| File name: | quotes request.zip |
| Full analysis: | https://app.any.run/tasks/e4cf79e3-23fc-45d7-9137-7959cf5b5cff |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 20, 2020, 10:11:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
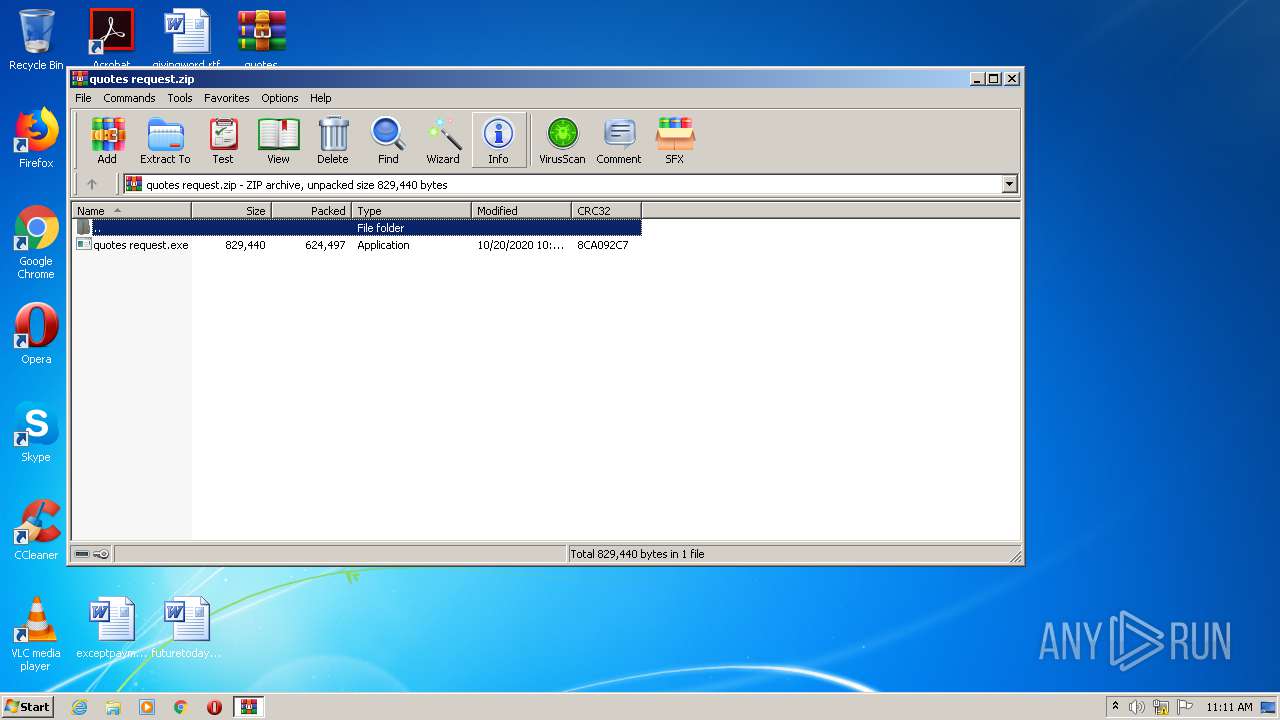
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B1486BAC2232052CD2E5EF26B7107D99 |
| SHA1: | 68D902726B7C49D44F614686D14F319297E9BF6B |
| SHA256: | 26991259E901AC65CEBE23EFC45F095B11595C8A10C160F04B949421D6E4E217 |
| SSDEEP: | 12288:lXzbdTz5nYpxdDzk/oSVw3QZ1TeLEaBCNRfW/a6SI2BIv8ugDQdphE:lDBTz8xNk/oSVHuzB8xoa6SICugDKpG |
MALICIOUS
Application was dropped or rewritten from another process
- quotes request.exe (PID: 3408)
- quotes request.exe (PID: 3544)
- quotes request.exe (PID: 2520)
- quotes request.exe (PID: 2192)
- quotes request.exe (PID: 3772)
- quotes request.exe (PID: 3380)
FORMBOOK was detected
- explorer.exe (PID: 392)
Connects to CnC server
- explorer.exe (PID: 392)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 392)
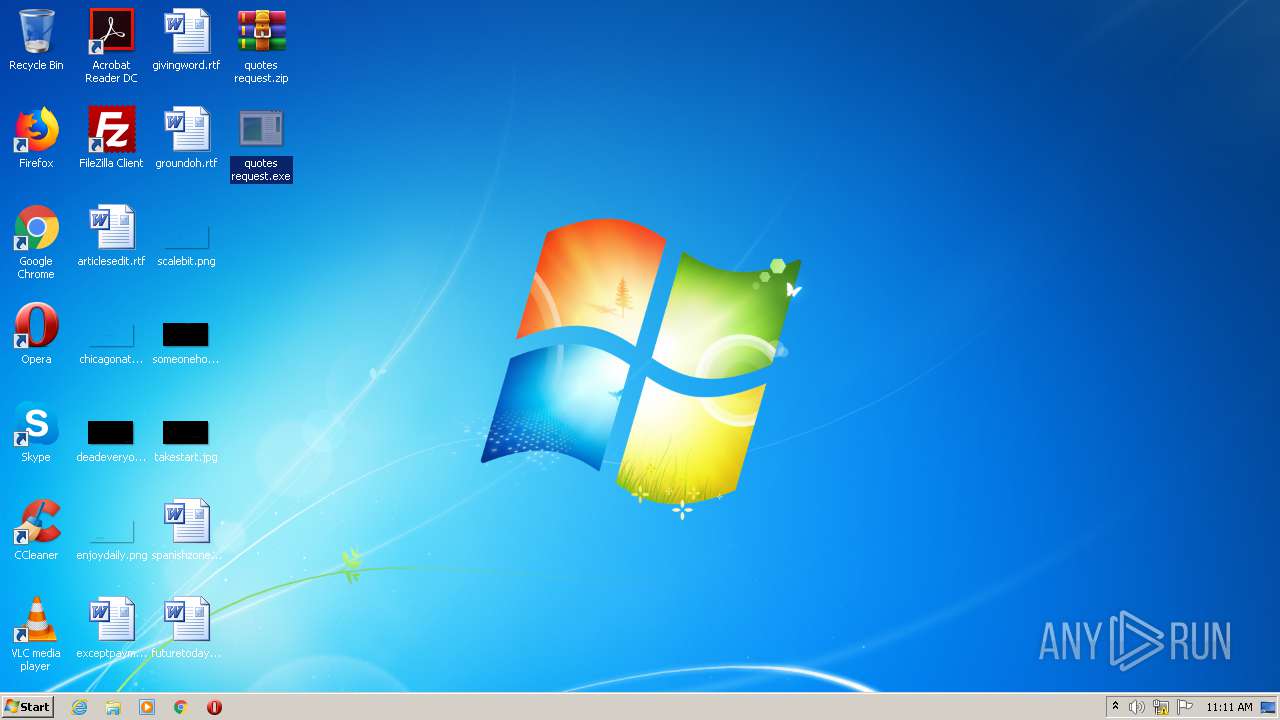
Executable content was dropped or overwritten
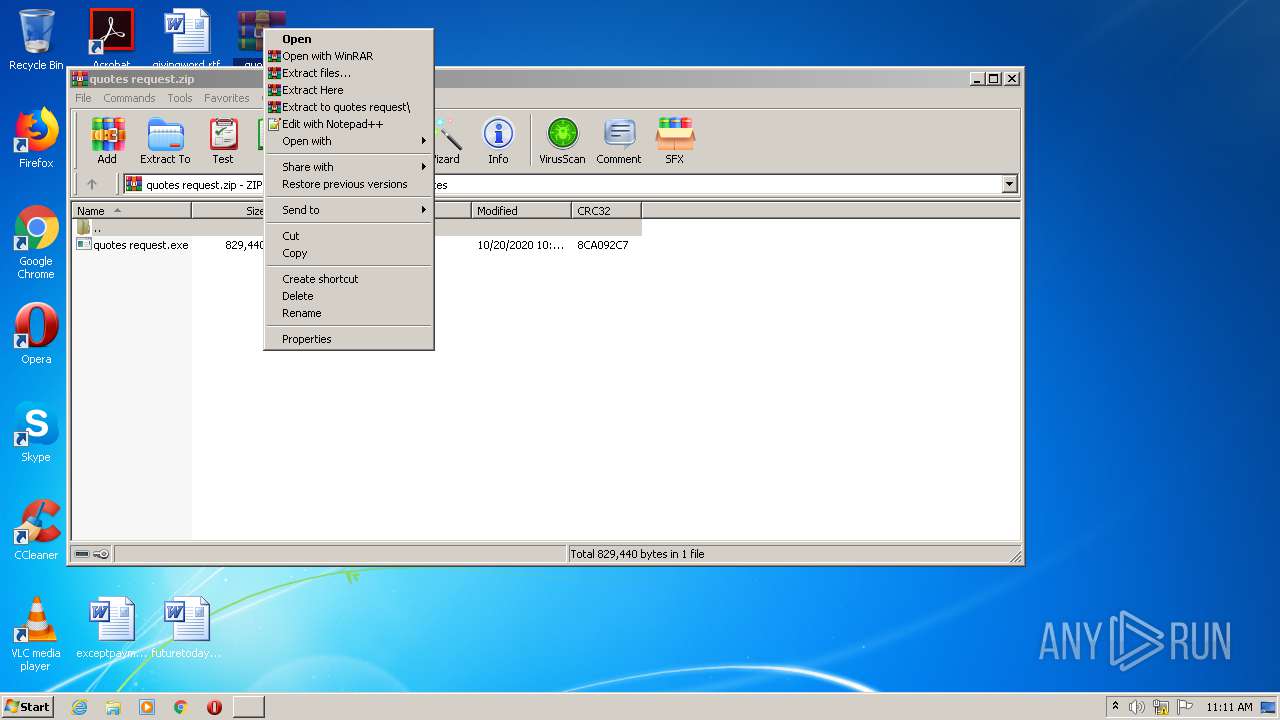
- WinRAR.exe (PID: 2772)
Application launched itself
- quotes request.exe (PID: 3408)
- quotes request.exe (PID: 3544)
- quotes request.exe (PID: 2520)
Starts CMD.EXE for commands execution
- audiodg.exe (PID: 2792)
Reads Internet Cache Settings
- audiodg.exe (PID: 2792)
INFO
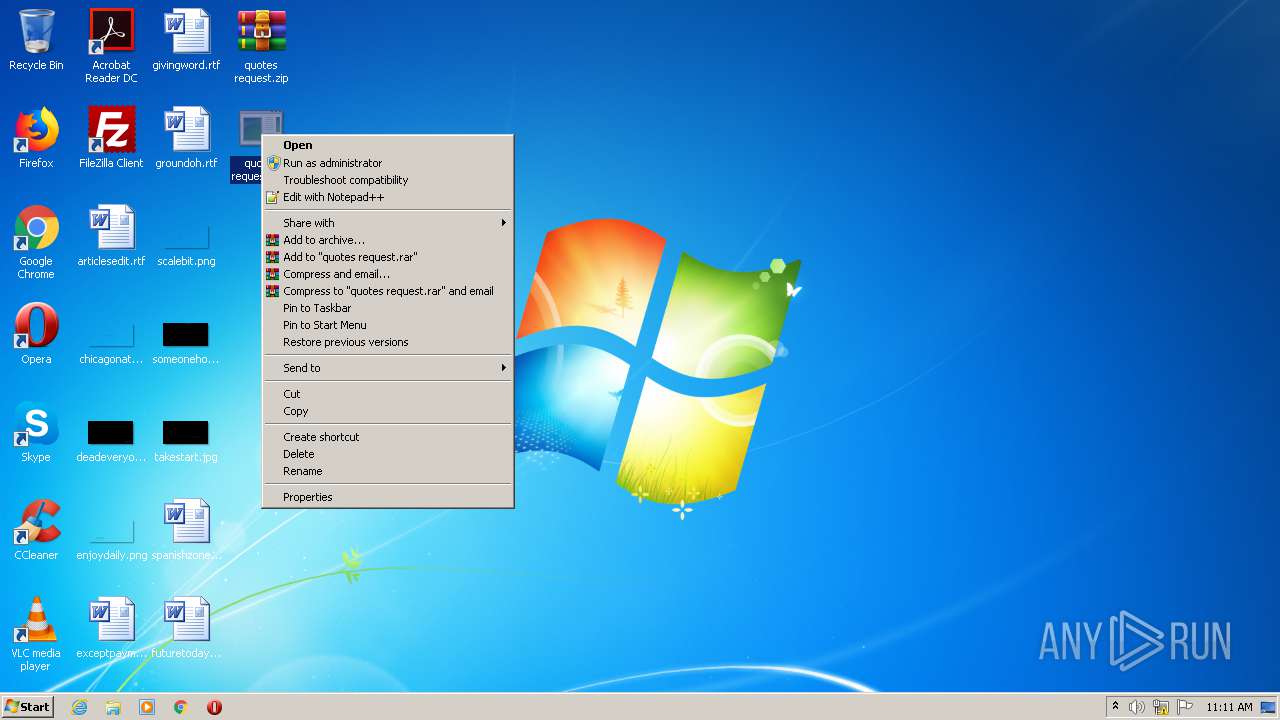
Manual execution by user
- WinRAR.exe (PID: 2772)
- quotes request.exe (PID: 3408)
- quotes request.exe (PID: 3544)
- quotes request.exe (PID: 2520)
- audiodg.exe (PID: 2792)
- services.exe (PID: 1084)
- chkdsk.exe (PID: 4032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:20 16:12:08 |
| ZipCRC: | 0x8ca092c7 |
| ZipCompressedSize: | 624497 |
| ZipUncompressedSize: | 829440 |
| ZipFileName: | quotes request.exe |
Total processes
52
Monitored processes
13
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | "C:\Windows\System32\services.exe" | C:\Windows\System32\services.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | /c del "C:\Users\admin\Desktop\quotes request.exe" | C:\Windows\System32\cmd.exe | — | audiodg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\Desktop\quotes request.exe" | C:\Users\admin\Desktop\quotes request.exe | — | quotes request.exe | |||||||||||
User: admin Company: AsIaNHaWk™ Creations Integrity Level: MEDIUM Description: PAYROLL MANAGEMENT SOFTWARE Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\quotes request.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\Desktop\quotes request.exe" | C:\Users\admin\Desktop\quotes request.exe | — | explorer.exe | |||||||||||
User: admin Company: AsIaNHaWk™ Creations Integrity Level: MEDIUM Description: PAYROLL MANAGEMENT SOFTWARE Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\quotes request.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2792 | "C:\Windows\System32\audiodg.exe" | C:\Windows\System32\audiodg.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Audio Device Graph Isolation Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | "C:\Users\admin\Desktop\quotes request.exe" | C:\Users\admin\Desktop\quotes request.exe | — | quotes request.exe | |||||||||||
User: admin Company: AsIaNHaWk™ Creations Integrity Level: MEDIUM Description: PAYROLL MANAGEMENT SOFTWARE Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 3408 | "C:\Users\admin\Desktop\quotes request.exe" | C:\Users\admin\Desktop\quotes request.exe | — | explorer.exe | |||||||||||
User: admin Company: AsIaNHaWk™ Creations Integrity Level: MEDIUM Description: PAYROLL MANAGEMENT SOFTWARE Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
2 302
Read events
2 205
Write events
97
Delete events
0
Modification events
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {B41DB860-8EE4-11D2-9906-E49FADC173CA} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000AA58F564C9A6D601 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs |
| Operation: | write | Name: | 11 |
Value: 710075006F00740065007300200072006500710075006500730074002E007A00690070000000800032000000000000000000000071756F74657320726571756573742E7A69702E6C6E6B00005A0008000400EFBE00000000000000002A00000000000000000000000000000000000000000000000000710075006F00740065007300200072006500710075006500730074002E007A00690070002E006C006E006B00000026000000 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs\.zip |
| Operation: | write | Name: | 0 |
Value: 710075006F00740065007300200072006500710075006500730074002E007A00690070000000800032000000000000000000000071756F74657320726571756573742E7A69702E6C6E6B00005A0008000400EFBE00000000000000002A00000000000000000000000000000000000000000000000000710075006F00740065007300200072006500710075006500730074002E007A00690070002E006C006E006B00000026000000 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs\.zip |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 392 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\quotes request.zip.lnk | lnk | |
MD5:— | SHA256:— | |||
| 392 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 392 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2772 | WinRAR.exe | C:\Users\admin\Desktop\quotes request.exe | executable | |
MD5:— | SHA256:— | |||
| 2792 | audiodg.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\z0po[1].htm | html | |
MD5:3EA1C8D079B38532A6E01A96216BA5E2 | SHA256:87A9323AC85CE28867D5D7CE590C8F29B8D1A999961FCA71BB33ADEF48683691 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
13
DNS requests
12
Threats
40
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
392 | explorer.exe | GET | — | 121.254.178.252:80 | http://www.smalltree2021.com/z0po/?zXq4AN=P3voFln/iKMZ5C0WdoR3EmdK8jeyfWfkMl1WTrMoCI7YNwVu6xtCZlxPQOg+rMfdTb8GeQ==&T6Q=OvRHThcPZdnxWJ | KR | — | — | malicious |
392 | explorer.exe | GET | — | 172.217.16.211:80 | http://www.wealthprotein.com/z0po/?zXq4AN=htDx/9KJA91tGJ8QOPZfKSFJ9LUca0/kkCIWlA0Q52v8hG8dx+ftxBzhqwjHQlvE5GECtQ==&T6Q=OvRHThcPZdnxWJ | US | — | — | malicious |
392 | explorer.exe | GET | 403 | 34.102.136.180:80 | http://www.pepperhaul.com/z0po/?zXq4AN=F0jn7sIApReyXwcl/4QUu+P9UOpRdQM3A04aku5A2RDPS8Mori3+OvRT0aLwAcmvoyt+9g==&T6Q=OvRHThcPZdnxWJ | US | html | 275 b | whitelisted |
392 | explorer.exe | GET | 403 | 34.102.136.180:80 | http://www.thehappyhourtimes.com/z0po/?zXq4AN=Do+nd56TSn1MyxWM0SeAoYgusqSwvwGTxafOK3Y80hbI14nGni0uuGb53RCr5Nc399twbw==&T6Q=OvRHThcPZdnxWJ | US | html | 275 b | whitelisted |
392 | explorer.exe | GET | 404 | 35.242.251.130:80 | http://www.epitomelab.com/z0po/?zXq4AN=T4aOnuVWTG4IwoPXLypZR9yOkyHyokDTPDddo0oSGPKjIoWeaCdDOEuEhQ6QwUV8vFLcYw==&T6Q=OvRHThcPZdnxWJ | US | html | 2.89 Kb | malicious |
392 | explorer.exe | GET | 403 | 34.102.136.180:80 | http://www.culinaryrambler.net/z0po/?zXq4AN=Dusj8lsujXh8tuEujIkzBUnrWhsKxgrv52f5zIyfMVRGed7DrXB2EWcTWw39BgCTyNaICw==&T6Q=OvRHThcPZdnxWJ | US | html | 275 b | whitelisted |
392 | explorer.exe | GET | 302 | 172.217.16.211:80 | http://www.gardenoffear.com/z0po/?zXq4AN=tSf2I2OF7yM5JGEzFf1pSV5JjlJ5XqUazl1JFj+Bt25F8KrpRLVEcoEYqeVm7JvhiCNr1Q==&T6Q=OvRHThcPZdnxWJ | US | html | 329 b | malicious |
392 | explorer.exe | GET | 404 | 160.124.83.93:80 | http://www.anthonyfung.com/z0po/?zXq4AN=2NTihudRGRKkfVTmeX8RYe53gsdIvpMoVuw7ZayPcW/2vcWj7ku/FgKqfukCha2n2JhkLA==&T6Q=OvRHThcPZdnxWJ | ZA | html | 146 b | malicious |
2792 | audiodg.exe | GET | 301 | 156.234.156.248:80 | http://www.czshht.com/z0po/?zXq4AN=JReIkFxS0LGIn12kv01MVdW7LxKMLJgxKNRfig+15oFpMGtv6KdreoKZhCg1F2ssgkJ0+g==&T6Q=OvRHThcPZdnxWJ | US | html | 166 b | malicious |
392 | explorer.exe | GET | 301 | 99.86.7.67:80 | http://www.top10bestblogsites.com/z0po/?zXq4AN=SwNUHyJUJwMynHP4Ngwq2TtbbmyP7f2OIoZPopGwYkHBRXk+fjhHtRhgA/NqkQwA9jo7Uw==&T6Q=OvRHThcPZdnxWJ | US | html | 183 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
392 | explorer.exe | 160.124.83.93:80 | www.anthonyfung.com | — | ZA | malicious |
392 | explorer.exe | 172.217.16.211:80 | www.gardenoffear.com | Google Inc. | US | whitelisted |
392 | explorer.exe | 35.242.251.130:80 | www.epitomelab.com | — | US | malicious |
392 | explorer.exe | 34.102.136.180:80 | www.thehappyhourtimes.com | — | US | whitelisted |
392 | explorer.exe | 99.86.7.67:80 | www.top10bestblogsites.com | AT&T Services, Inc. | US | malicious |
— | — | 34.102.136.180:80 | www.thehappyhourtimes.com | — | US | whitelisted |
2792 | audiodg.exe | 156.234.156.248:80 | www.czshht.com | MULTACOM CORPORATION | US | malicious |
392 | explorer.exe | 156.234.156.248:80 | www.czshht.com | MULTACOM CORPORATION | US | malicious |
392 | explorer.exe | 121.254.178.252:80 | www.smalltree2021.com | LG DACOM Corporation | KR | malicious |
2792 | audiodg.exe | 156.234.156.248:443 | www.czshht.com | MULTACOM CORPORATION | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.top10bestblogsites.com |
| suspicious |
www.anthonyfung.com |
| malicious |
www.gardenoffear.com |
| malicious |
www.epitomelab.com |
| malicious |
www.czshht.com |
| malicious |
www.thehappyhourtimes.com |
| whitelisted |
www.pepperhaul.com |
| whitelisted |
www.smalltree2021.com |
| malicious |
www.culinaryrambler.net |
| whitelisted |
www.wealthprotein.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
392 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
392 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
392 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
9 ETPRO signatures available at the full report