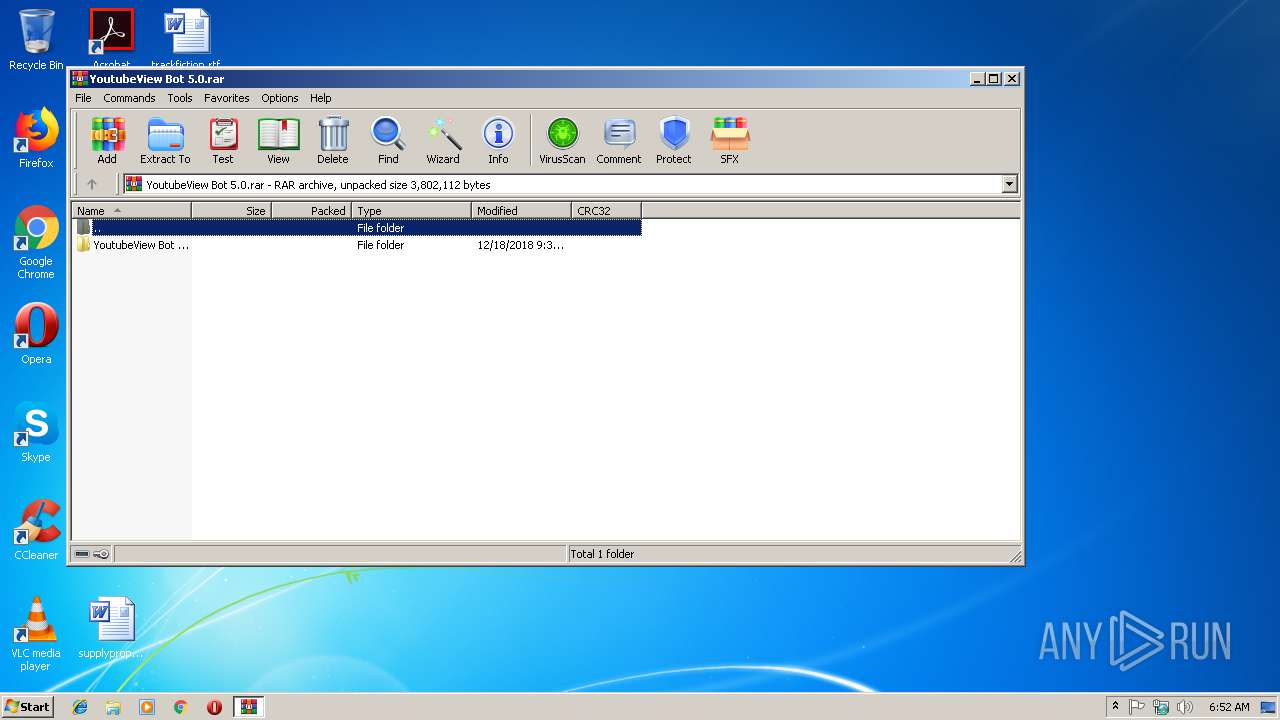
| File name: | YoutubeView Bot 5.0.rar |
| Full analysis: | https://app.any.run/tasks/aed87fa4-1d1f-4cca-8de5-27331e62a192 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
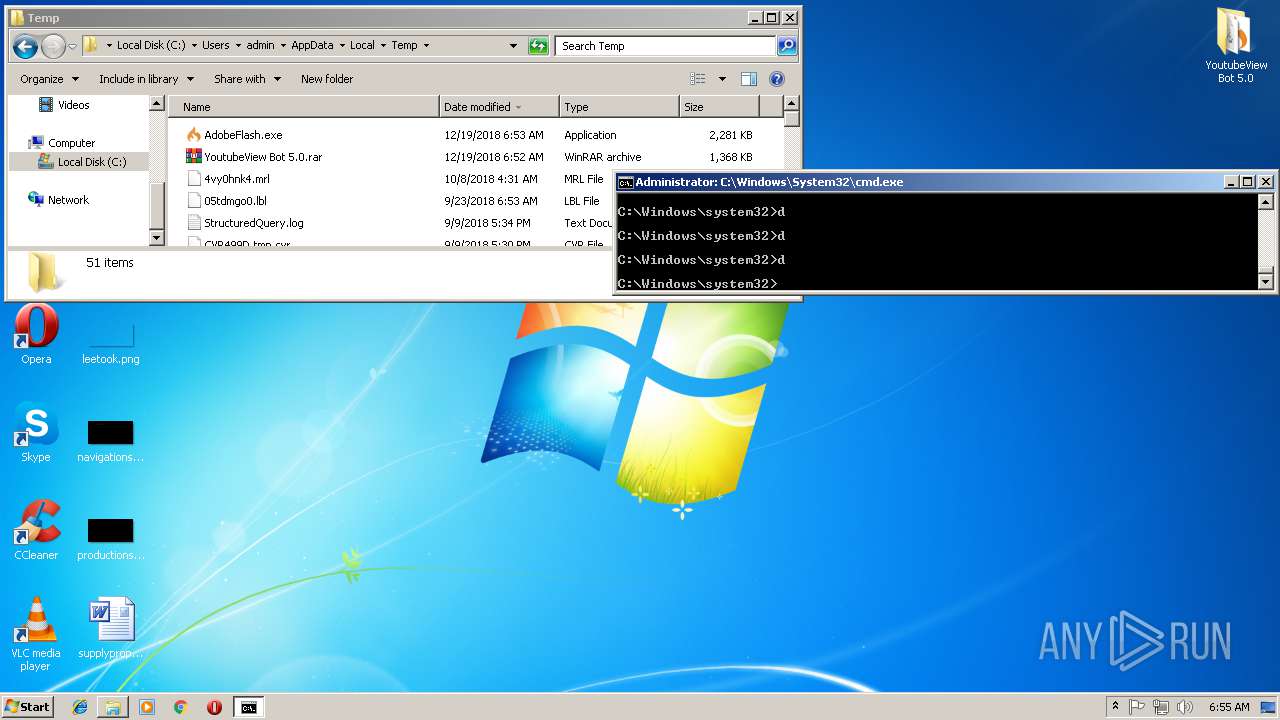
| Analysis date: | December 19, 2018, 06:52:15 |
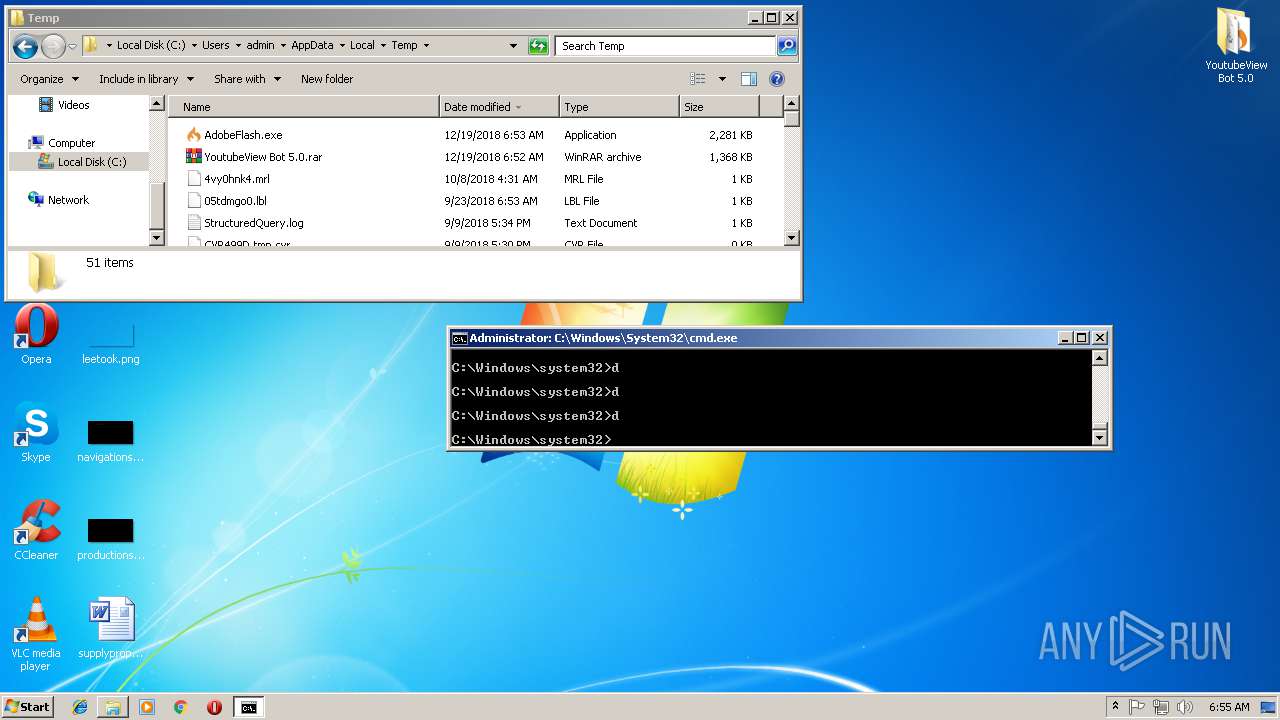
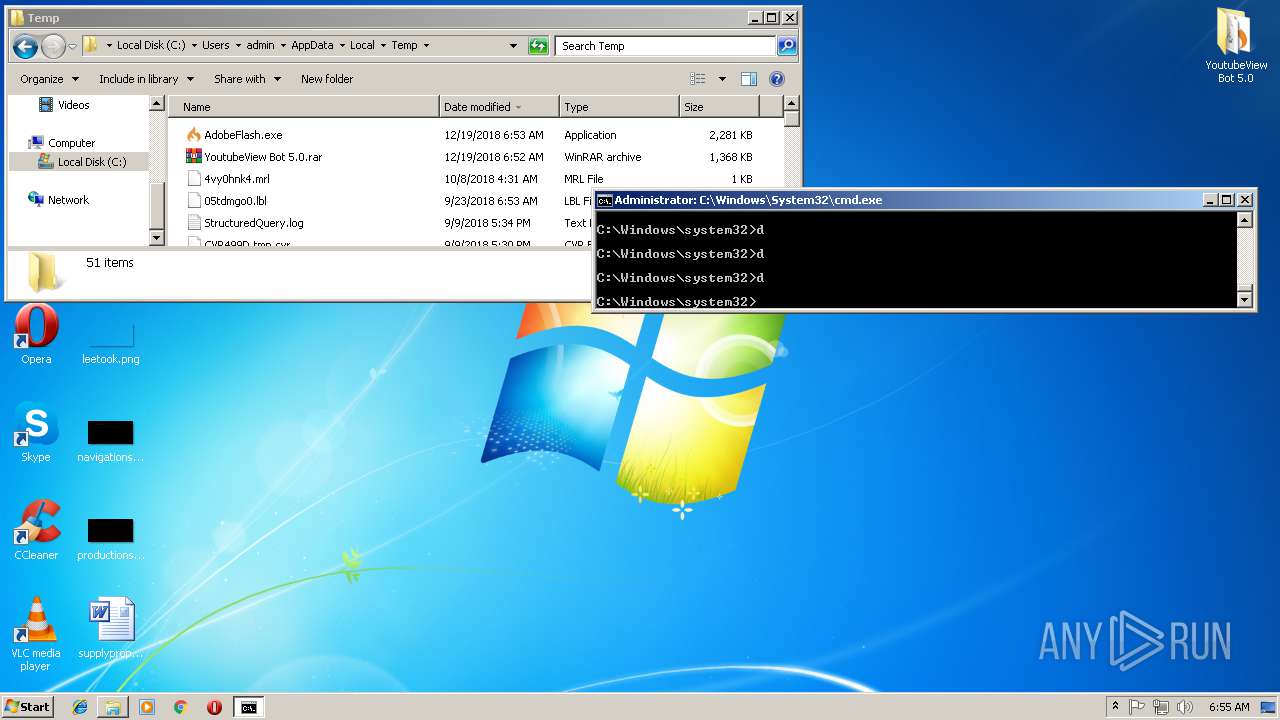
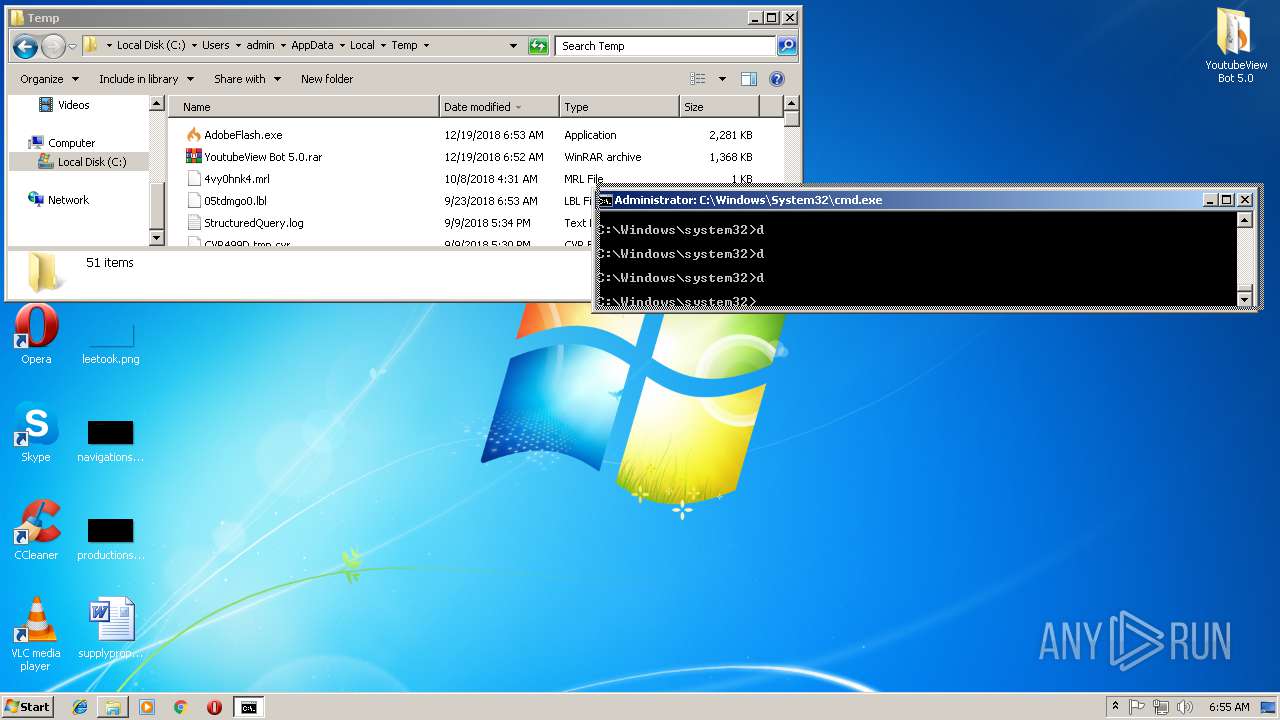
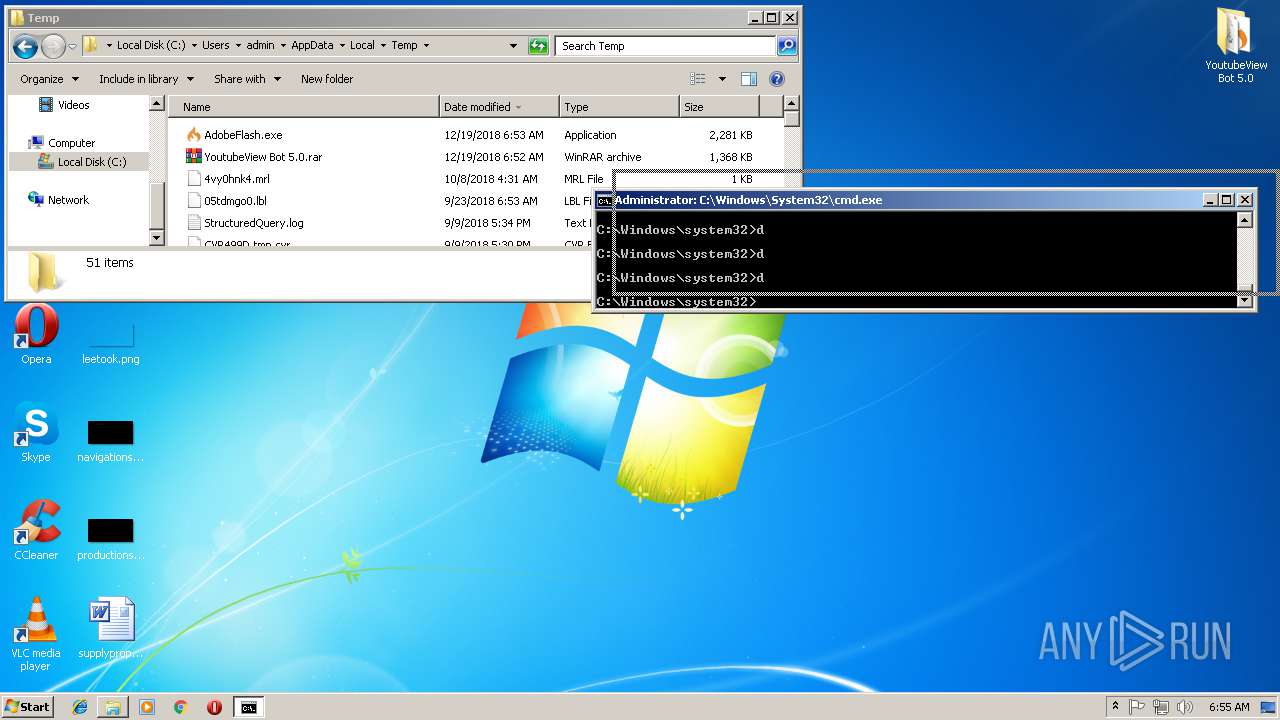
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 74E720956AD3BC201A7140A8A78A1E69 |
| SHA1: | 7AB2E96C9102F22F6BC5D2968B0148EA250F9A24 |
| SHA256: | 278BB25E2722954F8B04DA59F638A67334069C25FC3711A777BB351BF707655C |
| SSDEEP: | 24576:Tfk2Volx0wZxljdtk2N8LW6o5Z+ixZm4/XqsaN/8zhv/nHklQFZnAOupbN:TfNoH0aljdVPLZ+14ism/8RfHklWZb6Z |
MALICIOUS
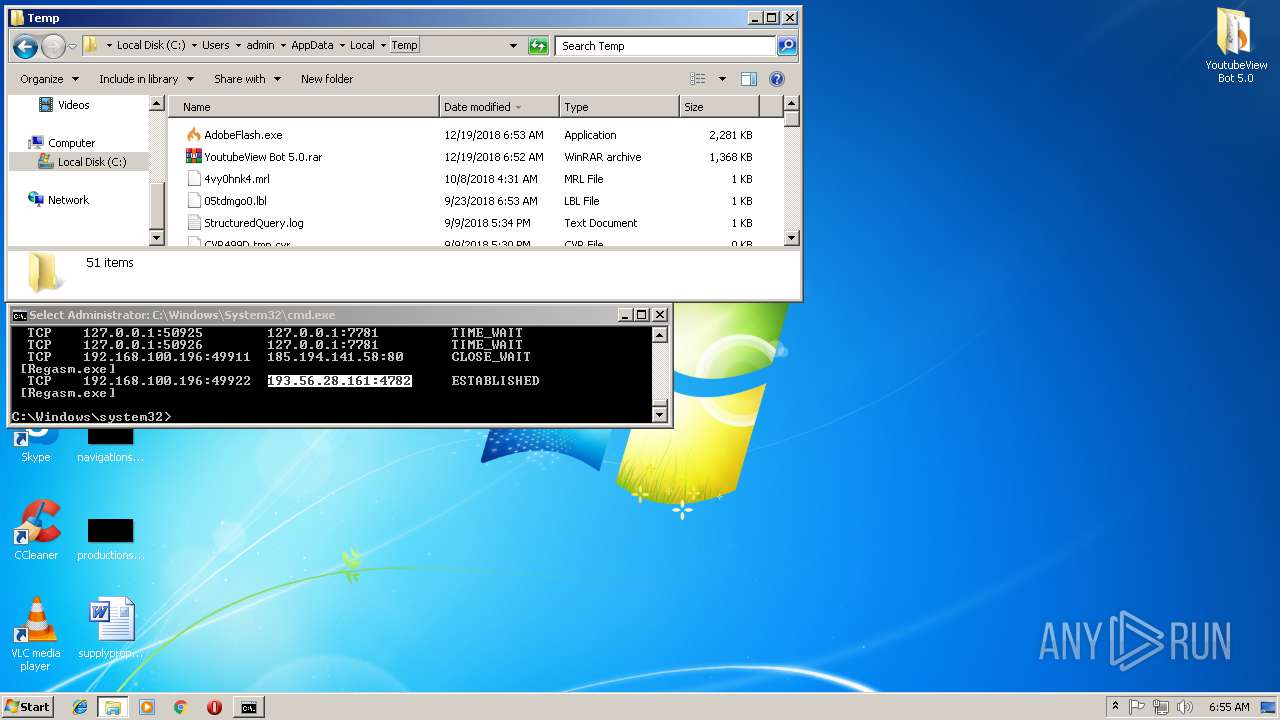
Application was dropped or rewritten from another process
- YoutubeViewBot5.0.exe (PID: 2604)
- AdobeFlash.exe (PID: 2416)
QUASAR was detected
- Regasm.exe (PID: 3928)
SUSPICIOUS
Executable content was dropped or overwritten
- YoutubeViewBot5.0.exe (PID: 2604)
Starts itself from another location
- YoutubeViewBot5.0.exe (PID: 2604)
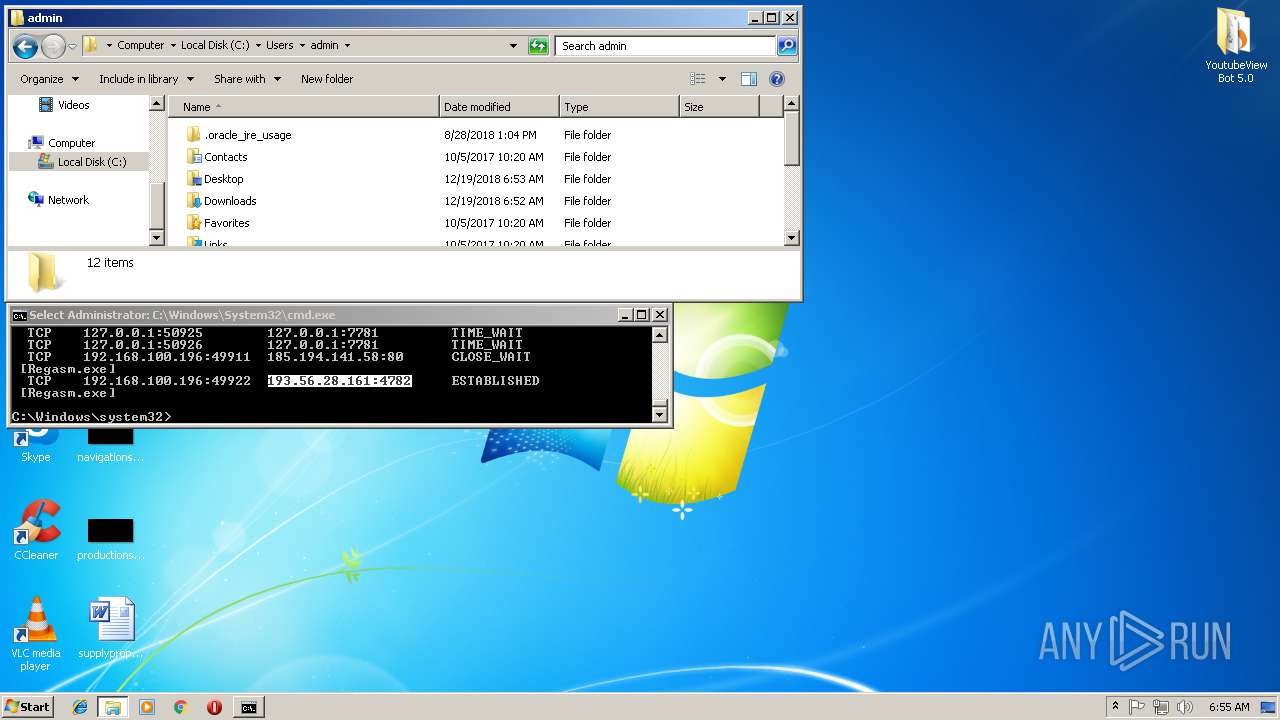
Creates files in the user directory
- Regasm.exe (PID: 3928)
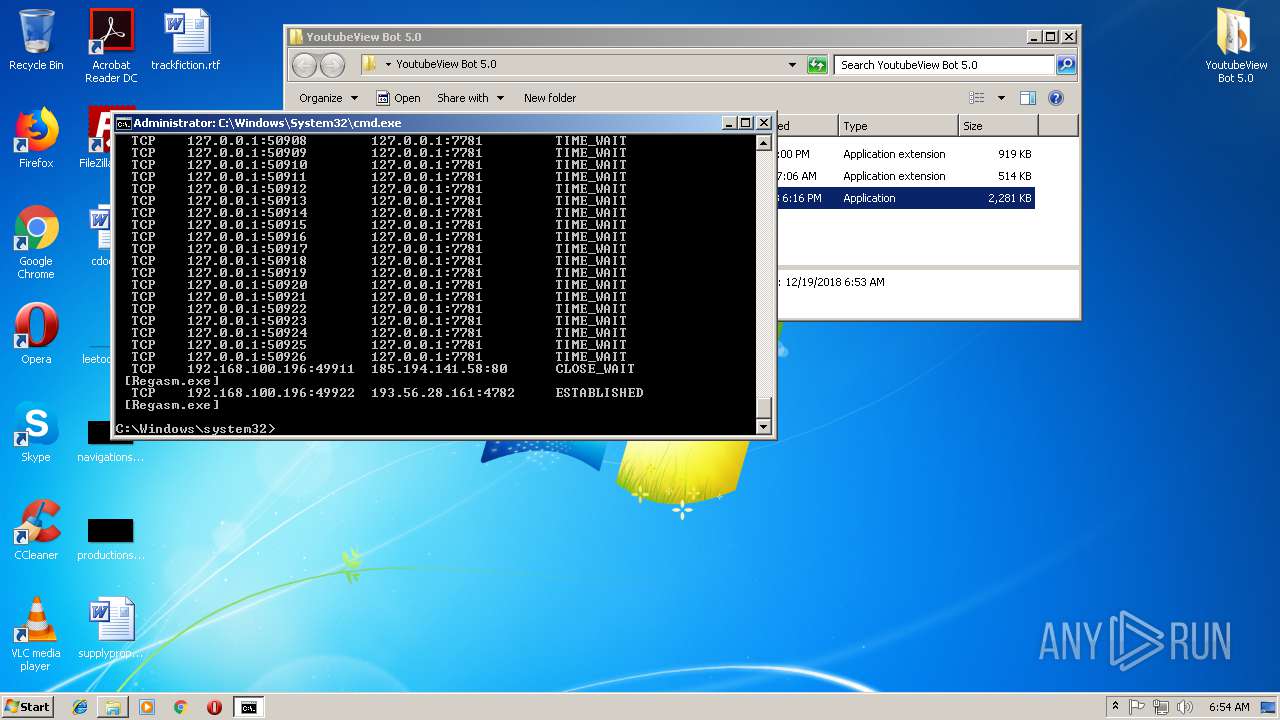
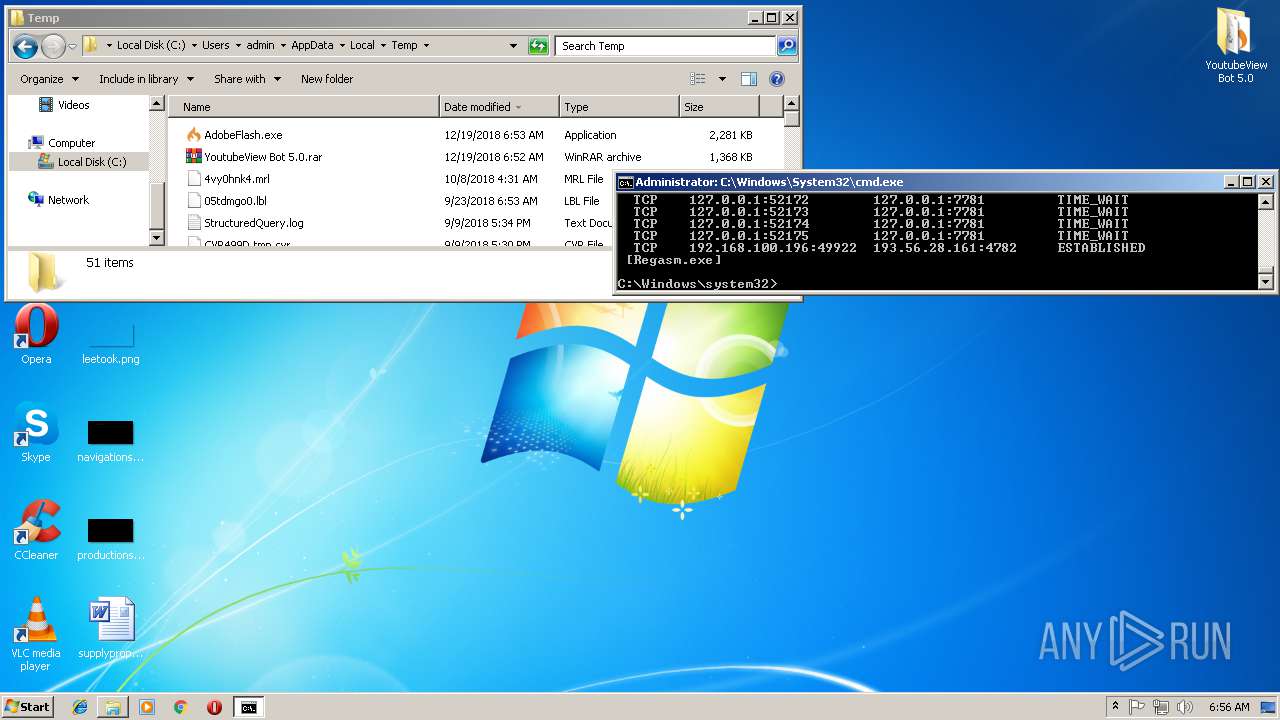
Checks for external IP
- Regasm.exe (PID: 3928)
Connects to unusual port
- Regasm.exe (PID: 3928)
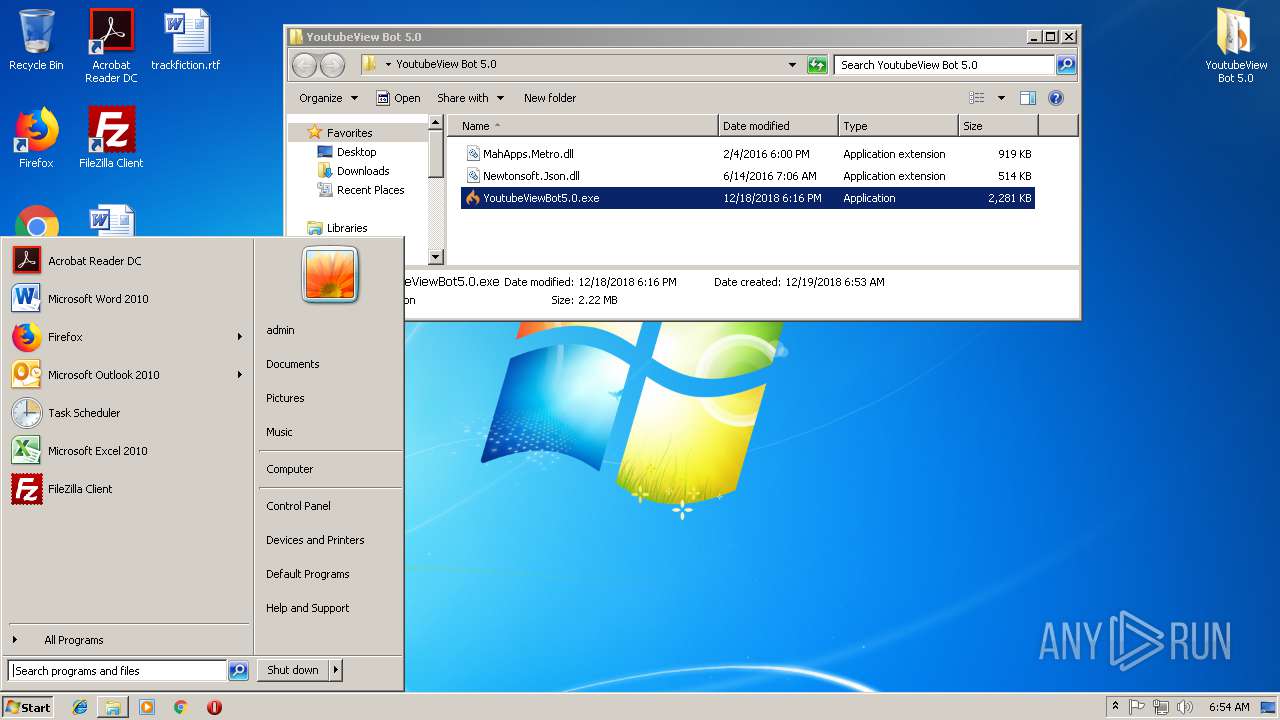
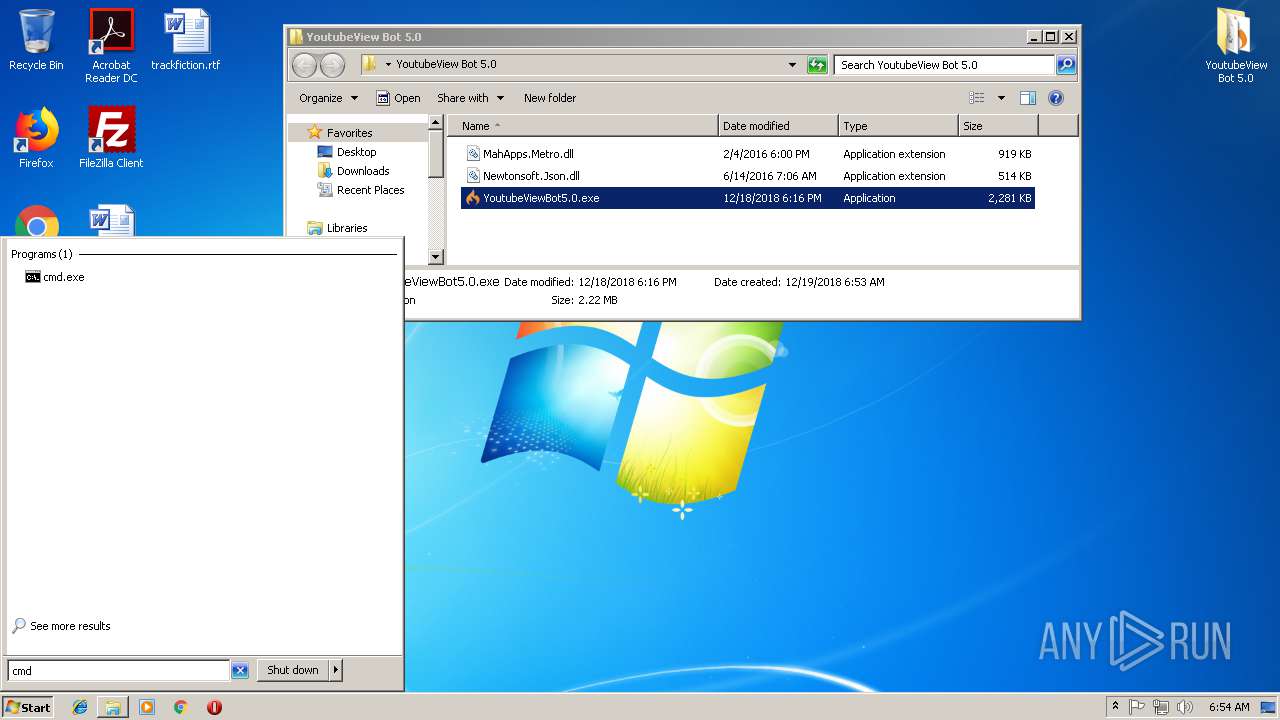
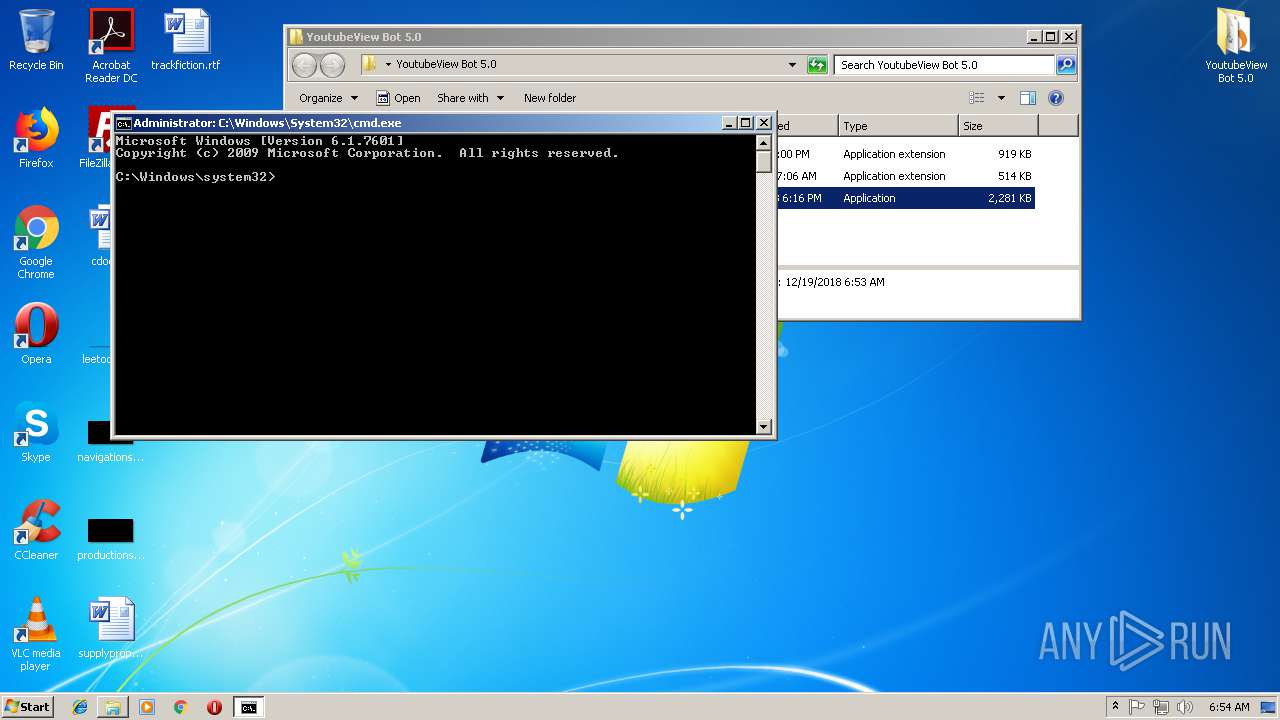
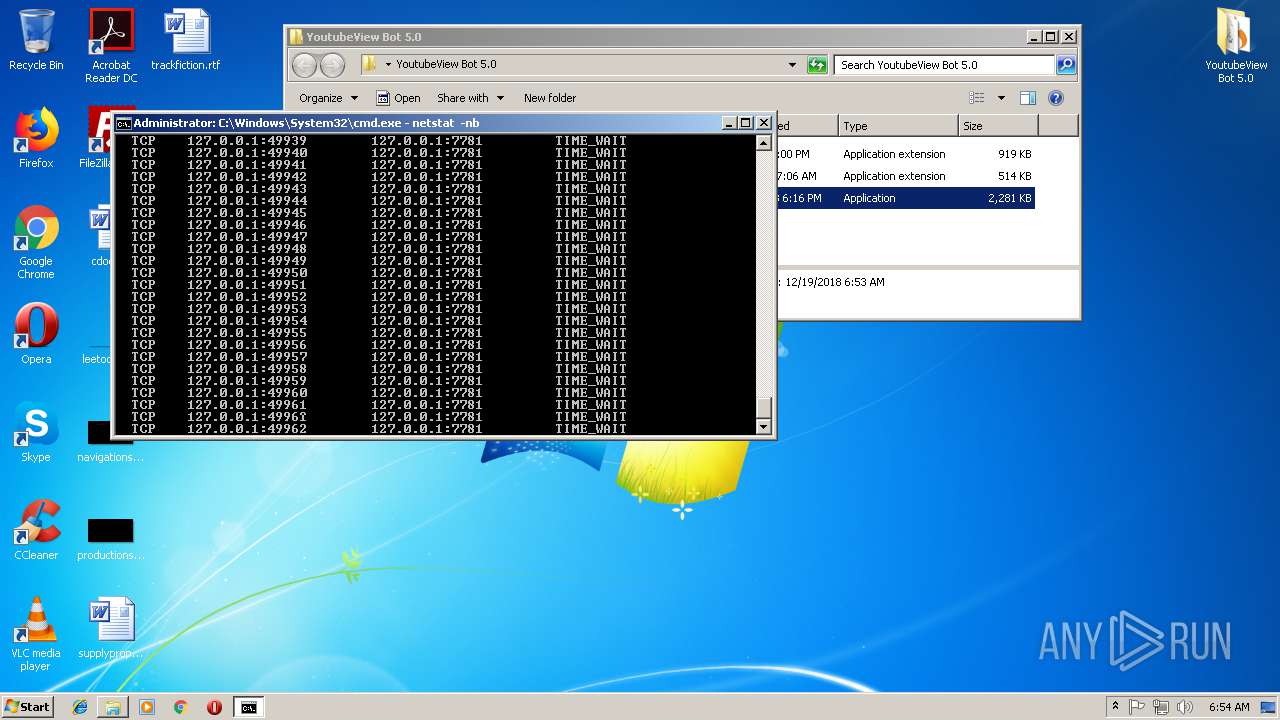
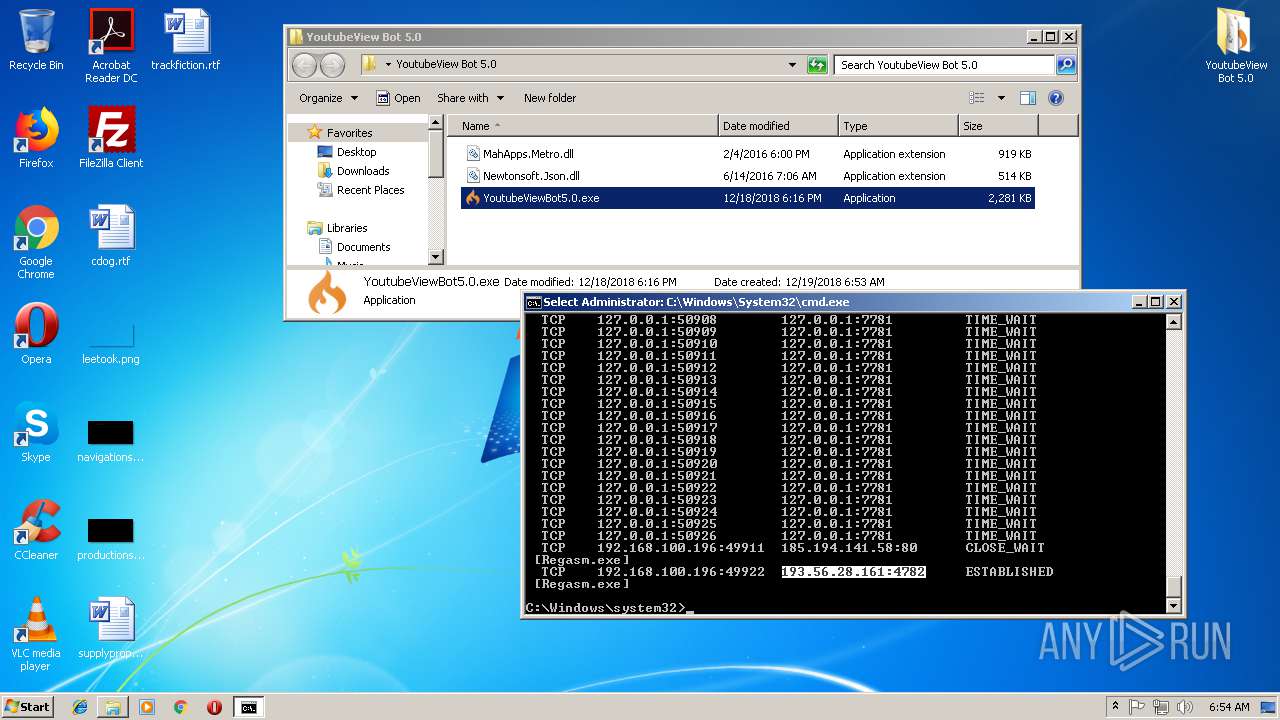
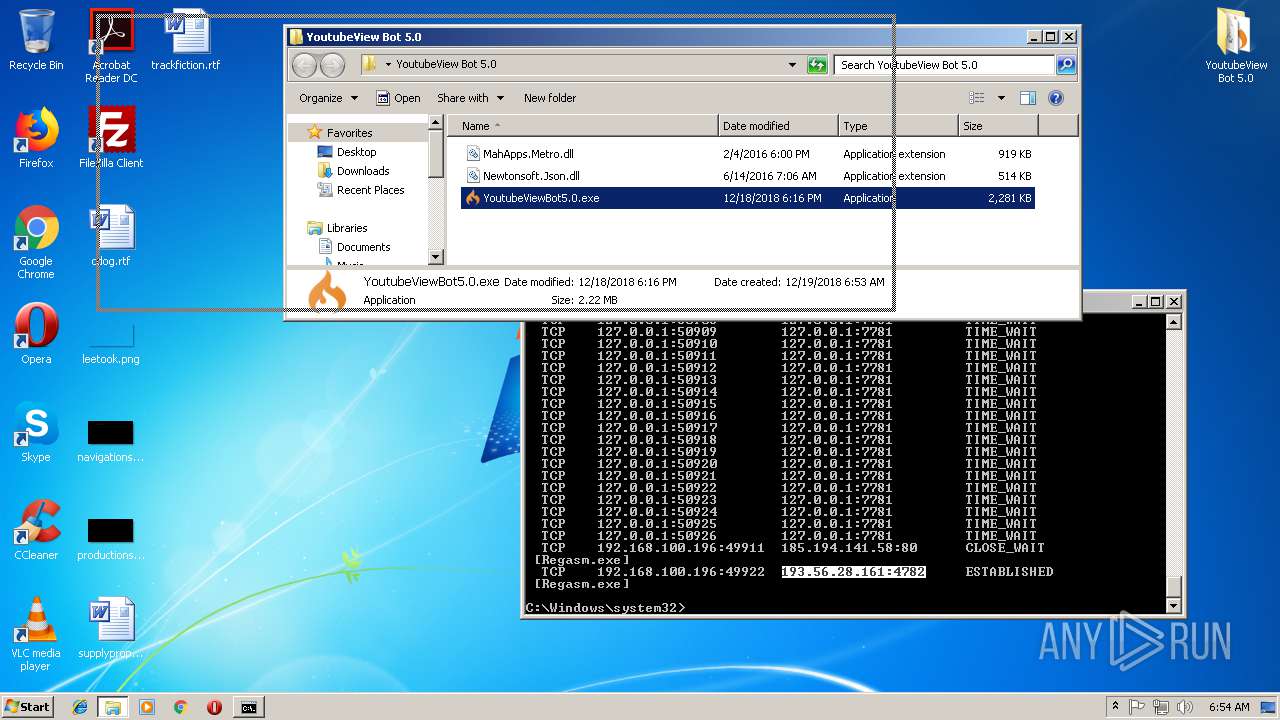
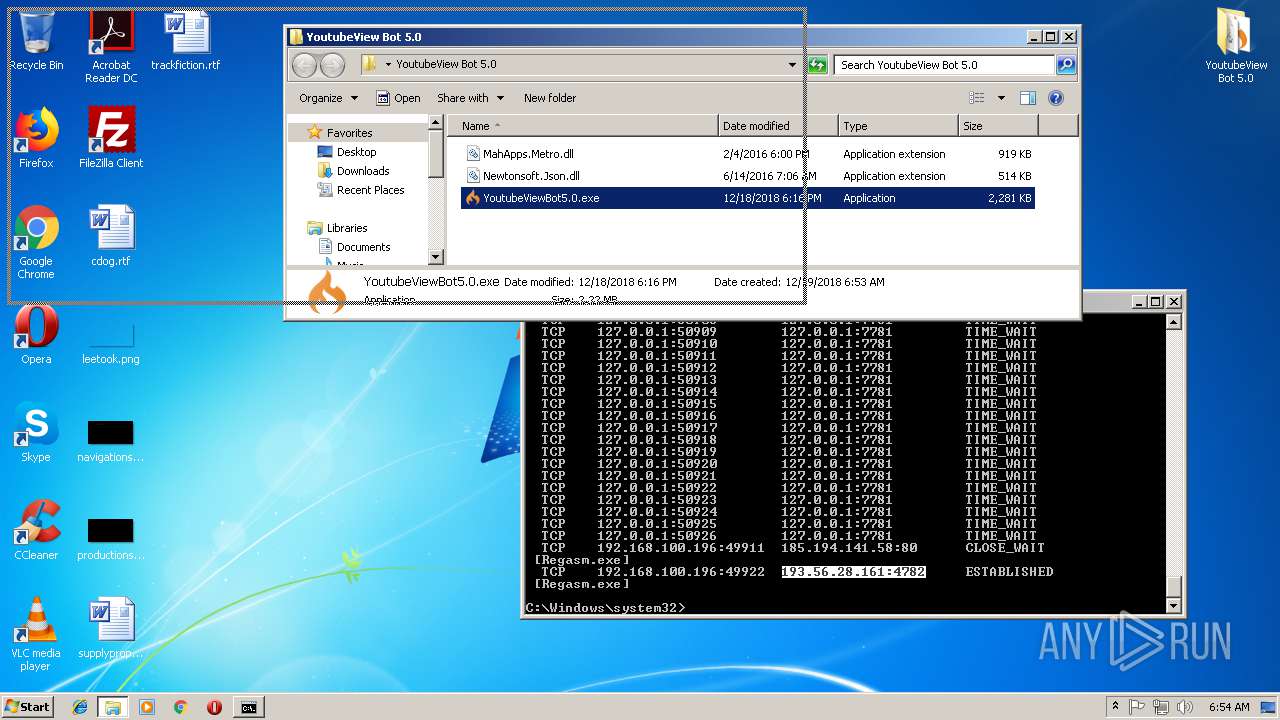
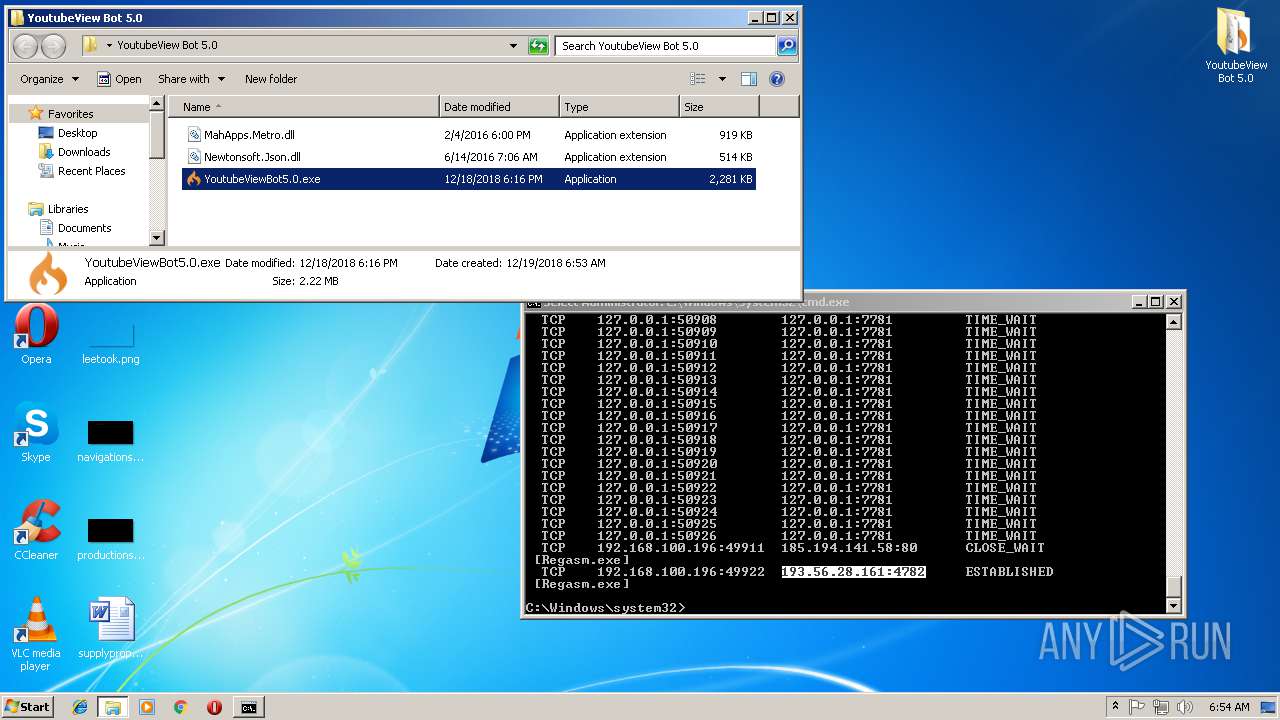
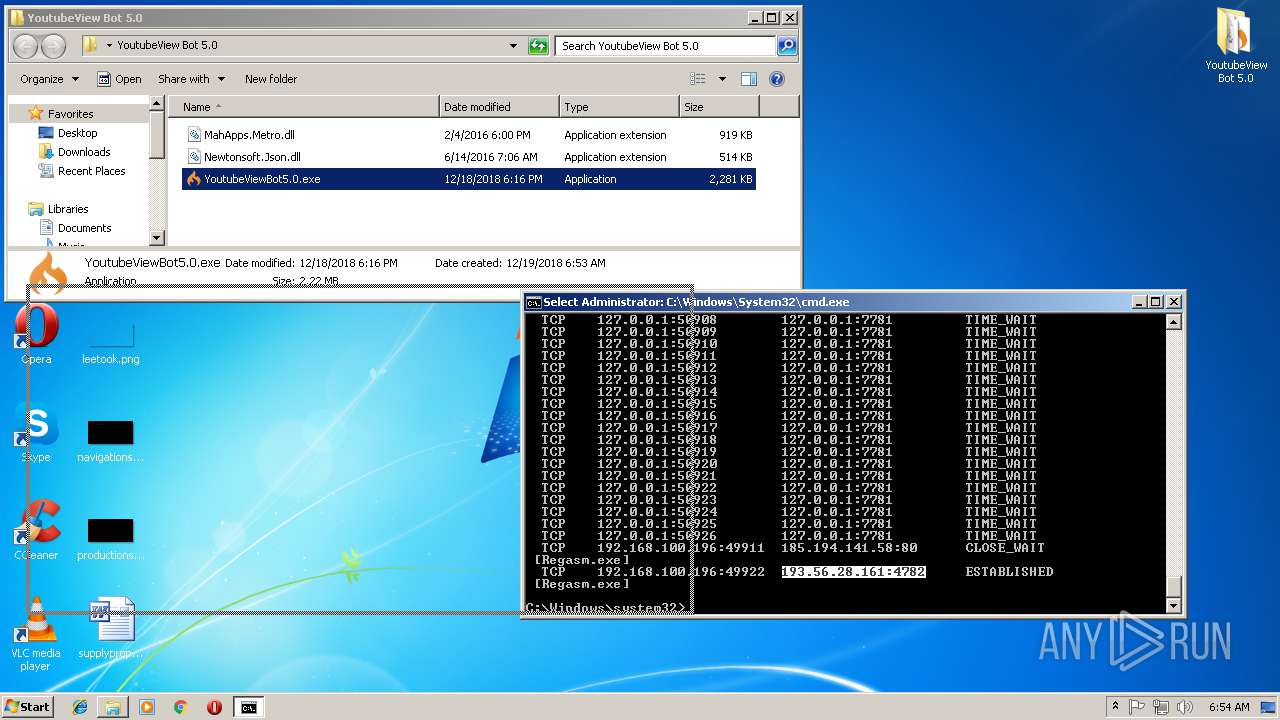
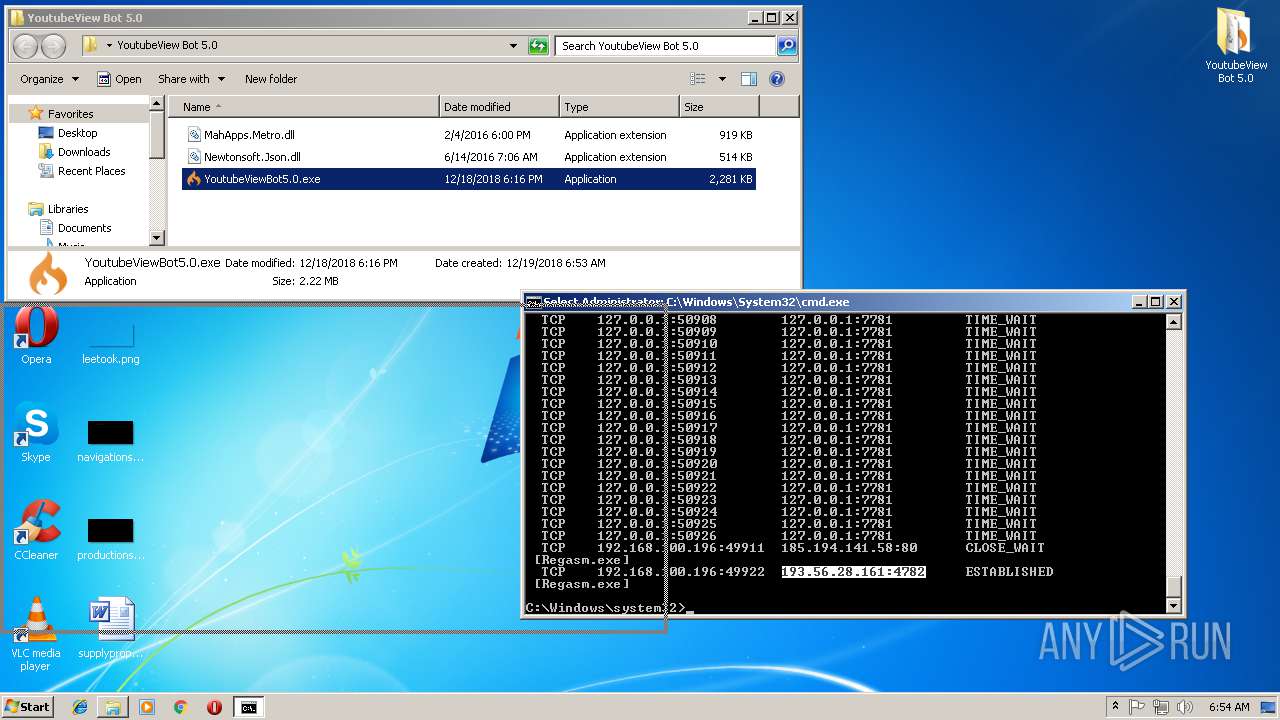
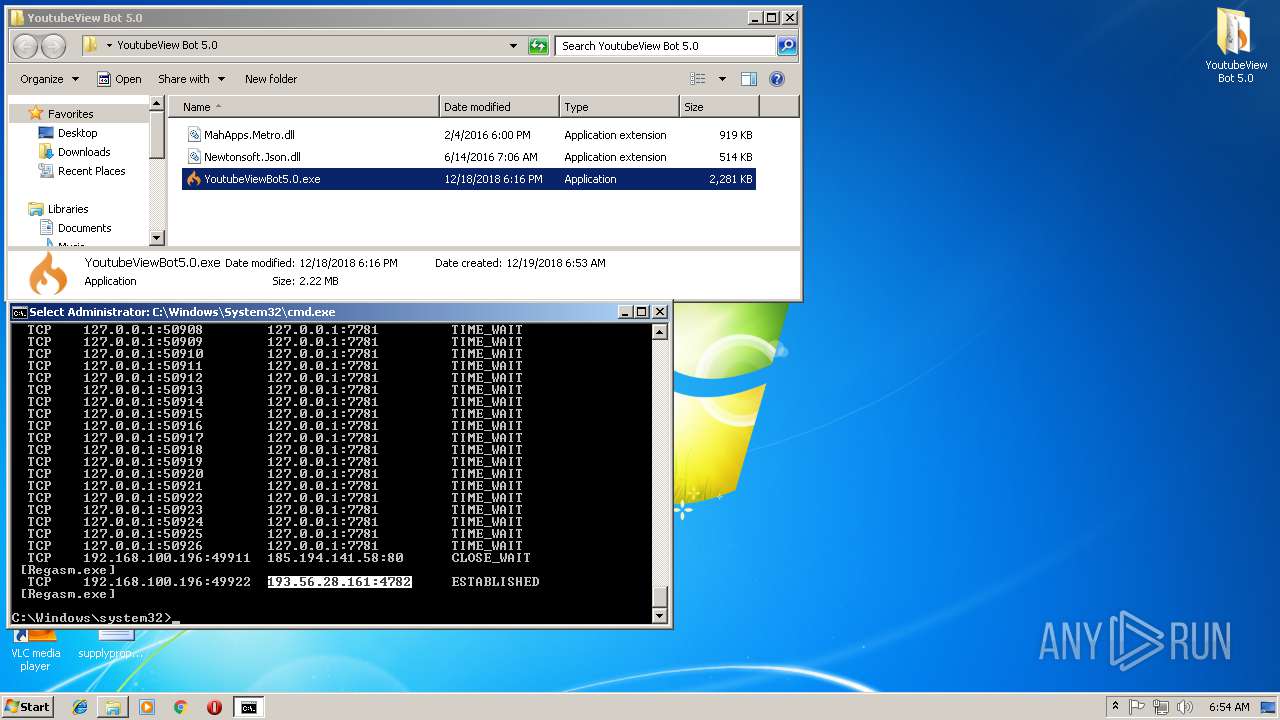
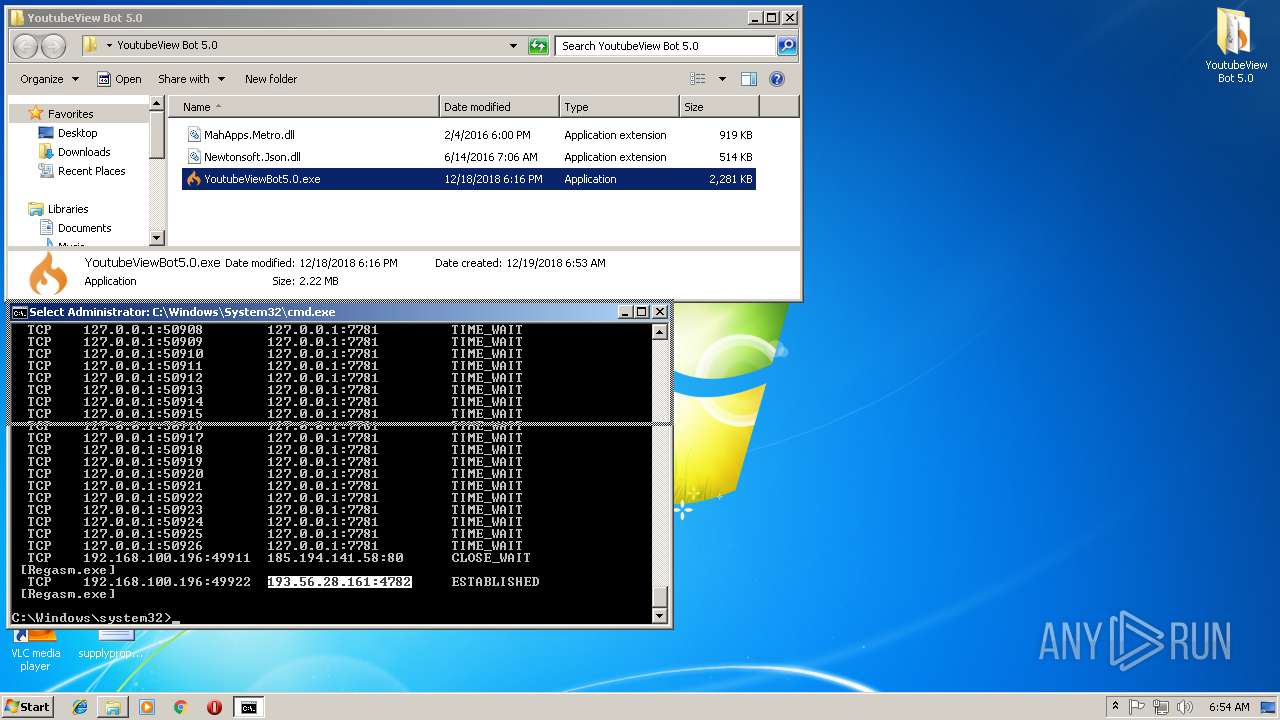
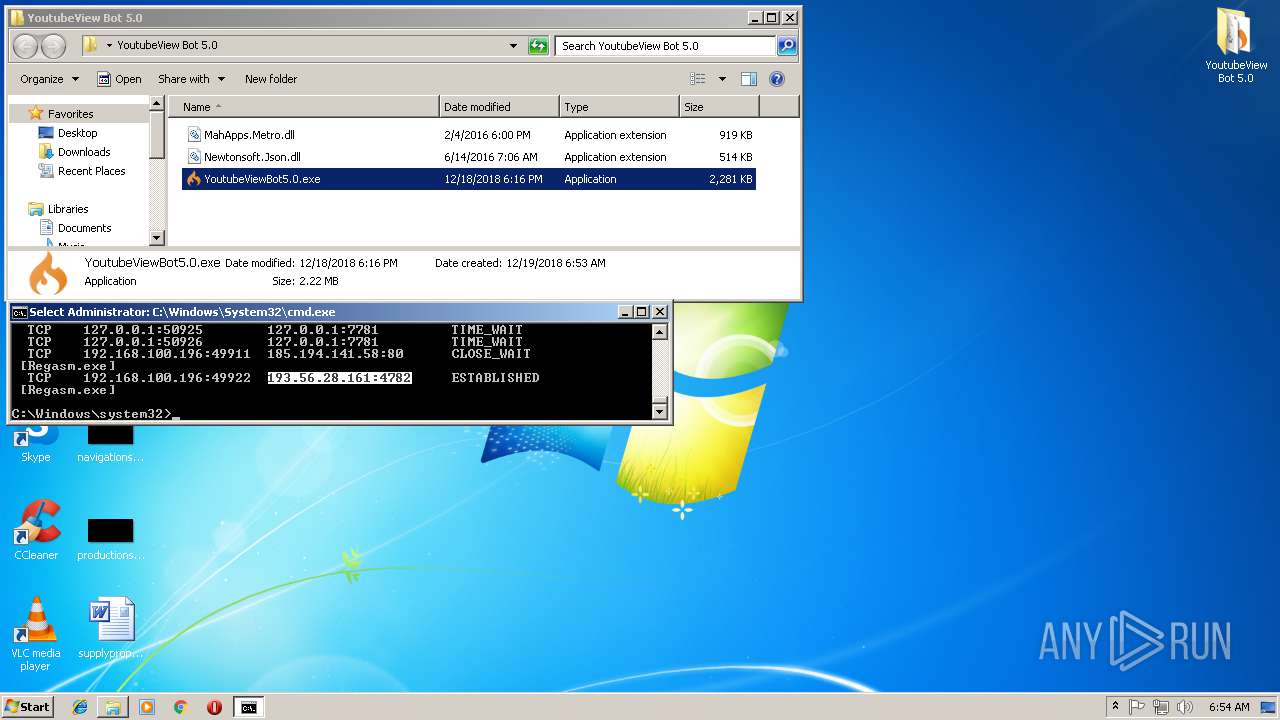
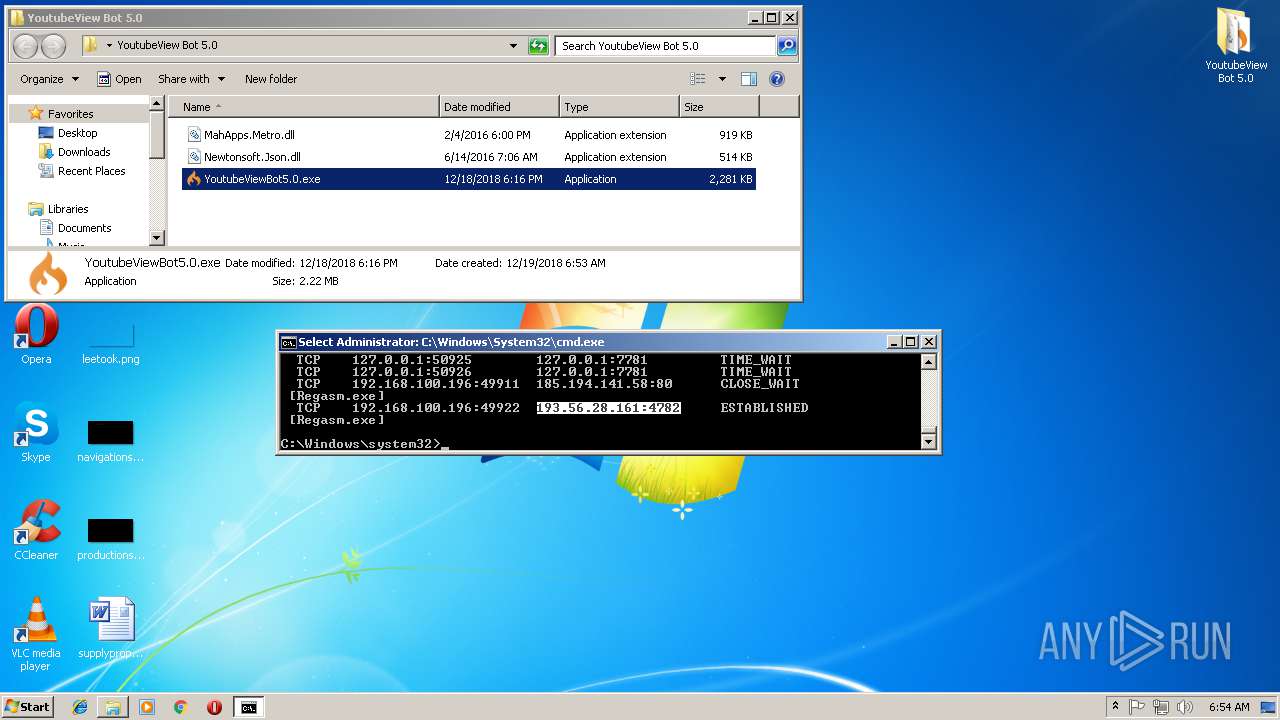
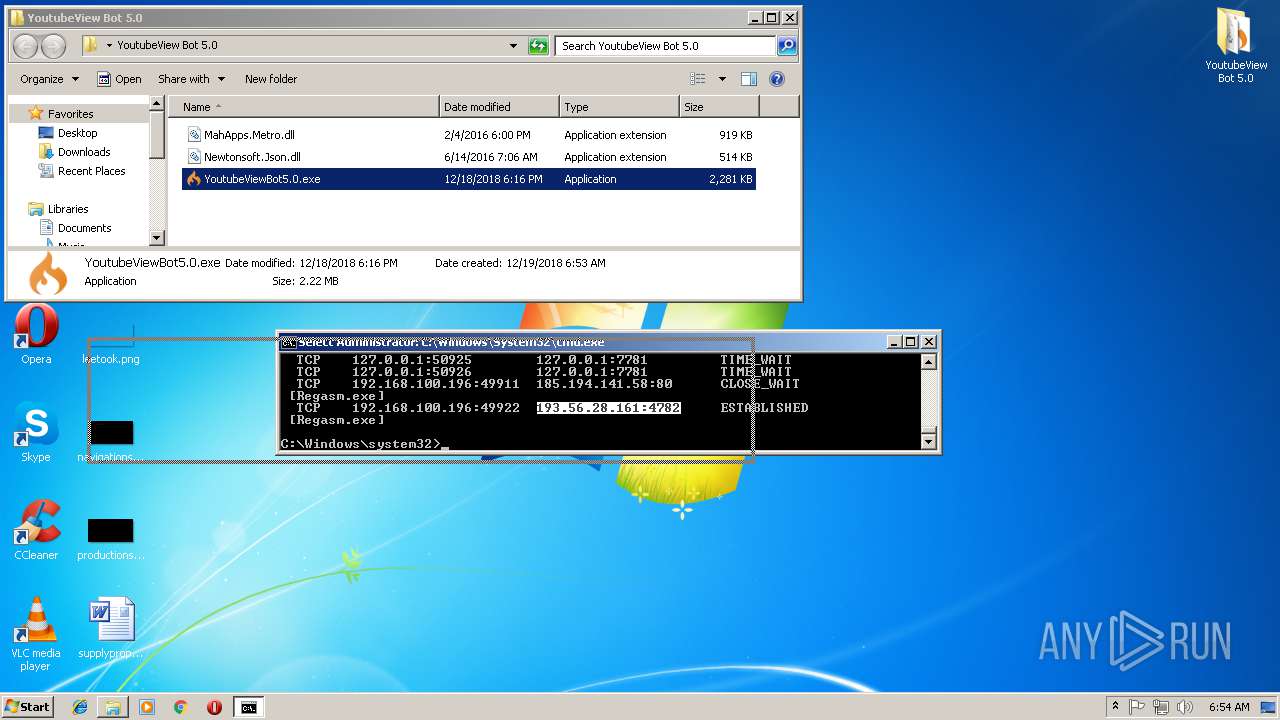
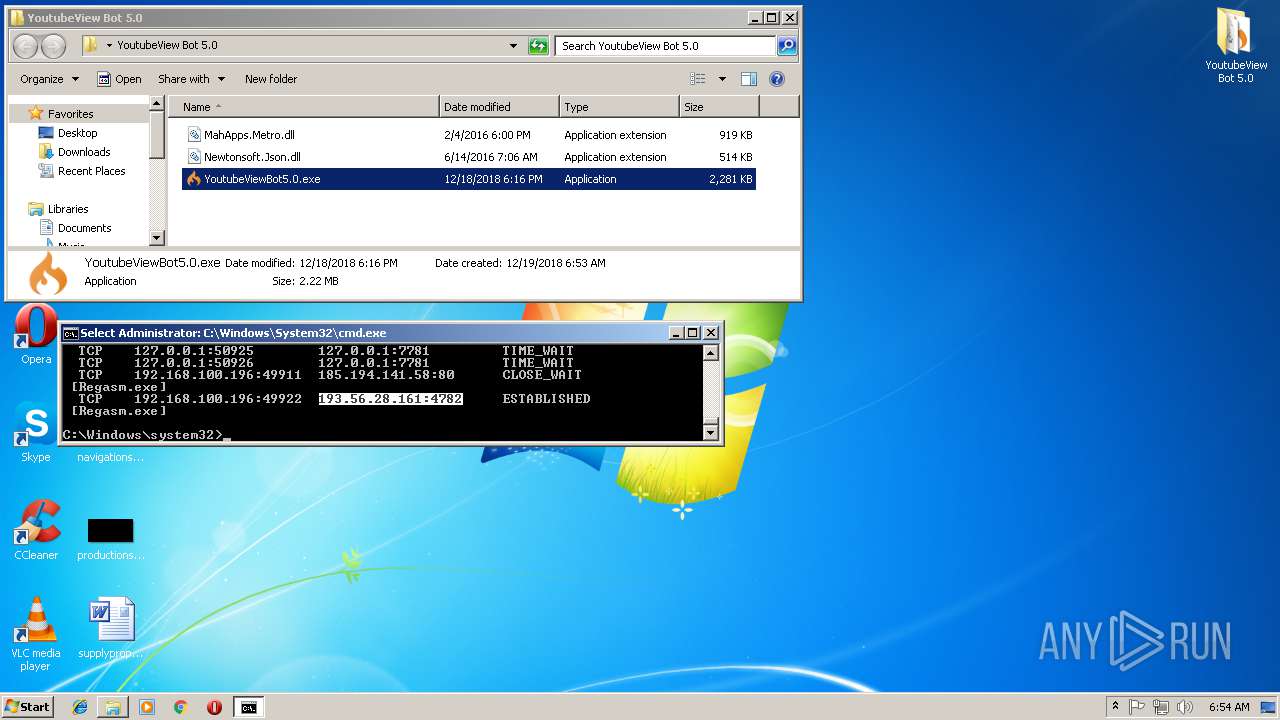
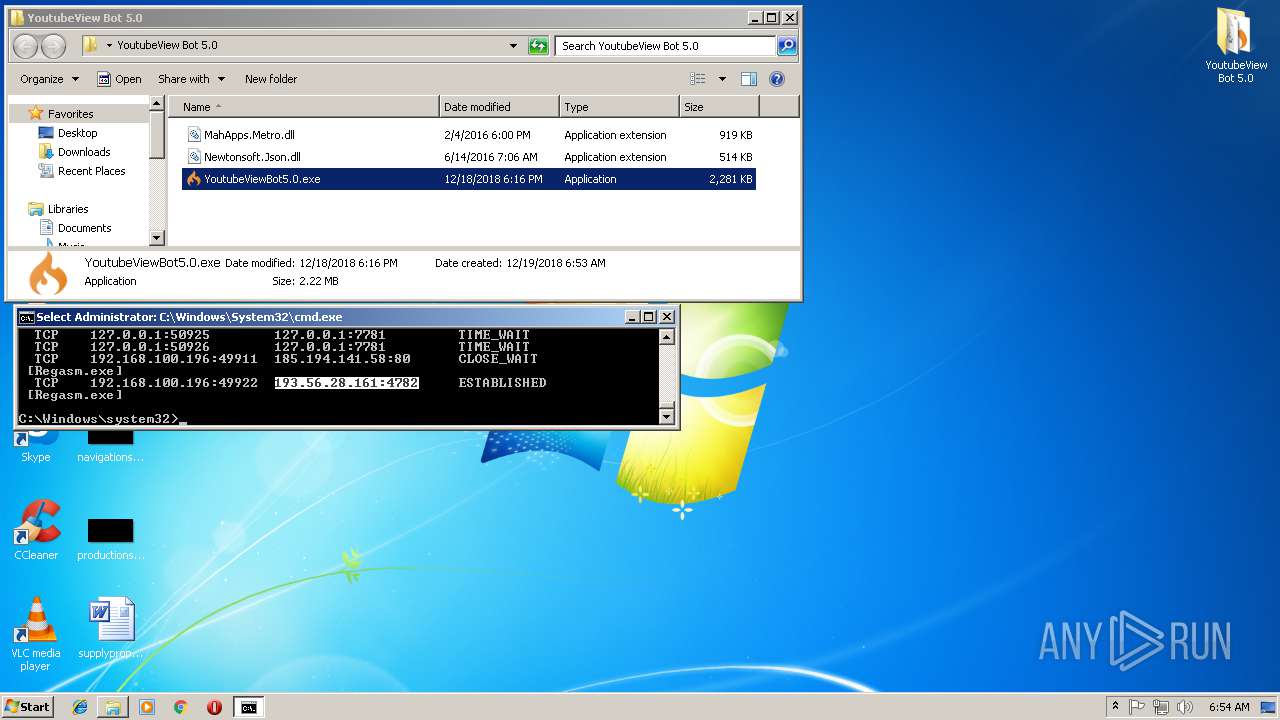
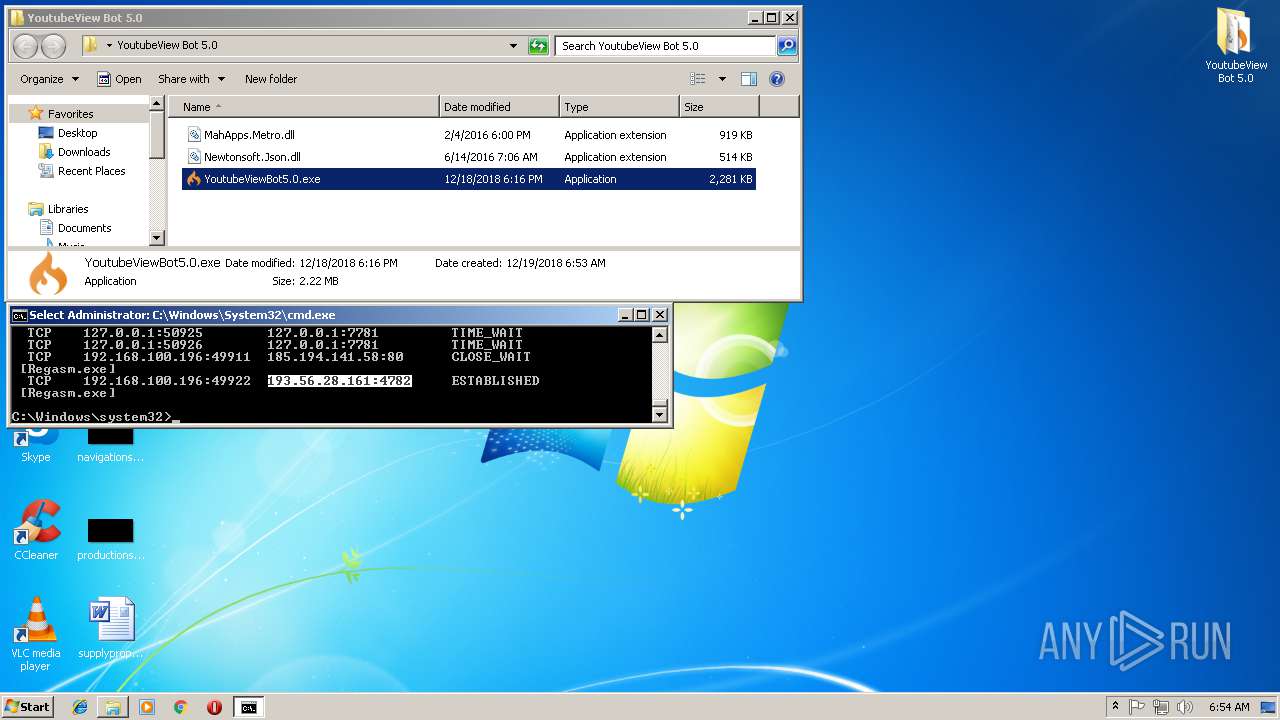
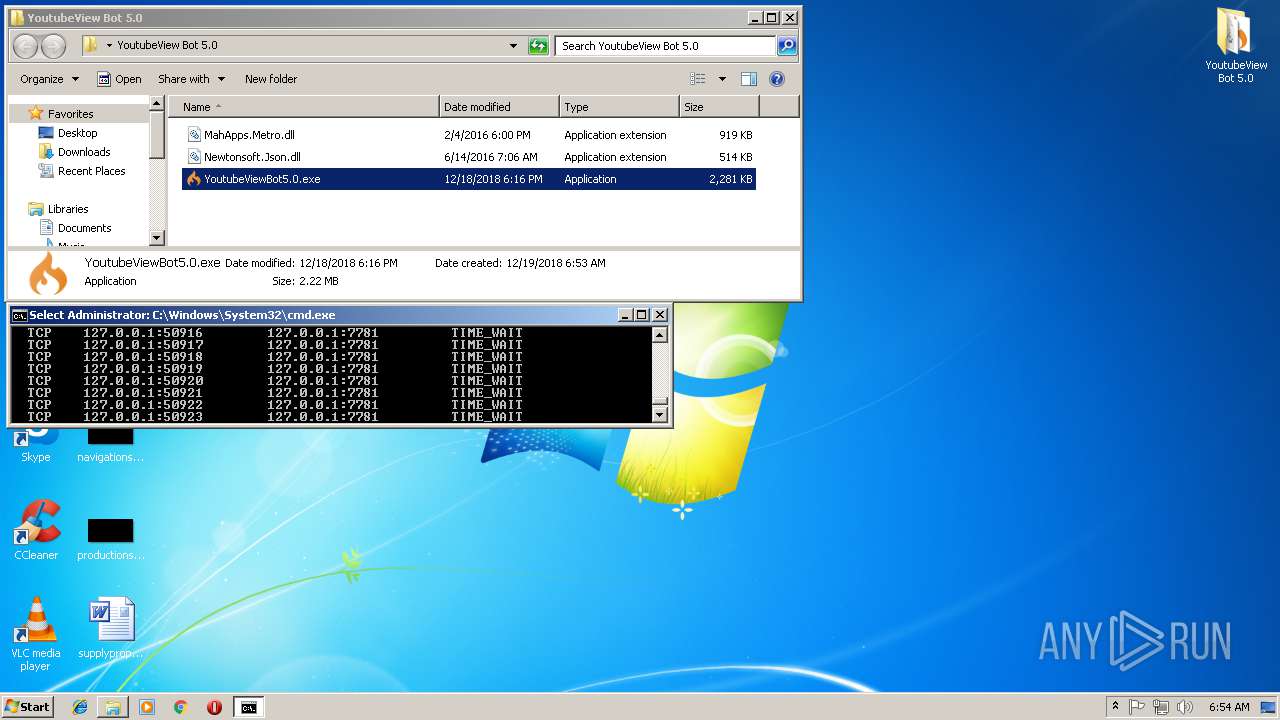
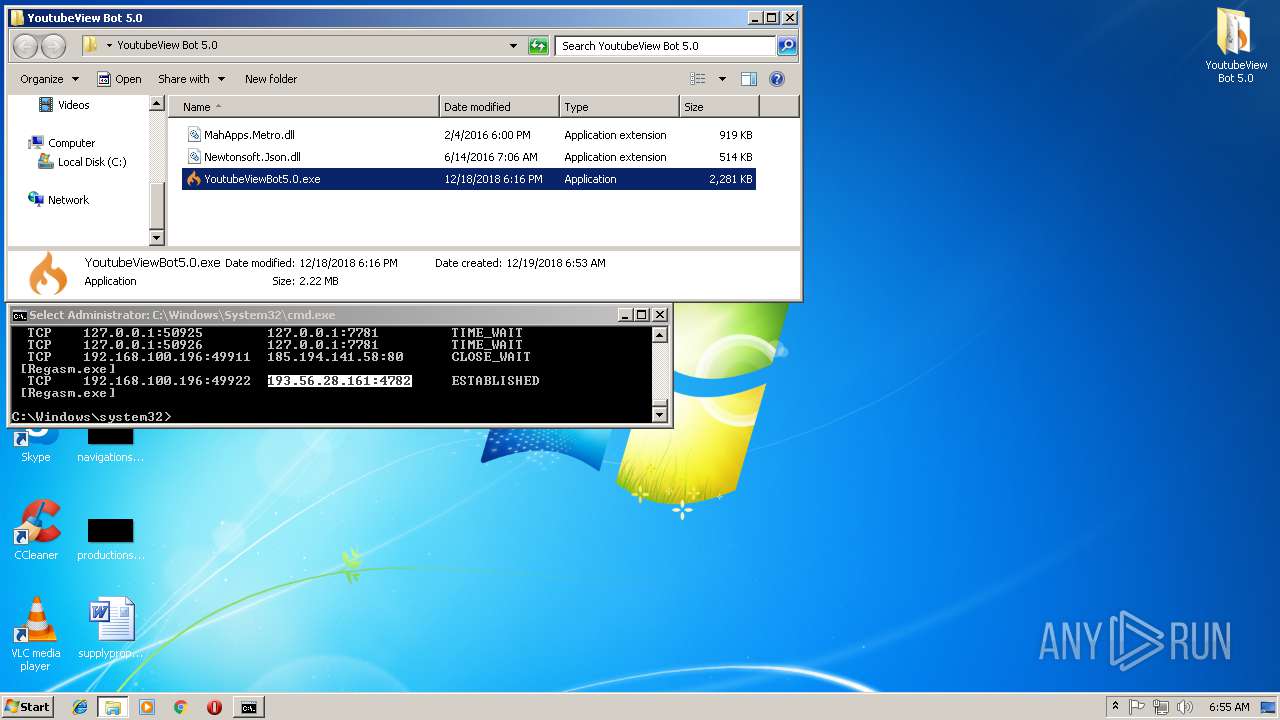
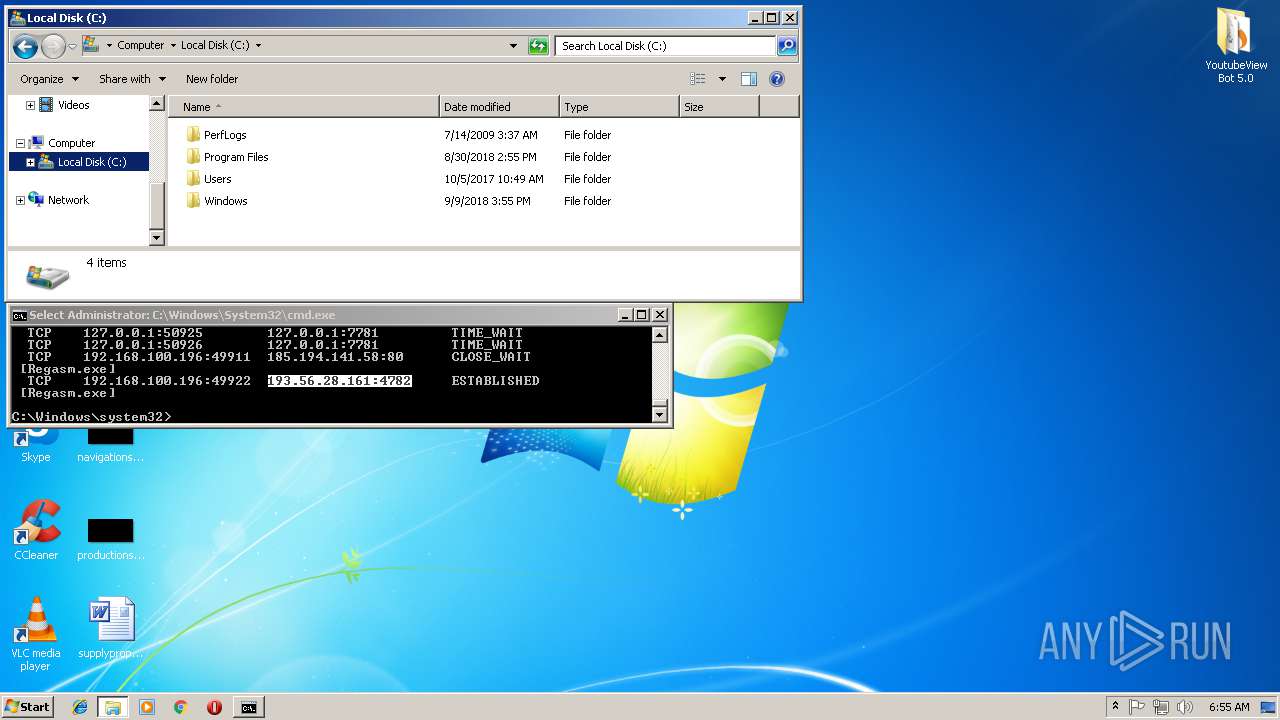
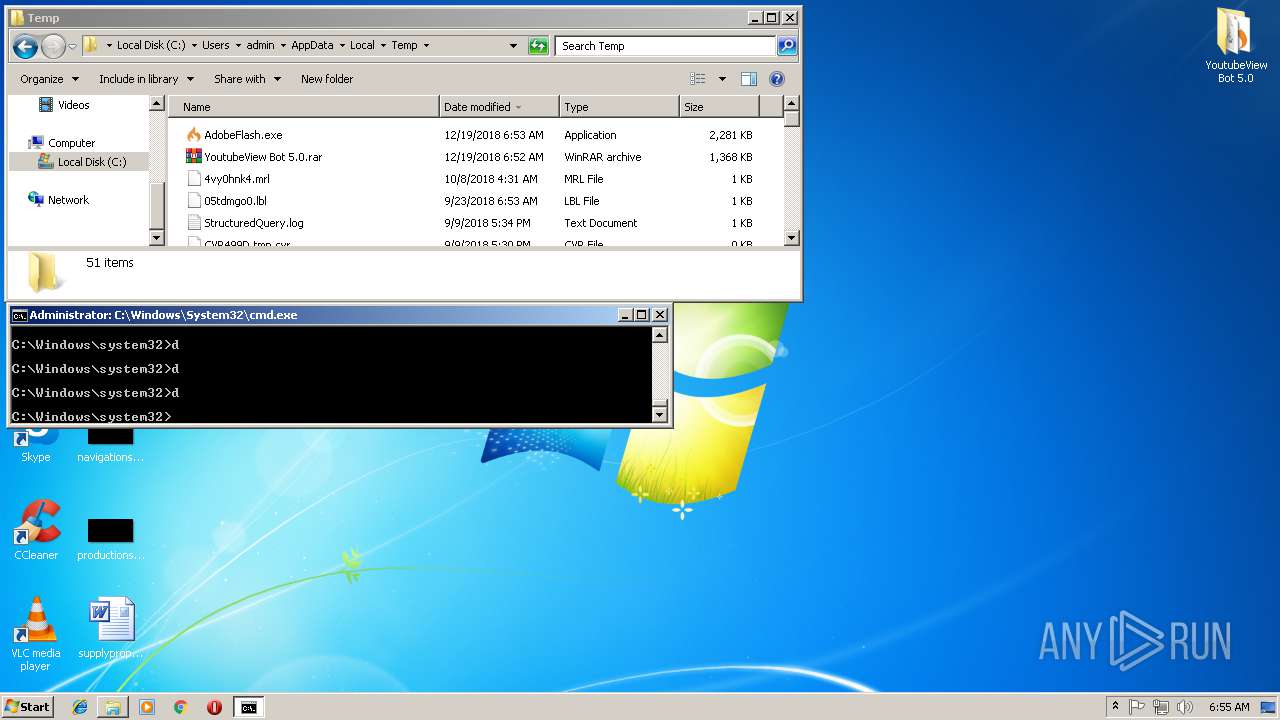
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3948)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
46
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1724 | netstat -nb | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\AppData\Local\Temp\AdobeFlash.exe" | C:\Users\admin\AppData\Local\Temp\AdobeFlash.exe | YoutubeViewBot5.0.exe | ||||||||||||
User: admin Company: CPUID Hardware Monitor Integrity Level: HIGH Description: HWMonitor.exe Exit code: 0 Version: 1.3.4.0 Modules
| |||||||||||||||
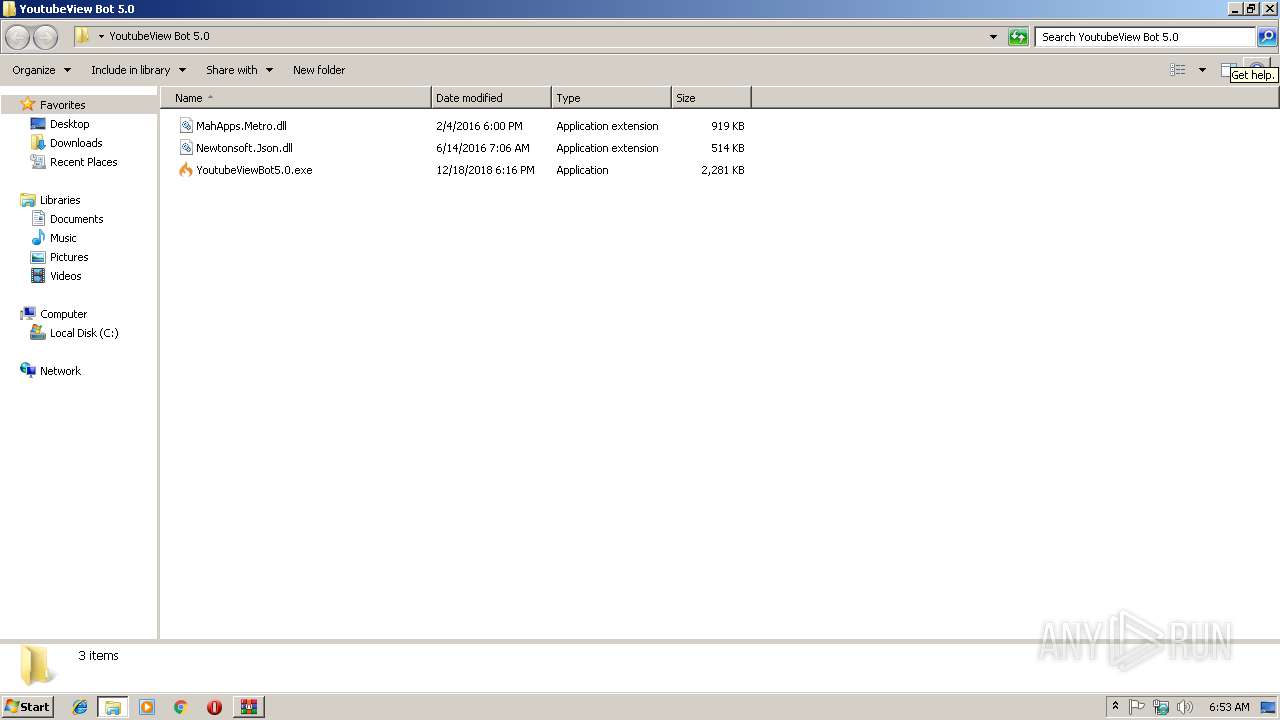
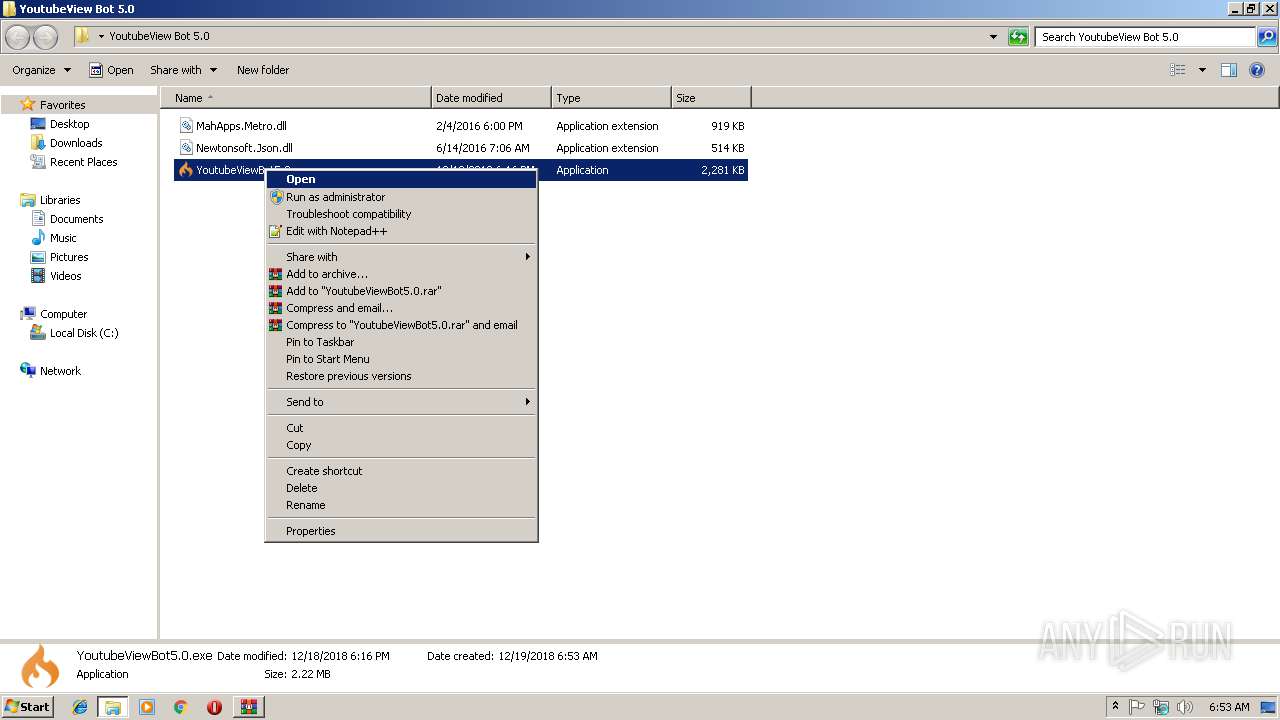
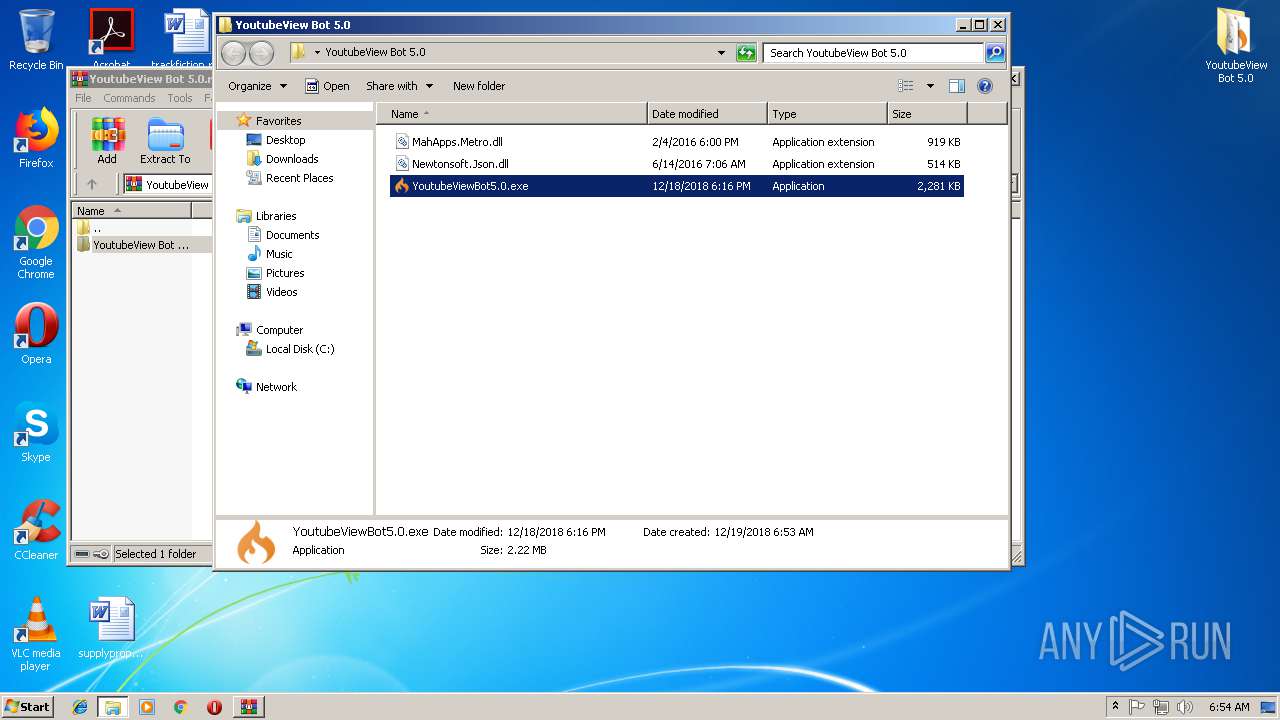
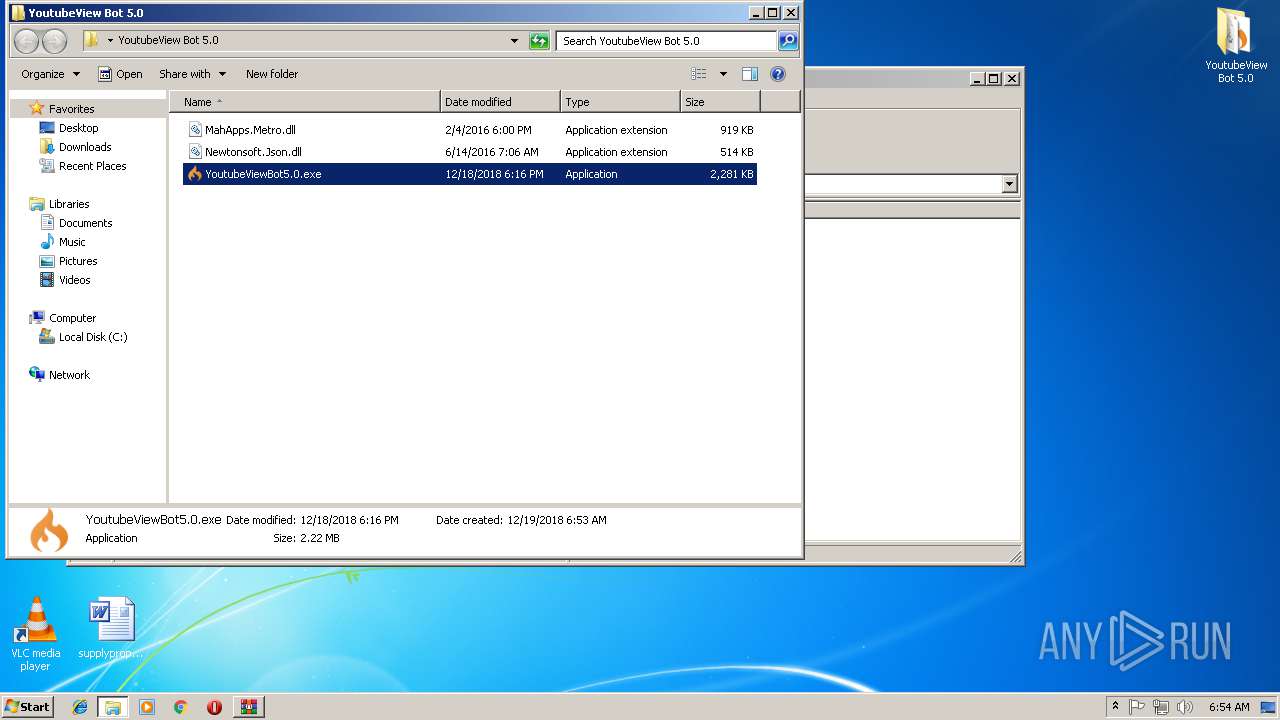
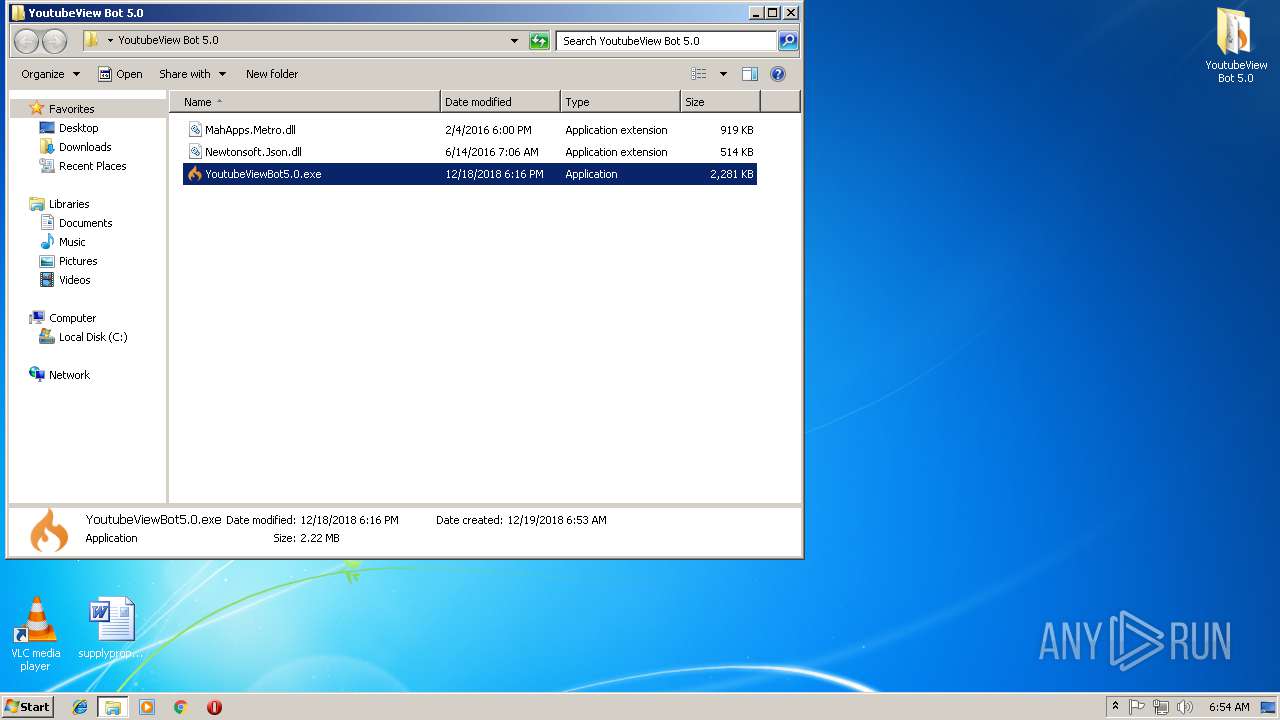
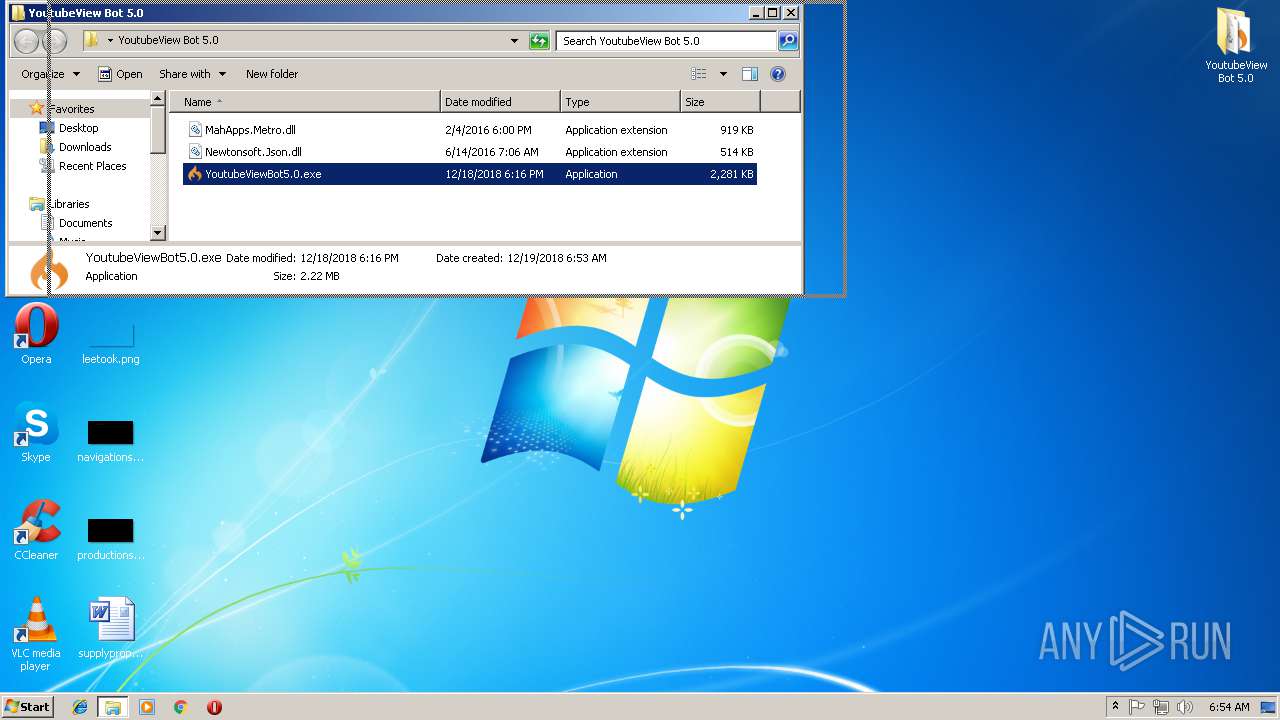
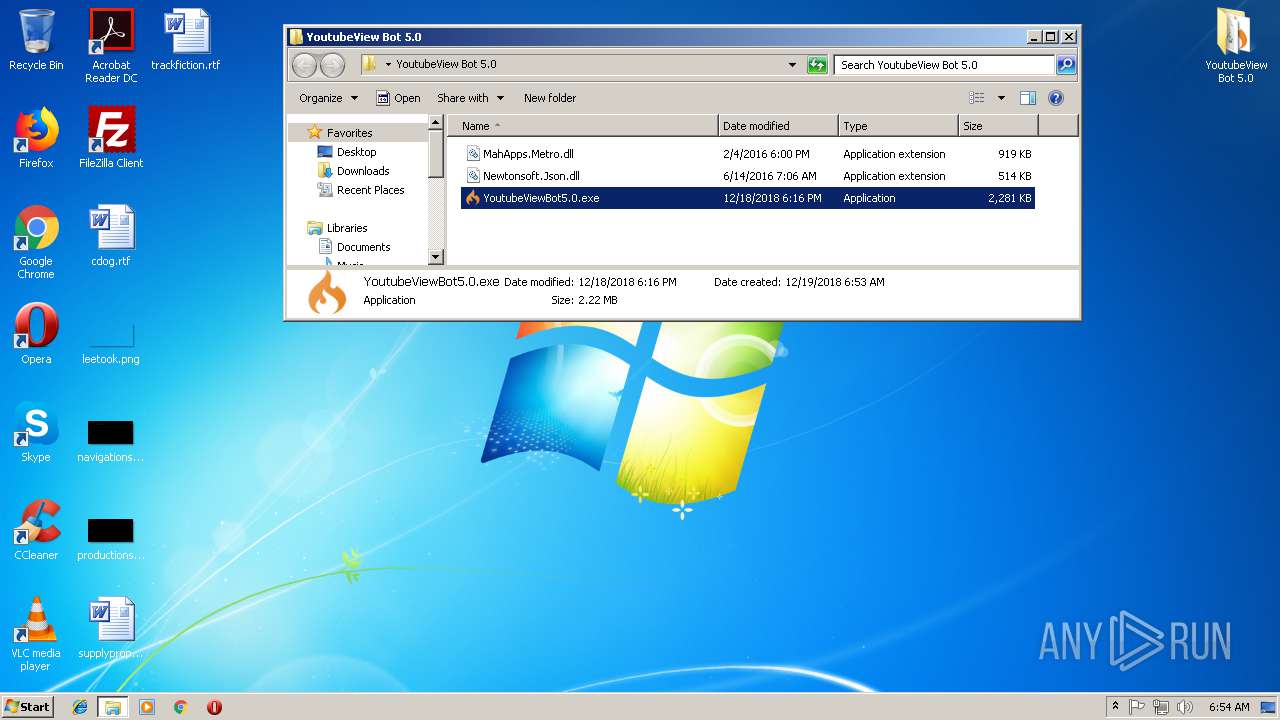
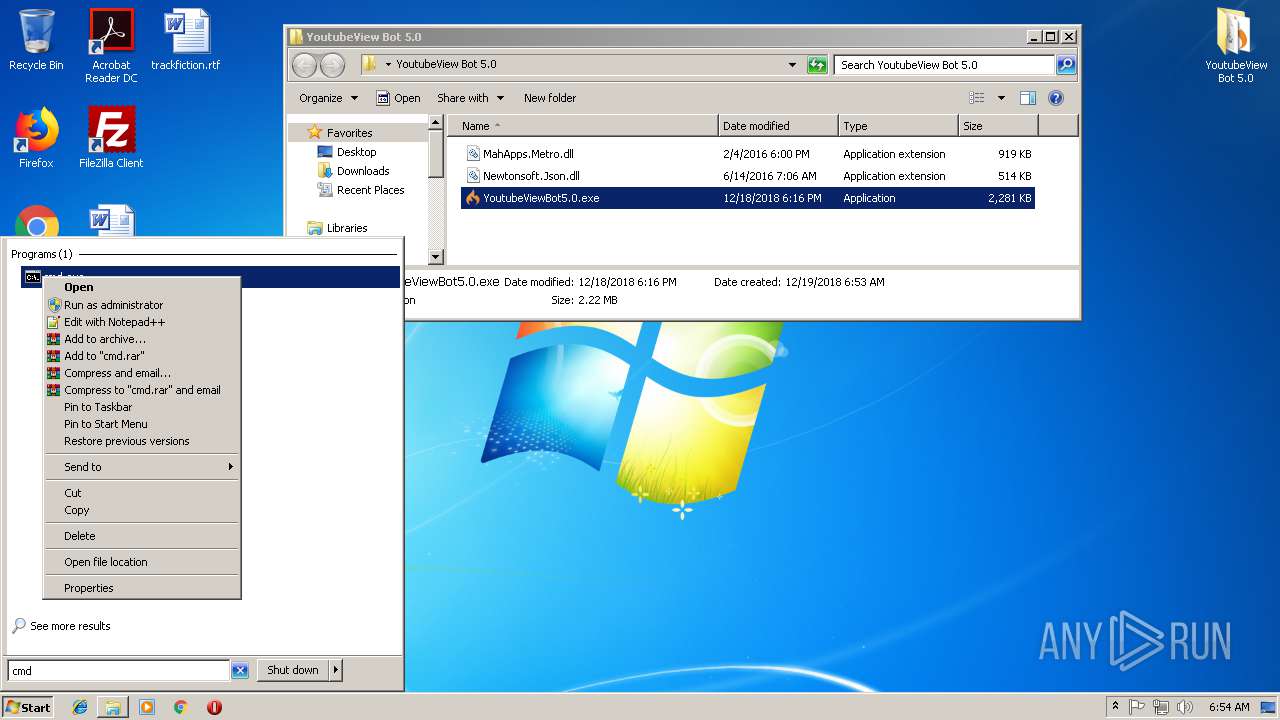
| 2604 | "C:\Users\admin\Desktop\YoutubeView Bot 5.0\YoutubeViewBot5.0.exe" | C:\Users\admin\Desktop\YoutubeView Bot 5.0\YoutubeViewBot5.0.exe | explorer.exe | ||||||||||||
User: admin Company: CPUID Hardware Monitor Integrity Level: HIGH Description: HWMonitor.exe Exit code: 0 Version: 1.3.4.0 Modules
| |||||||||||||||
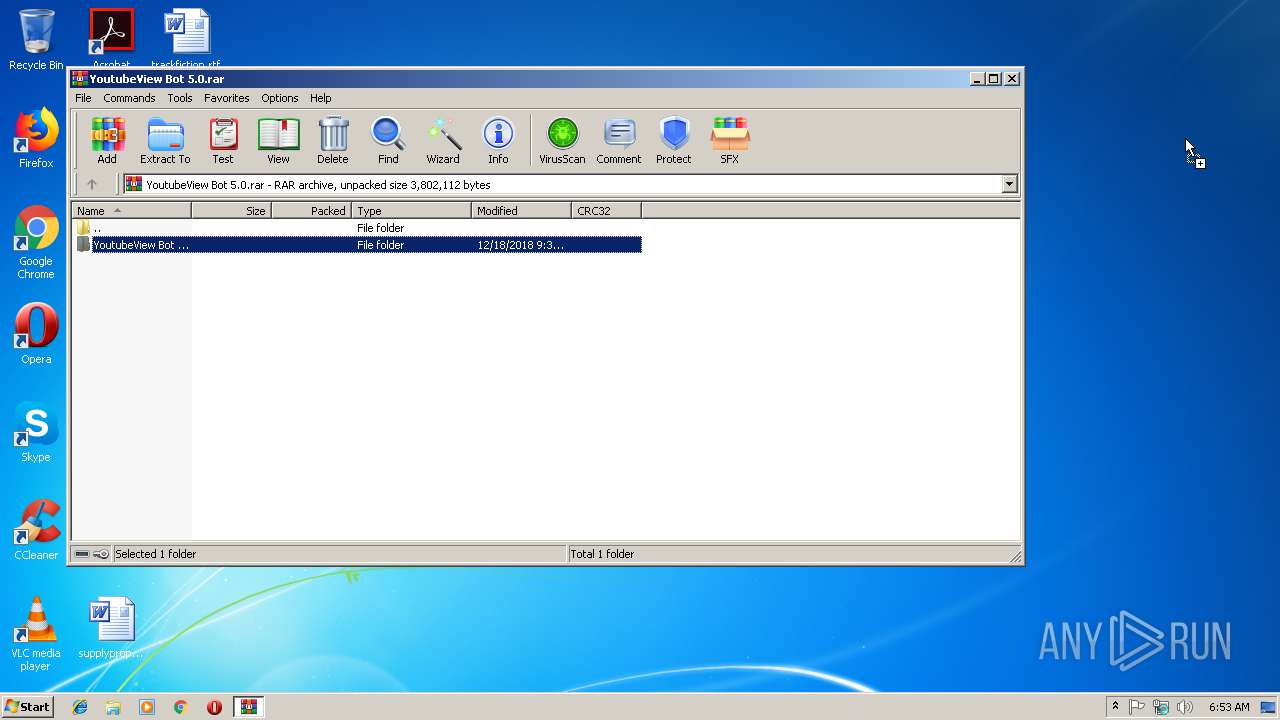
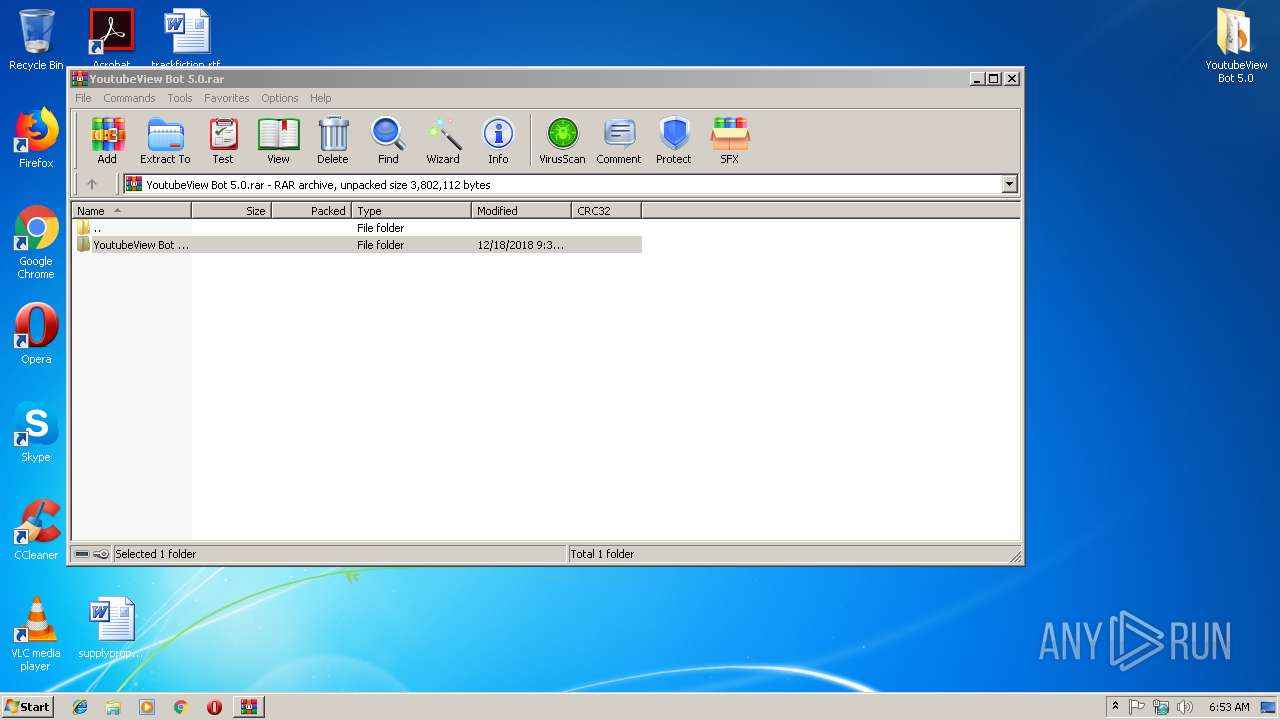
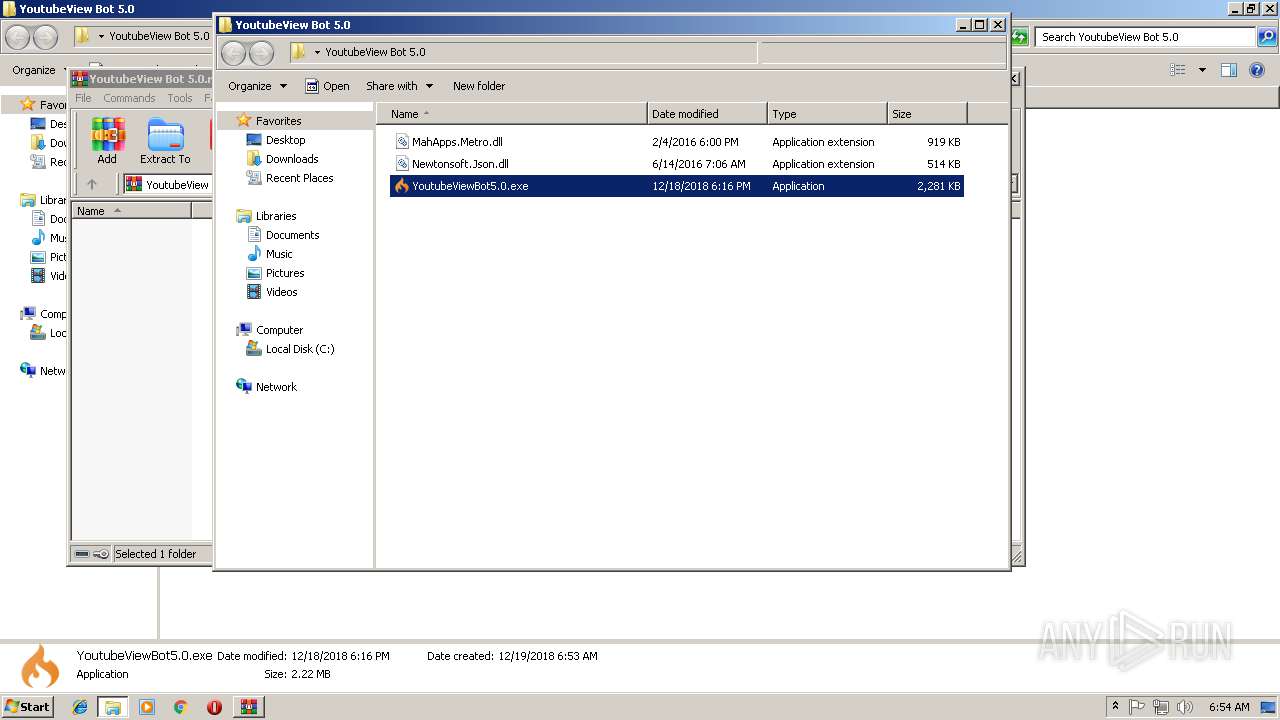
| 2880 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\YoutubeView Bot 5.0.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3036 | netstat -nb | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3928 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | AdobeFlash.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 3948 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
875
Read events
837
Write events
38
Delete events
0
Modification events
| (PID) Process: | (2880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2880) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\YoutubeView Bot 5.0.rar | |||
| (PID) Process: | (2880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2604) YoutubeViewBot5.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Run\CurrentVersion |
| Operation: | write | Name: | AdobeFlash.exe |
Value: C:\Users\admin\AppData\Local\Temp\AdobeFlash.exe | |||
| (PID) Process: | (2604) YoutubeViewBot5.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2880.39364\YoutubeView Bot 5.0\MahApps.Metro.dll | — | |
MD5:— | SHA256:— | |||
| 2880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2880.39364\YoutubeView Bot 5.0\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 2880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2880.39364\YoutubeView Bot 5.0\YoutubeViewBot5.0.exe | — | |
MD5:— | SHA256:— | |||
| 2604 | YoutubeViewBot5.0.exe | C:\Users\admin\AppData\Local\Temp\AdobeFlash.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | Regasm.exe | C:\Users\admin\AppData\Roaming\Logs\12-19-2018 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
4
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3928 | Regasm.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 266 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
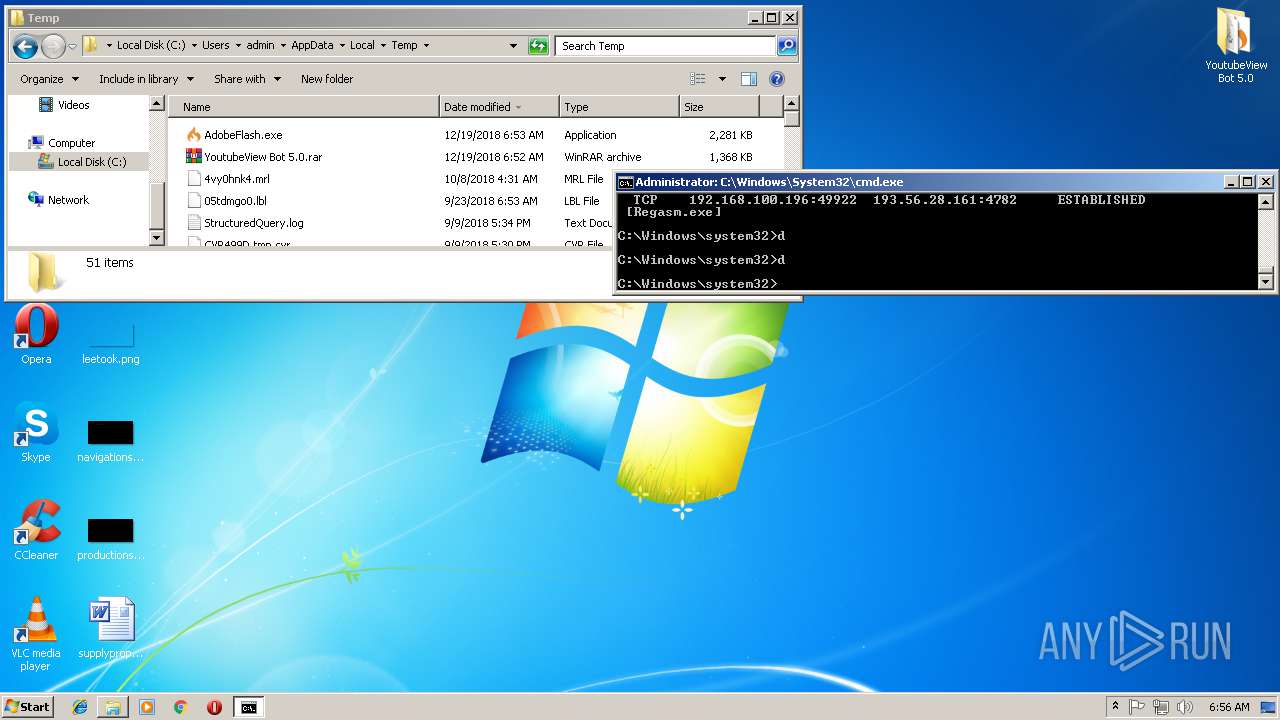
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | Regasm.exe | 193.56.28.161:4782 | repmodz11.duckdns.org | — | — | malicious |
3928 | Regasm.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
repmodz11.duckdns.org |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3928 | Regasm.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3928 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
1056 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
3928 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
YoutubeViewBot5.0.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
YoutubeViewBot5.0.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
YoutubeViewBot5.0.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
YoutubeViewBot5.0.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
YoutubeViewBot5.0.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
YoutubeViewBot5.0.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
YoutubeViewBot5.0.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
YoutubeViewBot5.0.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
AdobeFlash.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
AdobeFlash.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|