| File name: | joker.exe |
| Full analysis: | https://app.any.run/tasks/6a8a3694-8423-4b93-95fc-d81ae6d065aa |
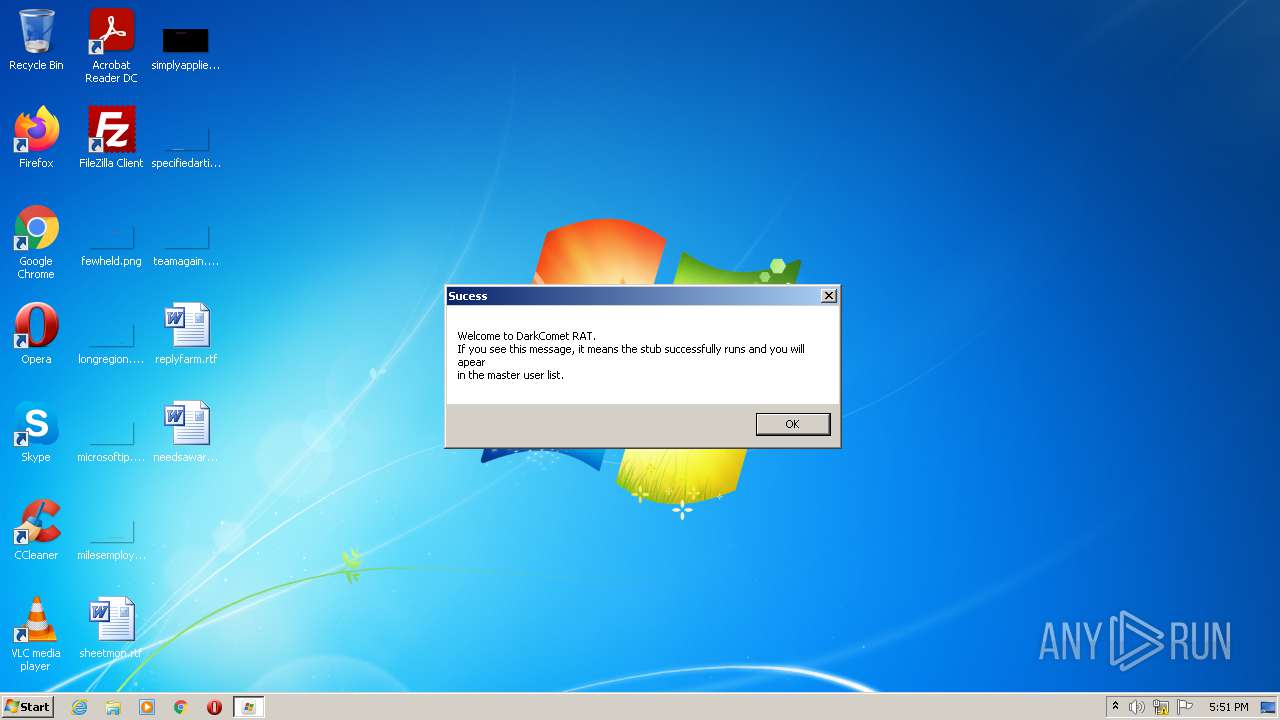
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | October 25, 2021, 16:51:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EB0AA0DA75E27010172B23845E993BC1 |
| SHA1: | 9FA6168354B70E3781C6C9A9E9715356E916804C |
| SHA256: | 2746FBE2BB6425AA492AEEB054A40AA1077B71E3CE1A21A0335FEDE10AD7280A |
| SSDEEP: | 12288:19HFJ9rJxRX1uVVjoaWSoynxdO1FVBaOiRZTERfIhNkNCCLo9Ek5C/hZs:/Z1xuVVjfFoynPaVBUR8f+kN10EBQ |
MALICIOUS
Changes the autorun value in the registry
- joker.exe (PID: 3984)
Changes the login/logoff helper path in the registry
- joker.exe (PID: 3984)
DARKCOMET was detected
- joker.exe (PID: 3984)
SUSPICIOUS
Checks supported languages
- joker.exe (PID: 3984)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2736)
Reads the computer name
- joker.exe (PID: 3984)
Starts CMD.EXE for commands execution
- joker.exe (PID: 3984)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2736)
INFO
Checks supported languages
- notepad.exe (PID: 2792)
- attrib.exe (PID: 3060)
- attrib.exe (PID: 3036)
- opera.exe (PID: 576)
Manual execution by user
- opera.exe (PID: 576)
Reads the computer name
- opera.exe (PID: 576)
Check for Java to be installed
- opera.exe (PID: 576)
Creates files in the user directory
- opera.exe (PID: 576)
Reads the date of Windows installation
- opera.exe (PID: 576)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:07 17:59:53+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 586752 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8f888 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Remote Service Application |
| CompanyName: | Microsoft Corp. |
| FileDescription: | Remote Service Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | MSRSAAPP |
| LegalCopyright: | Copyright (C) 1999 |
| OriginalFileName: | MSRSAAP.EXE |
| ProductName: | Remote Service Application |
| ProductVersion: | 4, 0, 0, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jun-2012 15:59:53 |
| Detected languages: |
|
| Comments: | Remote Service Application |
| CompanyName: | Microsoft Corp. |
| FileDescription: | Remote Service Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | MSRSAAPP |
| LegalCopyright: | Copyright (C) 1999 |
| OriginalFilename: | MSRSAAP.EXE |
| ProductName: | Remote Service Application |
| ProductVersion: | 4, 0, 0, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 07-Jun-2012 15:59:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008D8F0 | 0x0008DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55342 |
.itext | 0x0008F000 | 0x00001954 | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95375 |
.data | 0x00091000 | 0x00003D3C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.83487 |
.bss | 0x00095000 | 0x00007404 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0009D000 | 0x00004140 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.26814 |
.tls | 0x000A2000 | 0x00000038 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000A3000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 0x000A4000 | 0x00008ADC | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.72501 |
.rsrc | 0x000AD000 | 0x0000C40C | 0x0000C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52684 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34616 | 856 | Latin 1 / Western European | French - France | RT_VERSION |
2 | 2.80231 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
50 | 5.3168 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
51 | 5.45392 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
52 | 5.41522 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
AVICAP32.DLL |
SHELL32.DLL |
SHFolder.dll |
URLMON.DLL |
WS2_32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
gdiplus.dll |
kernel32.dll |
Total processes
41
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2644 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\AppData\Local\Temp\joker.exe" +s +h | C:\Windows\System32\cmd.exe | — | joker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2736 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\AppData\Local\Temp" +s +h | C:\Windows\System32\cmd.exe | — | joker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2792 | notepad | C:\Windows\system32\notepad.exe | — | joker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3036 | attrib "C:\Users\admin\AppData\Local\Temp\joker.exe" +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3060 | attrib "C:\Users\admin\AppData\Local\Temp" +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\Temp\joker.exe" | C:\Users\admin\AppData\Local\Temp\joker.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 314
Read events
1 194
Write events
120
Delete events
0
Modification events
| (PID) Process: | (3984) joker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicroUpdate |
Value: C:\ProgramData\Microsoft\Windows\Start Menu\Programs\MSDCSC\2etfnZ7m4W9C\msdcsc.exe | |||
| (PID) Process: | (3984) joker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | UserInit |
Value: C:\Windows\system32\userinit.exe,C:\ProgramData\Microsoft\Windows\Start Menu\Programs\MSDCSC\2etfnZ7m4W9C\msdcsc.exe | |||
| (PID) Process: | (3984) joker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3984) joker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3984) joker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3984) joker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (576) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (576) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
25
Text files
15
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprECD9.tmp | text | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\36FB2W7SW1EMRCV280V8.temp | binary | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprED47.tmp | xml | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RF1317f0.TMP | binary | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EM89UCVGE4U0MU1XGA1C.temp | binary | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | xml | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 576 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
43
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
576 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3984 | joker.exe | 86.127.110.136:8080 | — | RCS & RDS | RO | malicious |
576 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
576 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
576 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 86.127.110.136:8080 | — | RCS & RDS | RO | malicious |
— | — | 192.168.31.200:8080 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
Threats
5 ETPRO signatures available at the full report