| File name: | roblox.exe |
| Full analysis: | https://app.any.run/tasks/9f287ad2-98c6-49d0-9e9b-0fc35cd64fd8 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | February 21, 2026, 20:55:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 16 sections |
| MD5: | EAA99B78A54AB8F56751C033C2FC3B57 |
| SHA1: | 05501D42F508A72EEC30D51459A73A7377B55502 |
| SHA256: | 25FDB1DF13C9B81950CCA03453BA602D830D190A126571987CD6A01E7F033C53 |
| SSDEEP: | 98304:eYfbvircSrdPAasOtzidgNaGt9U4gWdCaOhdFr/9XKLOlOpY0AaJdzIulpJRqwZq:Kzx1/xd |
MALICIOUS
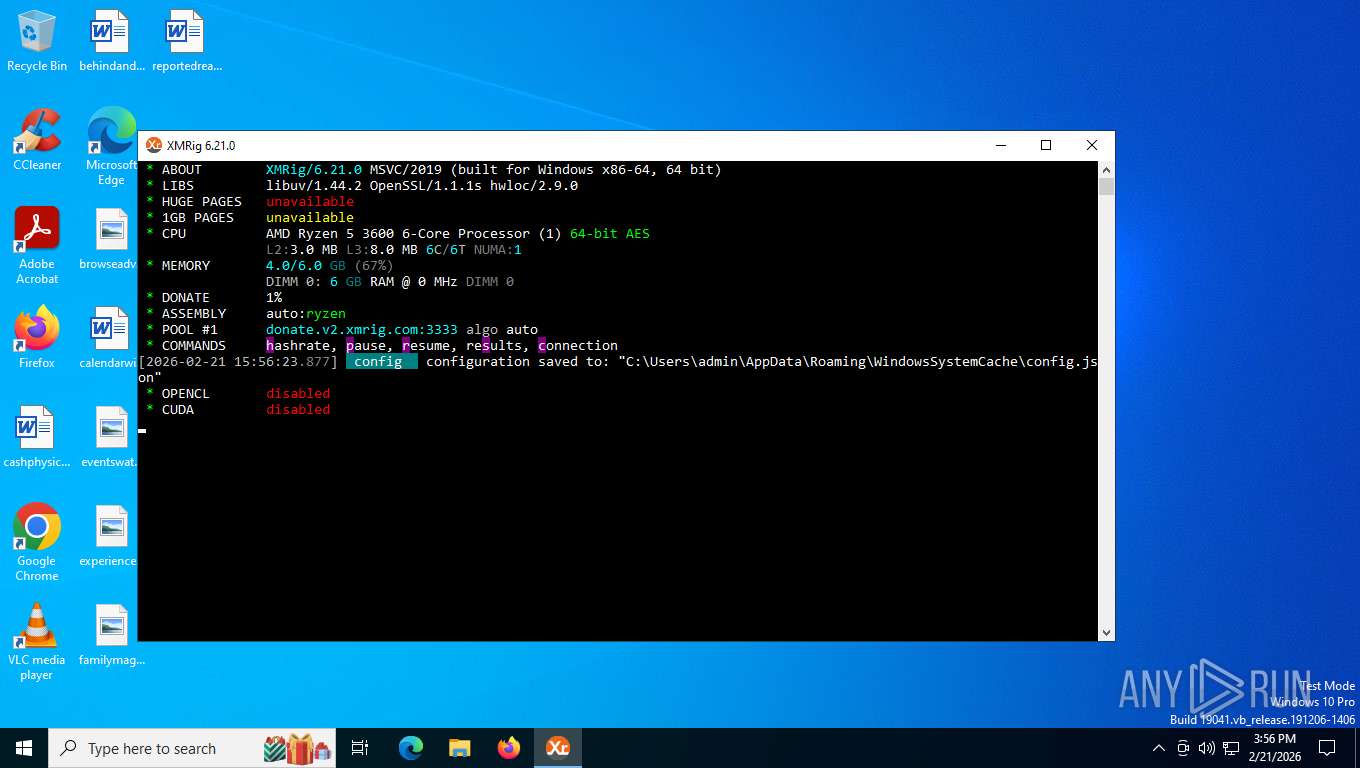
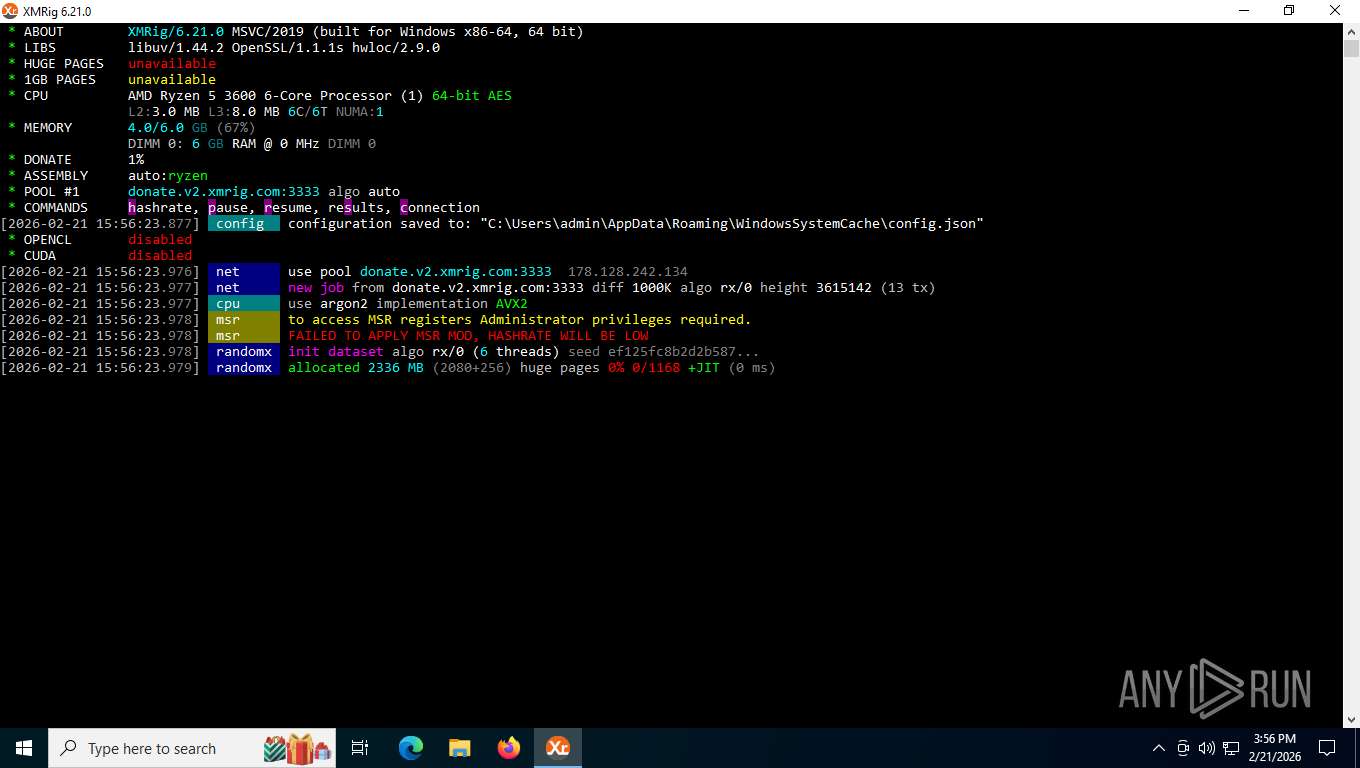
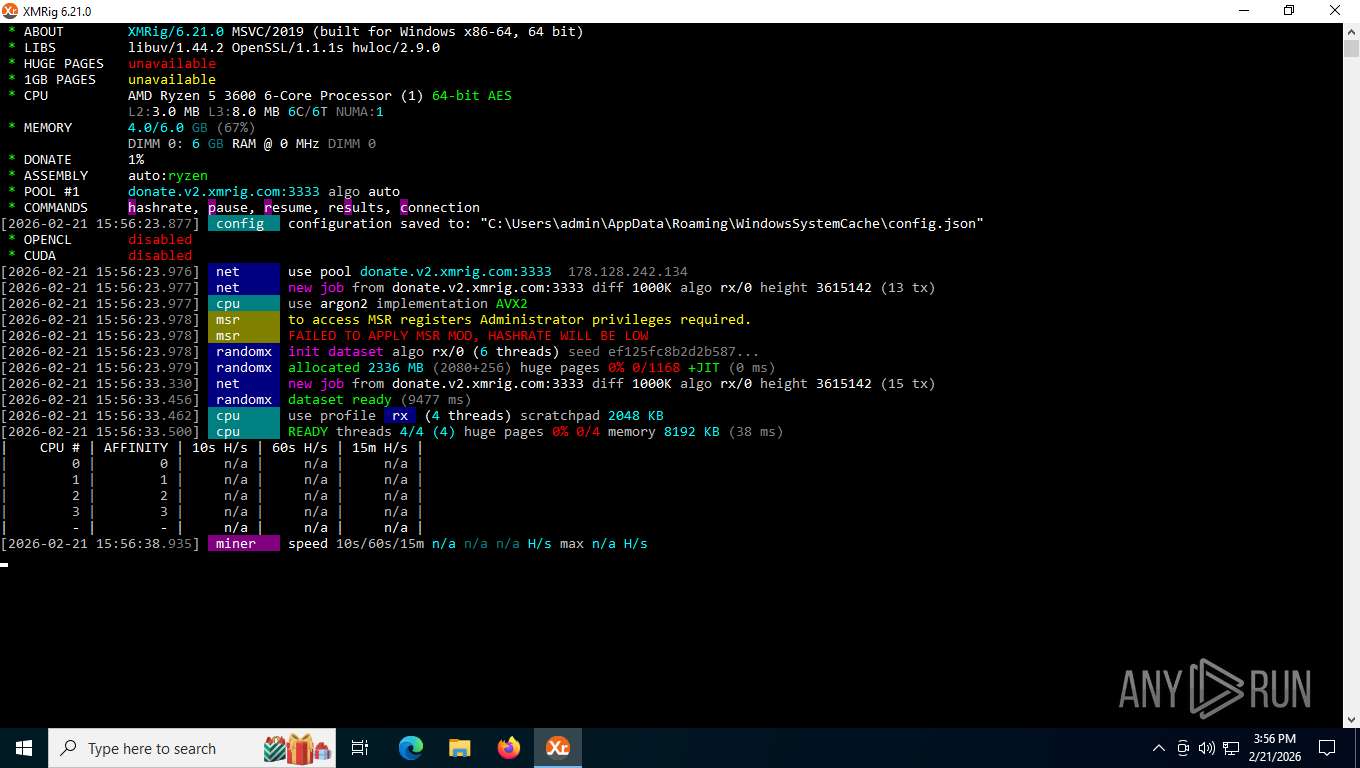
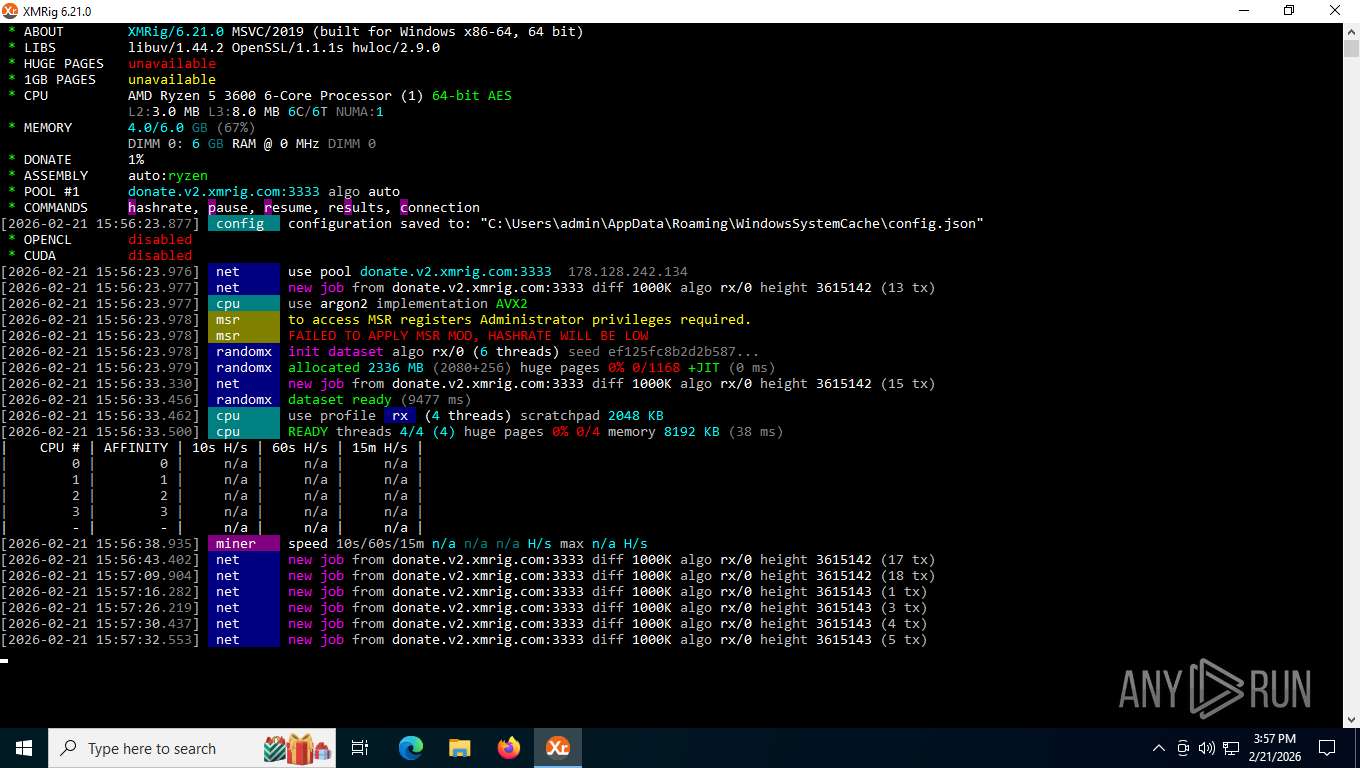
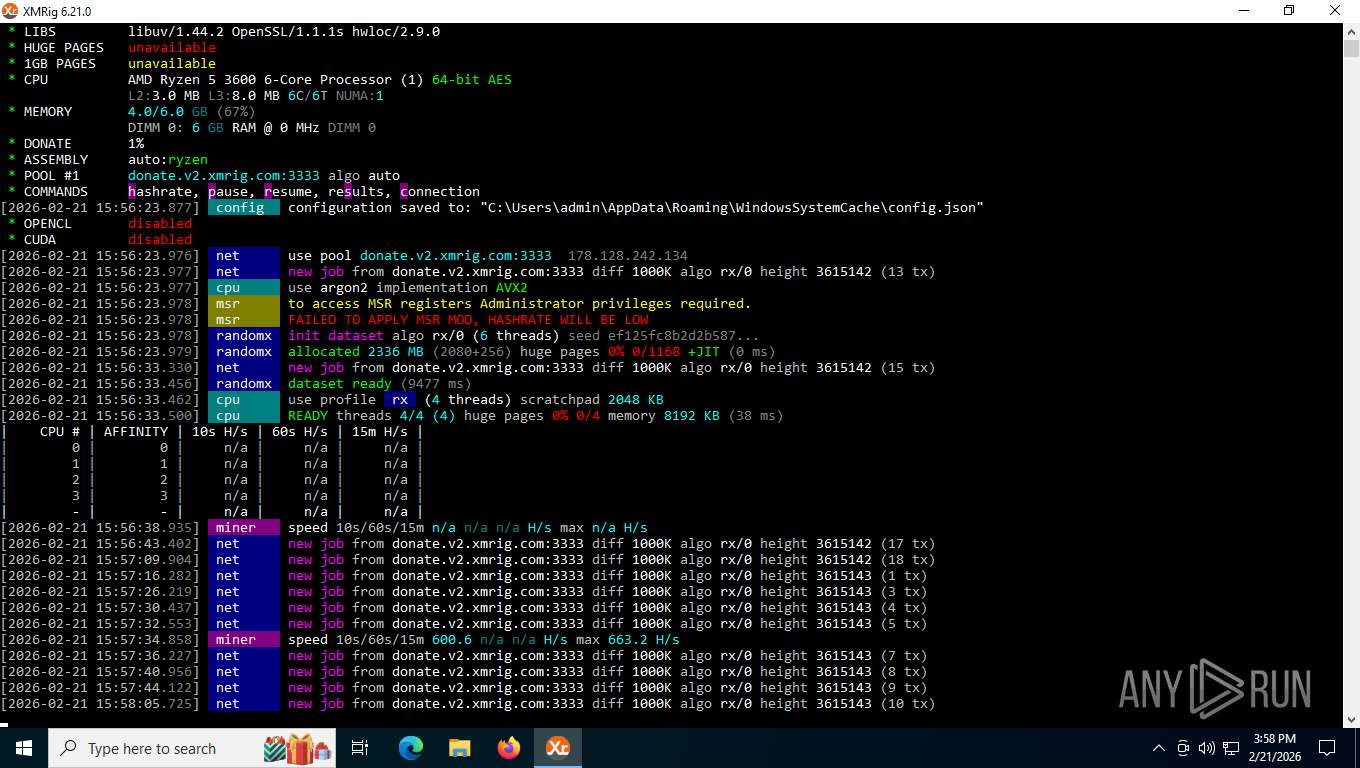
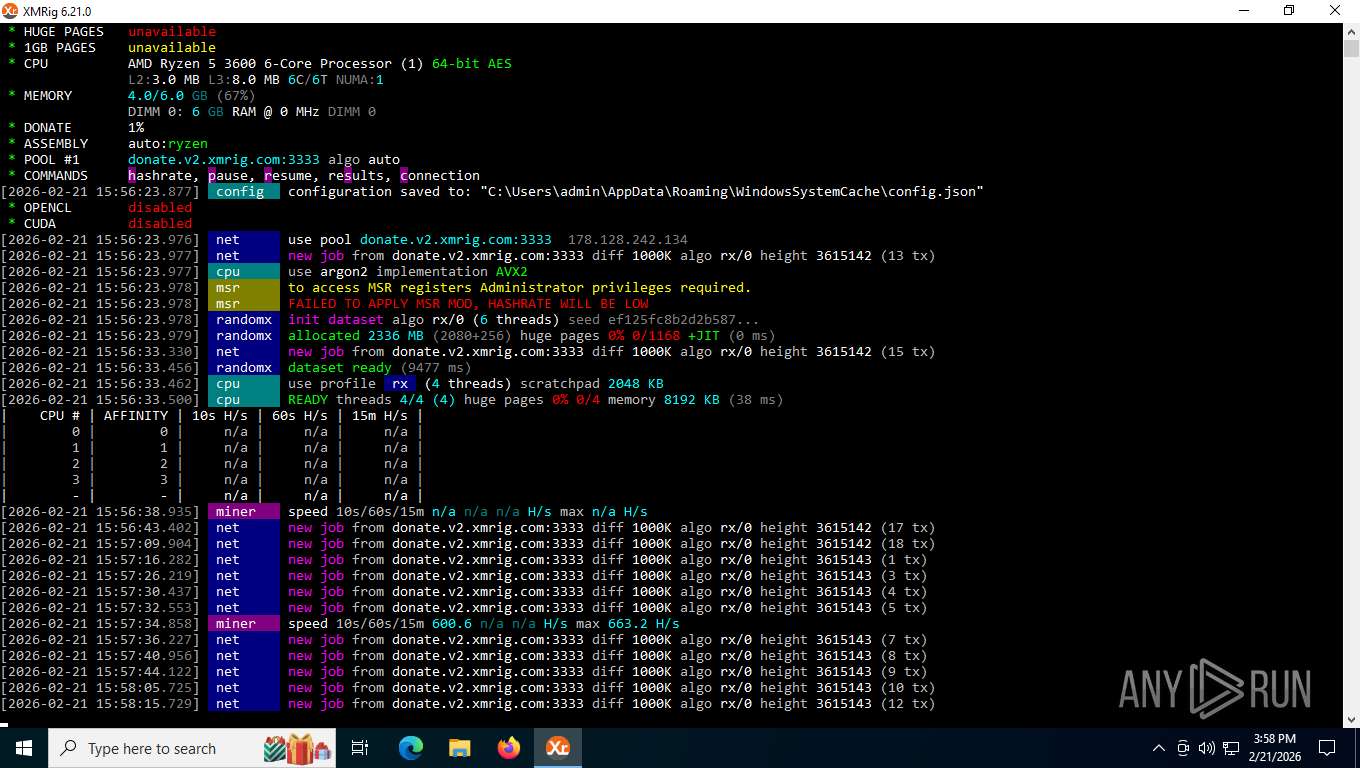
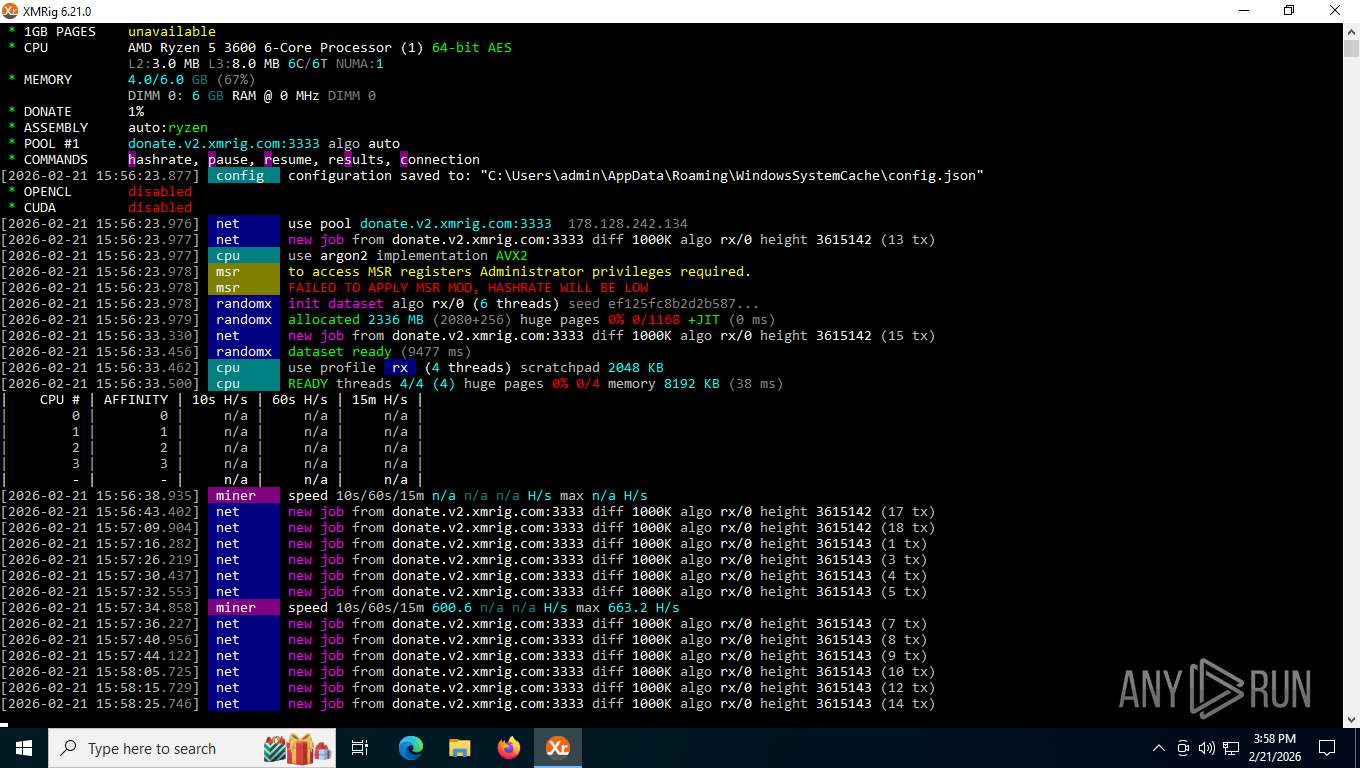
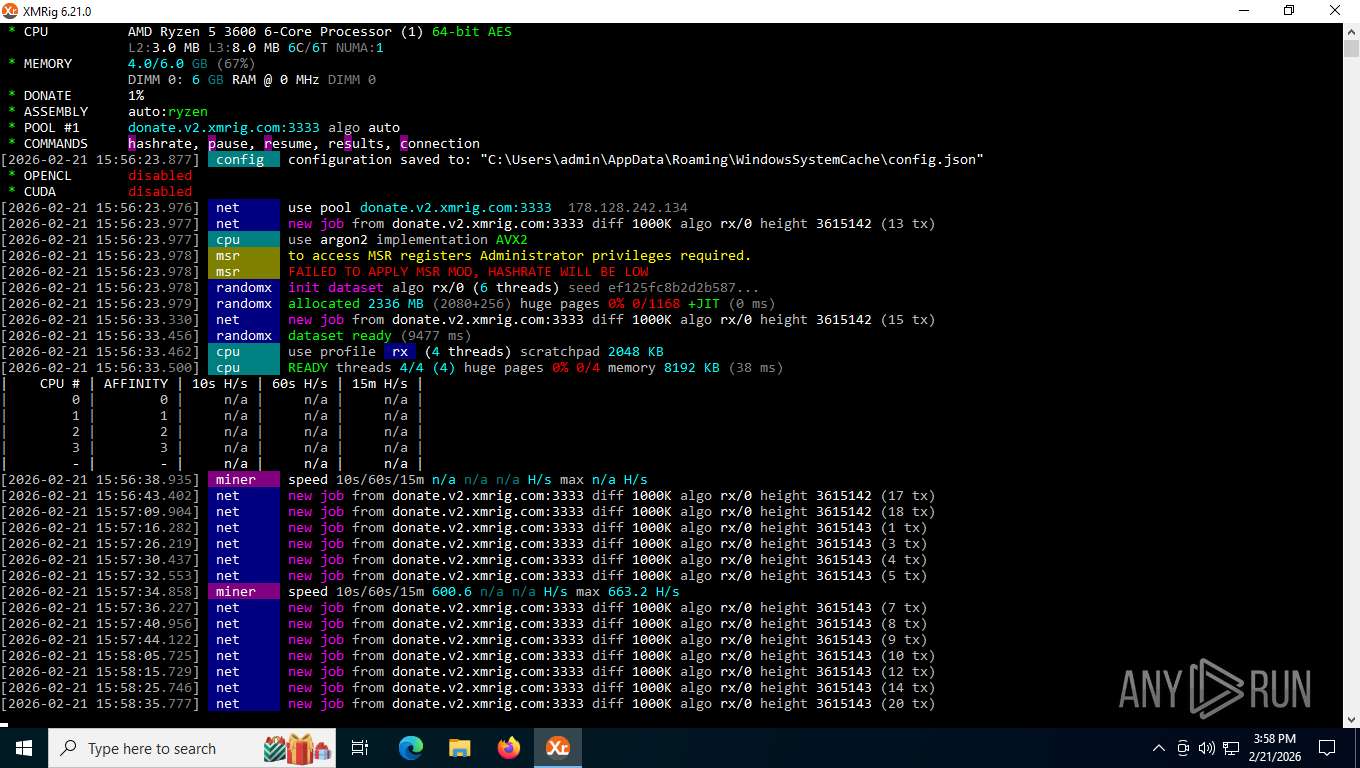
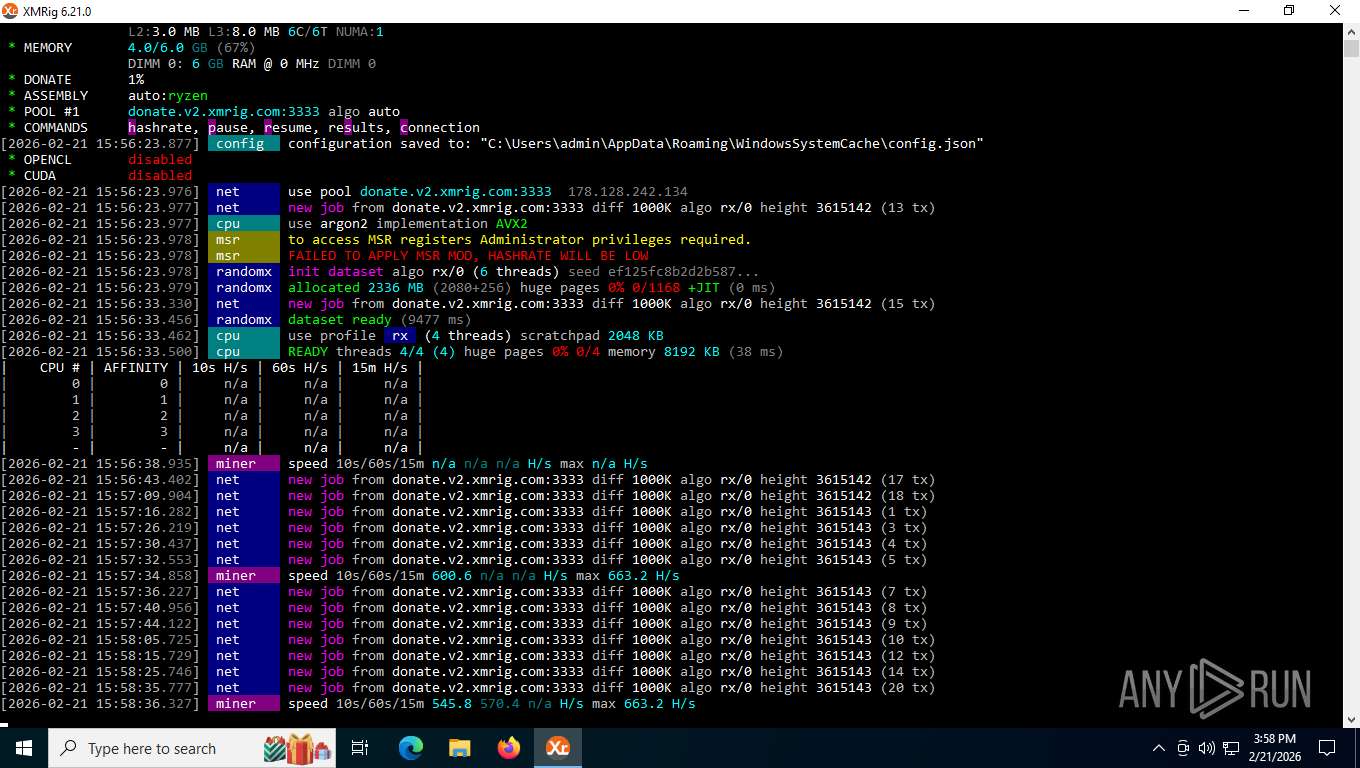
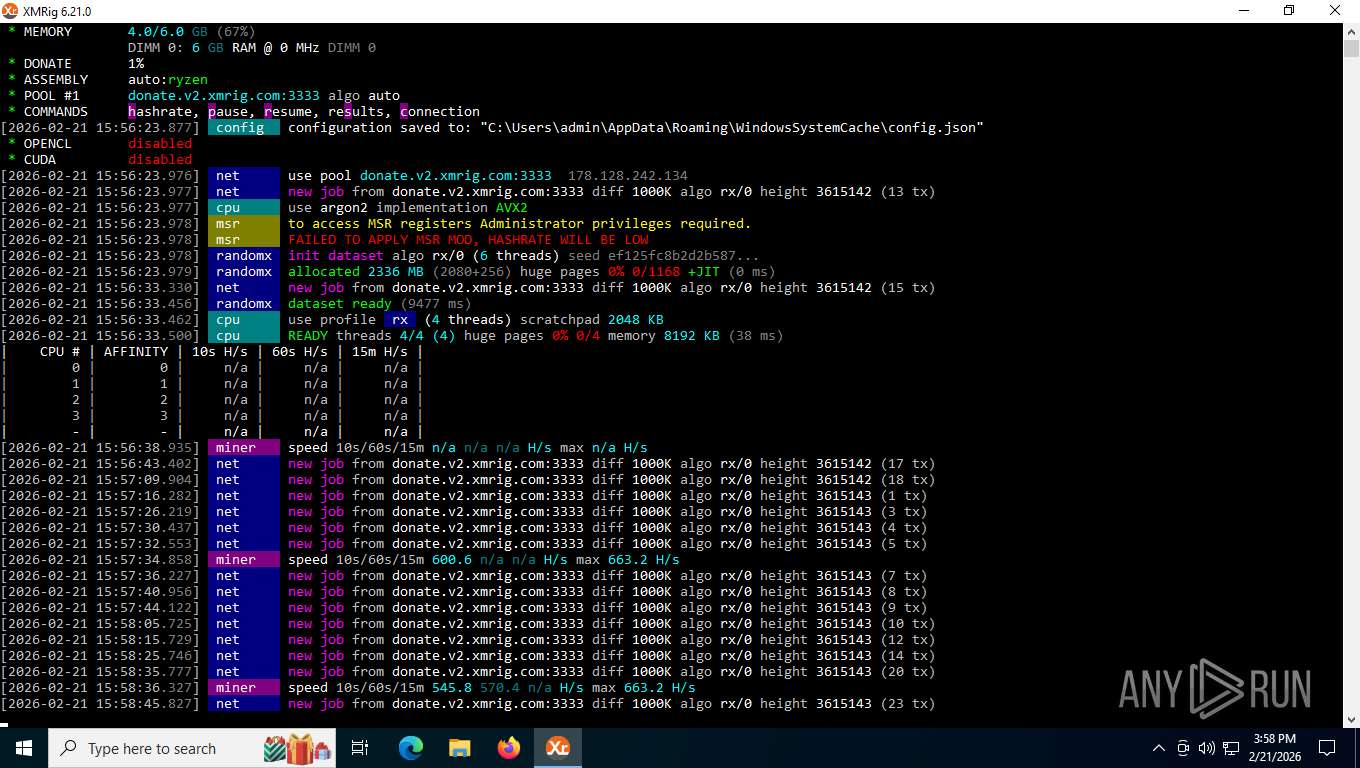
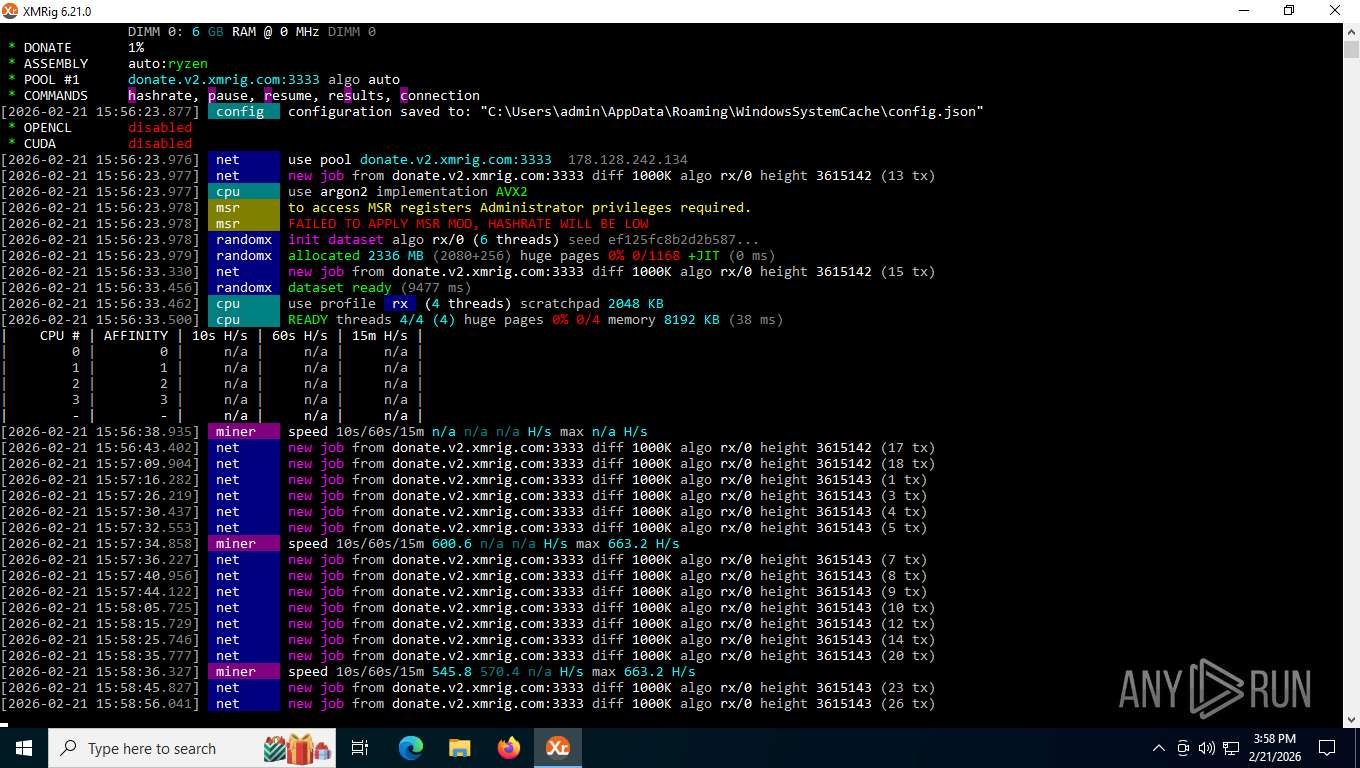
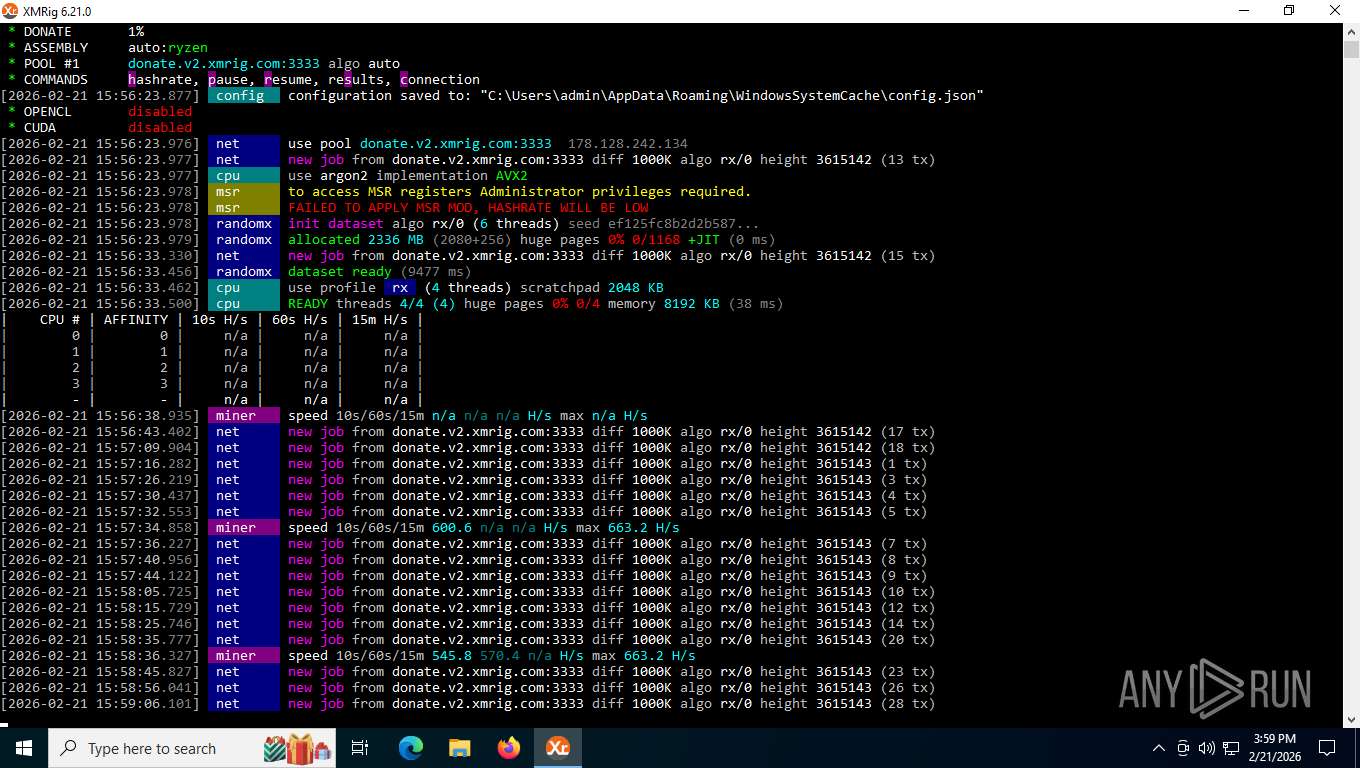
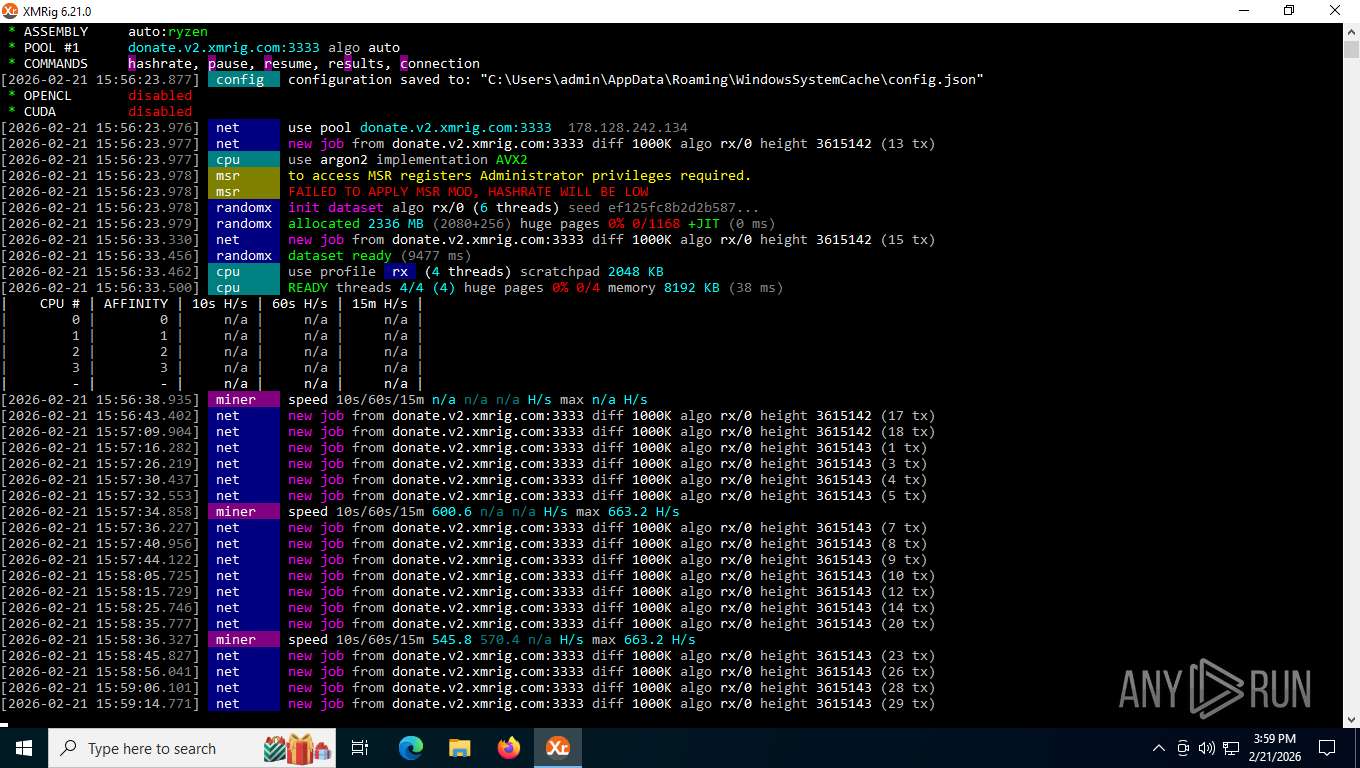
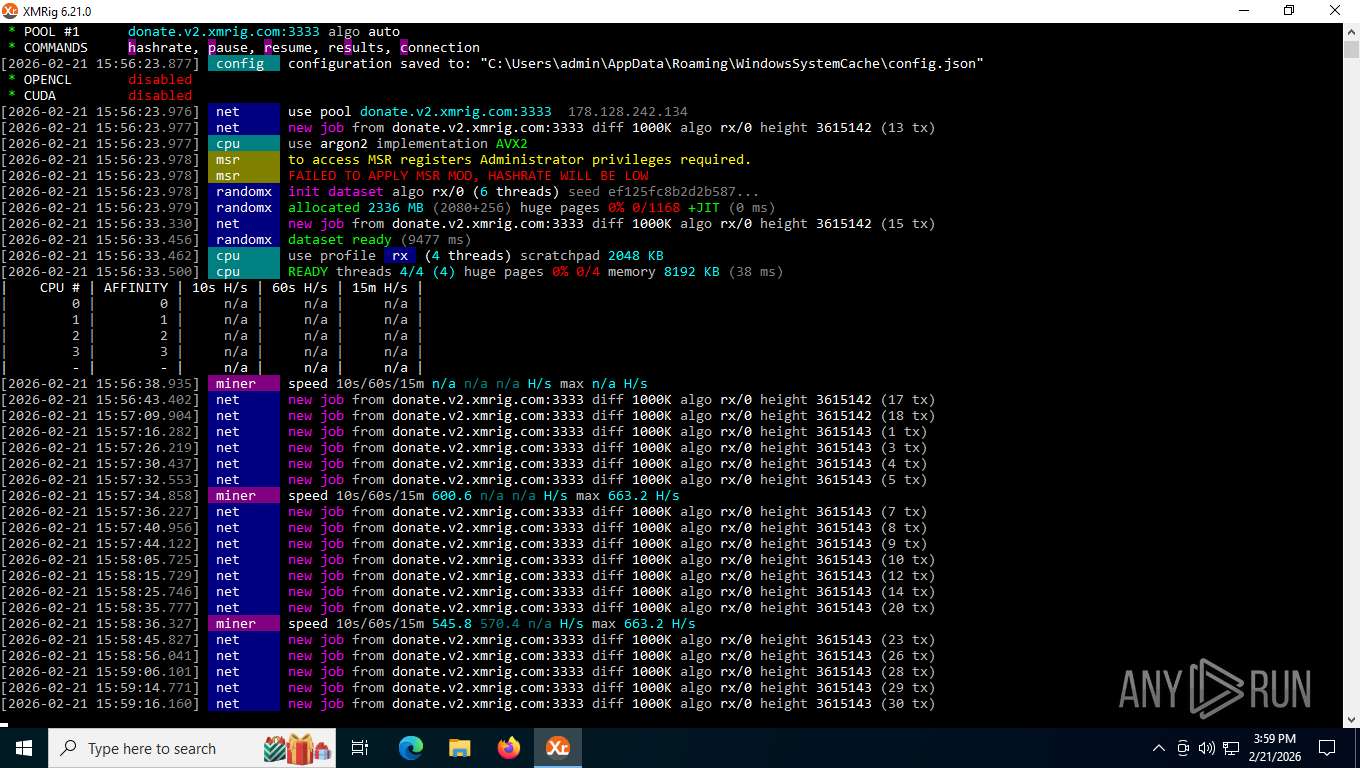
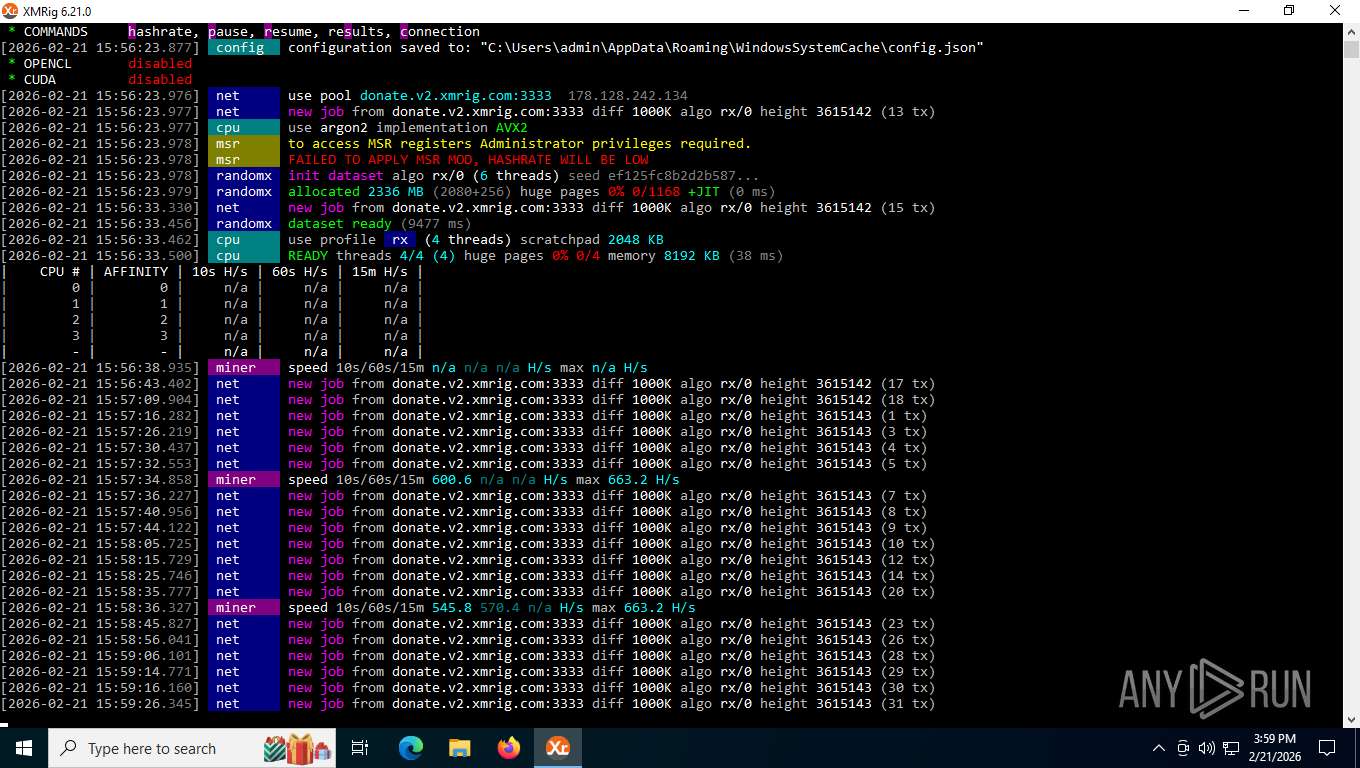
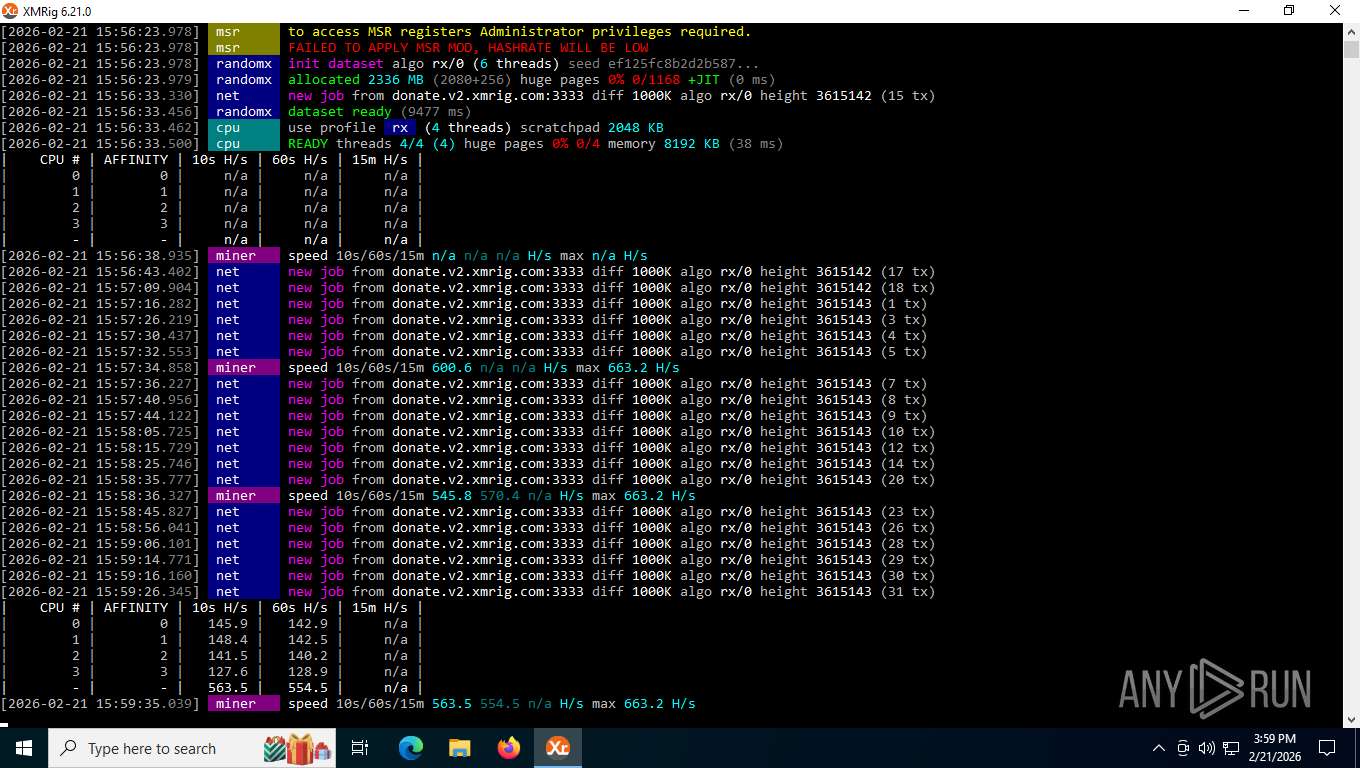
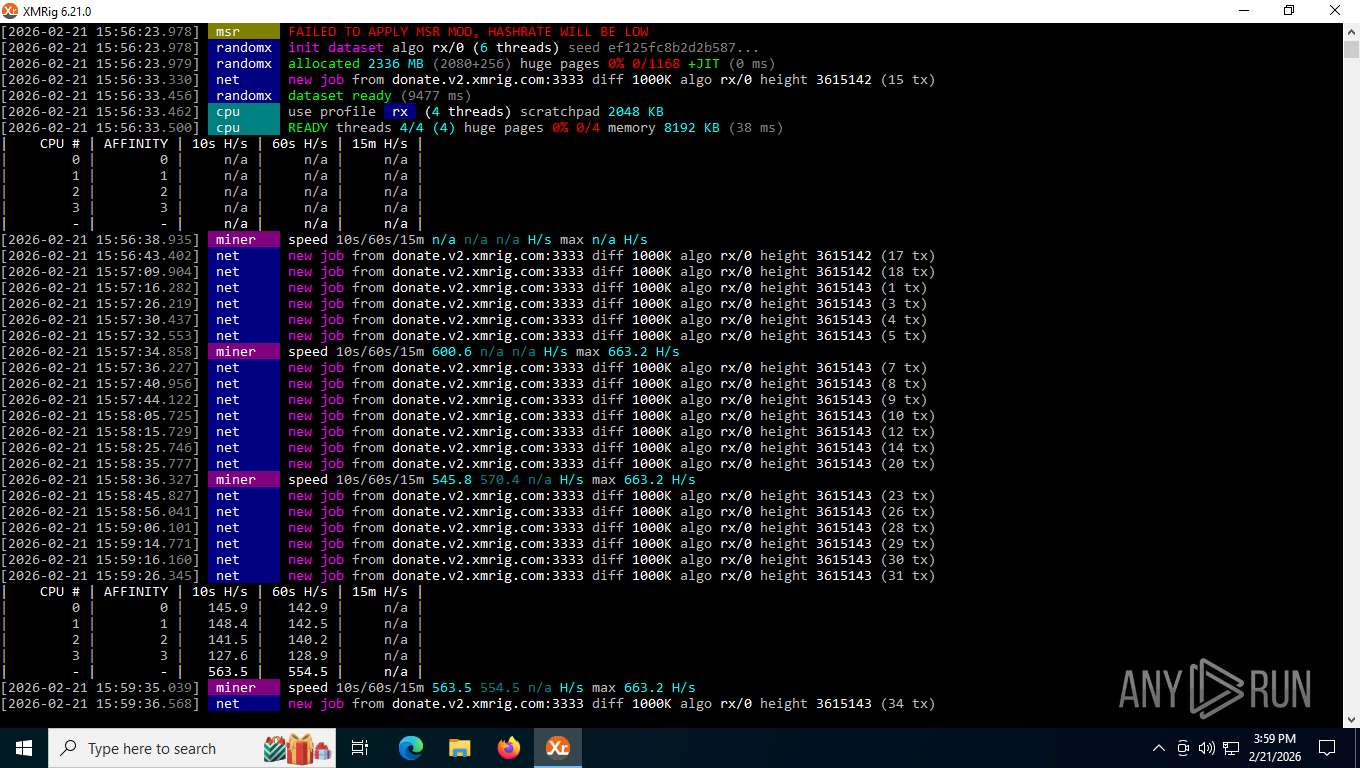
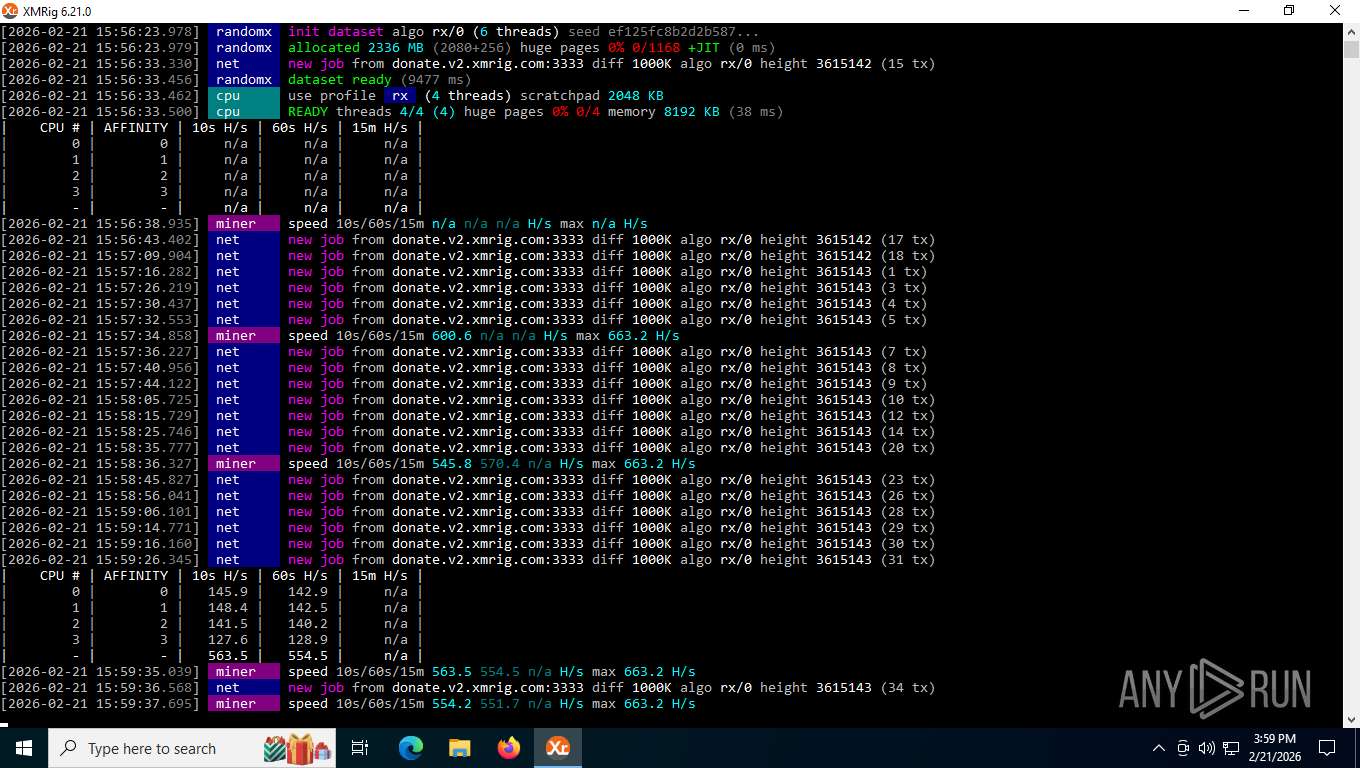
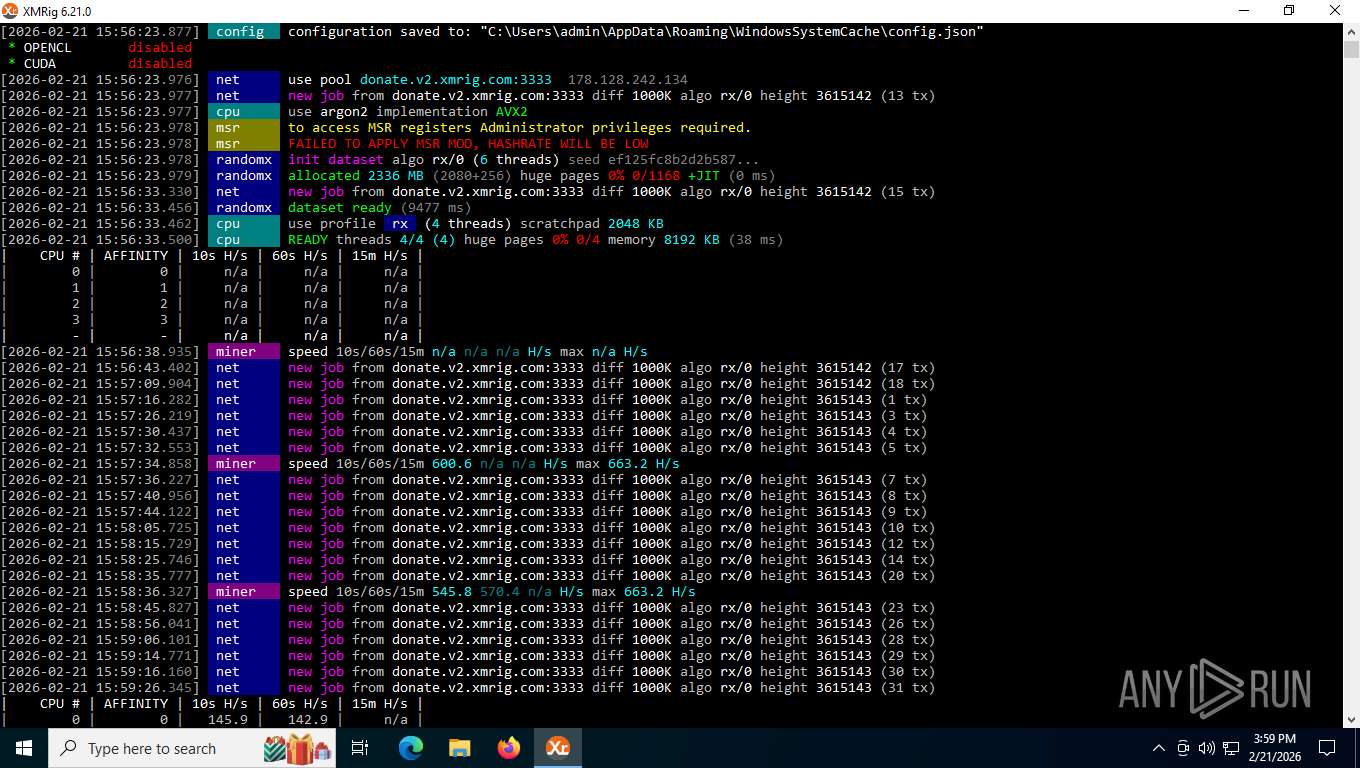
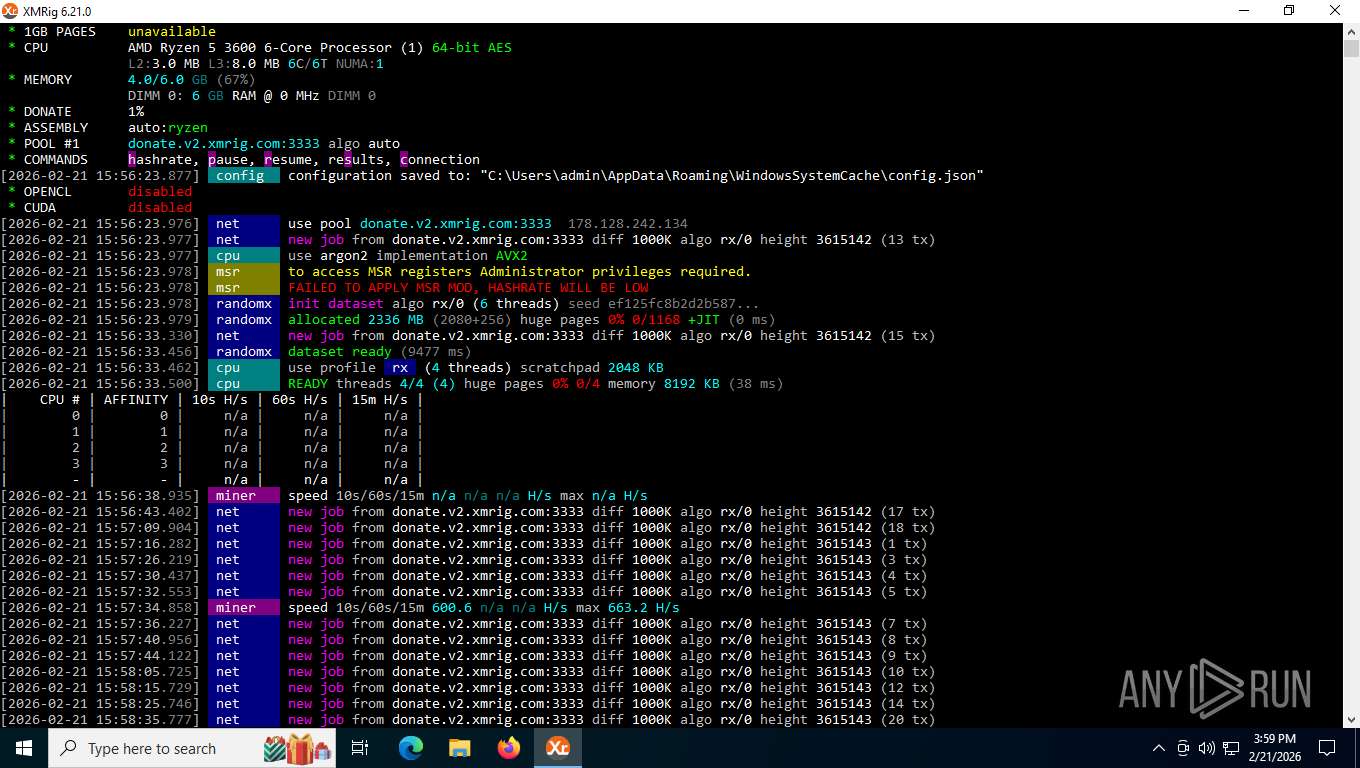
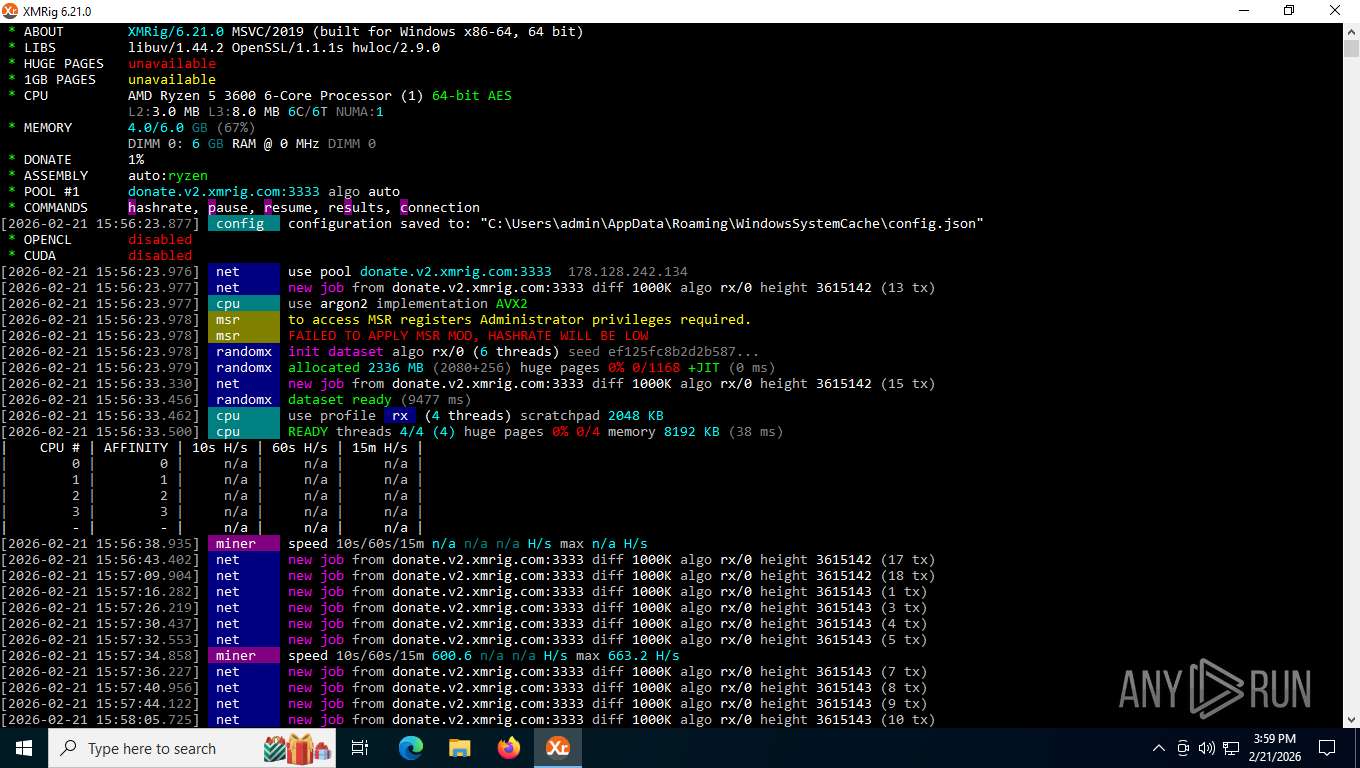
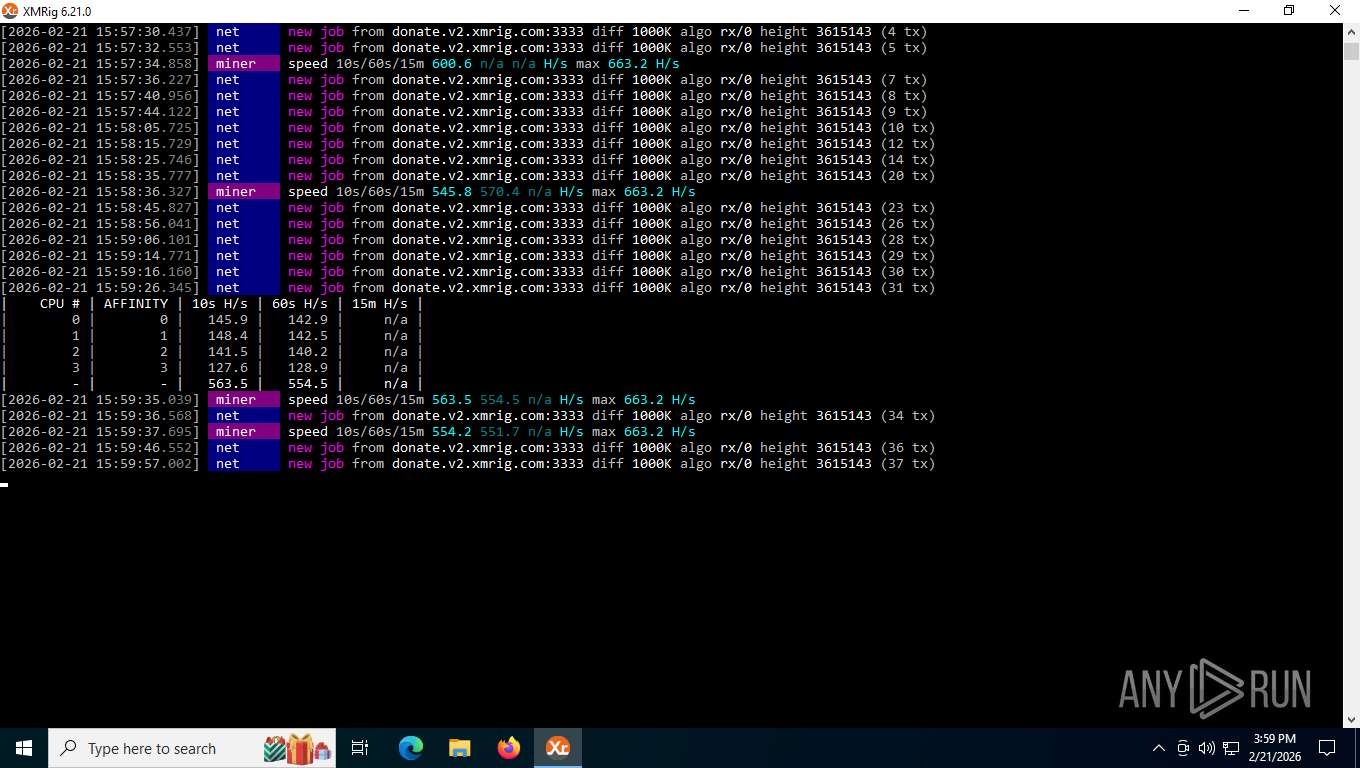
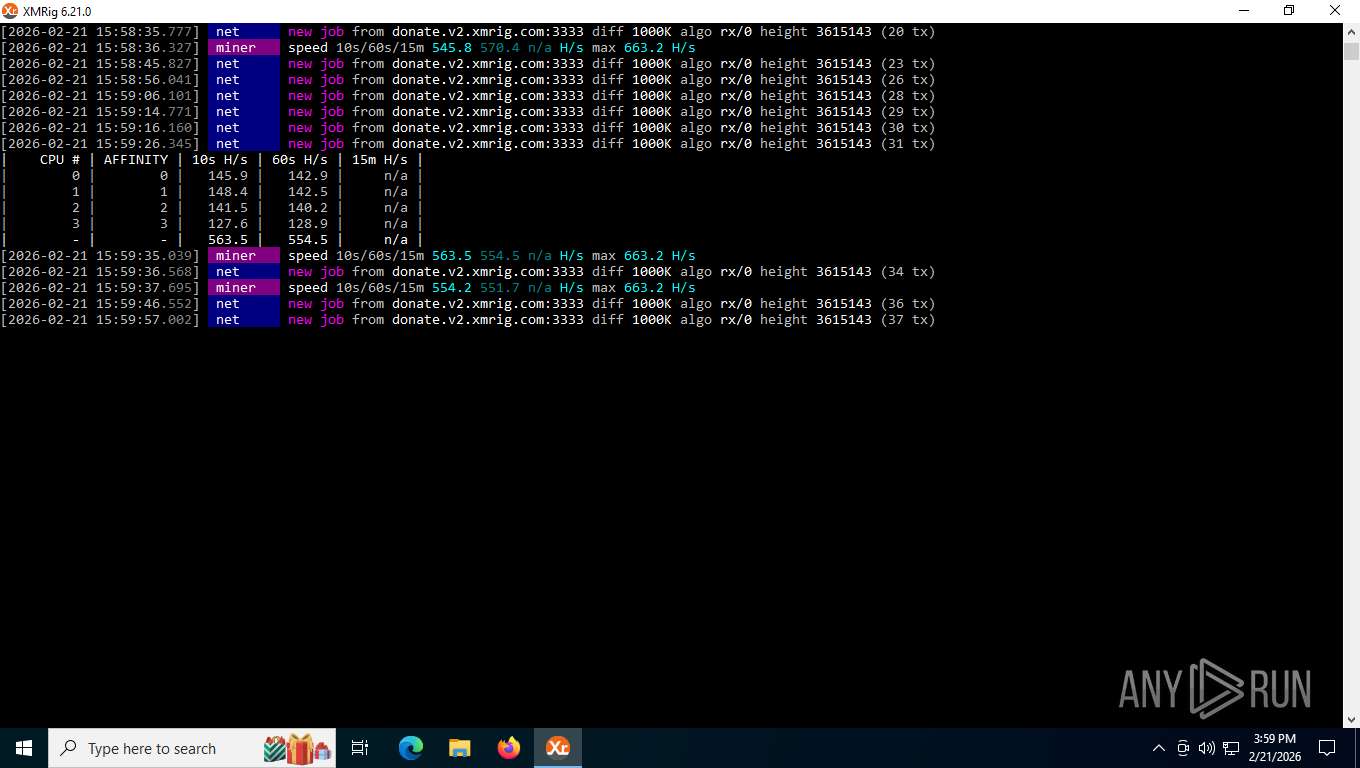
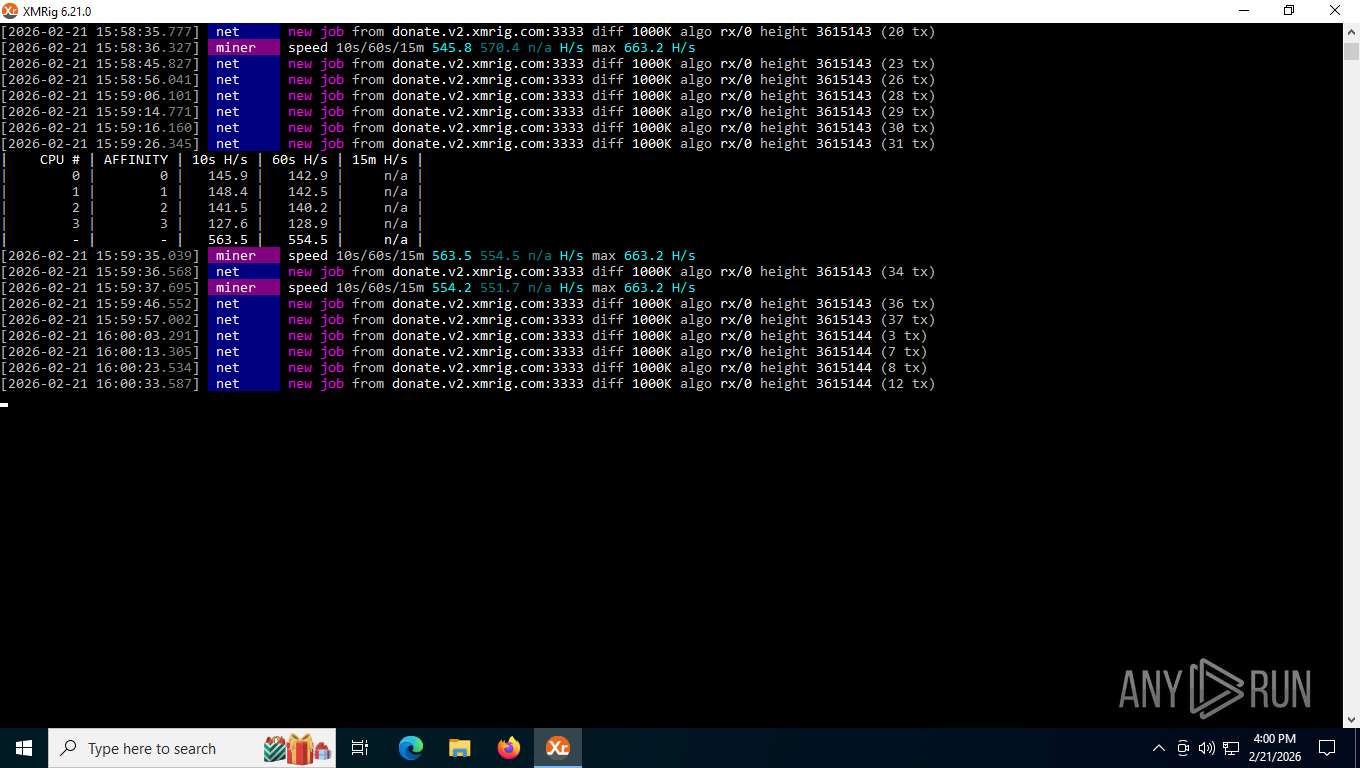
XMRig has been detected
- xmrig.exe (PID: 8708)
- xmrig.exe (PID: 2432)
Vulnerable driver has been detected
- roblox.exe (PID: 1984)
- roblox.exe (PID: 1984)
XMRIG has been detected
- roblox.exe (PID: 1984)
Changes the autorun value in the registry
- roblox.exe (PID: 1984)
Changes Windows Defender settings
- roblox.exe (PID: 1984)
Adds path to the Windows Defender exclusion list
- roblox.exe (PID: 1984)
MINER has been detected (SURICATA)
- xmrig.exe (PID: 8708)
- xmrig.exe (PID: 2432)
XMRIG has been detected (YARA)
- xmrig.exe (PID: 2432)
- xmrig.exe (PID: 8708)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- roblox.exe (PID: 1984)
Starts POWERSHELL.EXE for commands execution
- roblox.exe (PID: 1984)
Script adds exclusion path to Windows Defender
- roblox.exe (PID: 1984)
Potential Corporate Privacy Violation
- xmrig.exe (PID: 8708)
- xmrig.exe (PID: 2432)
INFO
Checks supported languages
- roblox.exe (PID: 1984)
- xmrig.exe (PID: 8708)
- xmrig.exe (PID: 2432)
Creates files or folders in the user directory
- roblox.exe (PID: 1984)
Reads the machine GUID from the registry
- roblox.exe (PID: 1984)
Launching a file from a Registry key
- roblox.exe (PID: 1984)
Drops script file
- roblox.exe (PID: 1984)
- powershell.exe (PID: 8004)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8004)
Drops encrypted JS script (Microsoft Script Encoder)
- roblox.exe (PID: 1984)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8004)
Reads the computer name
- roblox.exe (PID: 1984)
- xmrig.exe (PID: 8708)
- xmrig.exe (PID: 2432)
Manual execution by a user
- xmrig.exe (PID: 2432)
Checks proxy server information
- slui.exe (PID: 5216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 2729984 |
| InitializedDataSize: | 344576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7bda0 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
Total processes
159
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xmrig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1984 | "C:\Users\admin\AppData\Local\Temp\roblox.exe" | C:\Users\admin\AppData\Local\Temp\roblox.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2432 | C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig.exe --background | C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig.exe | explorer.exe | ||||||||||||
User: admin Company: www.xmrig.com Integrity Level: MEDIUM Description: XMRig miner Version: 6.21.0 Modules
| |||||||||||||||
| 2864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xmrig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5216 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7312 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8004 | powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming\WindowsSystemCache'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | roblox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8708 | C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig.exe -o rx.unmineable.com:3333 -a rx -k -u LTC:LfT7YtKU7odzC73pjVGEgeREGtfdnMXQxV.GUTHUB4#0000-0000 --threads=8 --background | C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig.exe | roblox.exe | ||||||||||||
User: admin Company: www.xmrig.com Integrity Level: MEDIUM Description: XMRig miner Version: 6.21.0 Modules
| |||||||||||||||
Total events
14 196
Read events
14 195
Write events
1
Delete events
0
Modification events
| (PID) Process: | (1984) roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WinSysUpdate |
Value: C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig.exe --background | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_32r1oybh.qwu.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ctoae05r.cnf.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ool2bw0l.05t.psm1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1984 | roblox.exe | C:\Users\admin\AppData\Roaming\WindowsSystemCache\setup.zip | binary | |
MD5:F2146C45B21C27921E3FEFE93135E814 | SHA256:4CF4198354ABFEE7E502C85F38E62DBB90FEC976E4DF38D0ECBFD811937C1981 | |||
| 8004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_li5gte33.hl0.psm1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8004 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:EE0EA649D9351DBC85C670F66981C852 | SHA256:3128018080C8F5AFC50E333B752DC816F0FCE9F94B038256815A406397F22EBC | |||
| 1984 | roblox.exe | C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig-6.21.0\benchmark_10M.cmd | binary | |
MD5:5BE1C4CACB5AE37C43527E99A097DC7A | SHA256:235A64E3520B1C2C27763122B303F78AEE8D7C083DFD9F1EB936CD5174383609 | |||
| 1984 | roblox.exe | C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig-6.21.0\solo_mine_example.cmd | binary | |
MD5:090703E56F46330ED625AC4363C9D25C | SHA256:33497C69C21FA96BBC96F1D7F09608E462F8AB22555364977C0BD35FEF27BC29 | |||
| 1984 | roblox.exe | C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig-6.21.0\WinRing0x64.sys | binary | |
MD5:0C0195C48B6B8582FA6F6373032118DA | SHA256:11BD2C9F9E2397C9A16E0990E4ED2CF0679498FE0FD418A3DFDAC60B5C160EE5 | |||
| 1984 | roblox.exe | C:\Users\admin\AppData\Roaming\WindowsSystemCache\xmrig-6.21.0\xmrig.exe | binary | |
MD5:118C2D536D52DD30116BAAF06DFE5E63 | SHA256:F07C7223FDB691ACBF0EBC7D9CC2AE614C0CF705920420C0130248A0C0E861D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
31
DNS requests
25
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2976 | svchost.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
5108 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5108 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
5108 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
5108 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
2976 | svchost.exe | GET | 200 | 184.24.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
2976 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
2976 | svchost.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | binary | 5.70 Kb | whitelisted |
356 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2976 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
876 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2976 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2976 | svchost.exe | 184.24.77.41:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
2976 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
1984 | roblox.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
1984 | roblox.exe | 185.199.108.133:443 | release-assets.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
release-assets.githubusercontent.com |
| whitelisted |
rx.unmineable.com |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2976 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
8708 | xmrig.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
2432 | xmrig.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
2432 | xmrig.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
8708 | xmrig.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |