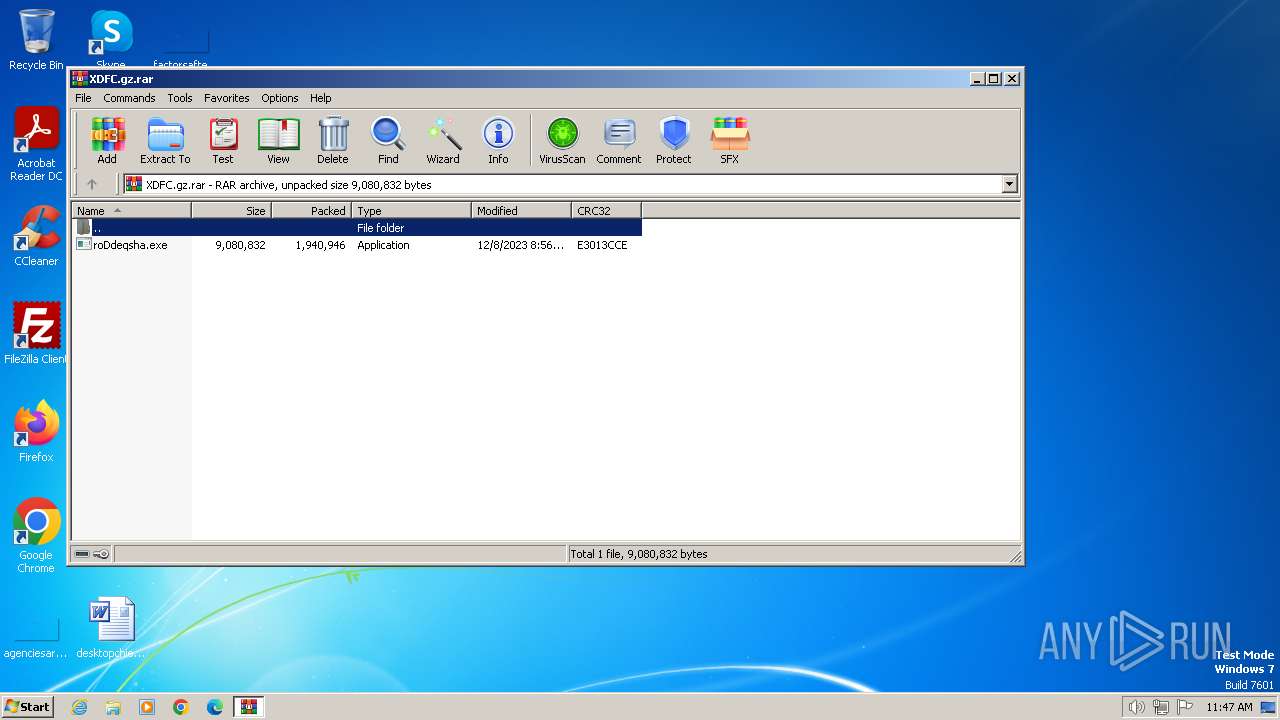
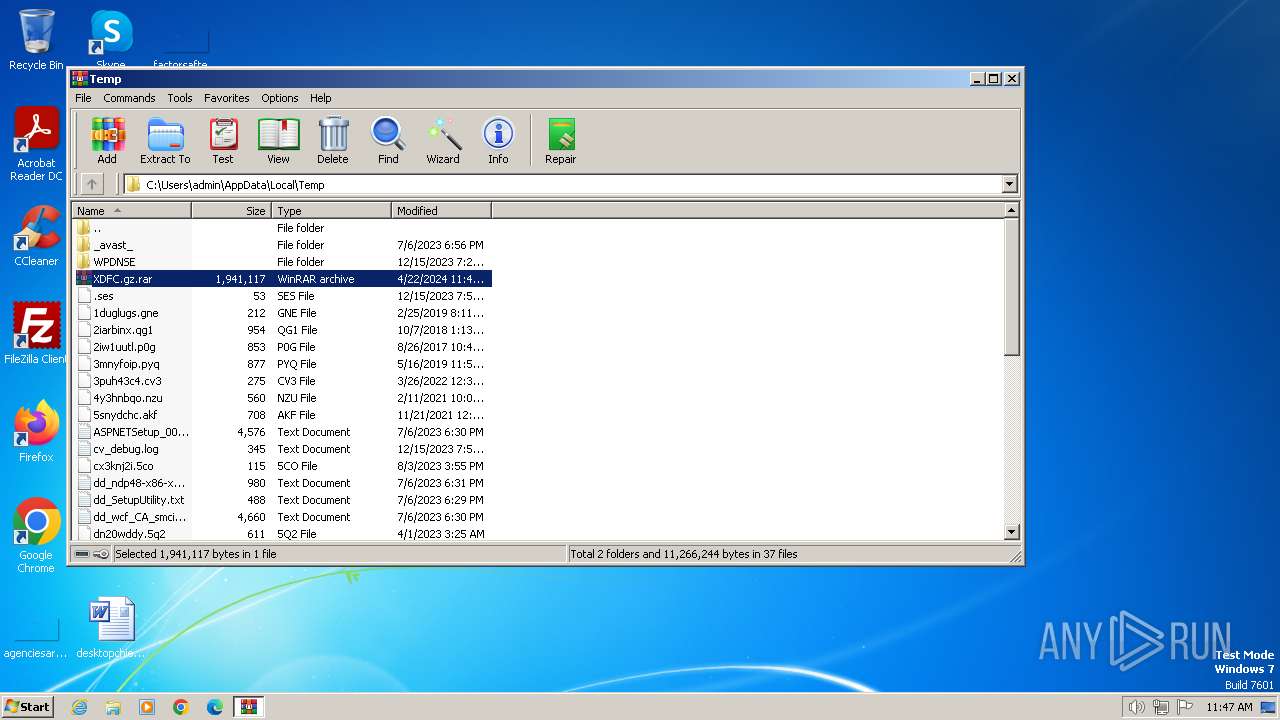
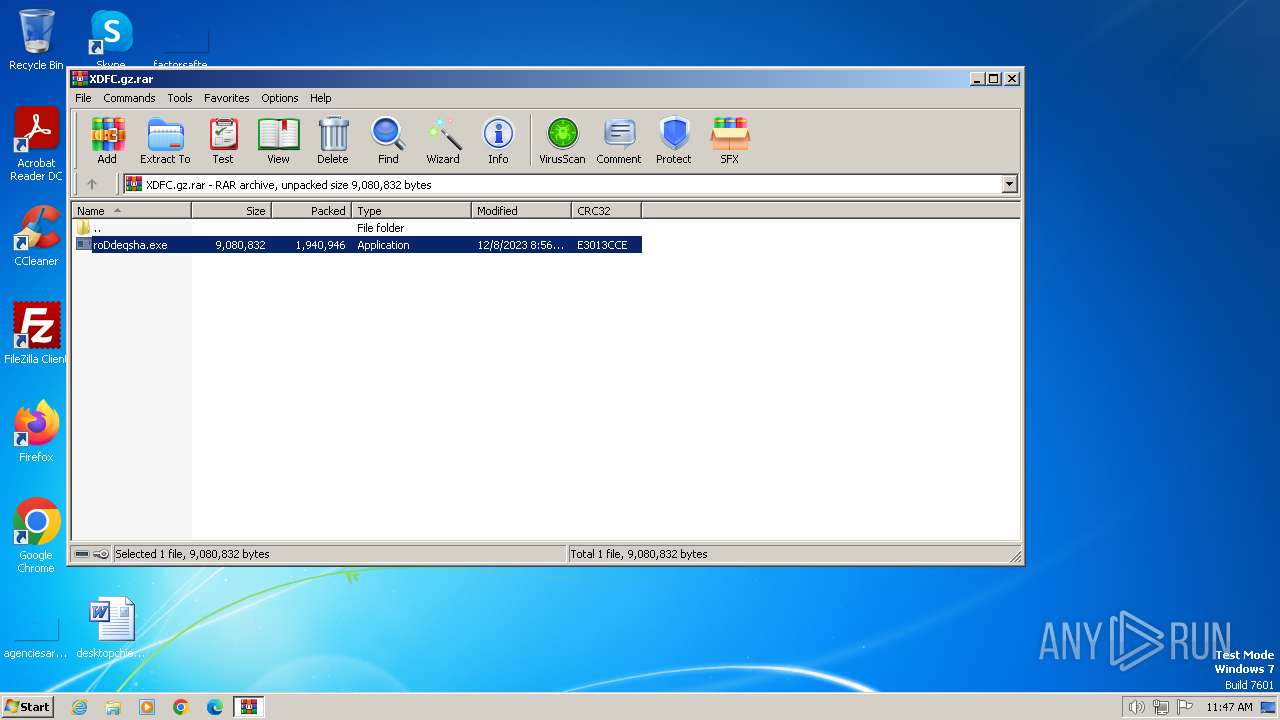
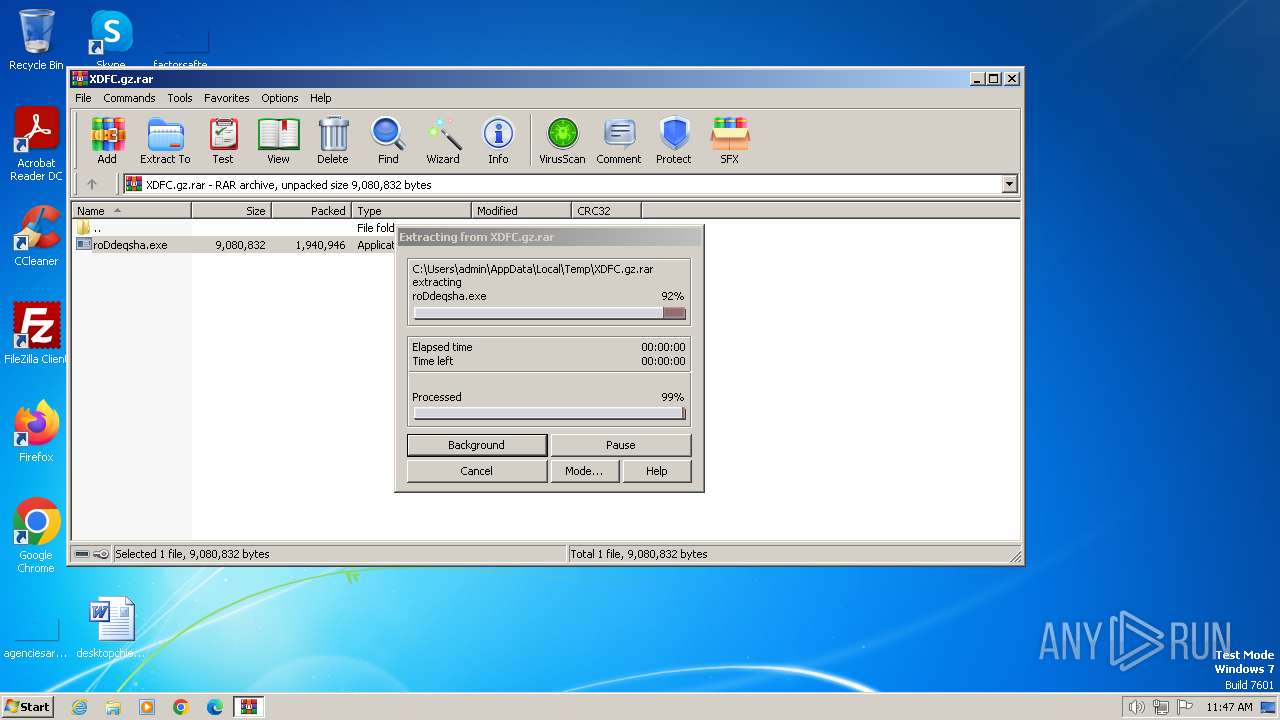
| File name: | XDFC.gz |
| Full analysis: | https://app.any.run/tasks/0eca3a64-7a0d-49e1-86c8-766e68bbb23b |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 22, 2024, 10:47:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
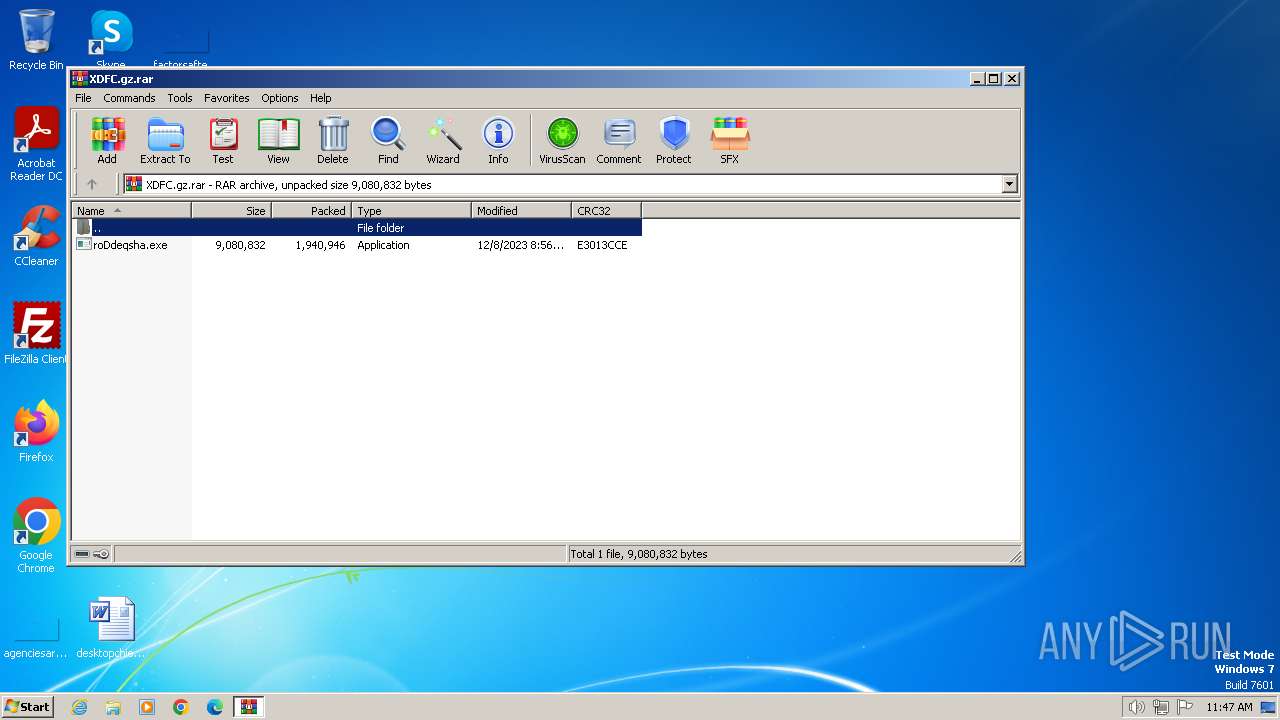
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 6130A8D84CD869CF916B20A8BC411716 |
| SHA1: | 7A8461C813D054995C50AA2D5139A9EF4341C8DB |
| SHA256: | 27866058AEF6D843E79DC8B301272AE2C9F76CBBD5EB32F993CEF74DA418BD60 |
| SSDEEP: | 98304:r1GsT9NwLA8uVr01BHtgyc3E8PvuhBQCVvWeArSzJk1p+NkSQHNh/5qxK/PWsQ+1:rpJCy |
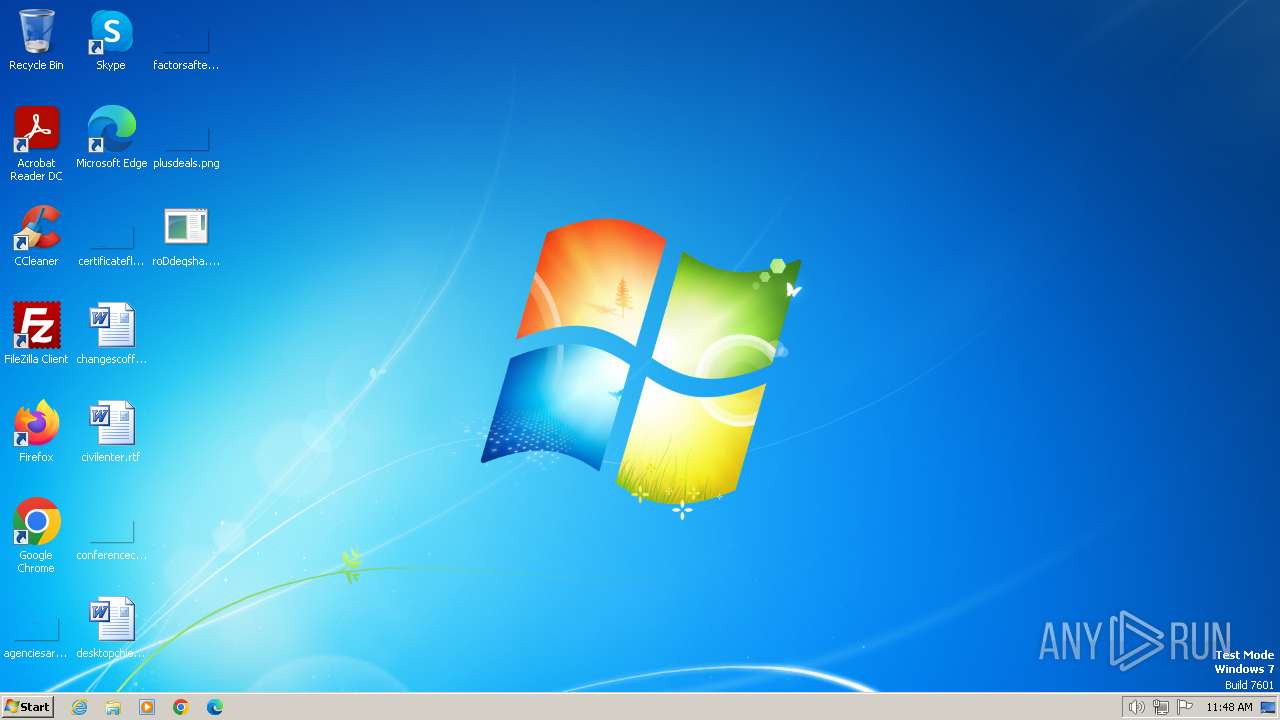
MALICIOUS
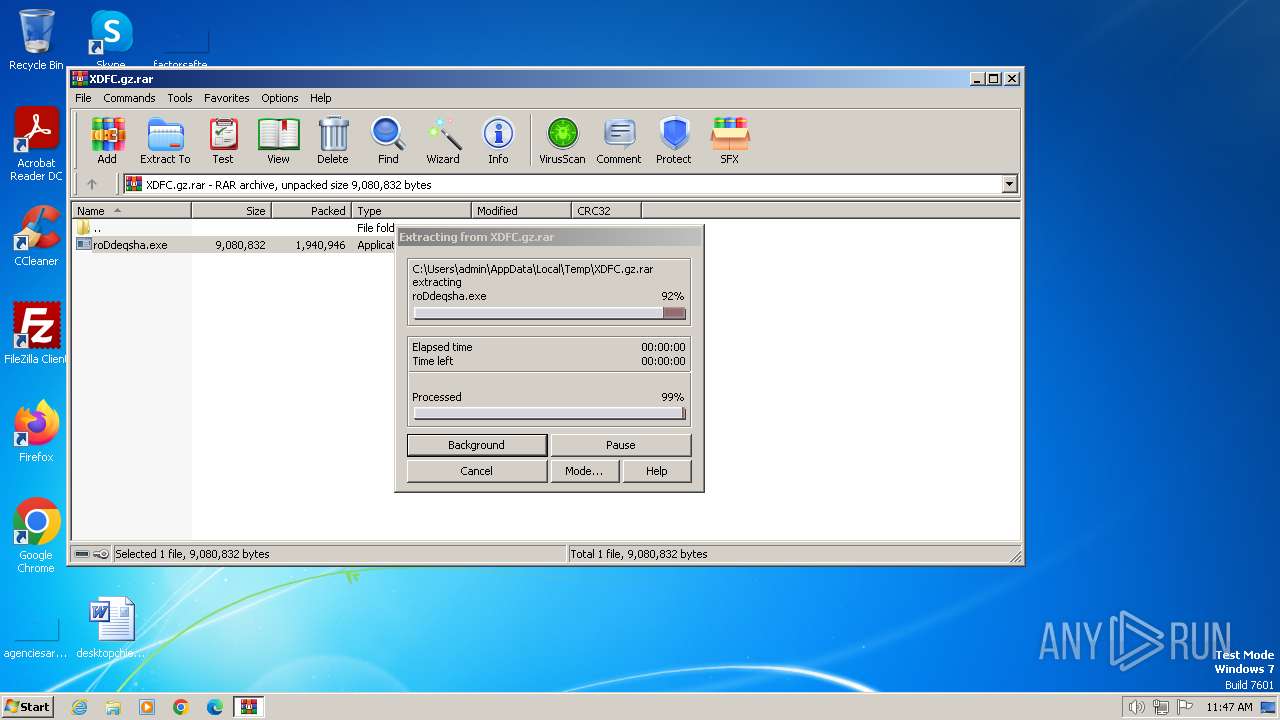
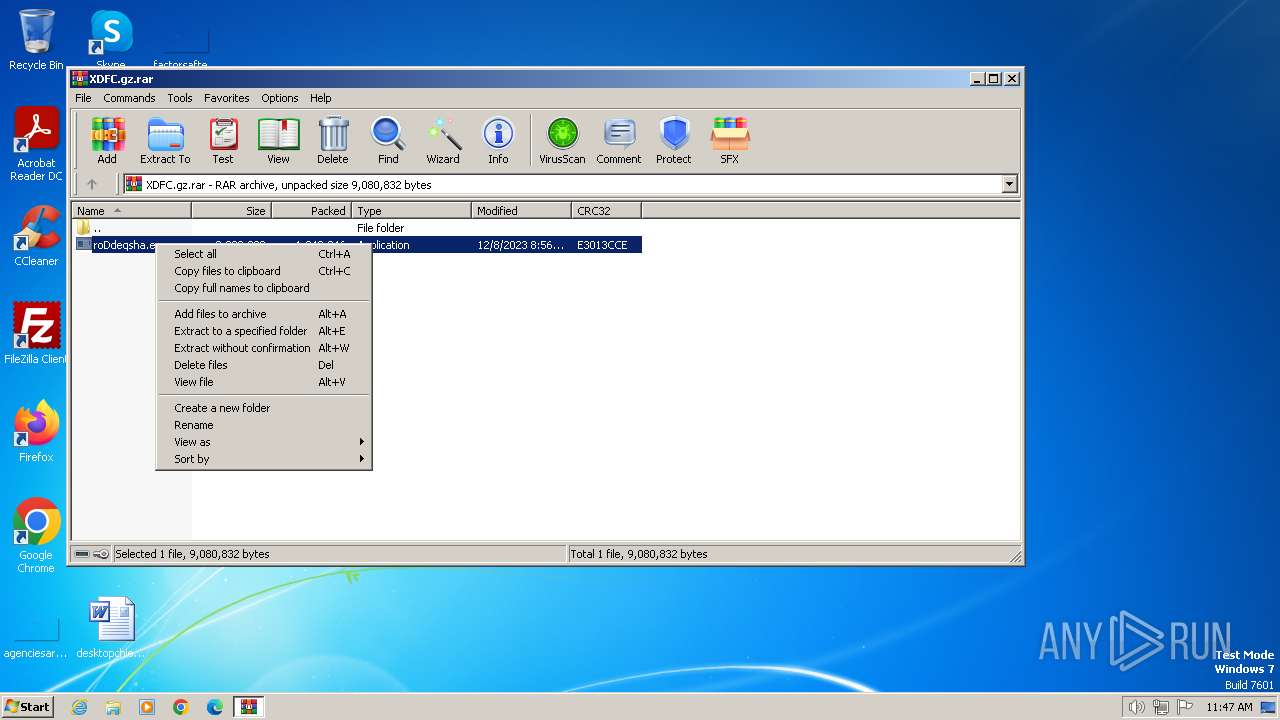
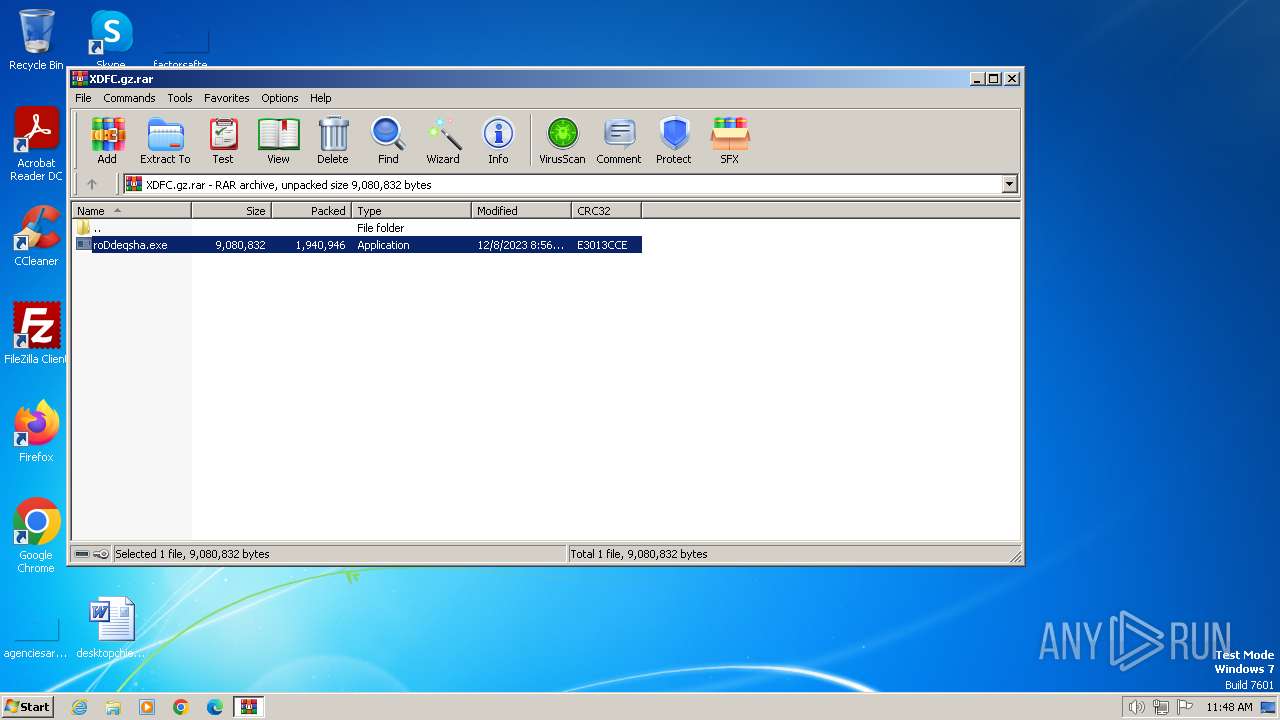
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1072)
Actions looks like stealing of personal data
- roDdeqsha.exe (PID: 2360)
AGENTTESLA has been detected (YARA)
- roDdeqsha.exe (PID: 2360)
Steals credentials from Web Browsers
- roDdeqsha.exe (PID: 2360)
SUSPICIOUS
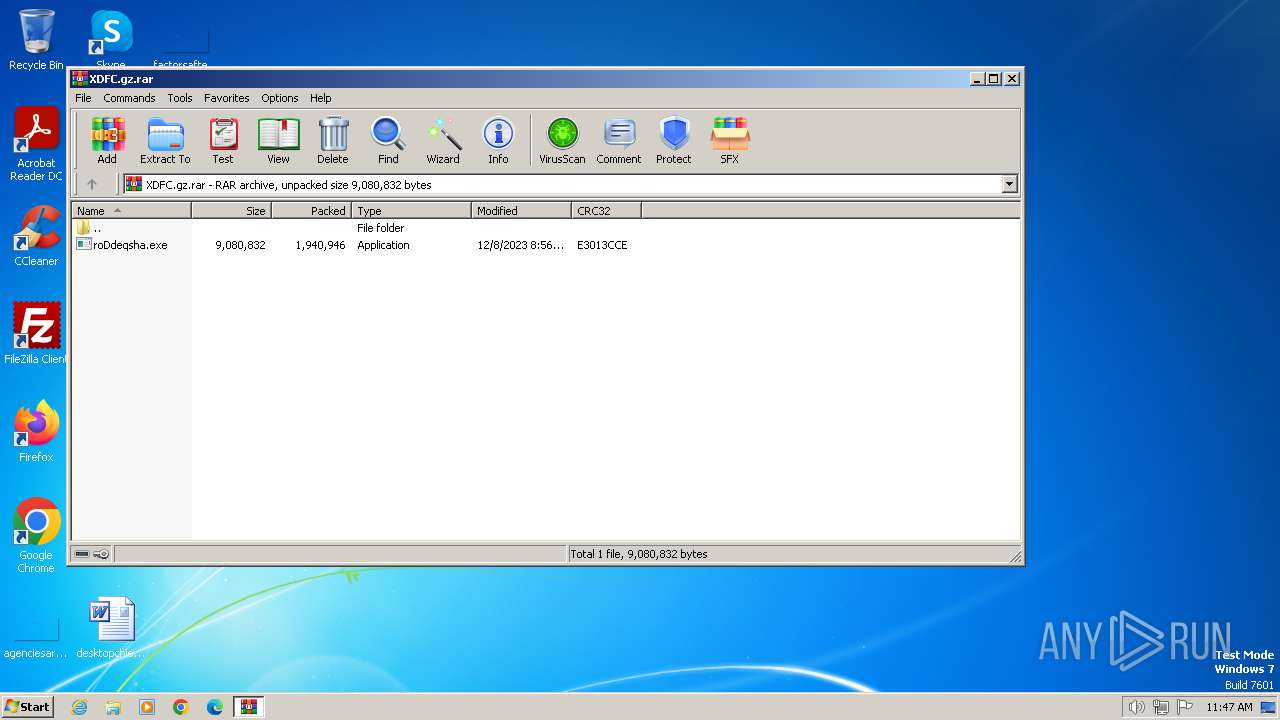
Creates file in the systems drive root
- WinRAR.exe (PID: 1072)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1072)
Application launched itself
- roDdeqsha.exe (PID: 2812)
Reads the Internet Settings
- roDdeqsha.exe (PID: 2360)
Connects to SMTP port
- roDdeqsha.exe (PID: 2360)
Checks for external IP
- roDdeqsha.exe (PID: 2360)
Accesses Microsoft Outlook profiles
- roDdeqsha.exe (PID: 2360)
INFO
Reads the computer name
- roDdeqsha.exe (PID: 2812)
- roDdeqsha.exe (PID: 2360)
Checks supported languages
- roDdeqsha.exe (PID: 2812)
- roDdeqsha.exe (PID: 2360)
Reads the machine GUID from the registry
- roDdeqsha.exe (PID: 2812)
- roDdeqsha.exe (PID: 2360)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1072)
Reads Environment values
- roDdeqsha.exe (PID: 2360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(2360) roDdeqsha.exe
Protocolsmtp
Hostmail.gencoldfire.com
Port587
Usernameroycoo@gencoldfire.com
PasswordU+&%W@y1mSEUOinP
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
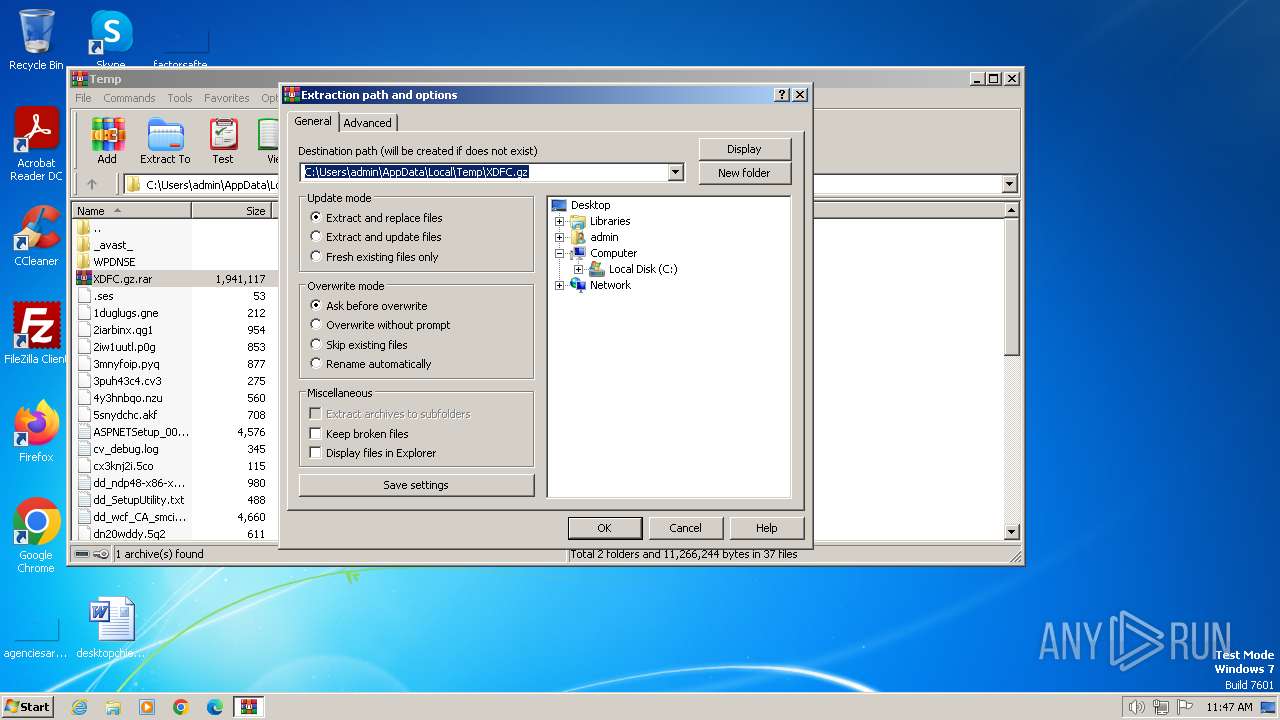
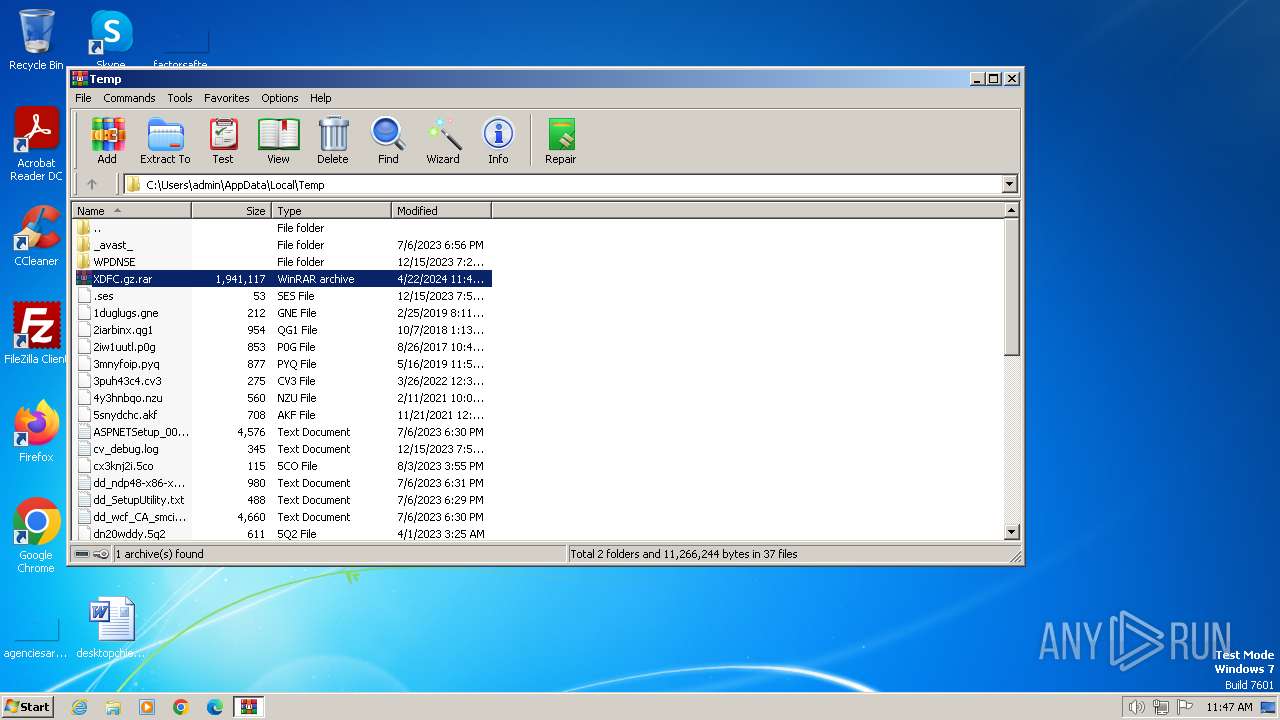
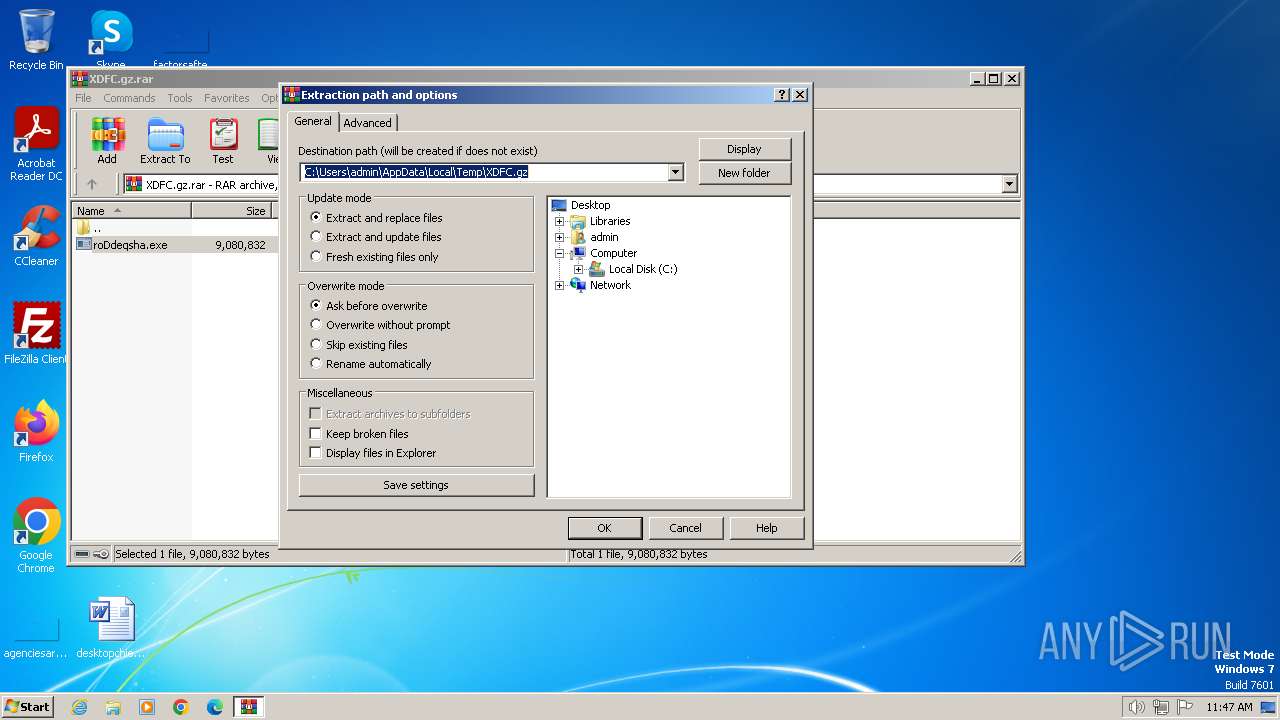
| 1072 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\XDFC.gz.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2360 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1072.16678\roDdeqsha.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1072.16678\roDdeqsha.exe | roDdeqsha.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: roDdeqsha Version: 1.0.0.0 Modules
AgentTesla(PID) Process(2360) roDdeqsha.exe Protocolsmtp Hostmail.gencoldfire.com Port587 Usernameroycoo@gencoldfire.com PasswordU+&%W@y1mSEUOinP | |||||||||||||||
| 2812 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1072.16678\roDdeqsha.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1072.16678\roDdeqsha.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: roDdeqsha Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
6 307
Read events
6 243
Write events
64
Delete events
0
Modification events
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\XDFC.gz.rar | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1072 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1072.16678\roDdeqsha.exe | executable | |
MD5:F319406EF27E59AD03A9772A888A0EF9 | SHA256:280477DBC907FFBA1A294CCD7A2B8B72A4DDC660956BE96C893BD2353D2B7ABA | |||
| 1072 | WinRAR.exe | C:\Users\admin\Desktop\roDdeqsha.exe | executable | |
MD5:F319406EF27E59AD03A9772A888A0EF9 | SHA256:280477DBC907FFBA1A294CCD7A2B8B72A4DDC660956BE96C893BD2353D2B7ABA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
3
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2360 | roDdeqsha.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | US | text | 6 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2360 | roDdeqsha.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
2360 | roDdeqsha.exe | 185.196.11.12:587 | mail.gencoldfire.com | Simple Carrier LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
mail.gencoldfire.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
— | — | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2360 | roDdeqsha.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 32 |
— | — | Misc activity | INFO [ANY.RUN] SMTP email client opens transfer with server (EHLO) |