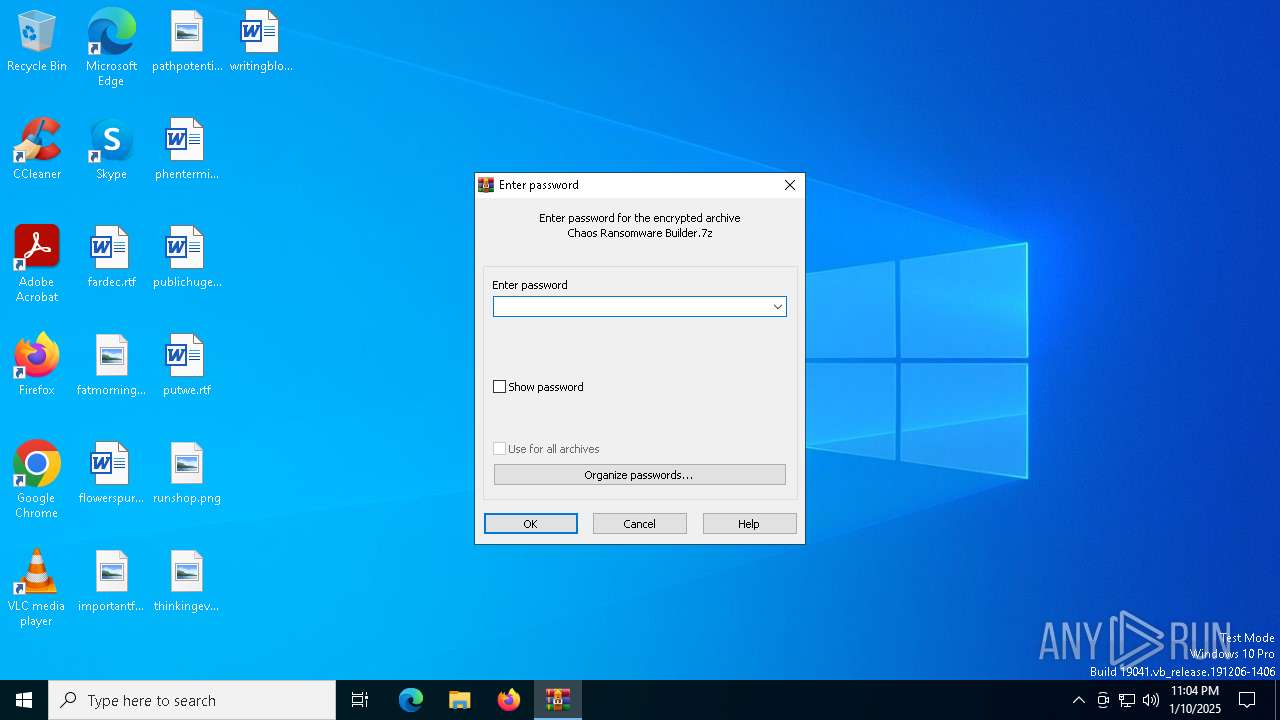
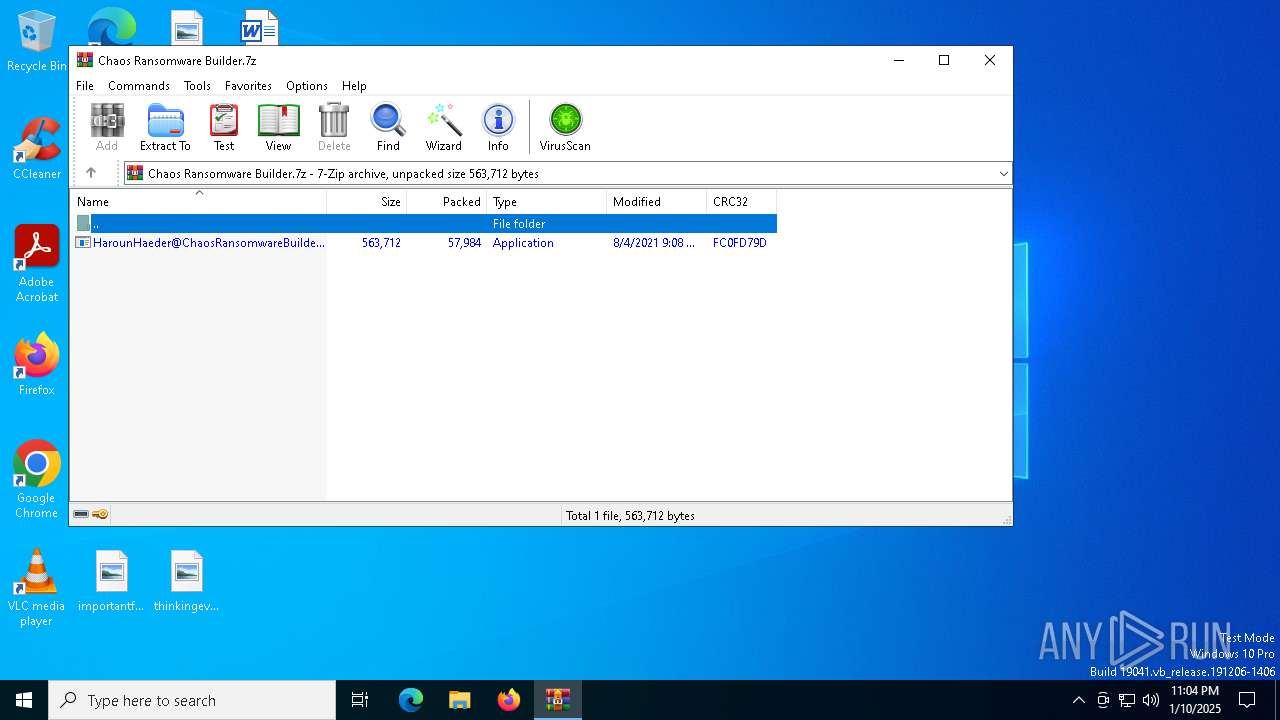
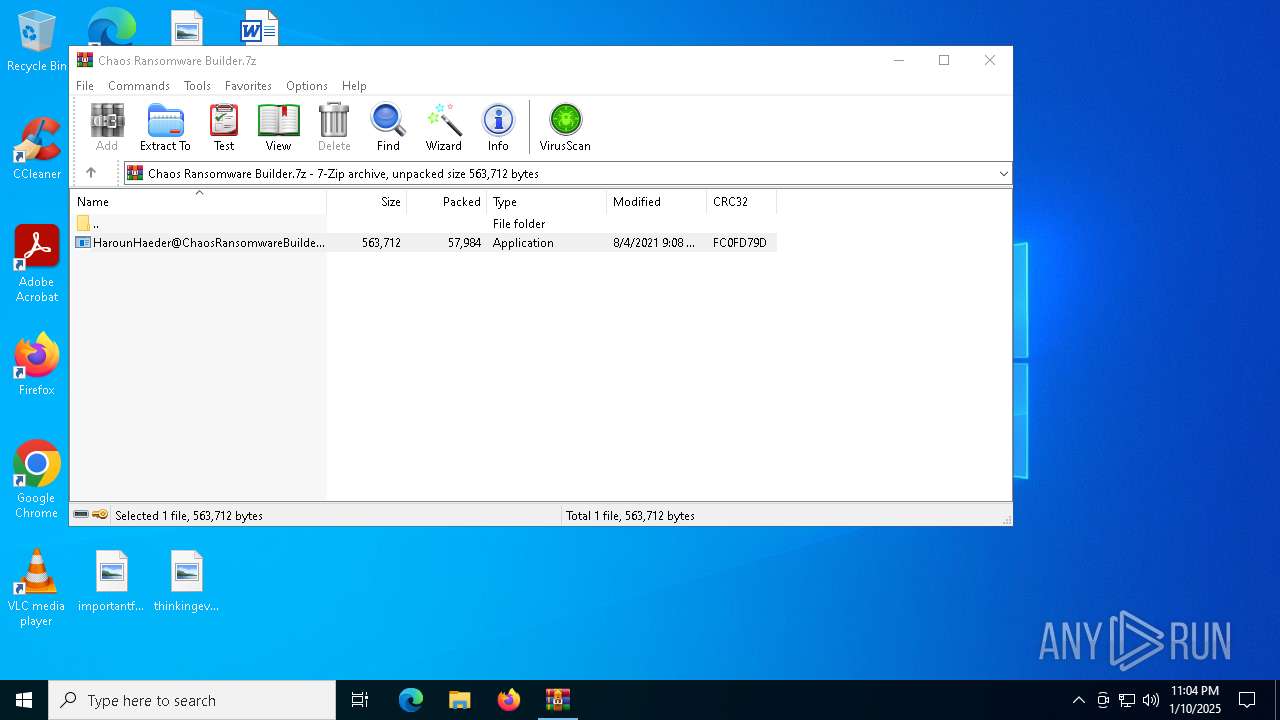
| File name: | Chaos Ransomware Builder.7z |
| Full analysis: | https://app.any.run/tasks/927a8ef5-7954-49b1-a1b3-e0c18d65bee8 |
| Verdict: | Malicious activity |
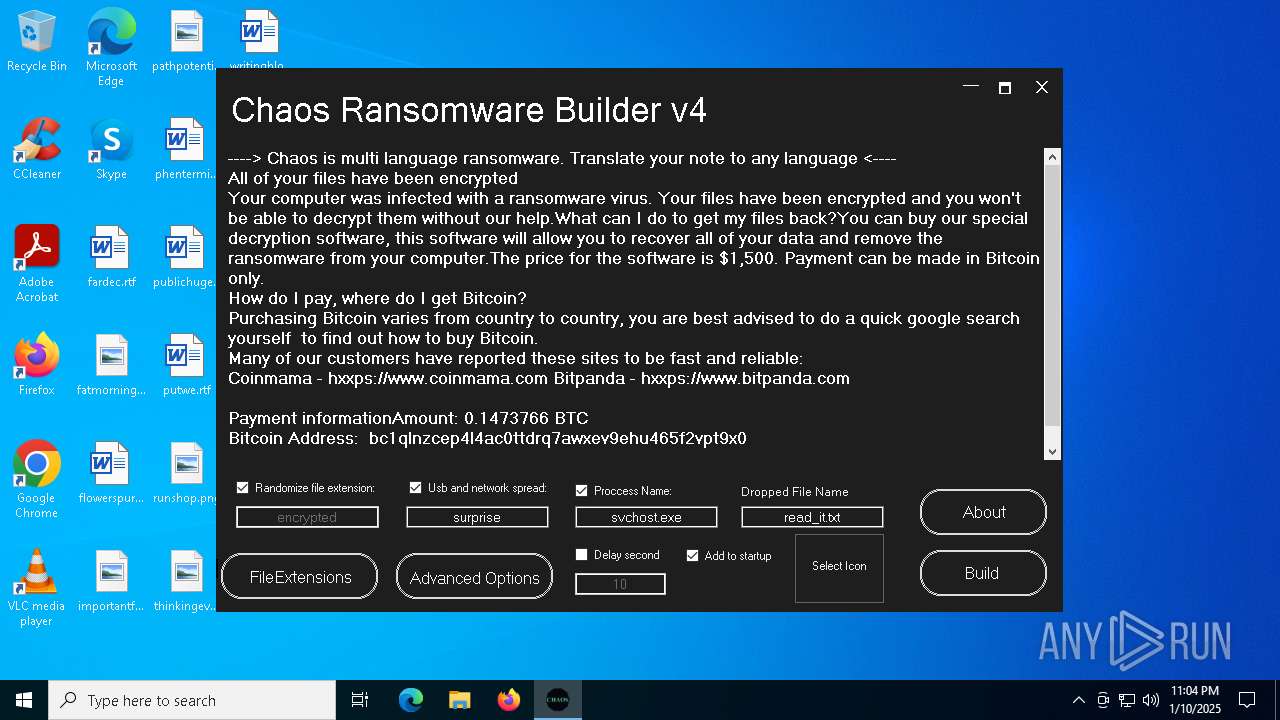
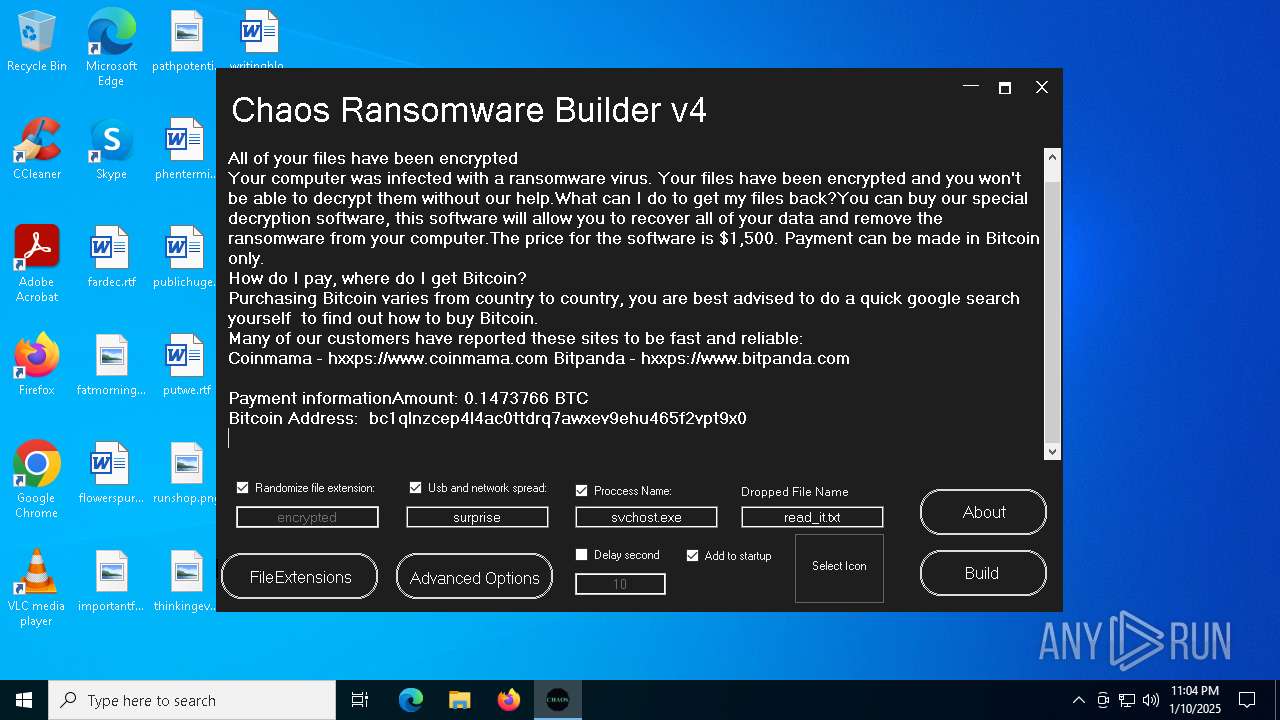
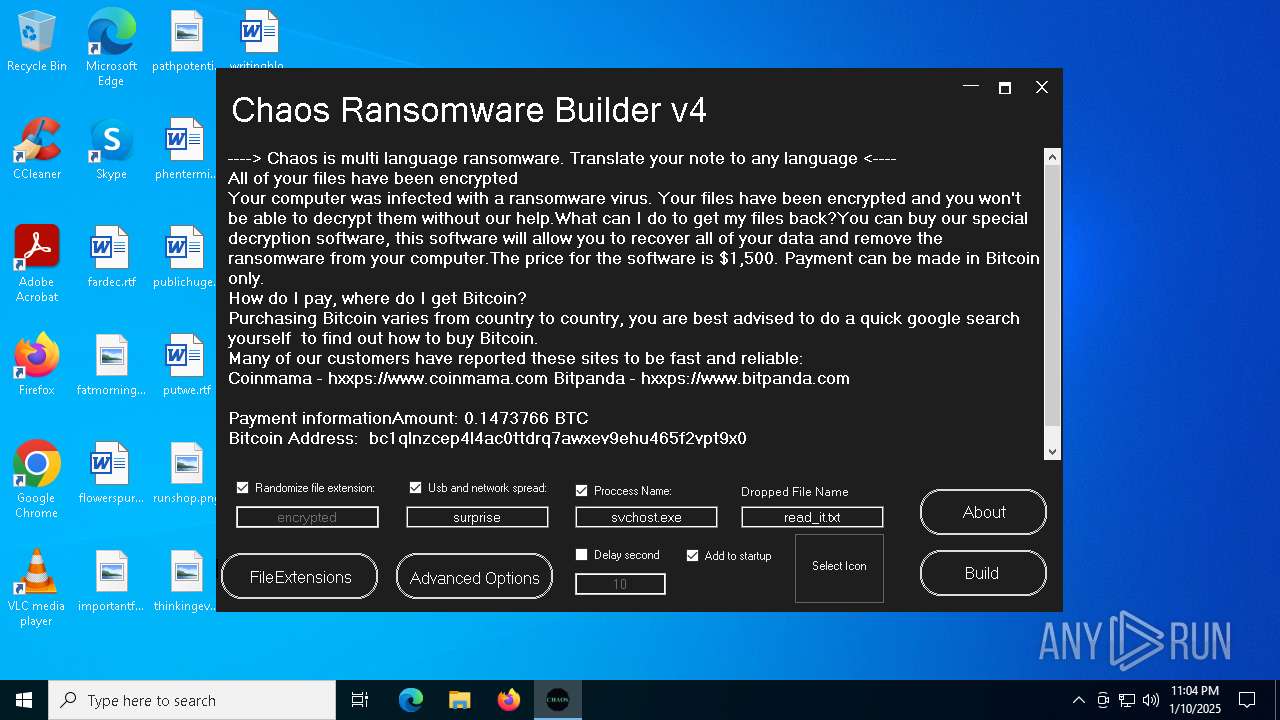
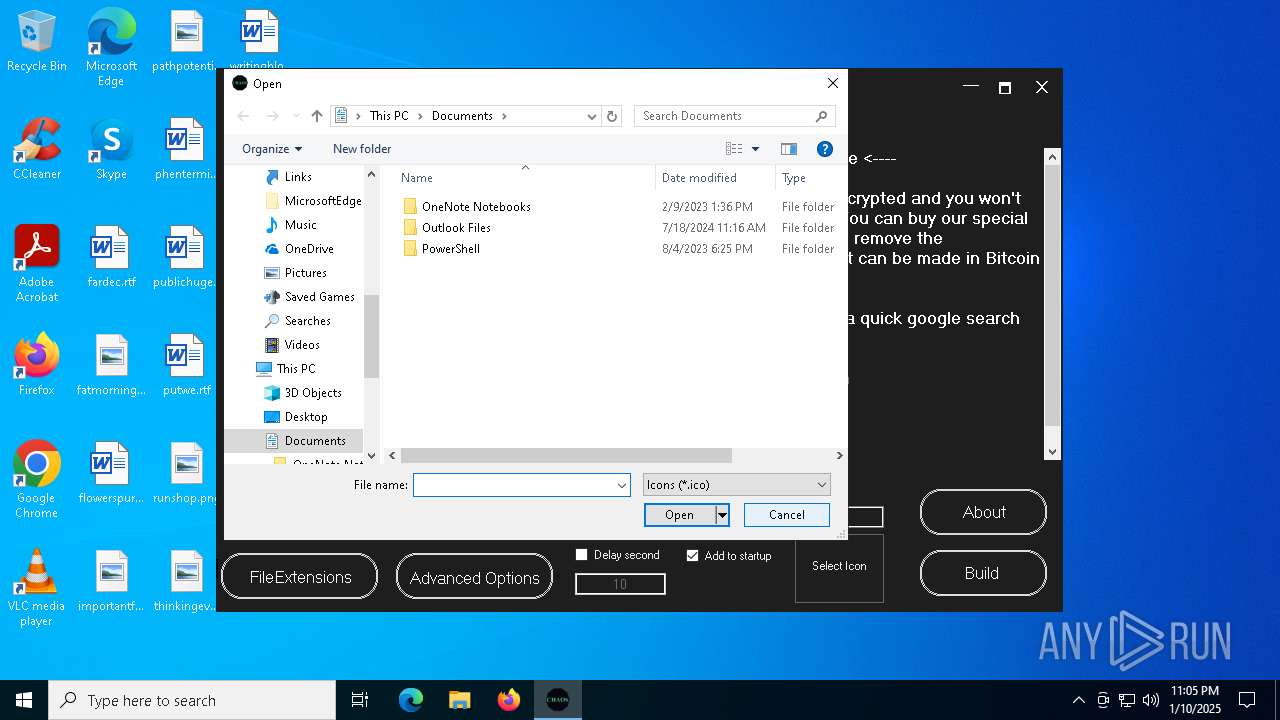
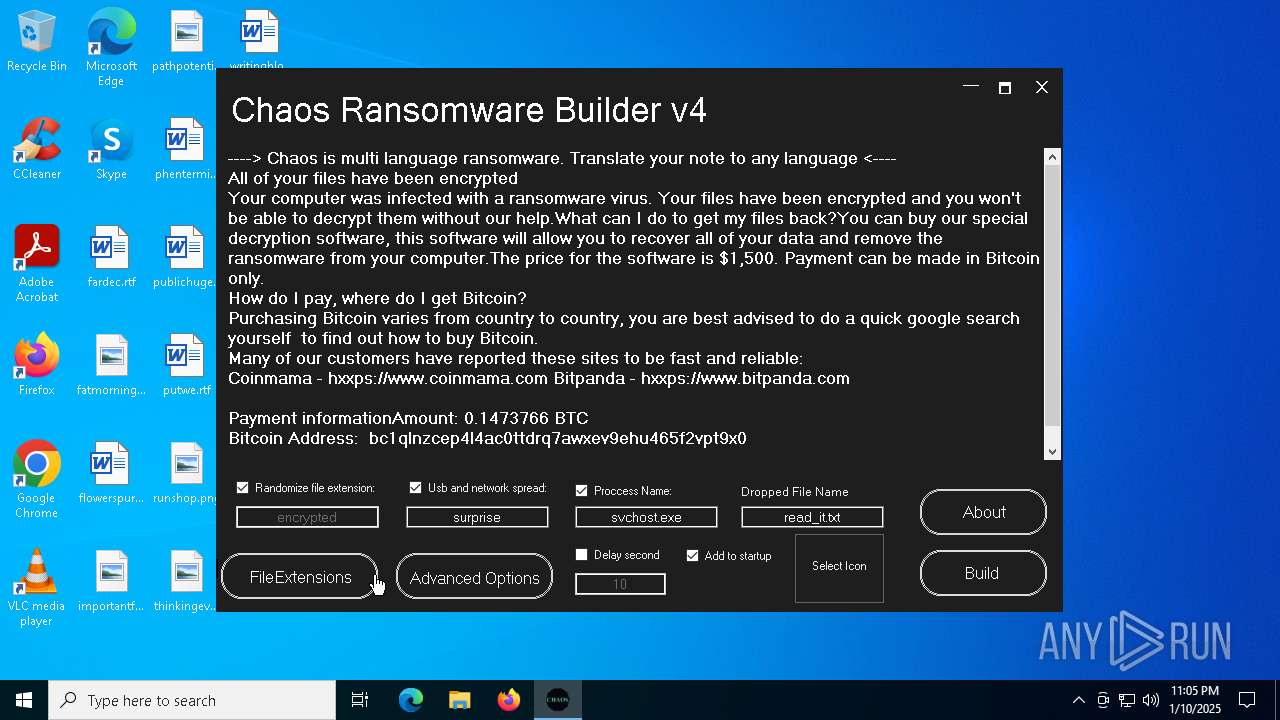
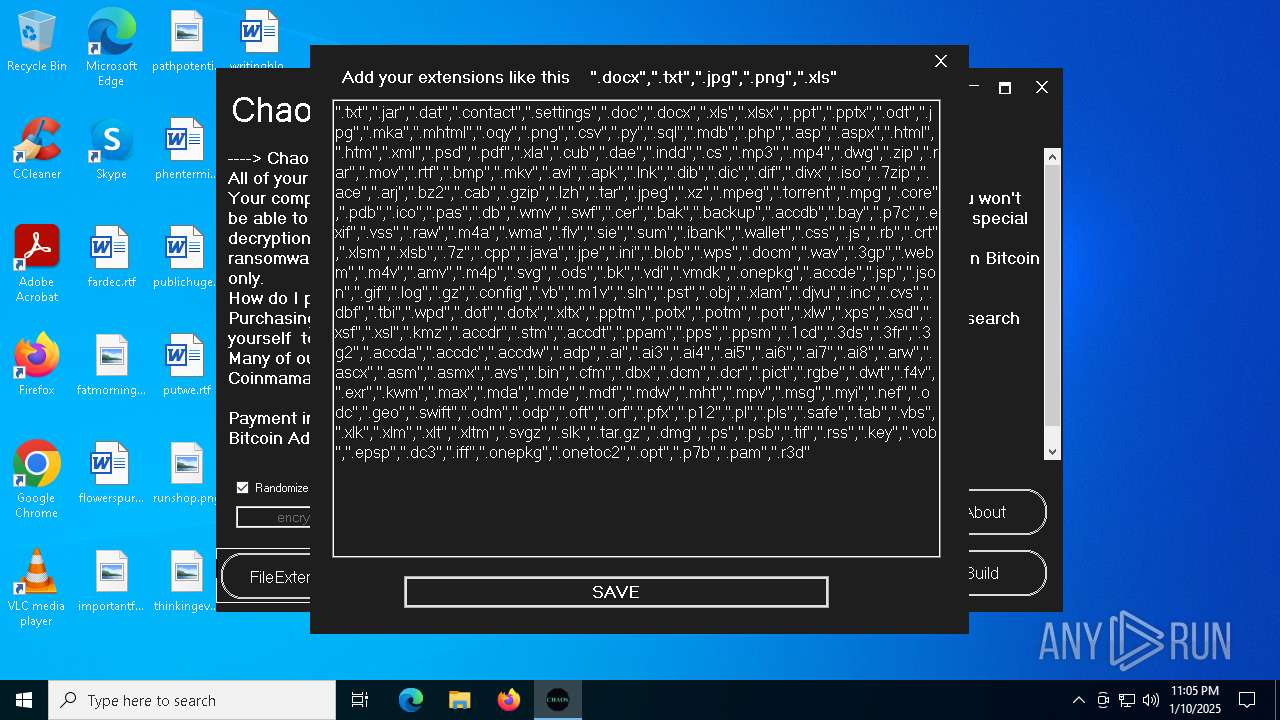
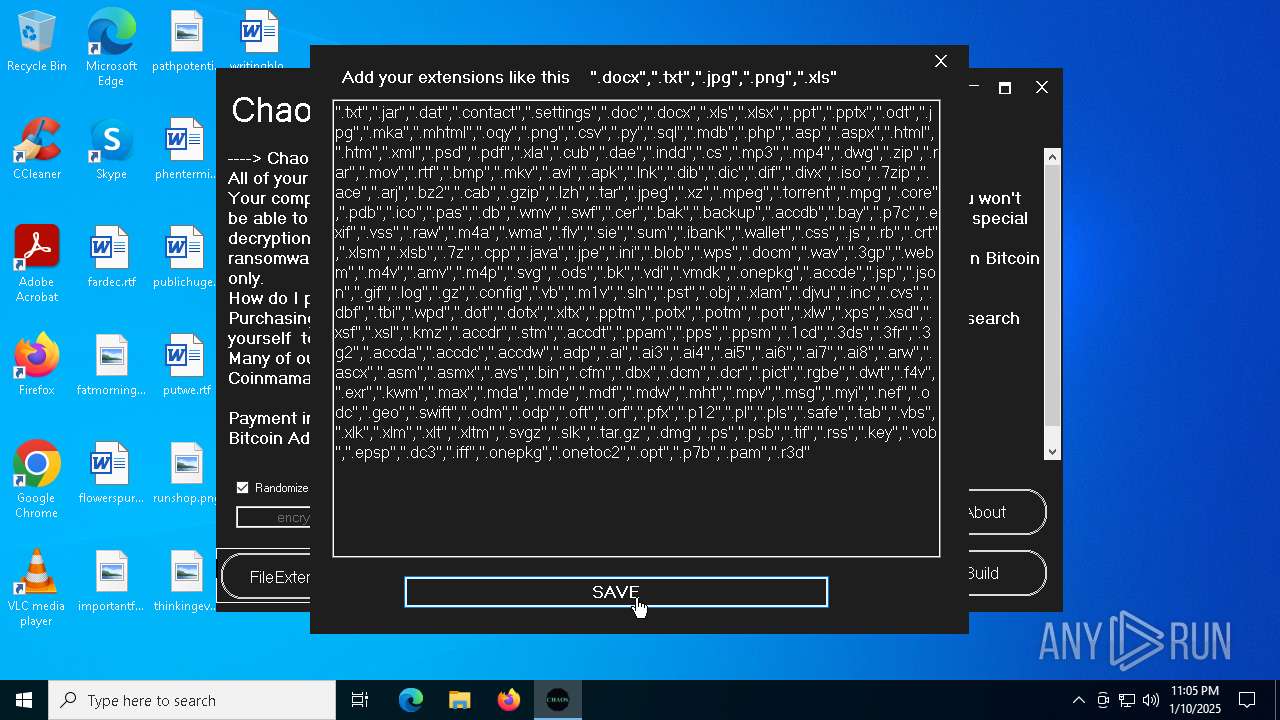
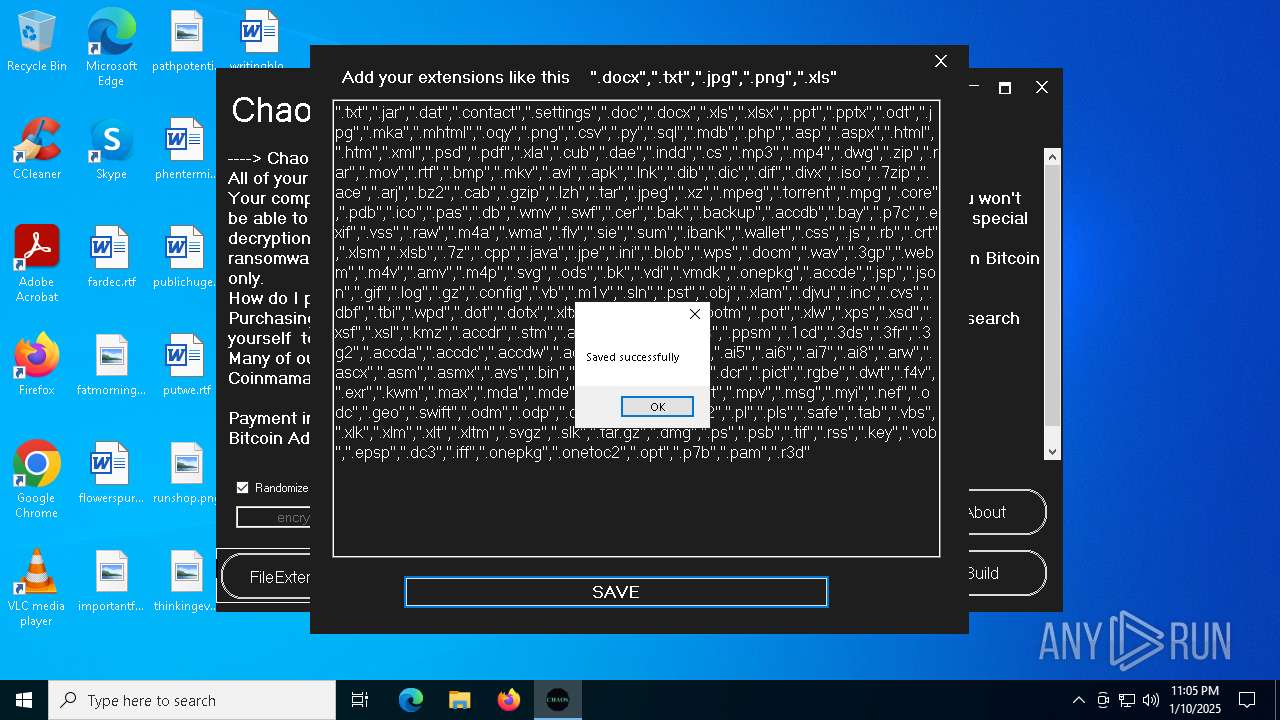
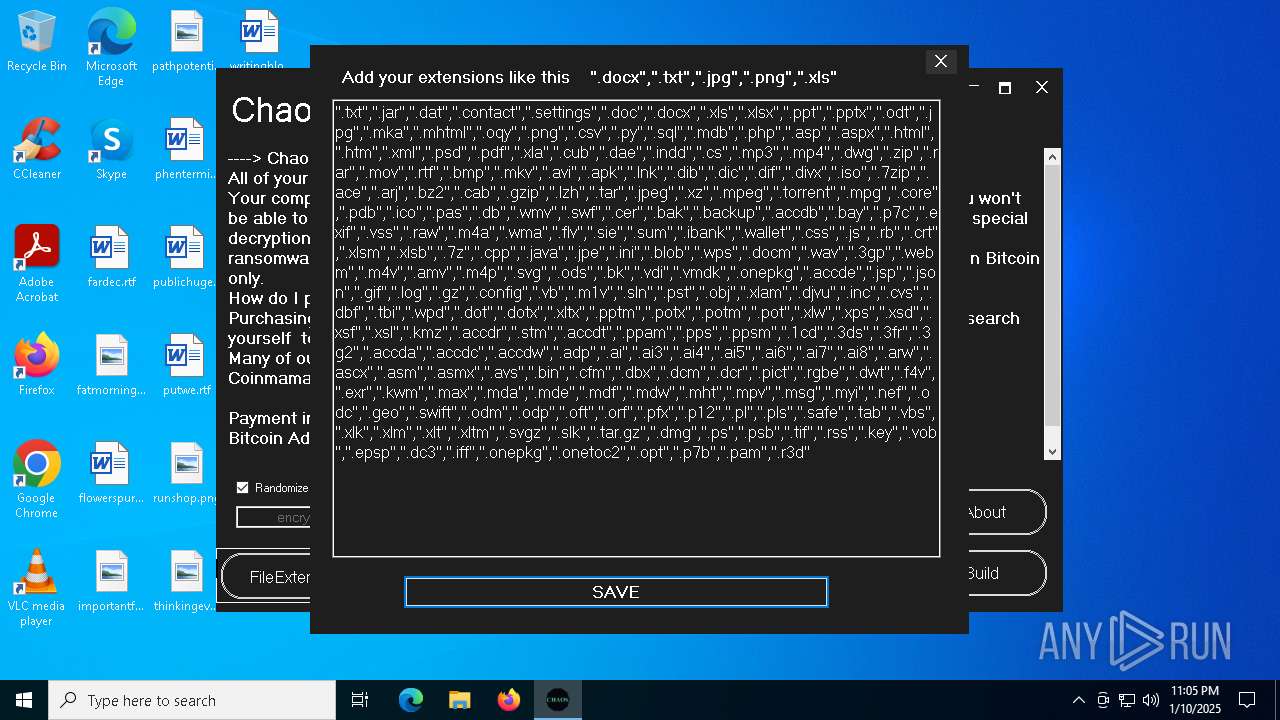
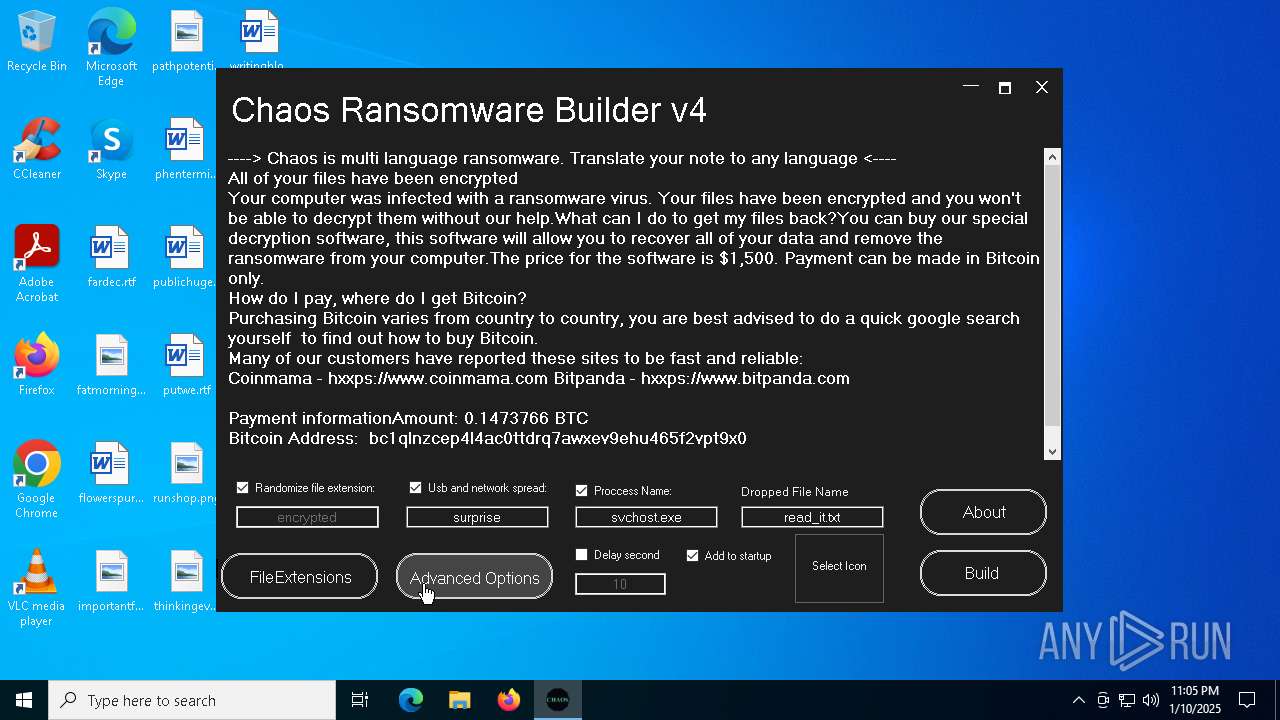
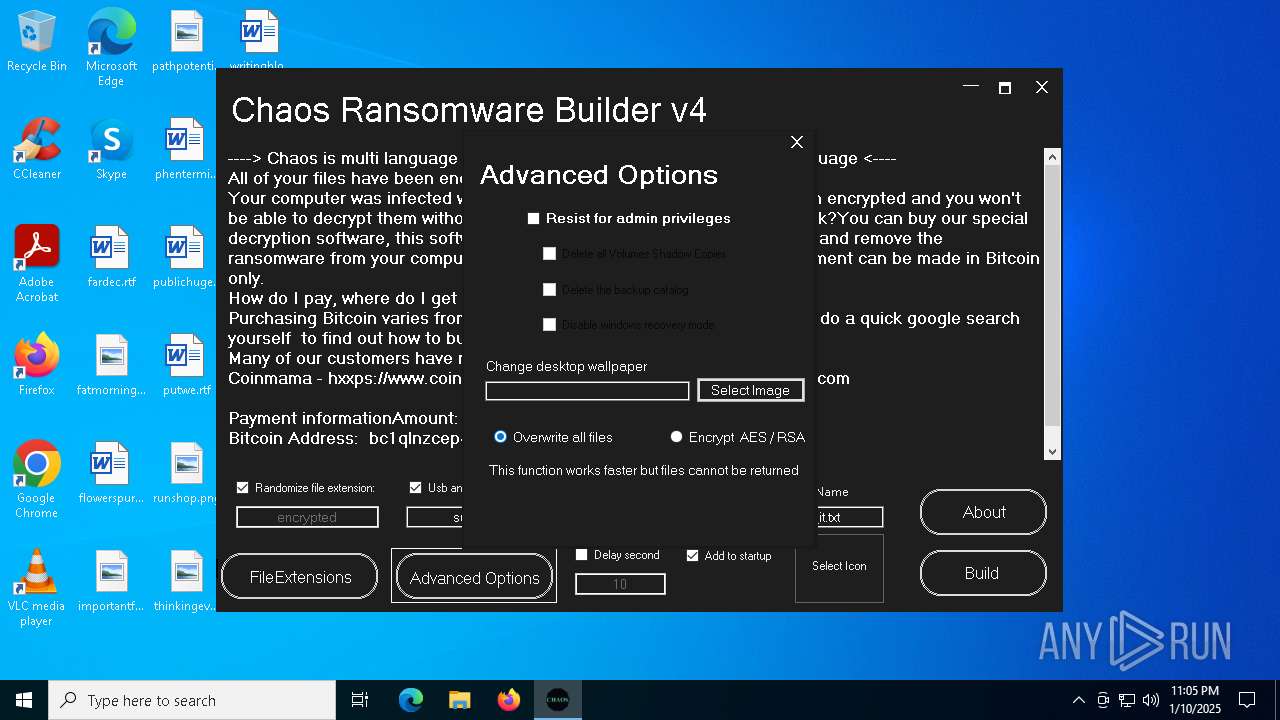
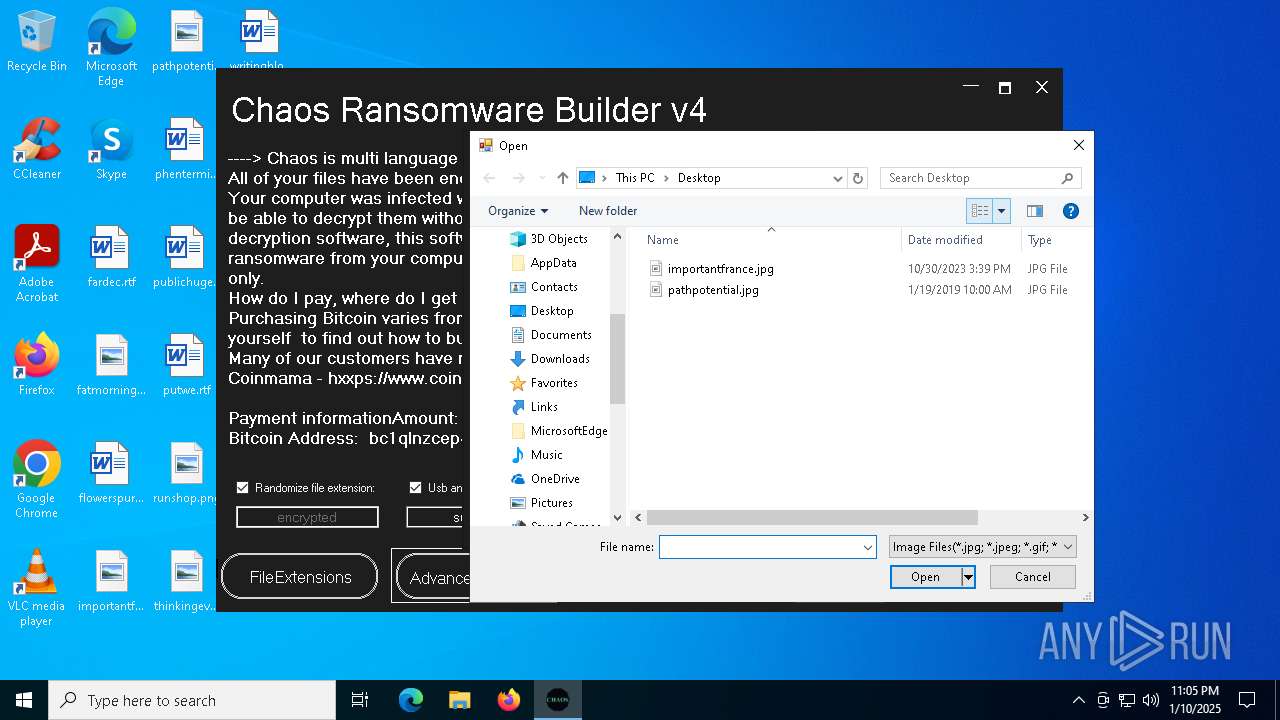
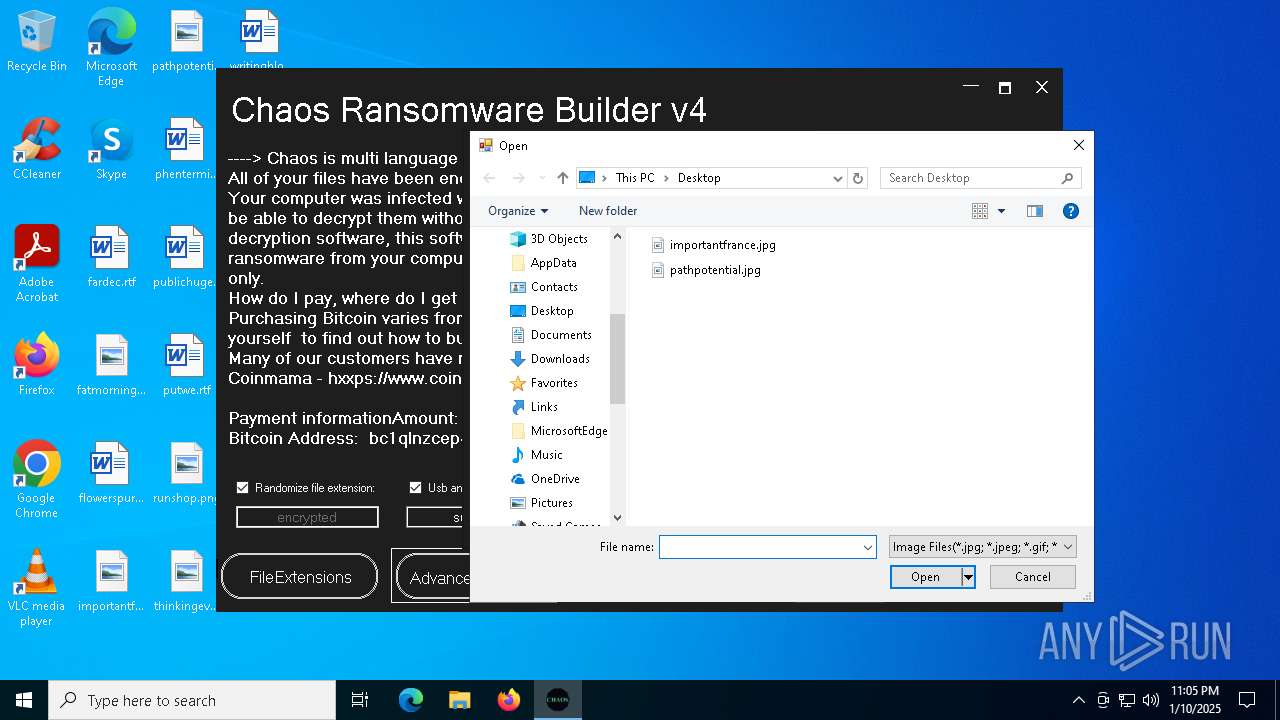
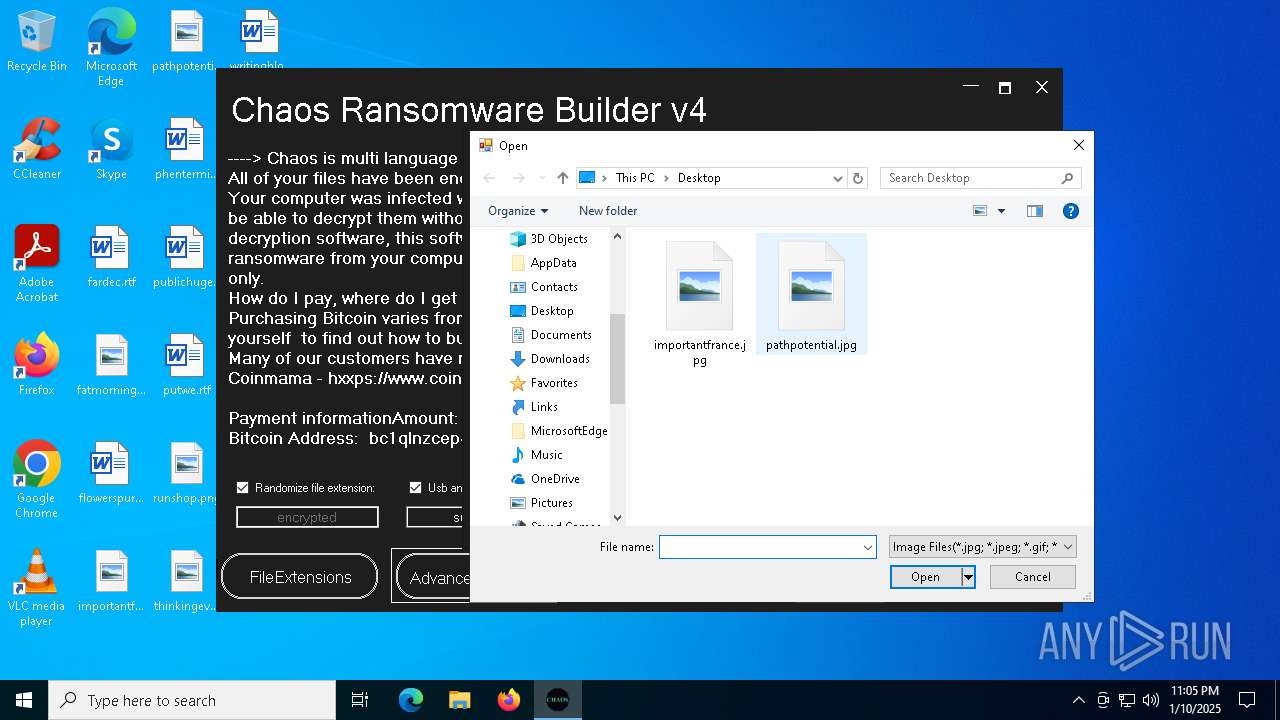
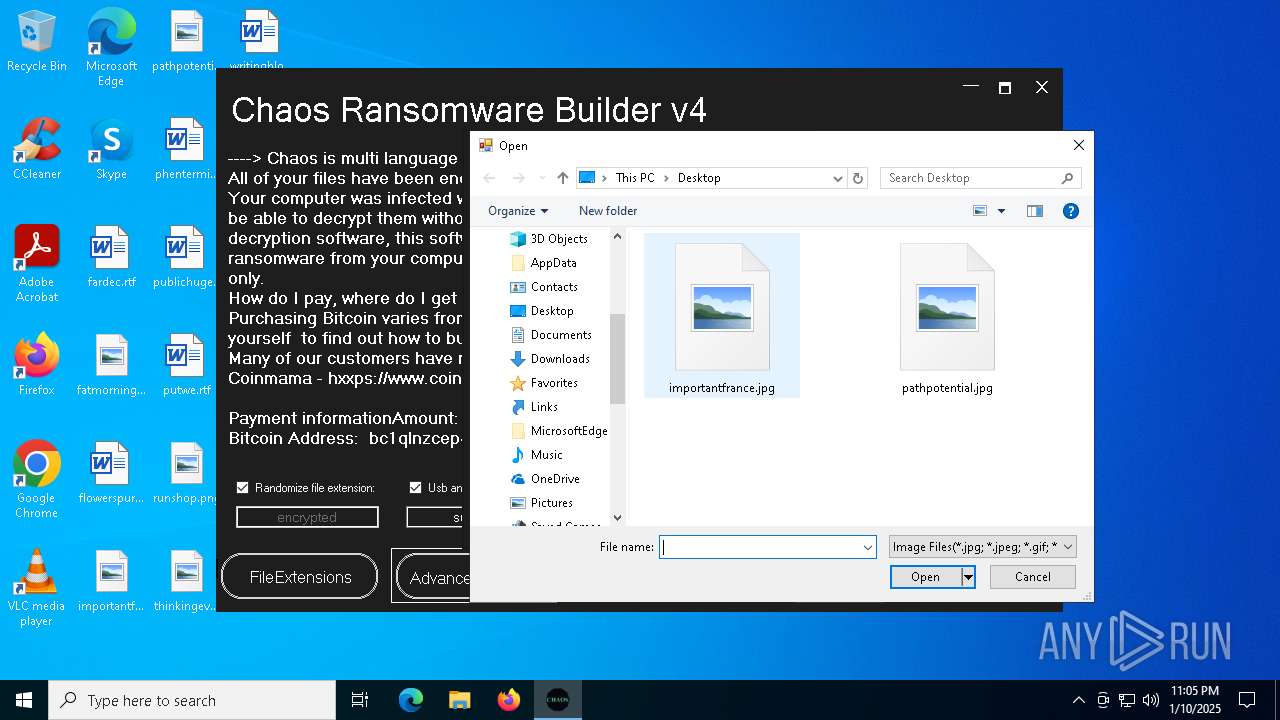
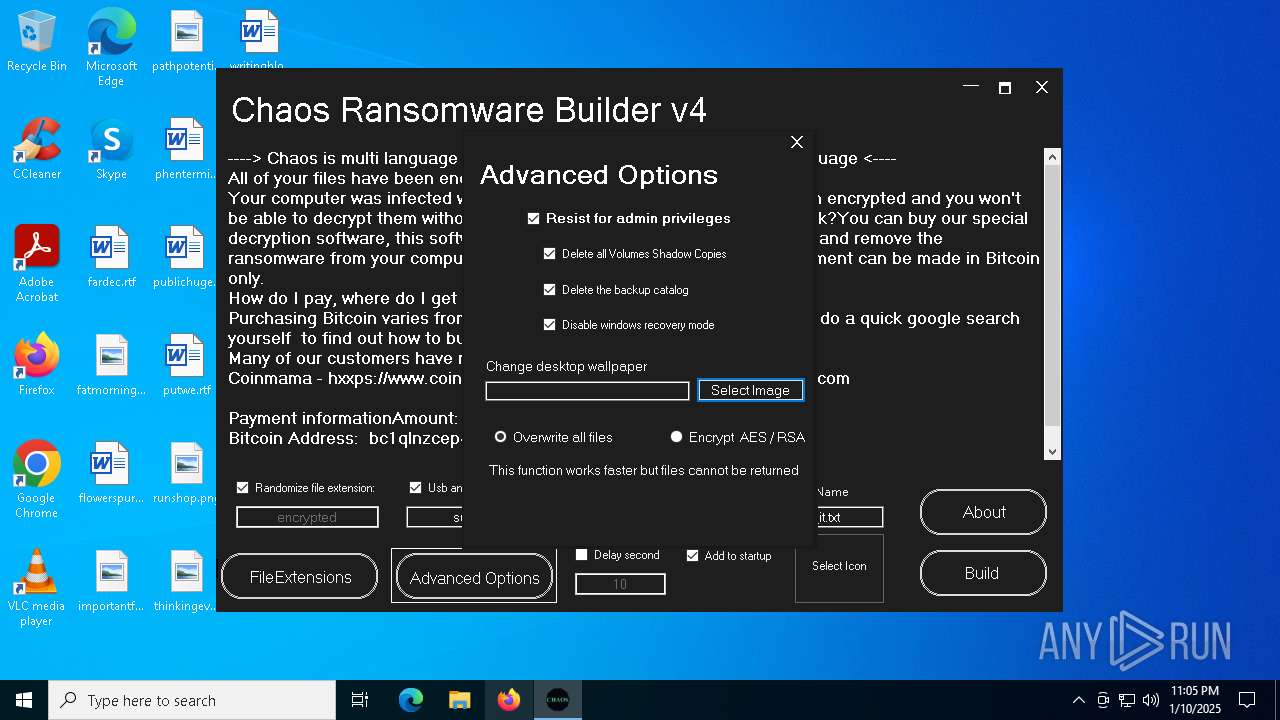
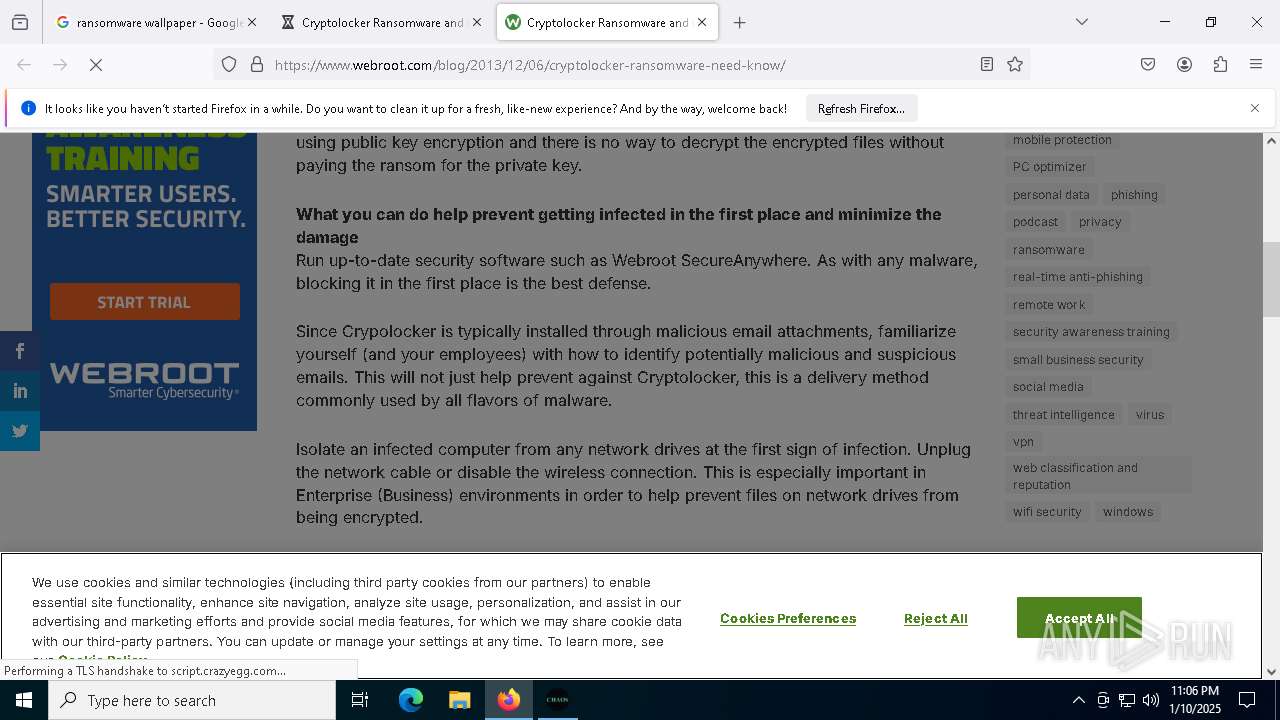
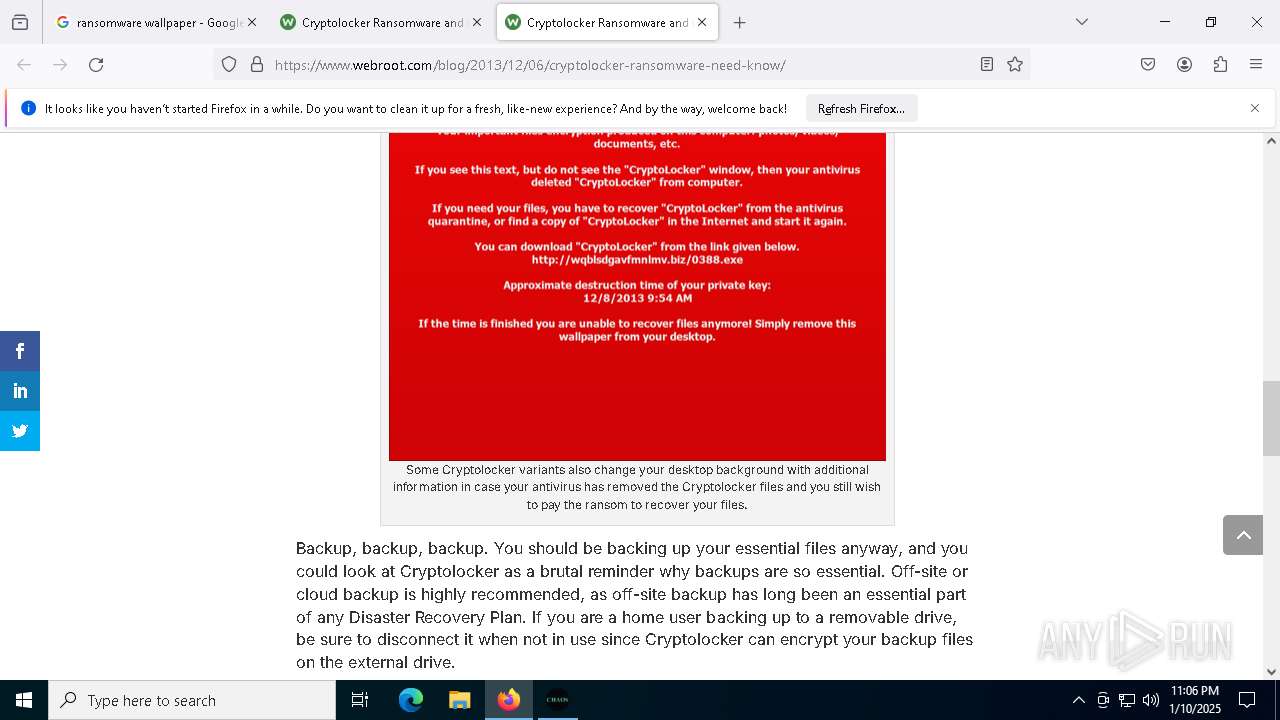
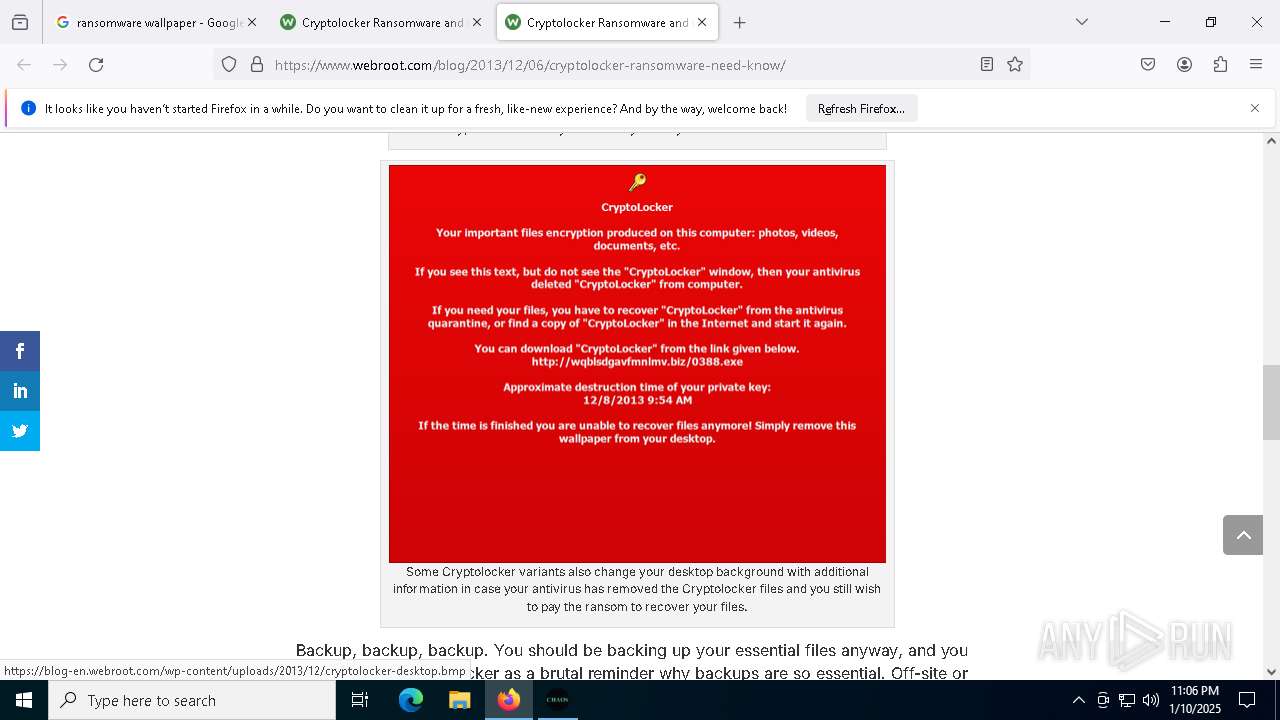
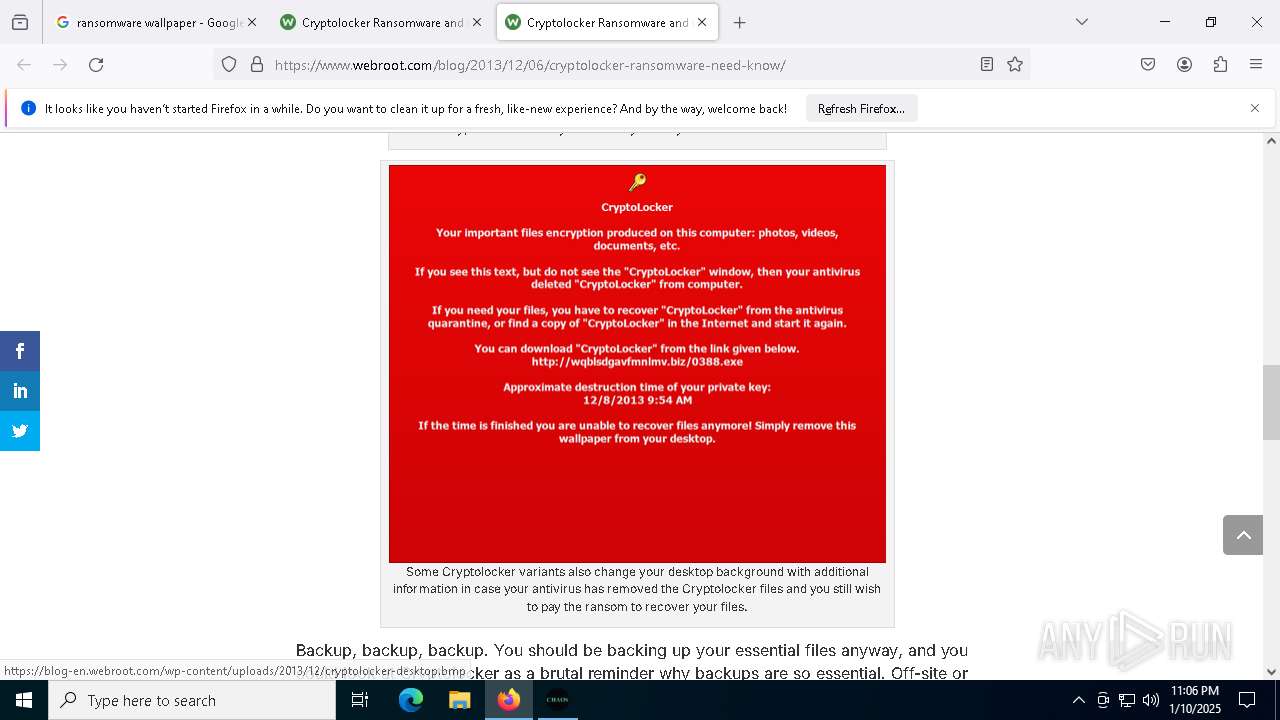
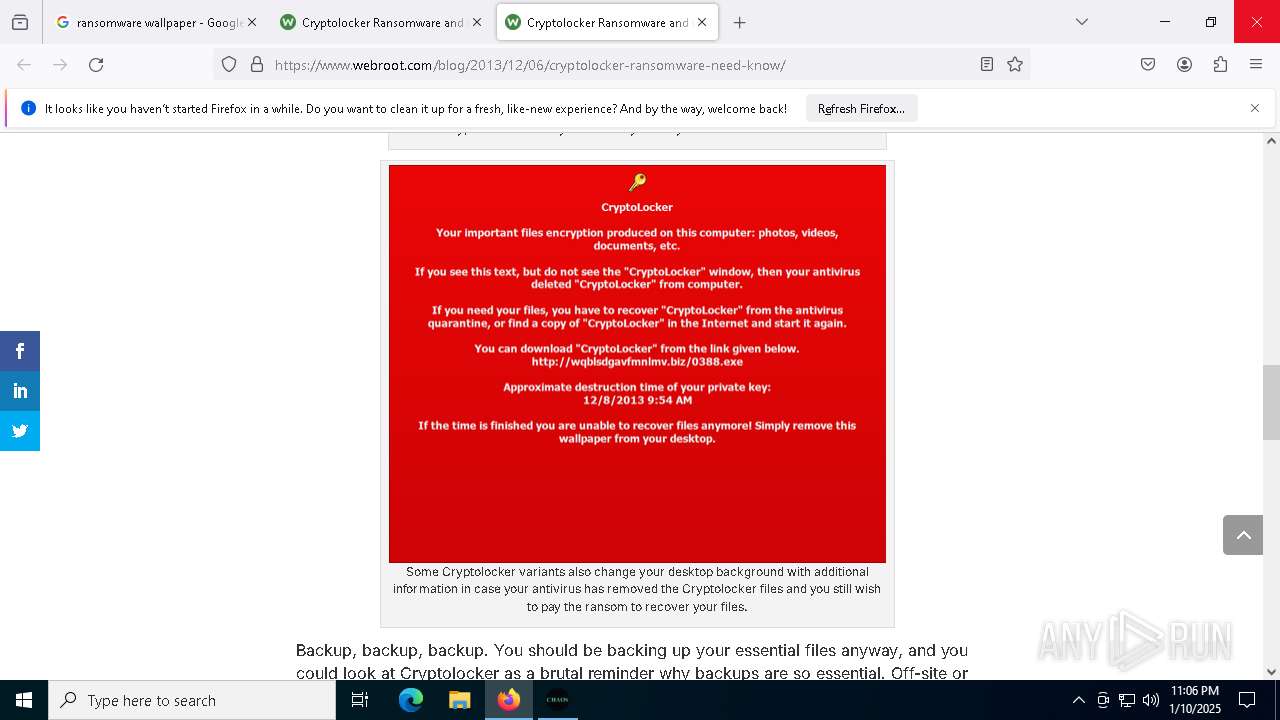
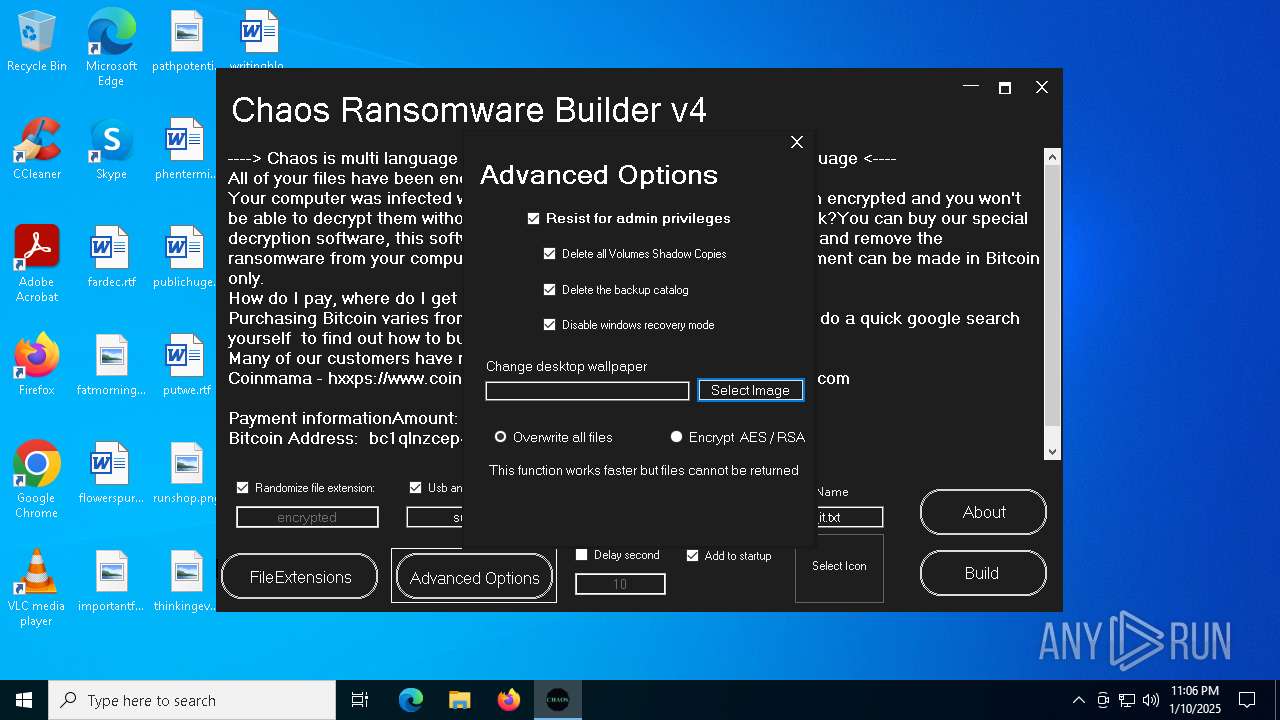
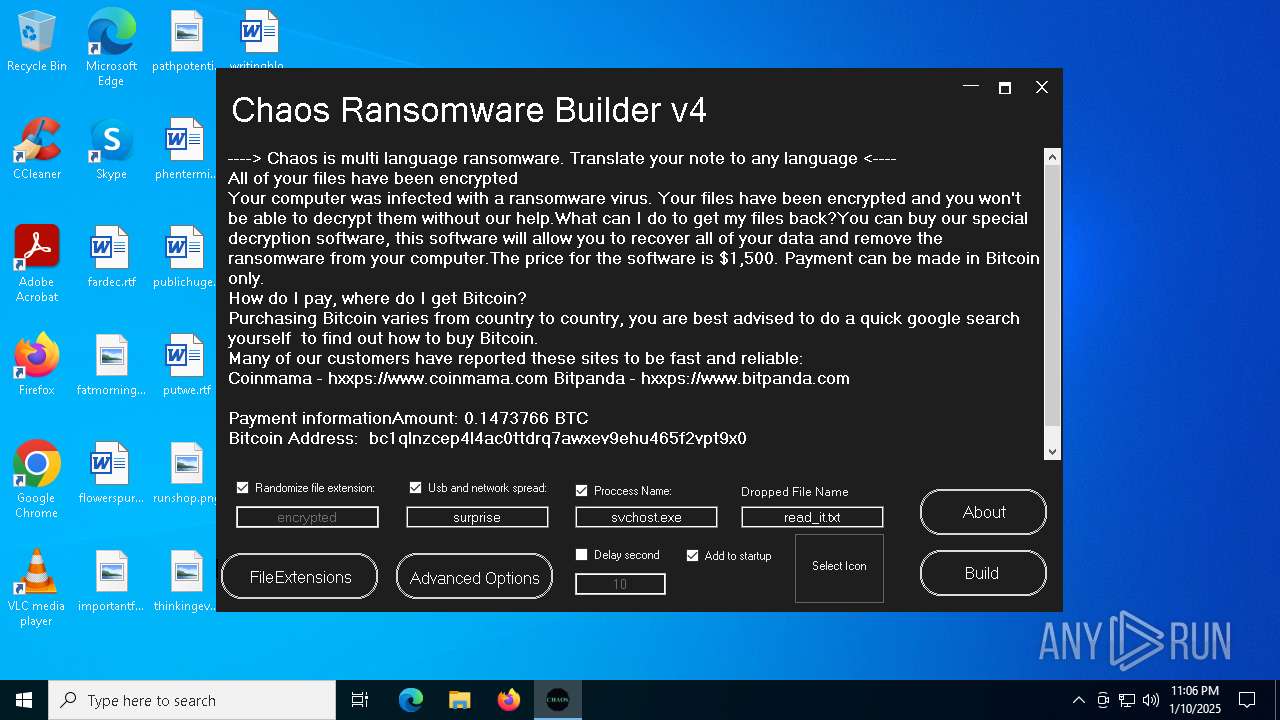
| Threats: | Chaos ransomware is a malware family known for its destructive capabilities and diverse variants. It first appeared in 2021 as a ransomware builder and later acted as a wiper. Unlike most ransomware strains that encrypt data to extort payment, early Chaos variants permanently corrupted files, while later versions adopted more conventional encryption techniques. |
| Analysis date: | January 10, 2025, 23:04:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 4213295AEA6FECD3DD288F57592D4EFA |
| SHA1: | 2331B85B626C5B728AB63AA6A137881721E4C7CE |
| SHA256: | 265DC5A14AA605A23B7E0A32A1EF3D8F501870988AB22EC91DC69465E9894140 |
| SSDEEP: | 1536:p9JDUBYfFd+MdDOx54dpZcXfCyAqbdFPmGtNxr0bywFMh:pnUBYfrX0mVqvPjtjYTs |
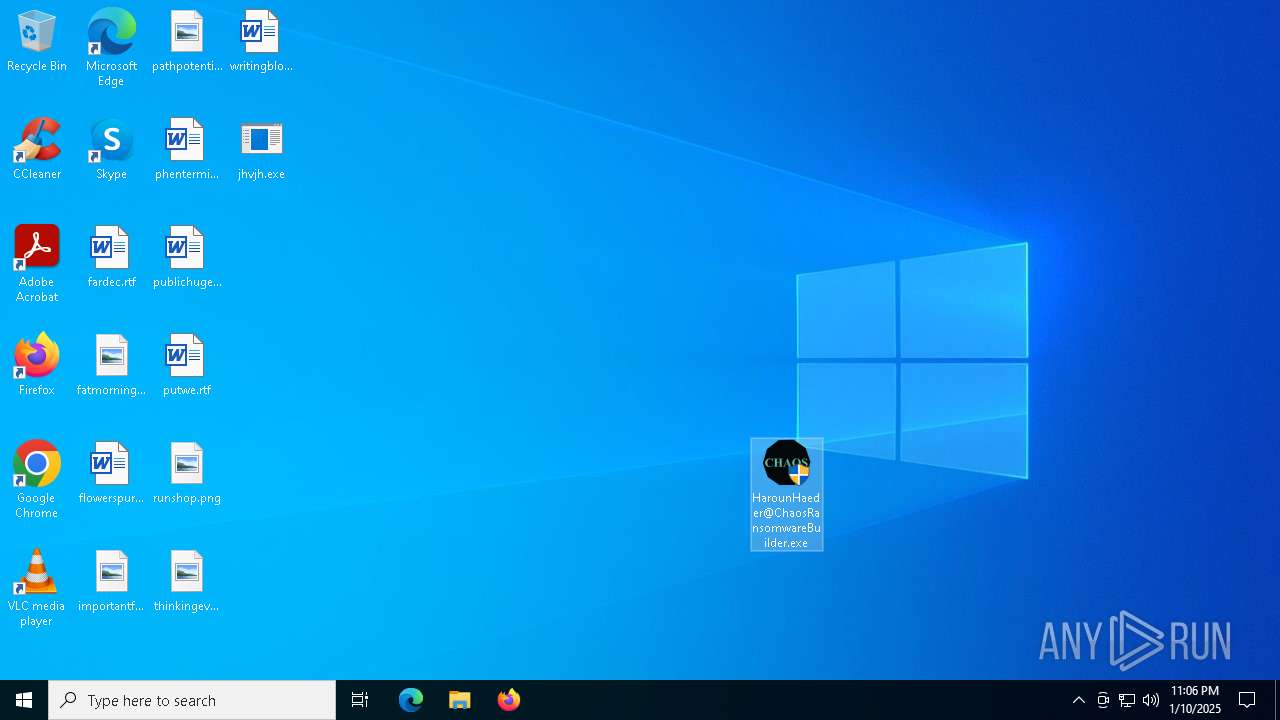
MALICIOUS
CHAOS has been detected (YARA)
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- svchost.exe (PID: 7032)
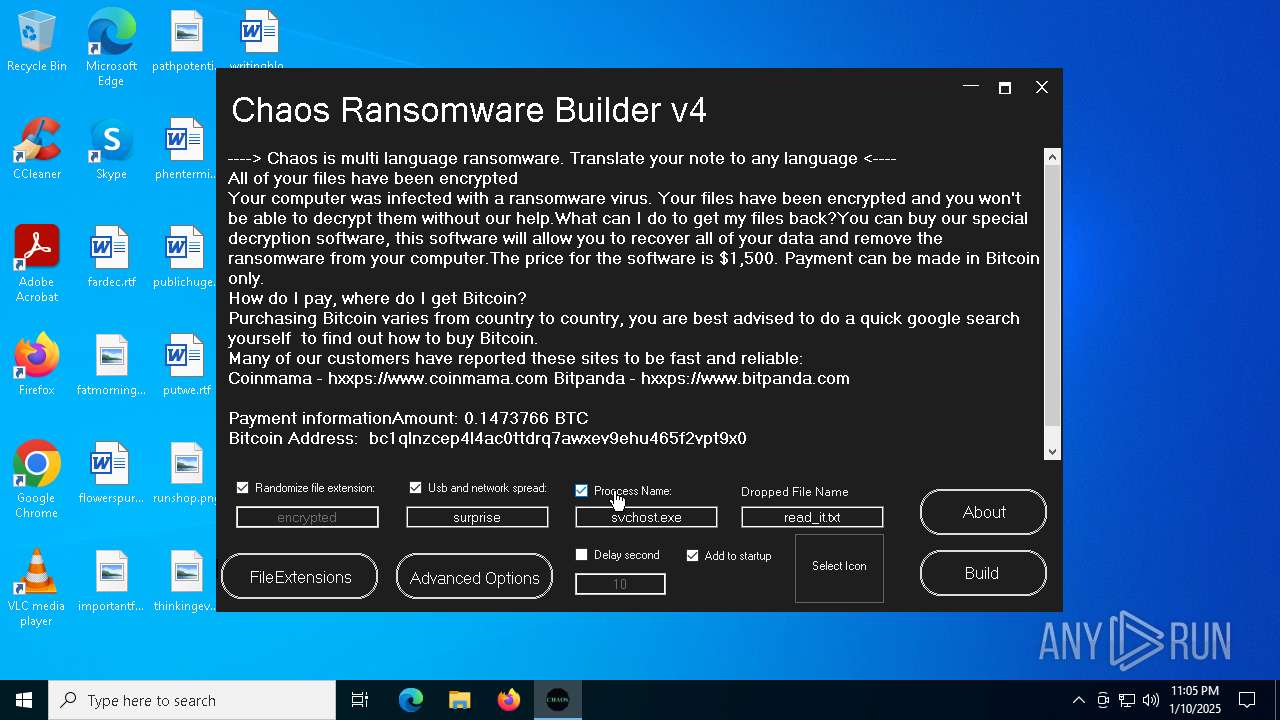
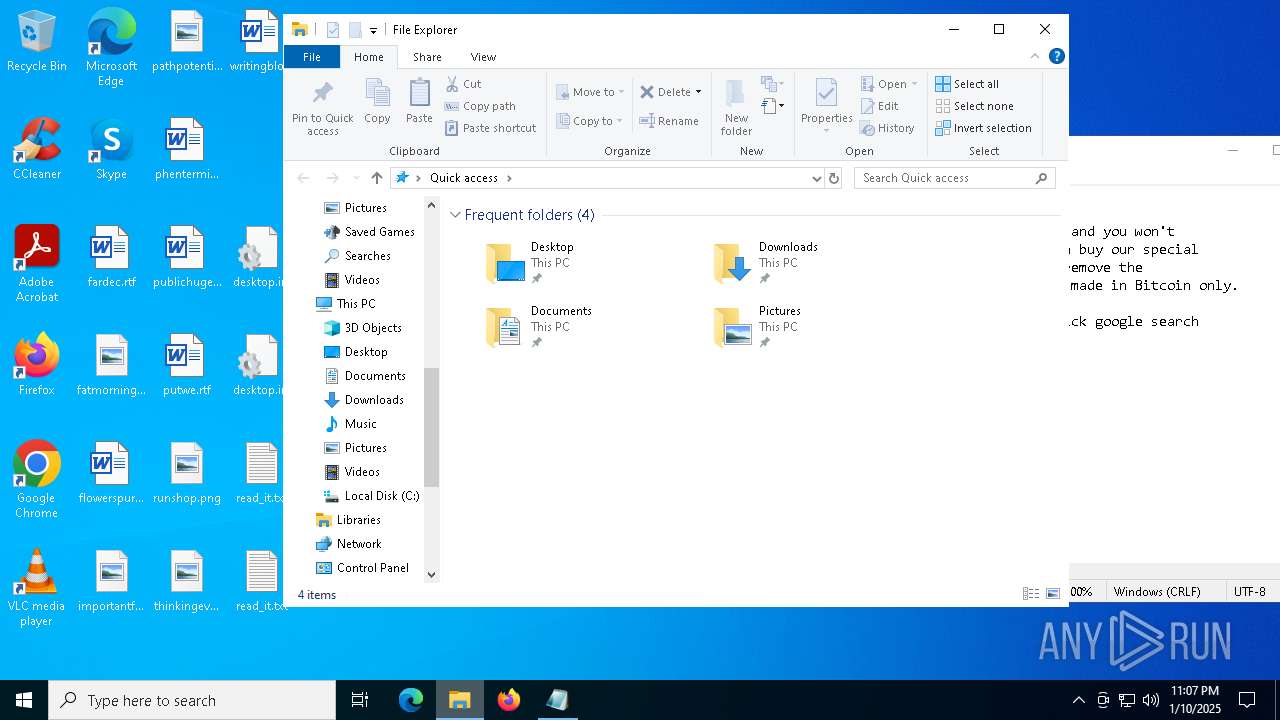
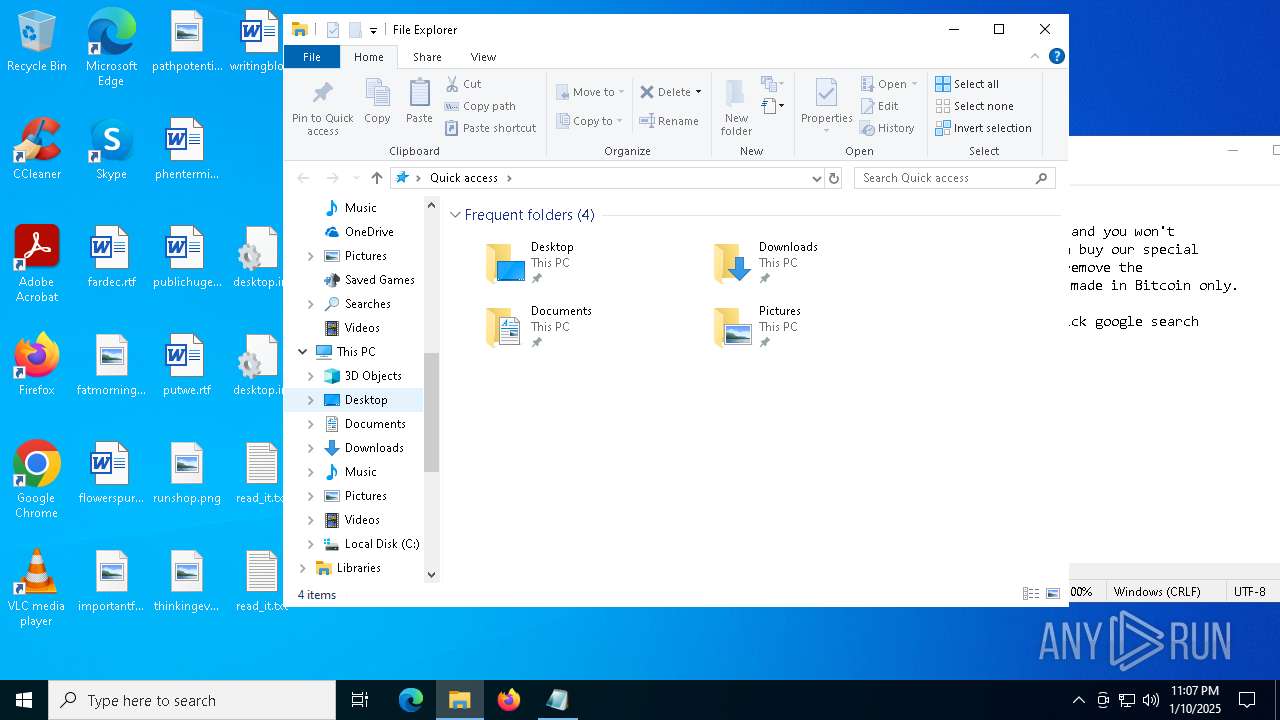
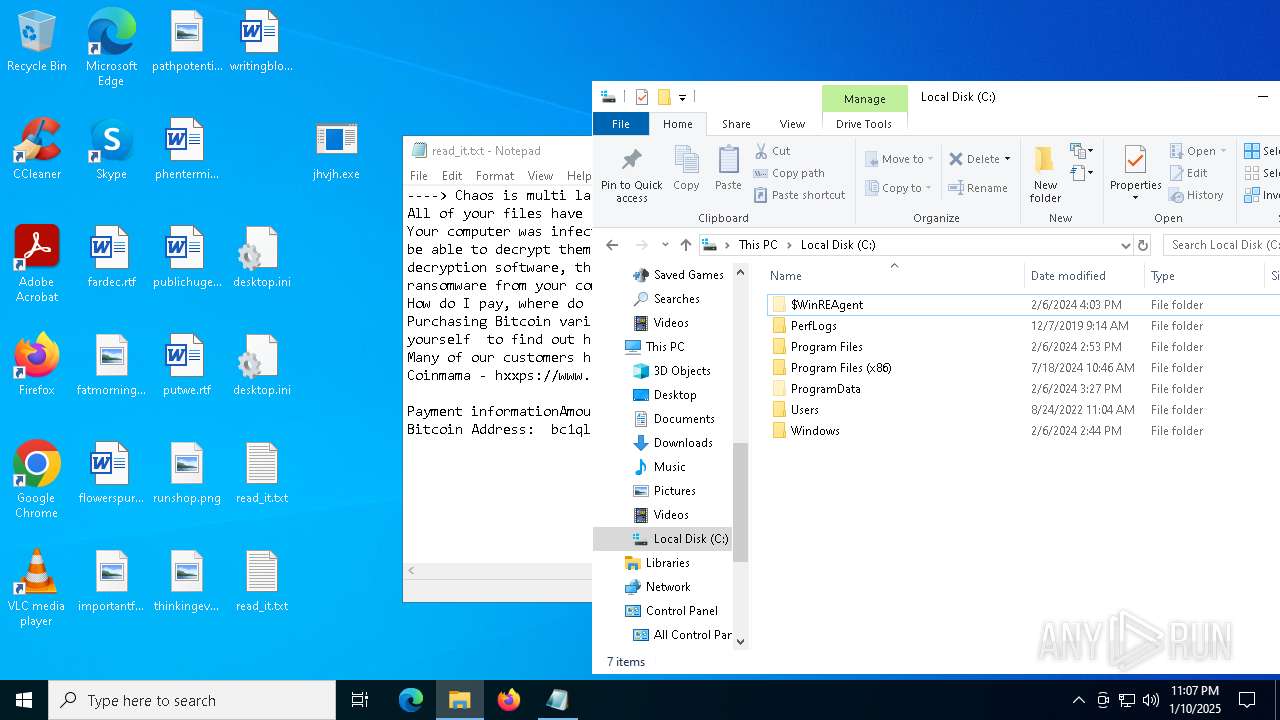
Create files in the Startup directory
- svchost.exe (PID: 7032)
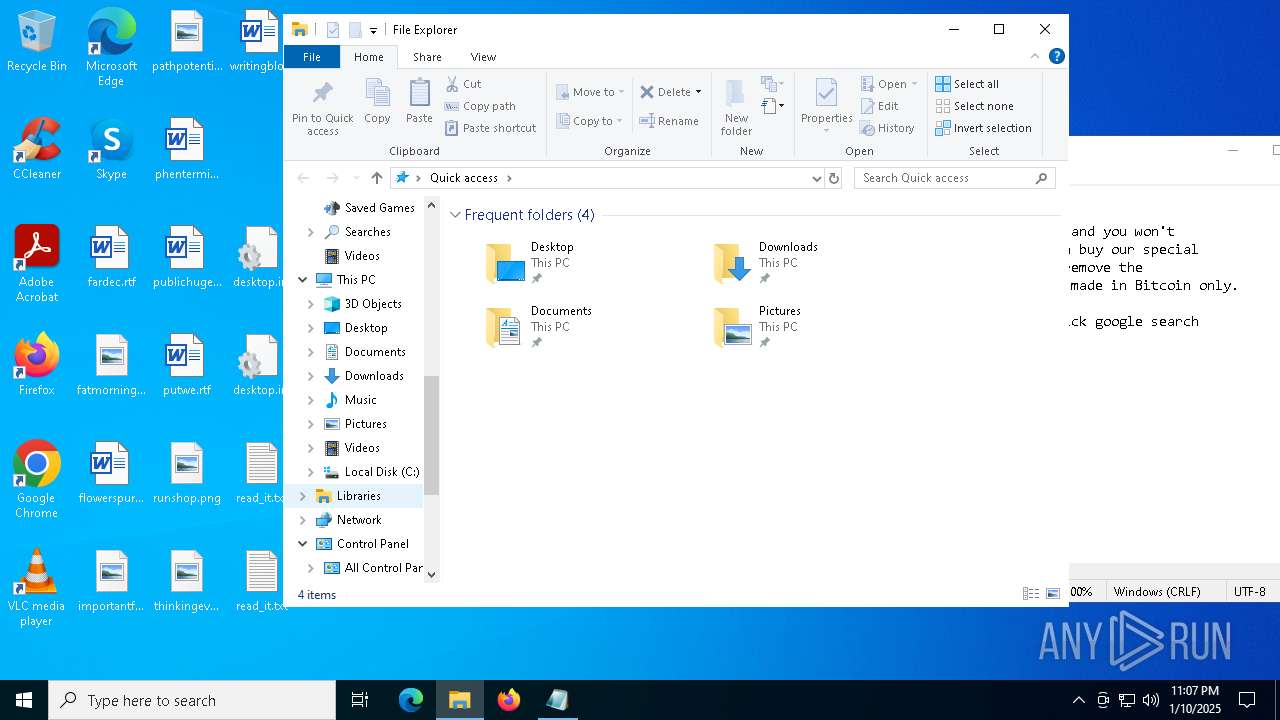
Deletes shadow copies
- cmd.exe (PID: 6076)
- cmd.exe (PID: 2612)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 3820)
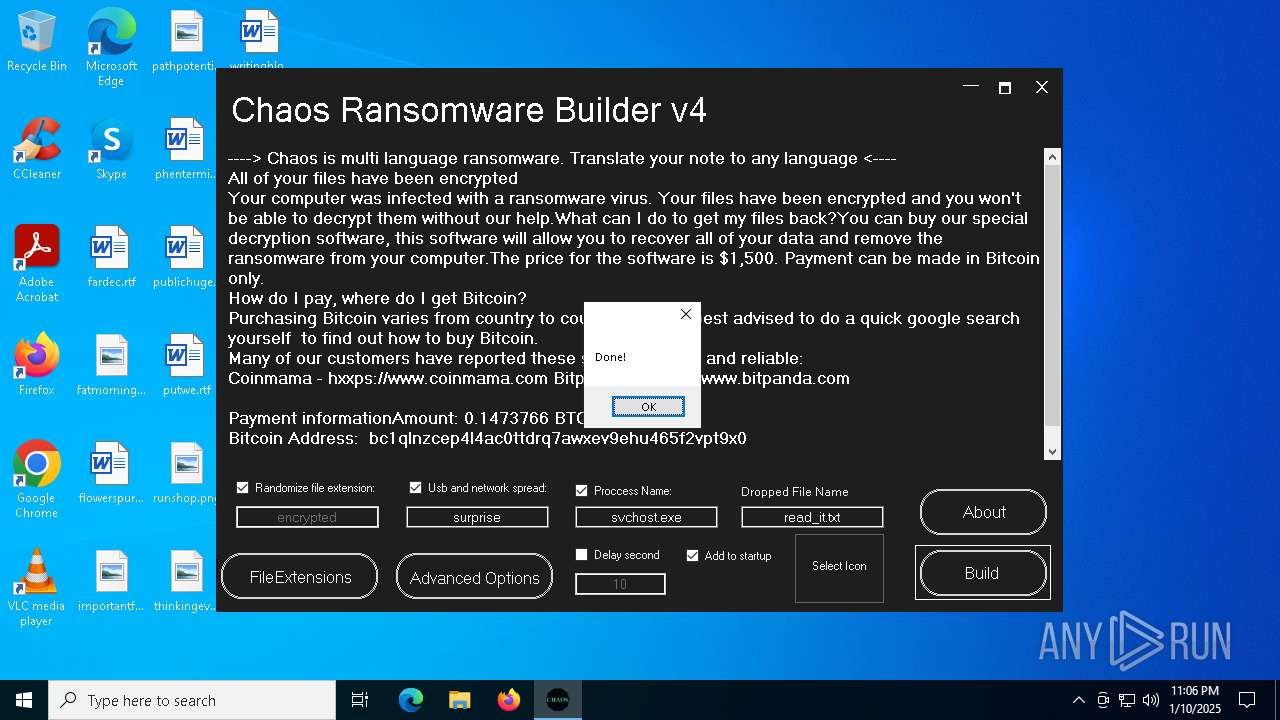
RANSOMWARE has been detected
- svchost.exe (PID: 7032)
Actions looks like stealing of personal data
- svchost.exe (PID: 7032)
SUSPICIOUS
Reads security settings of Internet Explorer
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- jhvjh.exe (PID: 4968)
- svchost.exe (PID: 7032)
- jhvjh.exe (PID: 6444)
Found regular expressions for crypto-addresses (YARA)
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- svchost.exe (PID: 7032)
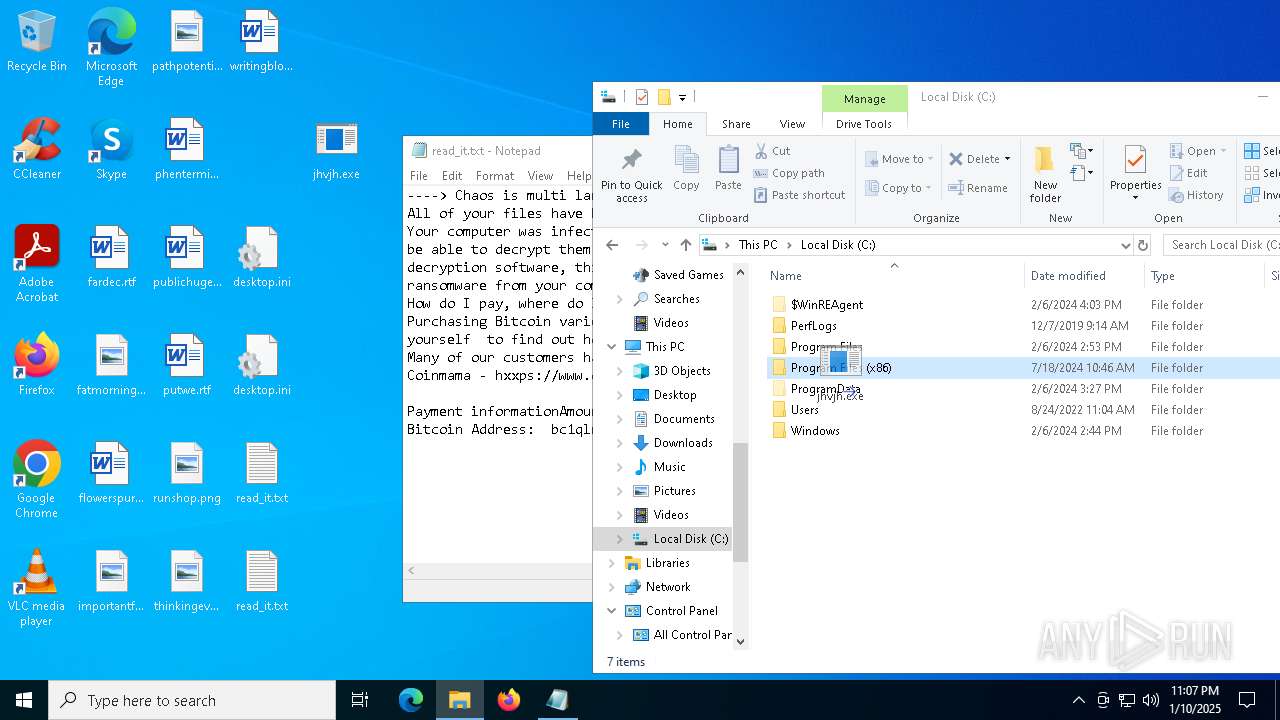
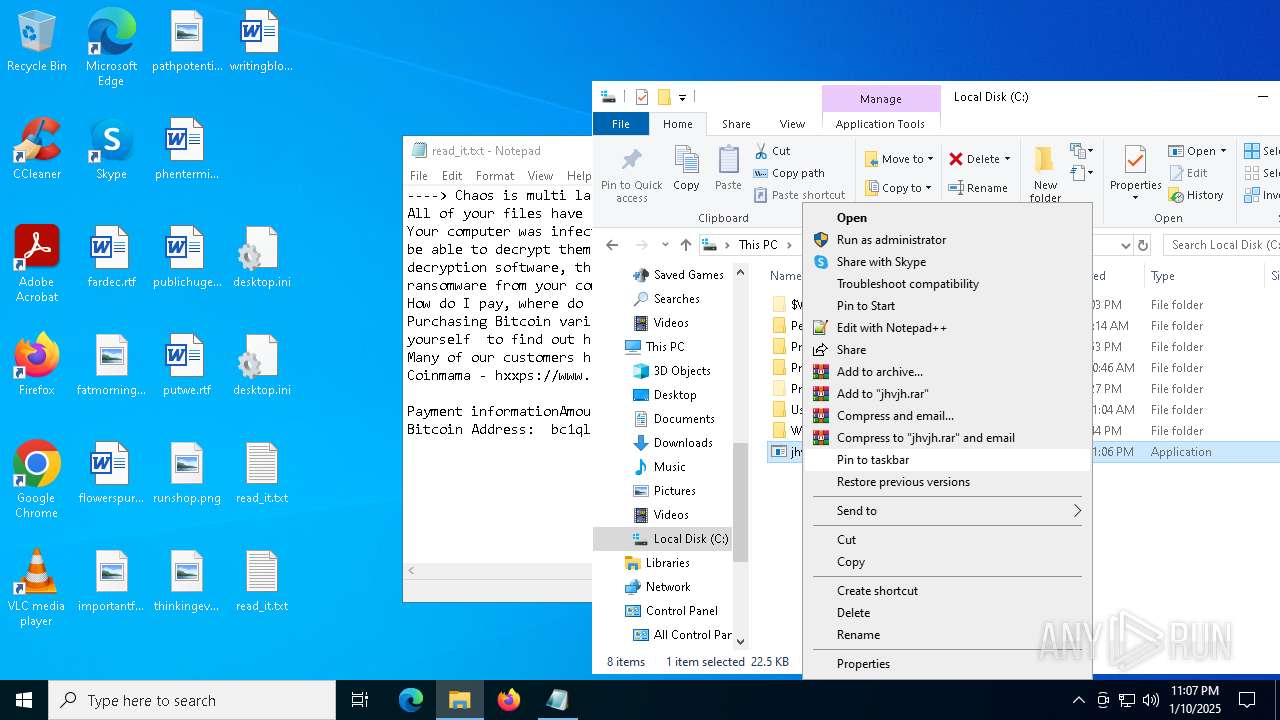
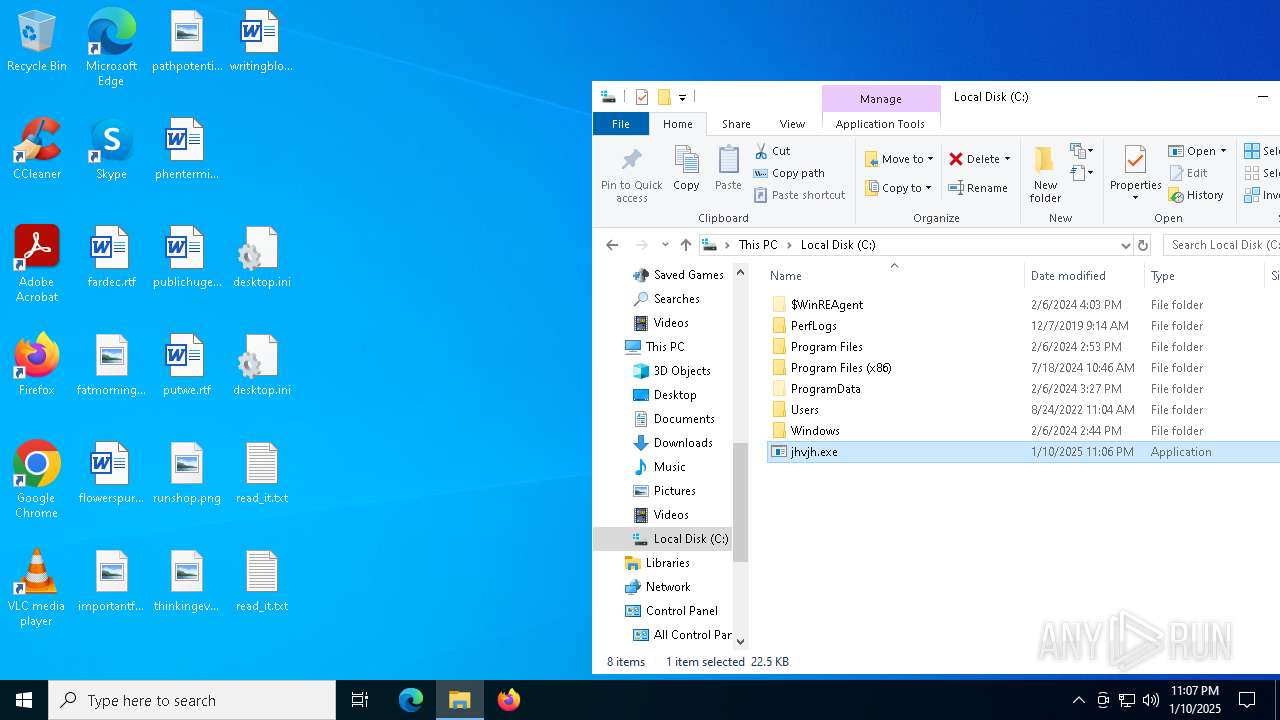
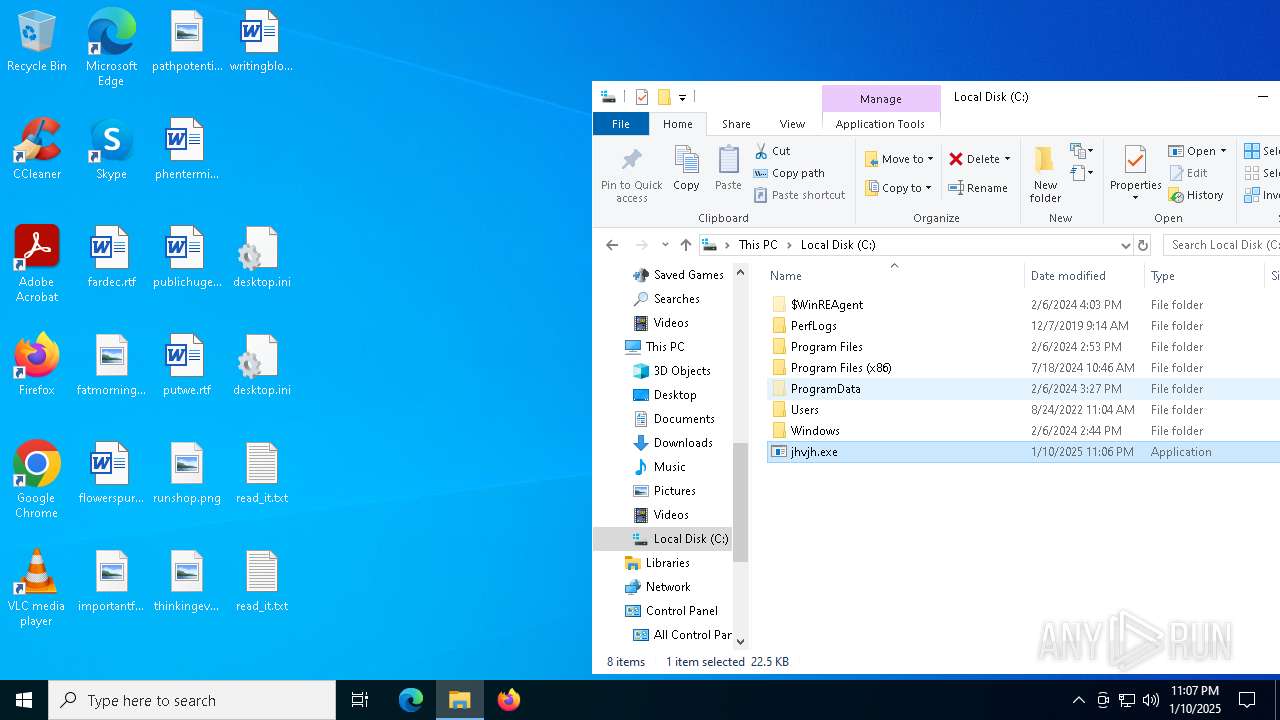
Executable content was dropped or overwritten
- csc.exe (PID: 2212)
- jhvjh.exe (PID: 4968)
- dllhost.exe (PID: 6532)
Executes as Windows Service
- VSSVC.exe (PID: 3612)
- wbengine.exe (PID: 4300)
- vds.exe (PID: 3640)
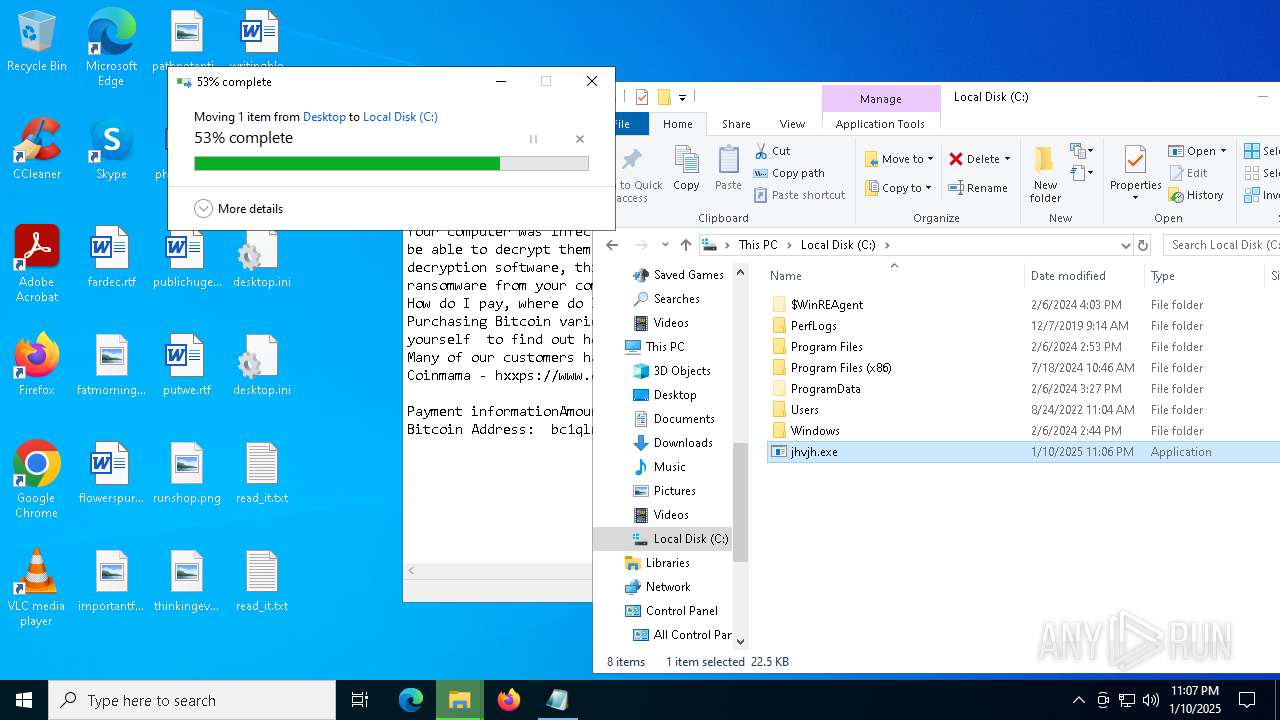
Starts itself from another location
- jhvjh.exe (PID: 4968)
- jhvjh.exe (PID: 6444)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 7032)
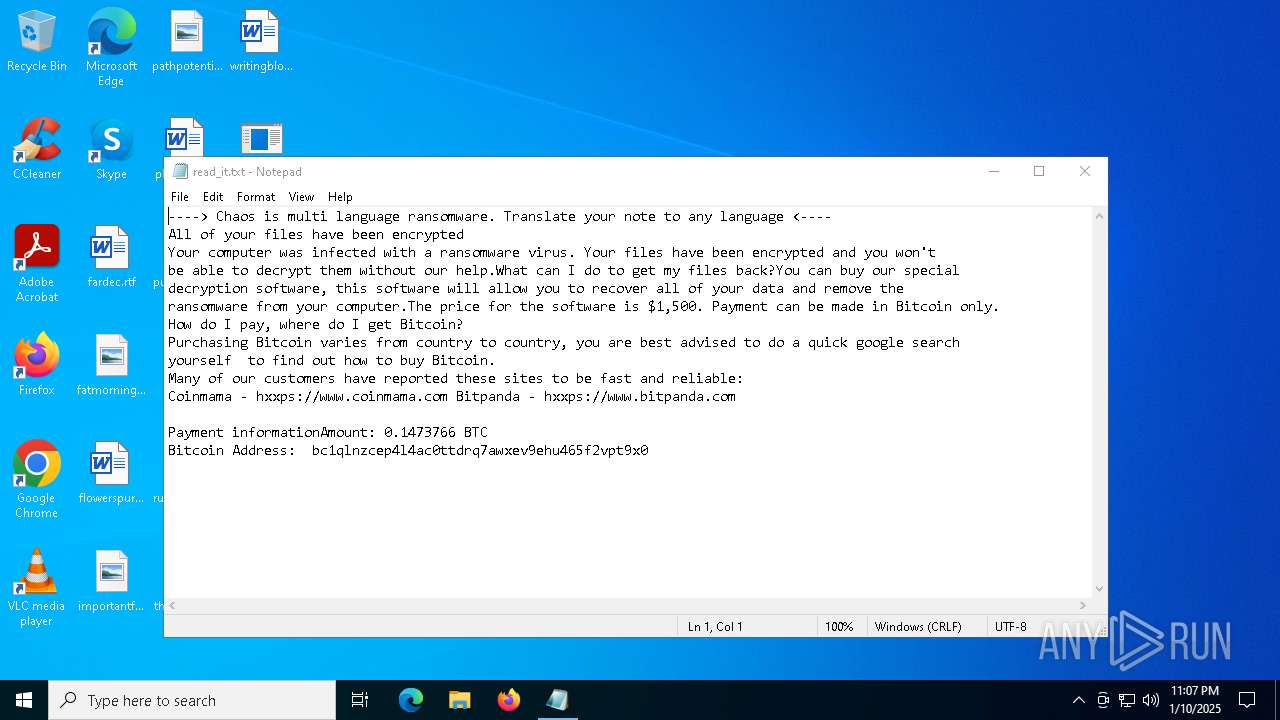
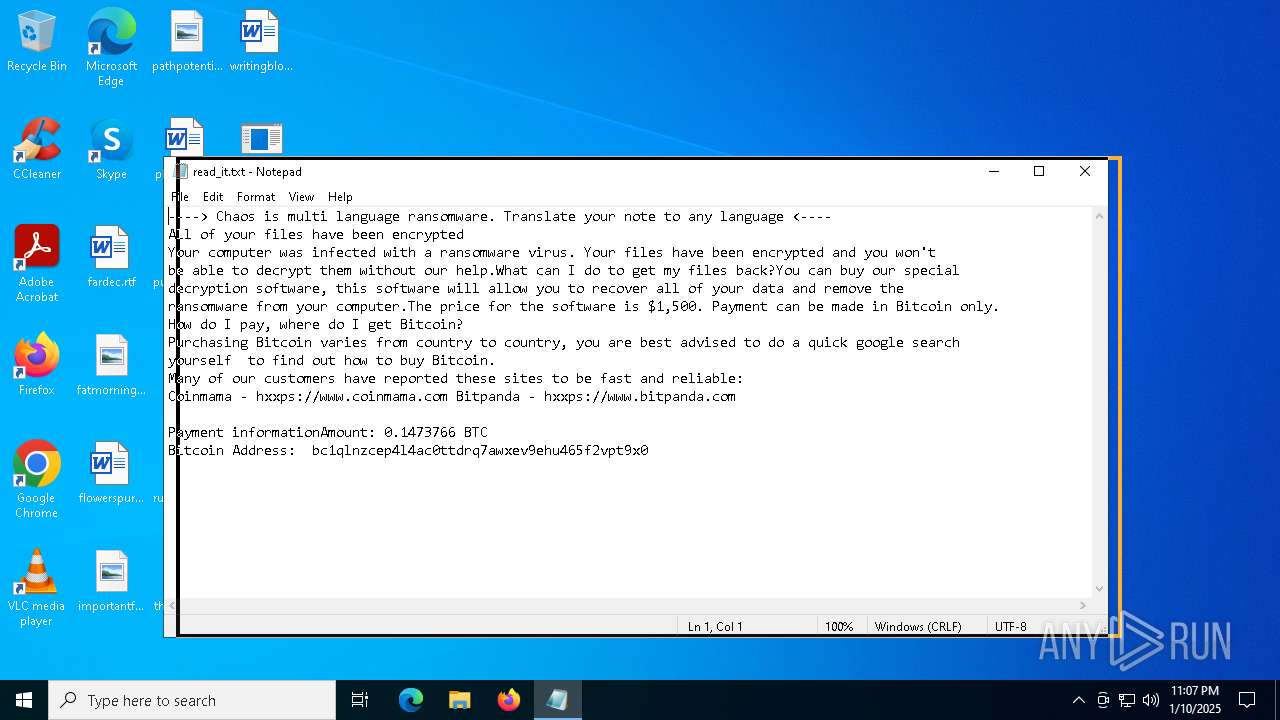
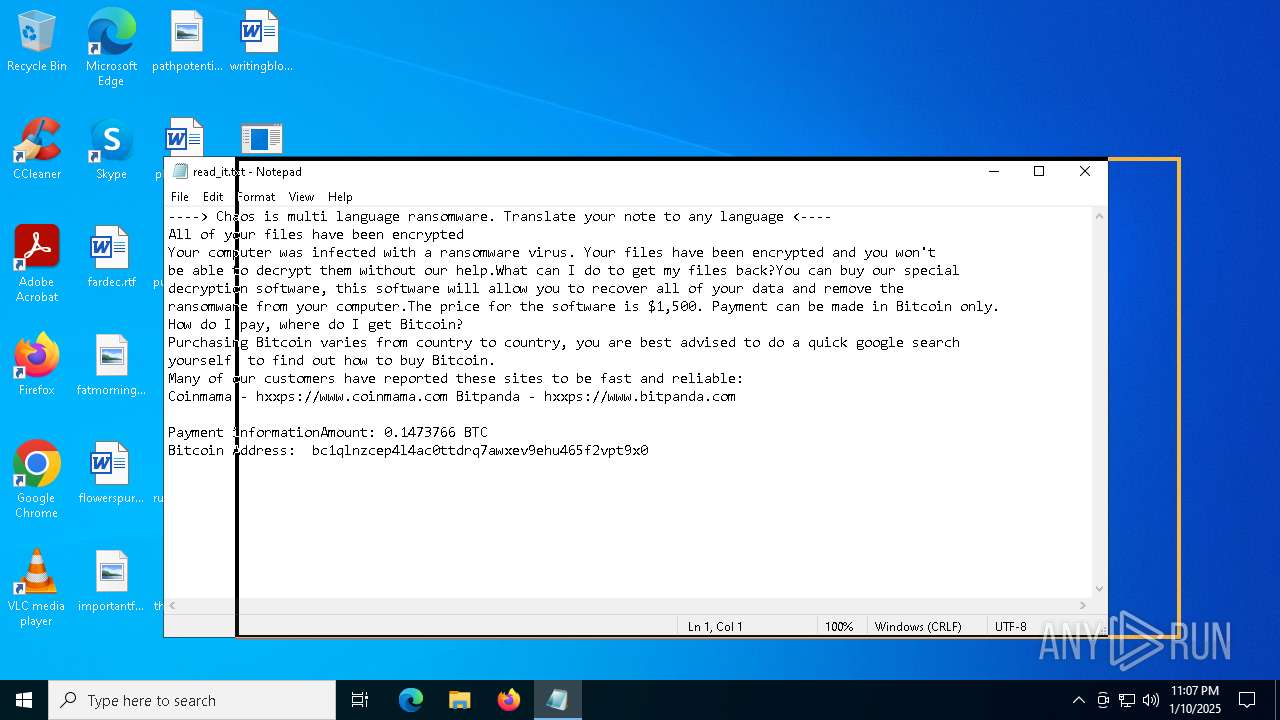
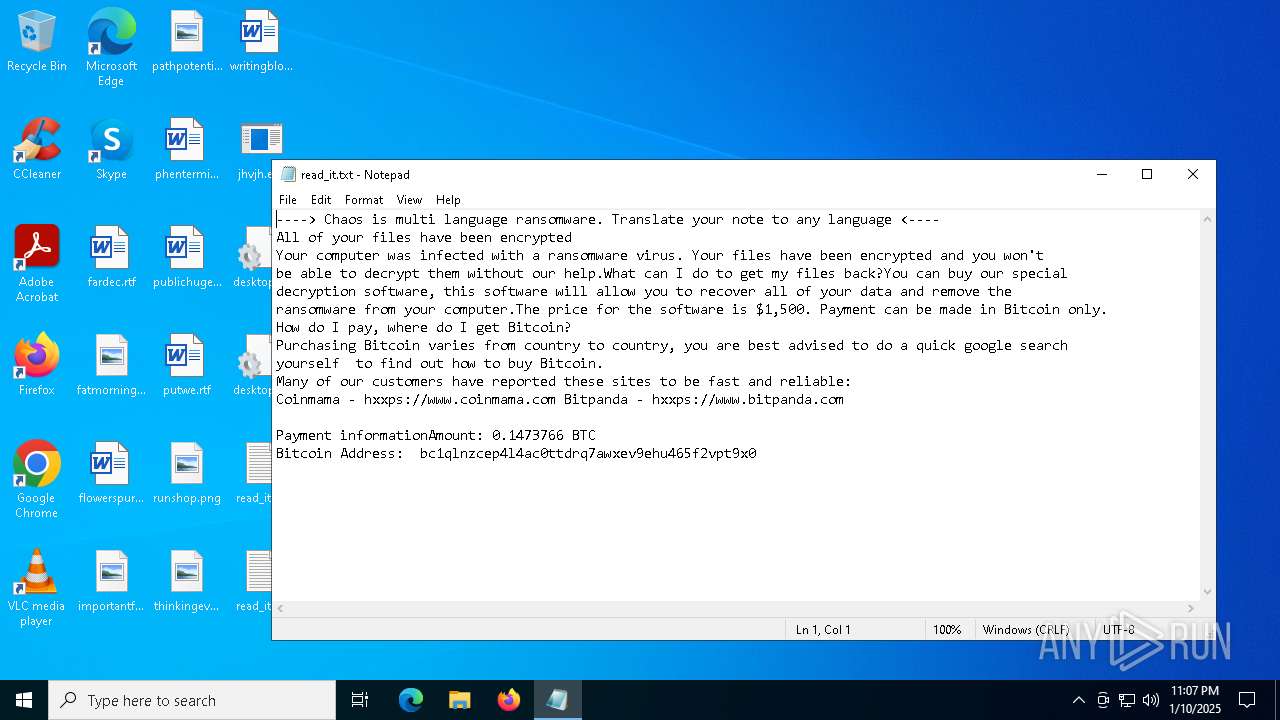
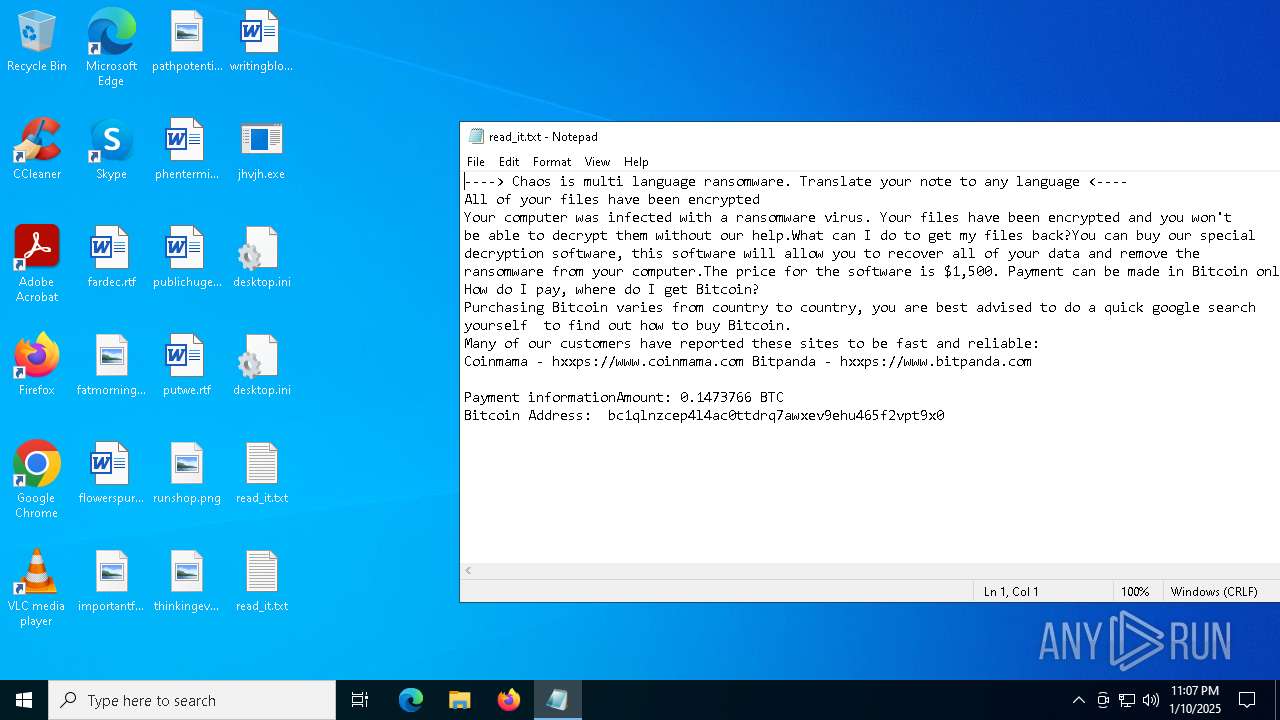
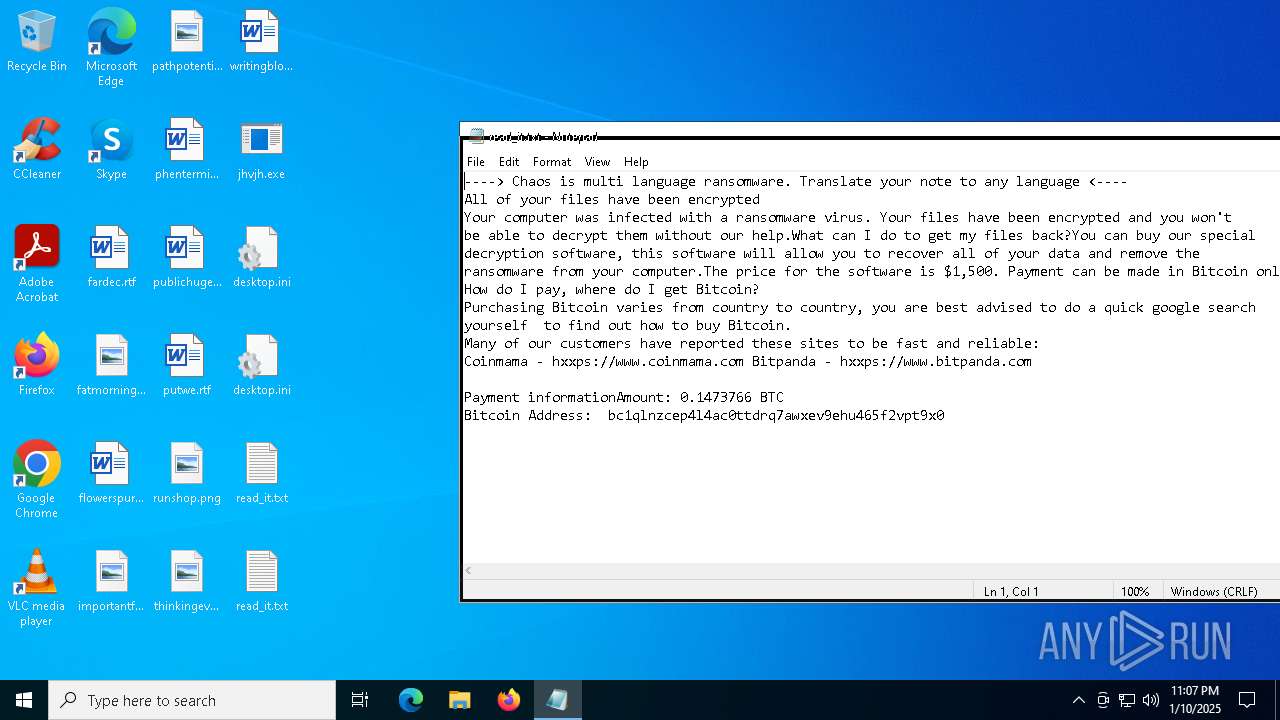
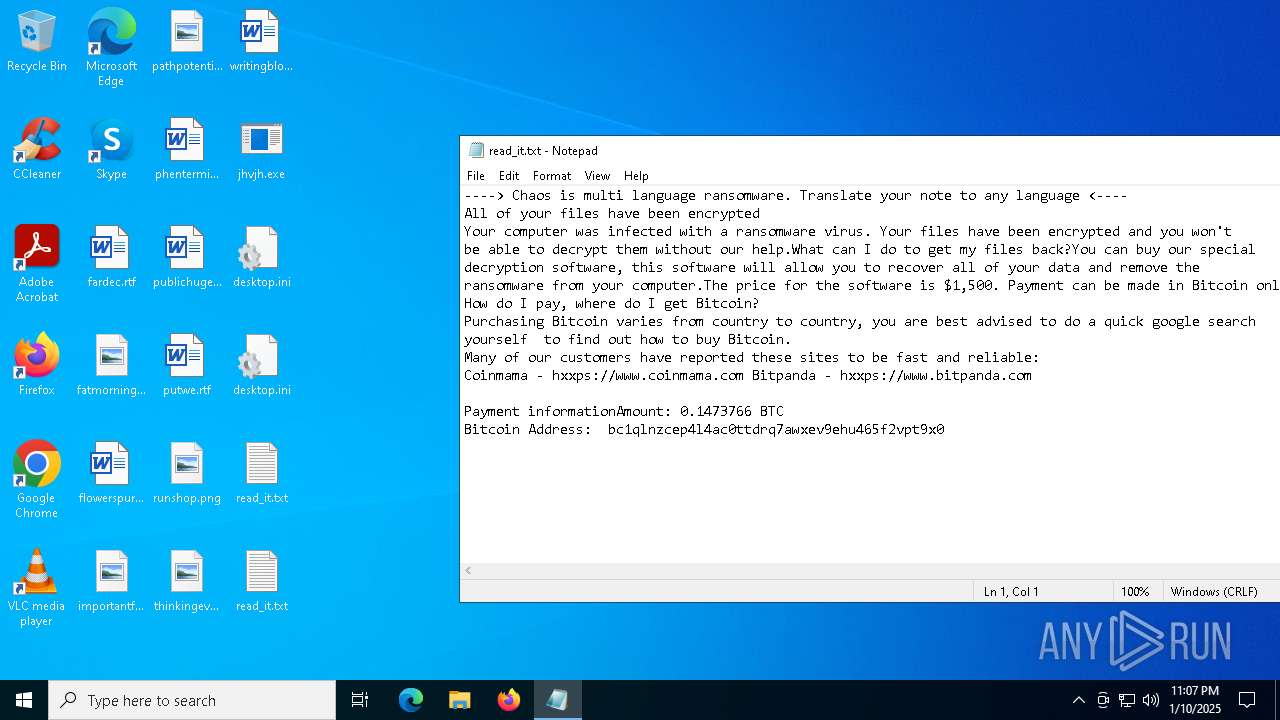
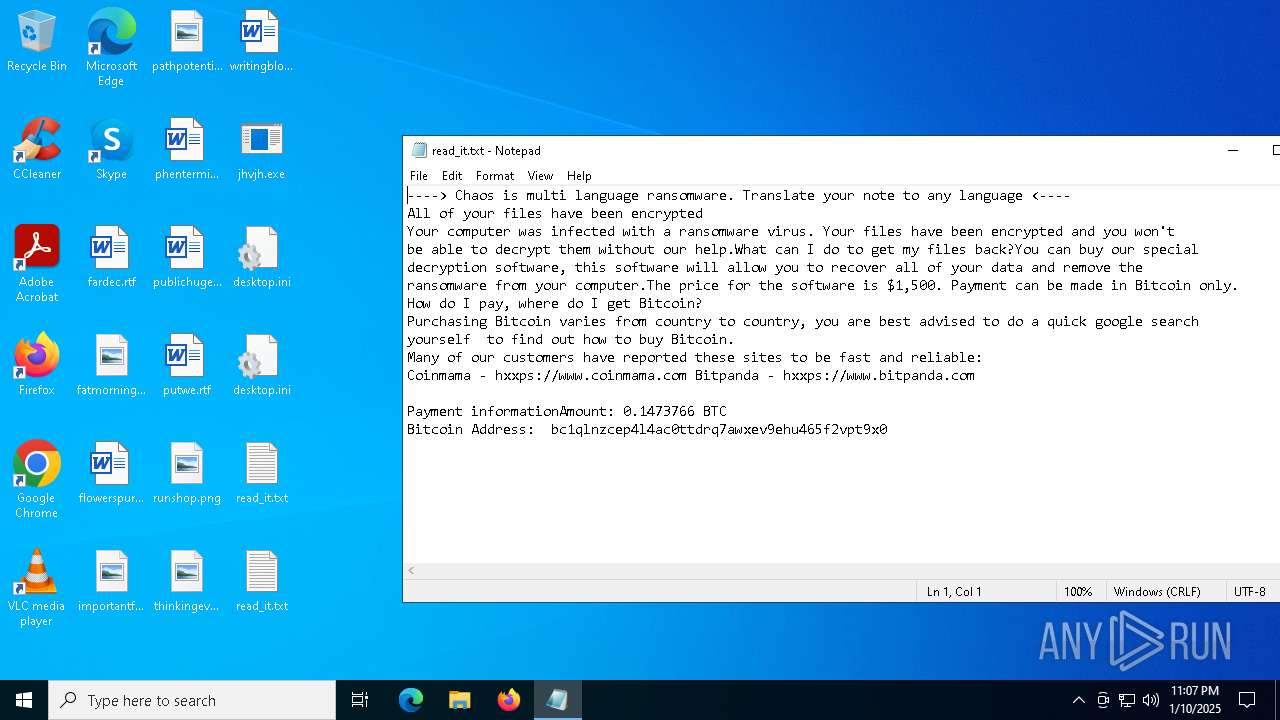
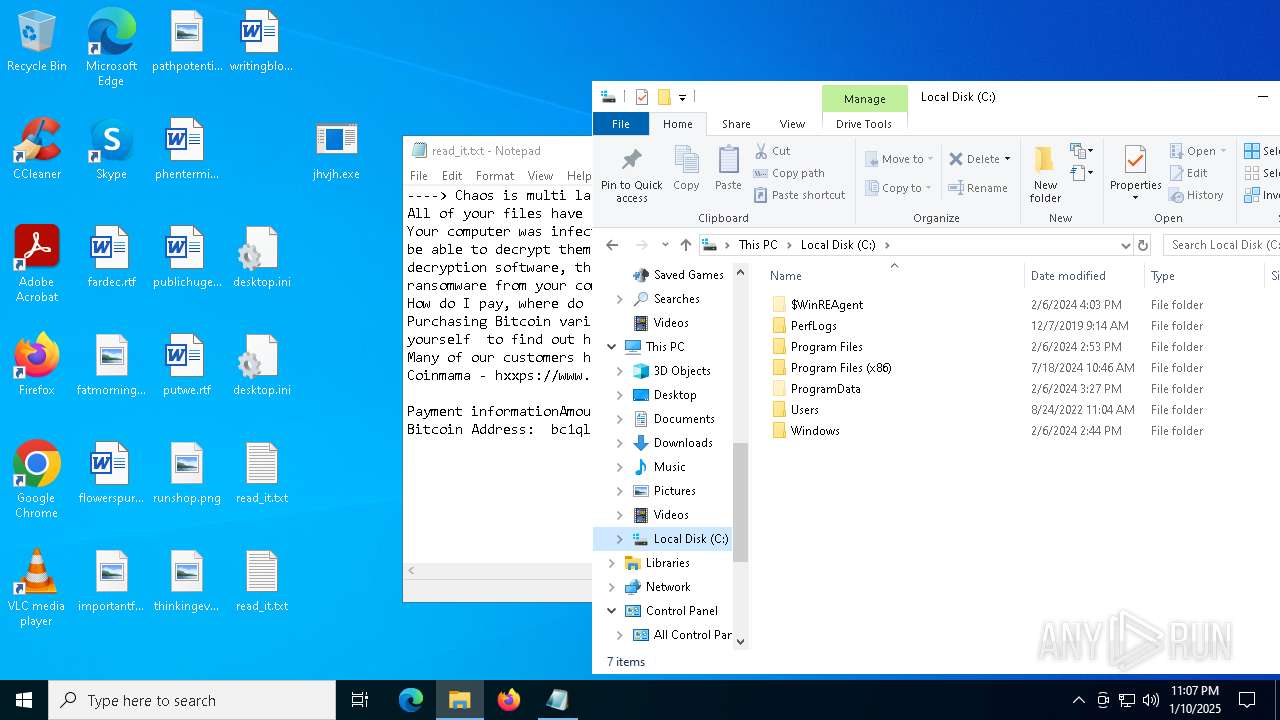
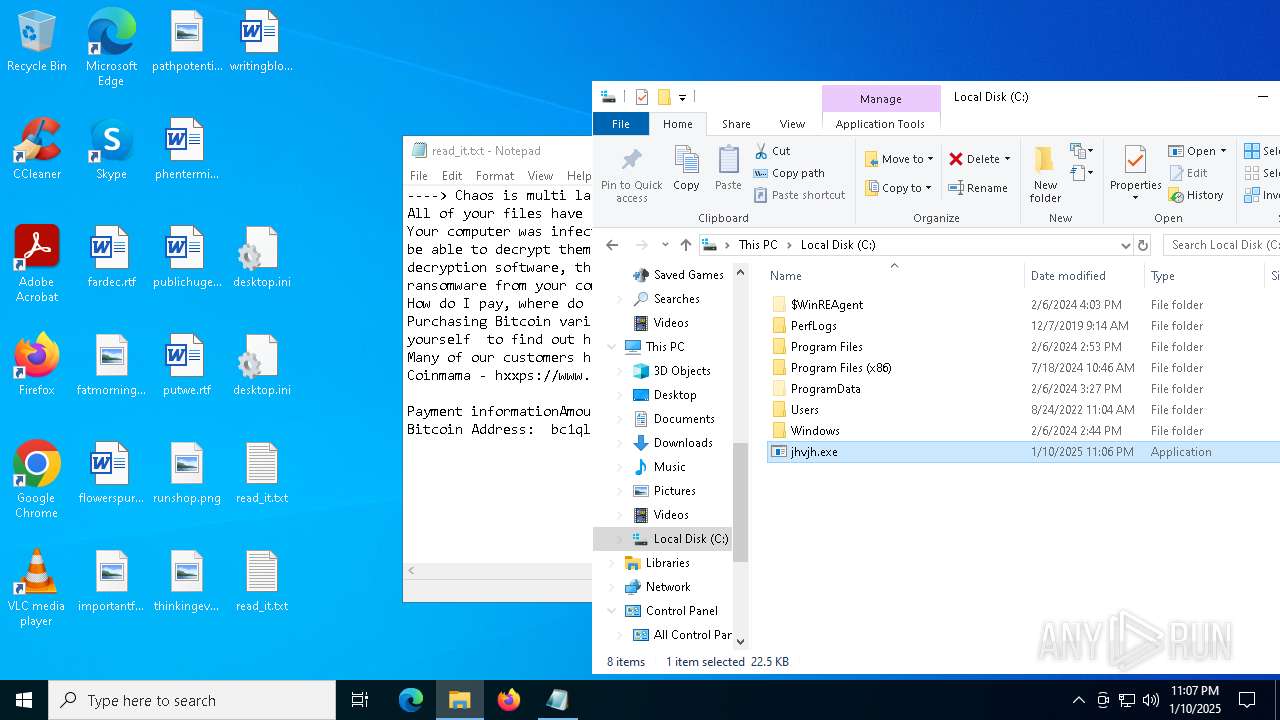
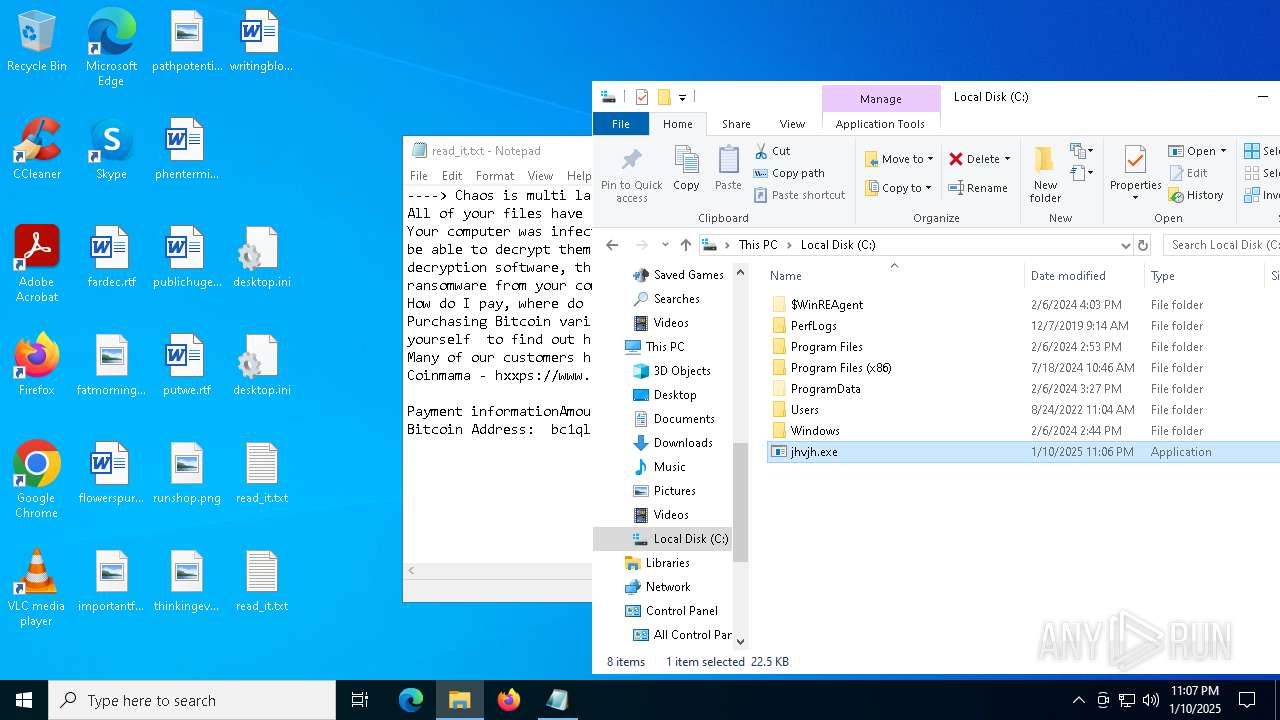
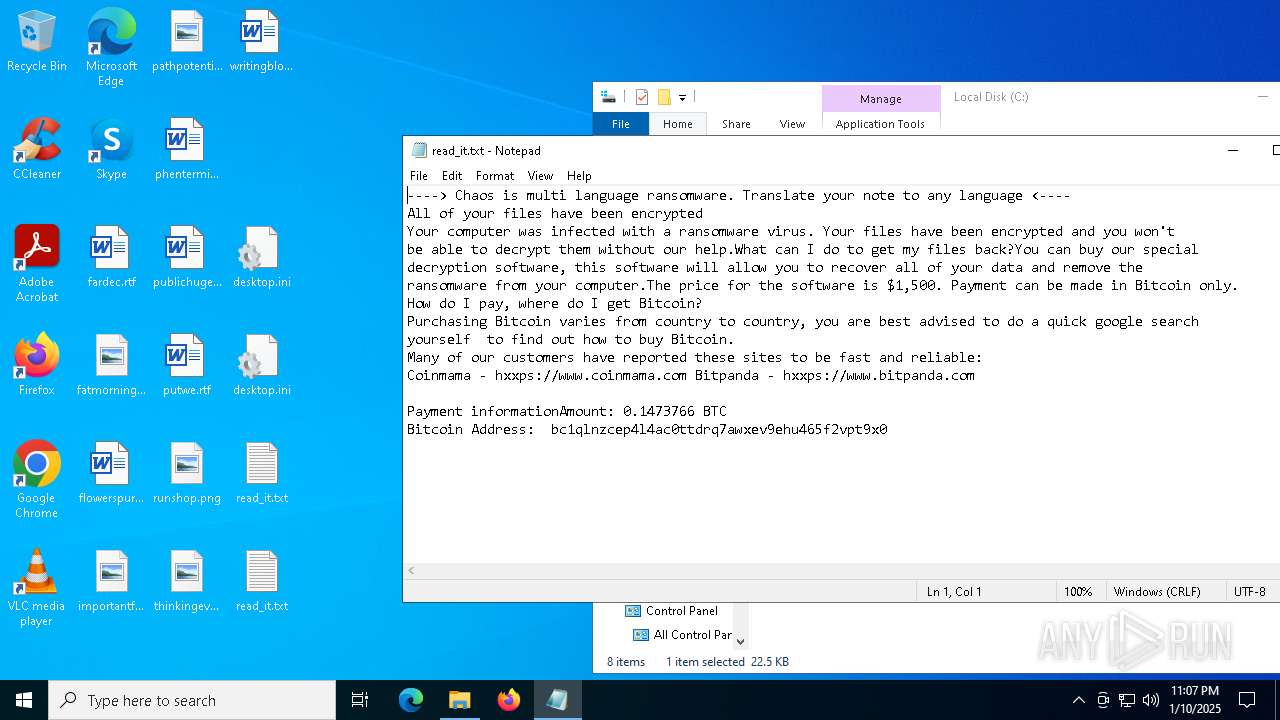
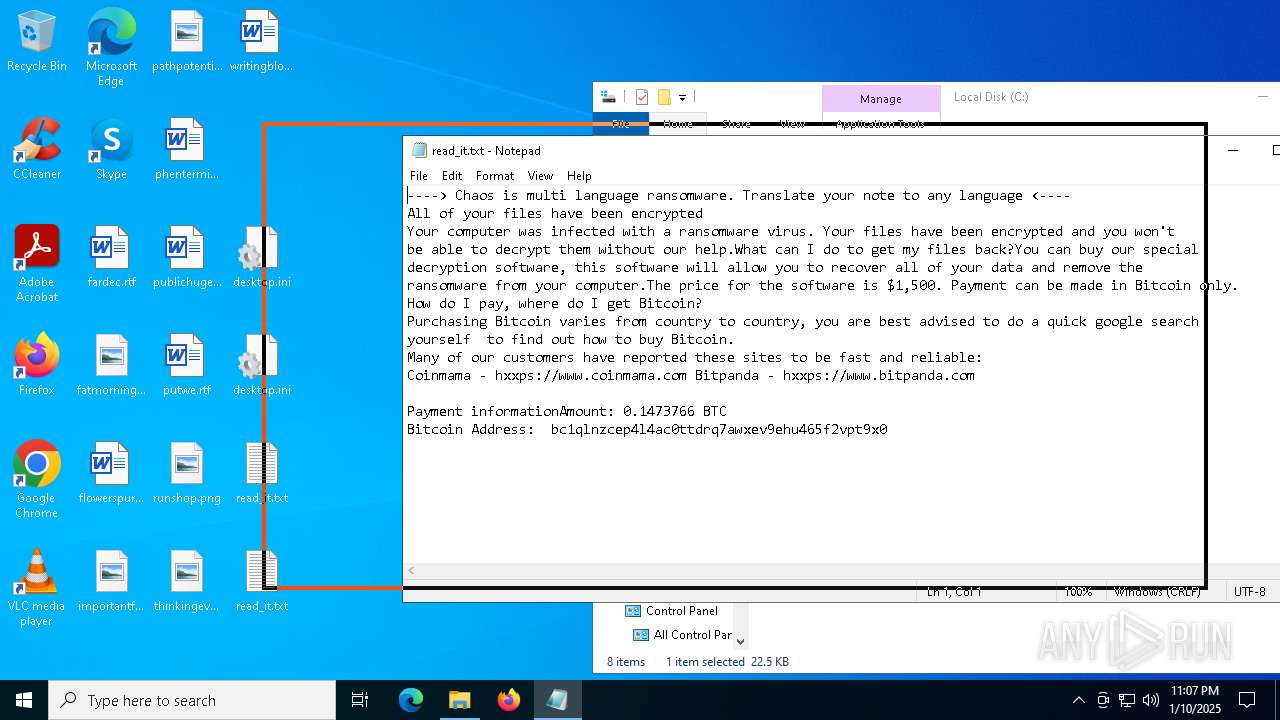
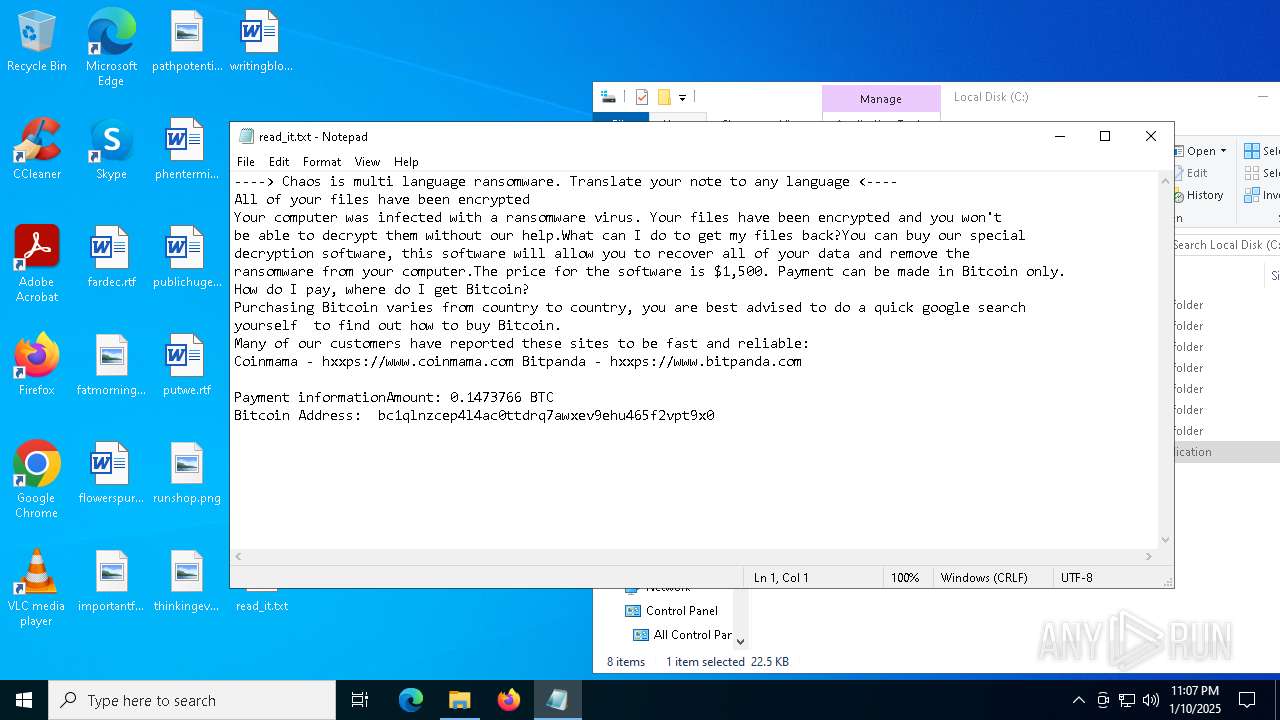
Start notepad (likely ransomware note)
- svchost.exe (PID: 7032)
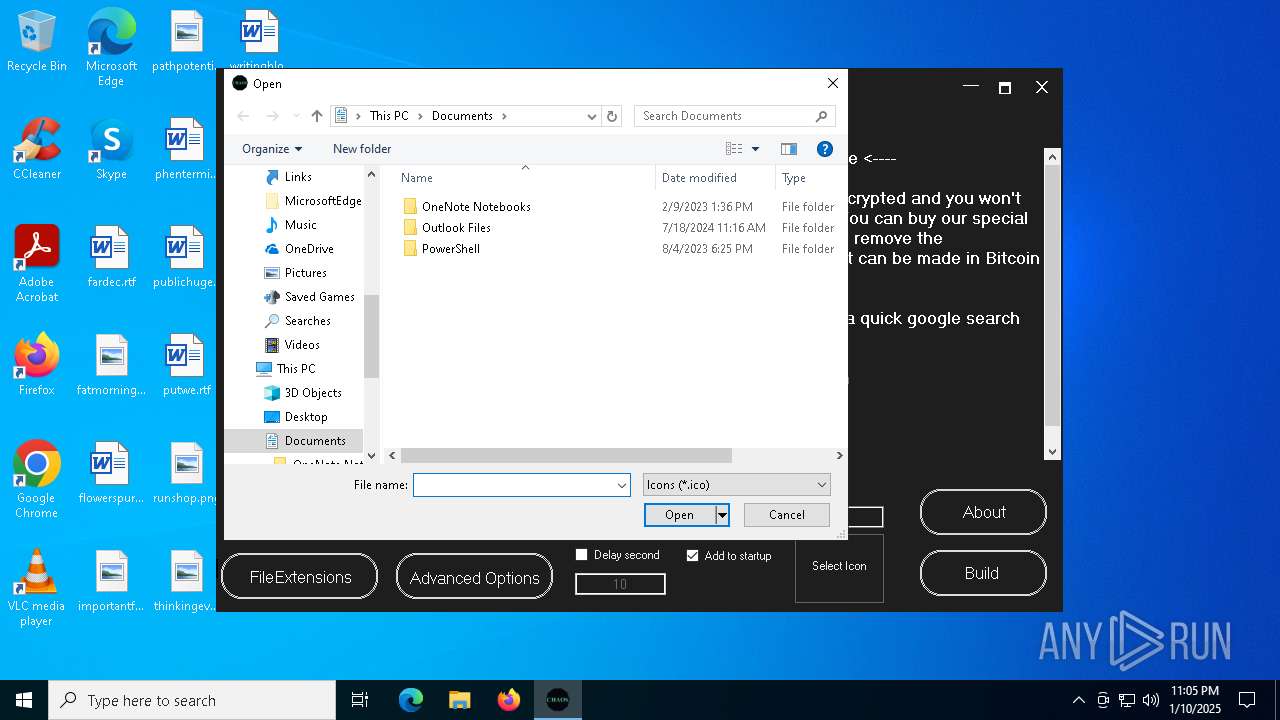
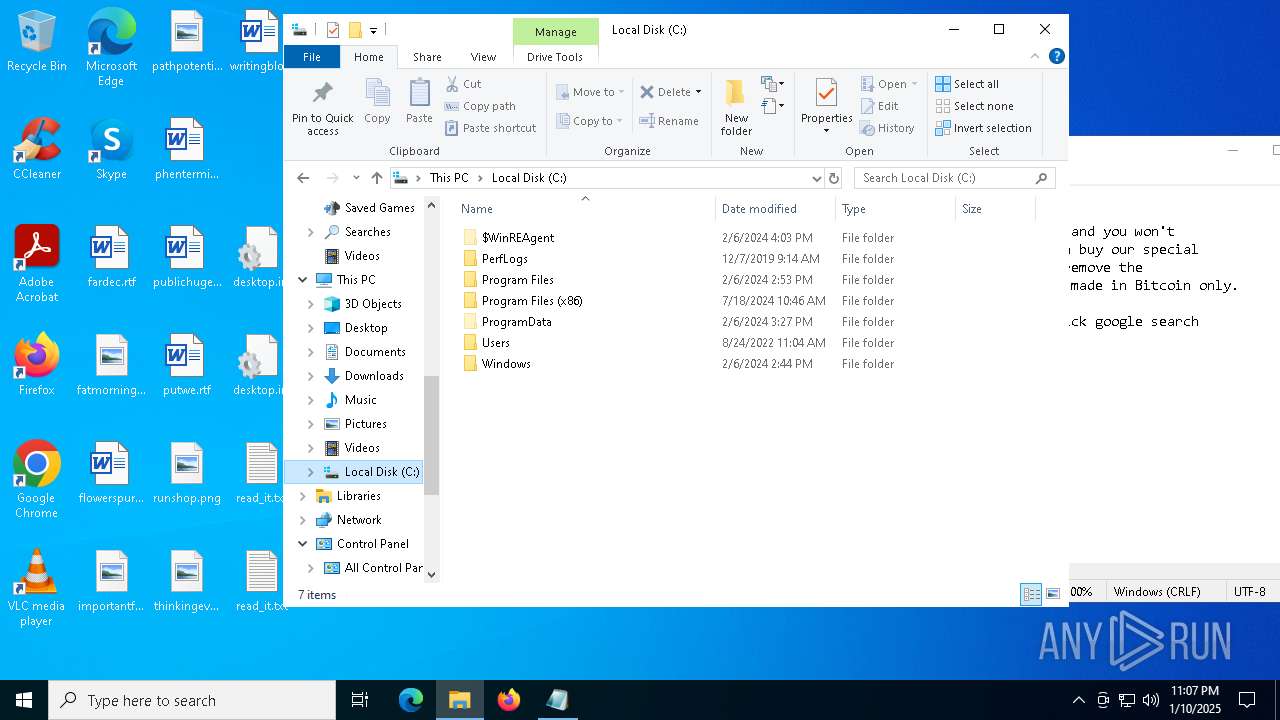
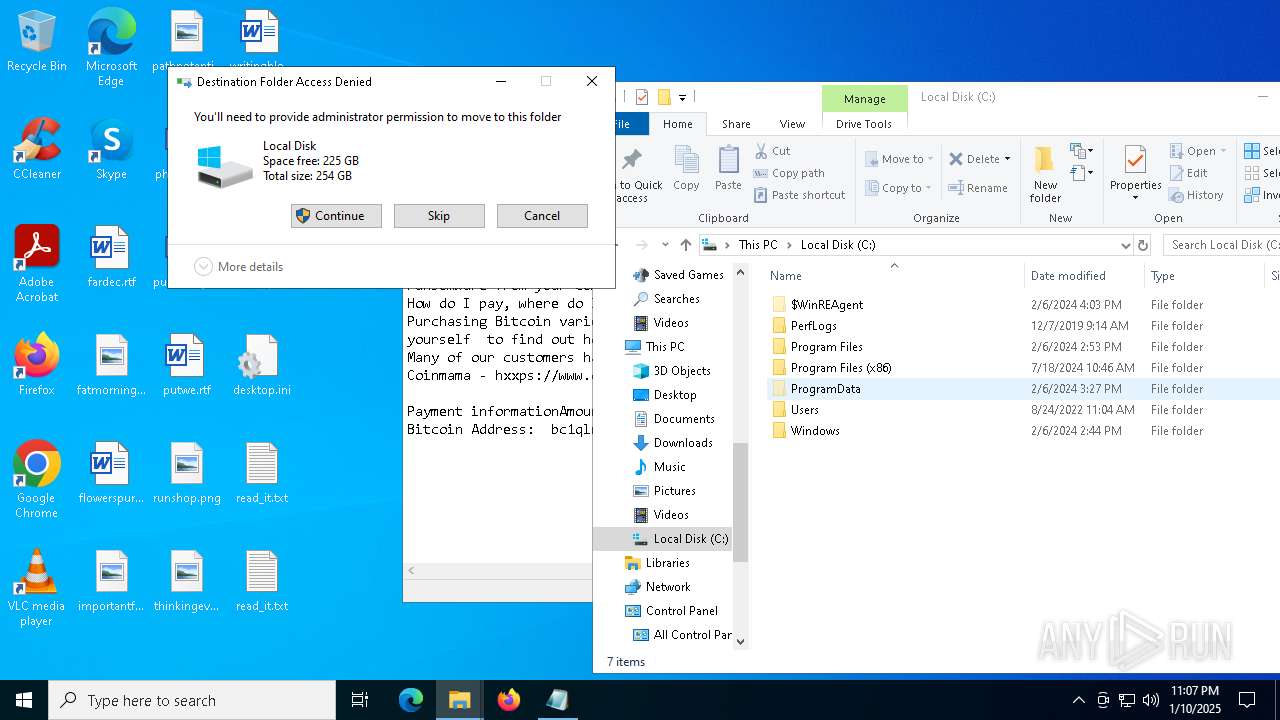
Creates file in the systems drive root
- dllhost.exe (PID: 6532)
- jhvjh.exe (PID: 6444)
Reads the date of Windows installation
- jhvjh.exe (PID: 6444)
INFO
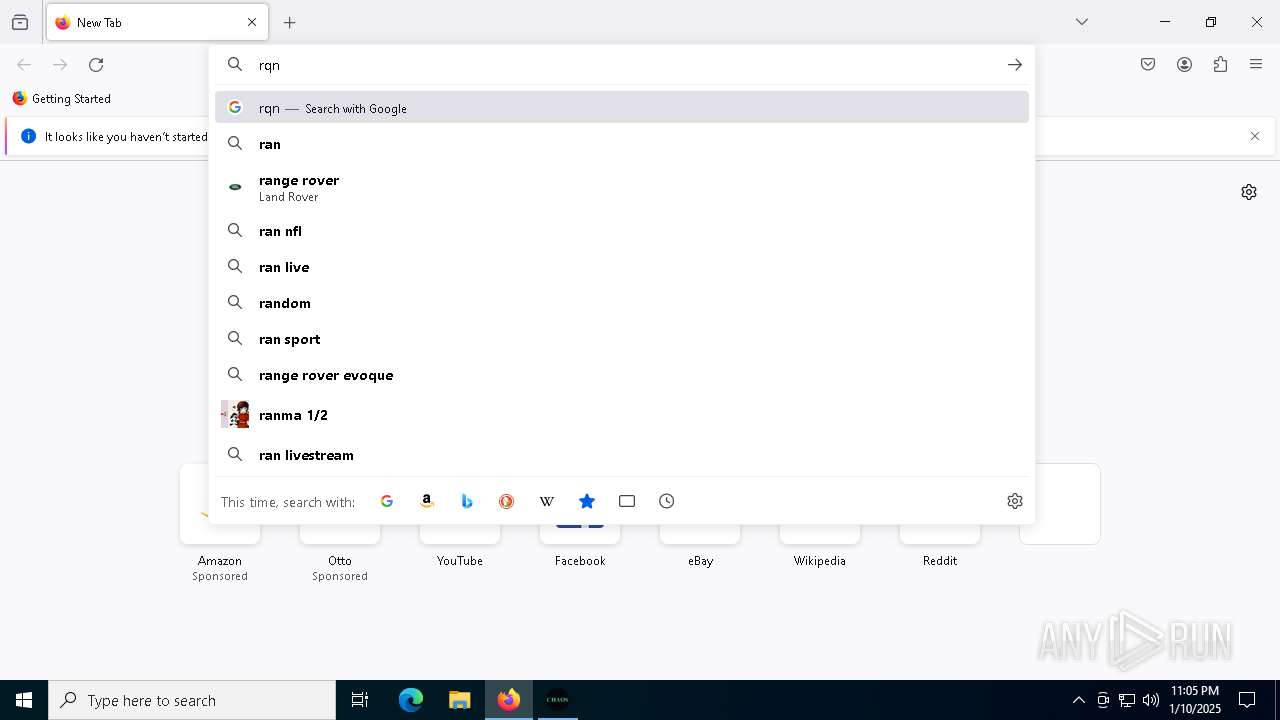
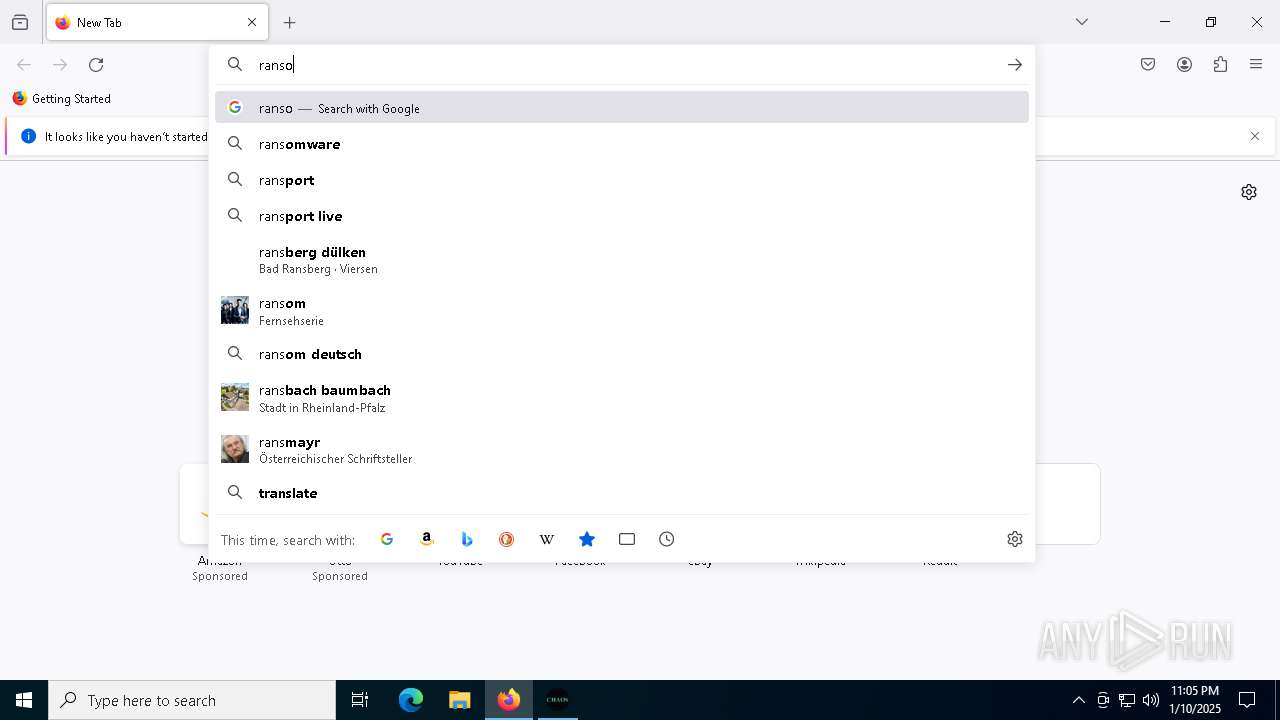
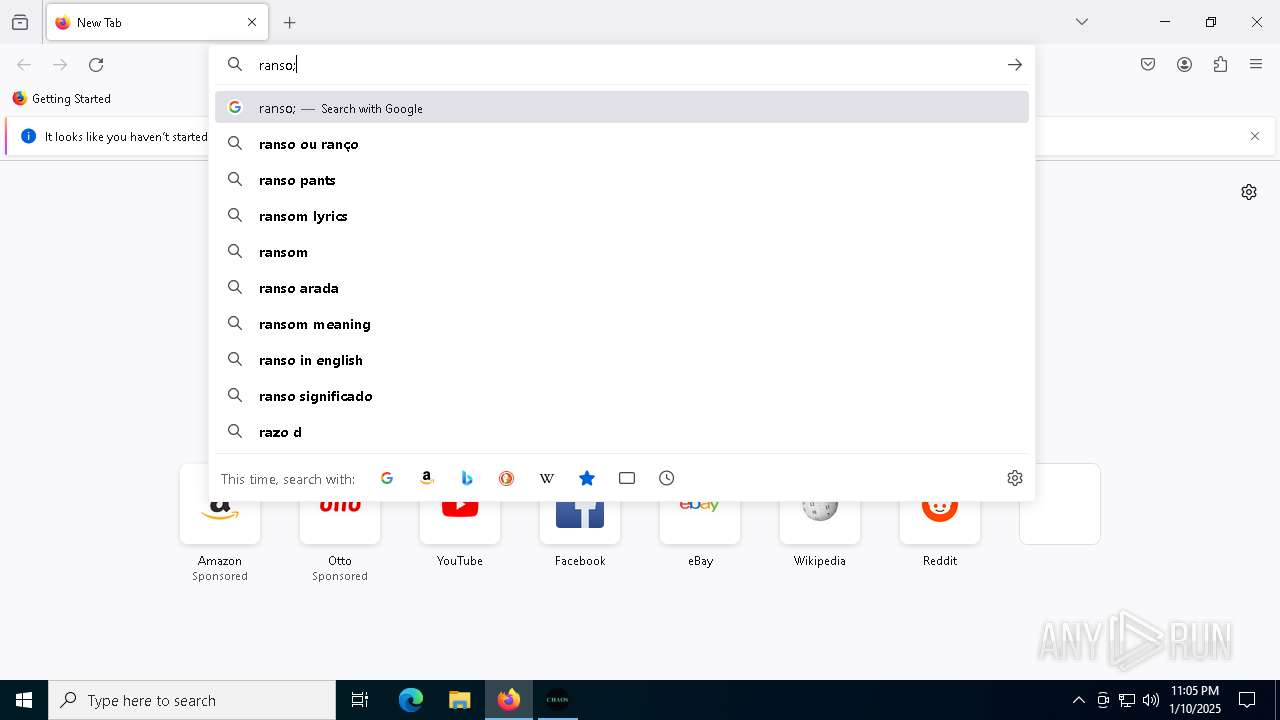
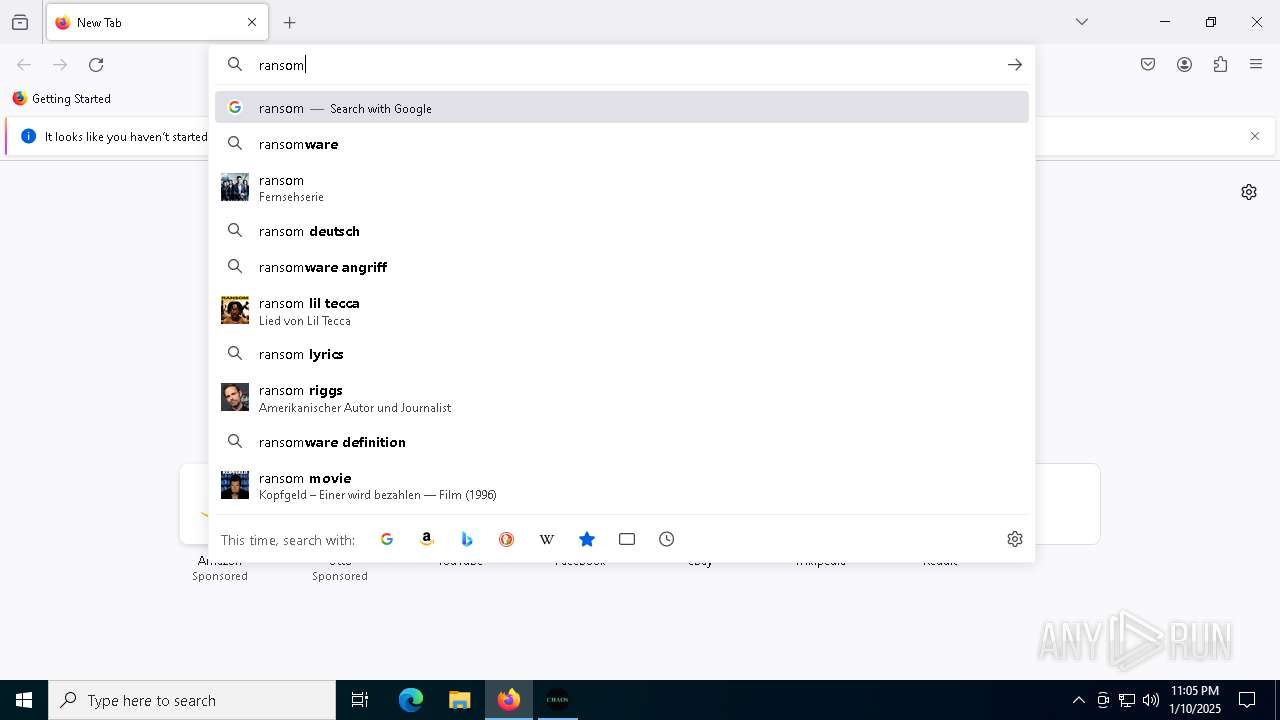
Manual execution by a user
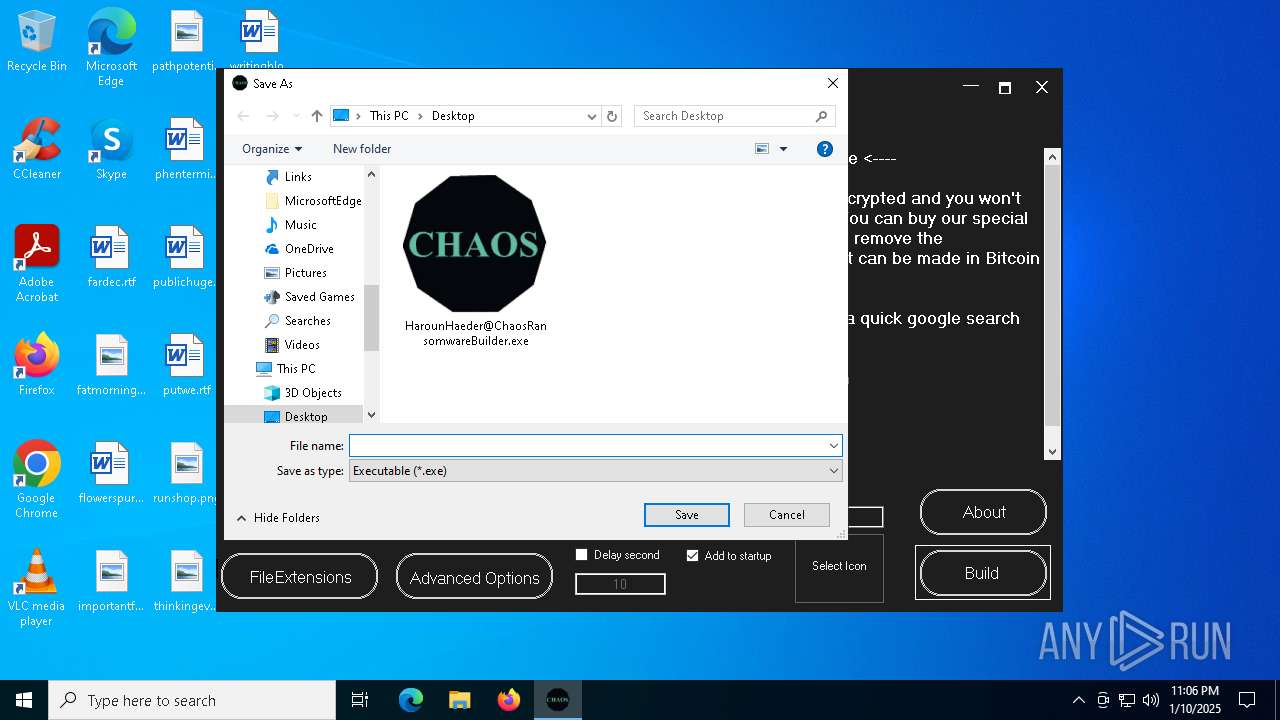
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7016)
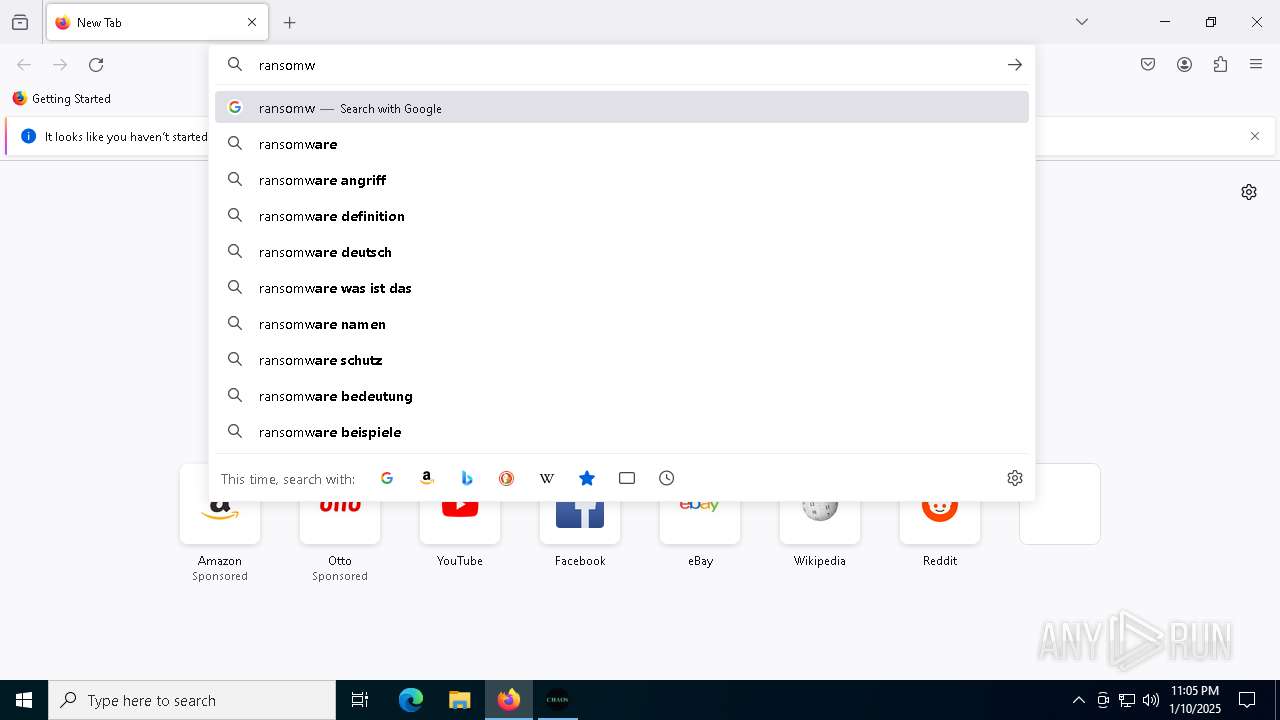
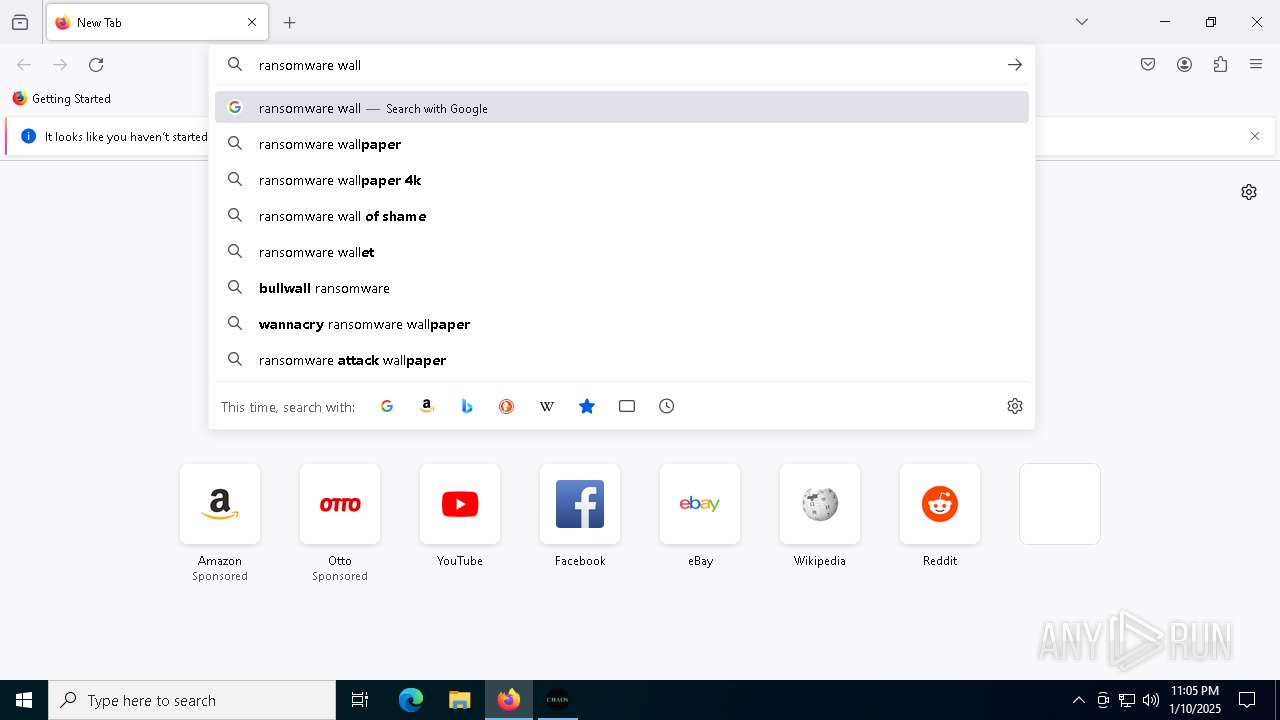
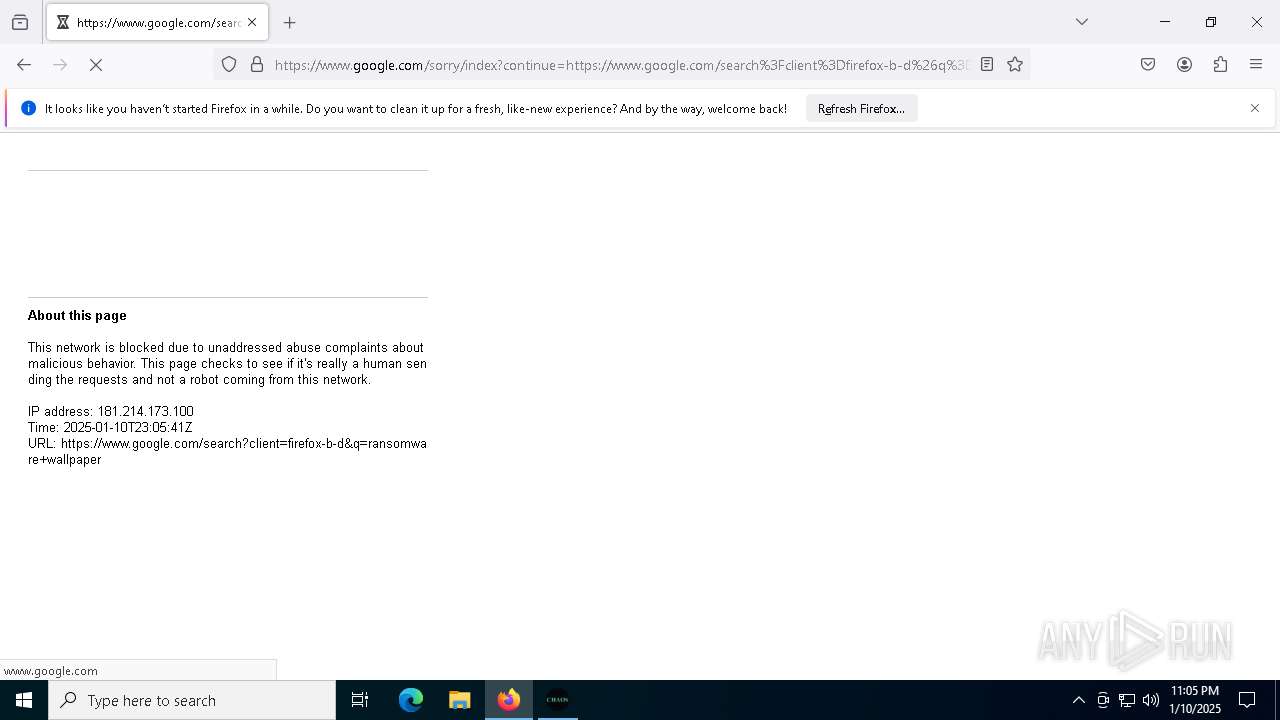
- firefox.exe (PID: 4764)
- jhvjh.exe (PID: 4968)
- jhvjh.exe (PID: 6444)
Reads the computer name
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- jhvjh.exe (PID: 4968)
- svchost.exe (PID: 3368)
The process uses the downloaded file
- WinRAR.exe (PID: 4504)
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- jhvjh.exe (PID: 4968)
- svchost.exe (PID: 7032)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4504)
Reads the machine GUID from the registry
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- csc.exe (PID: 2212)
- svchost.exe (PID: 7032)
Checks supported languages
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- csc.exe (PID: 2212)
- cvtres.exe (PID: 3984)
- jhvjh.exe (PID: 4968)
- svchost.exe (PID: 7032)
- jhvjh.exe (PID: 6444)
- svchost.exe (PID: 3368)
Application launched itself
- firefox.exe (PID: 4764)
- firefox.exe (PID: 5128)
Create files in a temporary directory
- HarounHaeder@ChaosRansomwareBuilder.exe (PID: 7084)
- cvtres.exe (PID: 3984)
Creates files or folders in the user directory
- svchost.exe (PID: 7032)
Process checks computer location settings
- svchost.exe (PID: 7032)
- jhvjh.exe (PID: 6444)
Sends debugging messages
- wbadmin.exe (PID: 6944)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2136)
- dllhost.exe (PID: 6532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
182
Monitored processes
44
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4128 -childID 6 -isForBrowser -prefsHandle 5648 -prefMapHandle 5700 -prefsLen 31324 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {111151b0-e362-4084-b689-162c8a1e4368} 5128 "\\.\pipe\gecko-crash-server-pipe.5128" 27c03cc84d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6524 -childID 12 -isForBrowser -prefsHandle 5764 -prefMapHandle 6220 -prefsLen 32060 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {8e7513f5-d109-4b65-b3e7-7c43116f11d4} 5128 "\\.\pipe\gecko-crash-server-pipe.5128" 27c03240310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 640 | bcdedit /set {default} recoveryenabled no | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 648 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5152 -childID 4 -isForBrowser -prefsHandle 5228 -prefMapHandle 5232 -prefsLen 31251 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {50ab33a5-b385-46b2-a2f4-1e30ec0482f9} 5128 "\\.\pipe\gecko-crash-server-pipe.5128" 27c050febd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2124 | wmic shadowcopy delete | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\read_it.txt | C:\Windows\System32\notepad.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\mvc4432l\mvc4432l.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | HarounHaeder@ChaosRansomwareBuilder.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2612 | "C:\Windows\System32\cmd.exe" /C wbadmin delete catalog -quiet | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 415
Read events
29 267
Write events
127
Delete events
21
Modification events
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Chaos Ransomware Builder.7z | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (4504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
4
Suspicious files
210
Text files
127
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5128 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5128 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 4504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4504.8897\HarounHaeder@ChaosRansomwareBuilder.exe | executable | |
MD5:8B855E56E41A6E10D28522A20C1E0341 | SHA256:F2665F89BA53ABD3DEB81988C0D5194992214053E77FC89B98B64A31A7504D77 | |||
| 5128 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5128 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5128 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5128 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5128 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 5128 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:39C0766F085F52FBB00483893939251C | SHA256:5DB9B07845FCCCE4F3ECAE5BA8183FDA846191903111AAB6D0954179F80856EC | |||
| 5128 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:7864FF2635881D25B5BD3B56B2FB15AC | SHA256:DE11BB746171FC7CEEBE0F606184479C2D28C9ED65D7ACA80D7C2C62E24E0D02 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
206
DNS requests
233
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7136 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5128 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5128 | firefox.exe | POST | 200 | 2.16.206.143:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5128 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
5128 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/jLM | unknown | — | — | whitelisted |
5128 | firefox.exe | POST | 200 | 2.16.206.143:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5128 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5128 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5128 | firefox.exe | POST | 200 | 2.16.206.143:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5128 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.16.204.149:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|