| File name: | SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe |
| Full analysis: | https://app.any.run/tasks/9a0c6721-3edd-4ddd-bbf3-92be3cdbae81 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | June 21, 2025, 15:26:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | F1983D7900A62D5518182B1F91288DAD |
| SHA1: | 62AFE8435F4F01AD25BDC3D5D91CDA0CC2BFC2DD |
| SHA256: | 269D27FE9542455527B4C44460C2A9C291D233C5EC1BD82206A77F1D228BCABF |
| SSDEEP: | 98304:1iRrKhVGDnH37jhawBJnXb899rZnmXIVwwcihwzEwBOi1UVlRt6Cq+hf6y3PRFR2:VrEB |
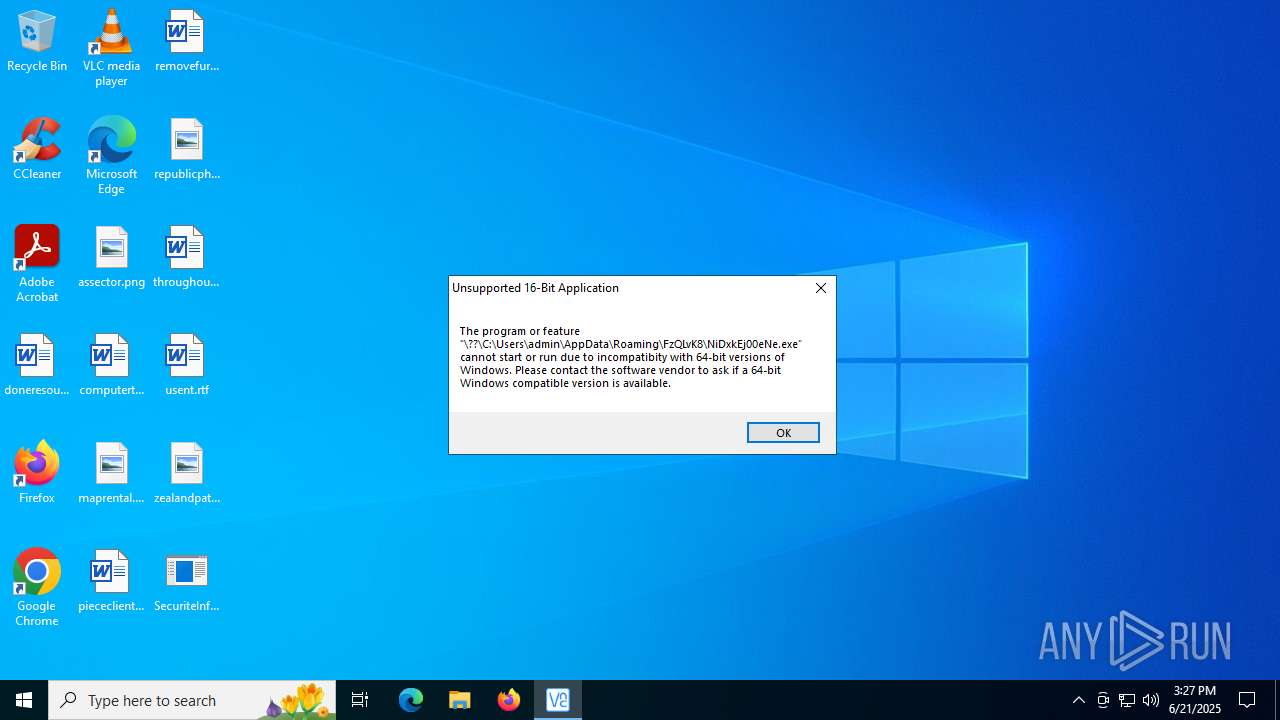
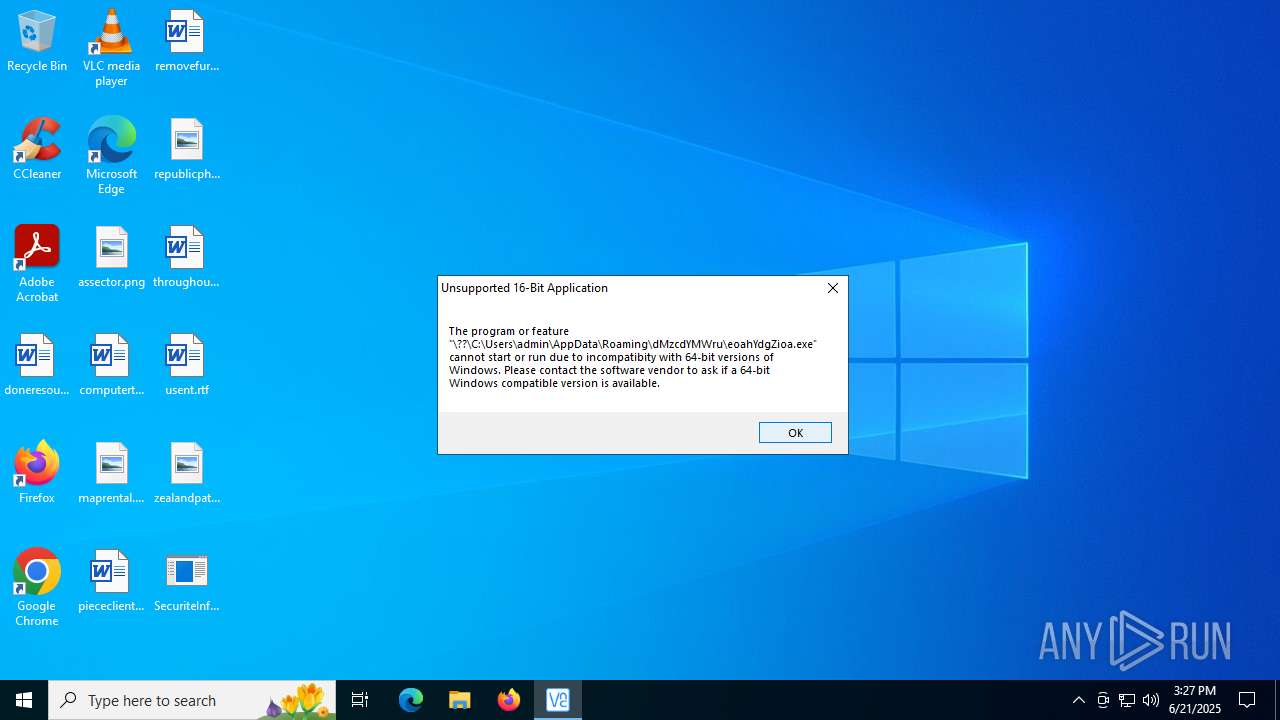
MALICIOUS
Executing a file with an untrusted certificate
- SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe (PID: 6584)
- svchost015.exe (PID: 2072)
- rmz0uMvwO5N.exe (PID: 316)
- LKw8iT8AxA.exe (PID: 7980)
- LKw8iT8AxA.exe (PID: 8036)
- blOahSM.exe (PID: 8024)
- blOahSM.exe (PID: 2524)
- EG11t89.exe (PID: 7008)
GCLEANER has been detected (YARA)
- svchost015.exe (PID: 2072)
GCLEANER has been detected (SURICATA)
- svchost015.exe (PID: 2072)
LUMMA mutex has been found
- 9RSErgNaXK.exe (PID: 2552)
- Oc.com (PID: 2140)
Registers / Runs the DLL via REGSVR32.EXE
- LKw8iT8AxA.tmp (PID: 8064)
LUMMA has been detected (YARA)
- 9RSErgNaXK.exe (PID: 2552)
Actions looks like stealing of personal data
- 9RSErgNaXK.exe (PID: 2552)
- Oc.com (PID: 2140)
- MSBuild.exe (PID: 4684)
AutoIt loader has been detected (YARA)
- Oc.com (PID: 2140)
Steals credentials from Web Browsers
- 9RSErgNaXK.exe (PID: 2552)
- Oc.com (PID: 2140)
- MSBuild.exe (PID: 4684)
GENERIC has been found (auto)
- svchost015.exe (PID: 2072)
AMADEY mutex has been found
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- ramez.exe (PID: 7080)
- ramez.exe (PID: 7868)
- amnew.exe (PID: 7156)
- varen.exe (PID: 4944)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 7080)
Connects to the CnC server
- ramez.exe (PID: 7080)
VIDAR mutex has been found
- MSBuild.exe (PID: 4684)
LCLIPPER mutex has been found
- b7ebf46823.exe (PID: 8276)
- GoogleChrome.exe (PID: 2064)
- GoogleChrome.exe (PID: 1752)
Changes the autorun value in the registry
- b7ebf46823.exe (PID: 8276)
Changes powershell execution policy
- wscript.exe (PID: 7944)
- powershell.exe (PID: 8544)
Run PowerShell with an invisible window
- powershell.exe (PID: 8544)
- powershell.exe (PID: 7472)
STEGOCAMPAIGN has been detected
- powershell.exe (PID: 7472)
AMADEY has been found (auto)
- ramez.exe (PID: 7080)
- amnew.exe (PID: 7156)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe (PID: 6584)
- svchost015.exe (PID: 2072)
- rmz0uMvwO5N.exe (PID: 316)
- Oc.com (PID: 2140)
Executable content was dropped or overwritten
- SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe (PID: 6584)
- oQiiLC0J1qdF.tmp (PID: 4460)
- svchost015.exe (PID: 2072)
- oQiiLC0J1qdF.exe (PID: 5504)
- openfilesviewer.exe (PID: 1180)
- LKw8iT8AxA.exe (PID: 7980)
- LKw8iT8AxA.tmp (PID: 7996)
- LKw8iT8AxA.exe (PID: 8036)
- LKw8iT8AxA.tmp (PID: 8064)
- 9RSErgNaXK.exe (PID: 2552)
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- ramez.exe (PID: 7080)
- b7ebf46823.exe (PID: 8276)
- csc.exe (PID: 5140)
- blOahSM.exe (PID: 8024)
- lab.exe (PID: 5552)
- lab.exe (PID: 8168)
- amnew.exe (PID: 7156)
Reads security settings of Internet Explorer
- svchost015.exe (PID: 2072)
- openfilesviewer.exe (PID: 1180)
- rmz0uMvwO5N.exe (PID: 316)
- LKw8iT8AxA.tmp (PID: 7996)
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- ramez.exe (PID: 7080)
- MSBuild.exe (PID: 4684)
- b7ebf46823.exe (PID: 8276)
- GoogleChrome.exe (PID: 2064)
- blOahSM.exe (PID: 2524)
- AutoIt3_x64.exe (PID: 4664)
- blOahSM.exe (PID: 8024)
Potential Corporate Privacy Violation
- svchost015.exe (PID: 2072)
- 9RSErgNaXK.exe (PID: 2552)
- ramez.exe (PID: 7080)
Connects to the server without a host name
- svchost015.exe (PID: 2072)
- 9RSErgNaXK.exe (PID: 2552)
- ramez.exe (PID: 7080)
Process drops legitimate windows executable
- oQiiLC0J1qdF.tmp (PID: 4460)
- ramez.exe (PID: 7080)
- blOahSM.exe (PID: 8024)
- lab.exe (PID: 5552)
- lab.exe (PID: 8168)
Starts POWERSHELL.EXE for commands execution
- openfilesviewer.exe (PID: 1180)
- regsvr32.exe (PID: 8100)
- MSBuild.exe (PID: 4684)
- wscript.exe (PID: 7944)
- powershell.exe (PID: 8544)
Reads the Windows owner or organization settings
- oQiiLC0J1qdF.tmp (PID: 4460)
- LKw8iT8AxA.tmp (PID: 8064)
- LKw8iT8AxA.tmp (PID: 7996)
The process drops C-runtime libraries
- oQiiLC0J1qdF.tmp (PID: 4460)
- blOahSM.exe (PID: 8024)
- lab.exe (PID: 8168)
- lab.exe (PID: 5552)
Starts CMD.EXE for commands execution
- rmz0uMvwO5N.exe (PID: 316)
- b7ebf46823.exe (PID: 8276)
- cmd.exe (PID: 1688)
- blOahSM.exe (PID: 8024)
- lab.exe (PID: 5552)
- 4TQHprw.exe (PID: 8476)
Get information on the list of running processes
- cmd.exe (PID: 1700)
- powershell.exe (PID: 8544)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1700)
Starts application with an unusual extension
- cmd.exe (PID: 1700)
The executable file from the user directory is run by the CMD process
- Oc.com (PID: 2140)
- GoogleChrome.exe (PID: 2064)
- Python.exe (PID: 3924)
Starts the AutoIt3 executable file
- cmd.exe (PID: 1700)
- blOahSM.exe (PID: 8024)
Reads the BIOS version
- 9RSErgNaXK.exe (PID: 2552)
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- ramez.exe (PID: 7080)
- b7ebf46823.exe (PID: 8276)
- GoogleChrome.exe (PID: 2064)
- GoogleChrome.exe (PID: 1752)
- ramez.exe (PID: 7868)
Executing commands from a ".bat" file
- rmz0uMvwO5N.exe (PID: 316)
- lab.exe (PID: 5552)
The process hide an interactive prompt from the user
- regsvr32.exe (PID: 8100)
- MSBuild.exe (PID: 4684)
The process bypasses the loading of PowerShell profile settings
- regsvr32.exe (PID: 8100)
- MSBuild.exe (PID: 4684)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Oc.com (PID: 2140)
- MSBuild.exe (PID: 4684)
- GoogleChrome.exe (PID: 2064)
Detected use of alternative data streams (AltDS)
- regsvr32.exe (PID: 8100)
Connects to SMTP port
- regsvr32.exe (PID: 8100)
Process requests binary or script from the Internet
- 9RSErgNaXK.exe (PID: 2552)
- ramez.exe (PID: 7080)
Starts itself from another location
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- amnew.exe (PID: 7156)
Contacting a server suspected of hosting an CnC
- ramez.exe (PID: 7080)
Searches for installed software
- 9RSErgNaXK.exe (PID: 2552)
- MSBuild.exe (PID: 4684)
- Oc.com (PID: 2140)
Starts a Microsoft application from unusual location
- v999f8.exe (PID: 3720)
- 4TQHprw.exe (PID: 8476)
Checks for external IP
- svchost.exe (PID: 2200)
- 09NlD7c.exe (PID: 9132)
- b7ebf46823.exe (PID: 8276)
- GoogleChrome.exe (PID: 2064)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 1100)
Application launched itself
- cmd.exe (PID: 1688)
- blOahSM.exe (PID: 2524)
- lab.exe (PID: 8168)
- powershell.exe (PID: 8544)
Base64-obfuscated command line is found
- MSBuild.exe (PID: 4684)
The process executes via Task Scheduler
- regsvr32.exe (PID: 8376)
- ramez.exe (PID: 7868)
Reads the date of Windows installation
- jzQILRF.exe (PID: 1164)
- blOahSM.exe (PID: 2524)
- blOahSM.exe (PID: 8024)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5496)
- powershell.exe (PID: 8544)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5496)
CSC.EXE is used to compile C# code
- csc.exe (PID: 5140)
BASE64 encoded PowerShell command has been detected
- MSBuild.exe (PID: 4684)
Executing commands from ".cmd" file
- blOahSM.exe (PID: 8024)
Process drops python dynamic module
- lab.exe (PID: 8168)
The process executes VB scripts
- cmd.exe (PID: 1356)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7944)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7944)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 7944)
Found IP address in command line
- powershell.exe (PID: 7472)
Probably download files using WebClient
- powershell.exe (PID: 8544)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7472)
INFO
Compiled with Borland Delphi (YARA)
- SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe (PID: 6584)
- oQiiLC0J1qdF.tmp (PID: 4460)
The sample compiled with chinese language support
- SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe (PID: 6584)
Checks supported languages
- SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe (PID: 6584)
- svchost015.exe (PID: 2072)
- oQiiLC0J1qdF.exe (PID: 5504)
- oQiiLC0J1qdF.tmp (PID: 4460)
- openfilesviewer.exe (PID: 1180)
- rmz0uMvwO5N.exe (PID: 316)
- OpenFilesViewer.exe (PID: 3976)
- extrac32.exe (PID: 1816)
- 9RSErgNaXK.exe (PID: 2552)
- Oc.com (PID: 2140)
- LKw8iT8AxA.tmp (PID: 7996)
- LKw8iT8AxA.tmp (PID: 8064)
- LKw8iT8AxA.exe (PID: 8036)
- ramez.exe (PID: 7080)
- LKw8iT8AxA.exe (PID: 7980)
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- 09NlD7c.exe (PID: 9132)
- MSBuild.exe (PID: 4684)
- b7ebf46823.exe (PID: 8276)
- v999f8.exe (PID: 3720)
- GoogleChrome.exe (PID: 2064)
- GoogleChrome.exe (PID: 1752)
- jzQILRF.exe (PID: 1164)
- csc.exe (PID: 5140)
- cvtres.exe (PID: 8388)
- blOahSM.exe (PID: 8024)
- blOahSM.exe (PID: 2524)
- AutoIt3_x64.exe (PID: 4664)
- ramez.exe (PID: 7868)
- EG11t89.exe (PID: 7008)
- lab.exe (PID: 8168)
- Python.exe (PID: 3924)
- lab.exe (PID: 5552)
- 4TQHprw.exe (PID: 8476)
- amnew.exe (PID: 7156)
Create files in a temporary directory
- SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe (PID: 6584)
- oQiiLC0J1qdF.exe (PID: 5504)
- oQiiLC0J1qdF.tmp (PID: 4460)
- rmz0uMvwO5N.exe (PID: 316)
- extrac32.exe (PID: 1816)
- LKw8iT8AxA.exe (PID: 7980)
- LKw8iT8AxA.tmp (PID: 8064)
- LKw8iT8AxA.tmp (PID: 7996)
- LKw8iT8AxA.exe (PID: 8036)
- 9RSErgNaXK.exe (PID: 2552)
- svchost015.exe (PID: 2072)
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- ramez.exe (PID: 7080)
- powershell.exe (PID: 5496)
- MSBuild.exe (PID: 4684)
- csc.exe (PID: 5140)
- cvtres.exe (PID: 8388)
- blOahSM.exe (PID: 8024)
- AutoIt3_x64.exe (PID: 4664)
- powershell.exe (PID: 6236)
- lab.exe (PID: 8168)
- lab.exe (PID: 5552)
- powershell.exe (PID: 8380)
- 4TQHprw.exe (PID: 8476)
- powershell.exe (PID: 7472)
The sample compiled with english language support
- SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe (PID: 6584)
- oQiiLC0J1qdF.tmp (PID: 4460)
- openfilesviewer.exe (PID: 1180)
- ramez.exe (PID: 7080)
- blOahSM.exe (PID: 8024)
- lab.exe (PID: 8168)
- lab.exe (PID: 5552)
Reads the computer name
- svchost015.exe (PID: 2072)
- oQiiLC0J1qdF.tmp (PID: 4460)
- openfilesviewer.exe (PID: 1180)
- rmz0uMvwO5N.exe (PID: 316)
- OpenFilesViewer.exe (PID: 3976)
- extrac32.exe (PID: 1816)
- Oc.com (PID: 2140)
- LKw8iT8AxA.tmp (PID: 7996)
- 9RSErgNaXK.exe (PID: 2552)
- LKw8iT8AxA.tmp (PID: 8064)
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- ramez.exe (PID: 7080)
- 09NlD7c.exe (PID: 9132)
- MSBuild.exe (PID: 4684)
- b7ebf46823.exe (PID: 8276)
- GoogleChrome.exe (PID: 2064)
- blOahSM.exe (PID: 2524)
- blOahSM.exe (PID: 8024)
- AutoIt3_x64.exe (PID: 4664)
- EG11t89.exe (PID: 7008)
- 4TQHprw.exe (PID: 8476)
- jzQILRF.exe (PID: 1164)
Checks proxy server information
- svchost015.exe (PID: 2072)
- ramez.exe (PID: 7080)
- slui.exe (PID: 6268)
- 09NlD7c.exe (PID: 9132)
- MSBuild.exe (PID: 4684)
- b7ebf46823.exe (PID: 8276)
- GoogleChrome.exe (PID: 2064)
- jzQILRF.exe (PID: 1164)
Reads the machine GUID from the registry
- svchost015.exe (PID: 2072)
- 9RSErgNaXK.exe (PID: 2552)
- Oc.com (PID: 2140)
- 09NlD7c.exe (PID: 9132)
- MSBuild.exe (PID: 4684)
- jzQILRF.exe (PID: 1164)
- csc.exe (PID: 5140)
- AutoIt3_x64.exe (PID: 4664)
- EG11t89.exe (PID: 7008)
- ramez.exe (PID: 7080)
- lab.exe (PID: 5552)
- GoogleChrome.exe (PID: 2064)
Reads the software policy settings
- svchost015.exe (PID: 2072)
- 9RSErgNaXK.exe (PID: 2552)
- Oc.com (PID: 2140)
- slui.exe (PID: 6268)
- 09NlD7c.exe (PID: 9132)
- MSBuild.exe (PID: 4684)
- GoogleChrome.exe (PID: 2064)
- powershell.exe (PID: 5496)
- jzQILRF.exe (PID: 1164)
- ramez.exe (PID: 7080)
- powershell.exe (PID: 6236)
- powershell.exe (PID: 8380)
- powershell.exe (PID: 7472)
Creates files or folders in the user directory
- svchost015.exe (PID: 2072)
- oQiiLC0J1qdF.tmp (PID: 4460)
- LKw8iT8AxA.tmp (PID: 8064)
- ramez.exe (PID: 7080)
- MSBuild.exe (PID: 4684)
- b7ebf46823.exe (PID: 8276)
- GoogleChrome.exe (PID: 2064)
Creates a software uninstall entry
- oQiiLC0J1qdF.tmp (PID: 4460)
Creates files in the program directory
- openfilesviewer.exe (PID: 1180)
- MSBuild.exe (PID: 4684)
Process checks computer location settings
- openfilesviewer.exe (PID: 1180)
- rmz0uMvwO5N.exe (PID: 316)
- svchost015.exe (PID: 2072)
- LKw8iT8AxA.tmp (PID: 7996)
- W69TAF8W7IIQ9WHRRM3ZBNQKQ8GN.exe (PID: 3972)
- ramez.exe (PID: 7080)
- blOahSM.exe (PID: 2524)
- blOahSM.exe (PID: 8024)
Changes the registry key values via Powershell
- openfilesviewer.exe (PID: 1180)
Manual execution by a user
- OpenFilesViewer.exe (PID: 3976)
- GoogleChrome.exe (PID: 1752)
Reads mouse settings
- Oc.com (PID: 2140)
- AutoIt3_x64.exe (PID: 4664)
Application launched itself
- chrome.exe (PID: 6004)
- chrome.exe (PID: 7260)
- chrome.exe (PID: 6176)
- chrome.exe (PID: 7680)
- msedge.exe (PID: 7804)
- msedge.exe (PID: 7440)
- msedge.exe (PID: 7460)
- chrome.exe (PID: 5768)
- chrome.exe (PID: 7396)
- msedge.exe (PID: 424)
- msedge.exe (PID: 8308)
- msedge.exe (PID: 8324)
- chrome.exe (PID: 7660)
- chrome.exe (PID: 8480)
- msedge.exe (PID: 8276)
- msedge.exe (PID: 8304)
- msedge.exe (PID: 3620)
- msedge.exe (PID: 7804)
- msedge.exe (PID: 6004)
- msedge.exe (PID: 7224)
- msedge.exe (PID: 6688)
- msedge.exe (PID: 2288)
- chrome.exe (PID: 8676)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 7480)
Detects InnoSetup installer (YARA)
- oQiiLC0J1qdF.exe (PID: 5504)
- oQiiLC0J1qdF.tmp (PID: 4460)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8140)
- powershell.exe (PID: 8016)
Themida protector has been detected
- 9RSErgNaXK.exe (PID: 2552)
Reads Environment values
- MSBuild.exe (PID: 4684)
- AutoIt3_x64.exe (PID: 4664)
Reads product name
- MSBuild.exe (PID: 4684)
Reads CPU info
- MSBuild.exe (PID: 4684)
Launching a file from a Registry key
- b7ebf46823.exe (PID: 8276)
Reads security settings of Internet Explorer
- powershell.exe (PID: 5496)
- powershell.exe (PID: 6236)
- powershell.exe (PID: 8380)
- powershell.exe (PID: 7472)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6236)
- powershell.exe (PID: 8380)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6236)
- powershell.exe (PID: 8380)
Python executable
- Python.exe (PID: 3924)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 8544)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8544)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 8544)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(2552) 9RSErgNaXK.exe
C2 (9)ropyi.xyz/zadf
skjgx.xyz/riuw
gewgb.xyz/axgh
baviip.xyz/twiw
equidn.xyz/xapq
spjeo.xyz/axka
firddy.xyz/yhbc
shaeb.xyz/ikxz
trqqe.xyz/xudu
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 494080 |
| InitializedDataSize: | 2997248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79814 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.7.0.1220 |
| ProductVersionNumber: | 3.7.0.1220 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | Fl as hGet3 |
| CompanyName: | Tren d Media Corporation Limited |
| FileDescription: | FlashGet3 |
| FileVersion: | 3, 7, 0, 1220 |
Total processes
387
Monitored processes
249
Malicious processes
30
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Users\admin\AppData\Roaming\Sp1qRrRbx\rmz0uMvwO5N.exe" | C:\Users\admin\AppData\Roaming\Sp1qRrRbx\rmz0uMvwO5N.exe | — | svchost015.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=4600,i,12356675327710538293,3263609604062285657,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | 9RSErgNaXK.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3720,i,17641693668202086582,1755806836017531433,262144 --variations-seed-version --mojo-platform-channel-handle=3776 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3484,i,4379786499156593958,2267130909063623904,262144 --variations-seed-version --mojo-platform-channel-handle=3504 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 856 | findstr /V "CLASSIFICATION" Stretch | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | cmd /C "ping localhost -n 1 && start C:\Users\admin\AppData\Local\GoogleChrome.exe" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Users\admin\AppData\Local\Temp\10457720101\jzQILRF.exe" | C:\Users\admin\AppData\Local\Temp\10457720101\jzQILRF.exe | ramez.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\openfilesviewer.exe" -i | C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\openfilesviewer.exe | oQiiLC0J1qdF.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Open Files Viewer Version: 1.16.0.471 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x228,0x22c,0x230,0x204,0x234,0x7ffc44cafff8,0x7ffc44cb0004,0x7ffc44cb0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
125 632
Read events
125 466
Write events
162
Delete events
4
Modification events
| (PID) Process: | (2072) svchost015.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2072) svchost015.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2072) svchost015.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4460) oQiiLC0J1qdF.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1 (a) | |||
| (PID) Process: | (4460) oQiiLC0J1qdF.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471 | |||
| (PID) Process: | (4460) oQiiLC0J1qdF.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\ | |||
| (PID) Process: | (4460) oQiiLC0J1qdF.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (4460) oQiiLC0J1qdF.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (4460) oQiiLC0J1qdF.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: English | |||
| (PID) Process: | (4460) oQiiLC0J1qdF.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | DisplayName |
Value: Open Files Viewer 1.16.0.471 | |||
Executable files
131
Suspicious files
332
Text files
490
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6584 | SecuriteInfo.com.Win32.MalwareX-gen.15343.21443.exe | C:\Users\admin\AppData\Local\Temp\svchost015.exe | executable | |
MD5:CEEAE1523C3864B719E820B75BF728AA | SHA256:4E04E2FB20A9C6846B5D693EA67098214F77737F4F1F3DF5F0C78594650E7F71 | |||
| 2072 | svchost015.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\text[1] | text | |
MD5:5E847B1CC501E8A09997640FED7DB52F | SHA256:C06903CB5A25E63794907092B488A8580074C872272A9FC51CEF5E76EEECF7A2 | |||
| 4460 | oQiiLC0J1qdF.tmp | C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\icuin51.dll | executable | |
MD5:A7F201C0B9AC05E950ECC55D4403EC16 | SHA256:173092C4E256958B100683A6AB2CE0D1C9895EC63F222198F9DE485E61C728CA | |||
| 2072 | svchost015.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\fuckingdllENCR[1].dll | binary | |
MD5:4BC1EF6688690AF3DD8D3D70906A9F98 | SHA256:7703A6B77C0B0935F5900A2D846CFA3AB59B46D03A1A0844F6BCB5CF9496B2FE | |||
| 2072 | svchost015.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\success[1].htm | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 5504 | oQiiLC0J1qdF.exe | C:\Users\admin\AppData\Local\Temp\is-GTBTN.tmp\oQiiLC0J1qdF.tmp | executable | |
MD5:85F74E5470B61C351EB351EEB1DB465F | SHA256:30EA63950BF5FA275F3A2FBD75B46467272E50C3D715944C372DE1E4D6C7678A | |||
| 2072 | svchost015.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\info[1].htm | text | |
MD5:FE9B08252F126DDFCB87FB82F9CC7677 | SHA256:E63E7EBE4C2DB7E61FFC71AF0675E870BCDE0A9D8916E5B3BE0CB252478030BF | |||
| 2072 | svchost015.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\ONE[1].file | executable | |
MD5:49642CEE0AD99E4882A6F45C478C55B7 | SHA256:CB7DEE0F26CC30B13E5775877D570FCD4CA2E4F1A89614CC12031D6070B78473 | |||
| 4460 | oQiiLC0J1qdF.tmp | C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\uninstall\unins000.exe | executable | |
MD5:25111058A1C6F22EB16782728FDCEEDE | SHA256:DFD545251DCB862882645149F741A619754804244B8F91344596795D78086DBC | |||
| 4460 | oQiiLC0J1qdF.tmp | C:\Users\admin\AppData\Local\Temp\is-DI44T.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
366
TCP/UDP connections
452
DNS requests
354
Threats
73
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2028 | RUXIMICS.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 216.58.212.129:443 | https://drive.usercontent.google.com/download?id=1YBVIDkZgygNfUU2rbJXXCYdrzay5rMdY&export=download&authuser=0&confirm=t | unknown | text | 14 b | whitelisted |
2072 | svchost015.exe | GET | 200 | 185.156.72.196:80 | http://185.156.72.196/success?substr=mixtwo&s=three&sub=none | unknown | — | — | malicious |
2072 | svchost015.exe | GET | 200 | 185.156.72.196:80 | http://185.156.72.196/info | unknown | — | — | malicious |
2072 | svchost015.exe | GET | 200 | 185.156.72.196:80 | http://185.156.72.196/update | unknown | — | — | malicious |
2072 | svchost015.exe | GET | 200 | 185.156.72.196:80 | http://185.156.72.196/service | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2028 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2028 | RUXIMICS.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
equidn.xyz |
| unknown |
QpADyRlQzssATcTYpEG.QpADyRlQzssATcTYpEG |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2072 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
2072 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
2072 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
2072 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
2072 | svchost015.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
2072 | svchost015.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2072 | svchost015.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2072 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
2072 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
2072 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
Process | Message |
|---|---|
9RSErgNaXK.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|