| File name: | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0 |
| Full analysis: | https://app.any.run/tasks/d27175ba-4caa-42e0-b26f-ed3f3de0c105 |
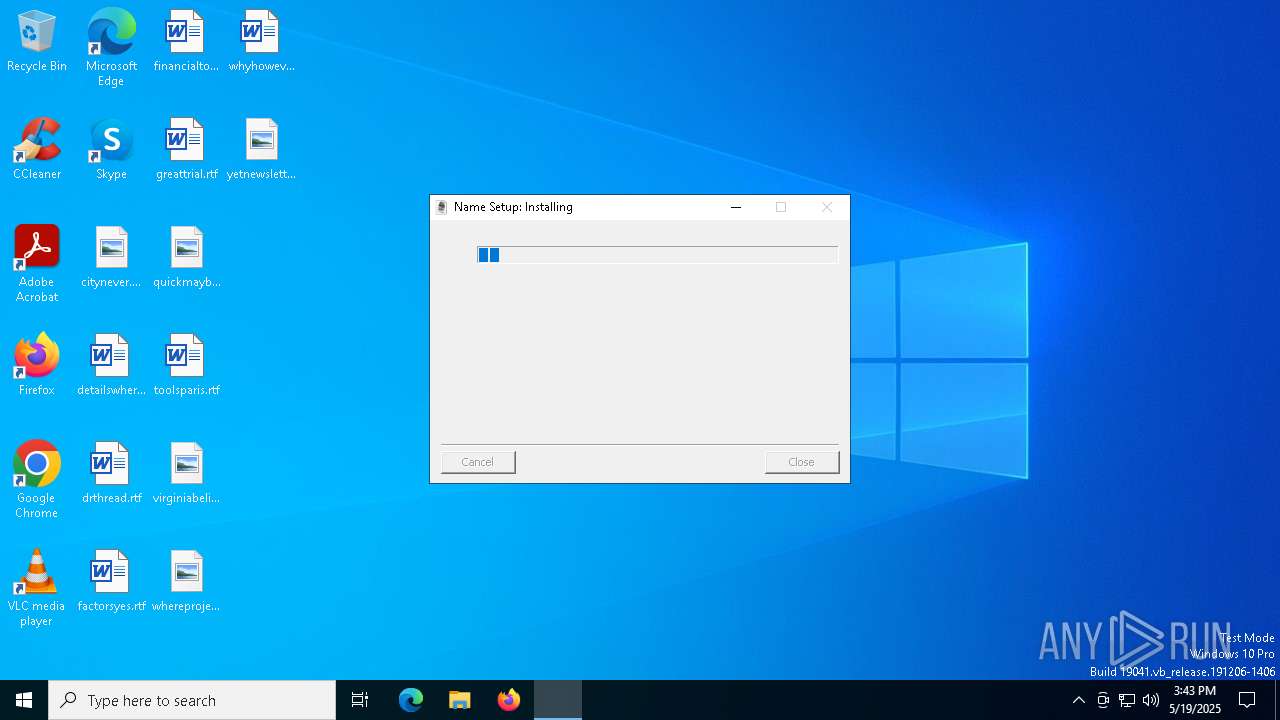
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | May 19, 2025, 15:43:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | A412943D7658CB194744FFA4008F6944 |
| SHA1: | 48C5A3B7315C869C93723AE041E38610A32E9555 |
| SHA256: | 2540722D53870E6DBE6FD73D56B3E12C20D9F4C29FC6D325D6CFD471D8E44EA0 |
| SSDEEP: | 49152:PnHNXOxO9VPaNPEdDGsjpiW0TirIHxNcZAVCG35d/OkYtLch73Qnq2nIzZ0Kr3jO:PnU0sNcksFiW+0UxNcZbG379ic53GnnD |
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 7492)
- findstr.exe (PID: 7632)
RHADAMANTHYS mutex has been found
- Acids.pif (PID: 7864)
- dialer.exe (PID: 960)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe (PID: 7352)
- cmd.exe (PID: 7400)
Reads security settings of Internet Explorer
- 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe (PID: 7352)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7400)
Suspicious file concatenation
- cmd.exe (PID: 7836)
Get information on the list of running processes
- cmd.exe (PID: 7400)
Executable content was dropped or overwritten
- cmd.exe (PID: 7400)
Executing commands from ".cmd" file
- 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe (PID: 7352)
Application launched itself
- cmd.exe (PID: 7400)
Starts application with an unusual extension
- cmd.exe (PID: 7400)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7400)
The executable file from the user directory is run by the CMD process
- Acids.pif (PID: 7864)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7400)
The process checks if it is being run in the virtual environment
- dialer.exe (PID: 960)
Connects to unusual port
- dialer.exe (PID: 960)
Executes application which crashes
- Acids.pif (PID: 7864)
INFO
Reads the computer name
- 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe (PID: 7352)
- Acids.pif (PID: 7864)
Creates files or folders in the user directory
- 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe (PID: 7352)
Process checks computer location settings
- 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe (PID: 7352)
Creates a new folder
- cmd.exe (PID: 7760)
Checks supported languages
- 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe (PID: 7352)
- Acids.pif (PID: 7864)
Manual execution by a user
- dialer.exe (PID: 960)
Reads mouse settings
- Acids.pif (PID: 7864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:24 22:17:55+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x348f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
146
Monitored processes
16
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\WINDOWS\system32\dialer.exe" | C:\Windows\SysWOW64\dialer.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Phone Dialer Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6972 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7864 -s 956 | C:\Windows\SysWOW64\WerFault.exe | — | Acids.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7352 | "C:\Users\admin\AppData\Local\Temp\2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe" | C:\Users\admin\AppData\Local\Temp\2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7400 | "C:\Windows\System32\cmd.exe" /k move Less Less.cmd & Less.cmd & exit | C:\Windows\SysWOW64\cmd.exe | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 9009 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7408 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7484 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7492 | findstr /I "wrsa.exe opssvc.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7624 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7632 | findstr /I "avastui.exe avgui.exe nswscsvc.exe sophoshealth.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7676 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 356
Read events
2 355
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7864) Acids.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\SibCode |
| Operation: | write | Name: | sn |
Value: | |||
Executable files
1
Suspicious files
35
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Procedure | binary | |
MD5:1011E7358B38486F66E531BE8F9C4985 | SHA256:04D545B5004B2F701944662AB5F52F71C172EDBFC22ECAF8C7E2636F8845D4C8 | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Details | binary | |
MD5:F27EB7F5AB846565B07136DFF3854D04 | SHA256:038E9D2FCB5A96E58578A86DA12405D2F55092611BAEF430EE646FF49B4AE9CE | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Hospital | binary | |
MD5:EB6864F48FB594E9FF3F0BEFA0438B4D | SHA256:7F5DA2DC0751033123891B6EF7B68EC4AC1C0DC65C31FACA0D0C068EA350214C | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Define | binary | |
MD5:202A35EF8DCD178FB841D6E99E0B7C1A | SHA256:283F5B09AE4DB48C339B623AF6026B2874CDD8CCA35EF701D76086965DEBF9B5 | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Suggestion | binary | |
MD5:67E121CBC751C47CFF1E39491794D1EF | SHA256:C16FA37A9216BF5F79A499495F37A5B4A1164BDD0C12CC79036D959D4A902784 | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Tions | binary | |
MD5:7DEC42889955562AD6E8B7EB23527B74 | SHA256:BEB7024232A41F9701F597AB2B369B6867C6AE2496EF2F08331D810A8A4AF522 | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Definitions | binary | |
MD5:D3D3097005A2FD1C63157A190918B91B | SHA256:9C51EA9774E1E05F91AB9C0B037909C5213650D35ADB4E56C34F9F2B93DCD1A8 | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Meal | binary | |
MD5:CE22AF53698BDAC9A842C8CAE4D342EF | SHA256:3760BD821A7A7D4E7F324CEE627855593921580EAEE160A44F21E7EFFA6CA687 | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Pays | binary | |
MD5:034BE95C63282436D0C8AB363B8C51BC | SHA256:62E2A8C8ACB1D64895CDB5ED42951543B154F16885C44F646DA53FDAE3139057 | |||
| 7352 | 2540722d53870e6dbe6fd73d56b3e12c20d9f4c29fc6d325d6cfd471d8e44ea0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Bio | binary | |
MD5:6AD761198331E44400A57E38EE54534D | SHA256:6D7AACB79D194A91B05A4362BE8C9AAE80C484F3768A27D00CE298FCEE9AA6E6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
28
DNS requests
14
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6728 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6728 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.16:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6728 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
RCzHoFfoHp.RCzHoFfoHp |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
960 | dialer.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 34 |