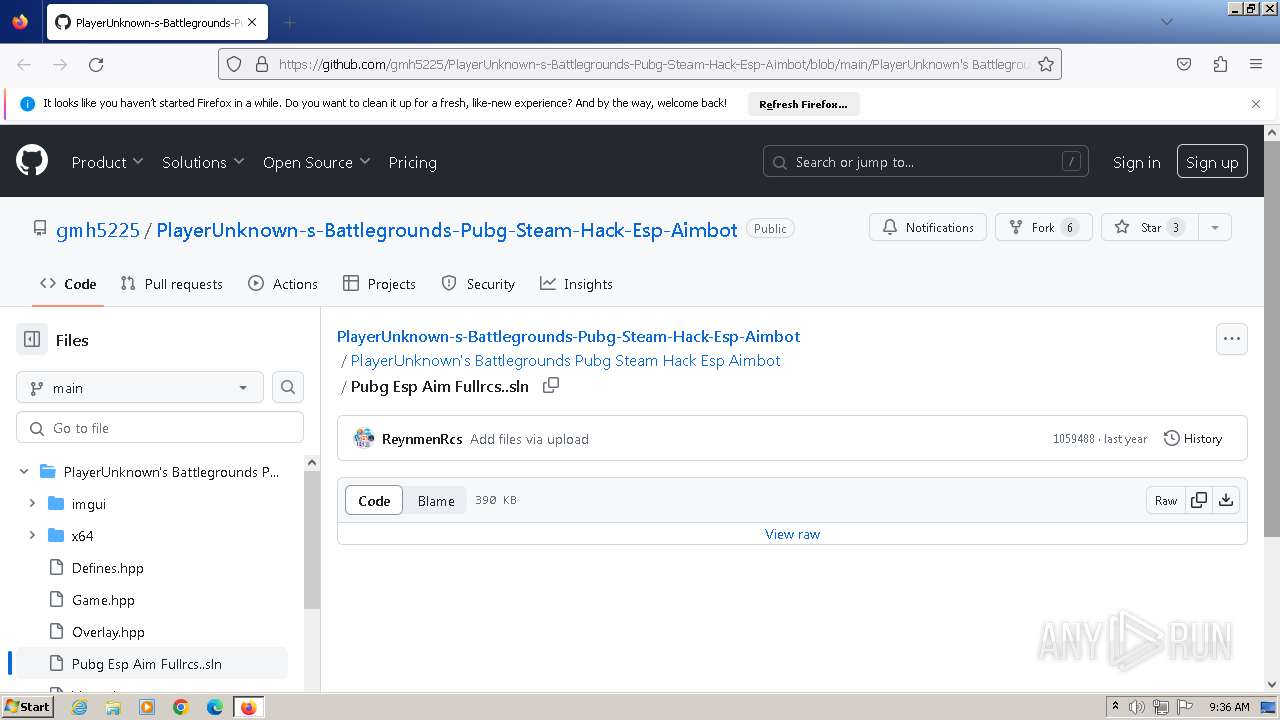
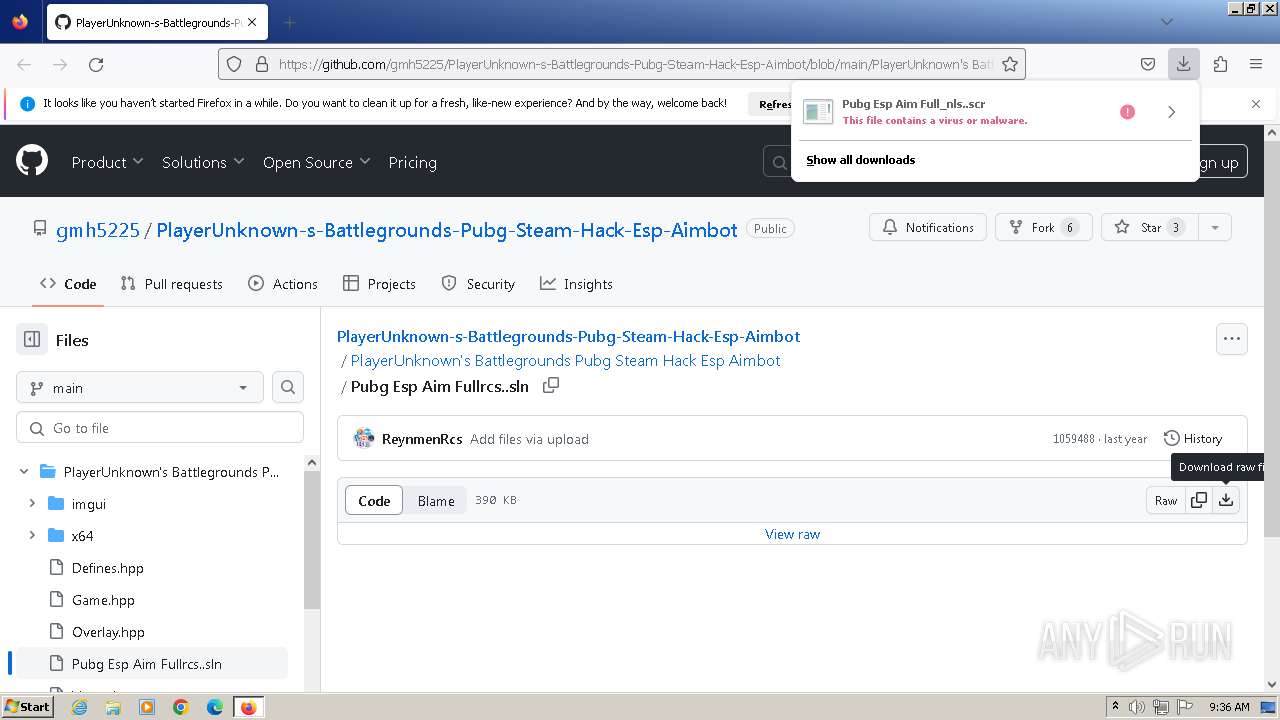
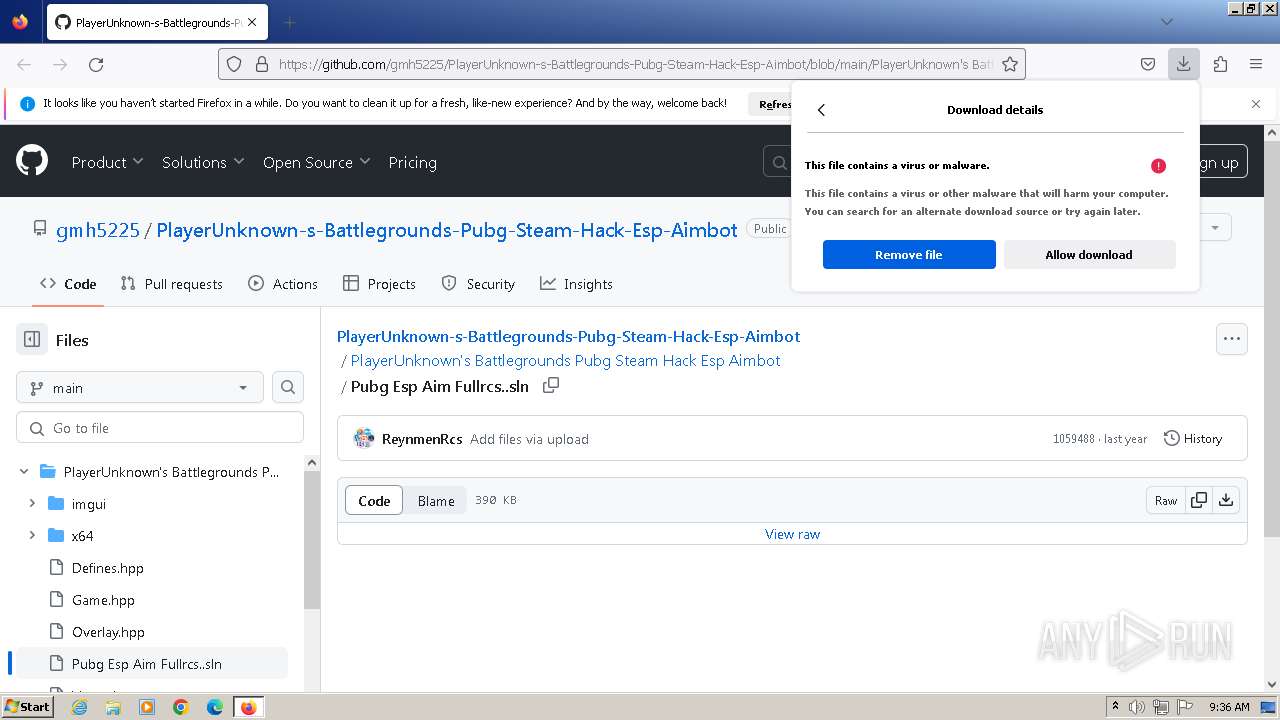
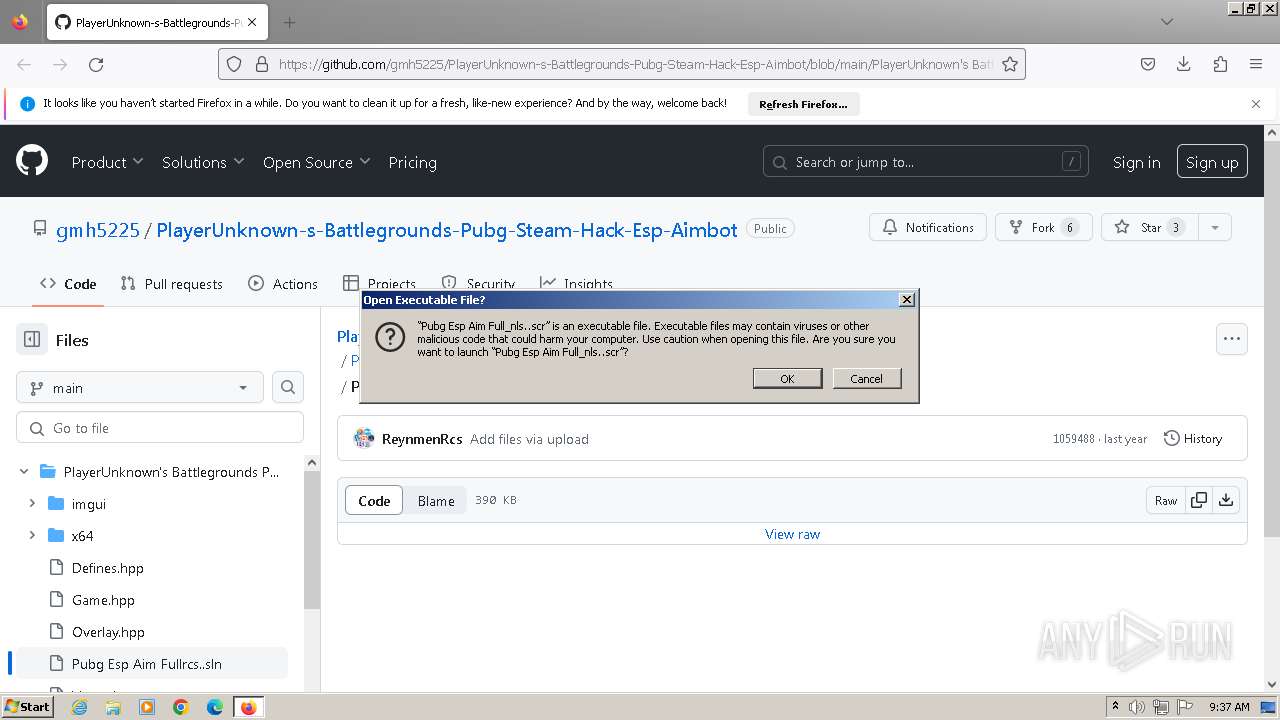
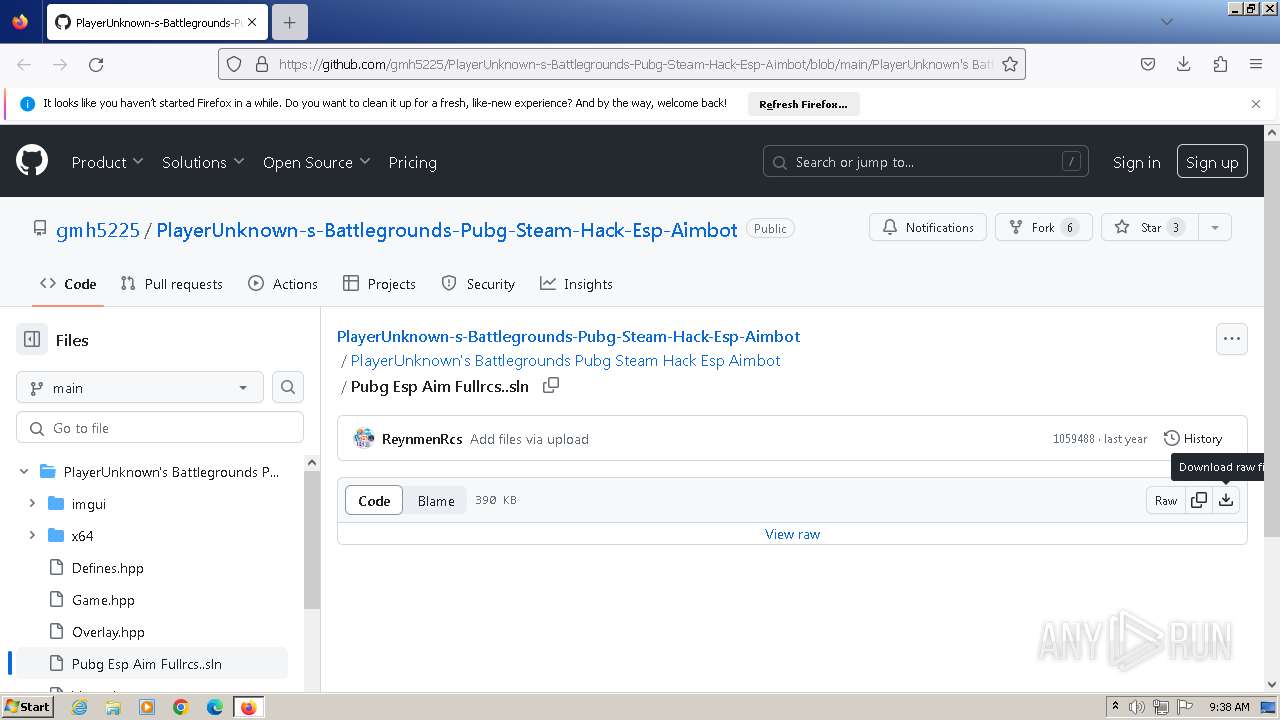
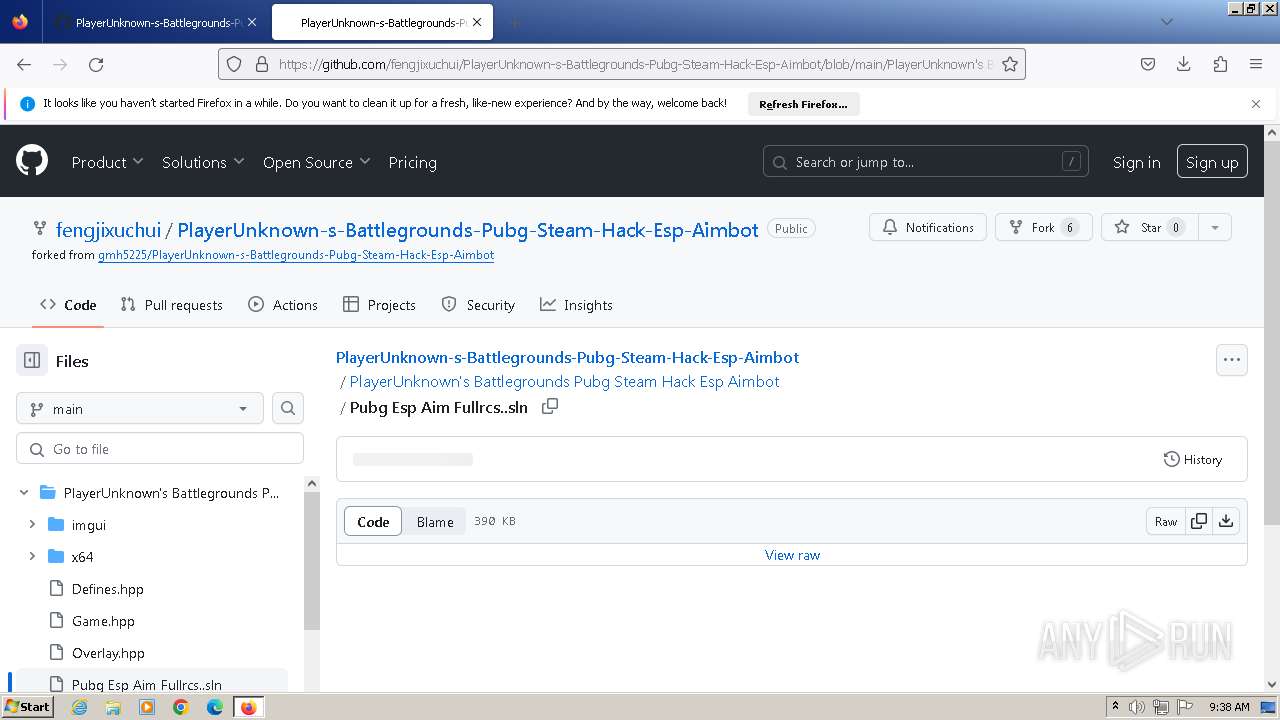
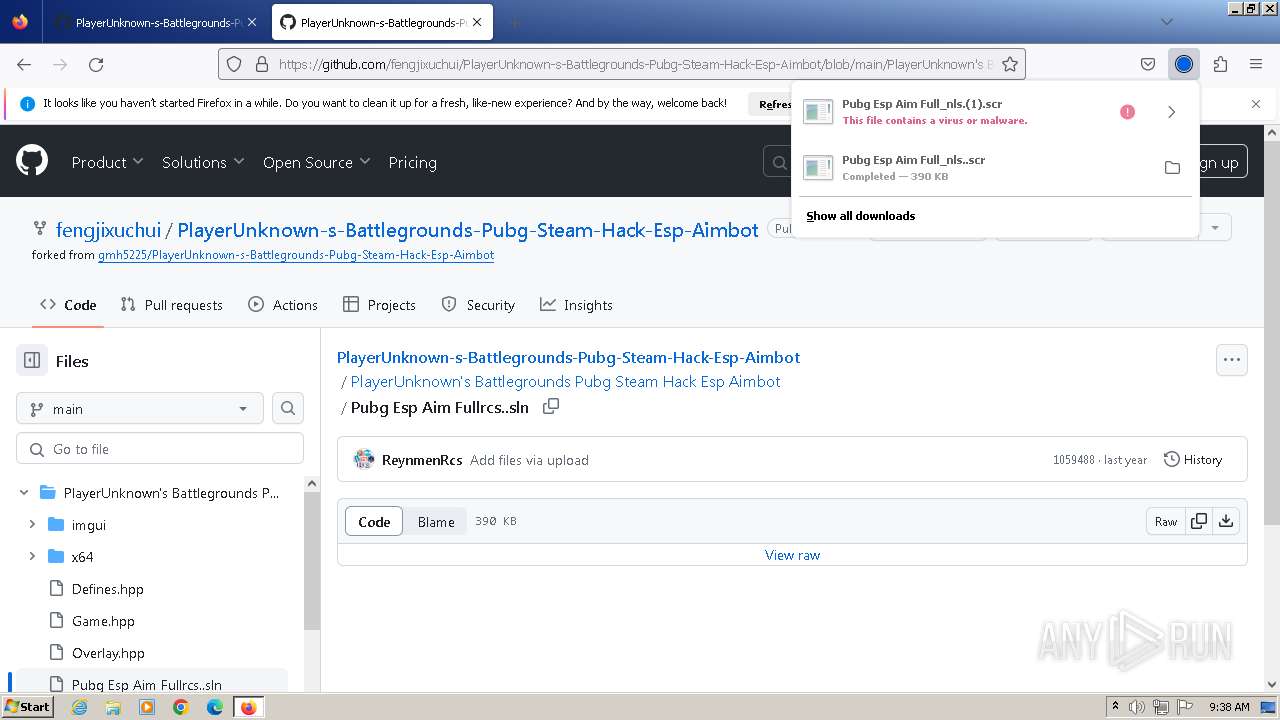
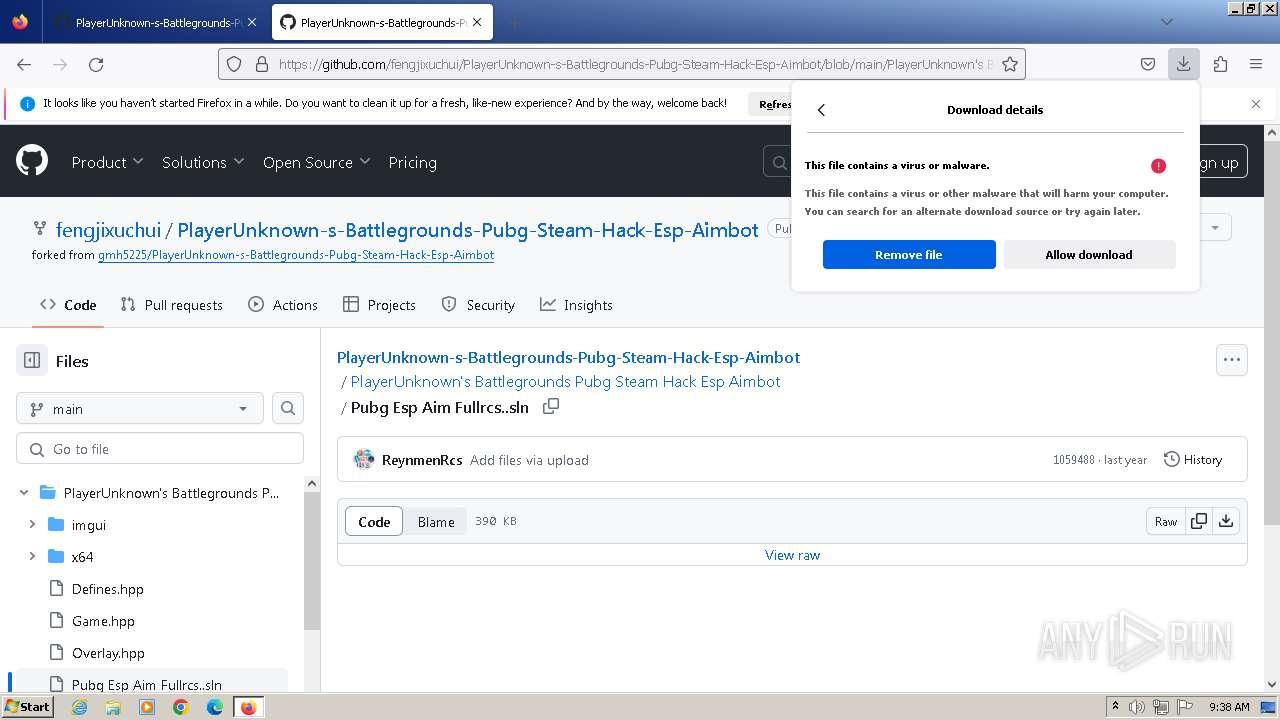
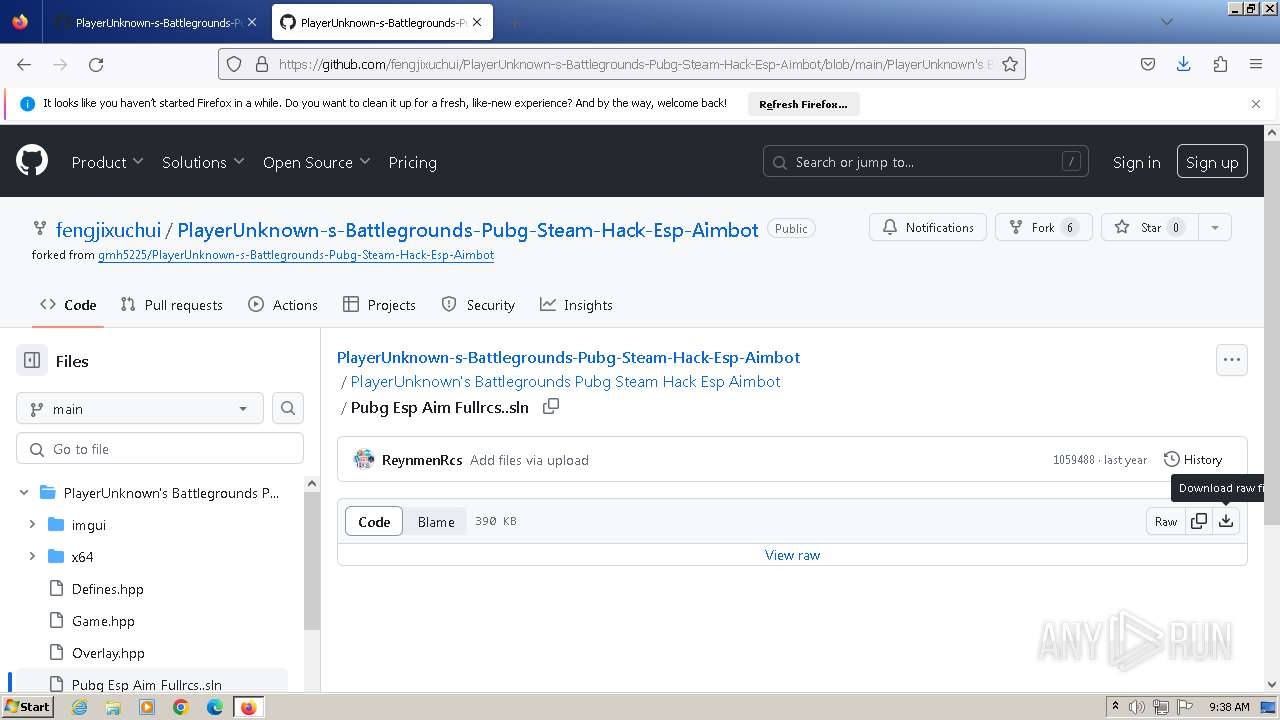
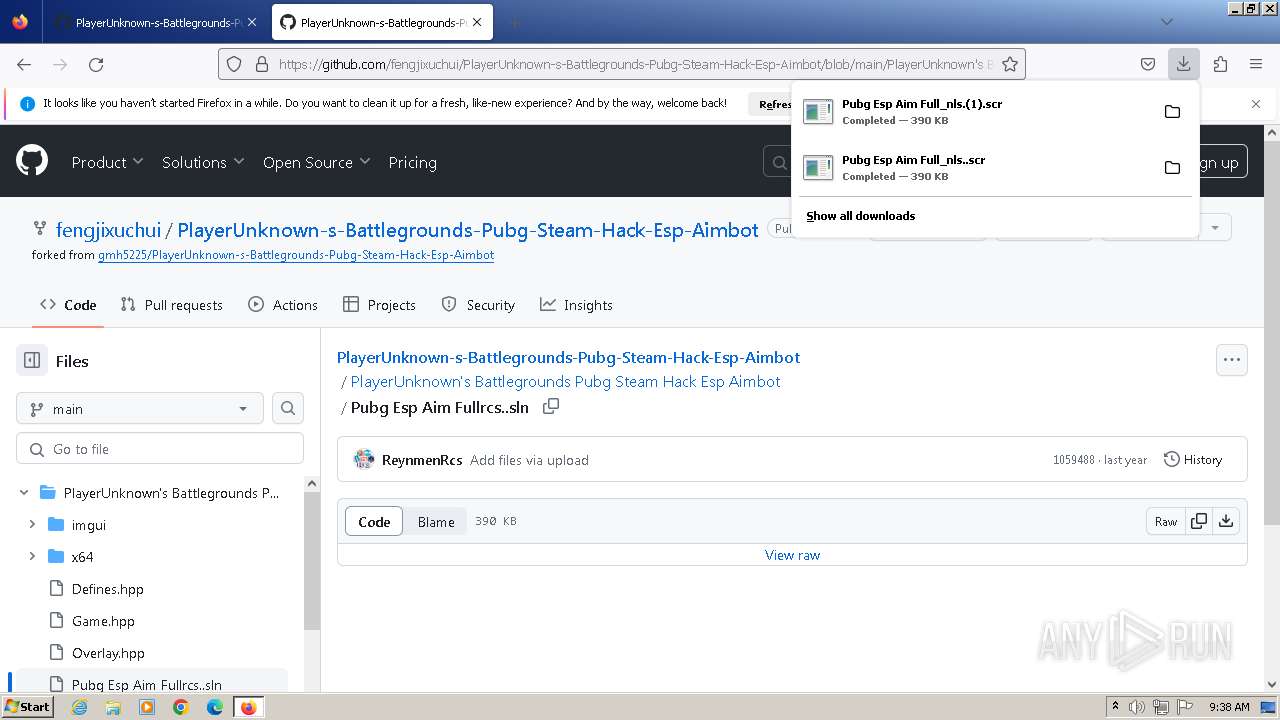
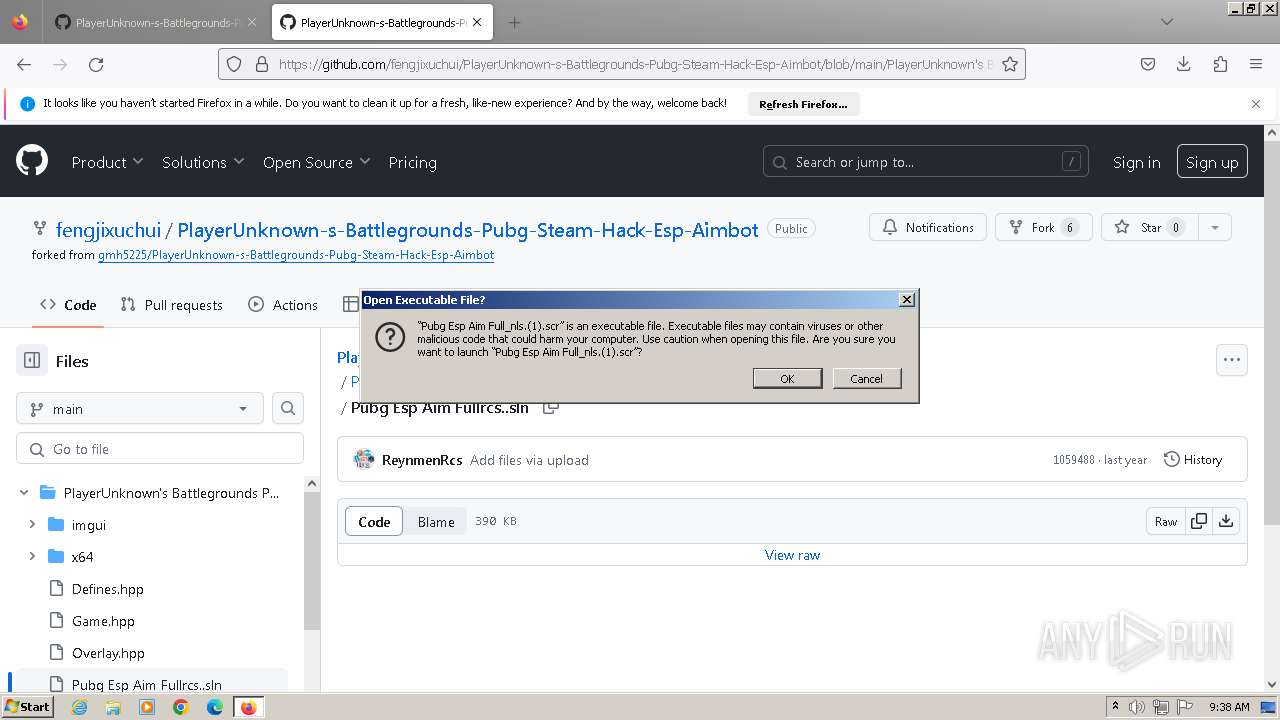
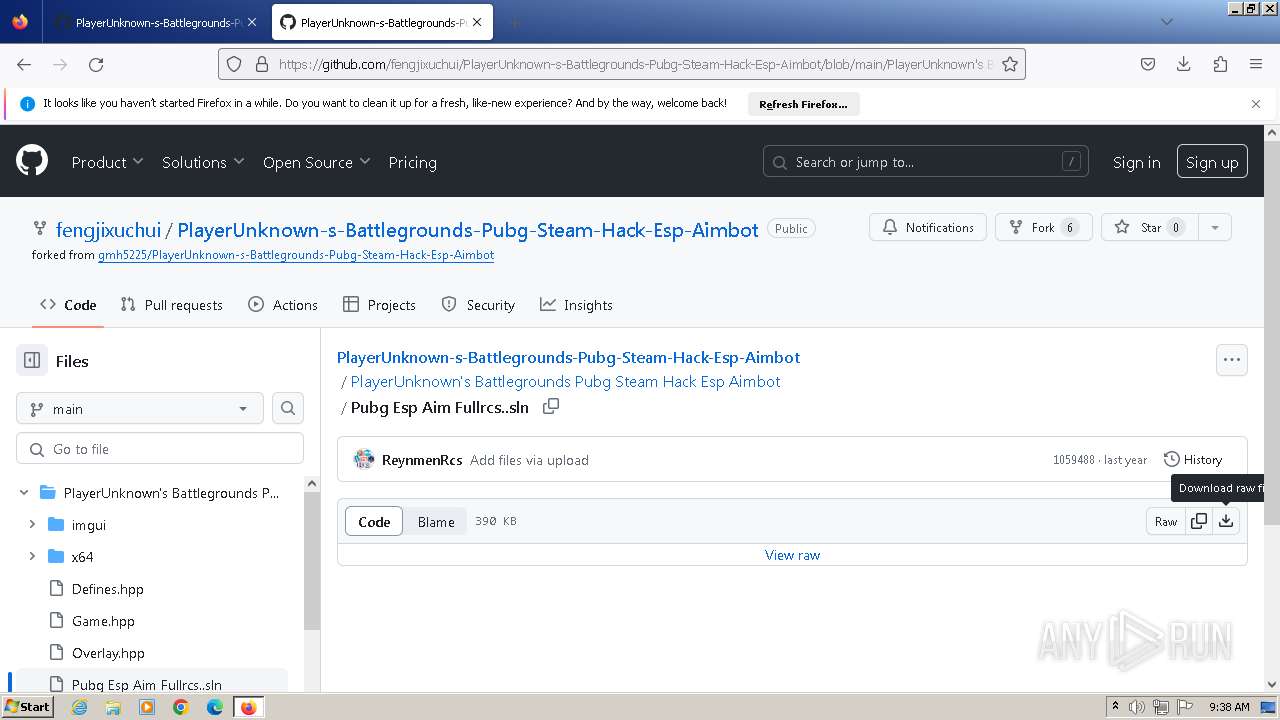
| URL: | https://github.com/gmh5225/PlayerUnknown-s-Battlegrounds-Pubg-Steam-Hack-Esp-Aimbot/blob/main/PlayerUnknown's%20Battlegrounds%20Pubg%20Steam%20Hack%20Esp%20Aimbot/Pubg%20Esp%20Aim%20Full%E2%80%AEnls..scr |
| Full analysis: | https://app.any.run/tasks/951719cb-68bb-431f-b16e-98ced99b876a |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | October 25, 2023, 08:36:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 41D49968A401C2B49BEC387051221529 |
| SHA1: | 8B82175F089990F6B5DF94C418BB47C72C9DBCF7 |
| SHA256: | 25EB03E7449268078D02E031F103952FB28F99E0AA31A80BE9EA643C2596315E |
| SSDEEP: | 3:N8tEdyINQXXdKRw6t8PJeN1SCkIpMIHRHJcKIERAw6t29cOTeFFaB2hIyPvXKSA6:2ukwQXXPPMcL8uTs9/yFt5vaC4aSja |
MALICIOUS
Application was dropped or rewritten from another process
- Pubg Esp Aim Full_nls..scr (PID: 2040)
- 31.EXE (PID: 1616)
- Pubg Esp Aim Full_nls.(1).scr (PID: 2372)
- 111111111111111111111111_PROTECTED.EXE (PID: 3932)
- 31.EXE (PID: 1128)
- 111111111111111111111111_PROTECTED.EXE (PID: 1124)
Drops the executable file immediately after the start
- Pubg Esp Aim Full_nls..scr (PID: 2040)
- 111111111111111111111111_PROTECTED.EXE (PID: 3932)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3268)
- cmd.exe (PID: 2420)
ASYNCRAT has been detected (YARA)
- RegAsm.exe (PID: 3404)
SUSPICIOUS
Reads the Internet Settings
- Pubg Esp Aim Full_nls..scr (PID: 2040)
- 31.EXE (PID: 1616)
- powershell.exe (PID: 3288)
- Pubg Esp Aim Full_nls.(1).scr (PID: 2372)
- 31.EXE (PID: 1128)
- powershell.exe (PID: 3080)
Process drops legitimate windows executable
- Pubg Esp Aim Full_nls..scr (PID: 2040)
Starts POWERSHELL.EXE for commands execution
- 111111111111111111111111_PROTECTED.EXE (PID: 3932)
- 31.EXE (PID: 1616)
- 111111111111111111111111_PROTECTED.EXE (PID: 1124)
- 31.EXE (PID: 1128)
Base64-obfuscated command line is found
- 31.EXE (PID: 1616)
- 31.EXE (PID: 1128)
BASE64 encoded PowerShell command has been detected
- 31.EXE (PID: 1616)
- 31.EXE (PID: 1128)
Starts CMD.EXE for commands execution
- 111111111111111111111111_PROTECTED.EXE (PID: 3932)
- 111111111111111111111111_PROTECTED.EXE (PID: 1124)
Unusual connection from system programs
- powershell.exe (PID: 3288)
- powershell.exe (PID: 3080)
Powershell version downgrade attack
- powershell.exe (PID: 3288)
- powershell.exe (PID: 3260)
- powershell.exe (PID: 3080)
- powershell.exe (PID: 1180)
The Powershell connects to the Internet
- powershell.exe (PID: 3288)
- powershell.exe (PID: 3080)
Connects to unusual port
- RegAsm.exe (PID: 3404)
INFO
Application launched itself
- firefox.exe (PID: 3828)
- firefox.exe (PID: 3520)
Reads the computer name
- Pubg Esp Aim Full_nls..scr (PID: 2040)
- 111111111111111111111111_PROTECTED.EXE (PID: 3932)
- 31.EXE (PID: 1616)
- RegAsm.exe (PID: 3404)
- Pubg Esp Aim Full_nls.(1).scr (PID: 2372)
- 111111111111111111111111_PROTECTED.EXE (PID: 1124)
- 31.EXE (PID: 1128)
- RegAsm.exe (PID: 1908)
Checks supported languages
- Pubg Esp Aim Full_nls..scr (PID: 2040)
- 111111111111111111111111_PROTECTED.EXE (PID: 3932)
- 31.EXE (PID: 1616)
- RegAsm.exe (PID: 3404)
- 111111111111111111111111_PROTECTED.EXE (PID: 1124)
- 31.EXE (PID: 1128)
- RegAsm.exe (PID: 1908)
- Pubg Esp Aim Full_nls.(1).scr (PID: 2372)
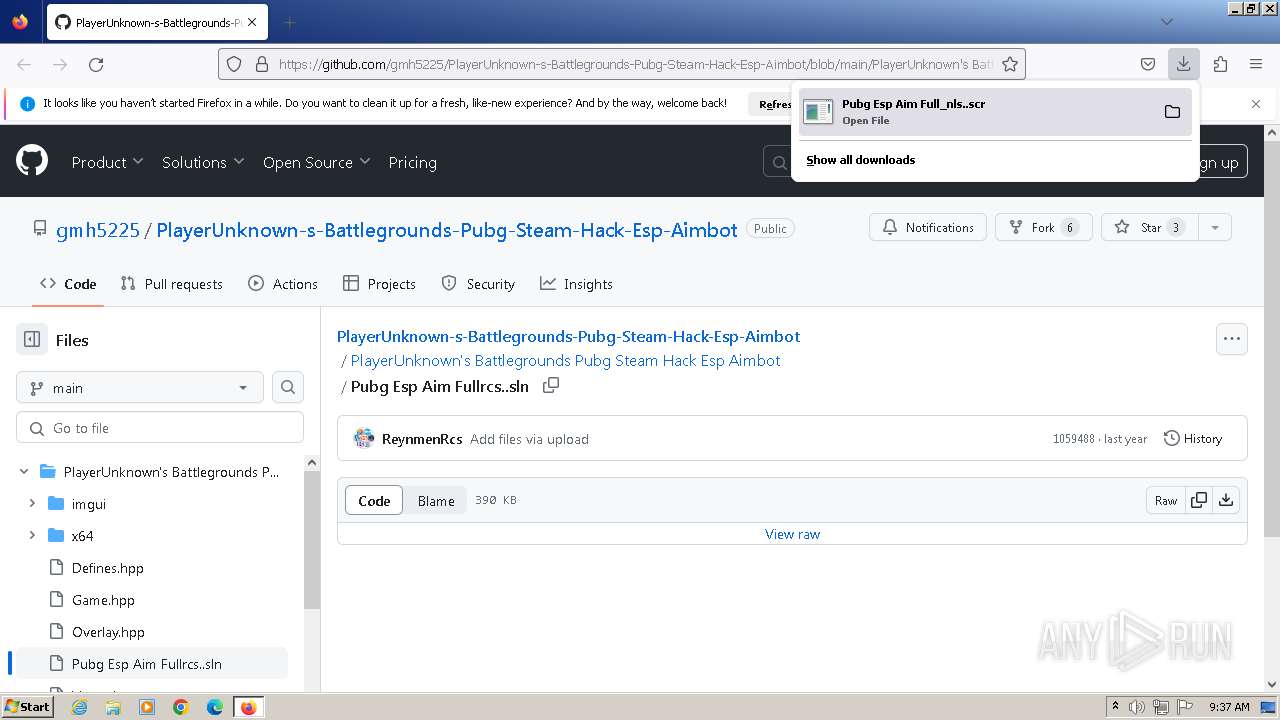
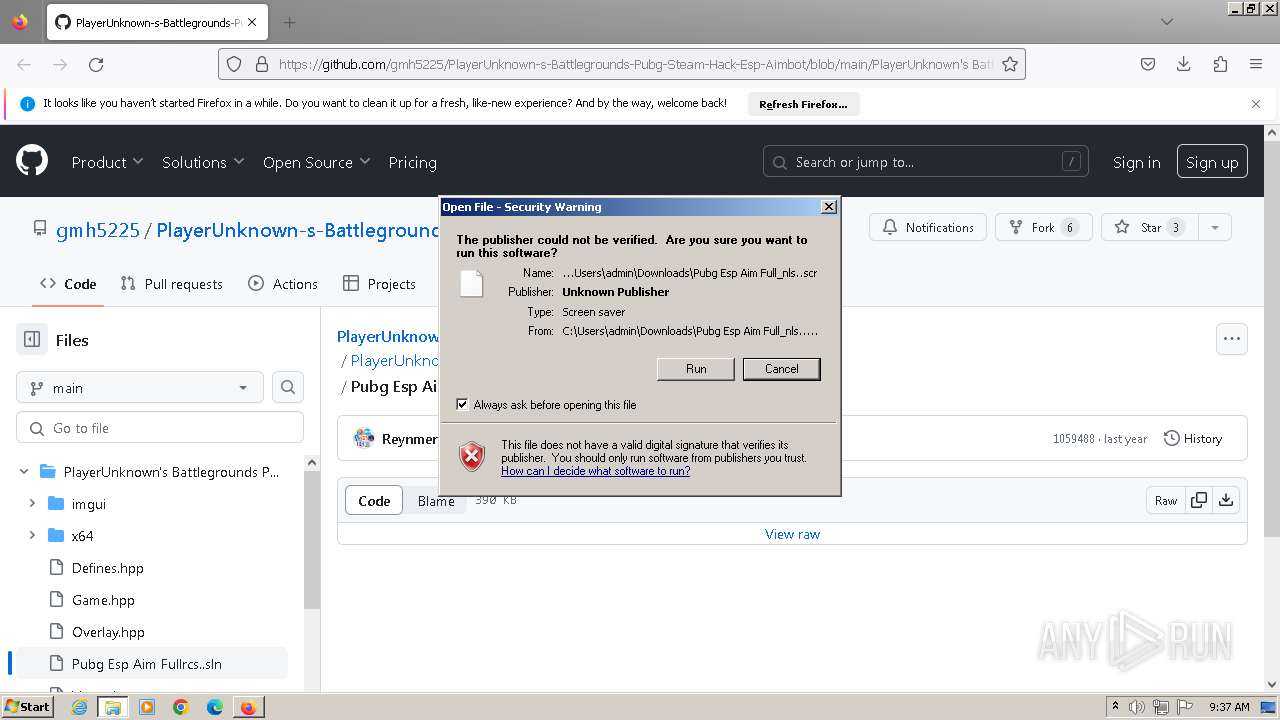
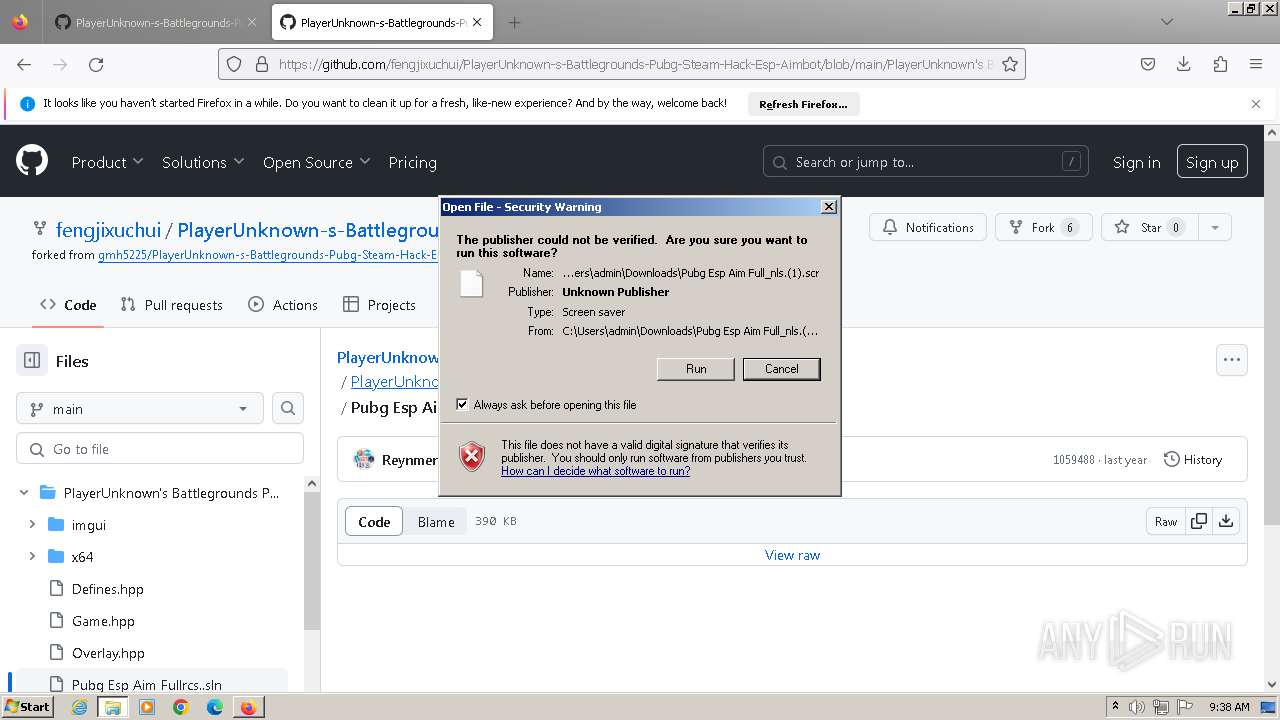
Manual execution by a user
- Pubg Esp Aim Full_nls..scr (PID: 2040)
- Pubg Esp Aim Full_nls.(1).scr (PID: 2372)
Creates files or folders in the user directory
- Pubg Esp Aim Full_nls..scr (PID: 2040)
- 111111111111111111111111_PROTECTED.EXE (PID: 3932)
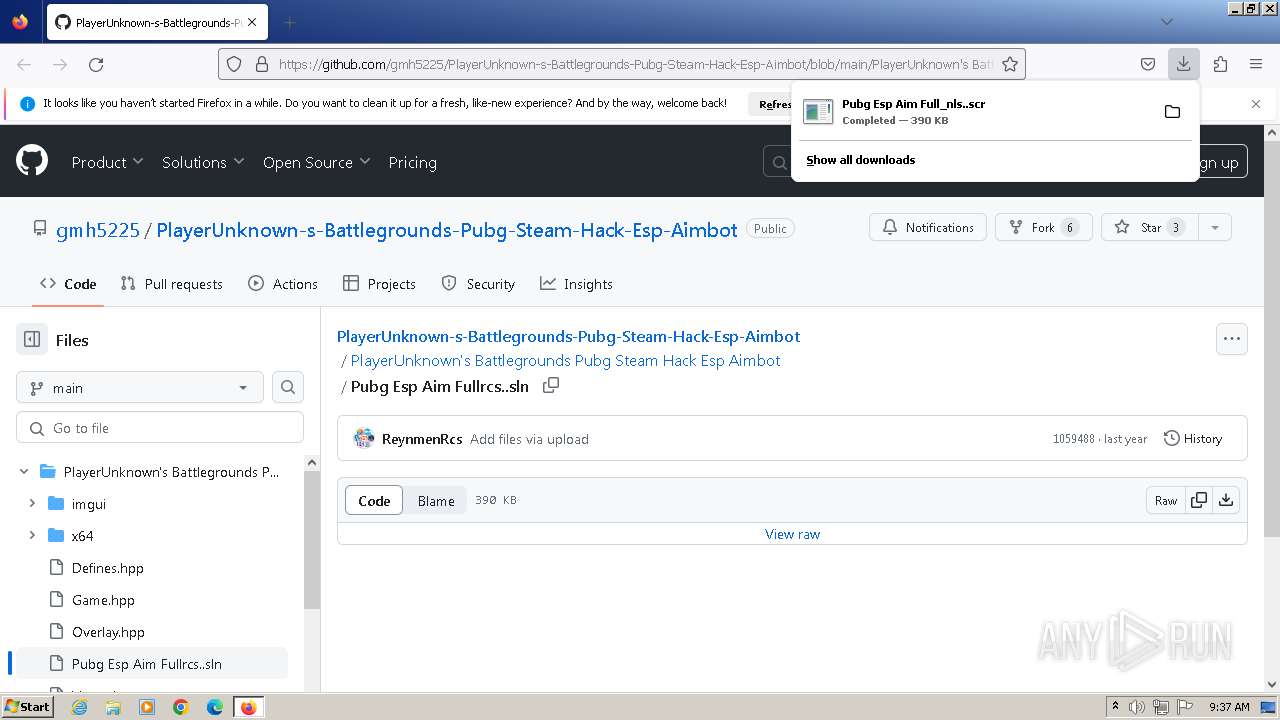
The process uses the downloaded file
- firefox.exe (PID: 3520)
Drops the executable file immediately after the start
- firefox.exe (PID: 3520)
Reads the machine GUID from the registry
- 111111111111111111111111_PROTECTED.EXE (PID: 3932)
- RegAsm.exe (PID: 3404)
- 111111111111111111111111_PROTECTED.EXE (PID: 1124)
- RegAsm.exe (PID: 1908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(3404) RegAsm.exe
C2 (1)217.64.31.3
Ports (2)8808
8437
BotnetWindows Session Manager
Version0.5.7B
Options
AutoRunfalse
MutexWindows Session Manager
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE4jCCAsqgAwIBAgIQAJmupDKFEn4QYTi6VNAu5zANBgkqhkiG9w0BAQ0FADASMRAwDgYDVQQDDAd3YXJyaW9yMCAXDTIyMDEzMDE3MzkzNFoYDzk5OTkxMjMxMjM1OTU5WjASMRAwDgYDVQQDDAd3YXJyaW9yMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA1p1heFXbFVfmtOd5Qw+jVCq6buTiUXzCHJ9ogNwGpJyyNyN70miKC4VIi30fCZ1IXcc8rAM4ODRzPV6HEPOKw29lKaG6kXtr...
Server_SignatureC79KvAXqeWNypPjSnsZWSXqvPH8g8lK8T3NJEMNEtmPa9vyqYMEPuTK4ruE1X78a31N52HJRyci/di8uAIUIzjKA2O+IDXtADiKhcOMQ774osQokab44CwyuP6B9b1dwDPJtqM9QTWZ845u9x8KwIt2lEp/qJivLP62rwCy+Er7Ii9VJyRxynu3T2CO9nBmRpDk1MnOajwGmWuoXOWP6tz21sp1d/RCrAkM9A+iVAnvyS3DrNM6jxvX8GEyi7alq9aMNUajm8VifQL82ZjapIyvETNyHsQHNFGmbksM/eY2W...
Keys
AES3d743405c5b7f48e626e812c0257eaef5c78eda6d768679cf0126960a60a9032
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
70
Monitored processes
27
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3520.7.436003563\877842779" -childID 6 -isForBrowser -prefsHandle 4020 -prefMapHandle 4016 -prefsLen 34436 -prefMapSize 244195 -jsInitHandle 908 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {f415f414-e2fc-4092-b27b-43872a05ae74} 3520 "\\.\pipe\gecko-crash-server-pipe.3520" 3908 198f8840 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1124 | "C:\Users\admin\AppData\Roaming\111111111111111111111111_PROTECTED.EXE" | C:\Users\admin\AppData\Roaming\111111111111111111111111_PROTECTED.EXE | — | Pubg Esp Aim Full_nls.(1).scr | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1128 | "C:\Users\admin\AppData\Roaming\31.EXE" | C:\Users\admin\AppData\Roaming\31.EXE | — | Pubg Esp Aim Full_nls.(1).scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Media Foundation Protected Pipeline EXE Exit code: 0 Version: 10,0,19041,1 (WinBuild Modules
| |||||||||||||||
| 1180 | "powershell.exe" Remove -ItemProperty -Path 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run' -Name 'Windows Session Manager';New-ItemProperty -Path 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run' -Name 'Windows Session Manager' -Value '"C:\Users\admin\AppData\Roaming\Windows Session Manager\Windows Session Manager.exe"' -PropertyType 'String' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | 111111111111111111111111_PROTECTED.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1616 | "C:\Users\admin\AppData\Roaming\31.EXE" | C:\Users\admin\AppData\Roaming\31.EXE | — | Pubg Esp Aim Full_nls..scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Media Foundation Protected Pipeline EXE Exit code: 0 Version: 10,0,19041,1 (WinBuild Modules
| |||||||||||||||
| 1908 | #cmd | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | 111111111111111111111111_PROTECTED.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3520.0.1464500087\397391409" -parentBuildID 20230710165010 -prefsHandle 1104 -prefMapHandle 1096 -prefsLen 28523 -prefMapSize 244195 -appDir "C:\Program Files\Mozilla Firefox\browser" - {2305f888-ea0a-4911-8d80-51296d1adca2} 3520 "\\.\pipe\gecko-crash-server-pipe.3520" 1188 d7ad1b0 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\Downloads\Pubg Esp Aim Full_nls..scr" /S | C:\Users\admin\Downloads\Pubg Esp Aim Full_nls..scr | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2372 | "C:\Users\admin\Downloads\Pubg Esp Aim Full_nls.(1).scr" /S | C:\Users\admin\Downloads\Pubg Esp Aim Full_nls.(1).scr | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2420 | "cmd" /C schtasks /create /tn \Windows Session Manager /tr "C:\Users\admin\AppData\Roaming\Windows Session Manager\Windows Session Manager.exe" /st 00:00 /du 9999:59 /sc once /ri 60 /f | C:\Windows\System32\cmd.exe | — | 111111111111111111111111_PROTECTED.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2147500037 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
21 117
Read events
20 745
Write events
372
Delete events
0
Modification events
| (PID) Process: | (3828) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 2166C0A101000000 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 044CC1A101000000 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SetDefaultBrowserUserChoice |
Value: 1 | |||
| (PID) Process: | (3520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|AppLastRunTime |
Value: D14E5F3C23B0D901 | |||
Executable files
11
Suspicious files
194
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3520 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:60E0DE9E05EC76C749D80F0D15A81B21 | SHA256:08252FA62CCCCD316474E20CC7317A6B5C932B2C972234318E8CCDA39EC2EF48 | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:B7A3C61D0C144CC5E166B1E769CA8F8C | SHA256:7FADCB77FFACA6B9E9F15C6F1CD3AAD4C20DCD90FA92429A627A3A7110CA2644 | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\activity-stream.discovery_stream.json.tmp | binary | |
MD5:56E00184320C47E259595C991123CE54 | SHA256:2A0190D4E1EE1FAD7A85EEA792117A4D138405AA9DA21356612B7FD3CE2021C1 | |||
| 3520 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage.sqlite-journal | binary | |
MD5:E043E67E3CDBE9025CBB728FF2A2D9F3 | SHA256:9A512370FC13D3F69D77835B426485D36DAC6024708F55D93E111C90B78D6109 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
82
DNS requests
160
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3520 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | unknown |
3520 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 471 b | unknown |
3520 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 312 b | unknown |
3520 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 312 b | unknown |
3520 | firefox.exe | POST | 200 | 184.24.77.57:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
3520 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 471 b | unknown |
3520 | firefox.exe | POST | 200 | 184.24.77.57:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
3520 | firefox.exe | POST | — | 184.24.77.57:80 | http://r3.o.lencr.org/ | DE | — | — | unknown |
3520 | firefox.exe | POST | 200 | 184.24.77.57:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
3520 | firefox.exe | POST | 200 | 52.222.229.217:80 | http://ocsp.r2m02.amazontrust.com/ | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3520 | firefox.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
3520 | firefox.exe | 142.250.184.234:443 | safebrowsing.googleapis.com | — | — | whitelisted |
3520 | firefox.exe | 34.117.65.55:443 | push.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3520 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
3520 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | unknown |
3520 | firefox.exe | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3520 | firefox.exe | 142.250.181.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3520 | firefox.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3520 | firefox.exe | 34.199.39.224:443 | spocs.getpocket.com | AMAZON-AES | US | unknown |
3520 | firefox.exe | 185.199.111.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
ipv4only.arpa |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
spocs.getpocket.com |
| shared |
fp2e7a.wpc.phicdn.net |
| whitelisted |
proxyserverecs-1736642167.us-east-1.elb.amazonaws.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
3288 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3288 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3080 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3080 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
Process | Message |
|---|---|
Pubg Esp Aim Full_nls..scr | C:\Users\admin\AppData\Roaming\111111111111111111111111_PROTECTED.EXE |
Pubg Esp Aim Full_nls..scr | C:\Users\admin\AppData\Roaming\31.EXE |
Pubg Esp Aim Full_nls.(1).scr | C:\Users\admin\AppData\Roaming\111111111111111111111111_PROTECTED.EXE |
Pubg Esp Aim Full_nls.(1).scr | C:\Users\admin\AppData\Roaming\31.EXE |