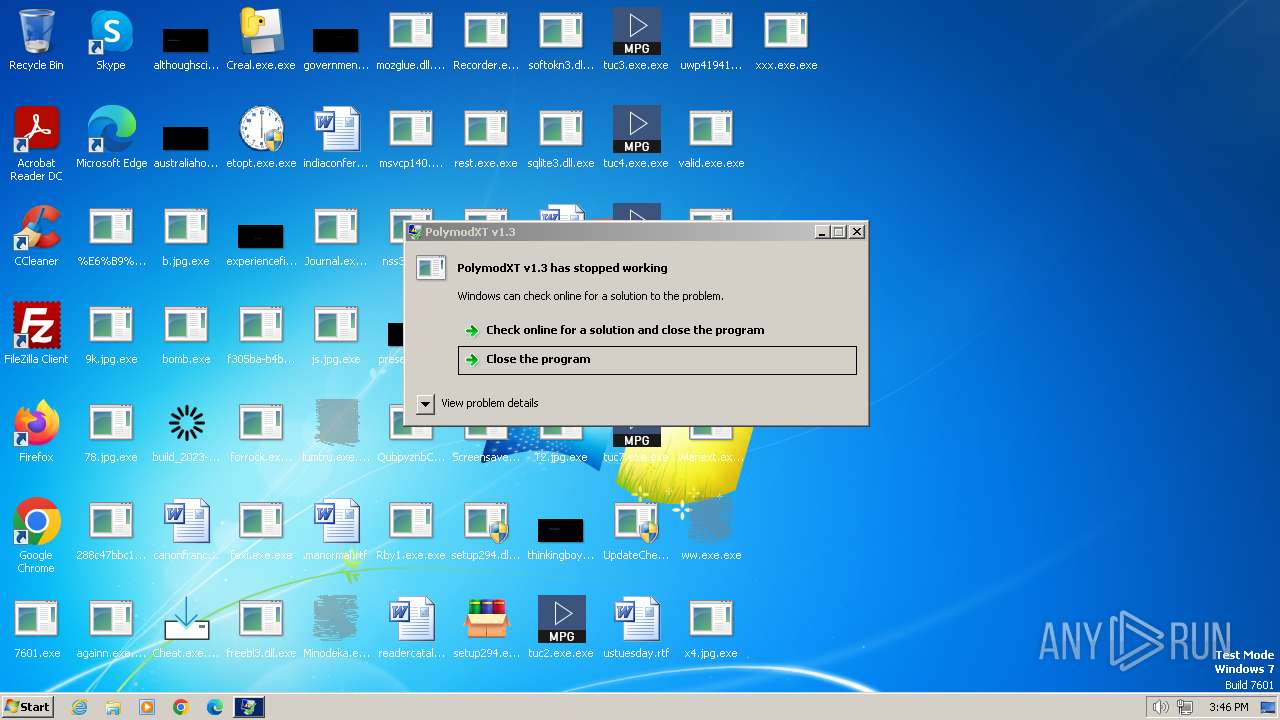
| 568 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\4Oa386lk.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\4Oa386lk.exe | — | valid.exe.exe | |||||||||||
User: admin Company: Polymod Inc. Integrity Level: MEDIUM Description: PolymodXT v1.3 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0x17c,0x180,0x184,0x150,0x190,0x61cff598,0x61cff5a8,0x61cff5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.facebook.com/login | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | 3Az54zw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1484 | "C:\Users\admin\Desktop\build_2023-12-19_21-29.exe.exe" | C:\Users\admin\Desktop\build_2023-12-19_21-29.exe.exe | bomb.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\Desktop\valid.exe.exe" | C:\Users\admin\Desktop\valid.exe.exe | — | bomb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | "C:\Users\admin\Desktop\Screensaver.exe.exe" | C:\Users\admin\Desktop\Screensaver.exe.exe | bomb.exe | ||||||||||||
User: admin Company: Apache Software Foundation Integrity Level: MEDIUM Description: ApacheBench command line utility Exit code: 0 Version: 2.2.14 Modules
| |||||||||||||||
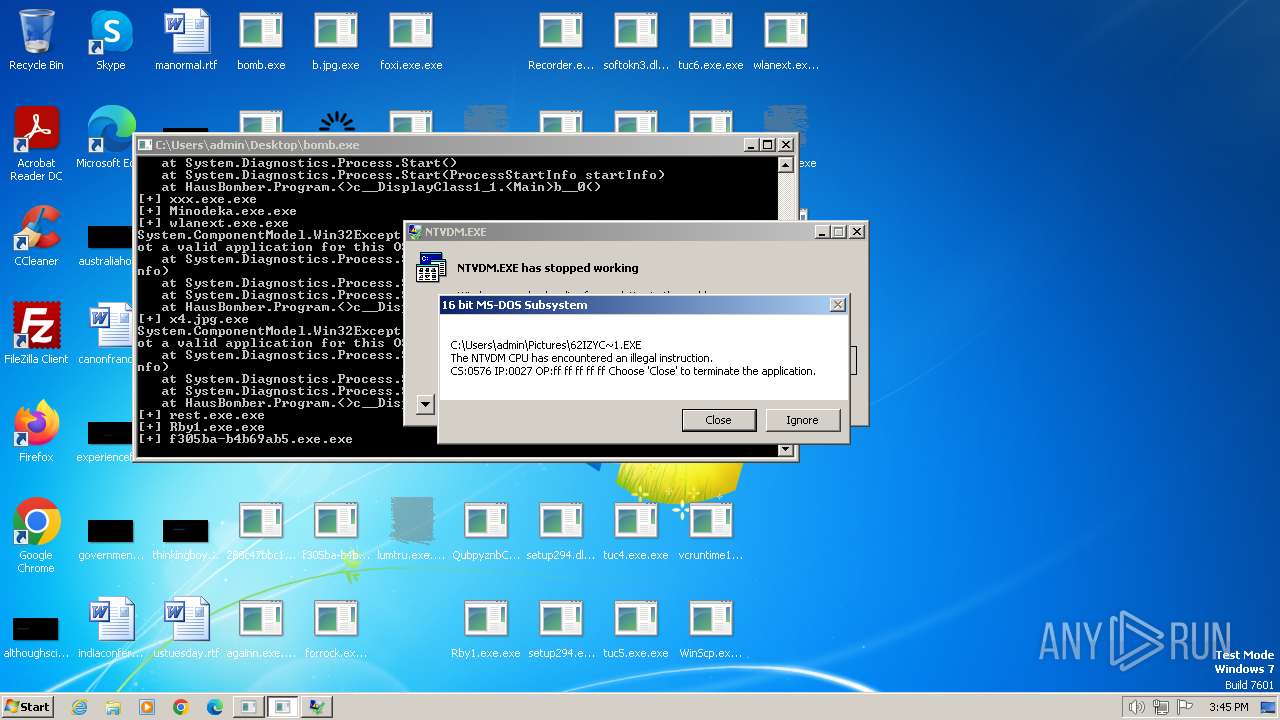
| 1732 | "C:\Windows\system32\ntvdm.exe" -i9 | C:\Windows\System32\ntvdm.exe | — | InstallUtil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1820 | "C:\Windows\system32\ntvdm.exe" -i8 | C:\Windows\System32\ntvdm.exe | InstallUtil.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | Rby1.exe.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
26 252
Read events
26 131
Write events
121
Delete events
0
Modification events
| (PID) Process: | (2040) bomb.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2040) bomb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2040) bomb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2040) bomb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2040) bomb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2484) WinScp.exe.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2316) POWERSHELL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2316) POWERSHELL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2316) POWERSHELL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2316) POWERSHELL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
19
Suspicious files
21
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs1E52.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 2040 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Cab16F1.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2040 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Cab16DF.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2040 | bomb.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:4E8E3E8AD74EF4C236C6014E1A5F3C75 | SHA256:17AF74C0CF61A952FCCC8DE00633112AE8F2F120BA240ED4505E5CB8AA5CE6EC | |||
| 2040 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Tar16E0.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2040 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Tar16F2.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2404 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs2363.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 2040 | bomb.exe | C:\Users\admin\Desktop\js.jpg.exe | image | |
MD5:F80162DD144998FA4C199EEF0757F244 | SHA256:819BE2AA1635E7B3A3C7F538549862ED7FA1D535EE3840B8D8BDBB2710A564B9 | |||
| 2472 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs1E51.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 2316 | POWERSHELL.exe | C:\Users\admin\AppData\Local\Temp\0bdhwvrx.kpp.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
90
TCP/UDP connections
213
DNS requests
40
Threats
222
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2040 | bomb.exe | GET | — | 5.42.65.125:80 | http://5.42.65.125/288c47bbc1871b42239df19ff4df68f076.exe | unknown | — | — | unknown |
2040 | bomb.exe | GET | 200 | 85.209.176.59:80 | http://85.209.176.59/server/execution/WinScp.exe | unknown | executable | 323 Kb | unknown |
2040 | bomb.exe | GET | — | 172.67.140.12:80 | http://1qwqewrewqweqwrqe.sbs/setup294.exe | unknown | — | — | unknown |
2040 | bomb.exe | GET | 200 | 185.16.38.38:555 | http://185.16.38.38:555/24/b.jpg | unknown | compressed | 196 Kb | unknown |
2040 | bomb.exe | GET | 200 | 109.107.182.3:80 | http://109.107.182.3/test/valid.exe | unknown | executable | 2.08 Mb | unknown |
2040 | bomb.exe | GET | 200 | 193.117.208.148:80 | http://193.117.208.148/Screensaver.exe | unknown | executable | 72.0 Kb | unknown |
2040 | bomb.exe | GET | — | 77.91.68.21:80 | http://77.91.68.21/nova/foxi.exe | unknown | — | — | unknown |
2040 | bomb.exe | GET | 200 | 5.42.66.58:80 | http://5.42.66.58/f059ec3d7eb90876/nss3.dll | unknown | executable | 1.95 Mb | unknown |
2040 | bomb.exe | GET | 200 | 198.46.174.147:80 | http://198.46.174.147/3470/wlanext.exe | unknown | executable | 940 Kb | unknown |
2040 | bomb.exe | GET | 200 | 15.204.49.148:80 | http://15.204.49.148/files/Rby1.exe | unknown | executable | 1.69 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2040 | bomb.exe | 151.101.2.49:443 | urlhaus.abuse.ch | FASTLY | US | unknown |
2040 | bomb.exe | 109.107.182.3:80 | — | Cloud assets LLC | RU | unknown |
2040 | bomb.exe | 5.42.66.58:80 | — | CJSC Kolomna-Sviaz TV | RU | unknown |
2040 | bomb.exe | 185.16.38.38:555 | — | Meverywhere sp. z o.o. | PL | unknown |
2040 | bomb.exe | 85.209.176.59:80 | — | Zenex 5ive Limited | FR | unknown |
2040 | bomb.exe | 77.91.68.21:80 | — | Foton Telecom CJSC | RU | unknown |
2040 | bomb.exe | 198.46.174.147:80 | — | AS-COLOCROSSING | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urlhaus.abuse.ch |
| whitelisted |
1qwqewrewqweqwrqe.sbs |
| unknown |
www.bcmnursing.com |
| unknown |
artemis.community |
| unknown |
github.com |
| shared |
uploaddeimagens.com.br |
| shared |
wallpapercave.com |
| whitelisted |
zateghar.com |
| unknown |
132xz-1319111867.cos.ap-beijing.myqcloud.com |
| malicious |
carthagefire.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2040 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2040 | bomb.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
2040 | bomb.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2040 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2040 | bomb.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
2040 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2040 | bomb.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2040 | bomb.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
2040 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2040 | bomb.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
9 ETPRO signatures available at the full report