| File name: | 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c |
| Full analysis: | https://app.any.run/tasks/9867ad6a-5112-421b-931f-5f3591d717e0 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | August 04, 2024, 08:48:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | D2733BF9C81DDF4F730C65FCE8E02629 |
| SHA1: | 139E56192C8AEE644355B21CFFC126C21DF9A9EB |
| SHA256: | 26B74954ED3E0E81B4F9304E3BAA149866320A10F5F6468883C9FA6358A75A6C |
| SSDEEP: | 24576:IuhM0wq9ZKk6k/p1MlvPfn8l6mylEbZSw:7M0wq9ZV6kUlv38l6mylEbZSw |
MALICIOUS
Drops the executable file immediately after the start
- 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe (PID: 6380)
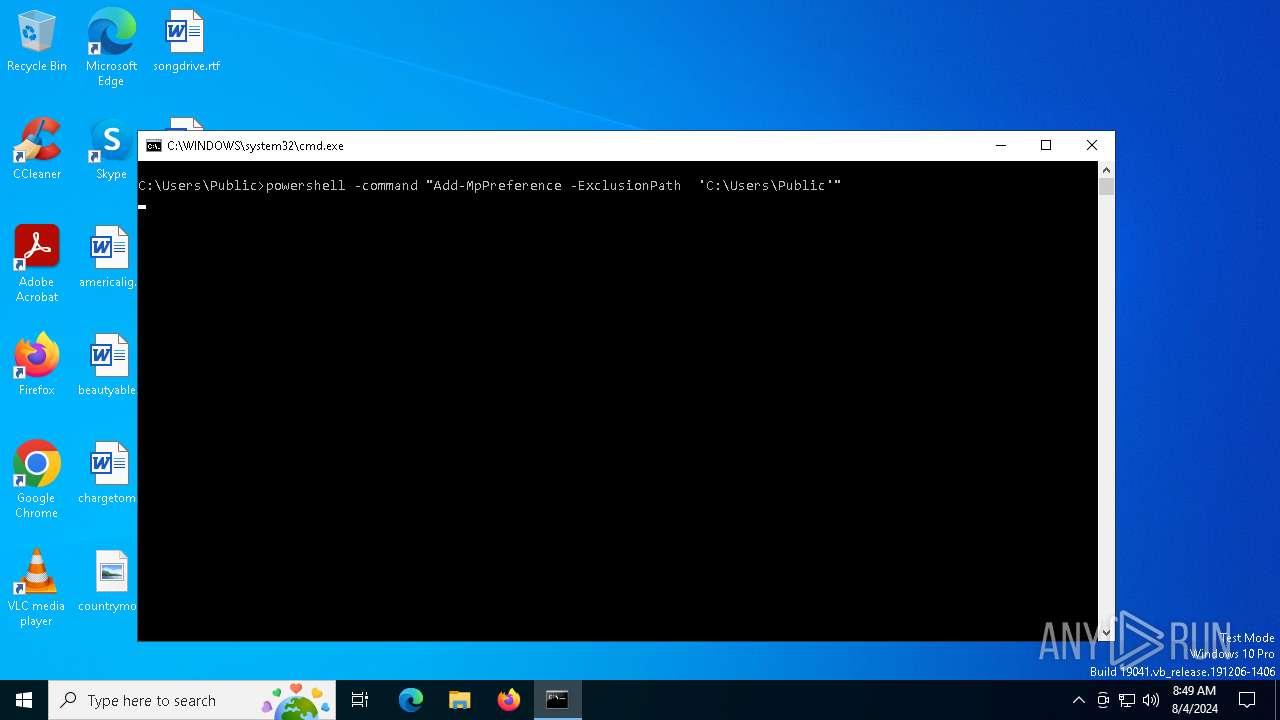
Adds extension to the Windows Defender exclusion list
- cmd.exe (PID: 6468)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 6468)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6468)
COBALTSTRIKE has been detected (YARA)
- WmiPrvSE.exe (PID: 6416)
SUSPICIOUS
Reads security settings of Internet Explorer
- 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe (PID: 6380)
- WmiPrvSE.exe (PID: 6416)
Reads the date of Windows installation
- 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe (PID: 6380)
Executing commands from a ".bat" file
- 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe (PID: 6380)
Starts CMD.EXE for commands execution
- 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe (PID: 6380)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6468)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 6468)
- certutil.exe (PID: 6336)
- WmiPrvSE.exe (PID: 6416)
- schtasks.exe (PID: 6368)
- powershell.exe (PID: 6860)
Script adds exclusion extension to Windows Defender
- cmd.exe (PID: 6468)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6468)
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 6468)
Executable content was dropped or overwritten
- certutil.exe (PID: 6336)
Connects to unusual port
- WmiPrvSE.exe (PID: 6416)
INFO
Reads the computer name
- 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe (PID: 6380)
- WmiPrvSE.exe (PID: 6416)
Checks supported languages
- 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe (PID: 6380)
- WmiPrvSE.exe (PID: 6416)
Process checks computer location settings
- 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe (PID: 6380)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 6860)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 6860)
Drops the executable file immediately after the start
- certutil.exe (PID: 6336)
Reads the machine GUID from the registry
- WmiPrvSE.exe (PID: 6416)
Checks proxy server information
- WmiPrvSE.exe (PID: 6416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
CobalStrike
(PID) Process(6416) WmiPrvSE.exe
C2 (1)45.76.192.215/load
BeaconTypeHTTPS
Port59611
SleepTime60000
MaxGetSize1048576
Jitter0
PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCCqQE9JgJFx+YokvbVGsISp1vU
xQ6ppPYh4YHfWDrRtBDqyhKNsGfjNpfJZi5SwIC1+bIdaMK6Xhi5gwNNh8Y5PzOm
SnWPDbpIsxAt304YhgS+8RLHKwaqgIsYuMpOkJTuRkt9Bdm8MOndSuqp+avBBQxD
xnF/gbN5ibD4gdwpWQIDAQAB
-----END PUBLIC KEY-----
DNS_strategyround-robin
DNS_strategy_rotate_seconds-1
DNS_strategy_fail_x-1
DNS_strategy_fail_seconds-1
SpawnTo00000000000000000000000000000000
Spawnto_x86%windir%\syswow64\rundll32.exe
Spawnto_x64%windir%\sysnative\rundll32.exe
CryptoScheme0
HttpGet_VerbGET
HttpPost_VerbPOST
HttpPostChunk0
Watermark987654321
bStageCleanupFalse
bCFGCautionFalse
UserAgentMozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; WOW64; Trident/6.0)
HttpPostUri/submit.php
HttpGet_Metadata
SessionId (2)base64
header: Cookie
HttpPost_Metadata
ConstHeaders (1)Content-Type: application/octet-stream
SessionId (1)parameter: id
Output (1)print
bUsesCookies0001
Proxy_BehaviorUse IE settings
tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
KillDate0-0-0
bProcInject_StartRWXTrue
bProcInject_UseRWXTrue
bProcInject_MinAllocSize0
ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_Stubae5afcfee8026674dc8f3b4f2da46c7f
ProcInject_AllocationMethodVirtualAllocEx
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:05:12 10:17:07+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.33 |
| CodeSize: | 288768 |
| InitializedDataSize: | 210944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32ee0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
143
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6336 | certutil -decode C:\Users\Public\NDTCN1.dat C:\Users\Public\WmiPrvSE.exe | C:\Windows\System32\certutil.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6368 | SchTasks /Create /SC DAILY /TN WmiPrvSE /TR "C:\Users\Public\WmiPrvSE.exe" /ST 19:00 /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6380 | "C:\Users\admin\AppData\Local\Temp\26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe" | C:\Users\admin\AppData\Local\Temp\26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6416 | C:\Users\Public\WmiPrvSE.exe | C:\Users\Public\WmiPrvSE.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
CobalStrike(PID) Process(6416) WmiPrvSE.exe C2 (1)45.76.192.215/load BeaconTypeHTTPS Port59611 SleepTime60000 MaxGetSize1048576 Jitter0 PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCCqQE9JgJFx+YokvbVGsISp1vU
xQ6ppPYh4YHfWDrRtBDqyhKNsGfjNpfJZi5SwIC1+bIdaMK6Xhi5gwNNh8Y5PzOm
SnWPDbpIsxAt304YhgS+8RLHKwaqgIsYuMpOkJTuRkt9Bdm8MOndSuqp+avBBQxD
xnF/gbN5ibD4gdwpWQIDAQAB
-----END PUBLIC KEY----- DNS_strategyround-robin DNS_strategy_rotate_seconds-1 DNS_strategy_fail_x-1 DNS_strategy_fail_seconds-1 SpawnTo00000000000000000000000000000000 Spawnto_x86%windir%\syswow64\rundll32.exe Spawnto_x64%windir%\sysnative\rundll32.exe CryptoScheme0 HttpGet_VerbGET HttpPost_VerbPOST HttpPostChunk0 Watermark987654321 bStageCleanupFalse bCFGCautionFalse UserAgentMozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; WOW64; Trident/6.0) HttpPostUri/submit.php HttpGet_Metadata SessionId (2)base64 header: Cookie HttpPost_Metadata ConstHeaders (1)Content-Type: application/octet-stream SessionId (1)parameter: id Output (1)print bUsesCookies0001 Proxy_BehaviorUse IE settings tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 KillDate0-0-0 bProcInject_StartRWXTrue bProcInject_UseRWXTrue bProcInject_MinAllocSize0 ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_Stubae5afcfee8026674dc8f3b4f2da46c7f ProcInject_AllocationMethodVirtualAllocEx | |||||||||||||||
| 6468 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\WmiPrvSE.bat" " | C:\Windows\System32\cmd.exe | — | 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6536 | powershell -command "Add-MpPreference -ExclusionPath 'C:\Users\Public'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6860 | powershell -command "Add-MpPreference -ExclusionExtension 'C:\Users\Public\WmiPrvSE.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 194
Read events
13 178
Write events
16
Delete events
0
Modification events
| (PID) Process: | (6380) 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6380) 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6380) 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6380) 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6416) WmiPrvSE.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6416) WmiPrvSE.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6416) WmiPrvSE.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6416) WmiPrvSE.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6380 | 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe | C:\Users\Public\NDTCN1.dat | text | |
MD5:B183EB98A872FBA5091122FF3F84B025 | SHA256:628DF0A54E9A5A18BBABDB2F33333E5F12898028132757A24A1EE5C6FD63FF67 | |||
| 6536 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:ACBF50B6473D9E967EDCD3AECF475AB5 | SHA256:04C249E6D2E6A33CCFEB5B3C5471C20BAAD24030BFCEA4CEAB4DA106FCA42351 | |||
| 6380 | 26b74954ed3e0e81b4f9304e3baa149866320a10f5f6468883c9fa6358a75a6c.exe | C:\Users\Public\WmiPrvSE.bat | text | |
MD5:F1944530E0E4C27AC00560AF1F92249B | SHA256:361DB3755D1CE2DB5FF0C28CEC3C5481CBE2ECAC0A45CC6617721DC375A4C7C7 | |||
| 6336 | certutil.exe | C:\Users\Public\WmiPrvSE.exe | executable | |
MD5:29FA5E4FD104FD12A870D2DD90E42B31 | SHA256:298EADA4723177FAC953AFC963A4BFFA56D7DBBA3D1BEA340E53953E736BCA80 | |||
| 6536 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_amc4ipkz.thu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6536 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vtmwwi0a.pyy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6860 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yk5i5e4a.f4e.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6860 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ylupddr4.x05.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
39
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7056 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7064 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4576 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1716 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4576 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 104.126.37.162:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |