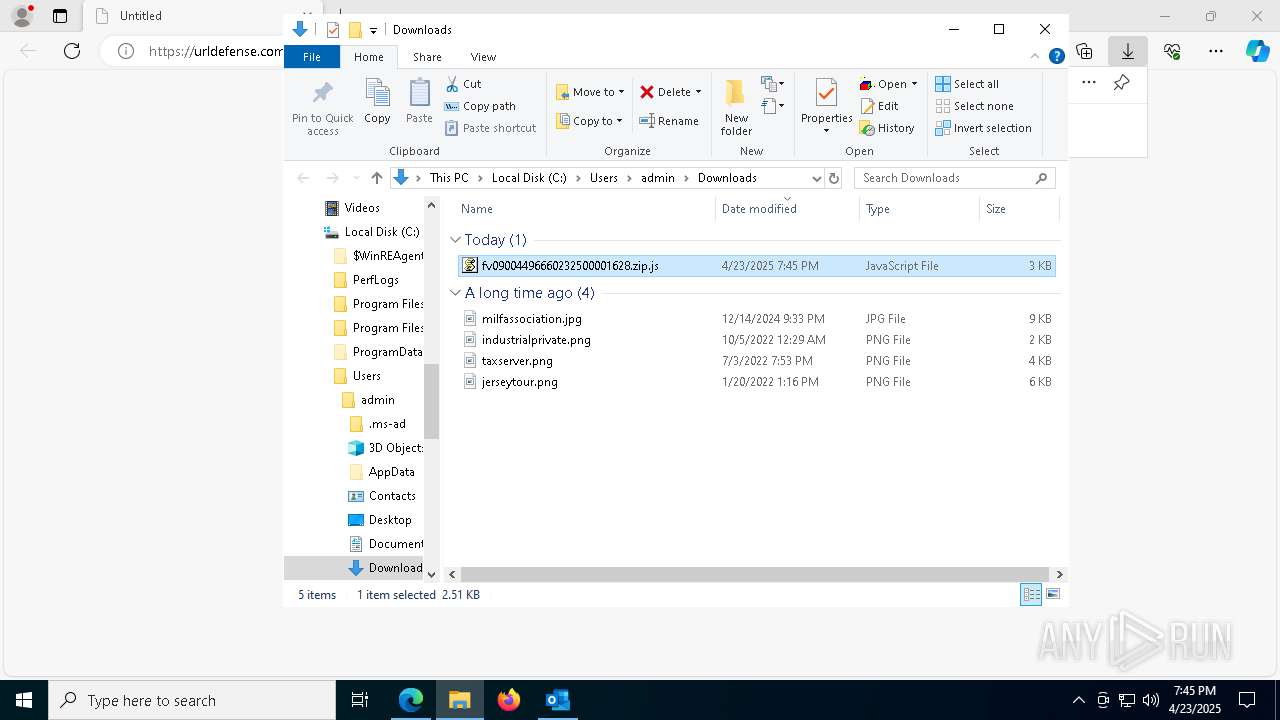
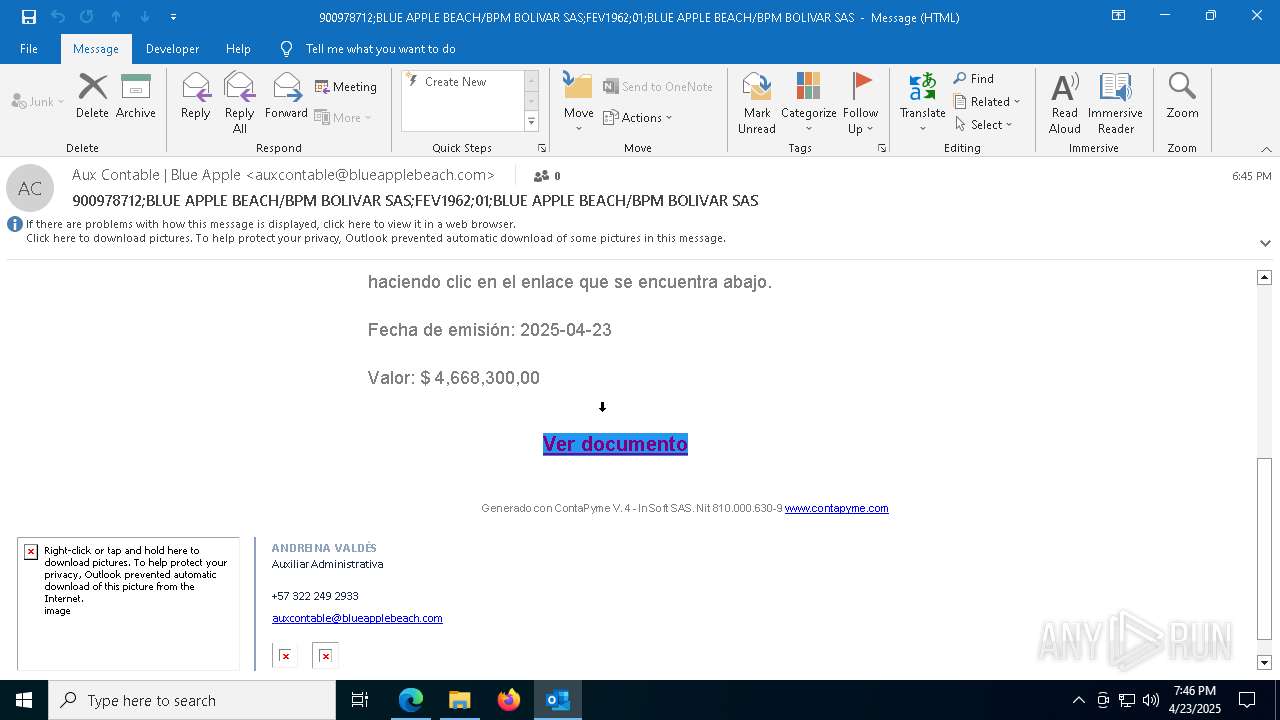
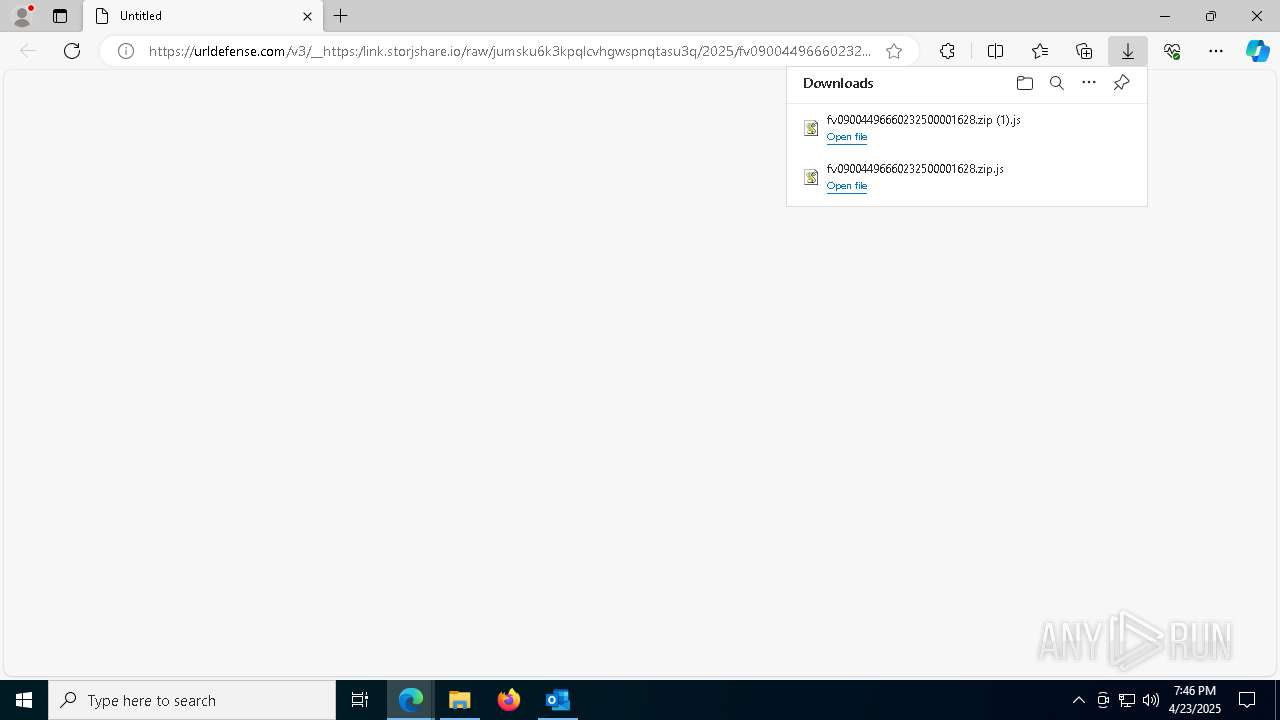
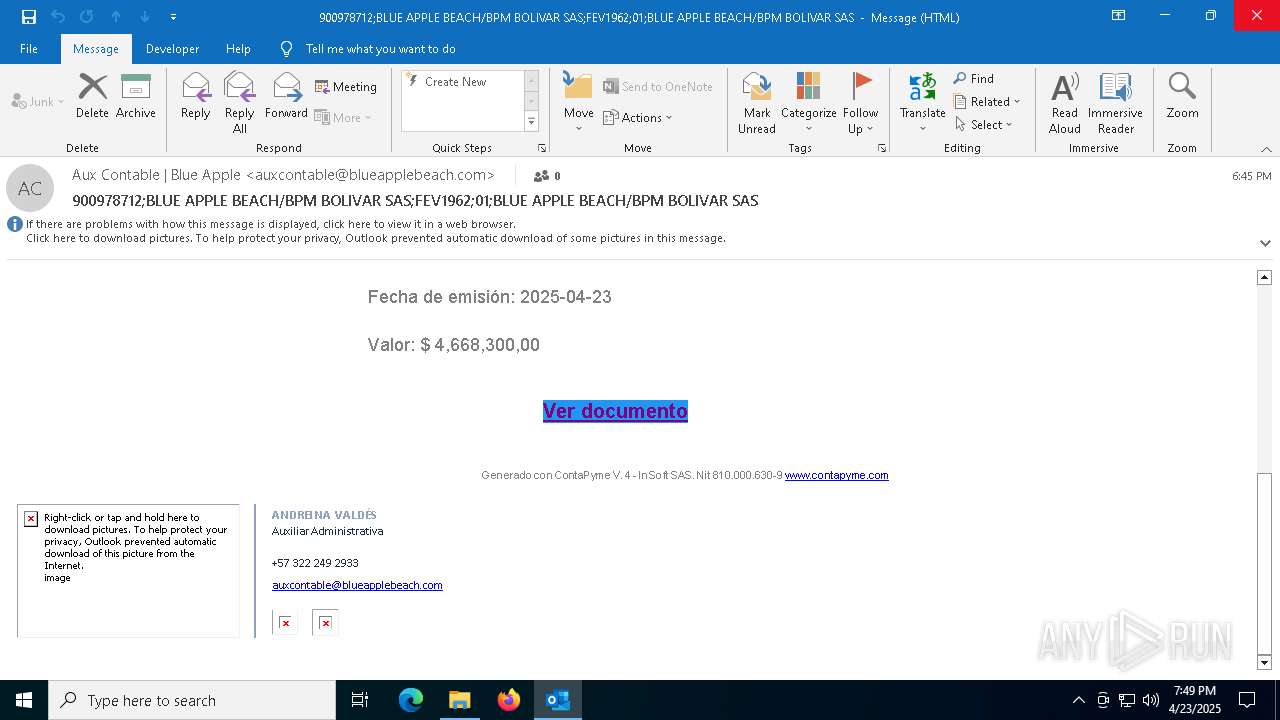
| File name: | 900978712_BLUE_APPLE_BEACH_BPM_BOLIVAR_SAS_FEV1962_01_BLUE_APPLE___BEACH_BPM_BOLIVAR_SAS.eml |
| Full analysis: | https://app.any.run/tasks/b72c063e-3e3b-48c4-8965-b7cec0c732f2 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 23, 2025, 19:44:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | ABA4995C2DB1842D65D20E4520A7179D |
| SHA1: | B03324547B9DF219FC3F388EE58762FC27AD1F40 |
| SHA256: | 2517AD3CEC8E67B226D730ECCAF1796078B771D1C170CB8A3BD2844182BABF60 |
| SSDEEP: | 384:Bj52PdgaK1prikRWhuxNk2NoZvrcLbRR/qWC5llg5e4wtAlY7X6Ajy:Bj52nK1p+k00xS2CF8bRR//elf4tle6Z |
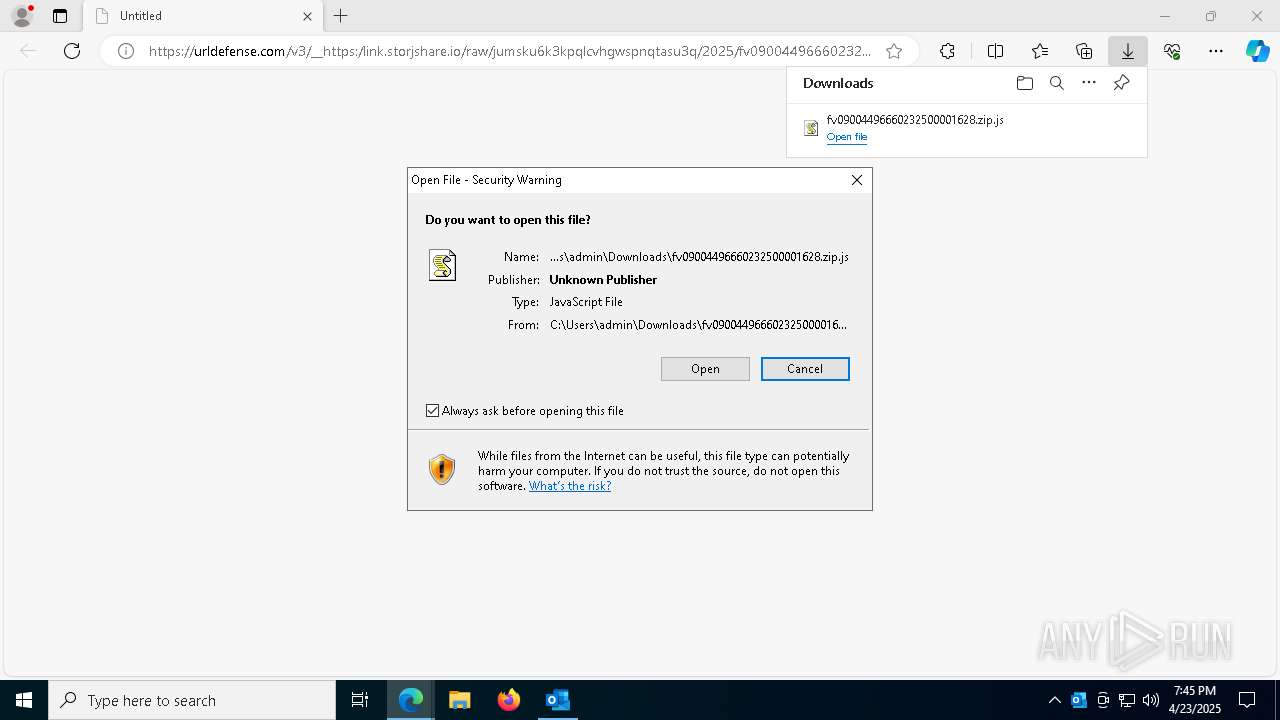
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
Run PowerShell with an invisible window
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
ASYNCRAT has been detected (SURICATA)
- jsc.exe (PID: 5384)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
ASYNCRAT has been detected (YARA)
- jsc.exe (PID: 5384)
SUSPICIOUS
Potential Corporate Privacy Violation
- wscript.exe (PID: 6456)
- powershell.exe (PID: 7864)
- wscript.exe (PID: 6644)
- powershell.exe (PID: 5200)
- wscript.exe (PID: 4488)
- powershell.exe (PID: 5228)
- wscript.exe (PID: 7872)
- powershell.exe (PID: 5212)
Base64-obfuscated command line is found
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
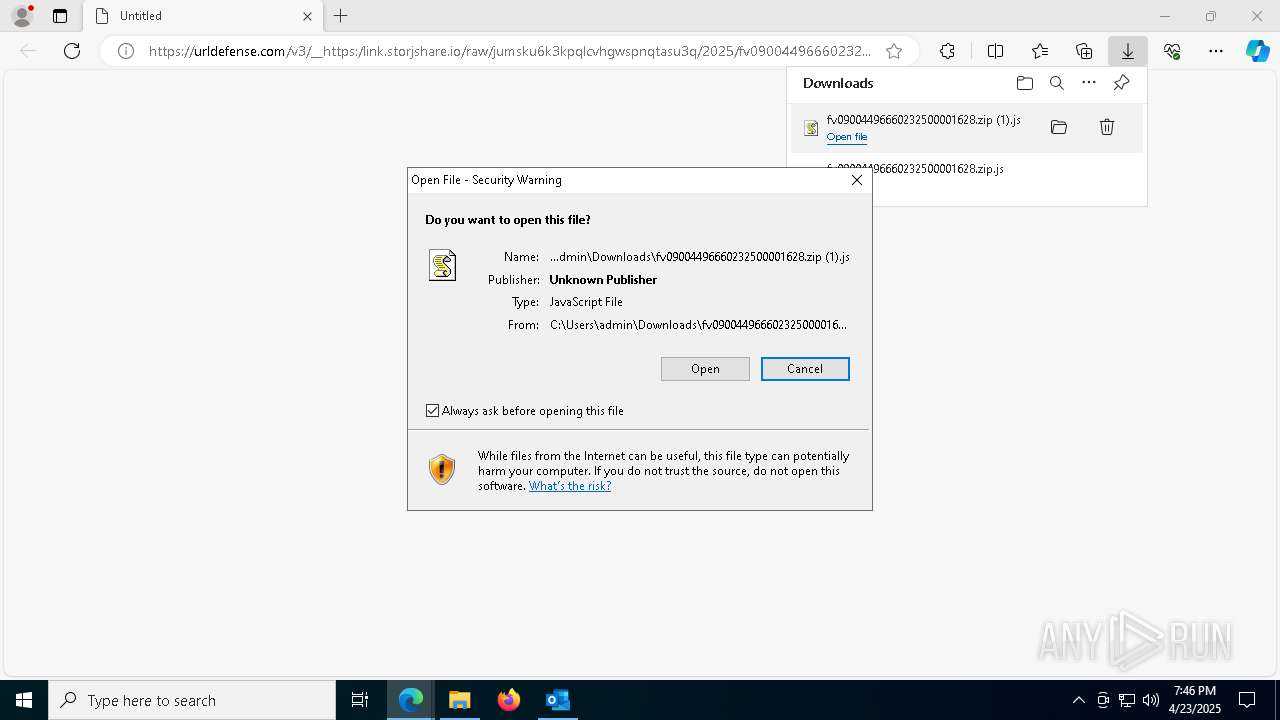
The process executes JS scripts
- msedge.exe (PID: 2244)
Executes script without checking the security policy
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6456)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- wscript.exe (PID: 7872)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7864)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 900)
Contacting a server suspected of hosting an CnC
- jsc.exe (PID: 5384)
Connects to unusual port
- jsc.exe (PID: 5384)
INFO
Checks supported languages
- identity_helper.exe (PID: 720)
- jsc.exe (PID: 5384)
- jsc.exe (PID: 2984)
- jsc.exe (PID: 5740)
- jsc.exe (PID: 6940)
Reads Environment values
- identity_helper.exe (PID: 720)
- identity_helper.exe (PID: 1704)
Reads the computer name
- identity_helper.exe (PID: 720)
- jsc.exe (PID: 5384)
- jsc.exe (PID: 2984)
- jsc.exe (PID: 5740)
- jsc.exe (PID: 6940)
- identity_helper.exe (PID: 1704)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2244)
Application launched itself
- msedge.exe (PID: 2244)
- msedge.exe (PID: 6904)
Checks proxy server information
- wscript.exe (PID: 6456)
- powershell.exe (PID: 7864)
- wscript.exe (PID: 6644)
- wscript.exe (PID: 4488)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- slui.exe (PID: 968)
- wscript.exe (PID: 7872)
- powershell.exe (PID: 5212)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
Disables trace logs
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 5212)
Reads the machine GUID from the registry
- jsc.exe (PID: 5384)
- jsc.exe (PID: 2984)
- jsc.exe (PID: 5740)
- jsc.exe (PID: 6940)
Reads the software policy settings
- slui.exe (PID: 8168)
- jsc.exe (PID: 5384)
- slui.exe (PID: 968)
.NET Reactor protector has been detected
- jsc.exe (PID: 5384)
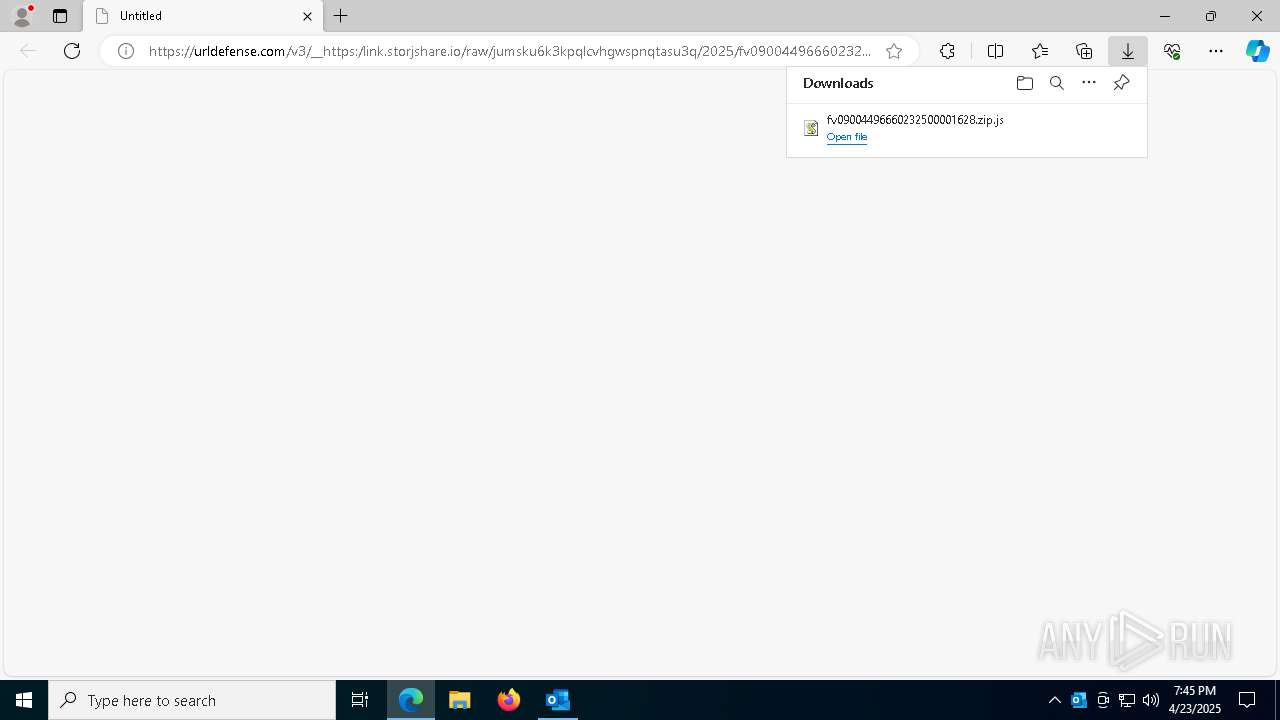
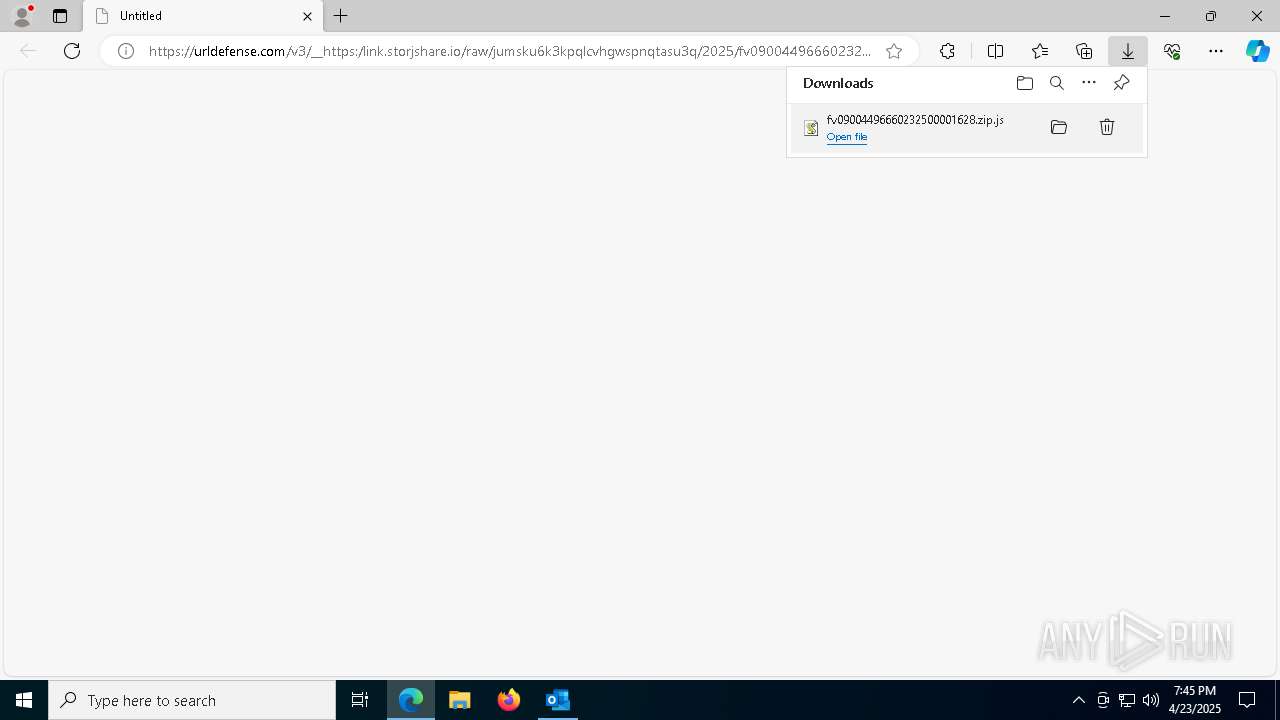
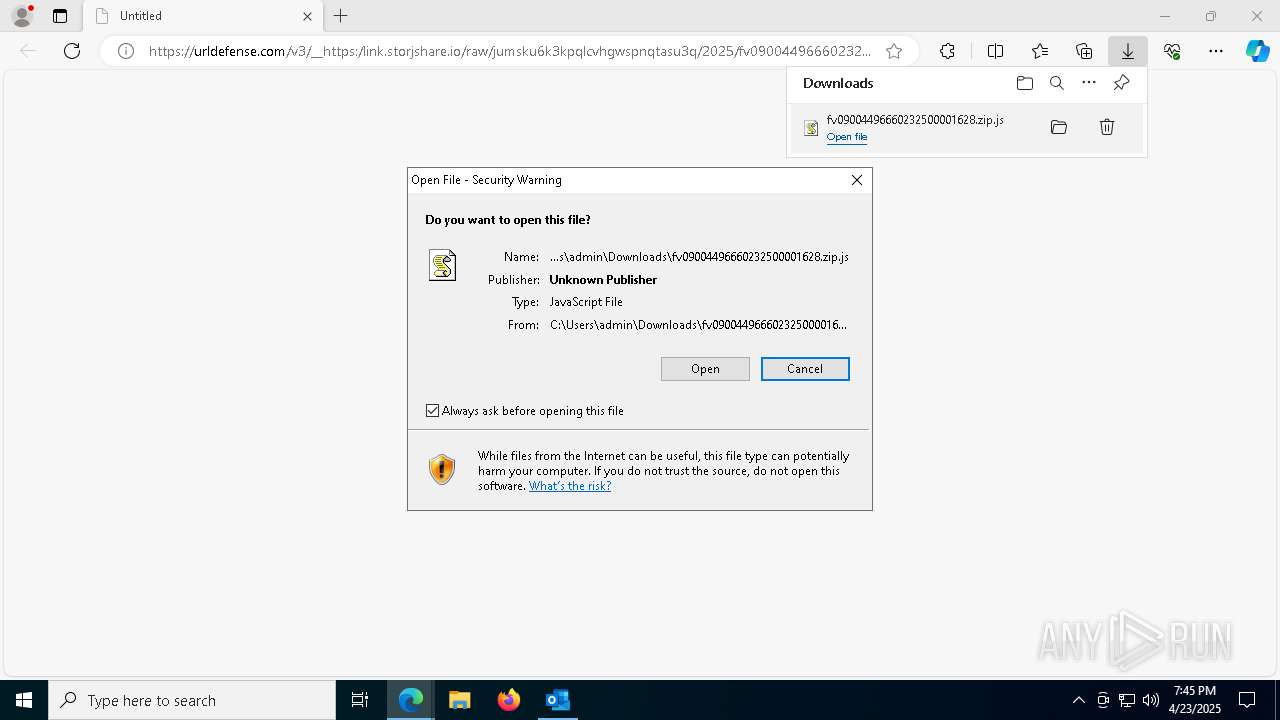
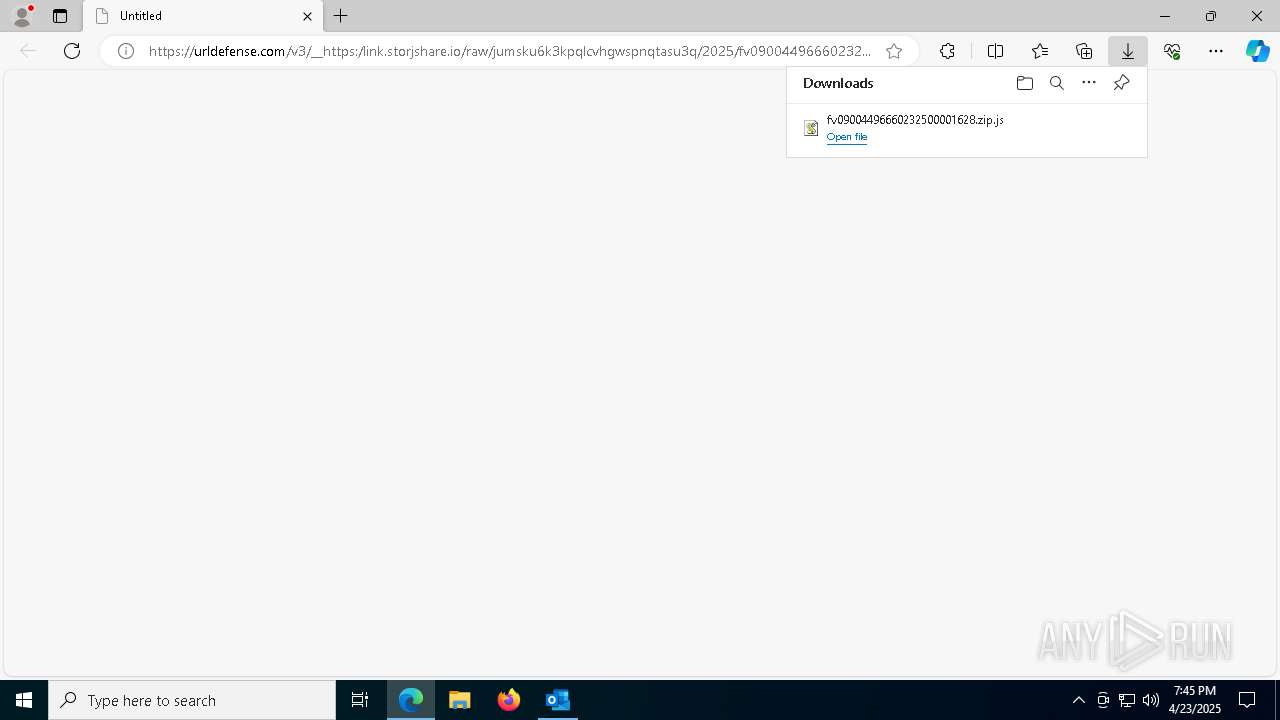
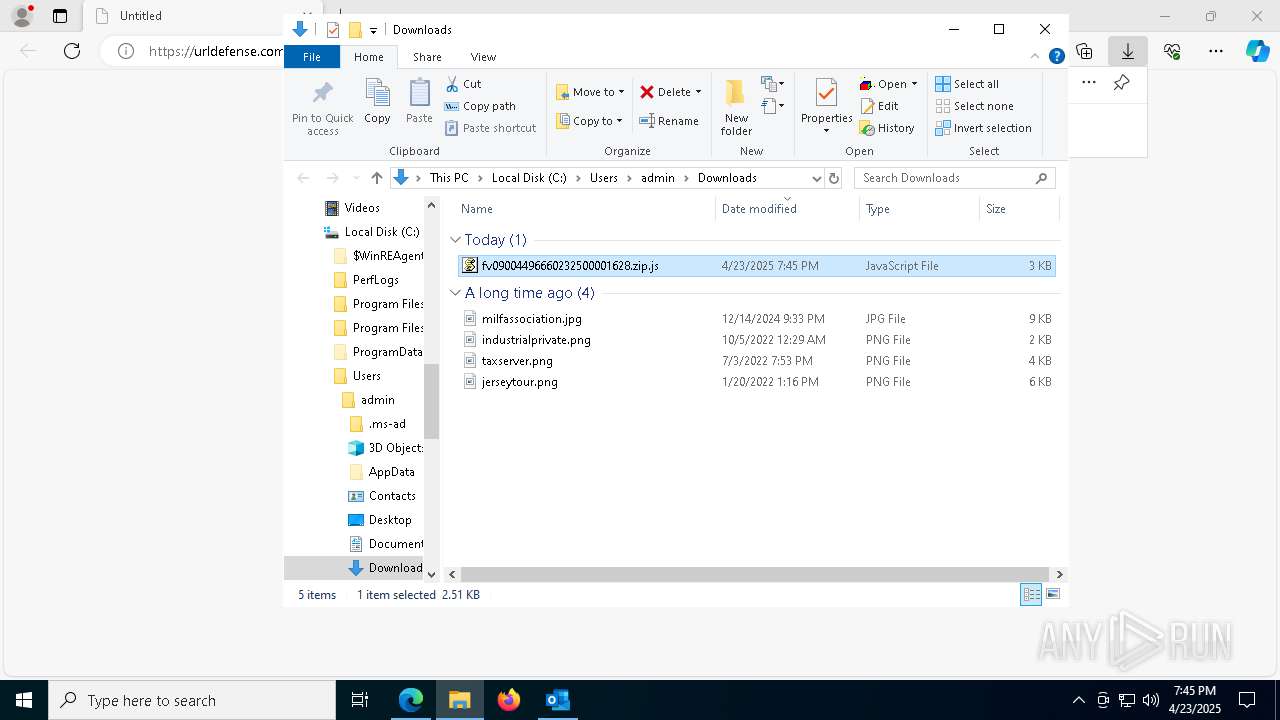
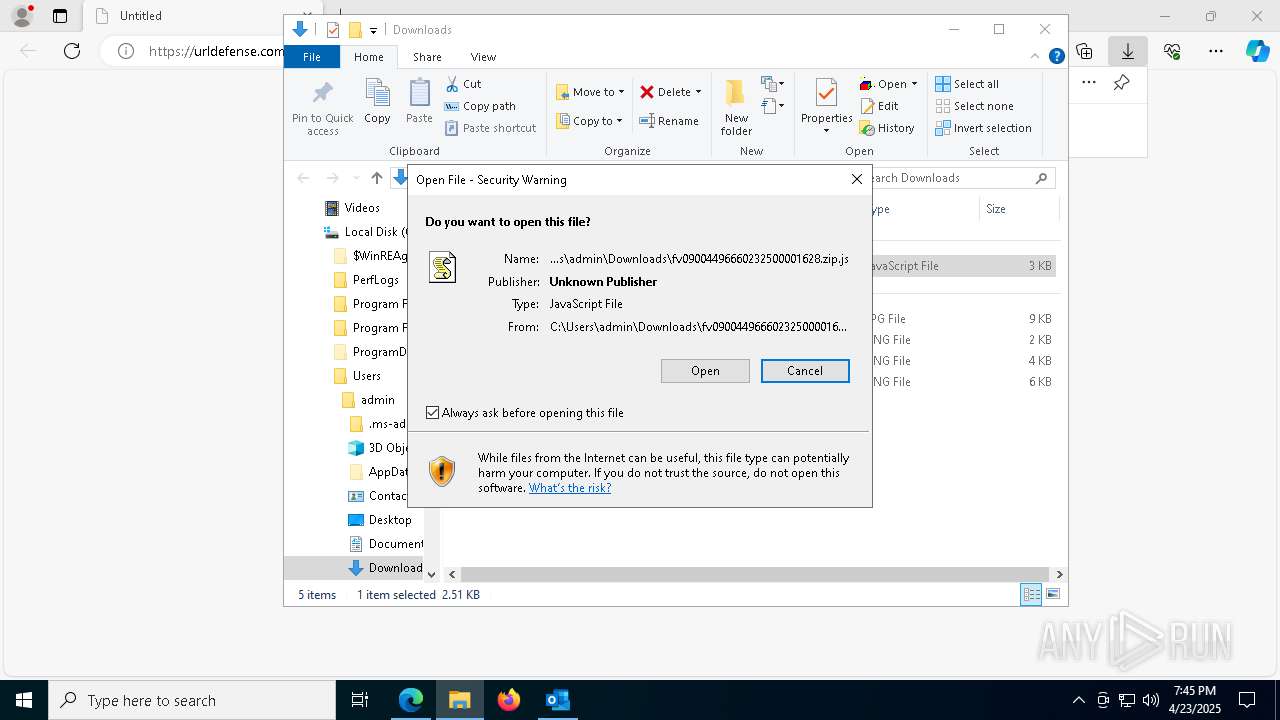
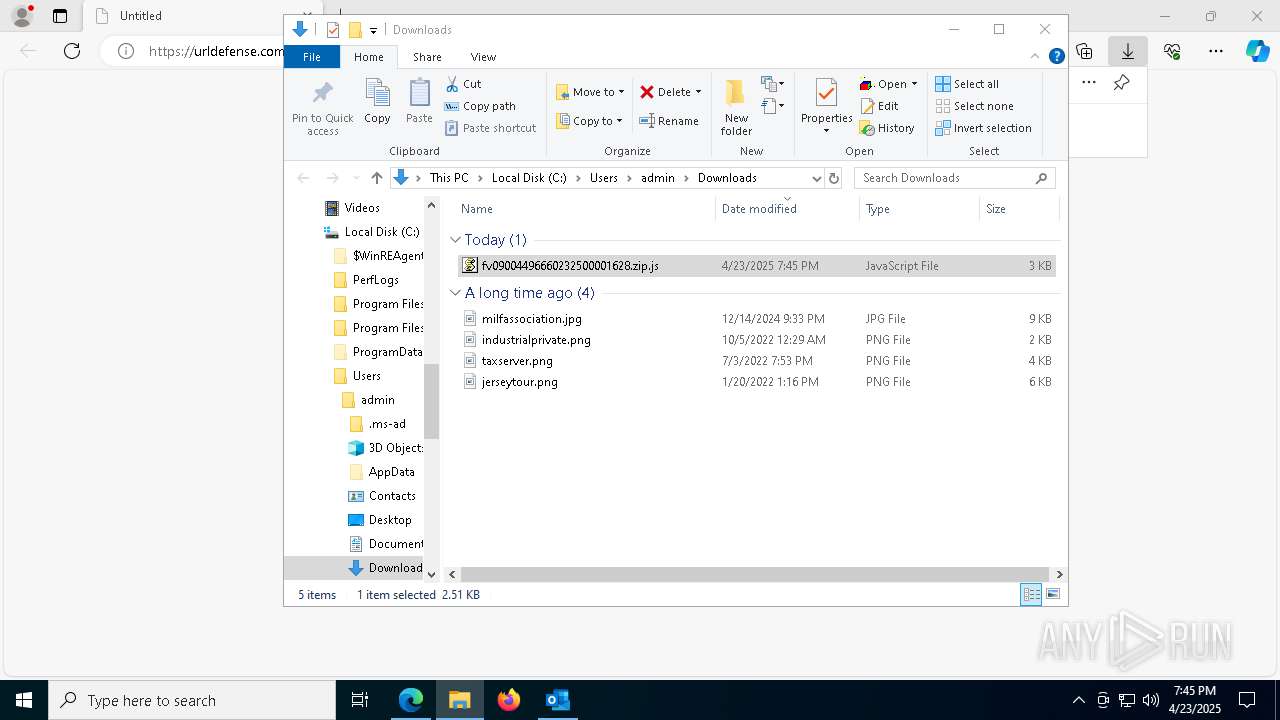
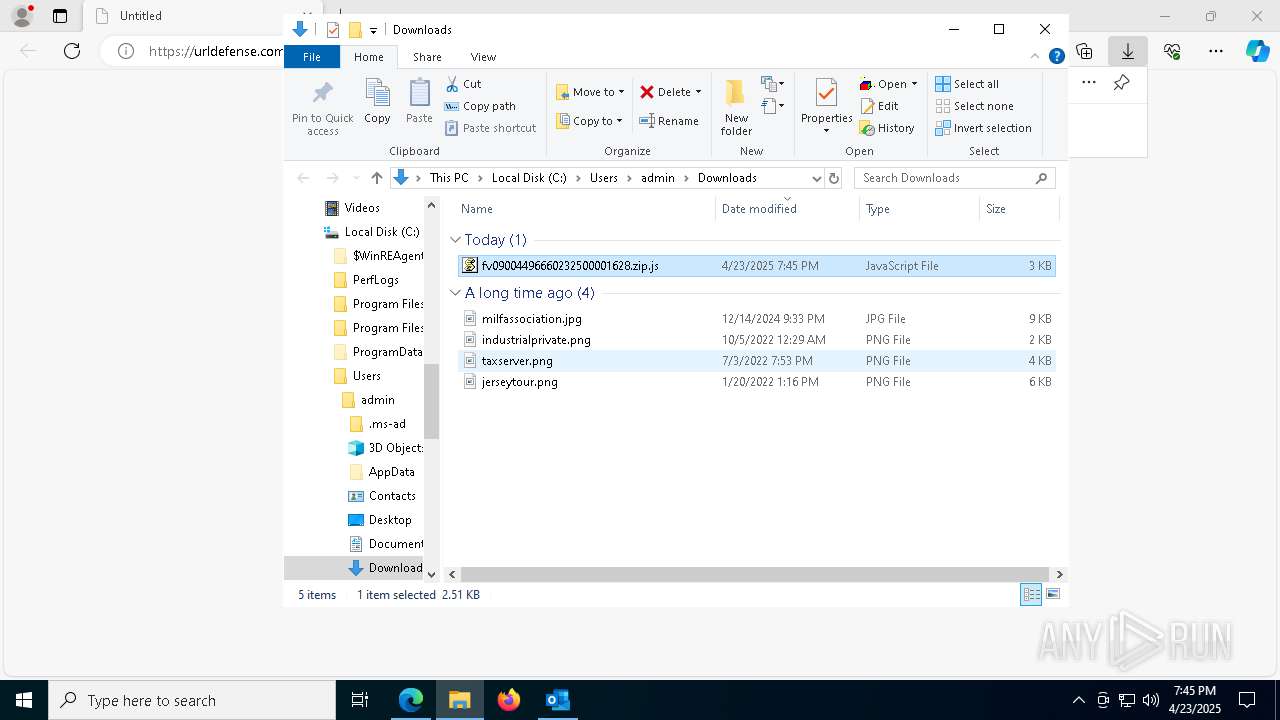
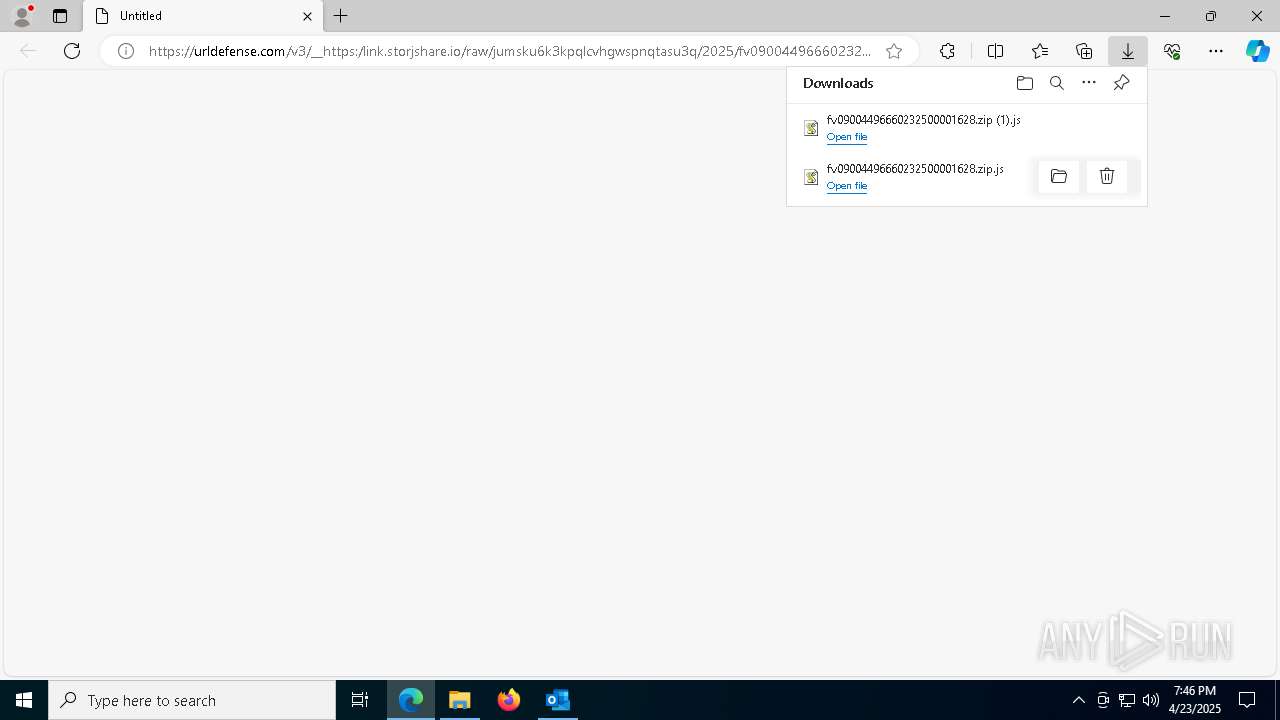
Manual execution by a user
- wscript.exe (PID: 4488)
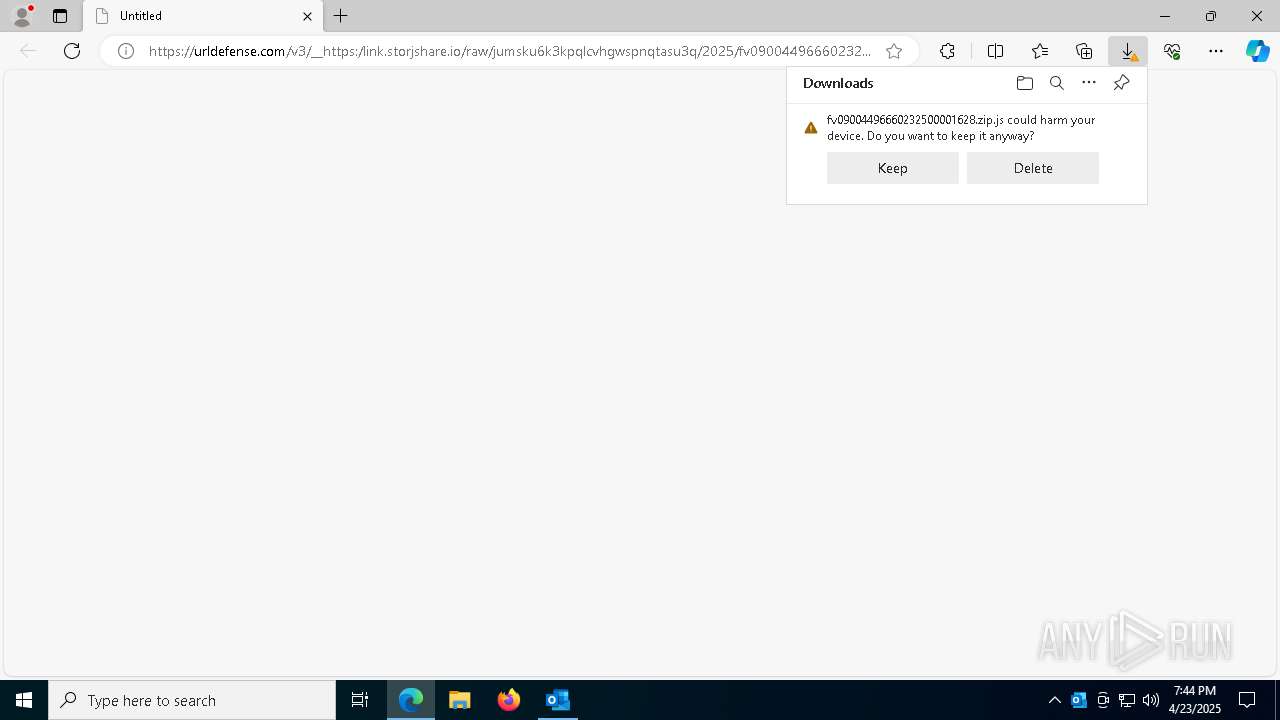
Executable content was dropped or overwritten
- msedge.exe (PID: 5796)
The sample compiled with english language support
- msedge.exe (PID: 5796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(5384) jsc.exe
C2 (1)arannsasaaransasaturituri2024.duckdns.org
Ports (1)3009
Version0.5.7B
Botnet202512
Options
AutoRunfalse
MutexMutex_6SI8Admxn
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAKxLlAkF1WRT8tAExBlQyzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwOTIwMTQyNzUwWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKrrWexesJSLqGeYC6kTxL6e4fbMdbCF6T1opNgSYFlyavRm733h8x2GXmzipr8dl/UHWmWcPmk8...
Server_SignatureaUJYEXRD16PdjWsVGUoEDC/1J06mt5QZ1omtU2iI7pPlXs4zpHUCvJet1MDT2ajfim6gAJ+FYra971v3kb3+G2GEGbjwGZ1oOYVZ8DwiaDfw7QgxRiImmT0I0CUO9+spPhTADC95gzwiceAy8MwW4b58aslG8KpEtWUQPIIJmuoj3wOLWF61XueIg6Z4HxgoYVAMxuEwwKXMqvvVSZS72Erwsjl3L+mWIhlTeZmfeNfUUxYeFK1c2dA+Uy3ZFQjyWdMUC3C1lF9ygLcF+yWNoKgG3BurqF67fO2gKbULXKwf...
Keys
AESdcdac48667980a3746d51f0c2cd7e93fe6fe063bf3f33d65e9fabcd2e3d8f36c
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
233
Monitored processes
95
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5808 --field-trial-handle=2312,i,4771563937363638449,8845051678972593161,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4324 --field-trial-handle=2312,i,4771563937363638449,8845051678972593161,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6272 --field-trial-handle=2312,i,4771563937363638449,8845051678972593161,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2412 --field-trial-handle=2312,i,4771563937363638449,8845051678972593161,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5256 --field-trial-handle=2312,i,4771563937363638449,8845051678972593161,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Windows\System32\cmd.exe" /C copy *.js "C:\Users\Public\Downloads\Aleichem.js" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3264 --field-trial-handle=2352,i,486599353462054026,10701698972529270911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
50 144
Read events
49 640
Write events
427
Delete events
77
Modification events
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\7564 |
| Operation: | write | Name: | 0 |
Value: 0B0E109B7C072DA2BB574CA330E663CB4AEDD0230046DCEBDEDA8191EDED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C5118C3BD2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (7564) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
15
Suspicious files
439
Text files
135
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7564 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 2244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF113342.TMP | — | |
MD5:— | SHA256:— | |||
| 2244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF113342.TMP | — | |
MD5:— | SHA256:— | |||
| 2244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF113342.TMP | — | |
MD5:— | SHA256:— | |||
| 2244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7564 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:10049A06282F9B0F0C1191A25AB07904 | SHA256:8AF13FF5D1434DD592F853F81968EC33C73C7A7B17DF5311C469F73A4A86EFDE | |||
| 2244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF113342.TMP | — | |
MD5:— | SHA256:— | |||
| 2244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
93
DNS requests
86
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7564 | OUTLOOK.EXE | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5528 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5528 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
616 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1745626152&P2=404&P3=2&P4=eXQVZraRpQAt3D0ZSDZNA0g7NggsGB2WmwdESNWogphMvwNQhvN2Txlg%2f0%2fbs2zLsfFg4l27WVQviuJorl8yqQ%3d%3d | unknown | — | — | whitelisted |
6644 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/TCCerER0/0 | unknown | — | — | shared |
4488 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/TCCerER0/0 | unknown | — | — | shared |
616 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1745626152&P2=404&P3=2&P4=eXQVZraRpQAt3D0ZSDZNA0g7NggsGB2WmwdESNWogphMvwNQhvN2Txlg%2f0%2fbs2zLsfFg4l27WVQviuJorl8yqQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.48.23.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7564 | OUTLOOK.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7564 | OUTLOOK.EXE | 52.109.76.243:443 | roaming.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7564 | OUTLOOK.EXE | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ecs.office.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
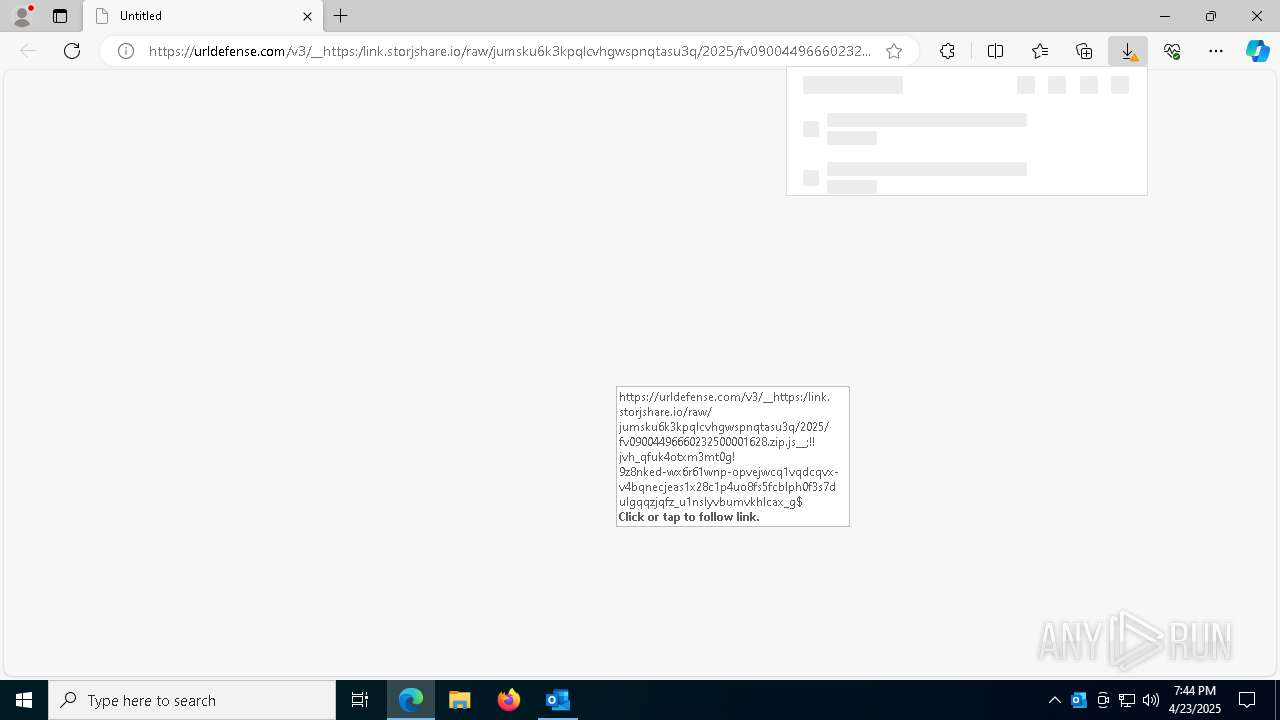
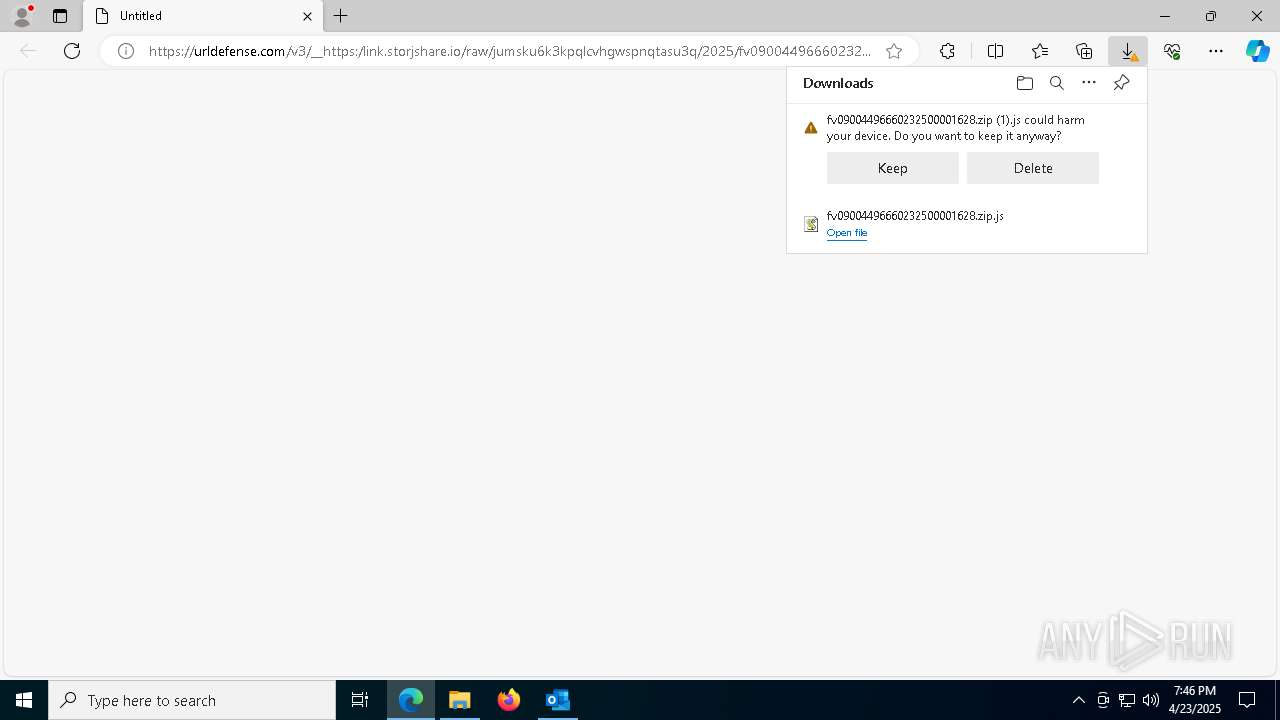
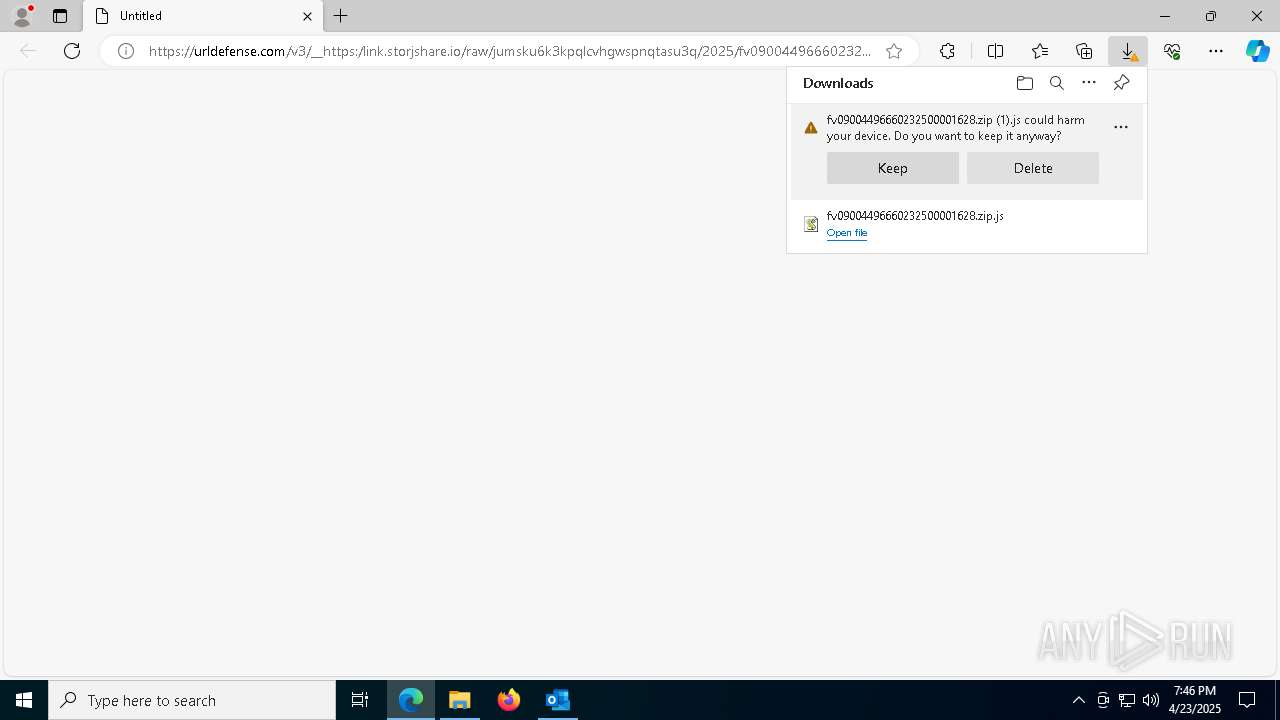
7788 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
7788 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
7788 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Commonly Actor Abused Online Service Domain (storjshare .io) |
7788 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (storjshare .io in TLS SNI) |
7788 | msedge.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Domain (link .storjshare .io in TLS SNI) |
7788 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Commonly Actor Abused Online Service Domain (storjshare .io) |
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
6456 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
7864 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |